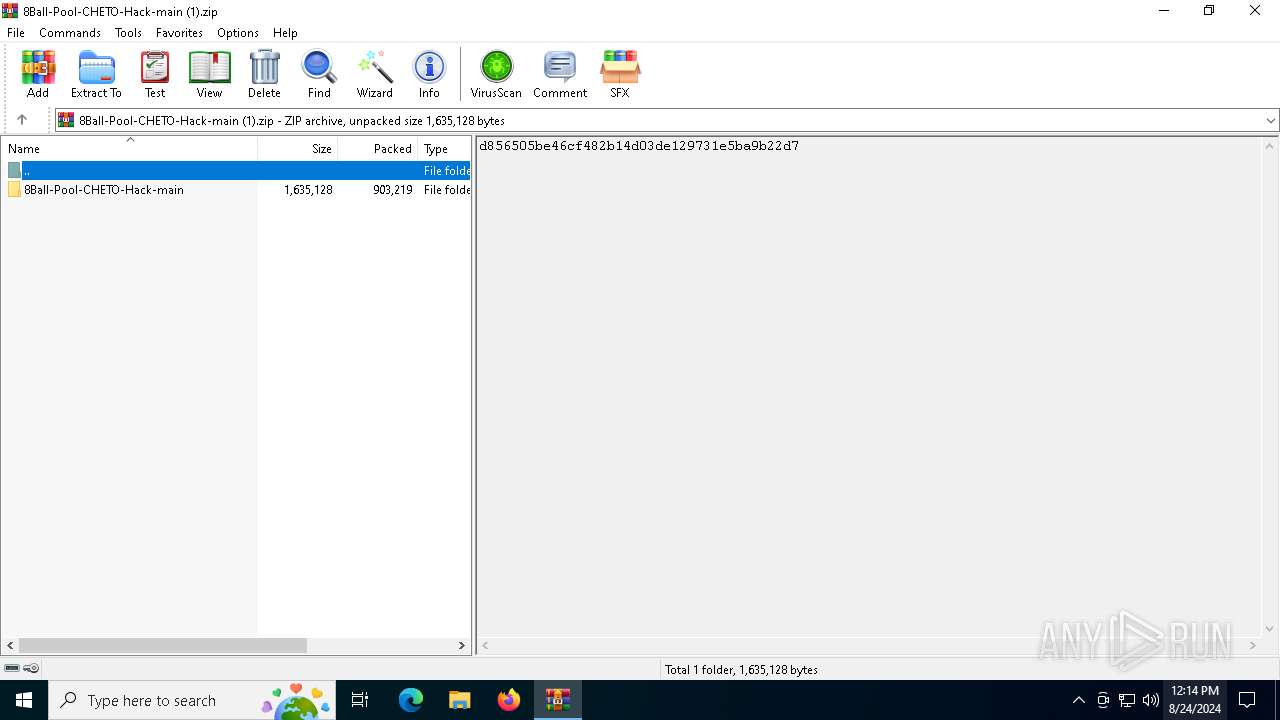
| File name: | 8Ball-Pool-CHETO-Hack-main (1).zip |
| Full analysis: | https://app.any.run/tasks/e7137719-30cd-4b4f-b25f-8fd9a6e0b9be |
| Verdict: | Malicious activity |
| Threats: | Rhadamanthys is a C++ information-stealing malware that extracts sensitive data from infiltrated machines. Its layered operational chain and advanced evasion tactics make it a major risk in cybersecurity landscapes. |
| Analysis date: | August 24, 2024, 12:14:47 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 9235225B2A9D394C1E18E135E65A6EE5 |
| SHA1: | 0E2C28128311DE834A9F4C6D75E7D9E3FB883160 |
| SHA256: | B8D717274BC433D50448ADF0699AB7CD23498023DD105FC009B7CF61B343CE82 |
| SSDEEP: | 49152:ZMU178jP4+Zzto7dJtr5T8oPDVgUGNGk9uV53RN9dxS1zrWTY0IySA2y07MB+Bb4:ZMU178b9tYvtrJx7+UM9uV5xvS1tyS1C |
MALICIOUS
RHADAMANTHYS has been detected (YARA)
- dialer.exe (PID: 7076)
SUSPICIOUS
Drops the executable file immediately after the start
- WinRAR.exe (PID: 6620)
The process checks if it is being run in the virtual environment
- dialer.exe (PID: 7076)
Connects to unusual port
- dialer.exe (PID: 7076)
INFO
Checks supported languages
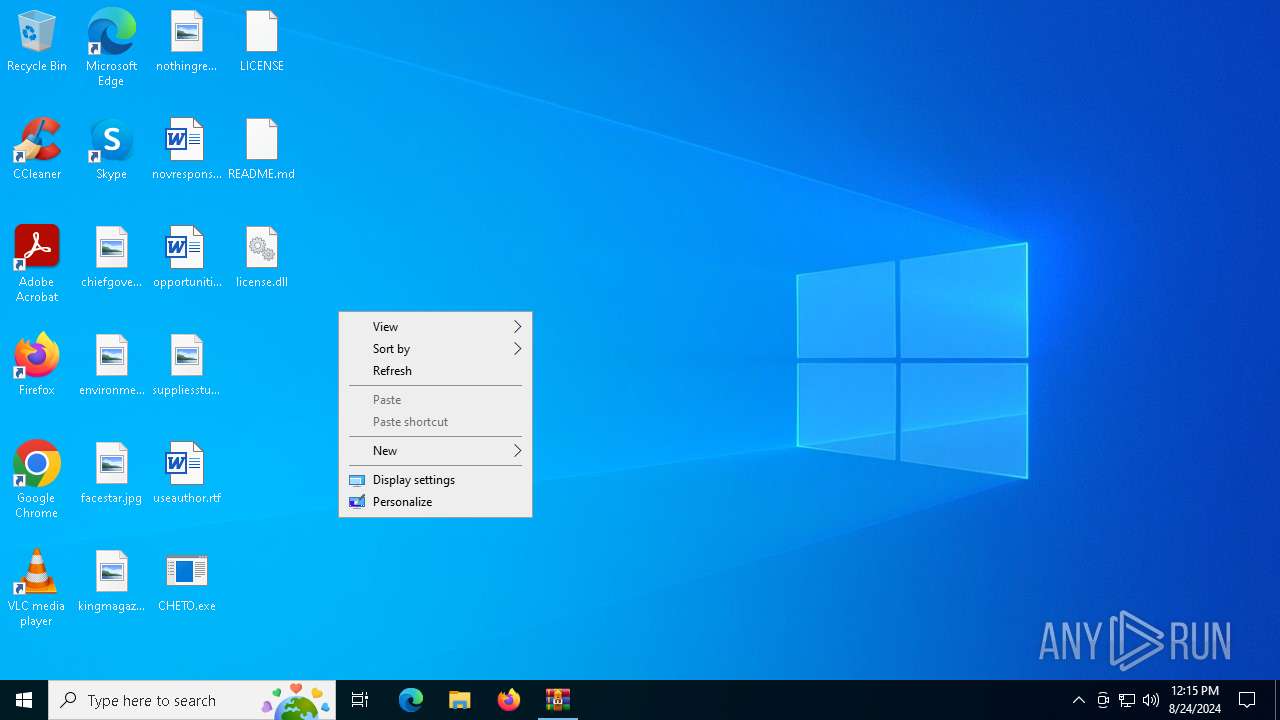
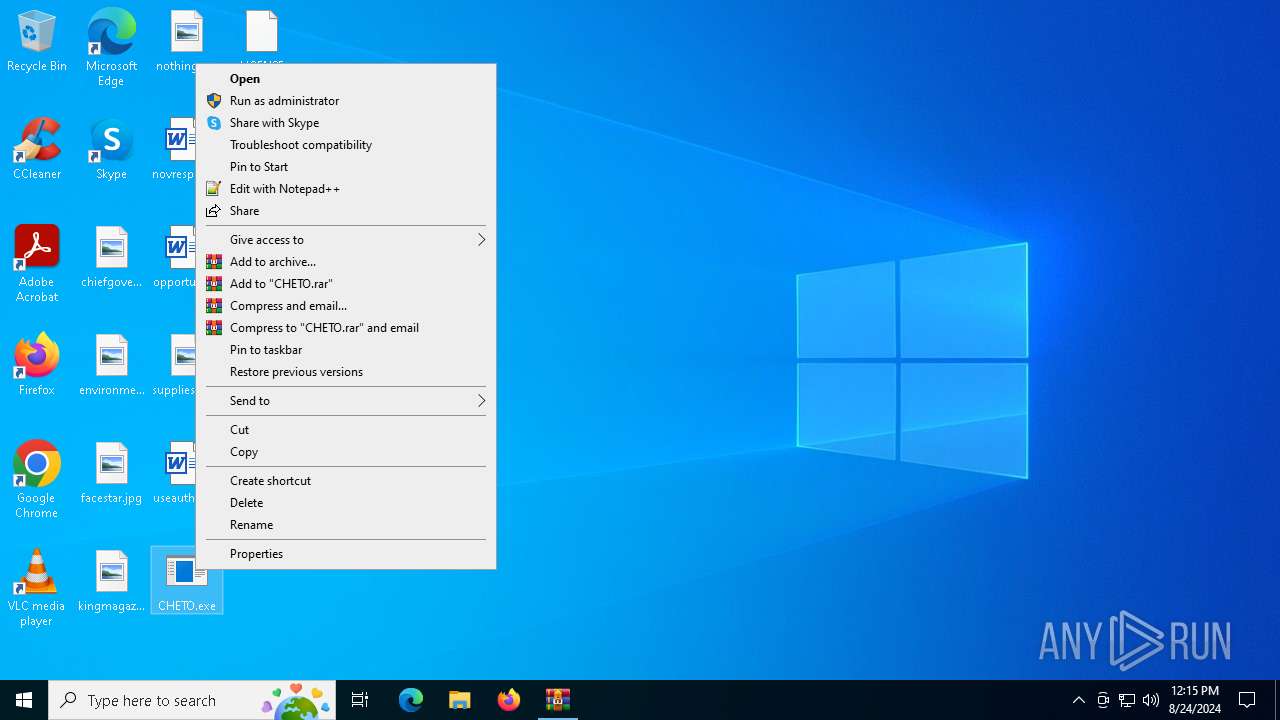
- CHETO.exe (PID: 7020)
- CHETO.exe (PID: 6268)
- CHETO.exe (PID: 6864)
- CHETO.exe (PID: 7012)
Manual execution by a user
- dialer.exe (PID: 7076)
- CHETO.exe (PID: 7020)
- CHETO.exe (PID: 6268)
- CHETO.exe (PID: 6864)
- CHETO.exe (PID: 7012)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:03:23 09:20:40 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | 8Ball-Pool-CHETO-Hack-main/ |
Total processes
135
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6268 | "C:\Users\admin\Desktop\CHETO.exe" | C:\Users\admin\Desktop\CHETO.exe | — | explorer.exe | |||||||||||
User: admin Company: deepxw Integrity Level: MEDIUM Description: TCP-Z, TCP/IP Connection Patch and Monitor. Exit code: 0 Version: 2.6.2.75 Modules
| |||||||||||||||
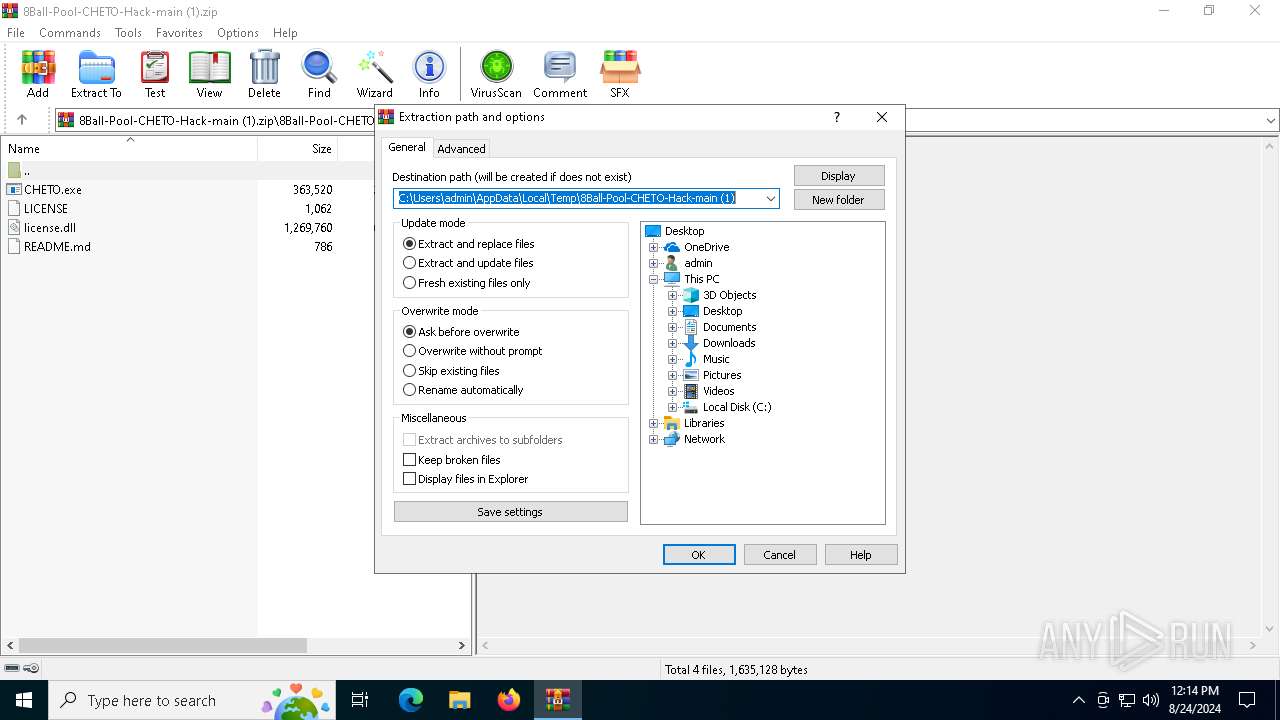
| 6620 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\8Ball-Pool-CHETO-Hack-main (1).zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6864 | "C:\Users\admin\Desktop\CHETO.exe" | C:\Users\admin\Desktop\CHETO.exe | explorer.exe | ||||||||||||
User: admin Company: deepxw Integrity Level: HIGH Description: TCP-Z, TCP/IP Connection Patch and Monitor. Exit code: 0 Version: 2.6.2.75 Modules
| |||||||||||||||
| 7012 | "C:\Users\admin\Desktop\CHETO.exe" | C:\Users\admin\Desktop\CHETO.exe | — | explorer.exe | |||||||||||
User: admin Company: deepxw Integrity Level: MEDIUM Description: TCP-Z, TCP/IP Connection Patch and Monitor. Exit code: 0 Version: 2.6.2.75 Modules
| |||||||||||||||
| 7020 | "C:\Users\admin\Desktop\CHETO.exe" | C:\Users\admin\Desktop\CHETO.exe | — | explorer.exe | |||||||||||
User: admin Company: deepxw Integrity Level: MEDIUM Description: TCP-Z, TCP/IP Connection Patch and Monitor. Exit code: 0 Version: 2.6.2.75 Modules
| |||||||||||||||
| 7076 | "C:\WINDOWS\system32\dialer.exe" | C:\Windows\SysWOW64\dialer.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Phone Dialer Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 038
Read events
6 025
Write events
13
Delete events
0
Modification events
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\8Ball-Pool-CHETO-Hack-main (1).zip | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (7020) CHETO.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\SibCode |
| Operation: | write | Name: | sn |
Value: | |||
Executable files
2
Suspicious files
0
Text files
2
Unknown types
0
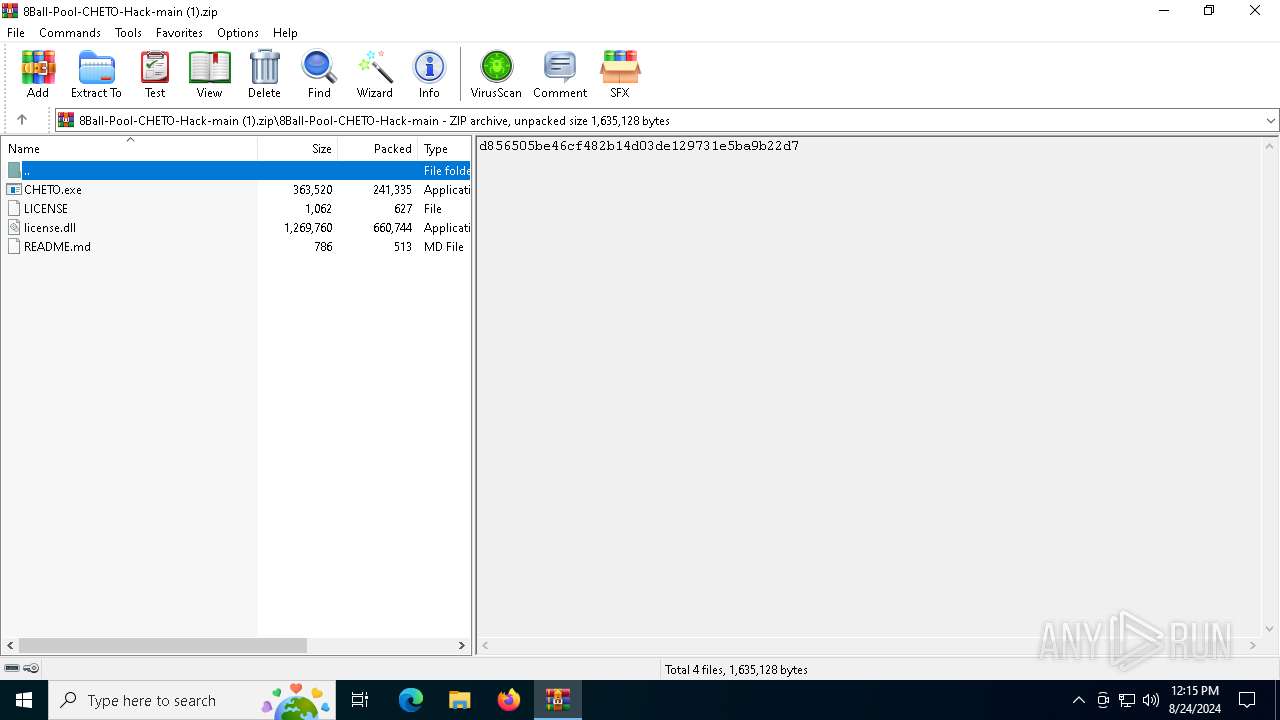
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6620 | WinRAR.exe | C:\Users\admin\Desktop\README.md | text | |
MD5:E0F1ABFB3D8CEAF7E185A86347BB570D | SHA256:386892749870FCEAA97C0CAE430325F51E00D6F60B63314D49C61663007CE7BD | |||
| 6620 | WinRAR.exe | C:\Users\admin\Desktop\CHETO.exe | executable | |
MD5:BB84CC2853596D21A318576C4995FCCE | SHA256:6135BDBCFD9F824B3DA0BEF2BA73018A998967E20C5D0274C6A1C0433649B017 | |||
| 6620 | WinRAR.exe | C:\Users\admin\Desktop\license.dll | executable | |
MD5:36DEA25D49B9DFF21ACEBFACE8EA2044 | SHA256:D960A2EAC5E7F1AA04E9F8D0DA4EB9BB0B097CA58D0CE83EA1BB8351BAF26301 | |||
| 6620 | WinRAR.exe | C:\Users\admin\Desktop\LICENSE | text | |
MD5:58ACB5A4A64FE30E79738DC6CAA6E0A8 | SHA256:9DCDF86B43B68CF84672D930A83A9638D3B18BFE49BE1FBB4F69FEBA15685A90 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
37
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6160 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6040 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5116 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2396 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6040 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
6040 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
7076 | dialer.exe | 185.125.50.38:3034 | — | — | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |