| File name: | miner.exe |
| Full analysis: | https://app.any.run/tasks/d073c642-e4c2-4af6-9ec6-901a288b232a |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | June 10, 2025, 05:55:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | B100225BD1EC7796677D7CA06556329C |
| SHA1: | 60ABDFB558D06F676C873371CDD0A095EA148F81 |
| SHA256: | B8DB7784BAB5443758D779DC1C0D5298EC1EB79719EAD6AC03E5919DECB6D40A |
| SSDEEP: | 98304:IBfORzkpFYbLnVM1D5w0YLMRawafDuLB6hKTYJxfE7qmC+qkzvmIXFFNH+UHets/:rYtGXFQHTs |
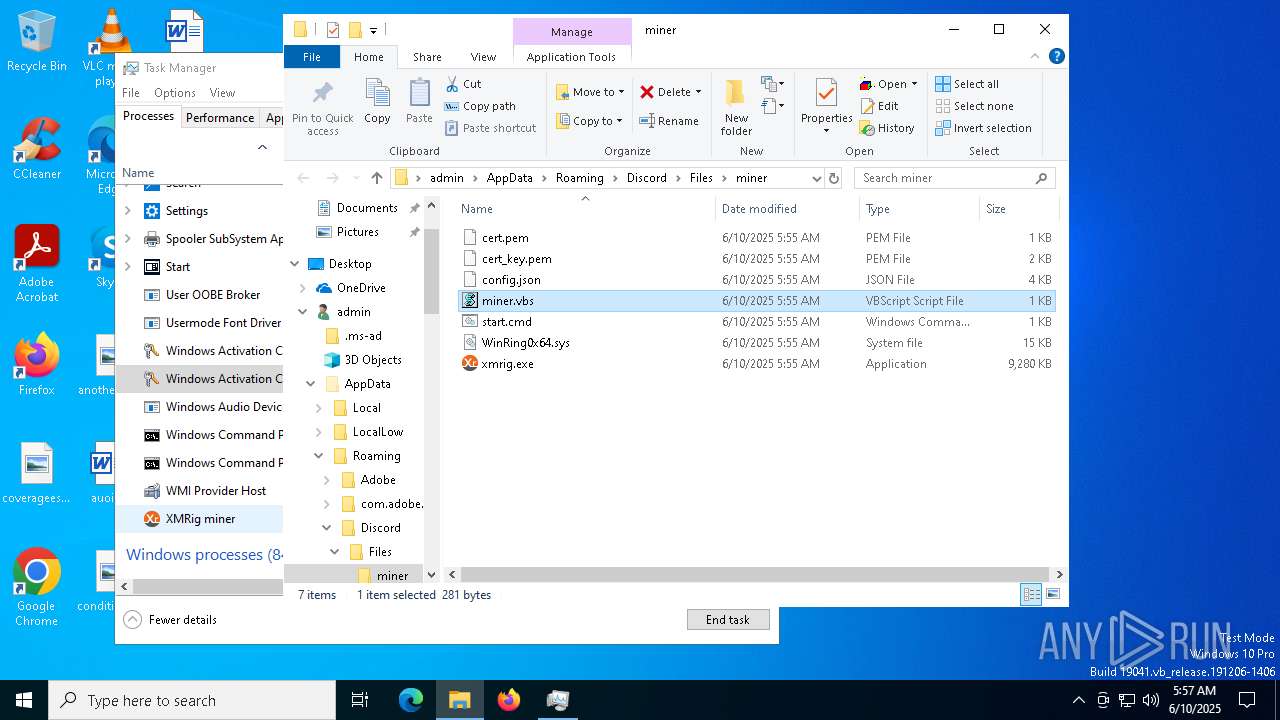
MALICIOUS
Vulnerable driver has been detected
- miner.exe (PID: 8056)
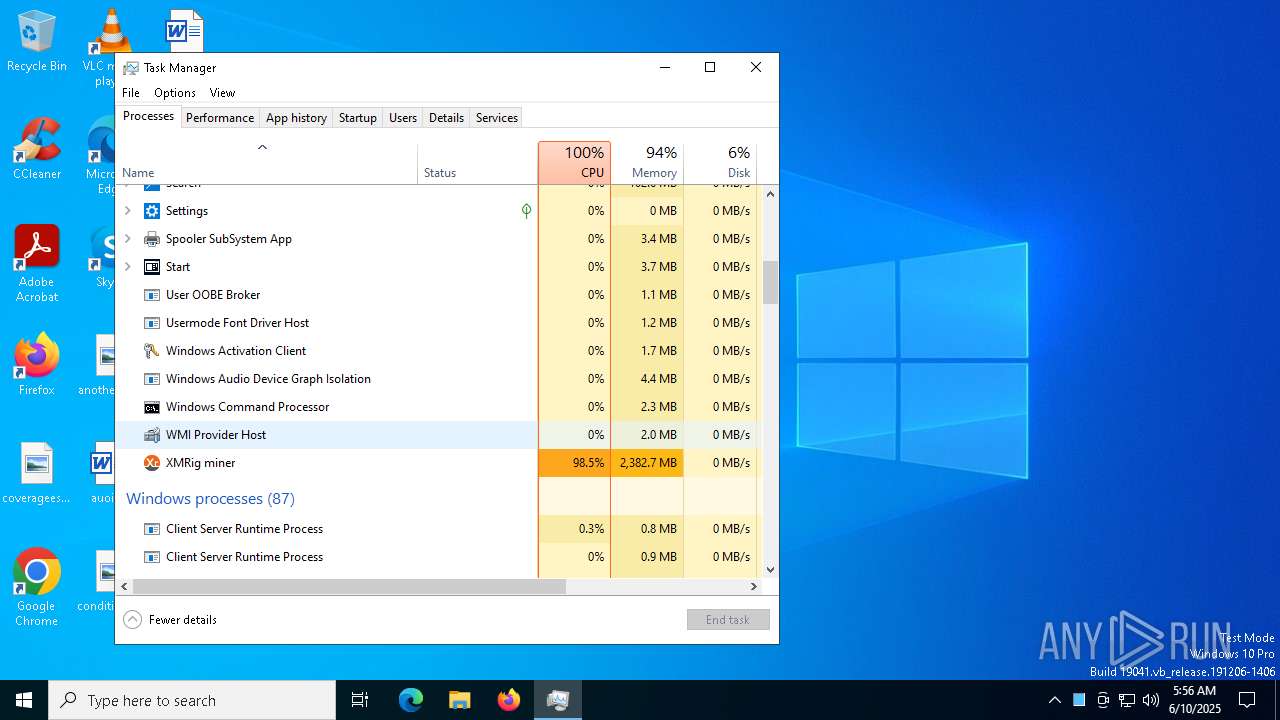
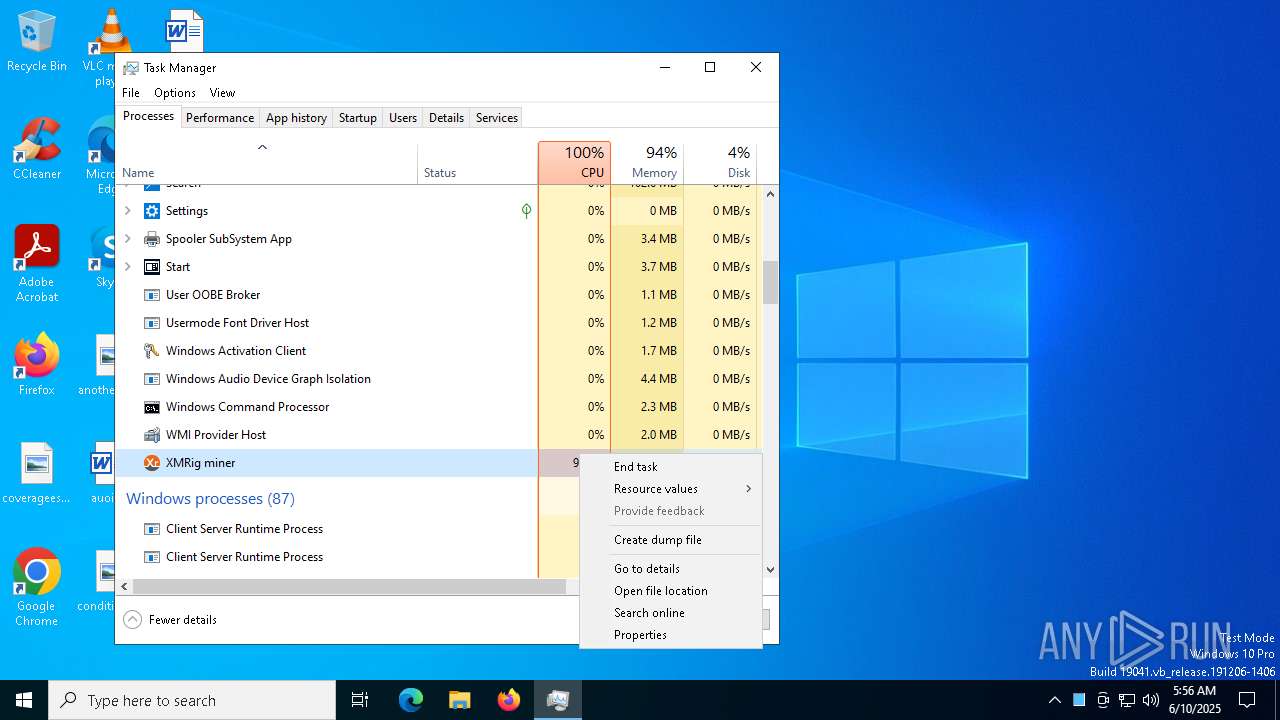
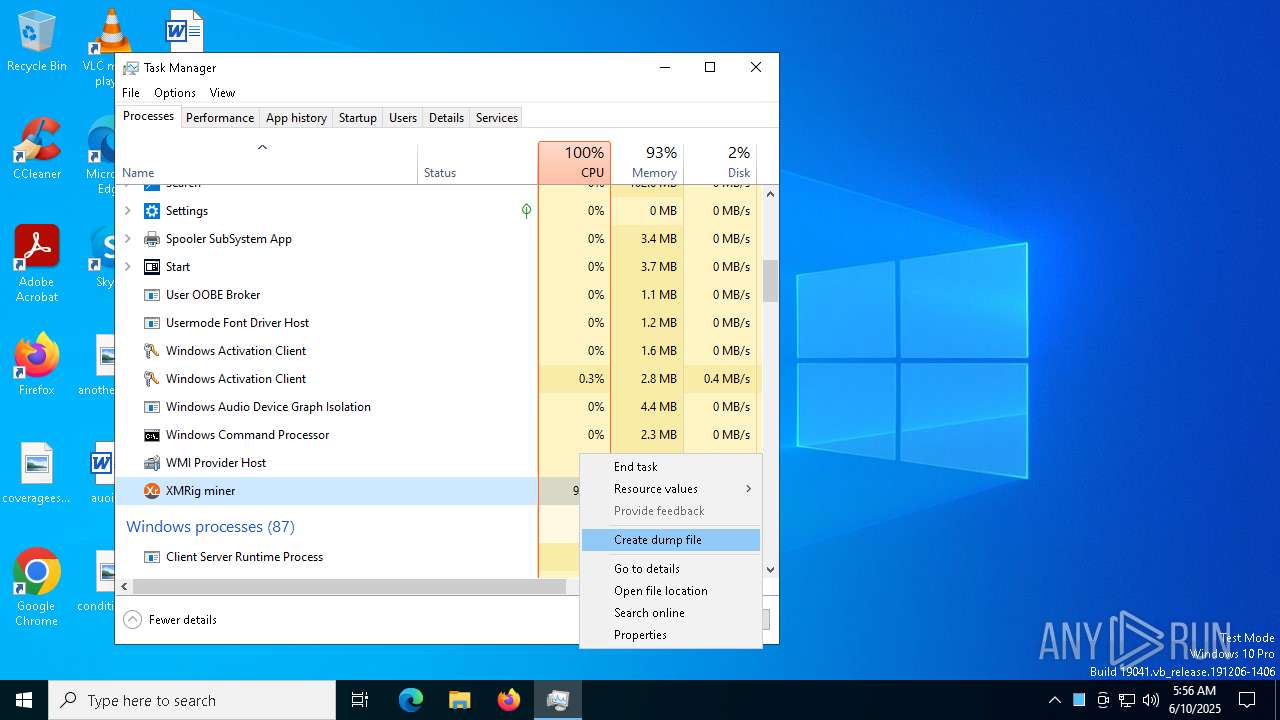
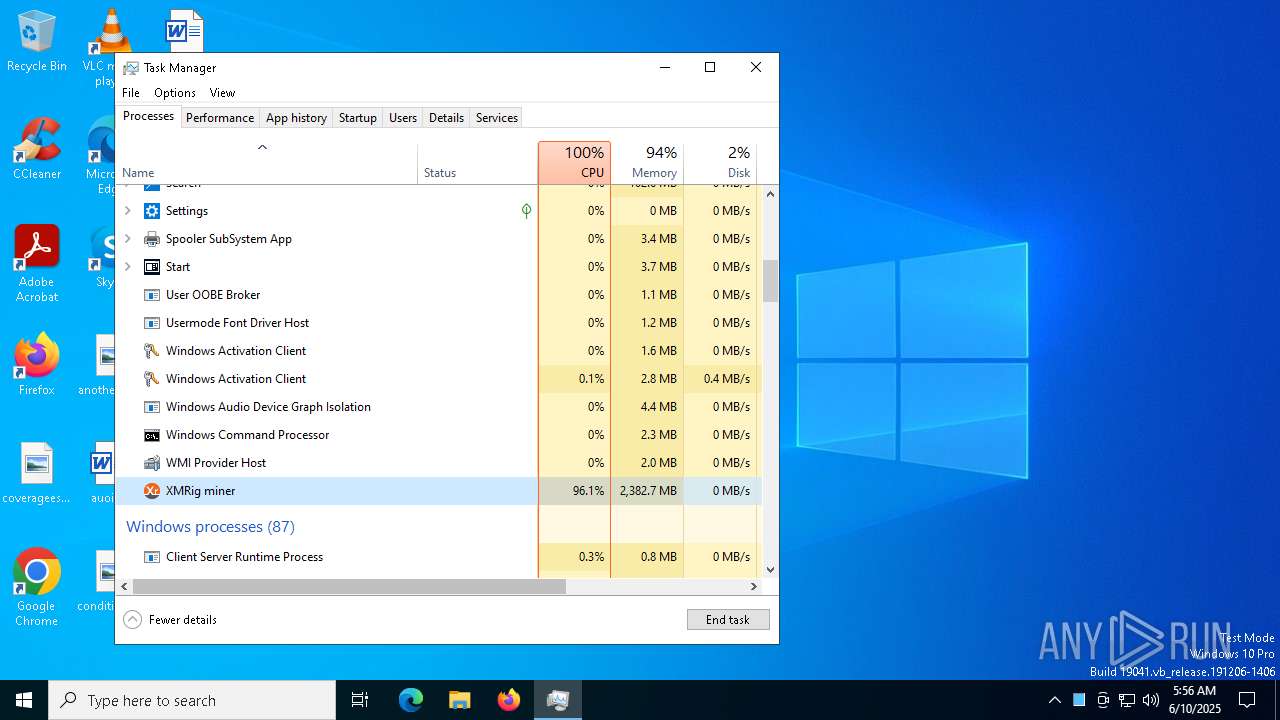
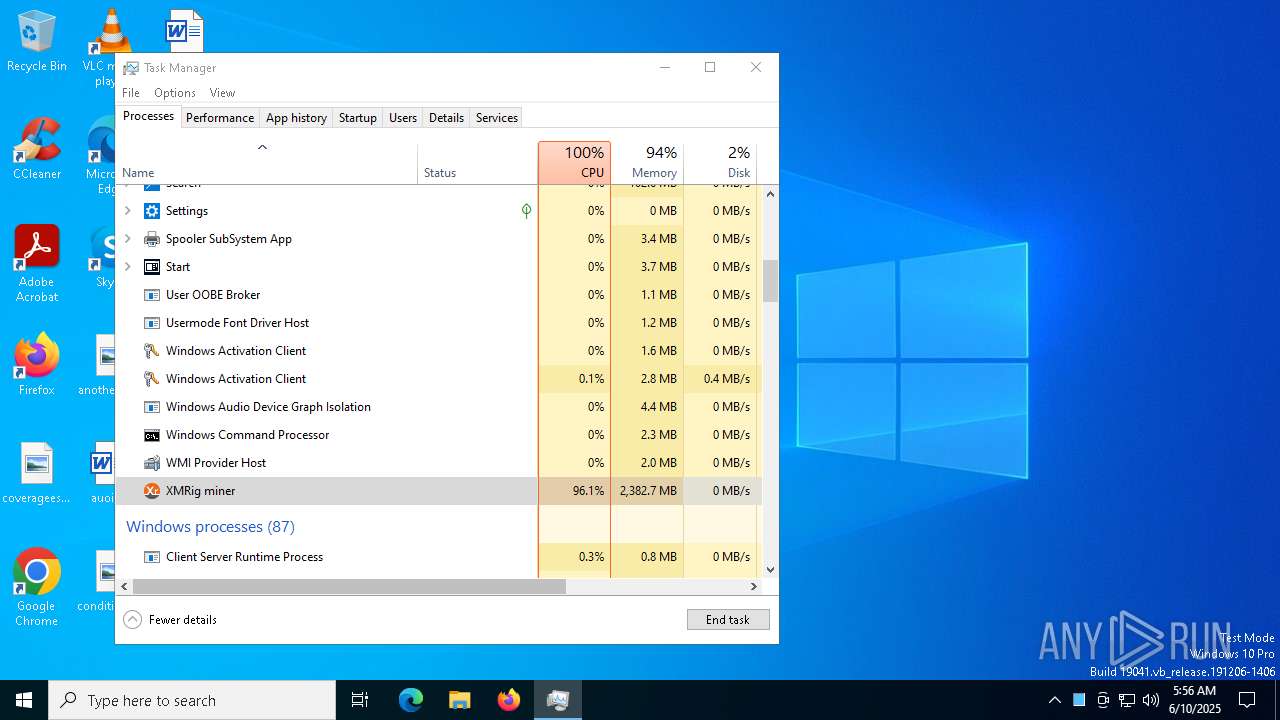
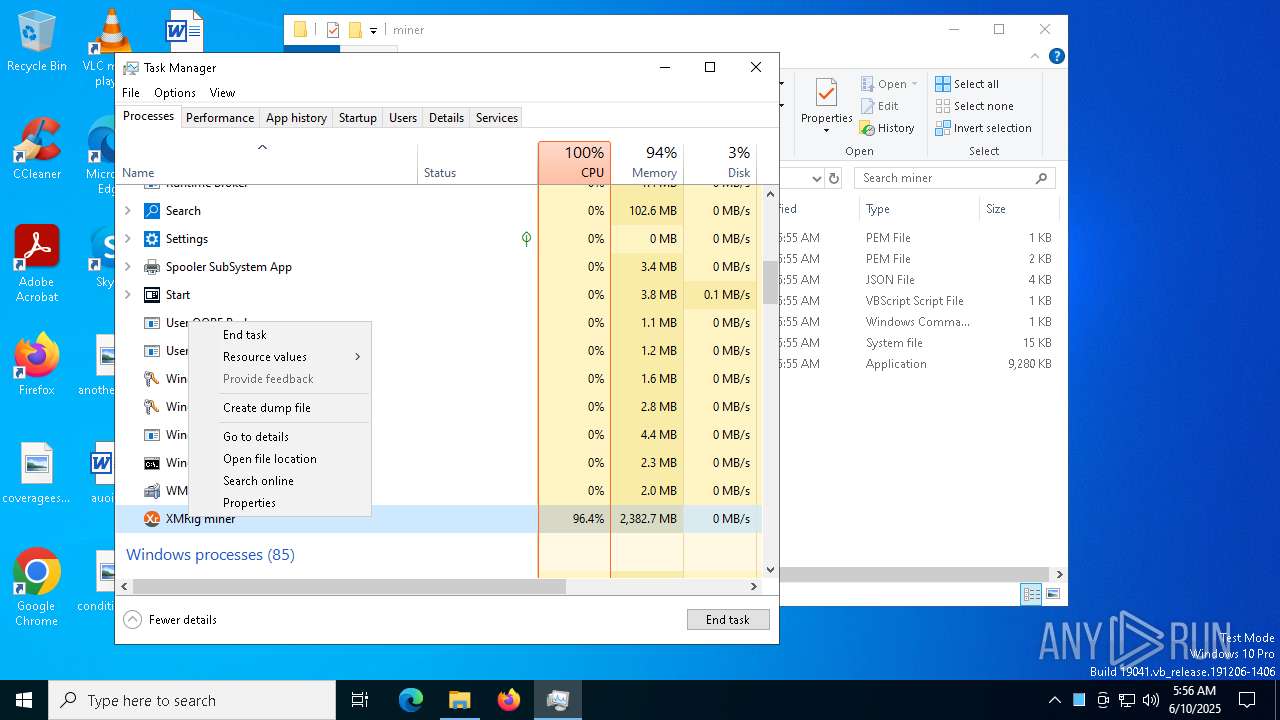
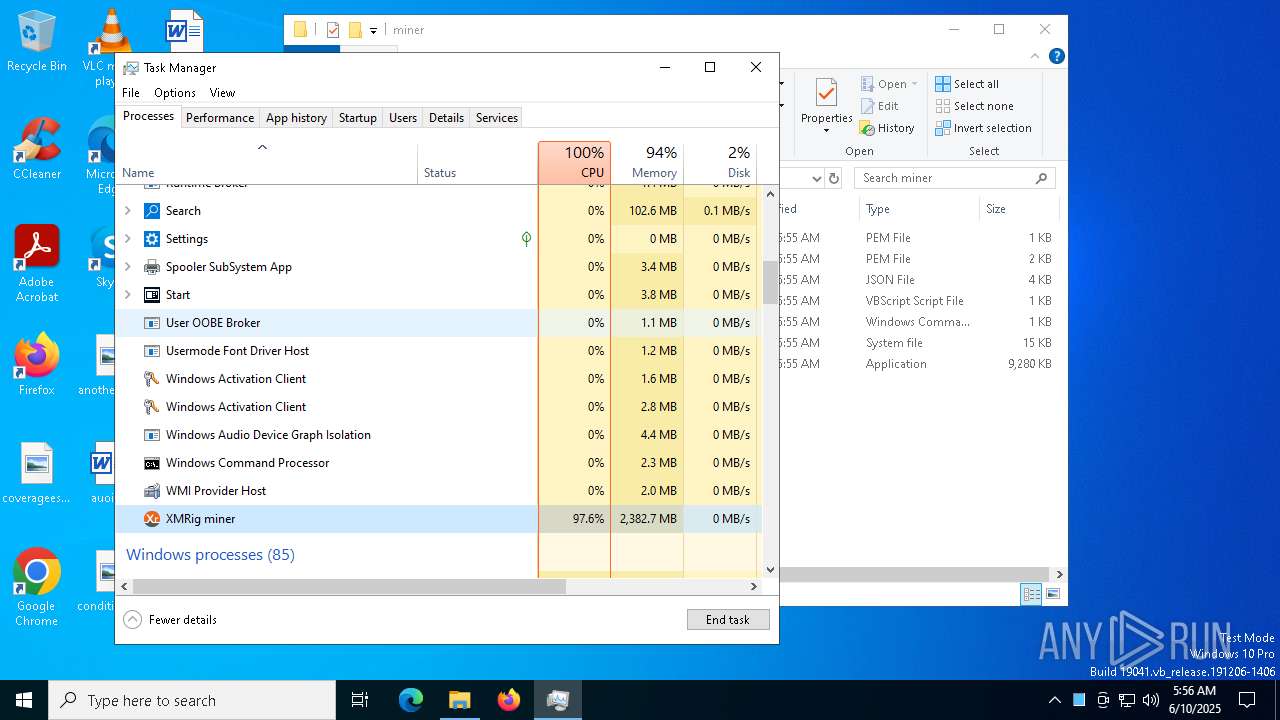
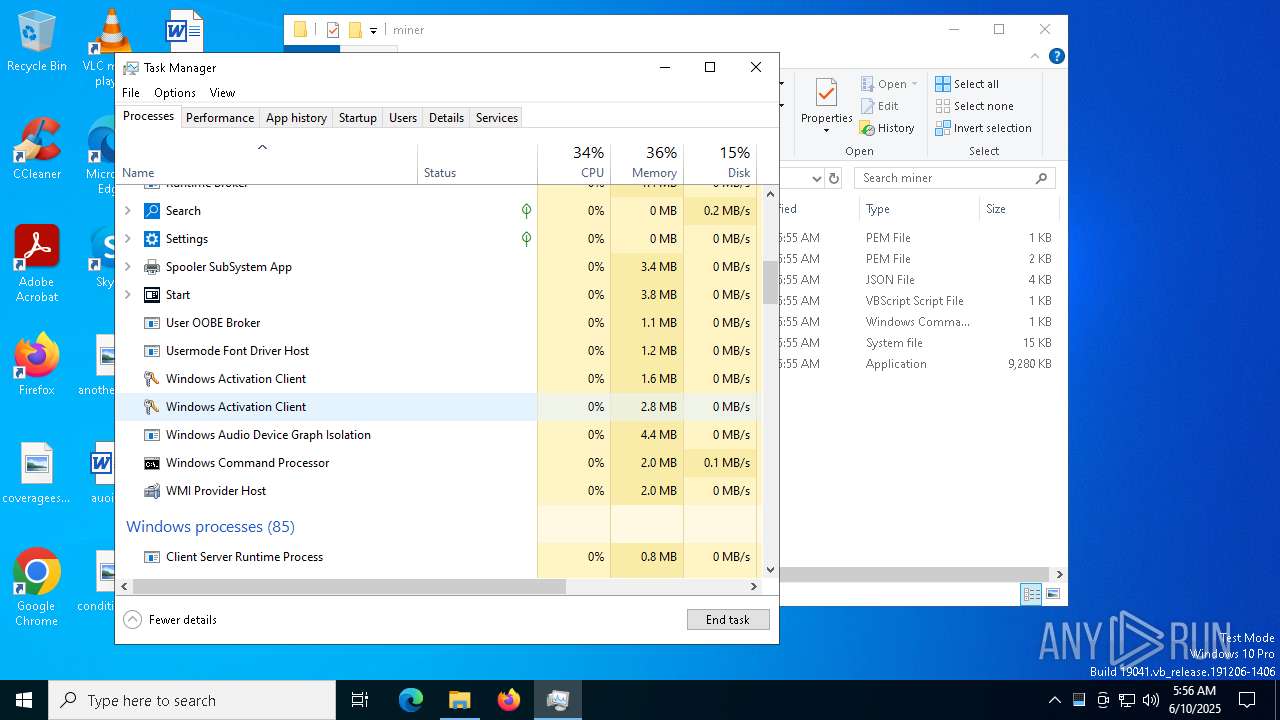
XMRig has been detected
- xmrig.exe (PID: 2852)
- xmrig.exe (PID: 8128)
MINER has been detected (SURICATA)
- svchost.exe (PID: 2196)
XMRIG has been detected (YARA)
- xmrig.exe (PID: 2852)
SUSPICIOUS
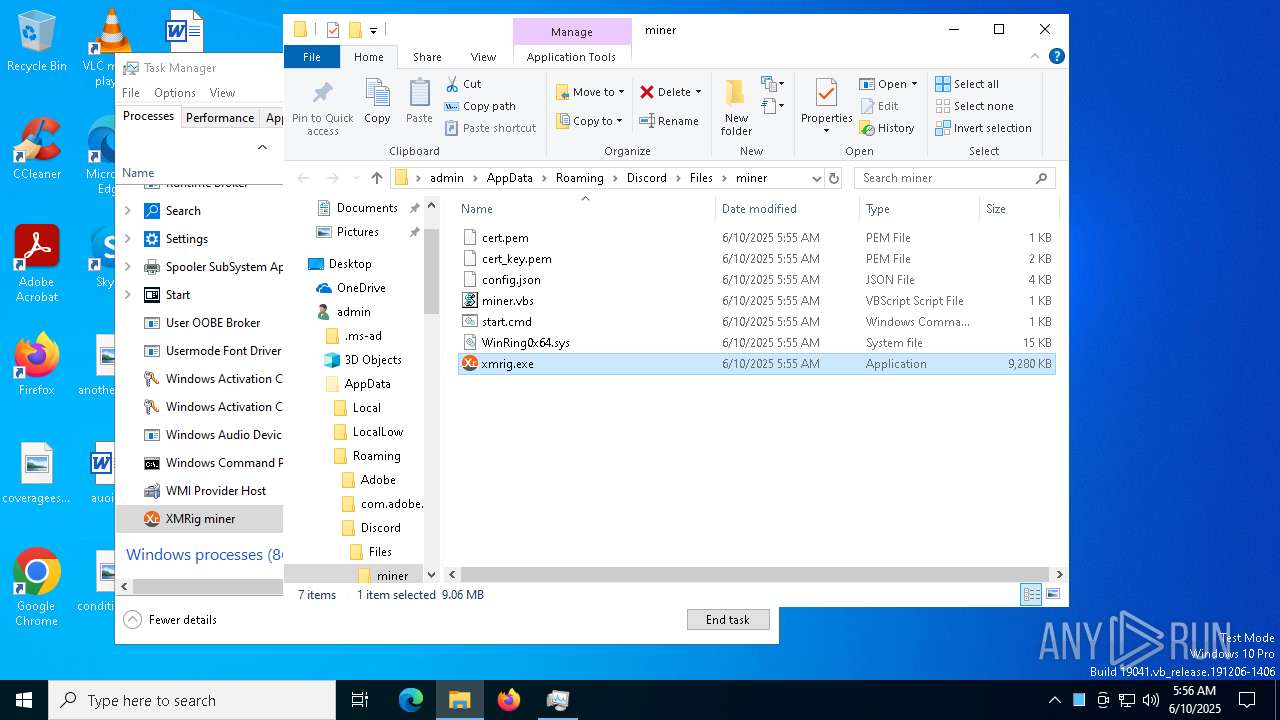
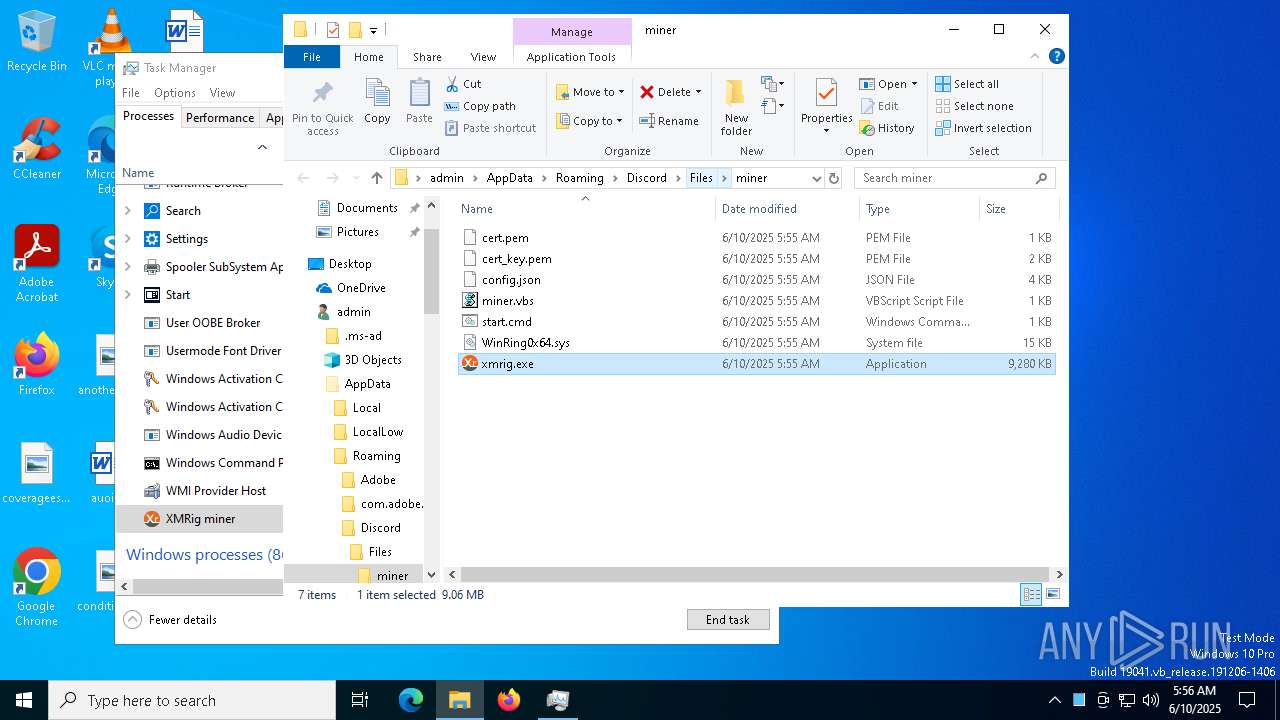
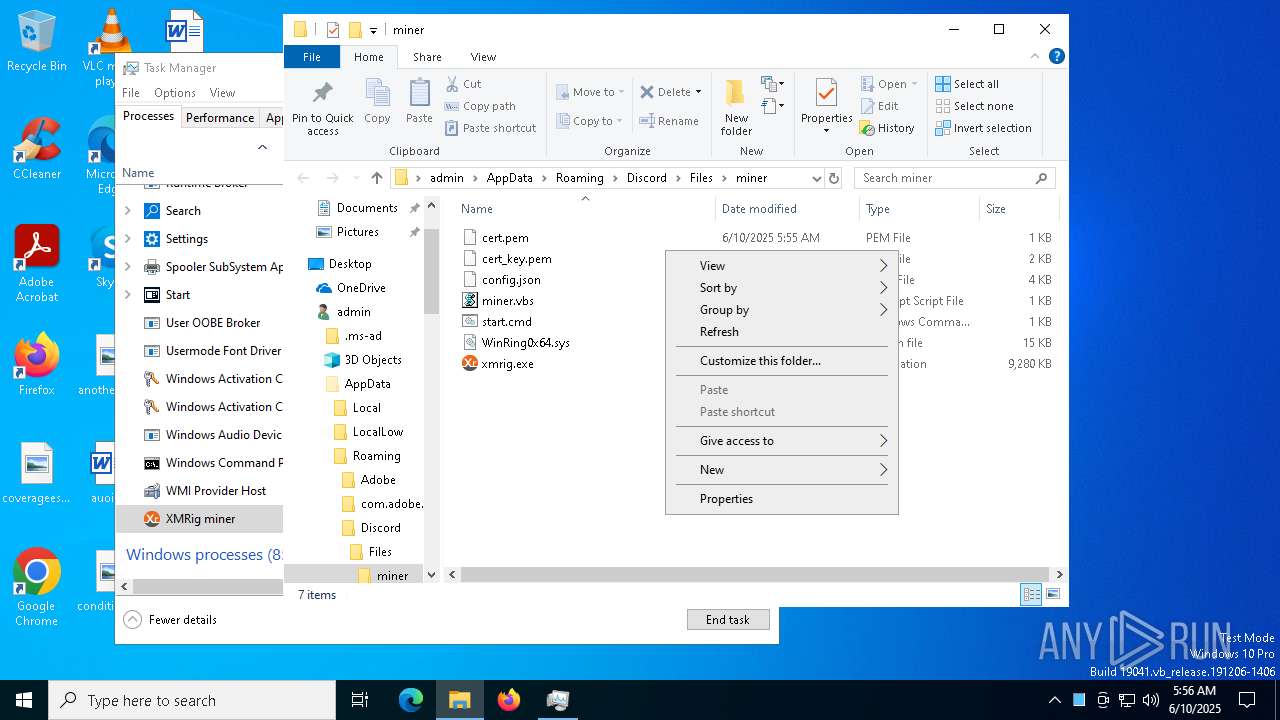
Executable content was dropped or overwritten
- miner.exe (PID: 8056)
Drops a system driver (possible attempt to evade defenses)
- miner.exe (PID: 8056)
Reads security settings of Internet Explorer
- miner.exe (PID: 8056)
Reads the date of Windows installation
- miner.exe (PID: 8056)
Runs shell command (SCRIPT)
- wscript.exe (PID: 4020)
- wscript.exe (PID: 7292)
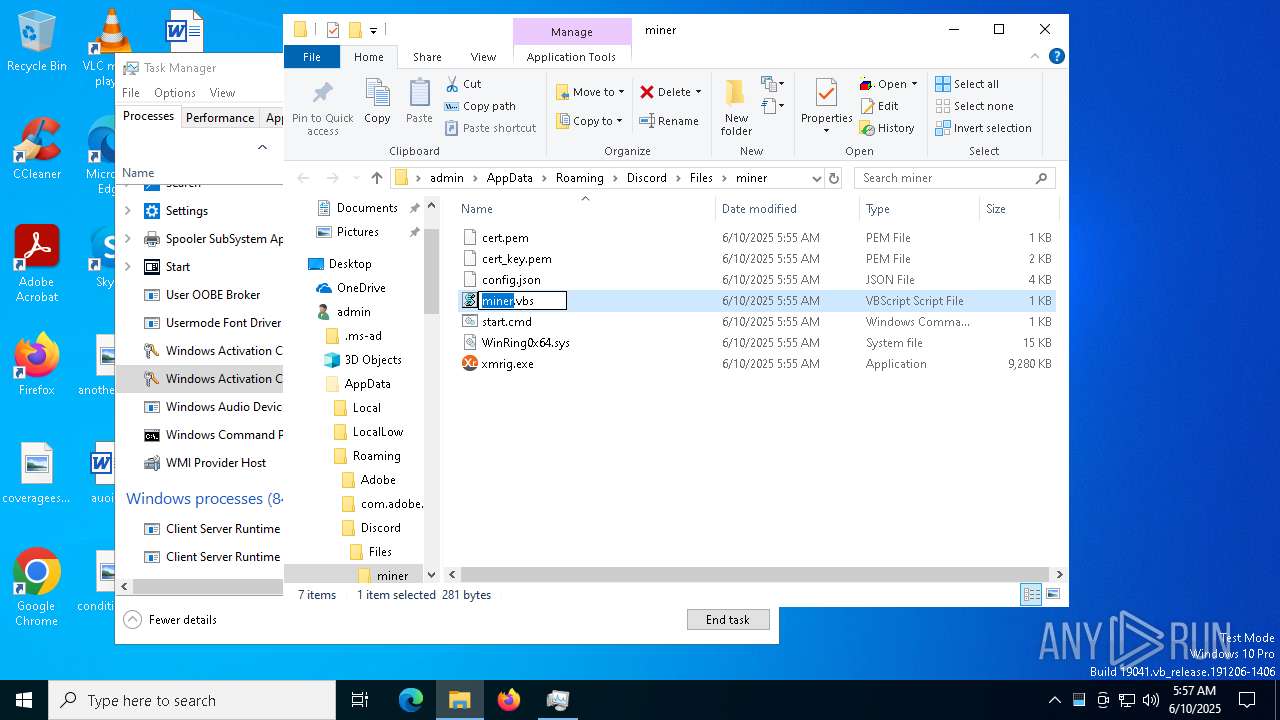
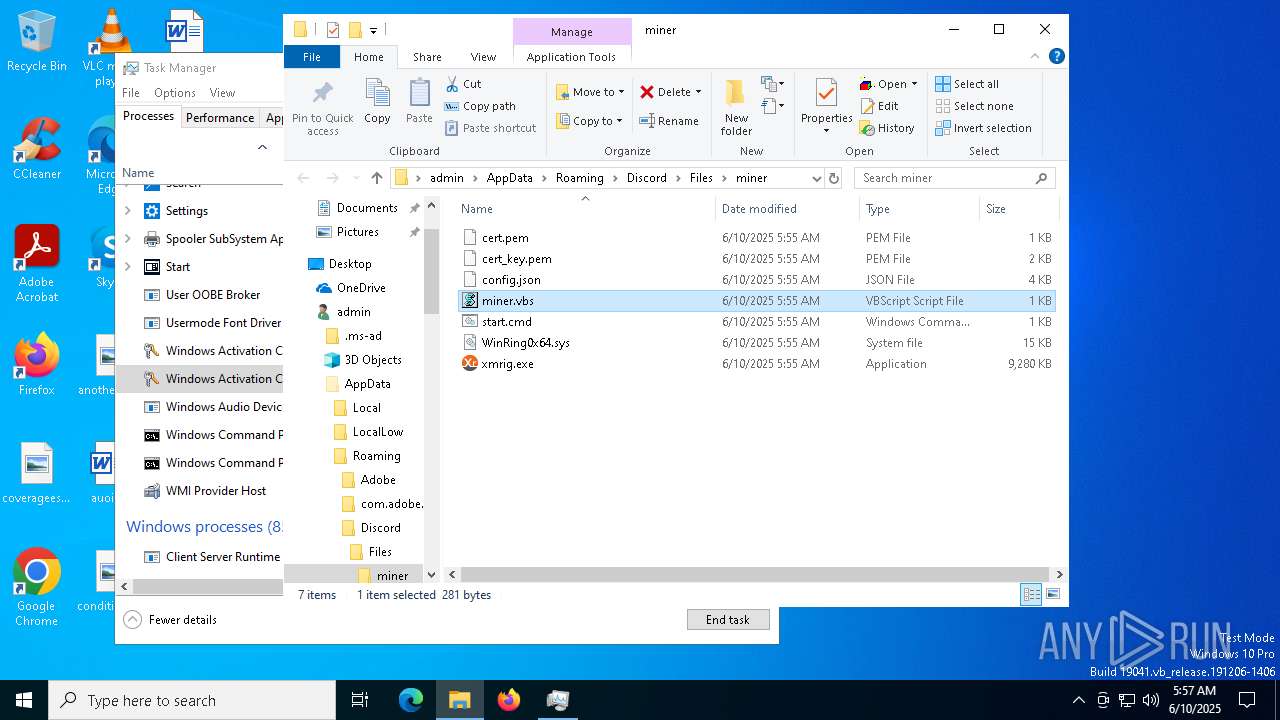
The process executes VB scripts
- miner.exe (PID: 8056)
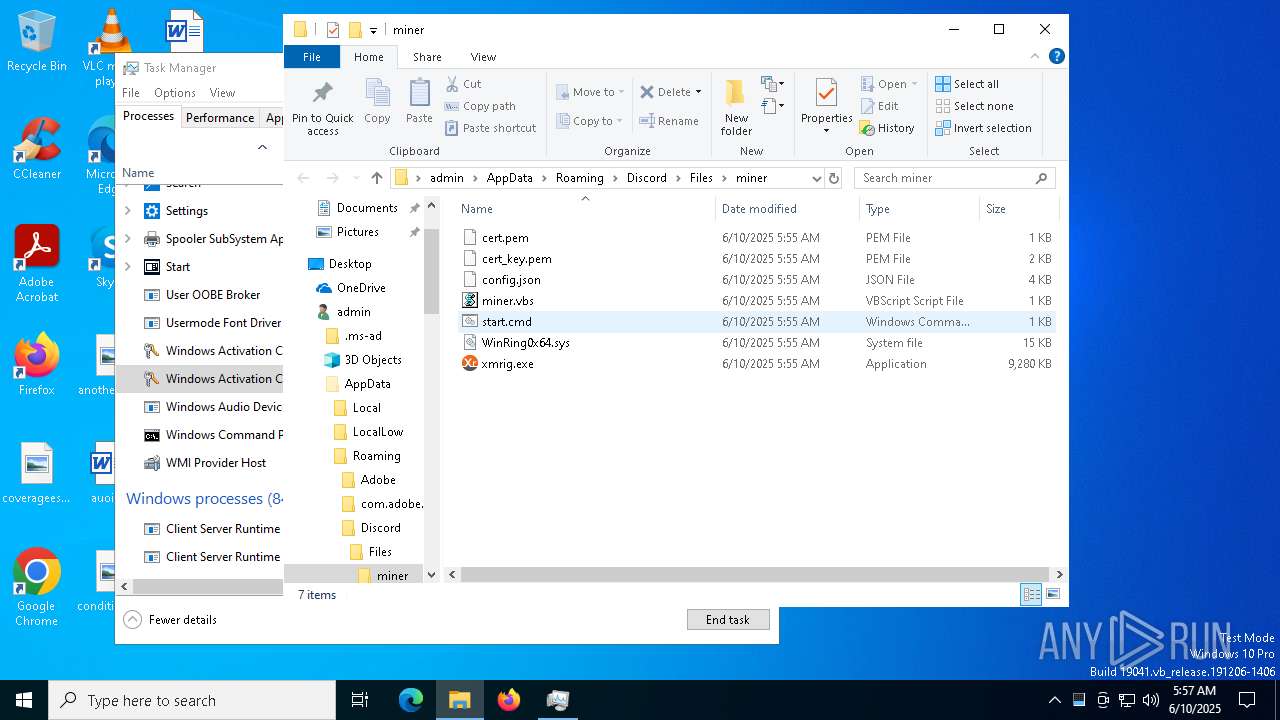
Executing commands from ".cmd" file
- wscript.exe (PID: 4020)
- wscript.exe (PID: 7292)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 4020)
- wscript.exe (PID: 7292)
The executable file from the user directory is run by the CMD process
- xmrig.exe (PID: 2852)
- xmrig.exe (PID: 8128)
Connects to unusual port
- xmrig.exe (PID: 2852)
- xmrig.exe (PID: 8128)
Crypto Currency Mining Activity Detected
- svchost.exe (PID: 2196)
INFO
Checks supported languages
- miner.exe (PID: 8056)
- xmrig.exe (PID: 2852)
- xmrig.exe (PID: 8128)
Creates files or folders in the user directory
- miner.exe (PID: 8056)
- xmrig.exe (PID: 2852)
Reads the machine GUID from the registry
- miner.exe (PID: 8056)
- xmrig.exe (PID: 2852)
- xmrig.exe (PID: 8128)
The sample compiled with japanese language support
- miner.exe (PID: 8056)
Reads the computer name
- miner.exe (PID: 8056)
- xmrig.exe (PID: 2852)
- xmrig.exe (PID: 8128)
Reads Microsoft Office registry keys
- miner.exe (PID: 8056)
Process checks computer location settings
- miner.exe (PID: 8056)
Reads the software policy settings
- slui.exe (PID: 7424)
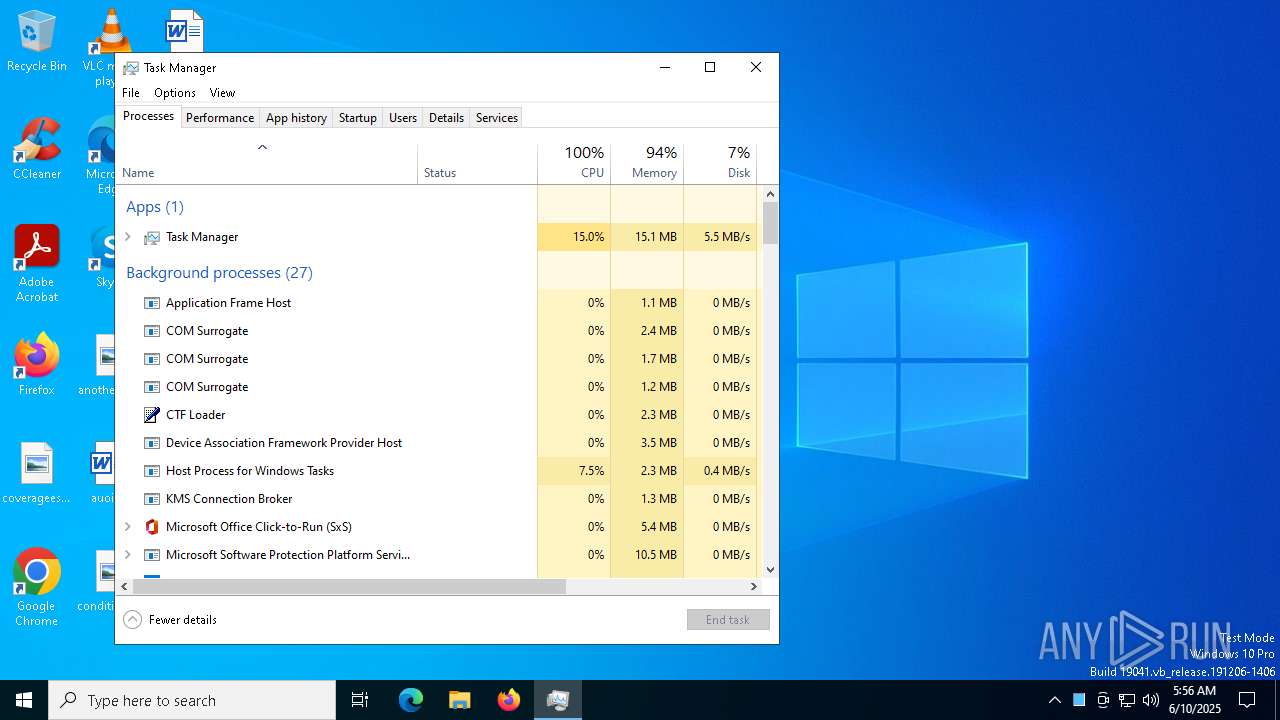
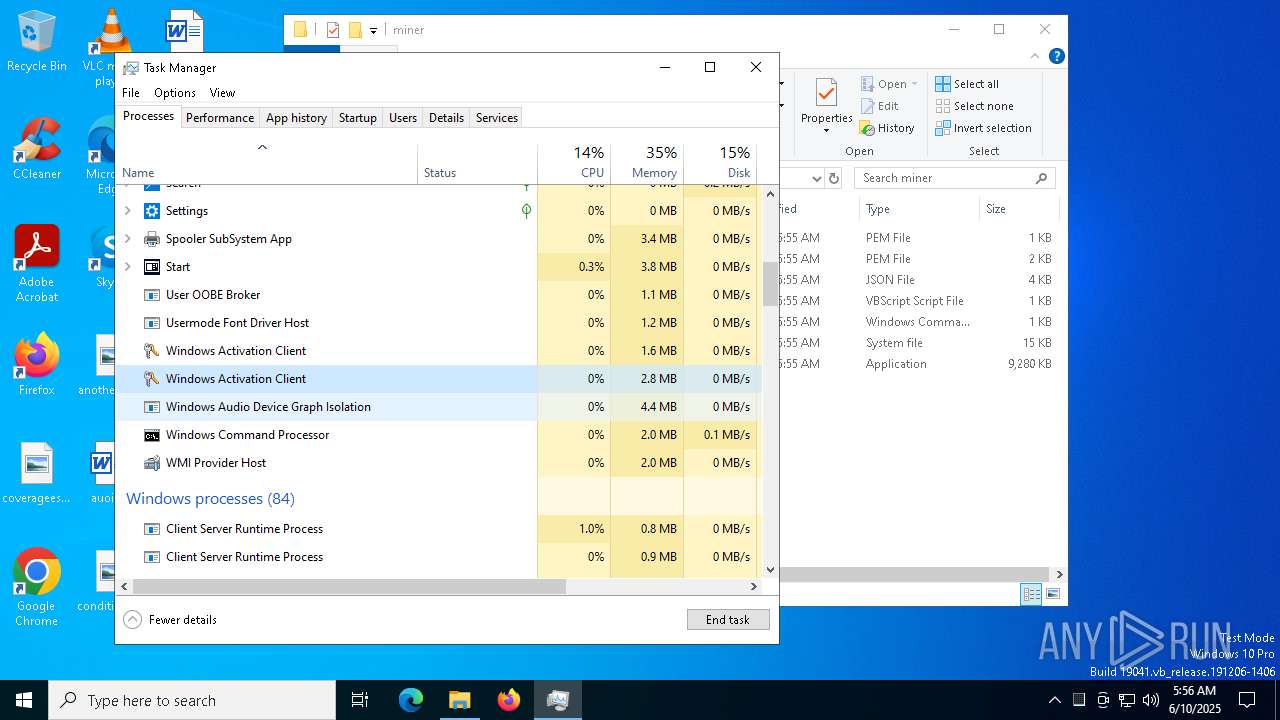
Manual execution by a user
- Taskmgr.exe (PID: 6184)
- Taskmgr.exe (PID: 7928)
- wscript.exe (PID: 7292)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 7928)
Checks proxy server information
- slui.exe (PID: 7424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:06:10 05:54:15+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 3902976 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3bac9e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 1.0.0.0 |
| InternalName: | miner.exe |
| LegalCopyright: | |
| OriginalFileName: | miner.exe |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
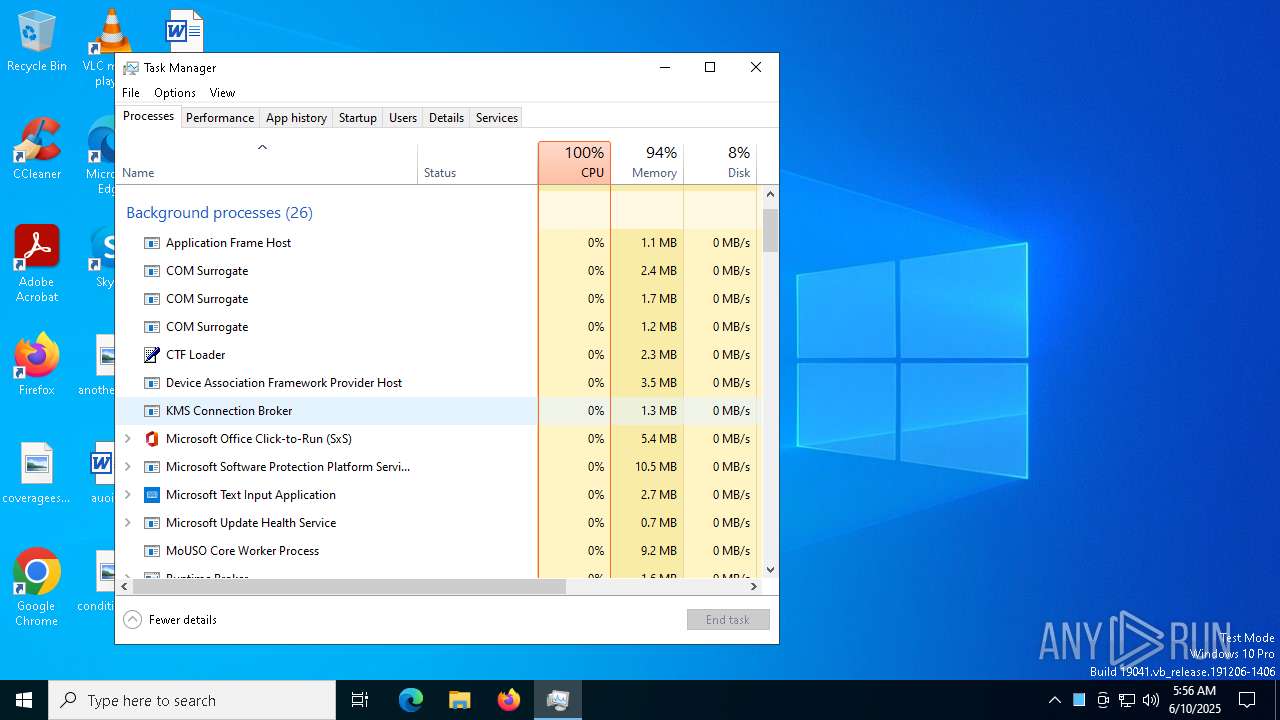
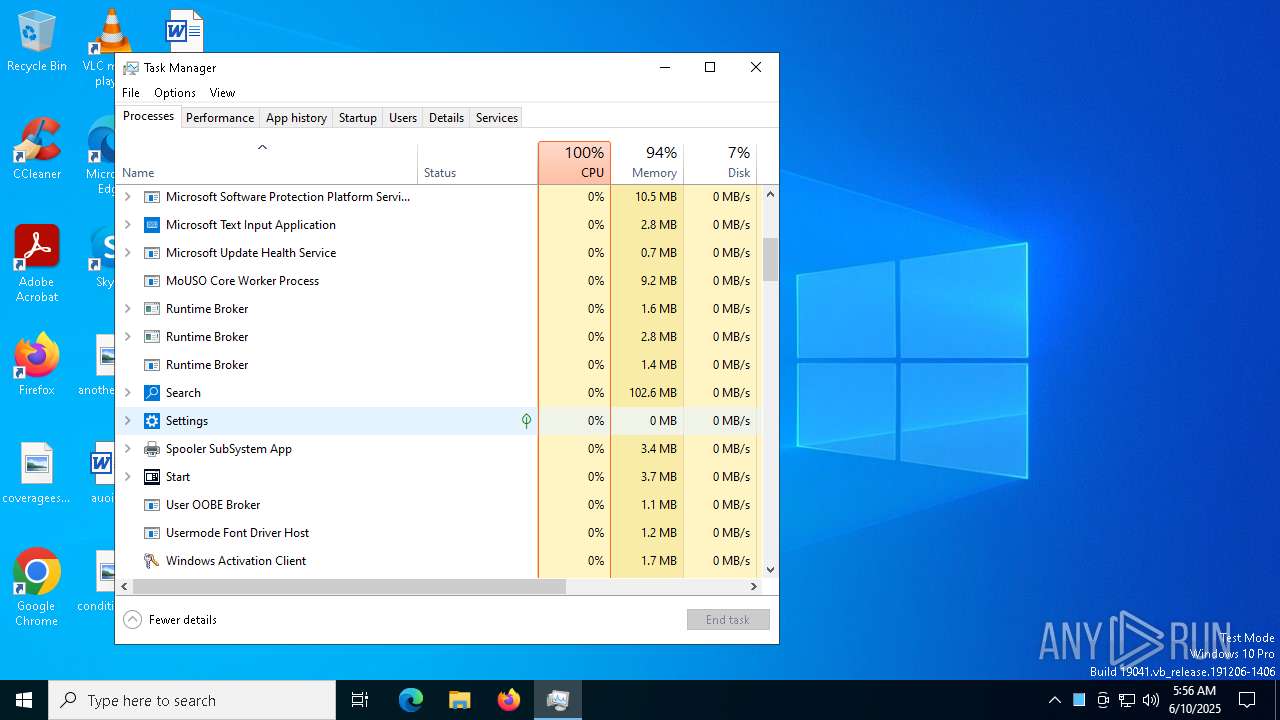
Total processes
141
Monitored processes
14
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2552 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2852 | xmrig.exe | C:\Users\admin\AppData\Roaming\Discord\Files\miner\xmrig.exe | cmd.exe | ||||||||||||
User: admin Company: www.xmrig.com Integrity Level: MEDIUM Description: XMRig miner Exit code: 1 Version: 6.22.3 Modules
| |||||||||||||||
| 4020 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\AppData\Roaming\Discord\Files\miner\miner.vbs" | C:\Windows\System32\wscript.exe | — | miner.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 4164 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6184 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6740 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7292 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\AppData\Roaming\Discord\Files\miner\miner.vbs" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 7424 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7428 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Roaming\Discord\Files\miner\start.cmd" " | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 065
Read events
5 062
Write events
2
Delete events
1
Modification events
| (PID) Process: | (8056) miner.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbs\OpenWithProgids |
| Operation: | write | Name: | VBSFile |
Value: | |||
| (PID) Process: | (7928) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | delete value | Name: | Preferences |
Value: | |||
| (PID) Process: | (7928) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 0D00000060000000600000006800000068000000E3010000DC010000000001000000008000000080D8010080DF010080000100016B00000034000000130300008C020000E80300000000000000000000000000000F000000010000000000000058AABE1FF67F00000000000000000000000000002E0100001E0000008990000000000000FF00000001015002000000000D0000000000000098AABE1FF67F00000000000000000000FFFFFFFF960000001E0000008B900000010000000000000000101001000000000300000000000000B0AABE1FF67F00000000000000000000FFFFFFFF780000001E0000008C900000020000000000000001021200000000000400000000000000C8AABE1FF67F00000000000000000000FFFFFFFF960000001E0000008D900000030000000000000000011001000000000200000000000000E8AABE1FF67F00000000000000000000FFFFFFFF320000001E0000008A90000004000000000000000008200100000000050000000000000000ABBE1FF67F00000000000000000000FFFFFFFFC80000001E0000008E90000005000000000000000001100100000000060000000000000028ABBE1FF67F00000000000000000000FFFFFFFF040100001E0000008F90000006000000000000000001100100000000070000000000000050ABBE1FF67F00000000000000000000FFFFFFFF49000000490000009090000007000000000000000004250000000000080000000000000080AABE1FF67F00000000000000000000FFFFFFFF49000000490000009190000008000000000000000004250000000000090000000000000070ABBE1FF67F00000000000000000000FFFFFFFF490000004900000092900000090000000000000000042508000000000A0000000000000088ABBE1FF67F00000000000000000000FFFFFFFF4900000049000000939000000A0000000000000000042508000000000B00000000000000A8ABBE1FF67F00000000000000000000FFFFFFFF490000004900000039A000000B0000000000000000042509000000001C00000000000000C8ABBE1FF67F00000000000000000000FFFFFFFFC8000000490000003AA000000C0000000000000000011009000000001D00000000000000F0ABBE1FF67F00000000000000000000FFFFFFFF64000000490000004CA000000D0000000000000000021508000000001E0000000000000010ACBE1FF67F00000000000000000000FFFFFFFF64000000490000004DA000000E000000000000000002150800000000030000000A000000010000000000000058AABE1FF67F0000000000000000000000000000D70000001E0000008990000000000000FF00000001015002000000000400000000000000C8AABE1FF67F0000000000000000000001000000960000001E0000008D900000010000000000000001011000000000000300000000000000B0AABE1FF67F00000000000000000000FFFFFFFF640000001E0000008C900000020000000000000000021000000000000C0000000000000040ACBE1FF67F0000000000000000000003000000640000001E00000094900000030000000000000001021000000000000D0000000000000068ACBE1FF67F00000000000000000000FFFFFFFF640000001E00000095900000040000000000000000011001000000000E0000000000000090ACBE1FF67F0000000000000000000005000000320000001E00000096900000050000000000000001042001000000000F00000000000000B8ACBE1FF67F0000000000000000000006000000320000001E00000097900000060000000000000001042001000000001000000000000000D8ACBE1FF67F0000000000000000000007000000460000001E00000098900000070000000000000001011001000000001100000000000000F8ACBE1FF67F00000000000000000000FFFFFFFF640000001E0000009990000008000000000000000001100100000000060000000000000028ABBE1FF67F0000000000000000000009000000040100001E0000008F9000000900000000000000010110010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000040000000B000000010000000000000058AABE1FF67F0000000000000000000000000000D70000001E0000009E90000000000000FF0000000101500200000000120000000000000020ADBE1FF67F00000000000000000000FFFFFFFF2D0000001E0000009B90000001000000000000000004200100000000140000000000000040ADBE1FF67F00000000000000000000FFFFFFFF640000001E0000009D90000002000000000000000001100100000000130000000000000068ADBE1FF67F00000000000000000000FFFFFFFF640000001E0000009C900000030000000000000000011001000000000300000000000000B0AABE1FF67F00000000000000000000FFFFFFFF640000001E0000008C90000004000000000000000102100000000000070000000000000050ABBE1FF67F000000000000000000000500000049000000490000009090000005000000000000000104210000000000080000000000000080AABE1FF67F000000000000000000000600000049000000490000009190000006000000000000000104210000000000090000000000000070ABBE1FF67F0000000000000000000007000000490000004900000092900000070000000000000001042108000000000A0000000000000088ABBE1FF67F0000000000000000000008000000490000004900000093900000080000000000000001042108000000000B00000000000000A8ABBE1FF67F0000000000000000000009000000490000004900000039A00000090000000000000001042109000000001C00000000000000C8ABBE1FF67F000000000000000000000A00000064000000490000003AA000000A00000000000000000110090000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000200000008000000010000000000000058AABE1FF67F0000000000000000000000000000C60000001E000000B090000000000000FF0000000101500200000000150000000000000088ADBE1FF67F00000000000000000000FFFFFFFF6B0000001E000000B1900000010000000000000000042500000000001600000000000000B8ADBE1FF67F00000000000000000000FFFFFFFF6B0000001E000000B2900000020000000000000000042500000000001800000000000000E0ADBE1FF67F00000000000000000000FFFFFFFF6B0000001E000000B490000003000000000000000004250000000000170000000000000008AEBE1FF67F00000000000000000000FFFFFFFF6B0000001E000000B390000004000000000000000004250000000000190000000000000040AEBE1FF67F00000000000000000000FFFFFFFFA00000001E000000B5900000050000000000000000042001000000001A0000000000000070AEBE1FF67F00000000000000000000FFFFFFFF7D0000001E000000B6900000060000000000000000042001000000001B00000000000000A0AEBE1FF67F00000000000000000000FFFFFFFF7D0000001E000000B790000007000000000000000004200100000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA00000000000000000000000000000000000000000000009D200000200000009100000064000000320000006400000050000000320000003200000028000000500000003C0000005000000050000000320000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C00000050000000500000009700000032000000780000003200000050000000500000005000000050000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C00000000000000000000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA000000000000000000000000000000000000009D200000200000009100000064000000320000009700000050000000320000003200000028000000500000003C000000500000005000000032000000500000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C0000005000000064000000780000003200000078000000780000003200000050000000500000005000000050000000C8000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C0000002D0000002E0000002F00000000000000000000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000100000002000000030000000400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000001000000000000000000000000000000 | |||
Executable files
2
Suspicious files
1
Text files
5
Unknown types
0
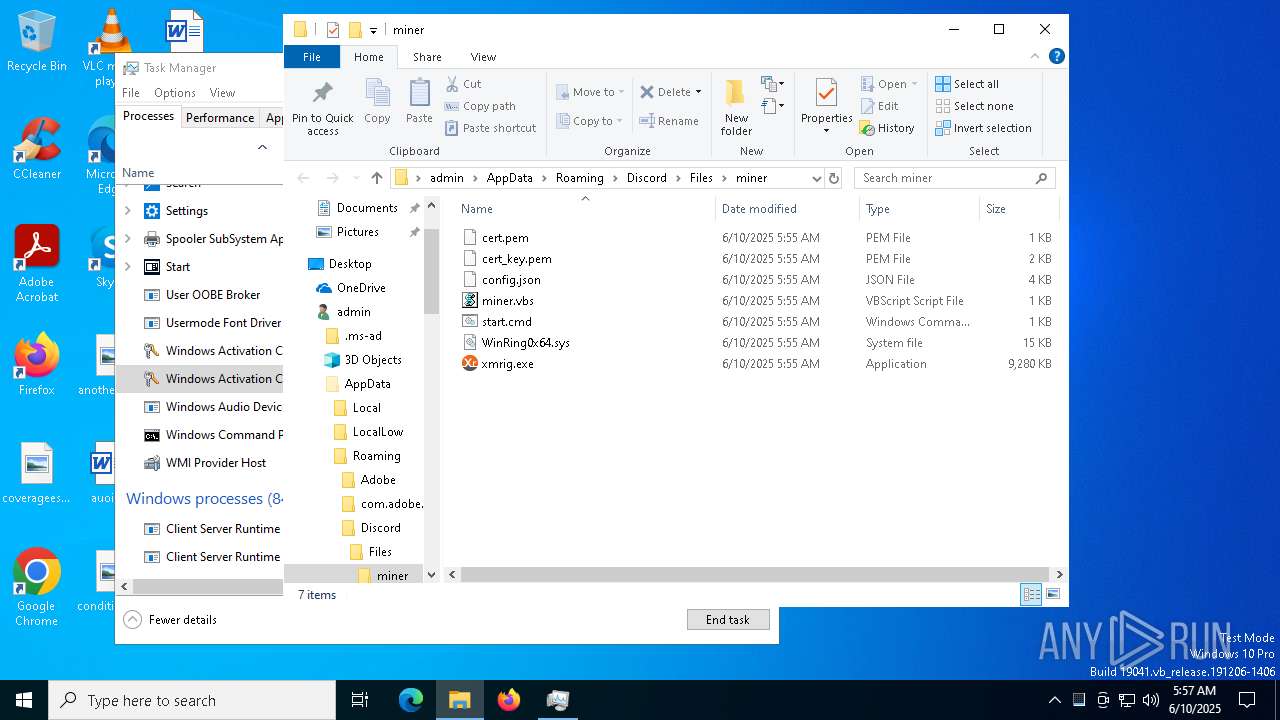
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8056 | miner.exe | C:\Users\admin\AppData\Roaming\Discord\Files\miner\start.cmd | text | |
MD5:EAF3A00CC0465F8AF471B849ADA29843 | SHA256:8E70EF38FE14A2EE2848DF3D6F7E260D1CAF8CFC15DE694D678B8AF151D62333 | |||
| 8056 | miner.exe | C:\Users\admin\AppData\Roaming\Discord\Files\miner\xmrig.exe | executable | |
MD5:5FB59EFD14651E2D750A817B7FCFA690 | SHA256:71AA7D419B24BFCE6AD7D5ED9F293ABB373274C9EF4168A53C42CD289D926C2A | |||
| 8056 | miner.exe | C:\Users\admin\AppData\Roaming\Discord\Files\miner\miner.vbs | text | |
MD5:32A50C0244E9BB34CADD51D55173D3A7 | SHA256:D93E4897A479F3F70EA97A09C86F7331030268D56735A3EB76745B61029EBE40 | |||
| 2852 | xmrig.exe | C:\Users\admin\AppData\Roaming\Discord\Files\miner\cert.pem | text | |
MD5:CA88420405426B3BE34244A961A48513 | SHA256:8337CE5269A70A2367E19CCDB3A831CDA94FAF8F2E66386477C1380FFF768173 | |||
| 7928 | Taskmgr.exe | C:\Users\admin\AppData\Local\D3DSCache\3534848bb9f4cb71\F4EB2D6C-ED2B-4BDD-AD9D-F913287E6768.lock | text | |
MD5:F49655F856ACB8884CC0ACE29216F511 | SHA256:7852FCE59C67DDF1D6B8B997EAA1ADFAC004A9F3A91C37295DE9223674011FBA | |||
| 8056 | miner.exe | C:\Users\admin\AppData\Roaming\Discord\Files\miner\WinRing0x64.sys | executable | |
MD5:0C0195C48B6B8582FA6F6373032118DA | SHA256:11BD2C9F9E2397C9A16E0990E4ED2CF0679498FE0FD418A3DFDAC60B5C160EE5 | |||
| 2852 | xmrig.exe | C:\Users\admin\AppData\Roaming\Discord\Files\miner\cert_key.pem | text | |
MD5:F39CE8D9B3F62E62166B64DB43313269 | SHA256:53CAB103CC81C1824A4B16FBCC72E7C41251F937602AA09EFA198477AEF166A3 | |||
| 8056 | miner.exe | C:\Users\admin\AppData\Roaming\Discord\Files\miner\config.json | binary | |
MD5:C9AF6B9C545380412A381D5BA5548A05 | SHA256:7CD9A550EA0550B09F4C4D54DADE04033F21CDD2CF6F75EFED850C33F6E7E631 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
27
DNS requests
15
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.11:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.11:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6544 | svchost.exe | 40.126.32.136:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2852 | xmrig.exe | 141.95.126.31:1111 | de.monero.herominers.com | OVH SAS | FR | malicious |
6544 | svchost.exe | 20.190.160.131:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
5064 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
de.monero.herominers.com |
| malicious |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Crypto Currency Mining Activity Detected | ET COINMINER Observed DNS Query to herominers Domain (herominers .com) |