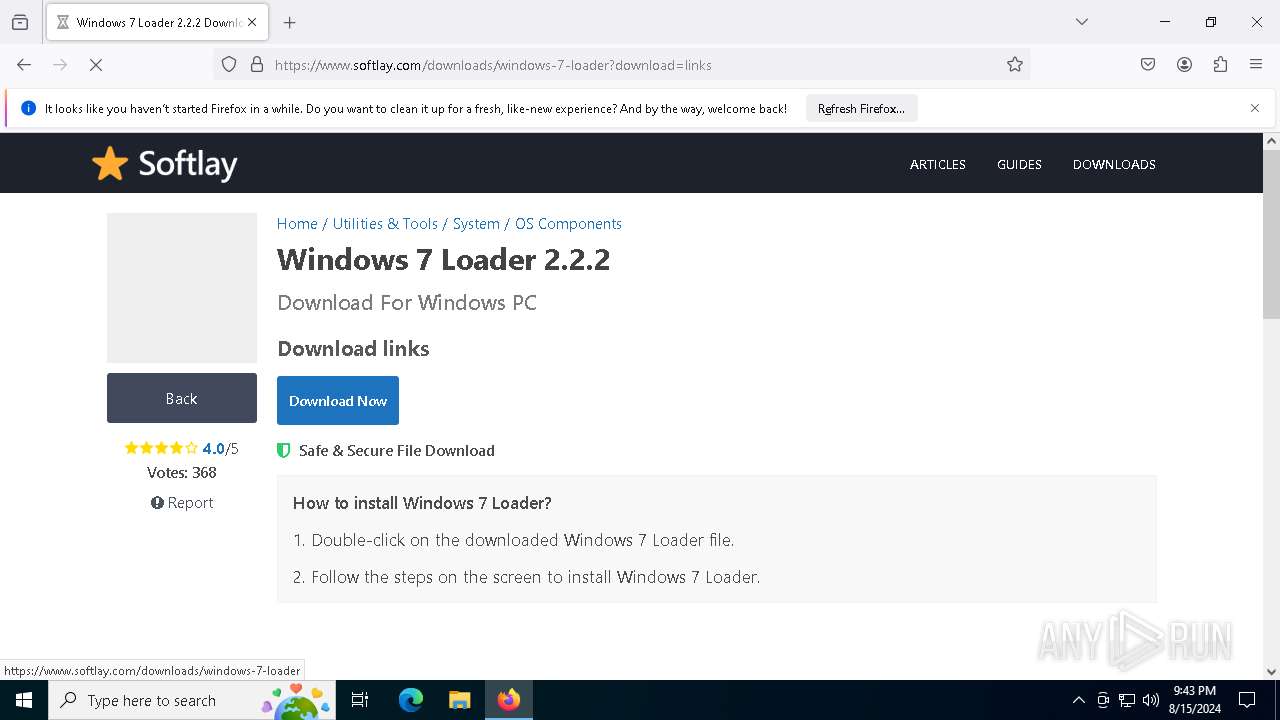
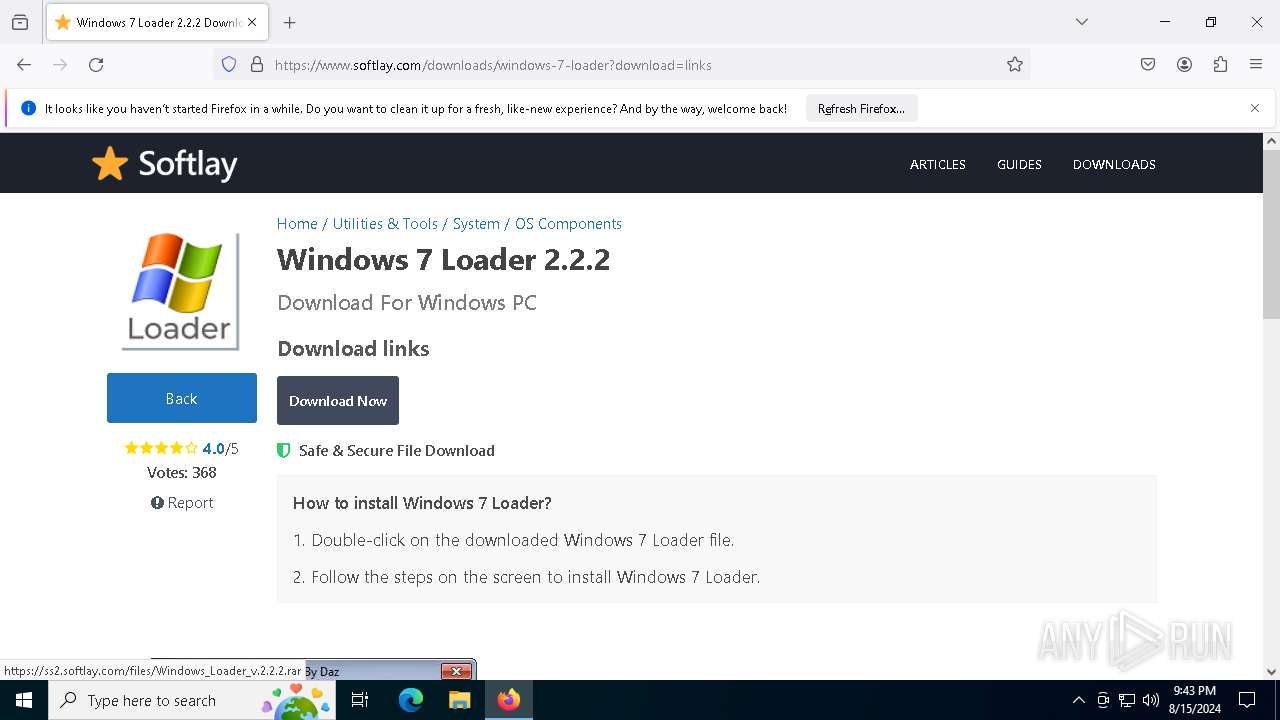
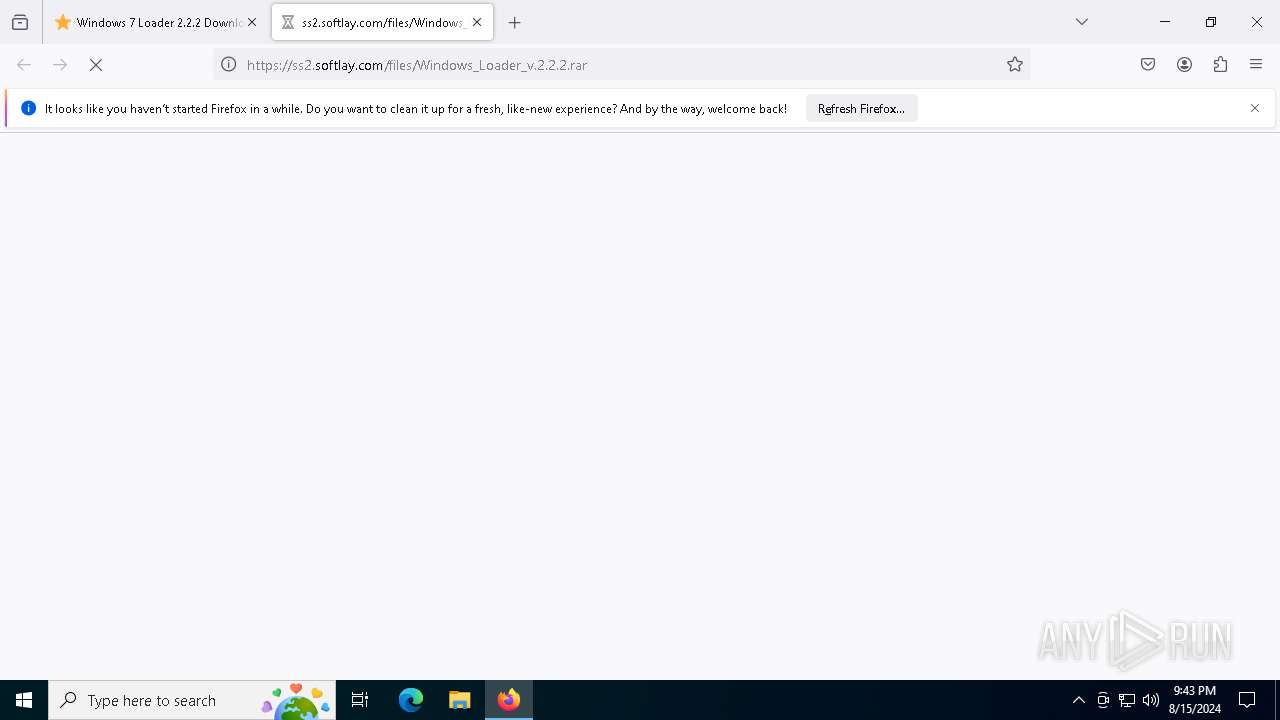
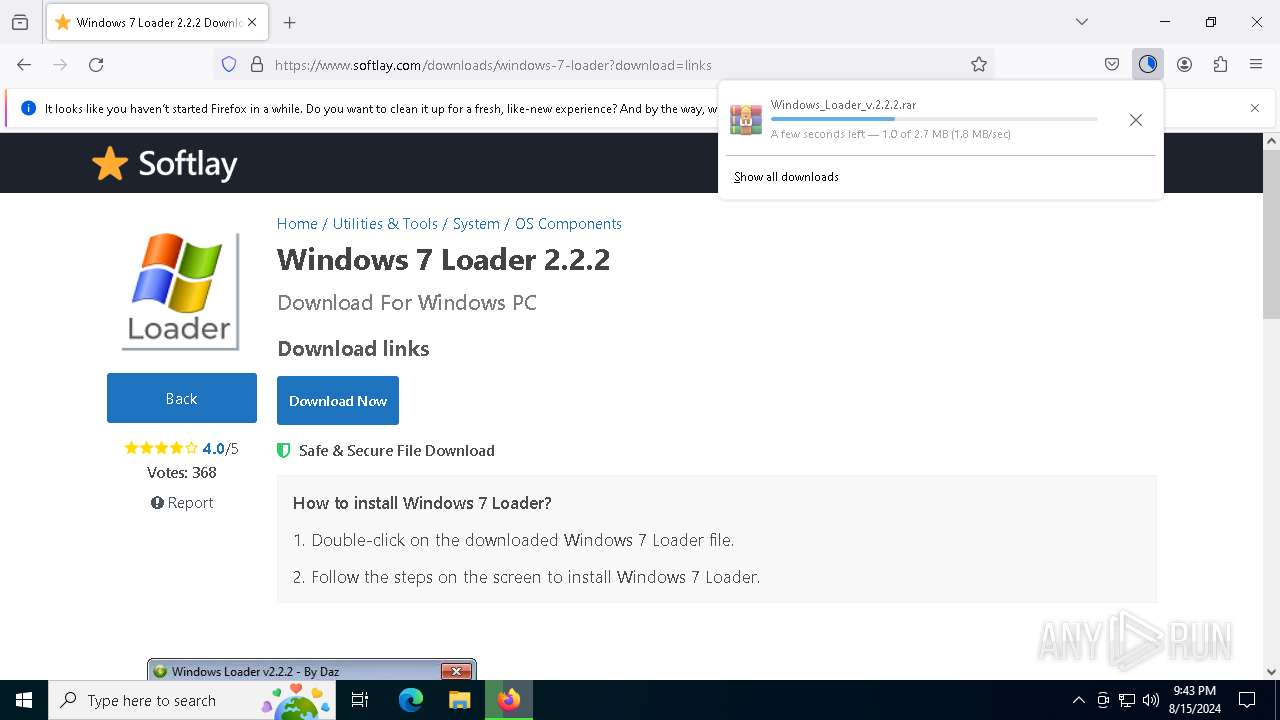
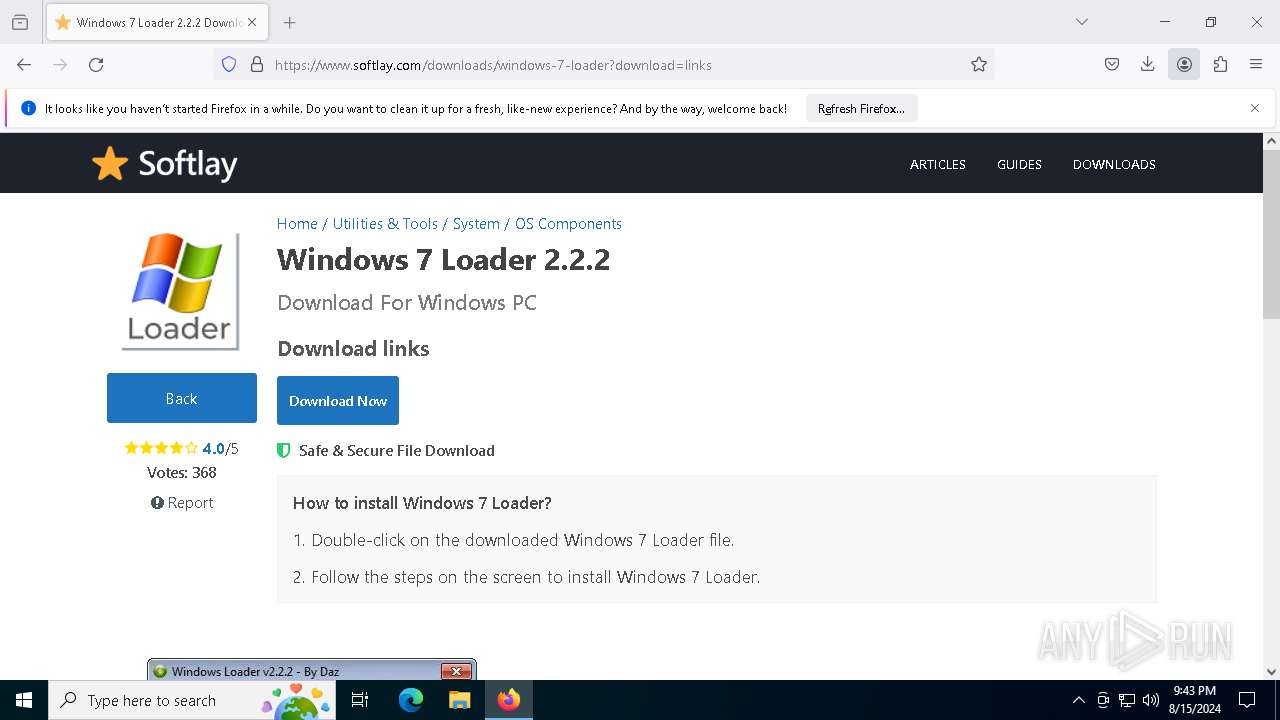
| URL: | https://www.google.es/url?sa=t&source=web&rct=j&opi=89978449&url=https://www.softlay.com/downloads/windows-7-loader&ved=2ahUKEwj05uzT-_eHAxWWFBAIHTE1AkEQFnoECCEQAQ&usg=AOvVaw2TwhmGUm1xid-TsJMVIsbA |
| Full analysis: | https://app.any.run/tasks/98febe16-7273-4cfc-b390-cbf9f2d6db9c |
| Verdict: | Malicious activity |
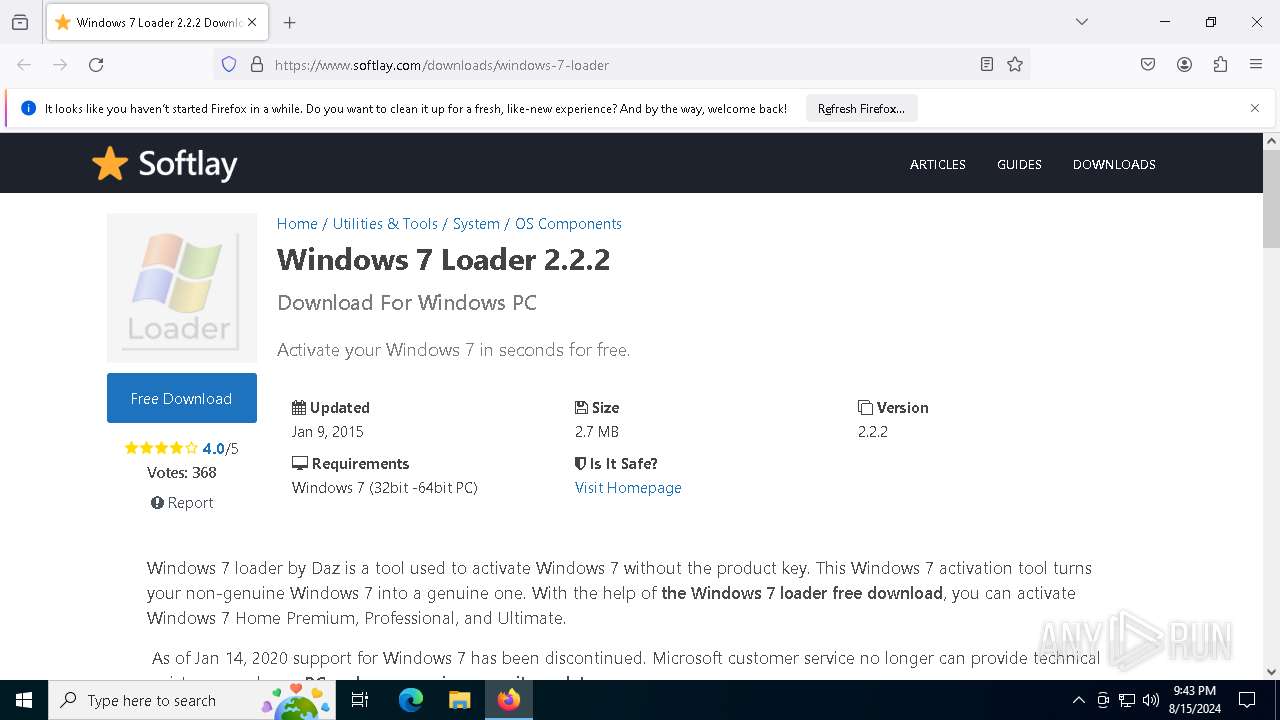
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | August 15, 2024, 21:43:23 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E02FC03D9A9DF8F0DBE0AF1A964A0540 |
| SHA1: | 087EBF7EF5F6215CA999317A5199391CD68BCB06 |
| SHA256: | B8BF7DAEA1A9CFF2B633E330AD8EB21B61D57D1A6432FCD6C29311DB16833D37 |
| SSDEEP: | 6:2OLIslQpUNRROGLXmaI5UNGQCaaOMkQHLSU2RoozsBn:2VGmrKNGQJaOMkQrsaozU |
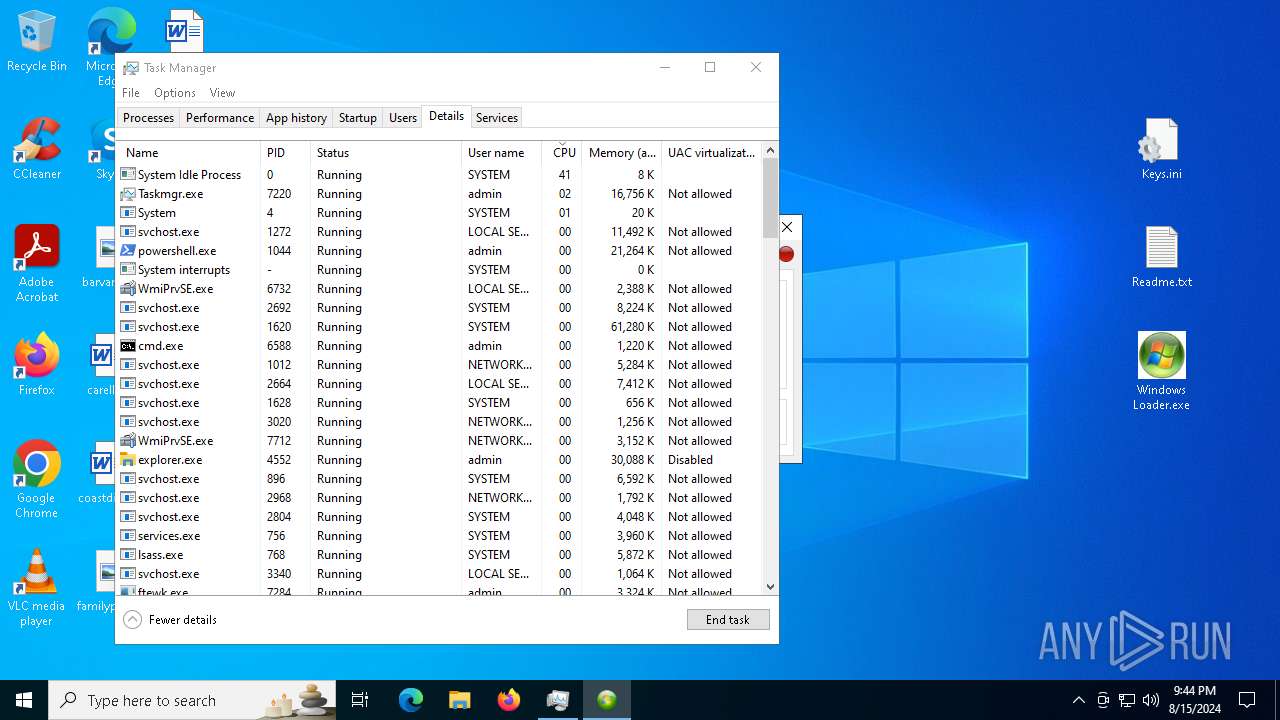
MALICIOUS
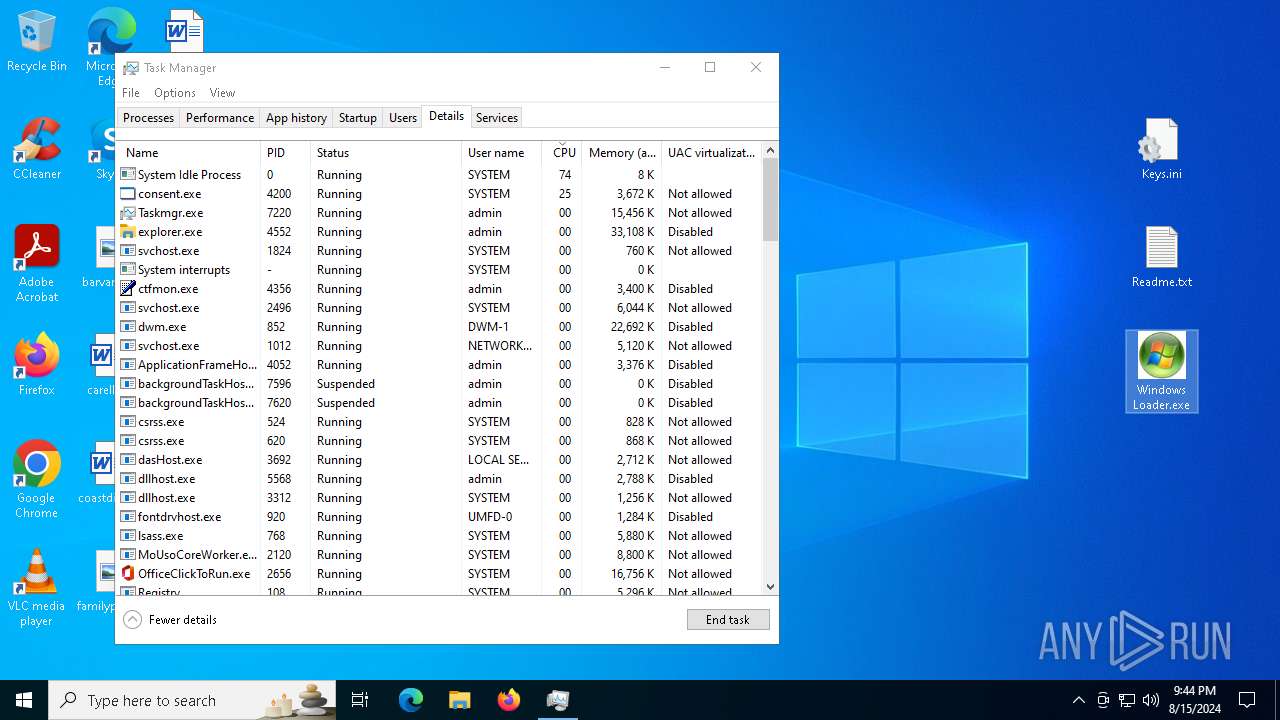
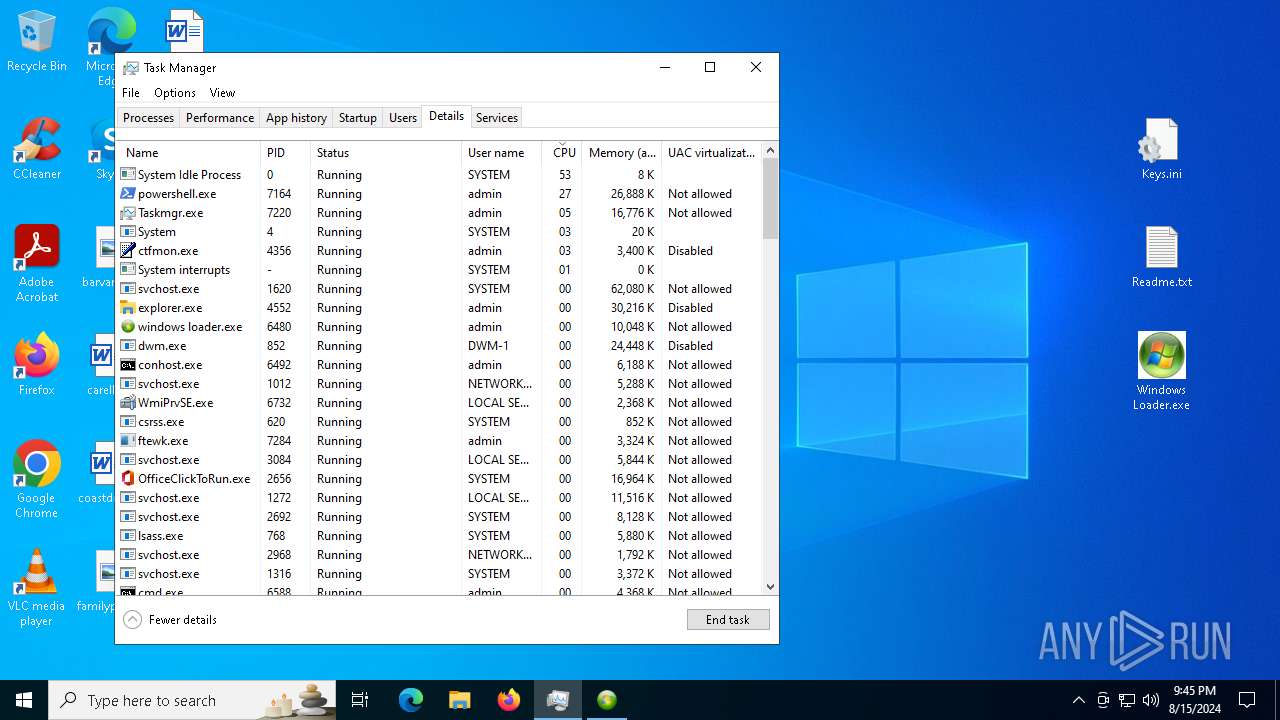
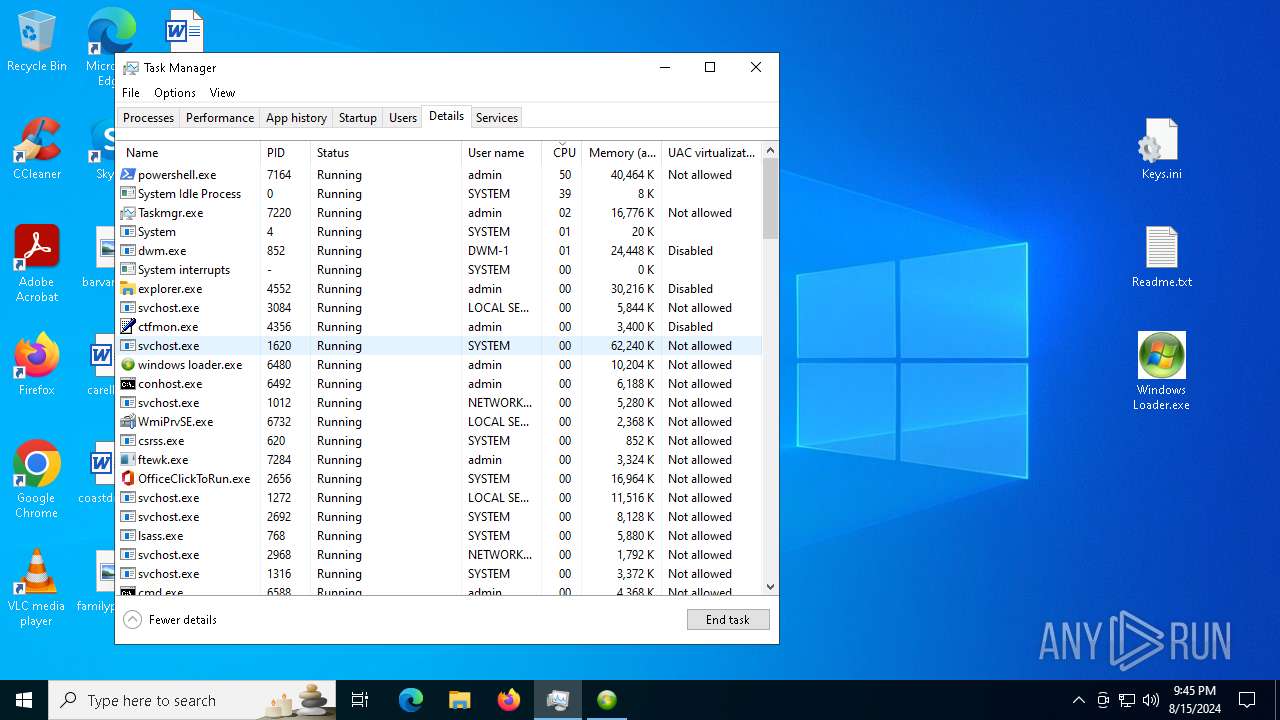
Windows Defender preferences modified via 'Set-MpPreference'
- cmd.exe (PID: 6588)
Uses Task Scheduler to run other applications
- ftewk.exe (PID: 7284)
Changes the autorun value in the registry
- reg.exe (PID: 5500)
Disables Windows Defender
- reg.exe (PID: 3684)
- reg.exe (PID: 2900)
- reg.exe (PID: 8076)
- reg.exe (PID: 3376)
- reg.exe (PID: 3256)
AMADEY has been detected (YARA)
- ftewk.exe (PID: 7284)
SUSPICIOUS
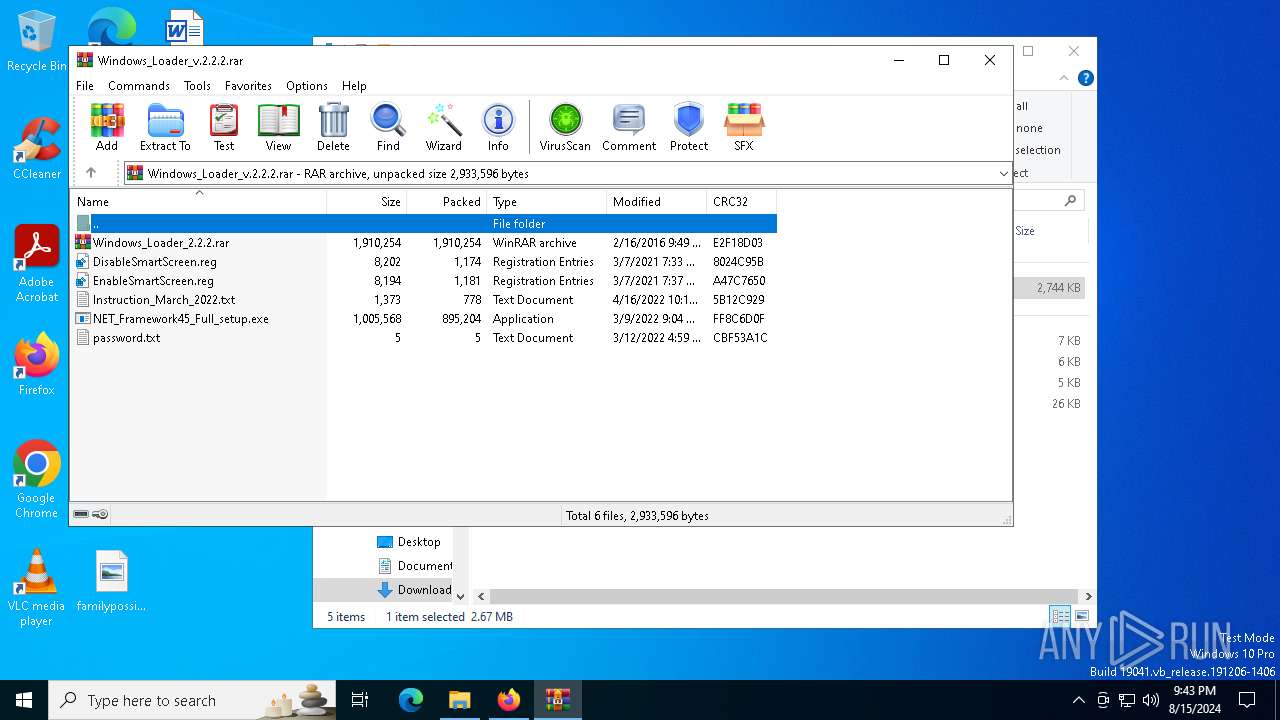
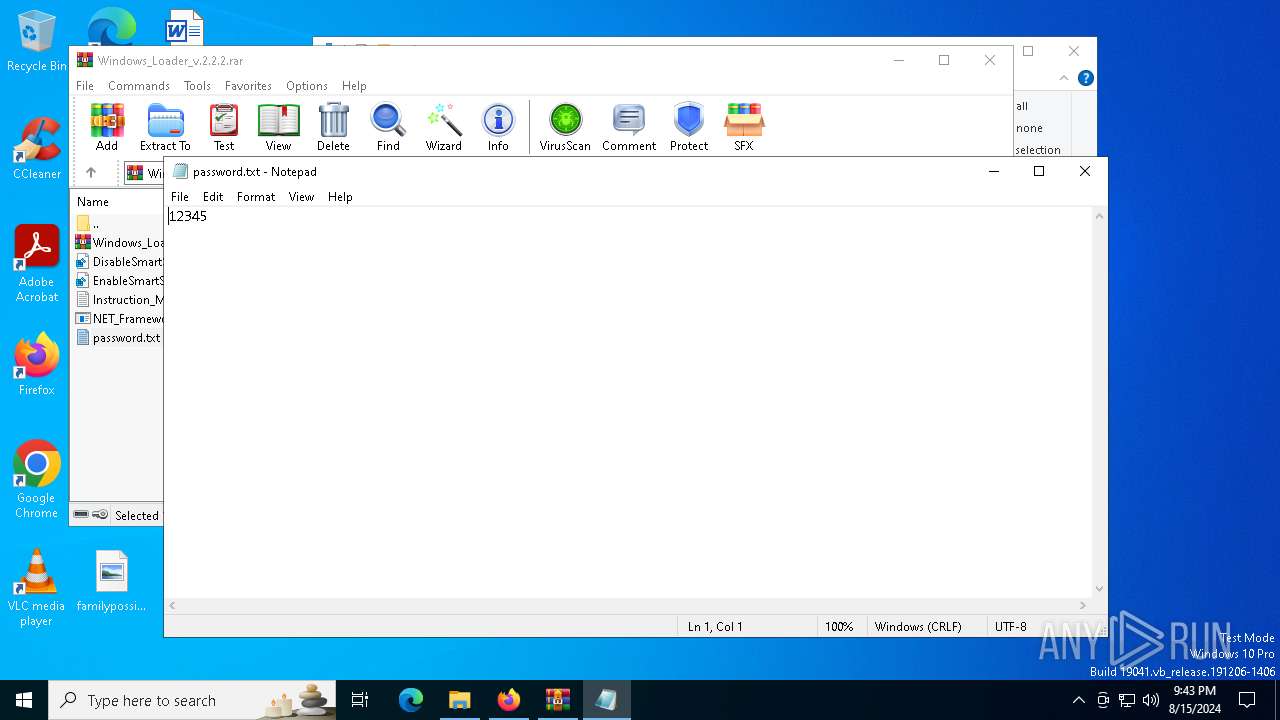
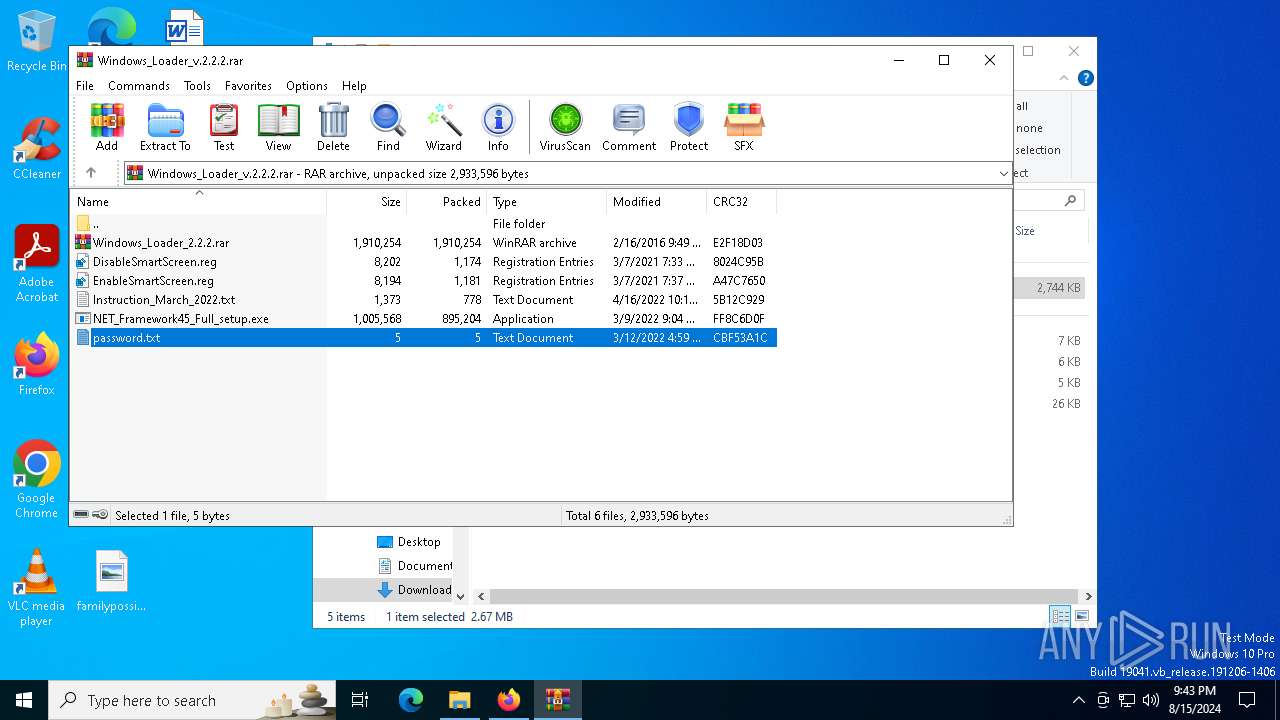
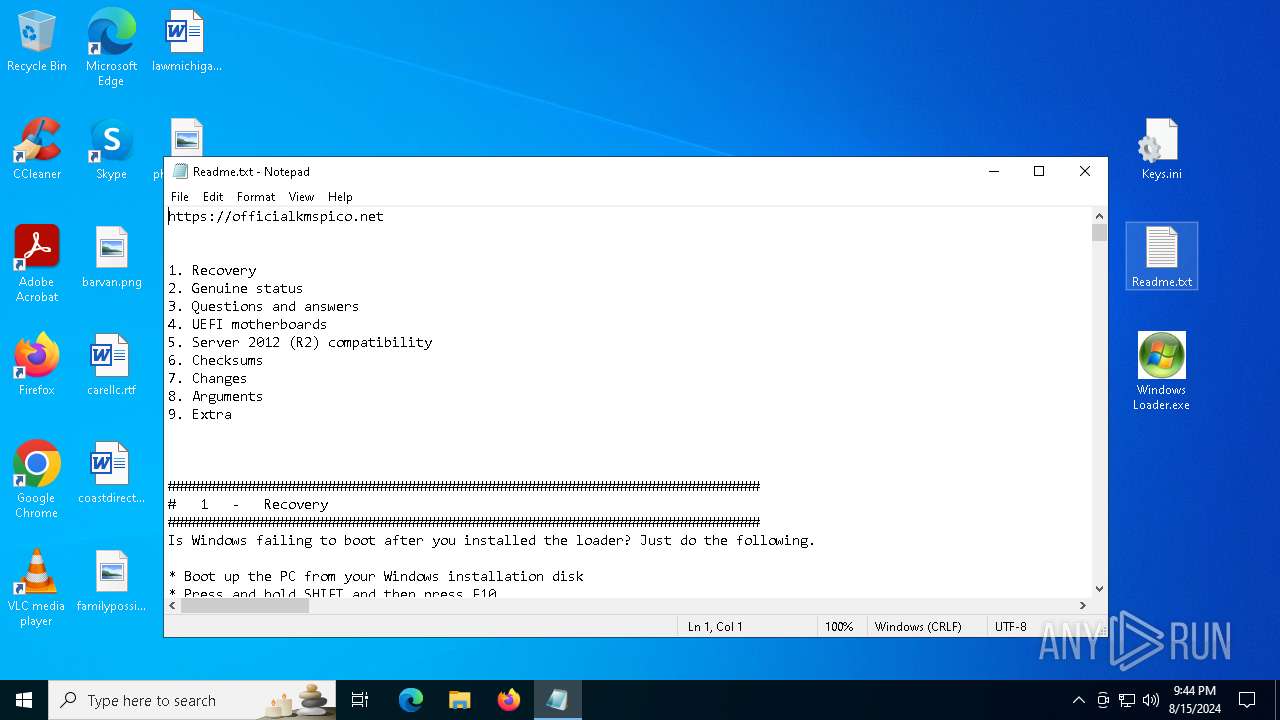
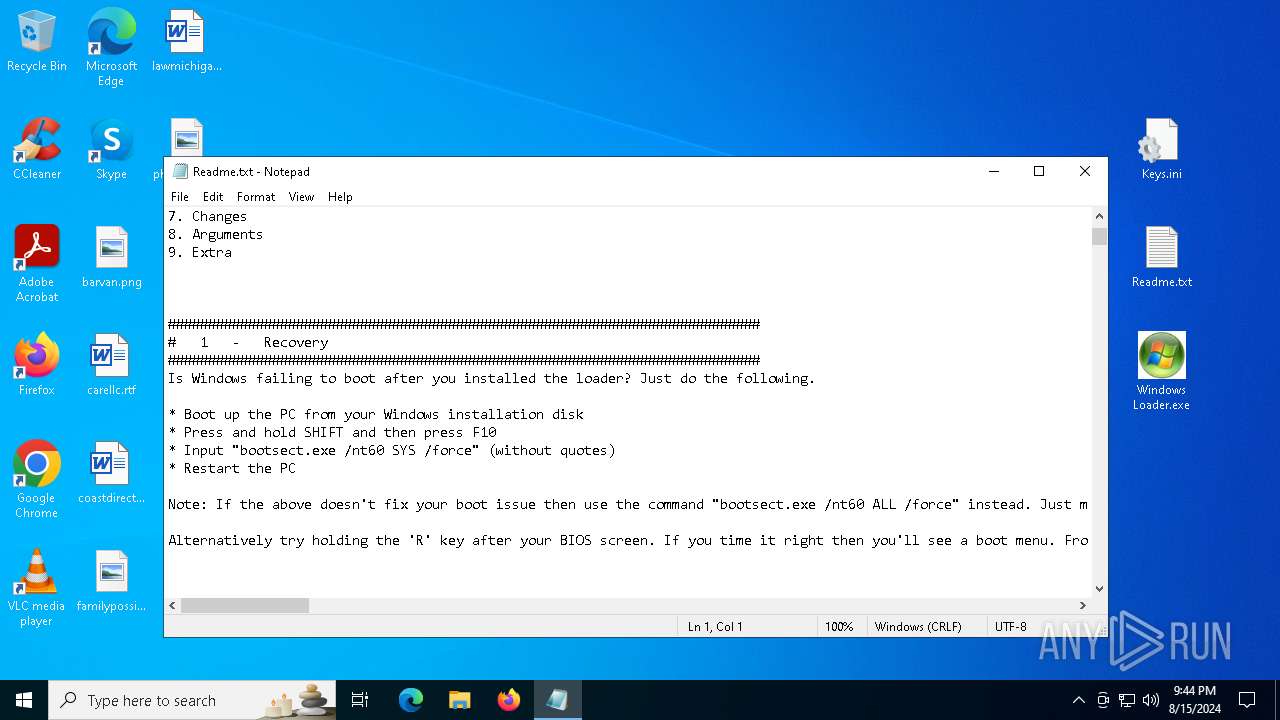
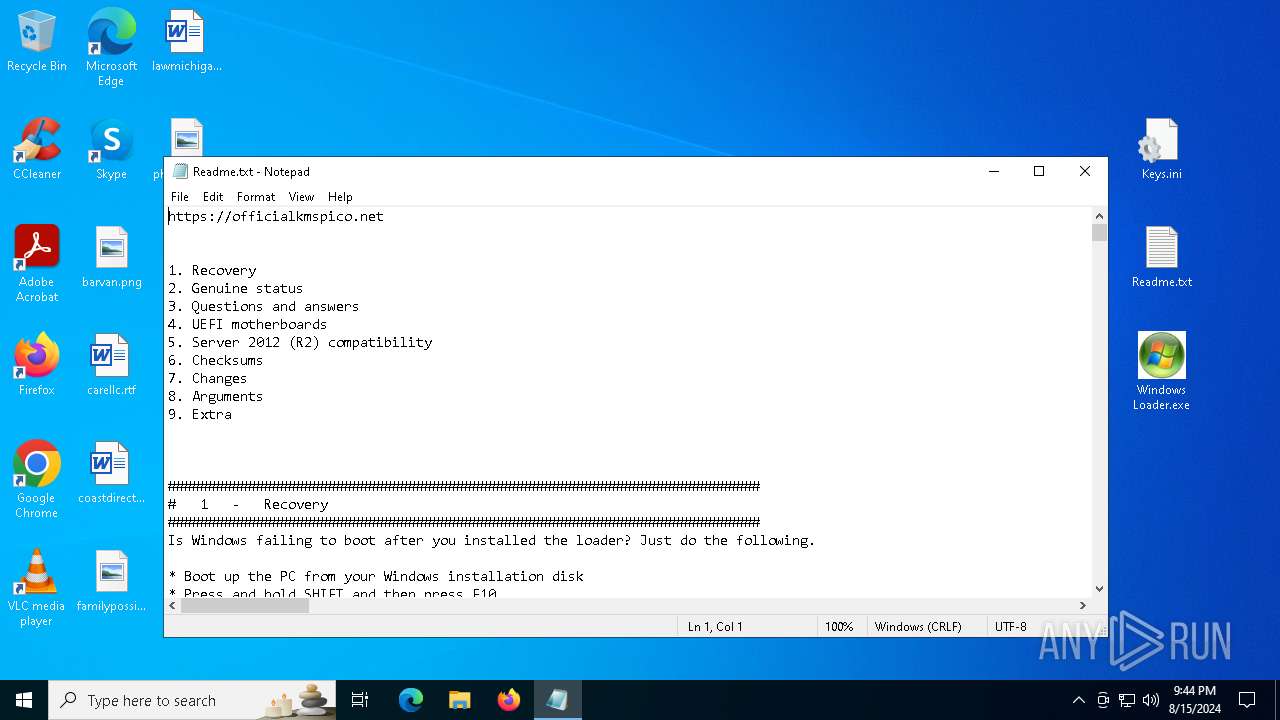
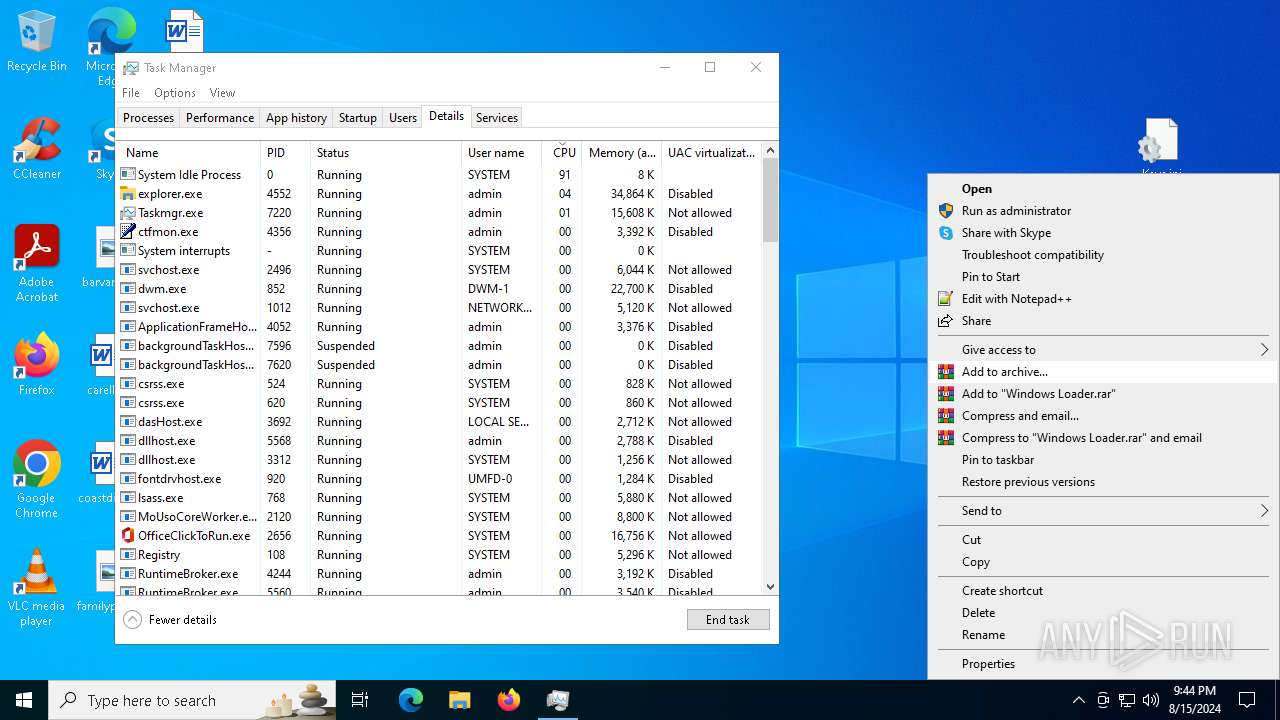
Start notepad (likely ransomware note)
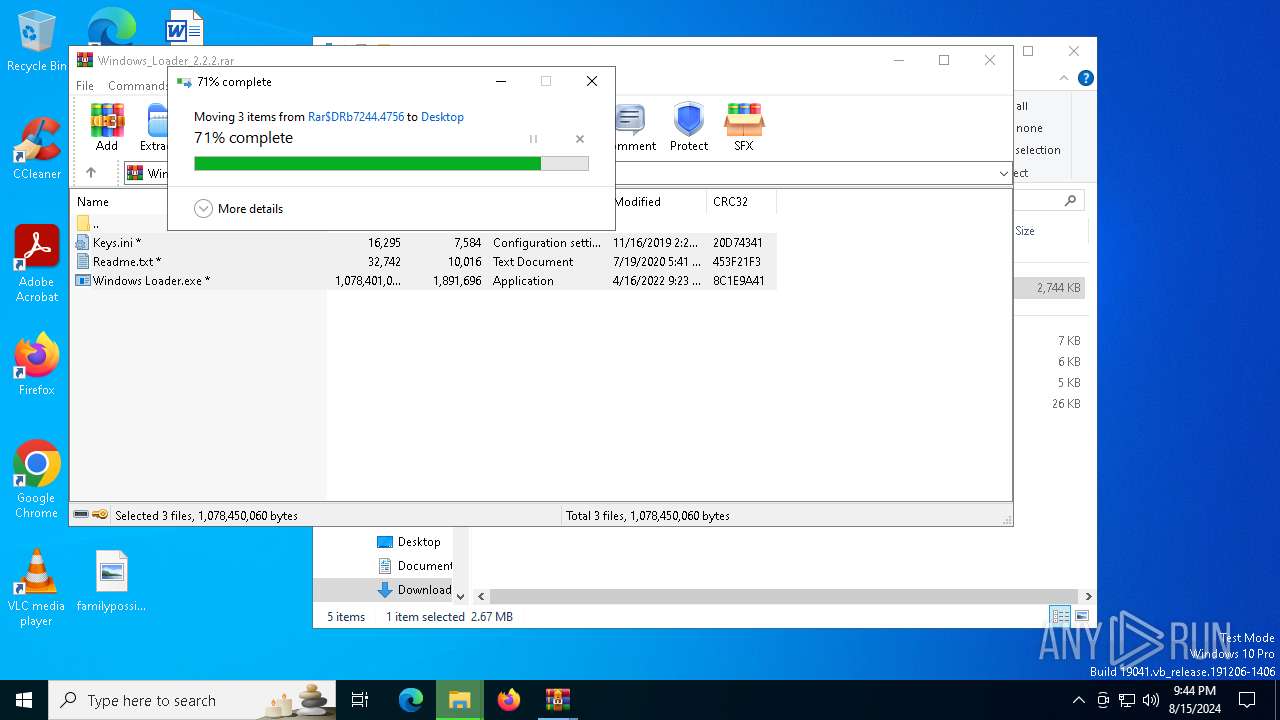
- WinRAR.exe (PID: 7516)
Application launched itself
- WinRAR.exe (PID: 7516)
- Taskmgr.exe (PID: 6952)
Process drops legitimate windows executable
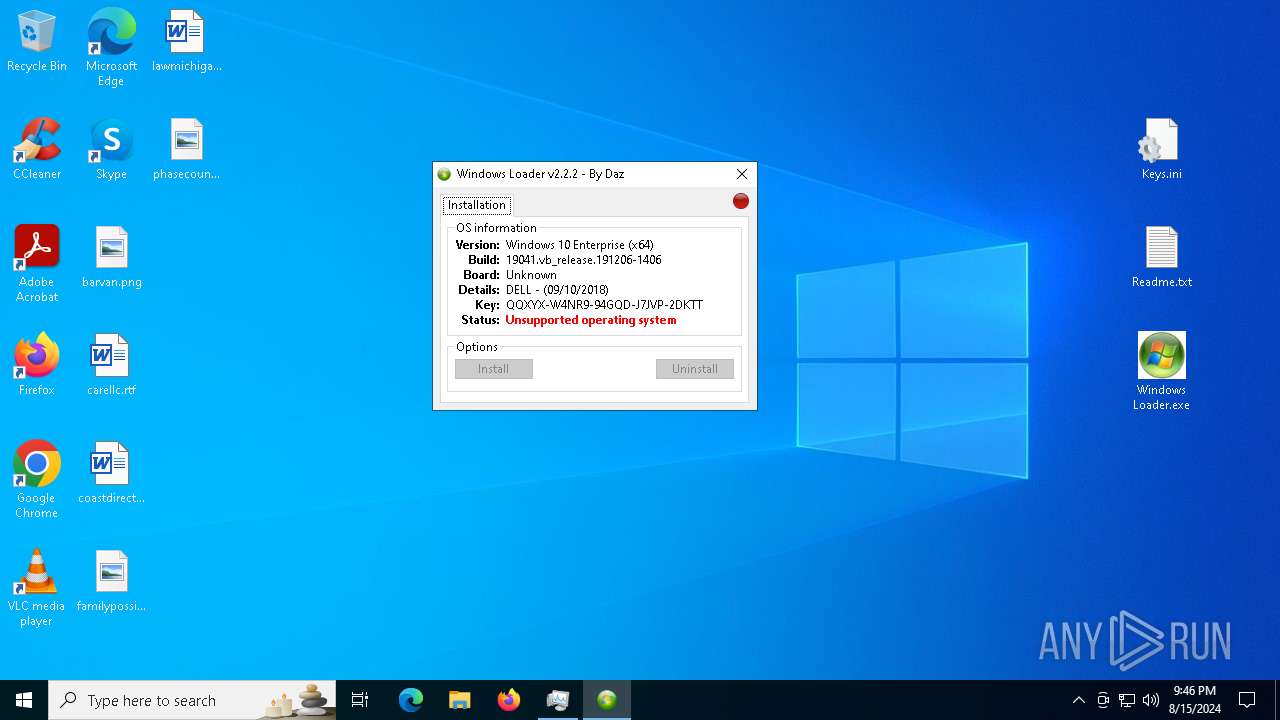
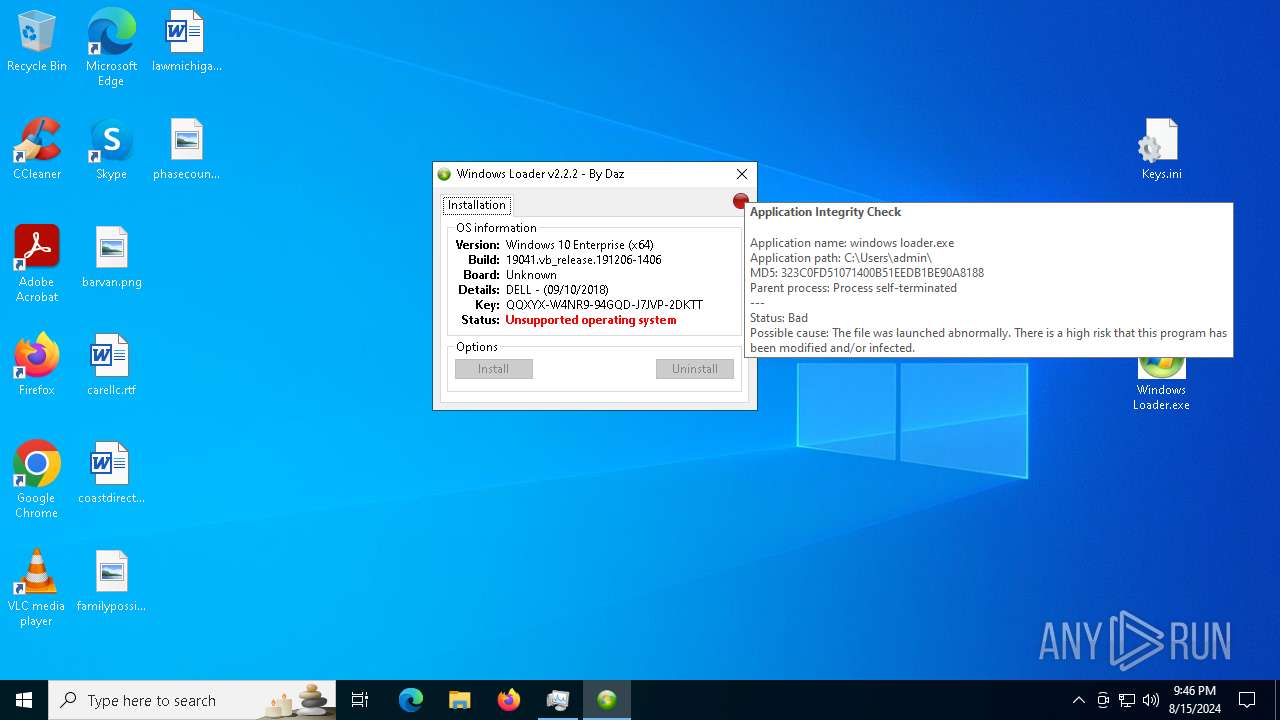
- firefox.exe (PID: 6360)
- Windows Loader.exe (PID: 6980)
- system32.exe (PID: 6460)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7516)
- ShellExperienceHost.exe (PID: 7968)
- activationdriver.exe (PID: 6720)
- Windows Loader.exe (PID: 6980)
- services32.exe (PID: 6664)
- system32.exe (PID: 6460)
- ftewk.exe (PID: 7284)
Reads the date of Windows installation
- Windows Loader.exe (PID: 6980)
- activationdriver.exe (PID: 6720)
- system32.exe (PID: 6460)
- ftewk.exe (PID: 7284)
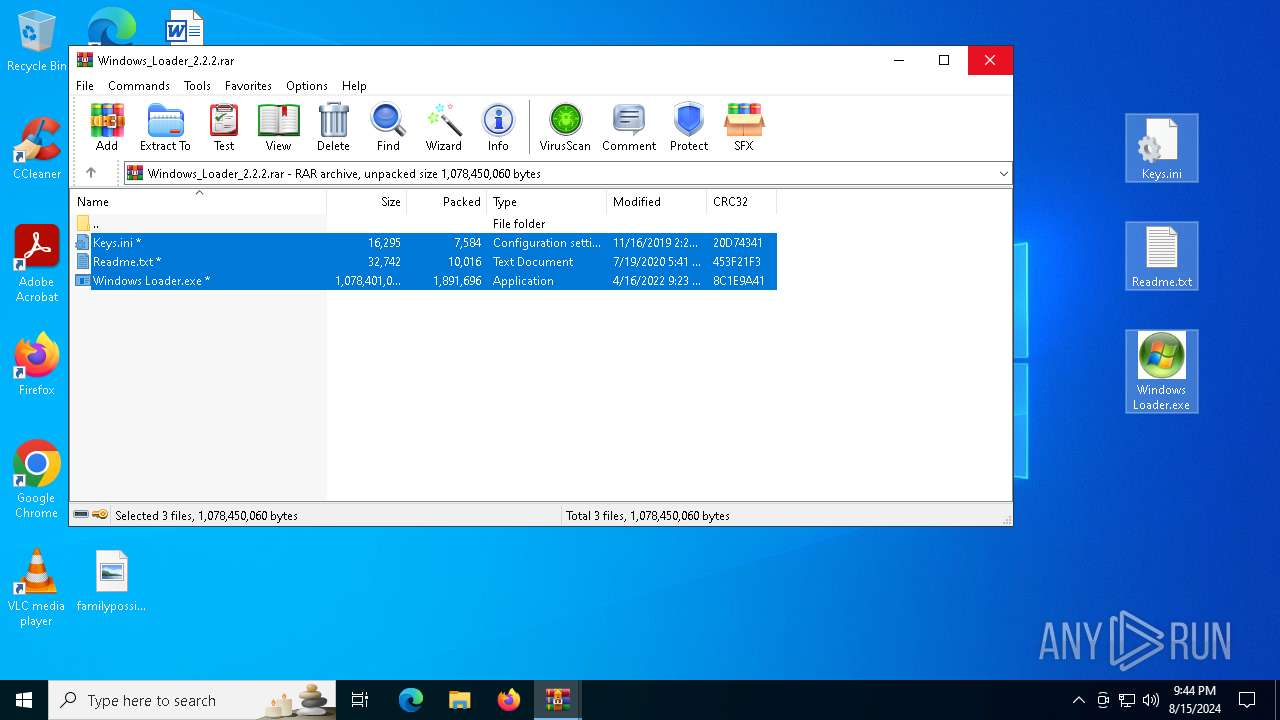
Executable content was dropped or overwritten
- Windows Loader.exe (PID: 6980)
- system32.exe (PID: 6460)
Drops the executable file immediately after the start
- Windows Loader.exe (PID: 6980)
- system32.exe (PID: 6460)
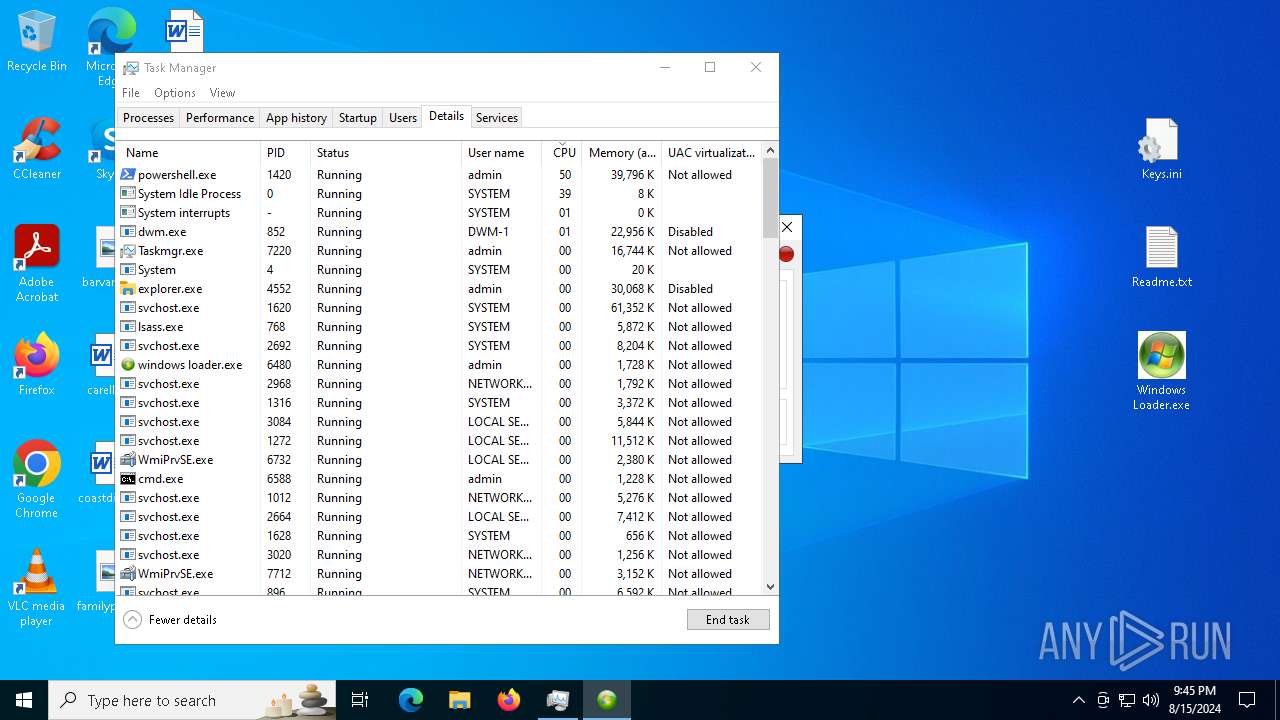
Executing commands from a ".bat" file
- activationdriver.exe (PID: 6720)
Starts CMD.EXE for commands execution
- activationdriver.exe (PID: 6720)
- ftewk.exe (PID: 7284)
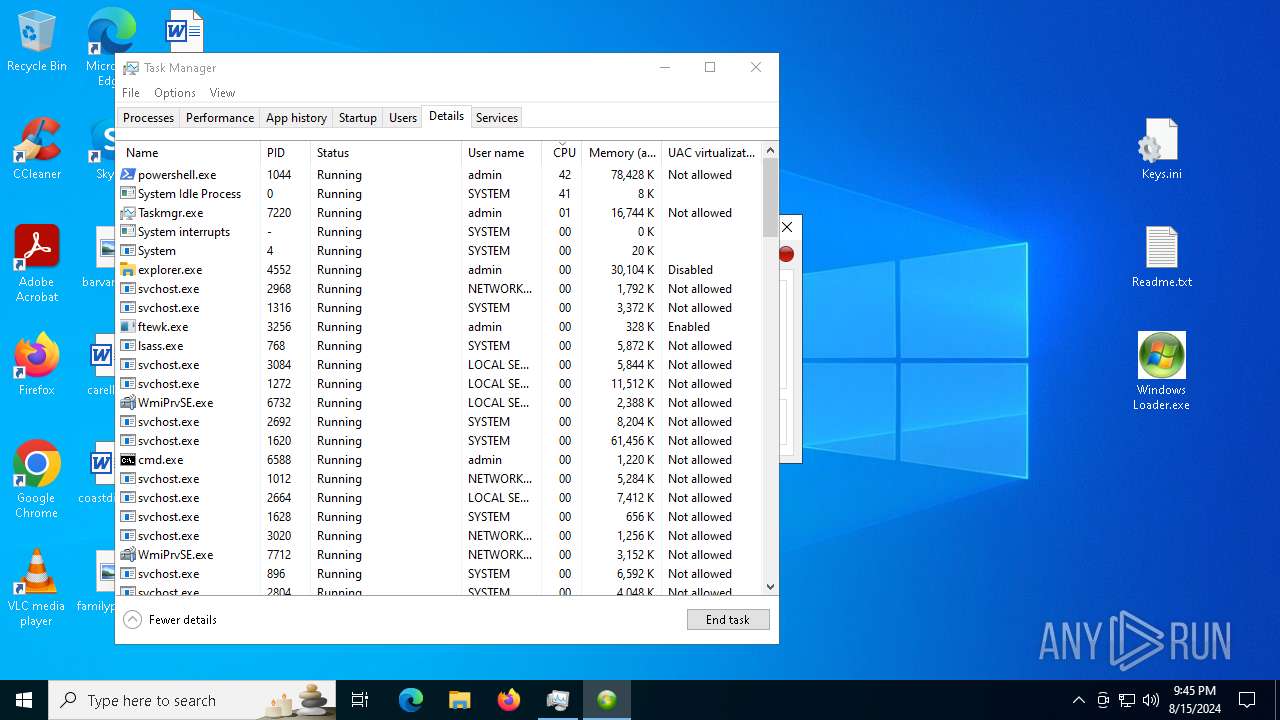
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6588)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 6588)
Checks Windows Trust Settings
- services32.exe (PID: 6664)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 6364)
Reads the BIOS version
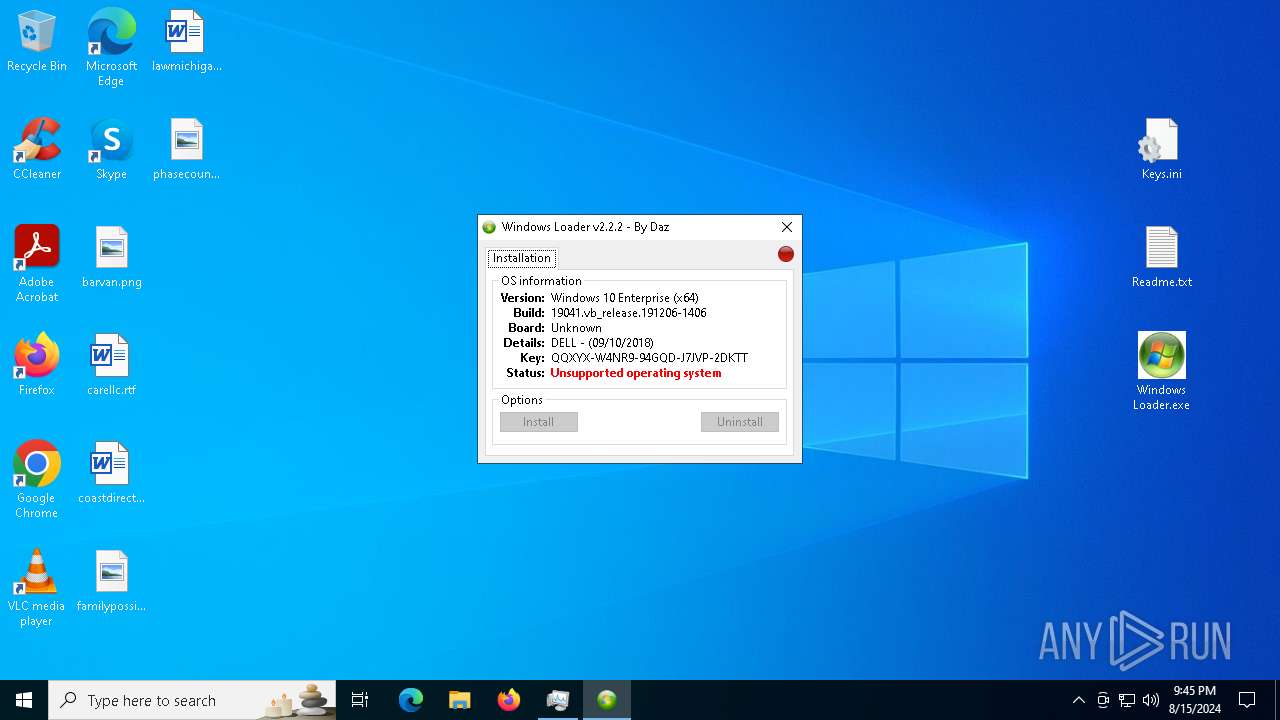
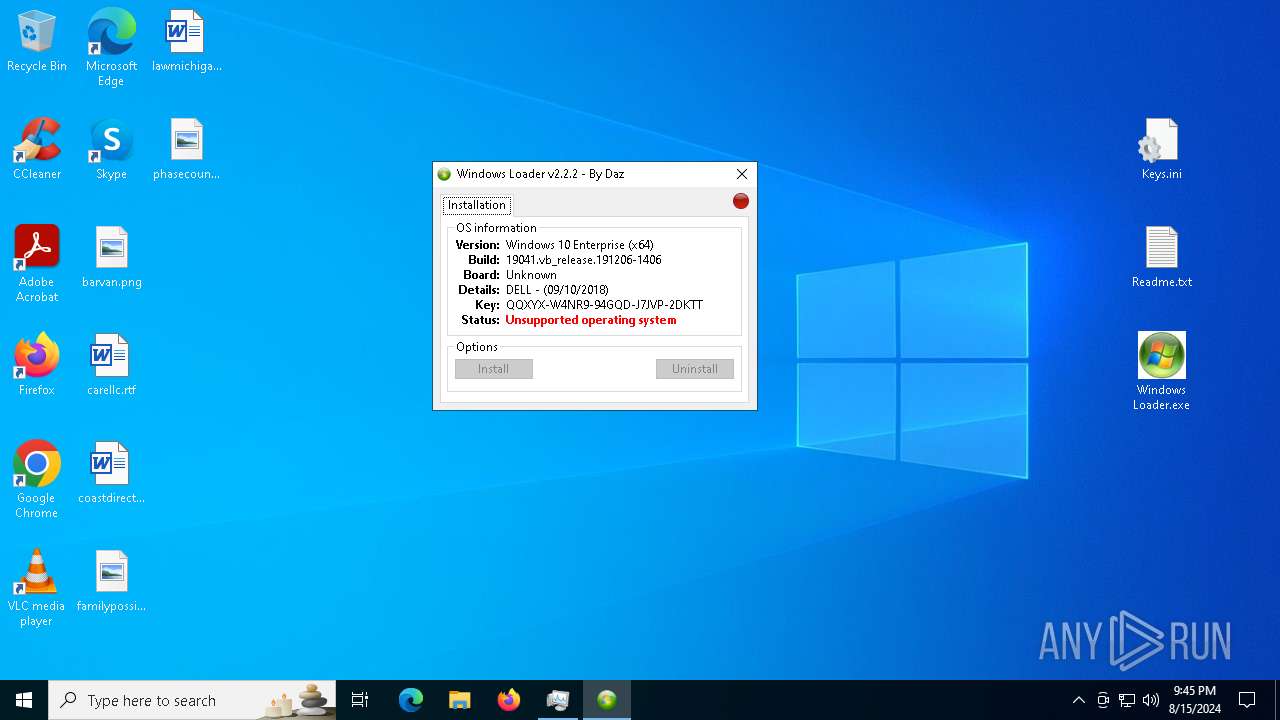
- windows loader.exe (PID: 6480)
Starts a Microsoft application from unusual location
- ftewk.exe (PID: 7284)
- ftewk.exe (PID: 3256)
- ftewk.exe (PID: 6548)
Starts itself from another location
- system32.exe (PID: 6460)
Executes application which crashes
- system32.exe (PID: 6460)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 4064)
- cmd.exe (PID: 6588)
Script disables Windows Defender's behavior monitoring
- cmd.exe (PID: 6588)
The process executes via Task Scheduler
- ftewk.exe (PID: 3256)
- ftewk.exe (PID: 6548)
Script disables Windows Defender's IPS
- cmd.exe (PID: 6588)
There is functionality for communication over UDP network (YARA)
- windows loader.exe (PID: 6480)
Uses NETSH.EXE to change the status of the firewall
- powershell.exe (PID: 8136)
Modifies existing scheduled task
- schtasks.exe (PID: 7584)
- schtasks.exe (PID: 7628)
- schtasks.exe (PID: 7832)
- schtasks.exe (PID: 7912)
- schtasks.exe (PID: 1060)
INFO
Application launched itself
- firefox.exe (PID: 6296)
- firefox.exe (PID: 6360)
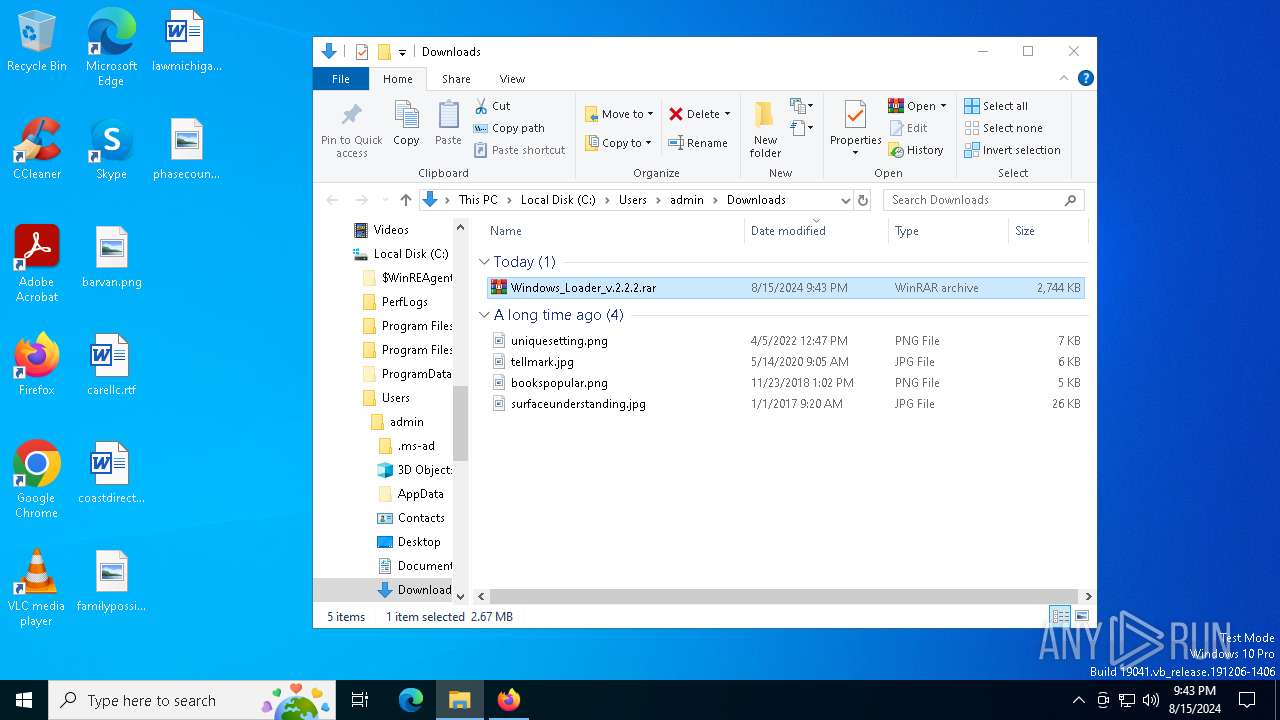
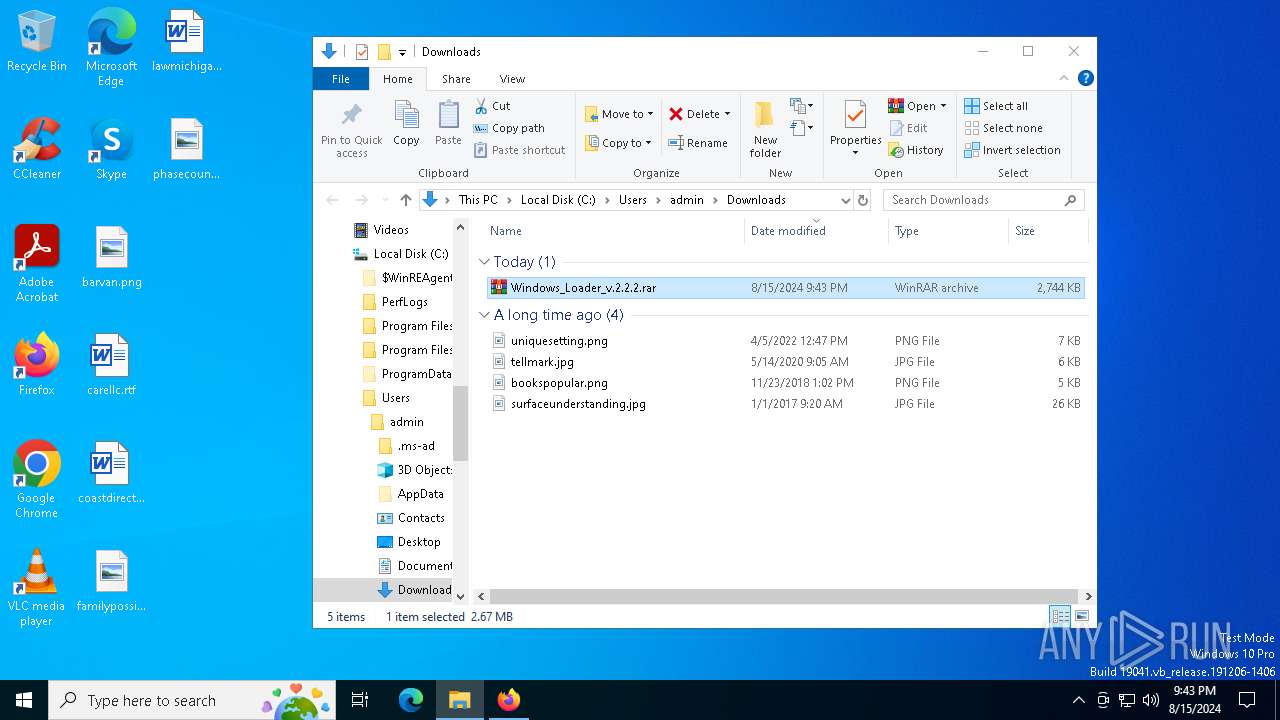
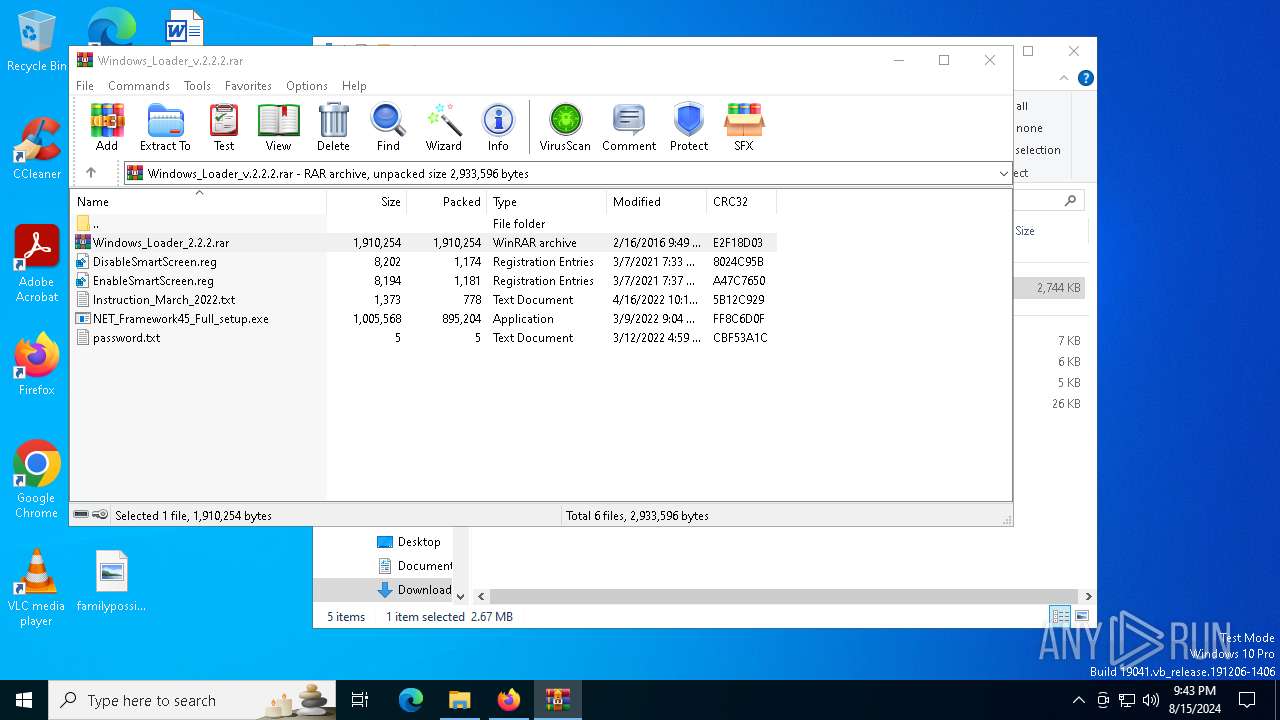
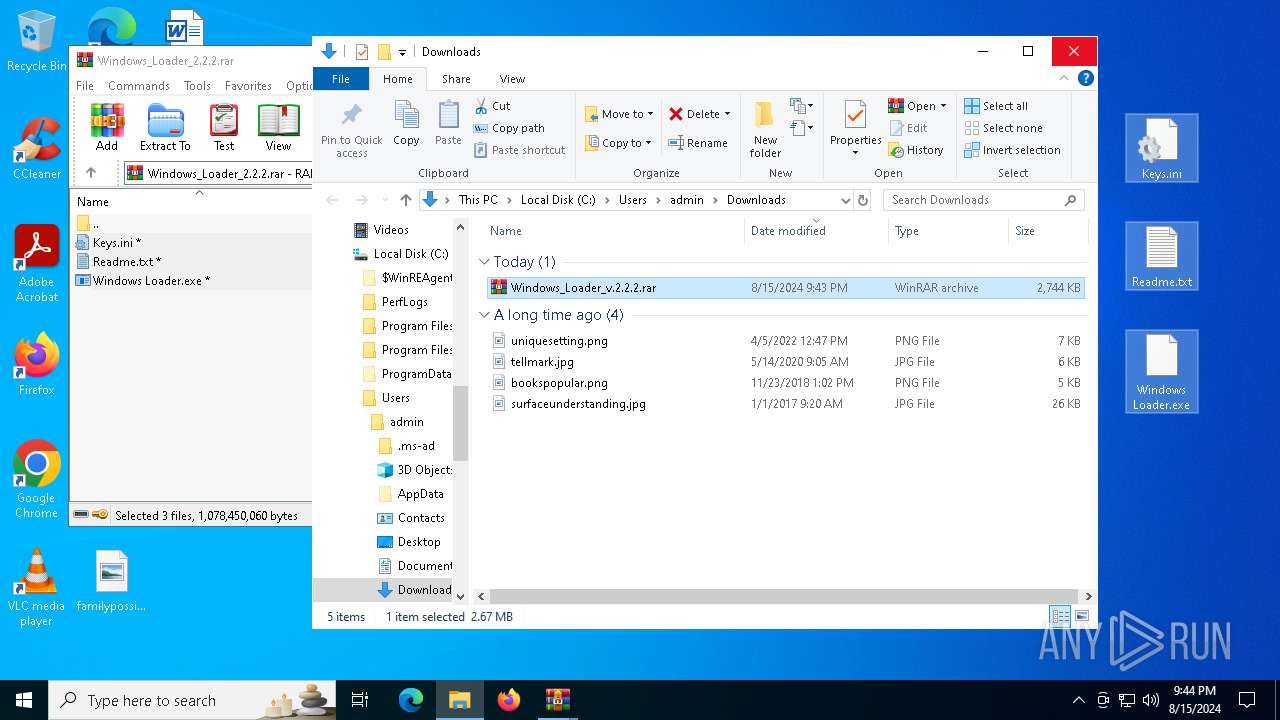
The process uses the downloaded file
- firefox.exe (PID: 6360)
- WinRAR.exe (PID: 7516)
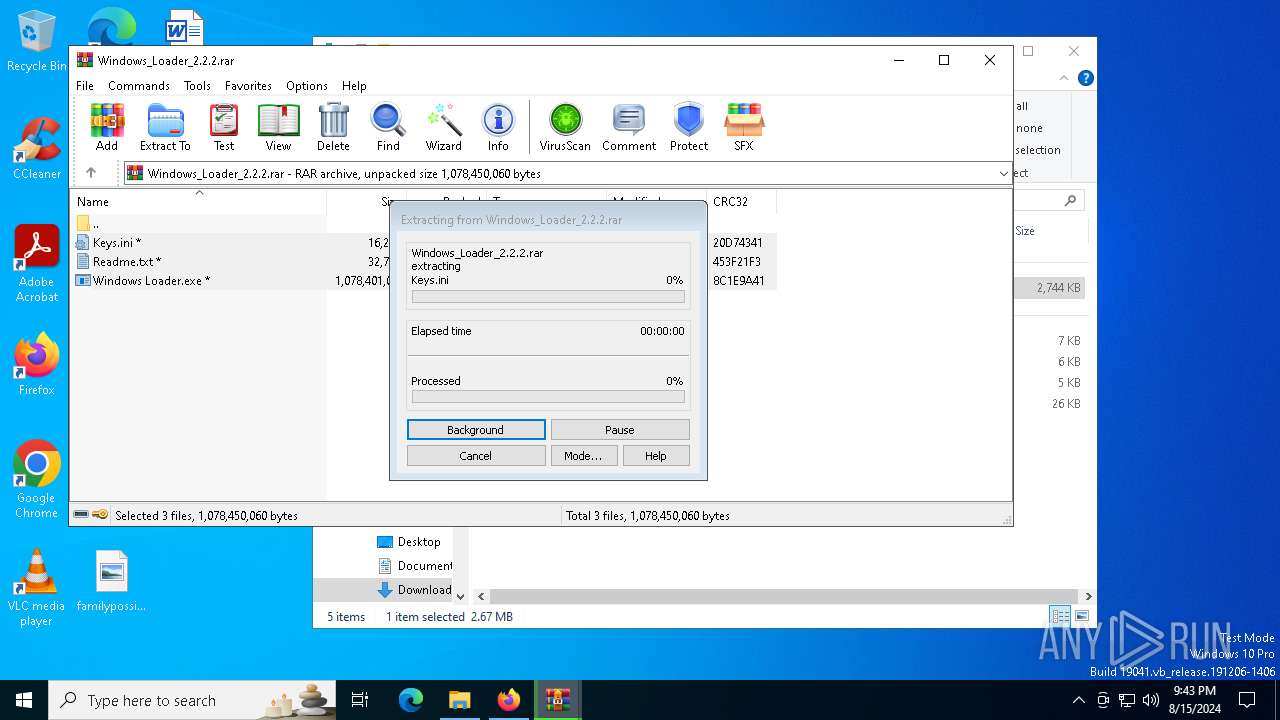
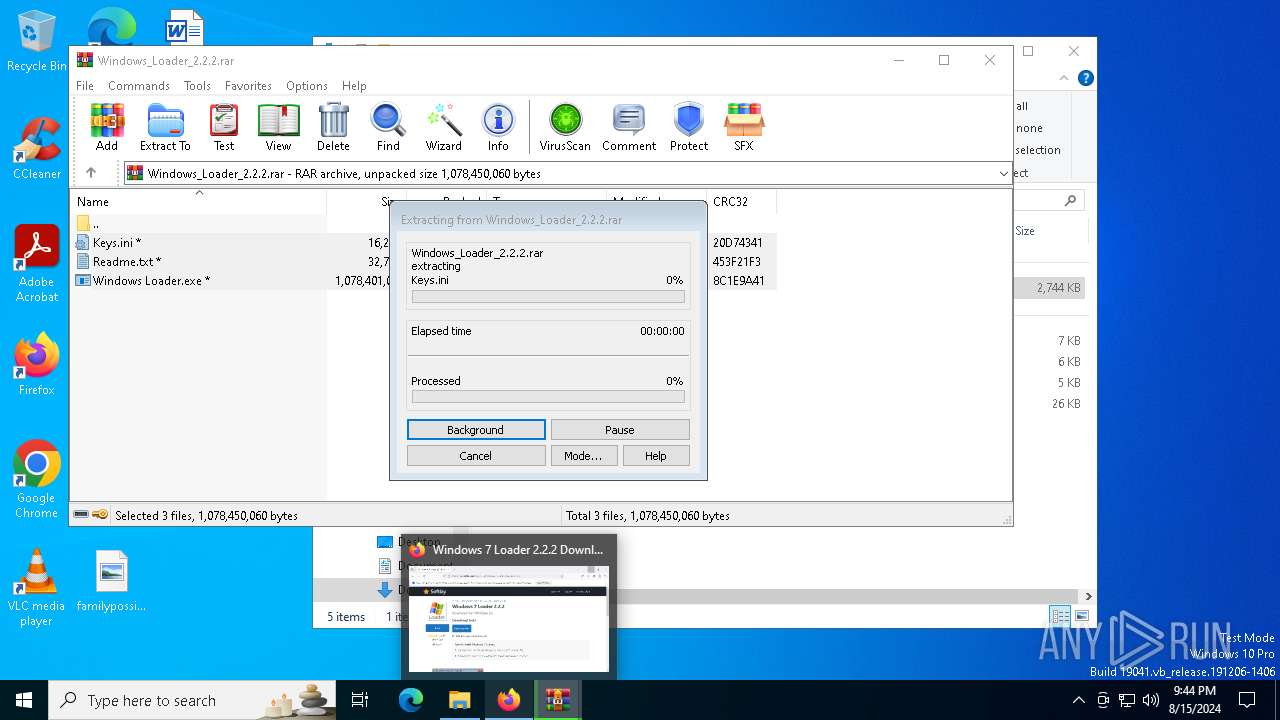
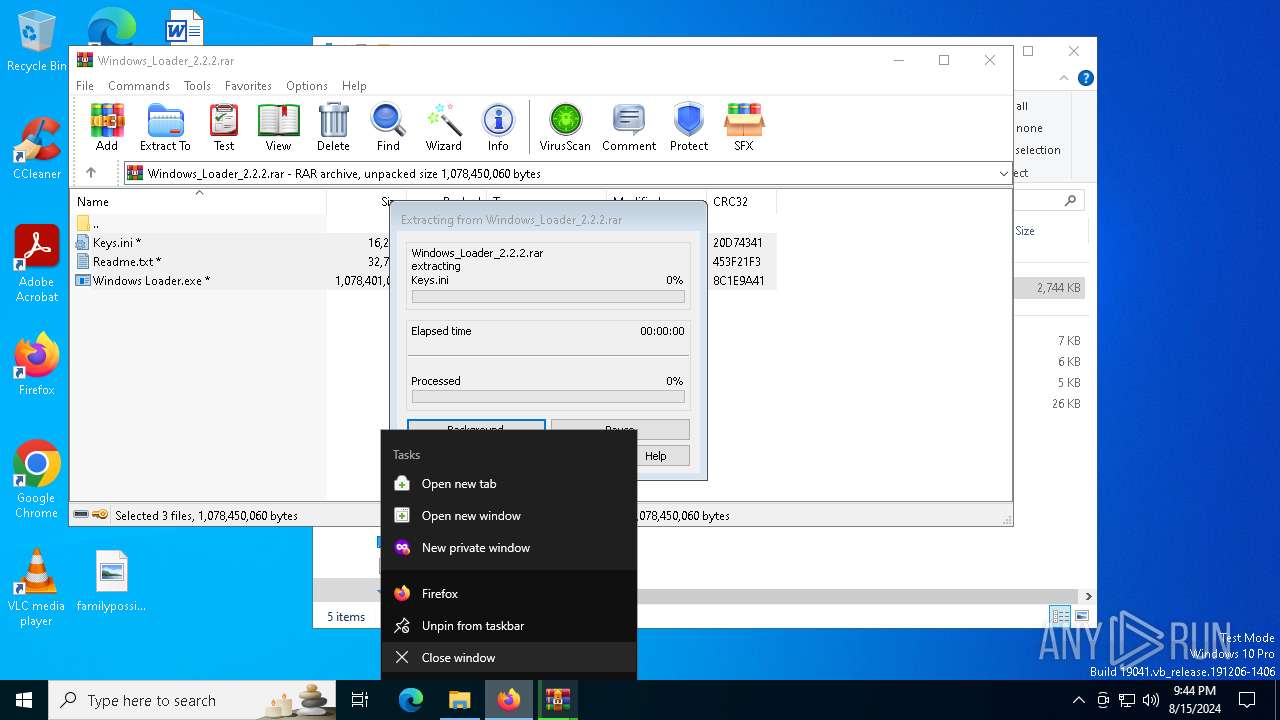
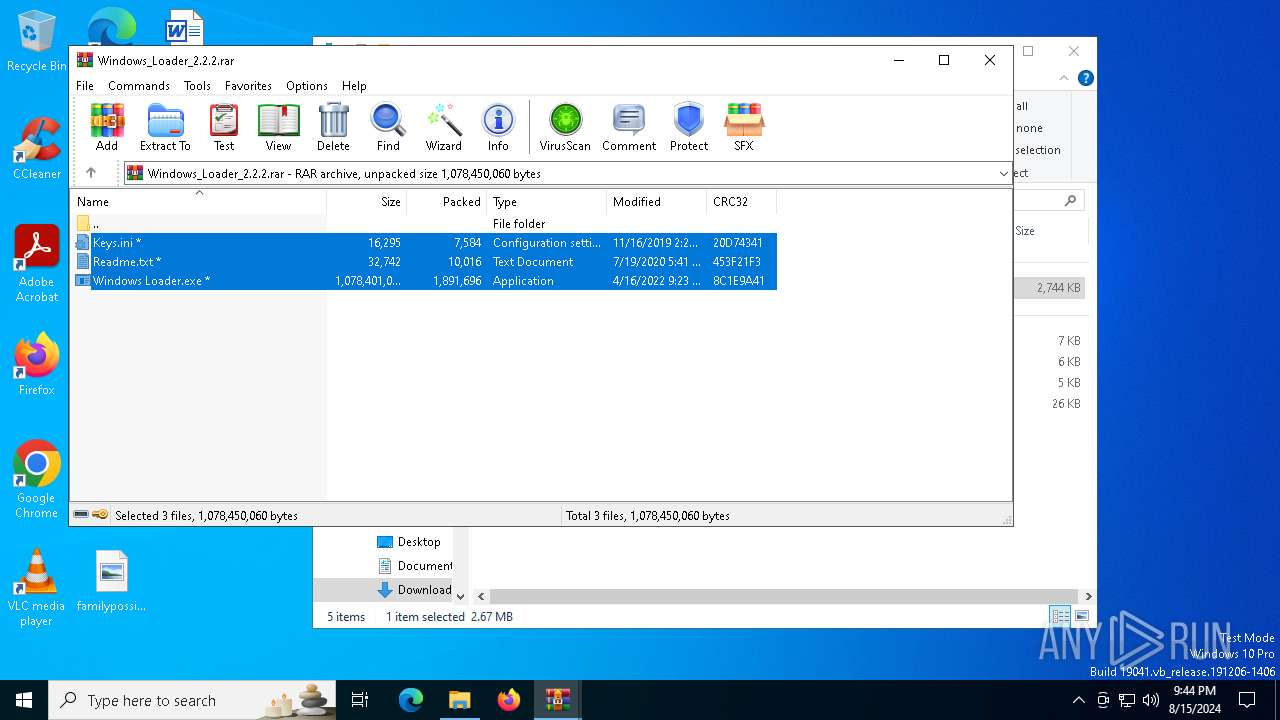
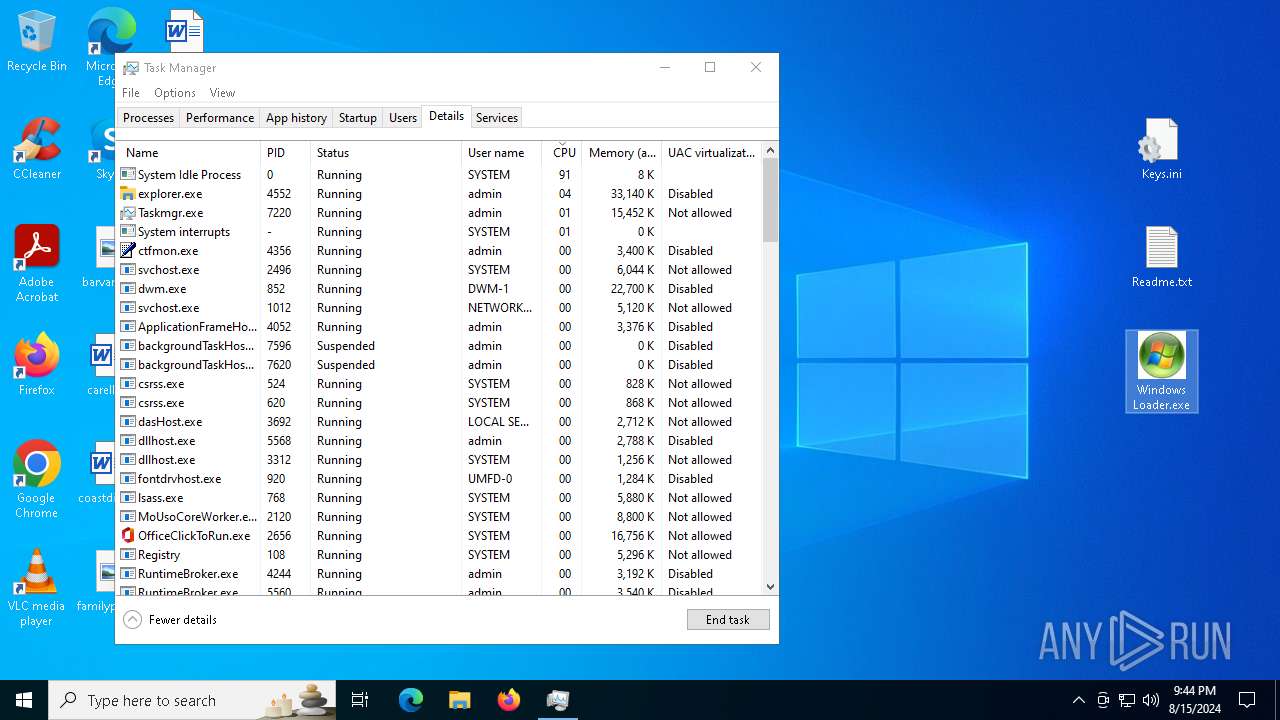
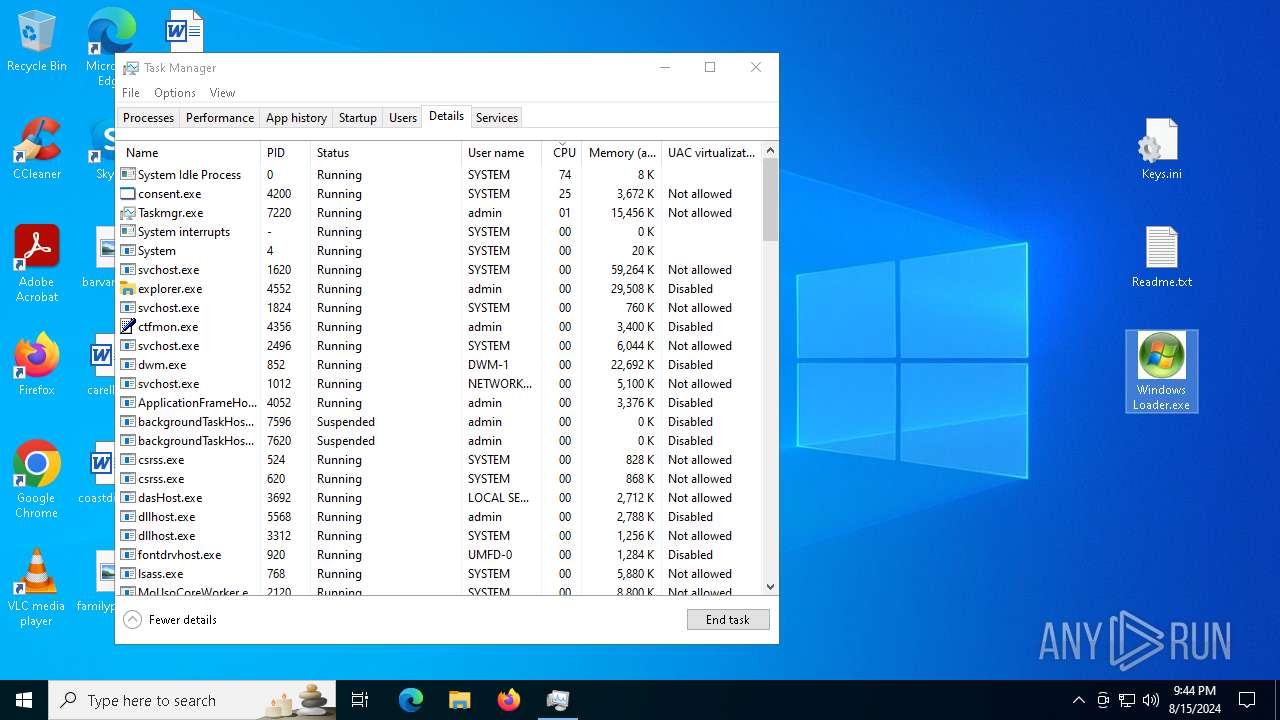
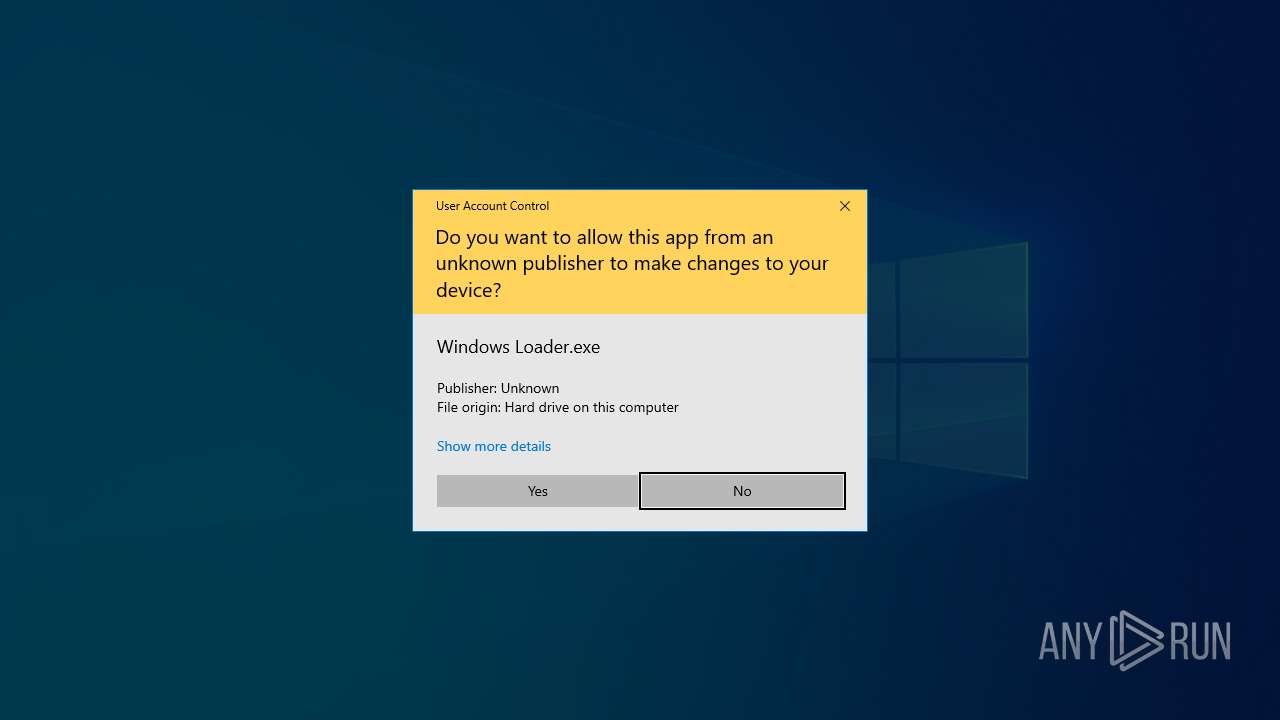
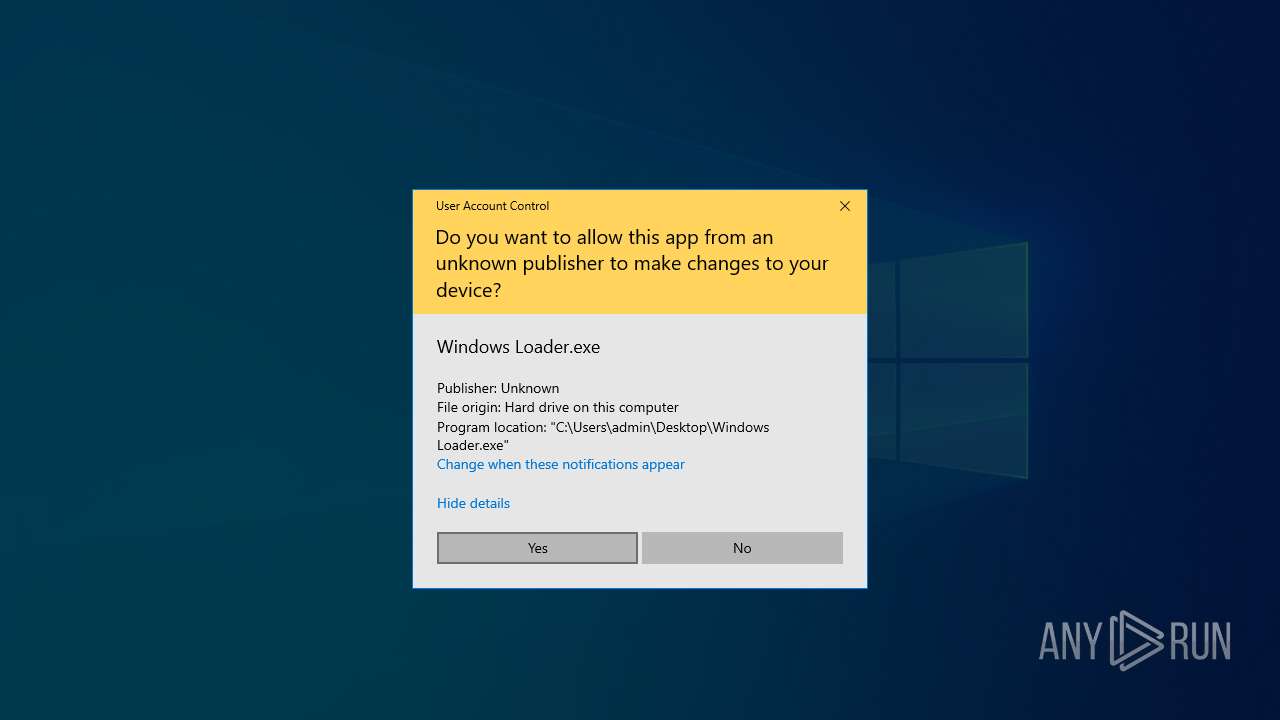
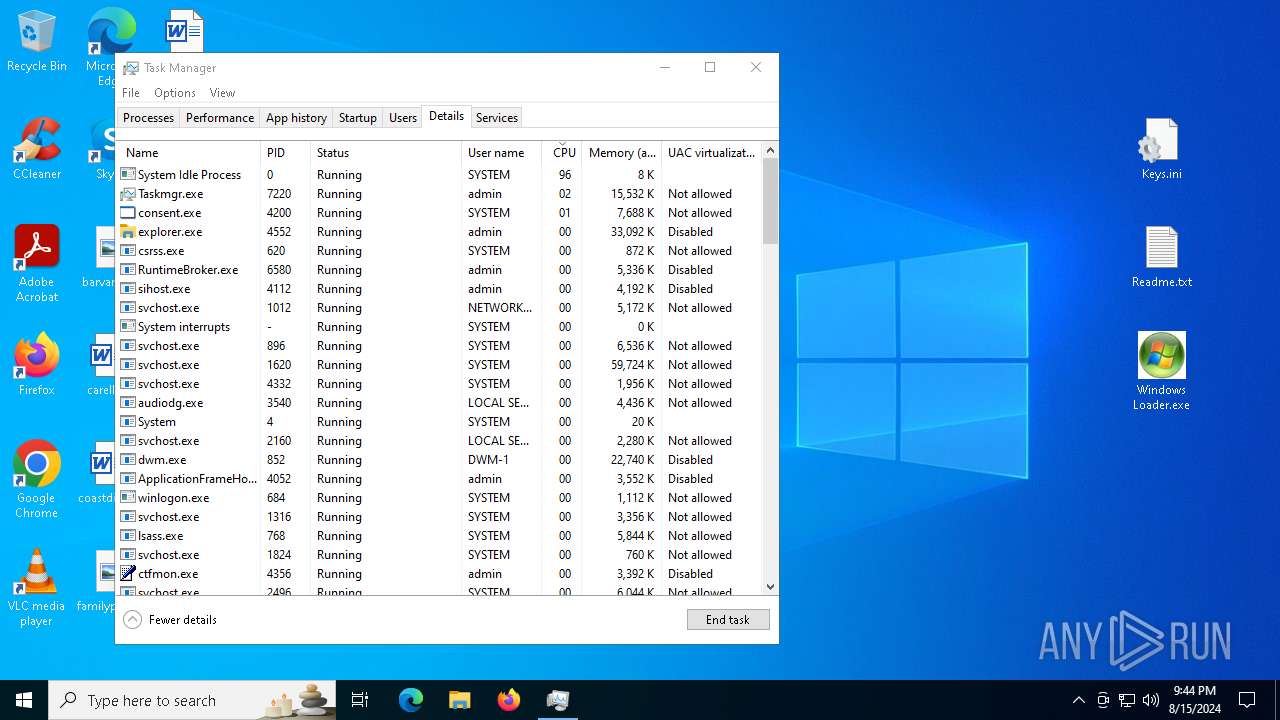
Manual execution by a user
- WinRAR.exe (PID: 7516)
- notepad.exe (PID: 2272)
- Taskmgr.exe (PID: 7176)
- Windows Loader.exe (PID: 6980)
- Taskmgr.exe (PID: 6952)
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 7516)
- firefox.exe (PID: 6360)
Reads security settings of Internet Explorer
- notepad.exe (PID: 4784)
- notepad.exe (PID: 2272)
- Taskmgr.exe (PID: 7220)
- Taskmgr.exe (PID: 6952)
Checks supported languages
- ShellExperienceHost.exe (PID: 7968)
- TextInputHost.exe (PID: 7140)
- Windows Loader.exe (PID: 6980)
- activationdriver.exe (PID: 6720)
- services32.exe (PID: 6664)
- system32.exe (PID: 6460)
- windows loader.exe (PID: 6480)
- ftewk.exe (PID: 7284)
- ftewk.exe (PID: 3256)
- ftewk.exe (PID: 6548)
Reads the computer name
- ShellExperienceHost.exe (PID: 7968)
- TextInputHost.exe (PID: 7140)
- Windows Loader.exe (PID: 6980)
- activationdriver.exe (PID: 6720)
- services32.exe (PID: 6664)
- windows loader.exe (PID: 6480)
- system32.exe (PID: 6460)
- ftewk.exe (PID: 7284)
- ftewk.exe (PID: 3256)
- ftewk.exe (PID: 6548)
Process checks computer location settings
- Windows Loader.exe (PID: 6980)
- activationdriver.exe (PID: 6720)
- system32.exe (PID: 6460)
- ftewk.exe (PID: 7284)
Create files in a temporary directory
- activationdriver.exe (PID: 6720)
- services32.exe (PID: 6664)
- system32.exe (PID: 6460)
- ftewk.exe (PID: 7284)
Reads the machine GUID from the registry
- services32.exe (PID: 6664)
Reads Environment values
- windows loader.exe (PID: 6480)
- ftewk.exe (PID: 7284)
- services32.exe (PID: 6664)
Checks proxy server information
- ftewk.exe (PID: 7284)
- WerFault.exe (PID: 7476)
- services32.exe (PID: 6664)
Reads the software policy settings
- services32.exe (PID: 6664)
- WerFault.exe (PID: 7476)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6364)
- services32.exe (PID: 6664)
- powershell.exe (PID: 7188)
- powershell.exe (PID: 4364)
- powershell.exe (PID: 1044)
- powershell.exe (PID: 1420)
- powershell.exe (PID: 3292)
- powershell.exe (PID: 7648)
- powershell.exe (PID: 5552)
- powershell.exe (PID: 7584)
- powershell.exe (PID: 6404)
- powershell.exe (PID: 7164)
- powershell.exe (PID: 7516)
- powershell.exe (PID: 4080)
- powershell.exe (PID: 6892)
- powershell.exe (PID: 1656)
Creates files or folders in the user directory
- WerFault.exe (PID: 7476)
- services32.exe (PID: 6664)
- ftewk.exe (PID: 7284)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6364)
- powershell.exe (PID: 7188)
- powershell.exe (PID: 4364)
- powershell.exe (PID: 1044)
- powershell.exe (PID: 7584)
- powershell.exe (PID: 1420)
- powershell.exe (PID: 7648)
- powershell.exe (PID: 7516)
- powershell.exe (PID: 6892)
- powershell.exe (PID: 5552)
- powershell.exe (PID: 6404)
- powershell.exe (PID: 7164)
- powershell.exe (PID: 1656)
- powershell.exe (PID: 4080)
UPX packer has been detected
- windows loader.exe (PID: 6480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
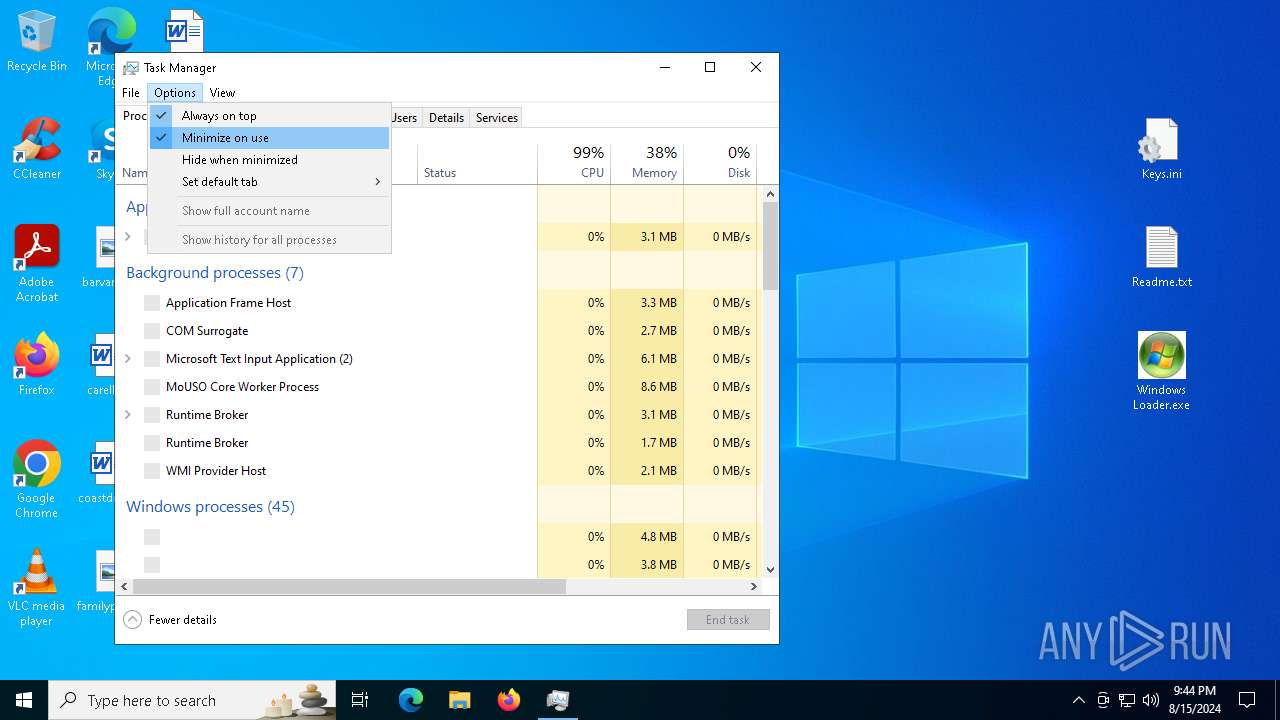
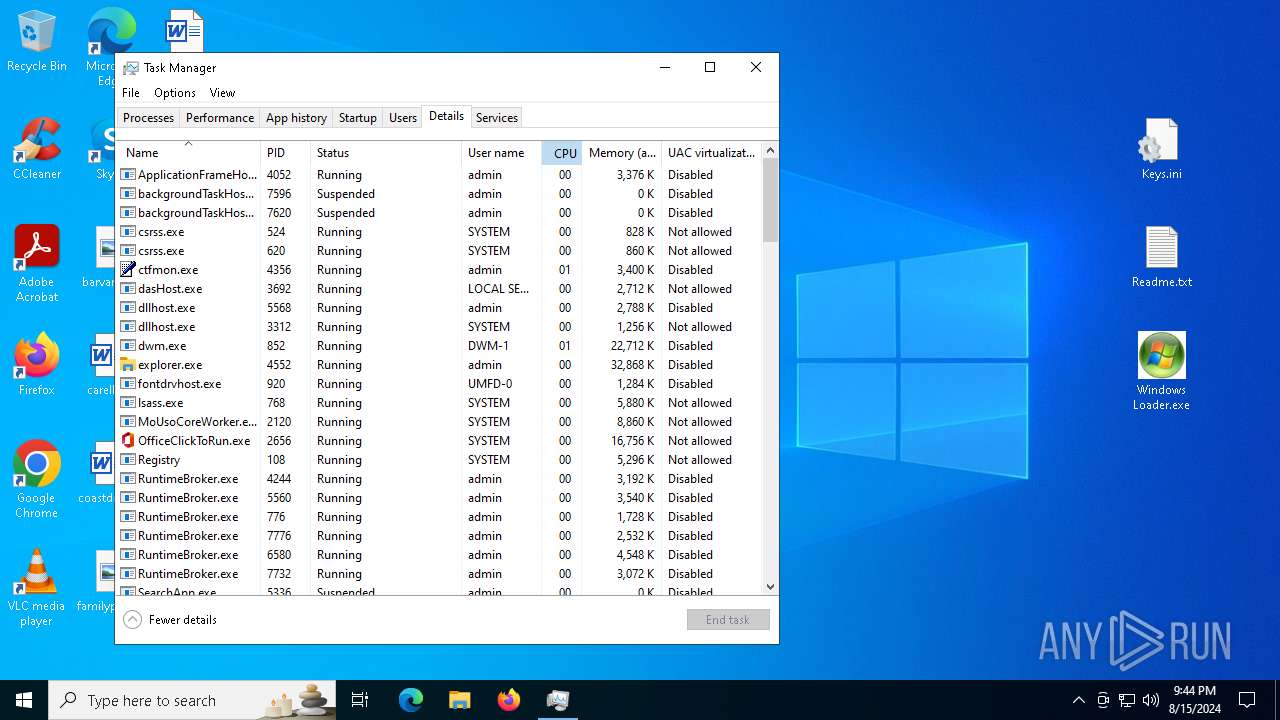
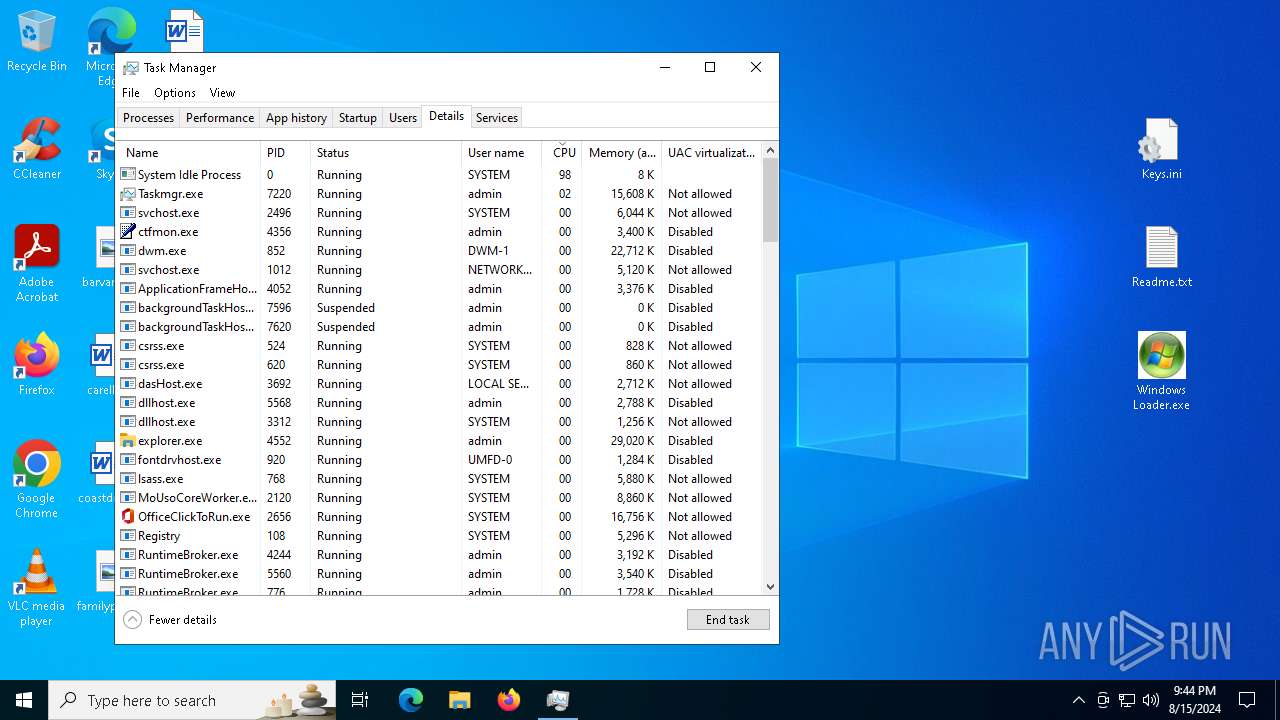
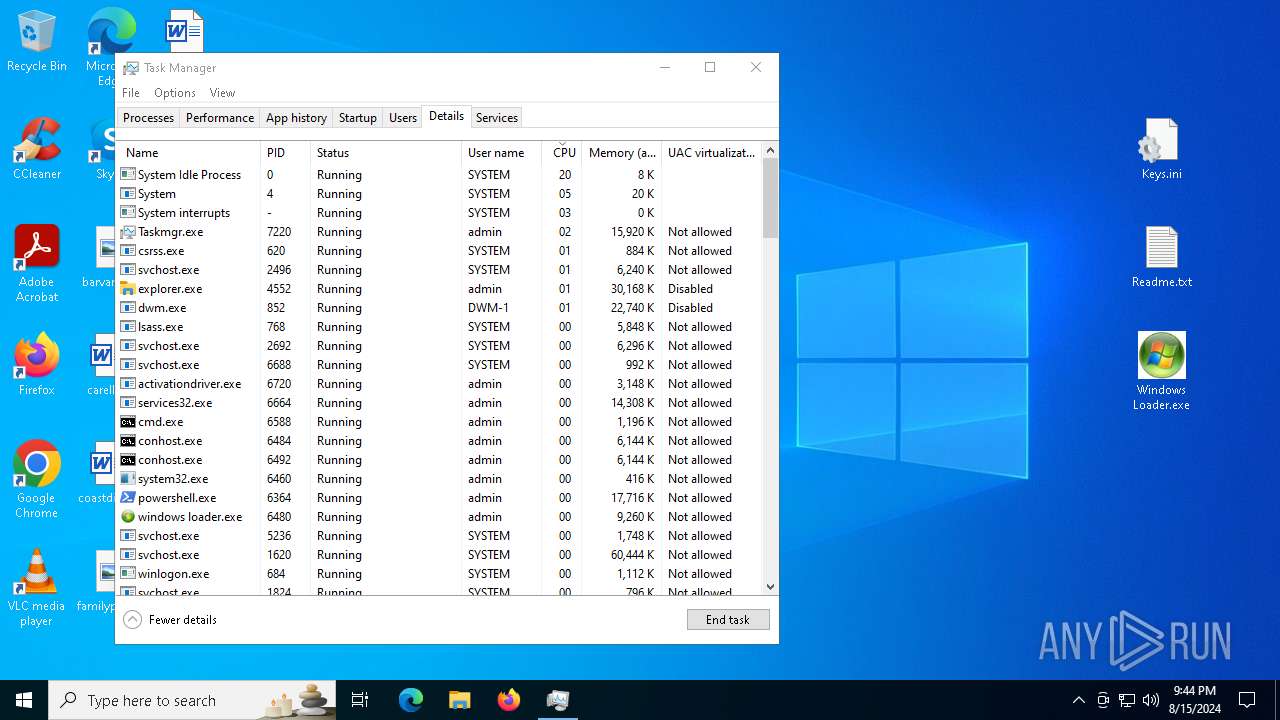
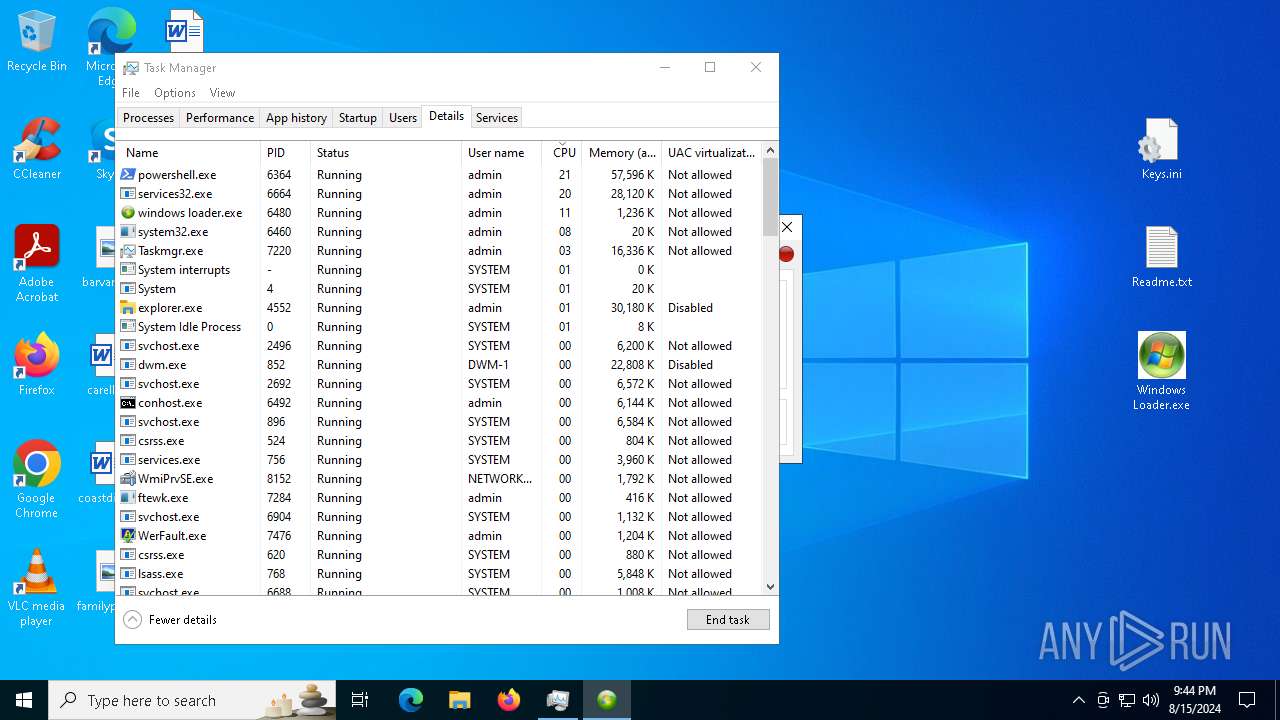
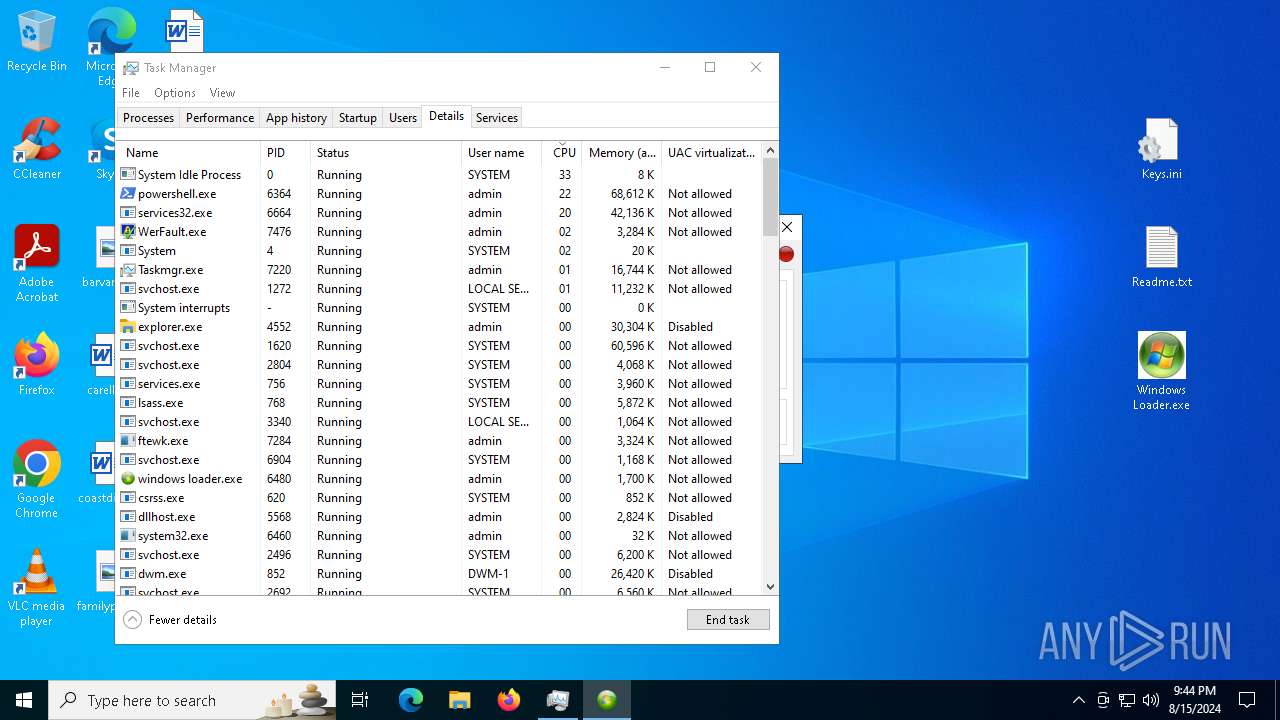
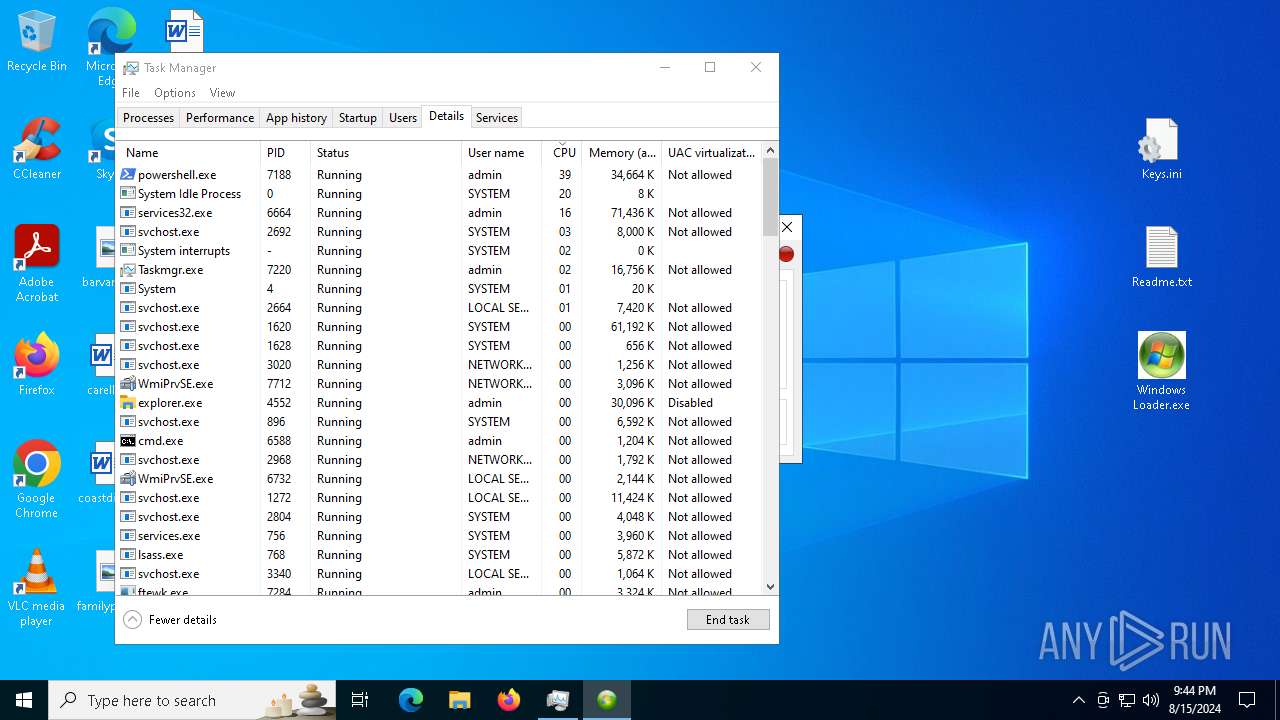
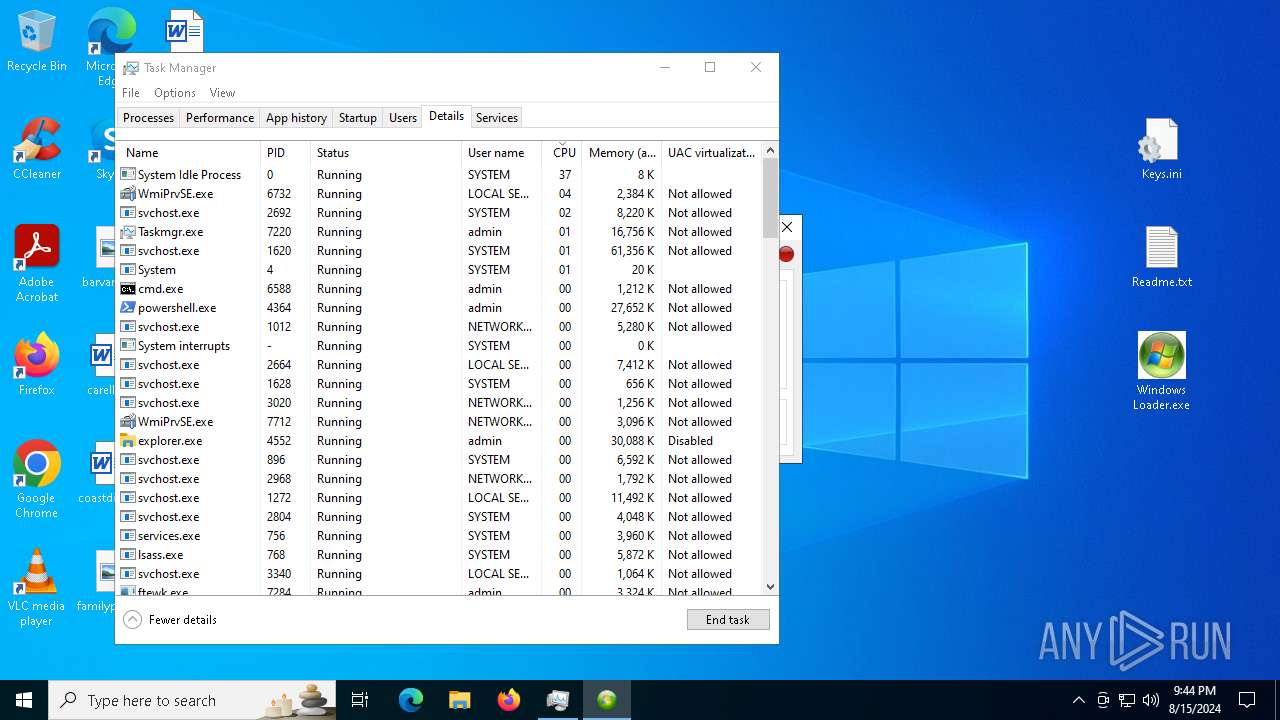
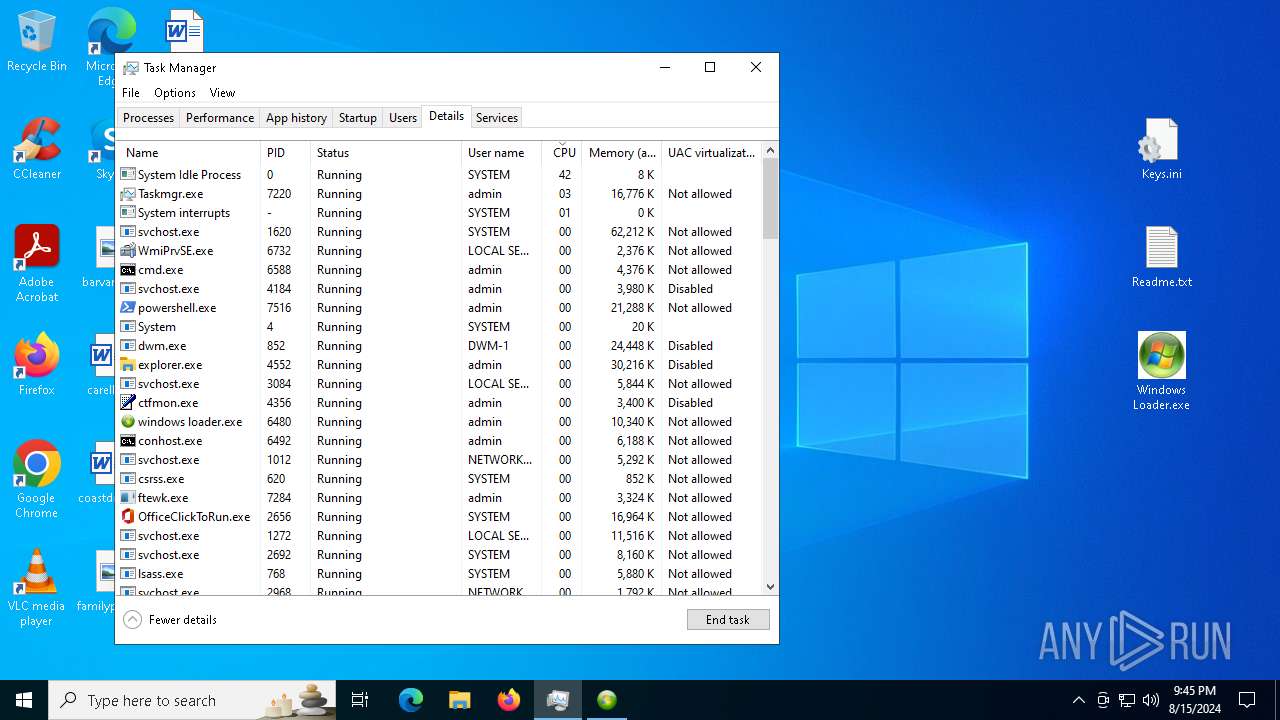
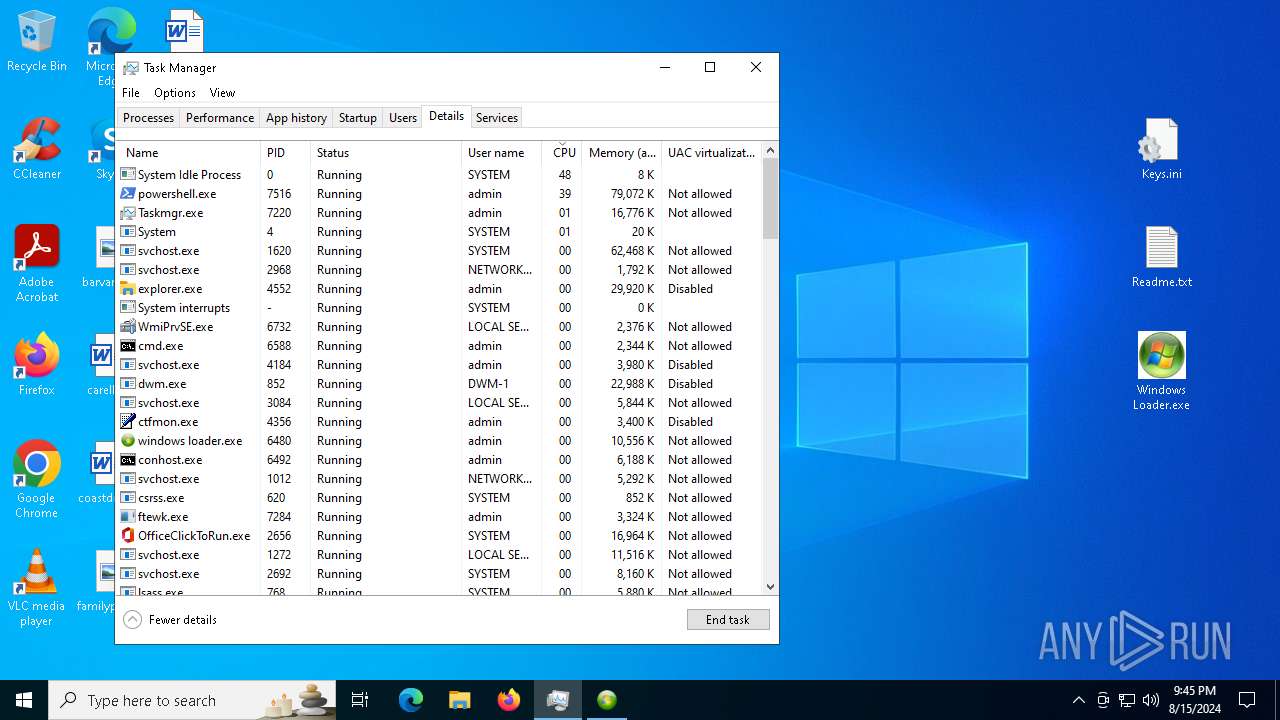
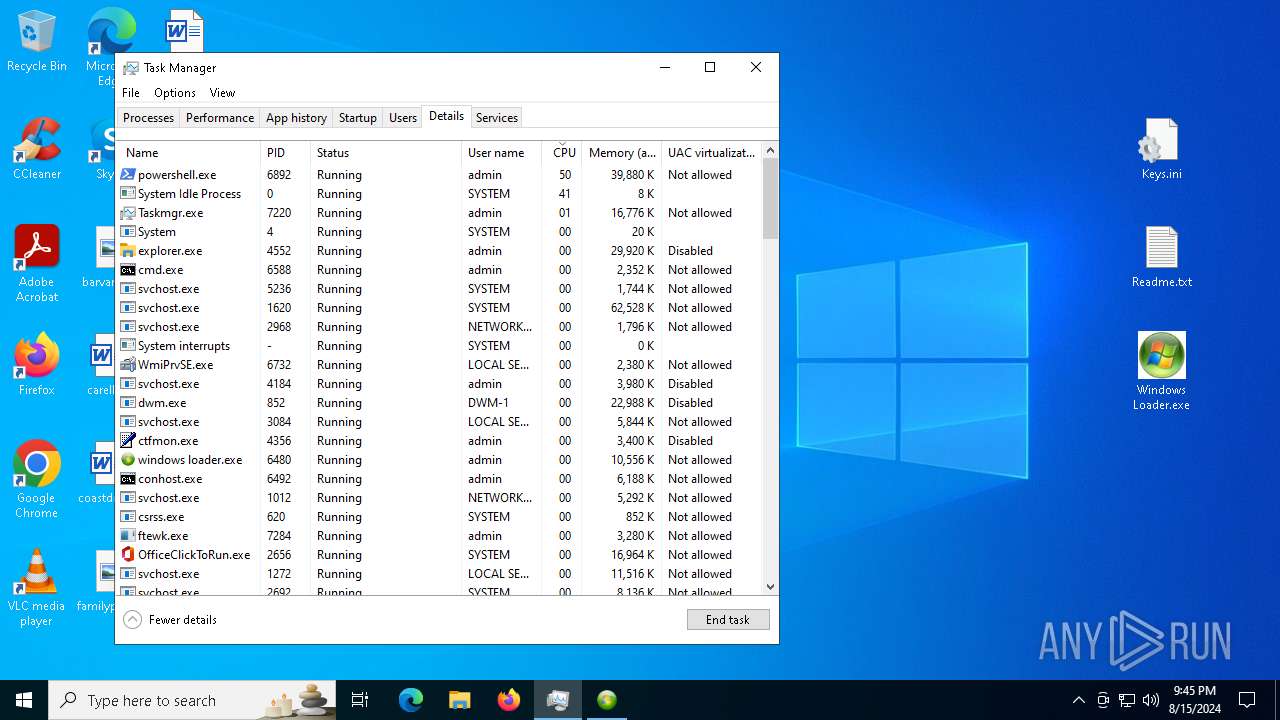
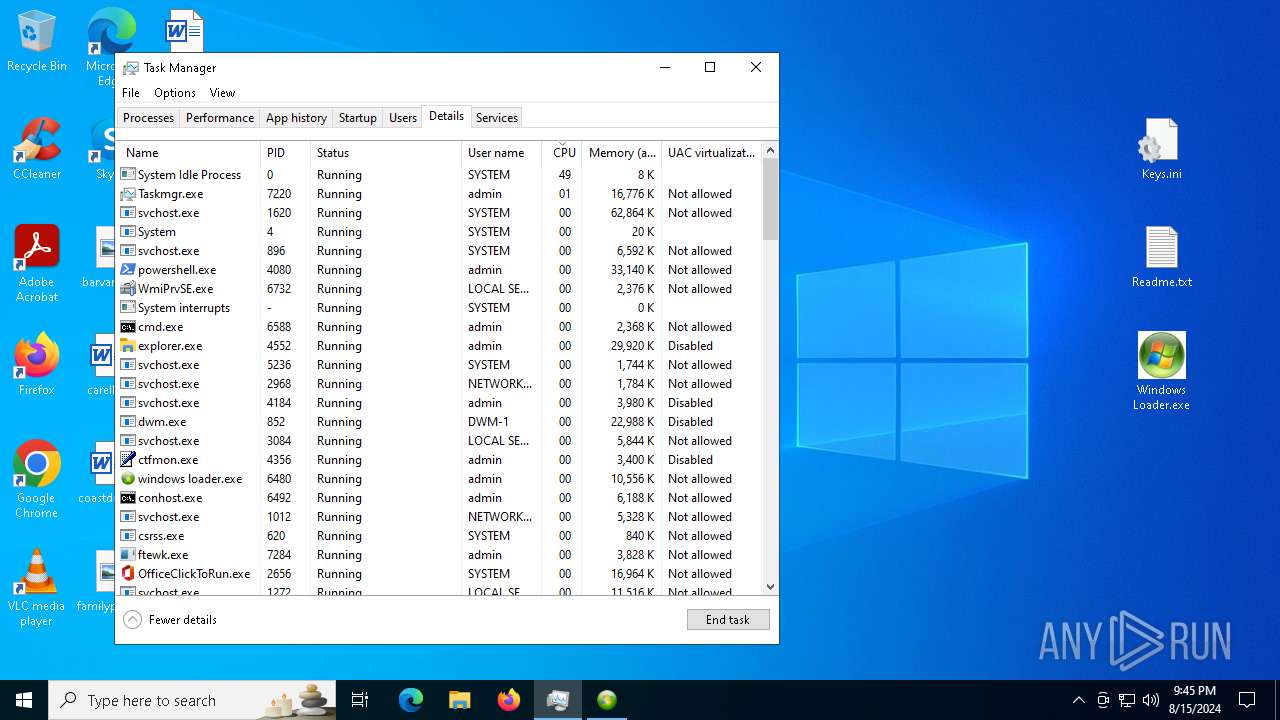
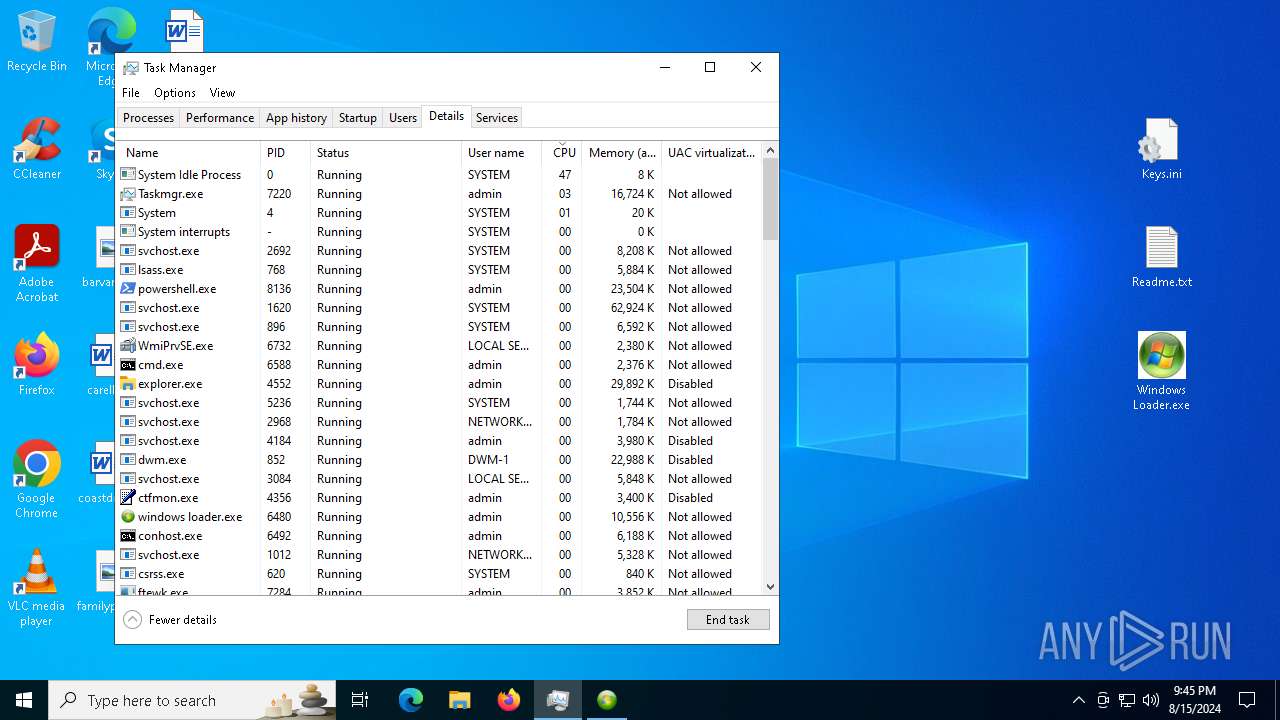
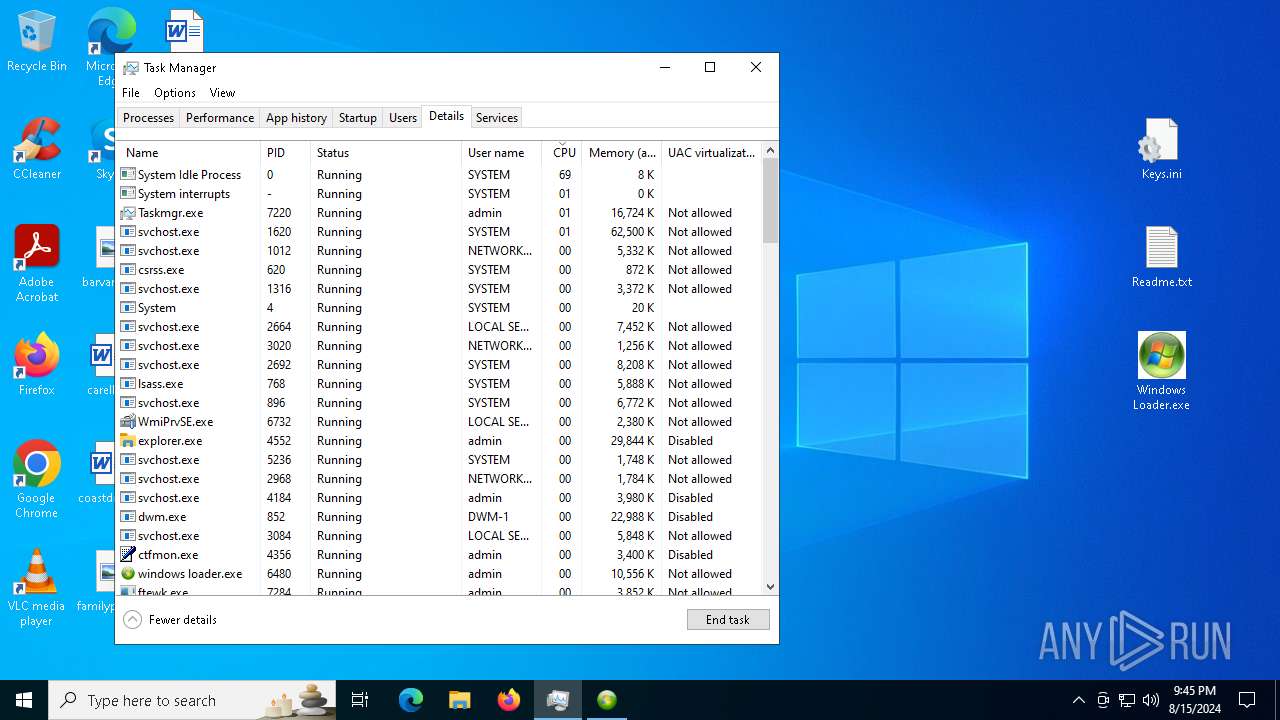
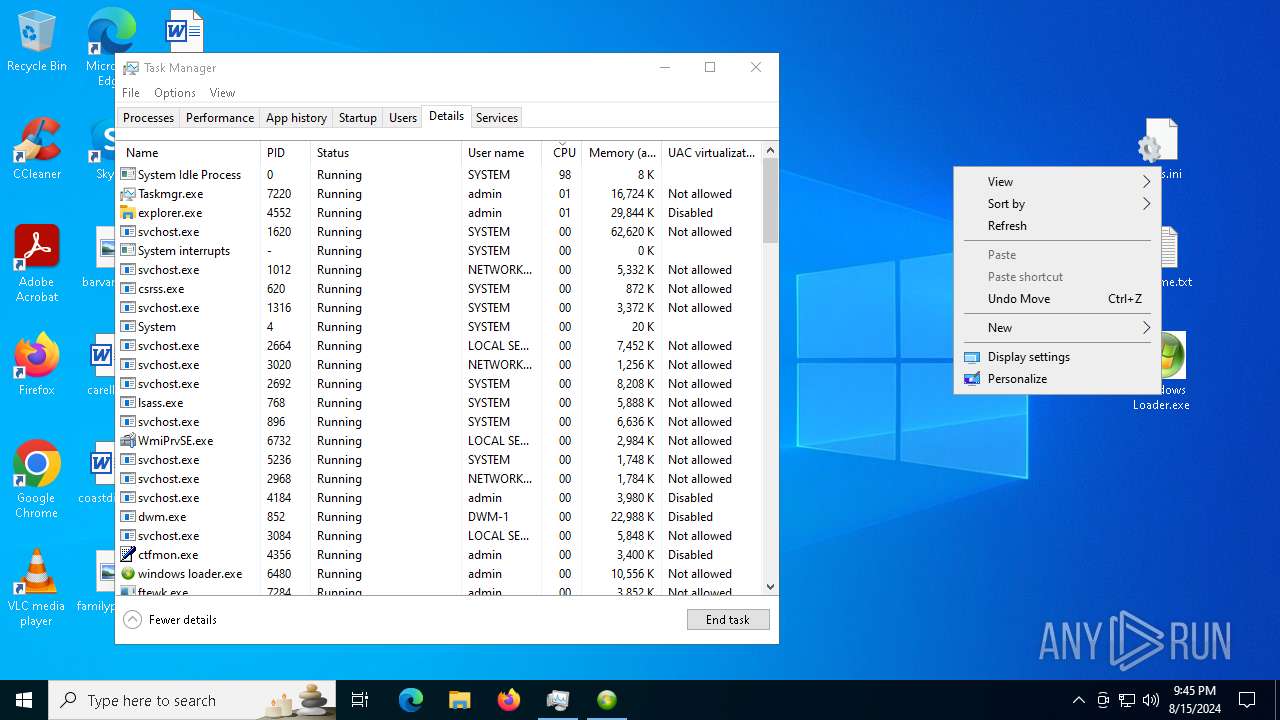
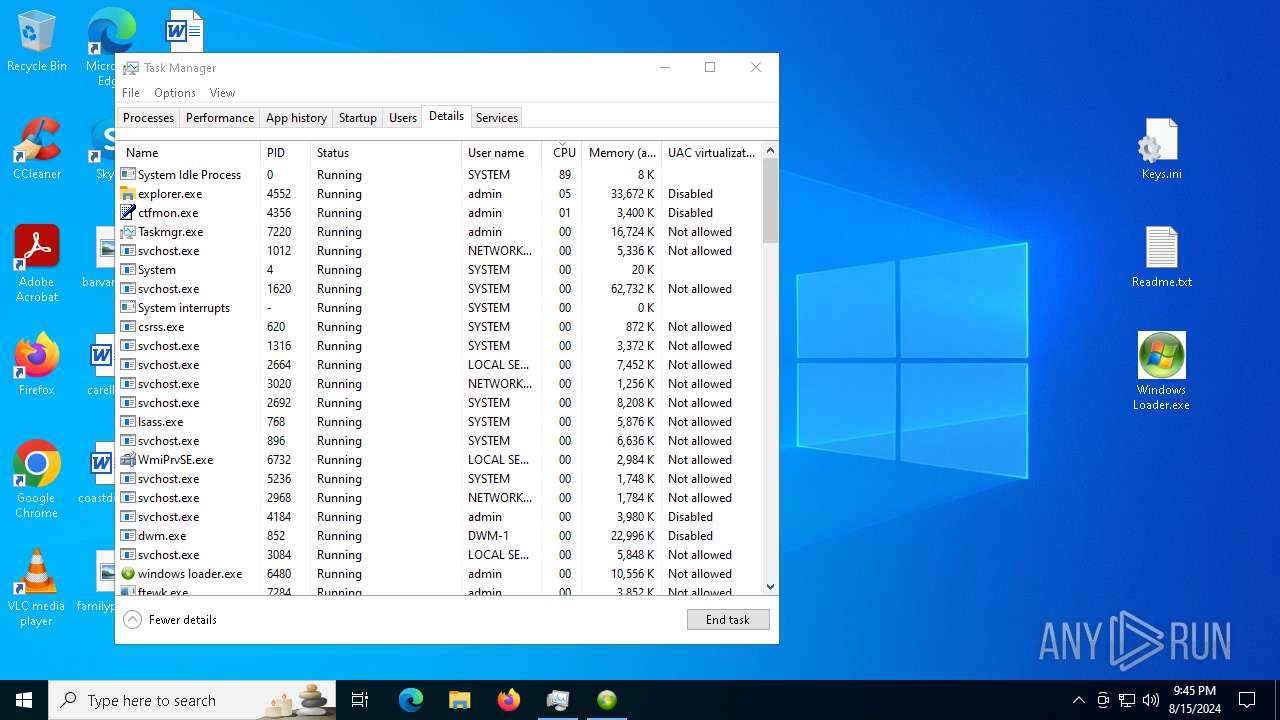
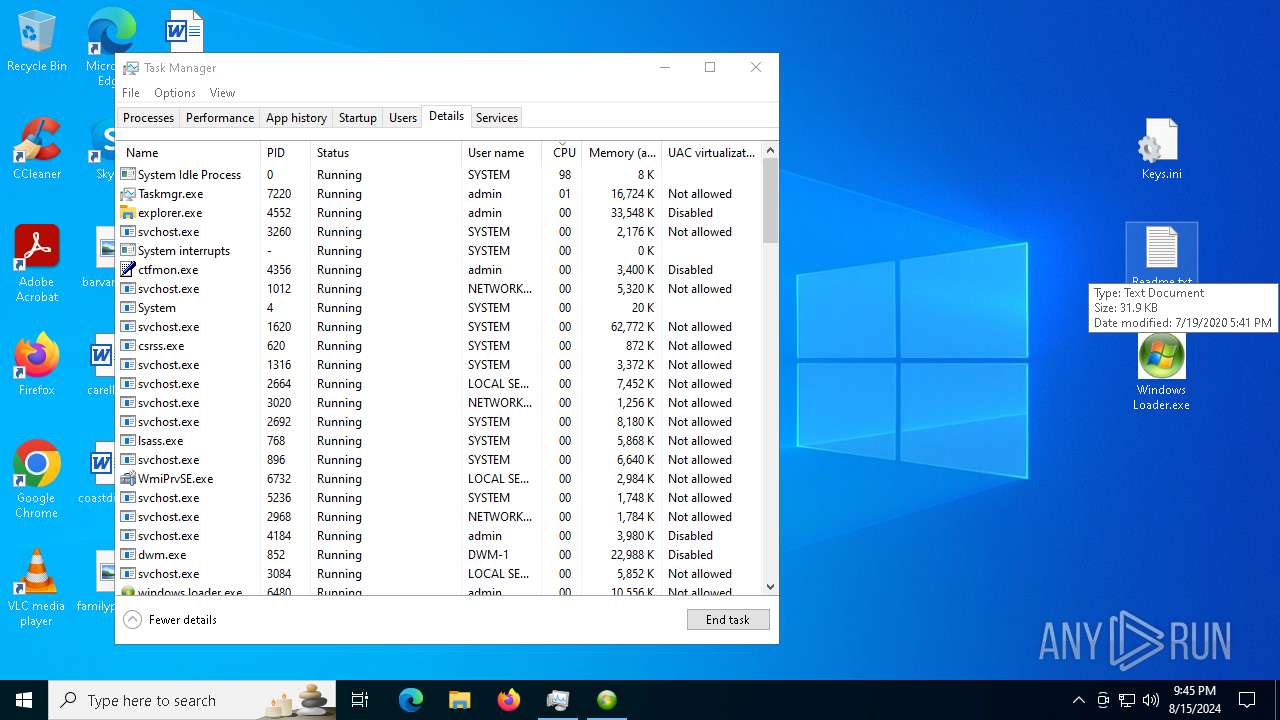
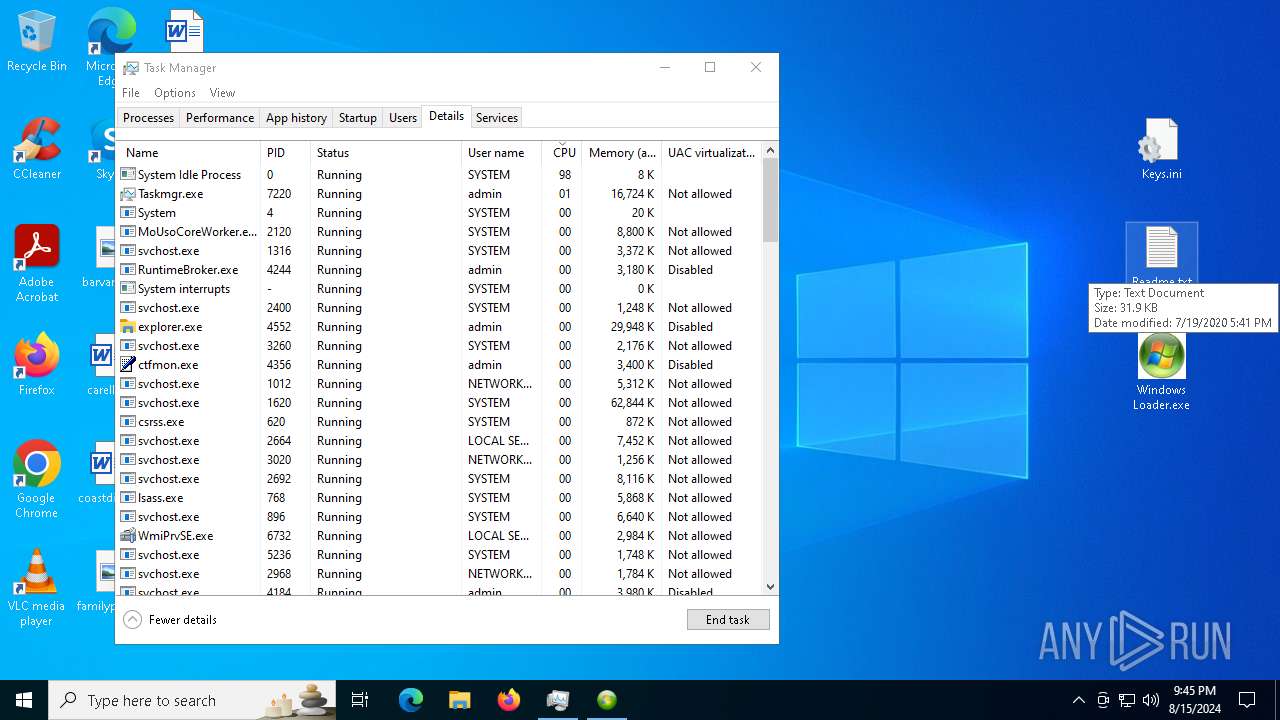
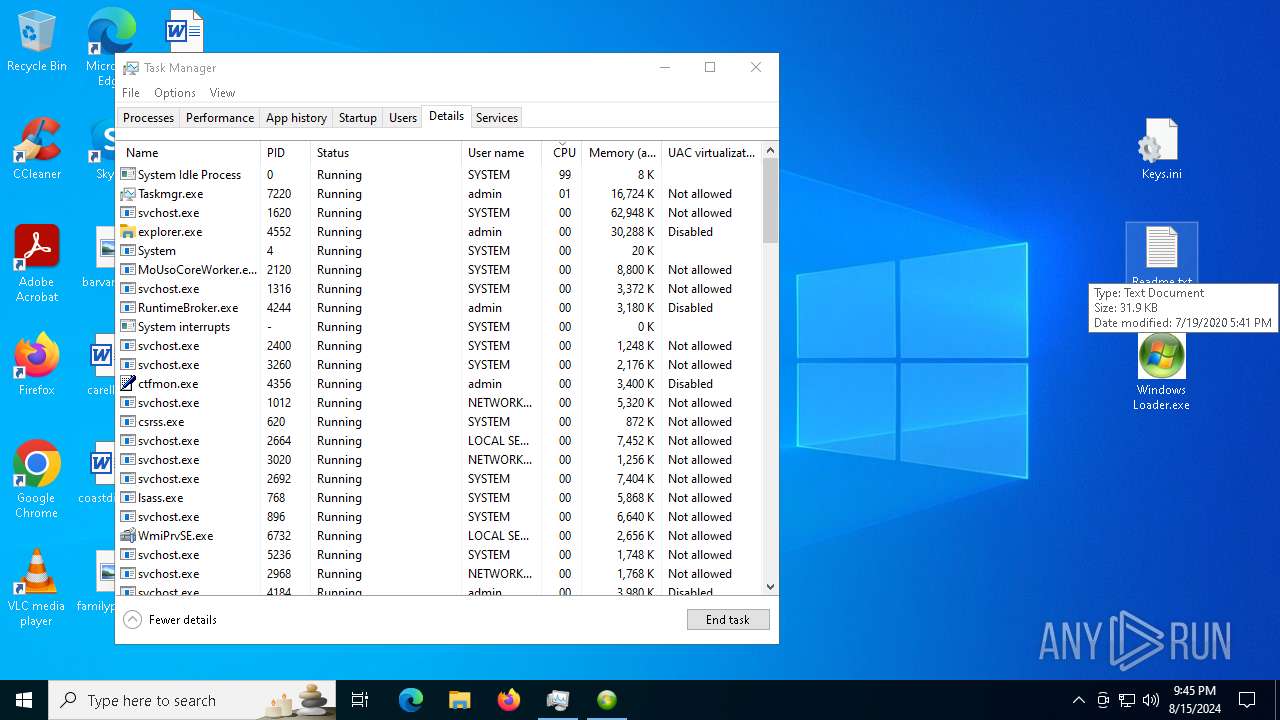
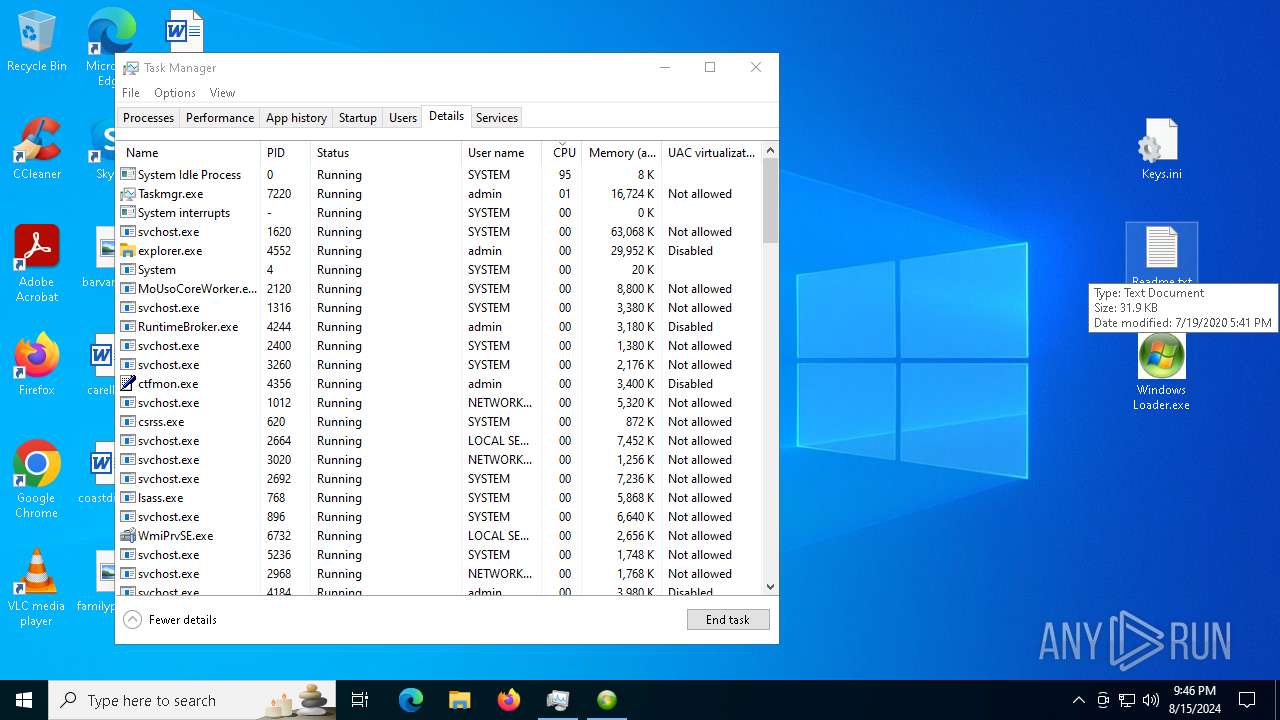
Total processes
229
Monitored processes
87
Malicious processes
6
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5944 -childID 5 -isForBrowser -prefsHandle 5804 -prefMapHandle 5744 -prefsLen 31161 -prefMapSize 244343 -jsInitHandle 1064 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {2cd29575-42b6-423c-ae55-b0d849923932} 6360 "\\.\pipe\gecko-crash-server-pipe.6360" 1a2e9b41a10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 460 | reg add "HKLM\Software\Policies\Microsoft\Windows Defender\SpyNet" /v "SubmitSamplesConsent" /t REG_DWORD /d "2" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1044 | powershell.exe -command "Set-MpPreference -DisableIOAVProtection $true" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1060 | schtasks /Change /TN "Microsoft\Windows\Windows Defender\Windows Defender Verification" /Disable | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5248 -parentBuildID 20240213221259 -sandboxingKind 0 -prefsHandle 5128 -prefMapHandle 4264 -prefsLen 34713 -prefMapSize 244343 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {ca9b9701-7695-4291-95cc-2c38f6147404} 6360 "\\.\pipe\gecko-crash-server-pipe.6360" 1a2e8eba710 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
| 1420 | powershell.exe -command "Set-MpPreference -DisablePrivacyMode $true" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1488 | reg delete "HKLM\Software\Microsoft\Windows\CurrentVersion\Run" /v "SecurityHealth" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1656 | powershell.exe -command "Set-MpPreference -LowThreatDefaultAction 6" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2272 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Readme.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2900 | reg add "HKLM\Software\Policies\Microsoft\Windows Defender\Real-Time Protection" /v "DisableBehaviorMonitoring" /t REG_DWORD /d "1" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
148 320
Read events
148 107
Write events
194
Delete events
19
Modification events
| (PID) Process: | (6296) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 028F41C800000000 | |||
| (PID) Process: | (6360) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 257C43C800000000 | |||
| (PID) Process: | (6360) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Progress |
Value: 0 | |||
| (PID) Process: | (6360) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Progress |
Value: 1 | |||
| (PID) Process: | (6360) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Installer\308046B0AF4A39CB |
| Operation: | delete value | Name: | installer.taskbarpin.win10.enabled |
Value: | |||
| (PID) Process: | (6360) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (6360) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (6360) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Theme |
Value: 1 | |||
| (PID) Process: | (6360) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Enabled |
Value: 1 | |||
| (PID) Process: | (6360) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
Executable files
5
Suspicious files
188
Text files
73
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6360 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6360 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:539C56CBB4C1DACC1A834B52654C9870 | SHA256:4362FD3F500B48FB5D66B61BE54920D6BB783747C8E4EF43E7FA5F94DFA285F2 | |||
| 6360 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6360 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 6360 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 6360 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6360 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\AlternateServices.bin | binary | |
MD5:5F4ADE587CCCB9C0DE51C15844671F5B | SHA256:20A00CD193159F96537774641FBC8CDCD93E5E60BB41BB05297720C47562BA7B | |||
| 6360 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 6360 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6360 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\datareporting\glean\db\data.safe.tmp | dbf | |
MD5:3B156E12141F8CBCE9D60CDCE2077617 | SHA256:E6287E44B44ABEA20E1B2E3F415D22B9E5E5FBBC155AD9DADBABA63951B2AF6F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
106
DNS requests
145
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6360 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
6360 | firefox.exe | POST | 200 | 23.53.40.154:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
6360 | firefox.exe | POST | 200 | 172.217.16.195:80 | http://o.pki.goog/wr2 | unknown | — | — | unknown |
6360 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
6360 | firefox.exe | POST | 200 | 2.16.241.15:80 | http://r11.o.lencr.org/ | unknown | — | — | unknown |
6360 | firefox.exe | POST | 200 | 2.16.241.15:80 | http://r11.o.lencr.org/ | unknown | — | — | unknown |
6360 | firefox.exe | POST | 200 | 95.101.54.99:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
6360 | firefox.exe | POST | 200 | 95.101.54.99:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
6360 | firefox.exe | POST | 200 | 172.217.16.195:80 | http://o.pki.goog/wr2 | unknown | — | — | unknown |
6360 | firefox.exe | POST | 200 | 95.101.54.99:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4056 | svchost.exe | 20.72.205.209:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4016 | RUXIMICS.exe | 20.72.205.209:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2120 | MoUsoCoreWorker.exe | 20.72.205.209:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6360 | firefox.exe | 142.250.186.67:443 | www.google.es | GOOGLE | US | whitelisted |
6360 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
6360 | firefox.exe | 34.117.188.166:443 | contile.services.mozilla.com | — | — | unknown |
6360 | firefox.exe | 142.250.184.234:443 | safebrowsing.googleapis.com | — | — | whitelisted |
6360 | firefox.exe | 34.107.243.93:443 | push.services.mozilla.com | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
www.google.es |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
o.pki.goog |
| whitelisted |