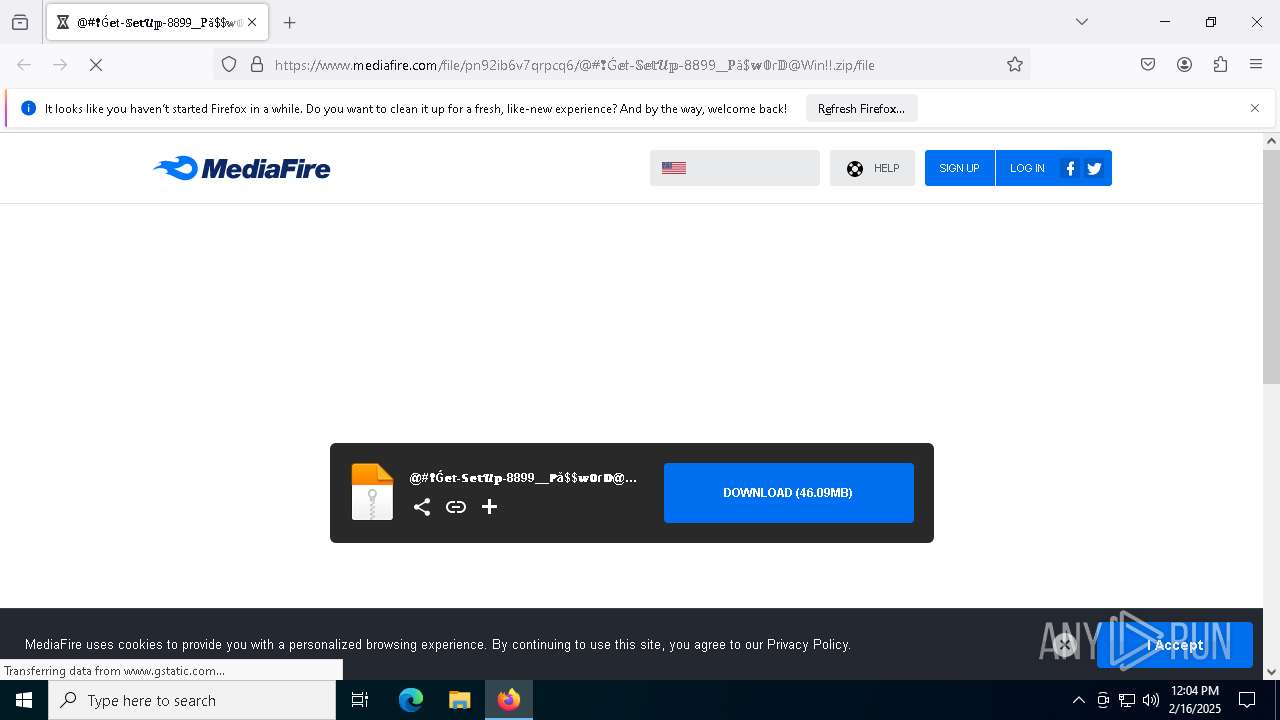
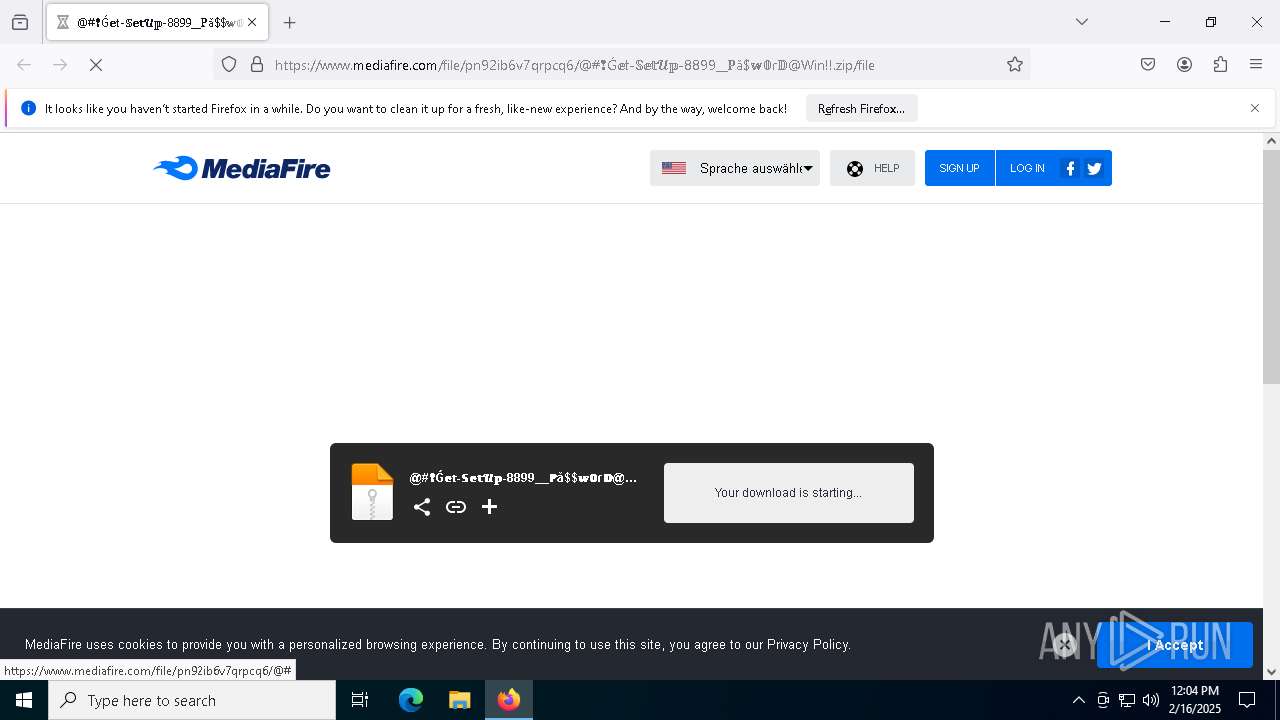
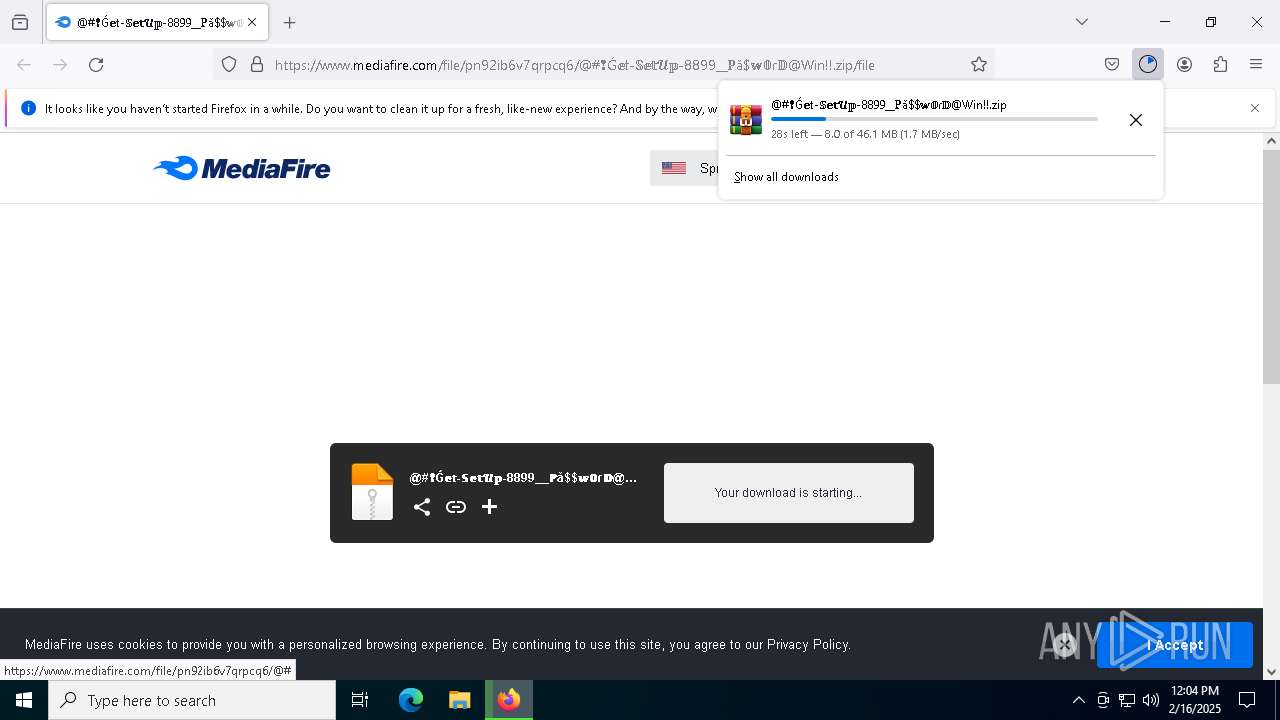
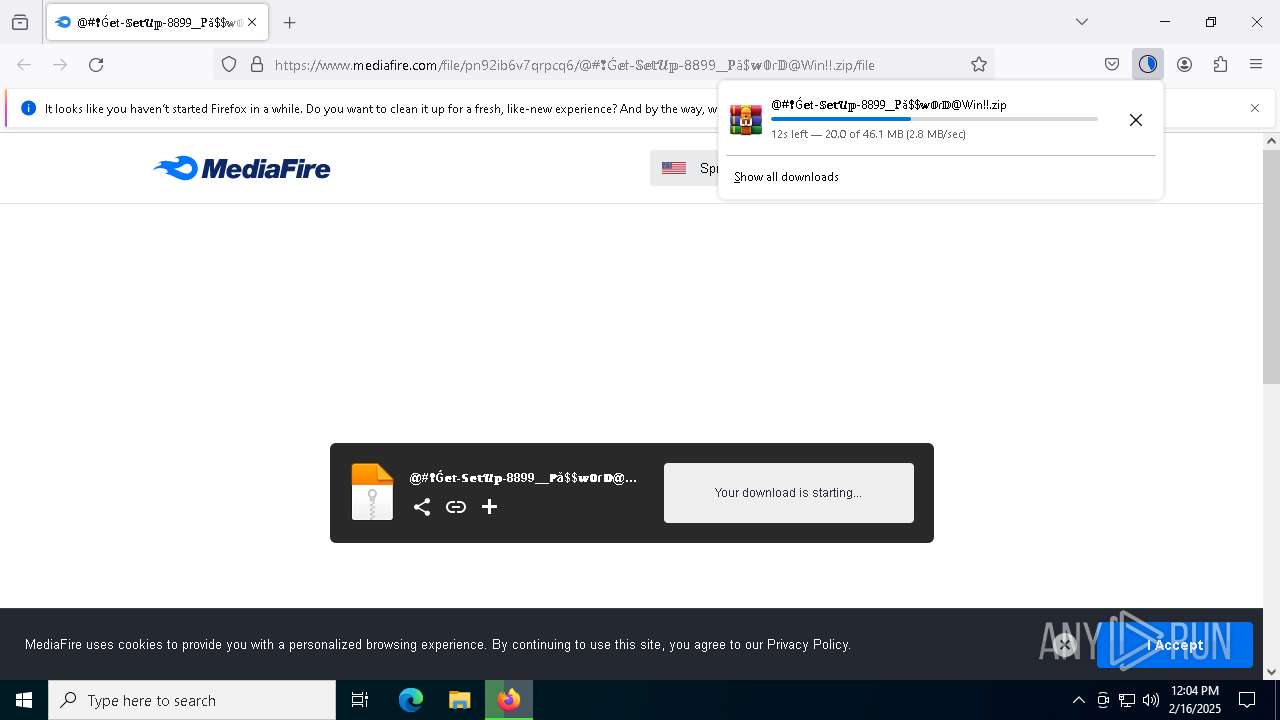
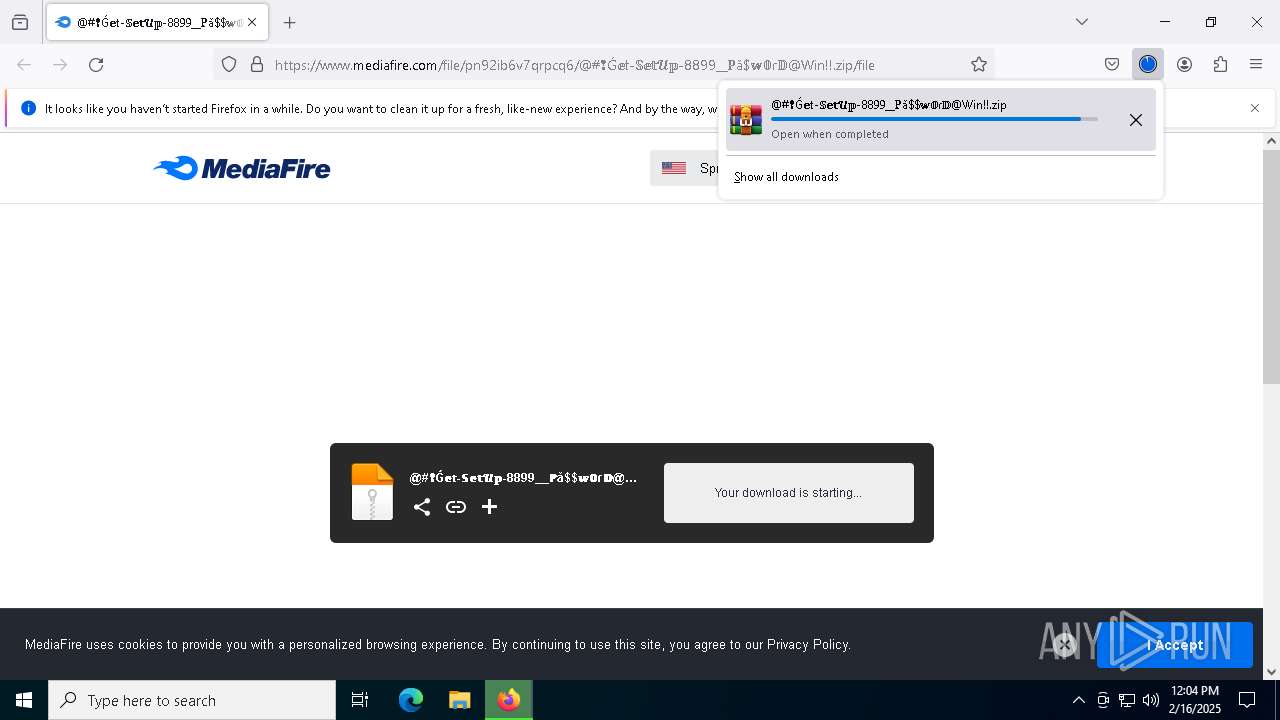
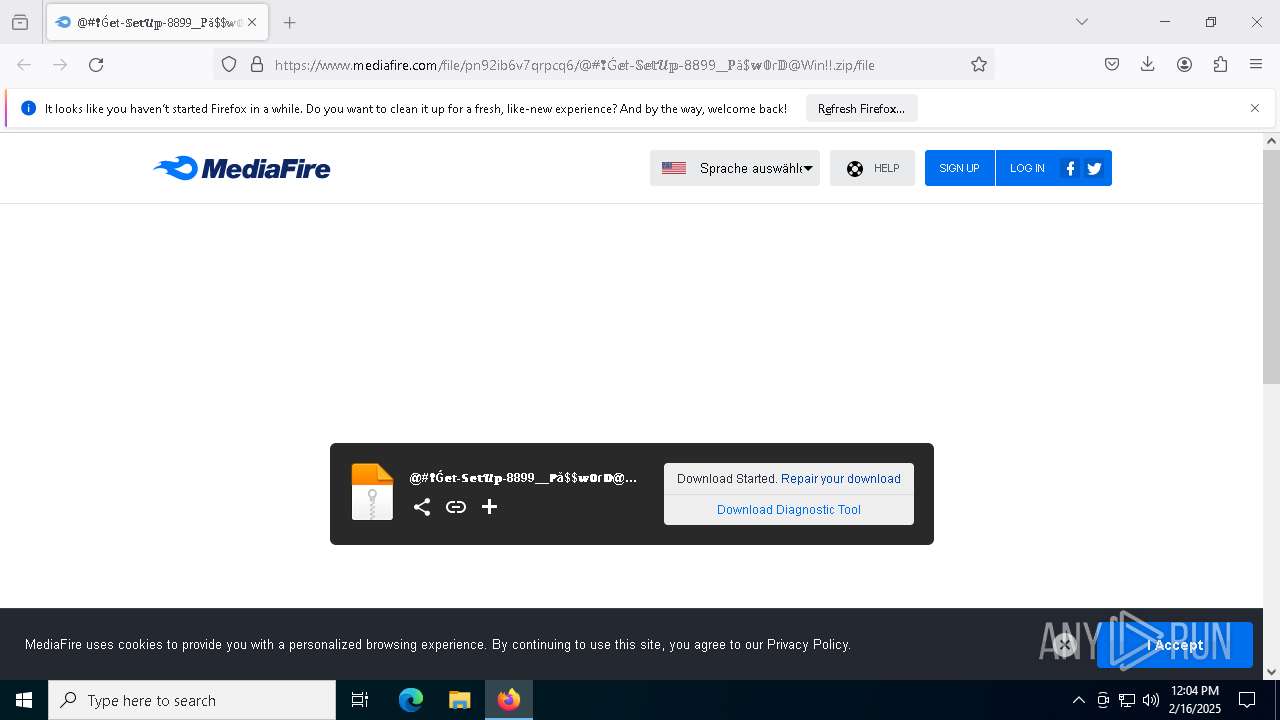
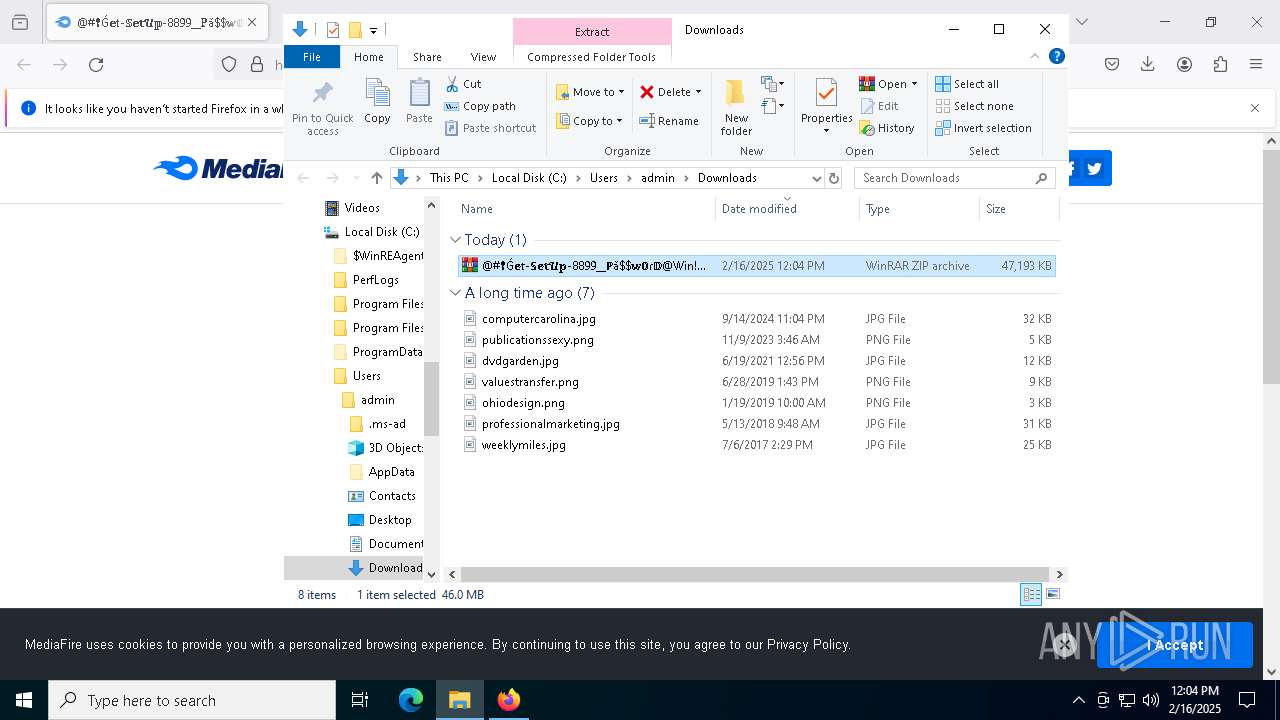
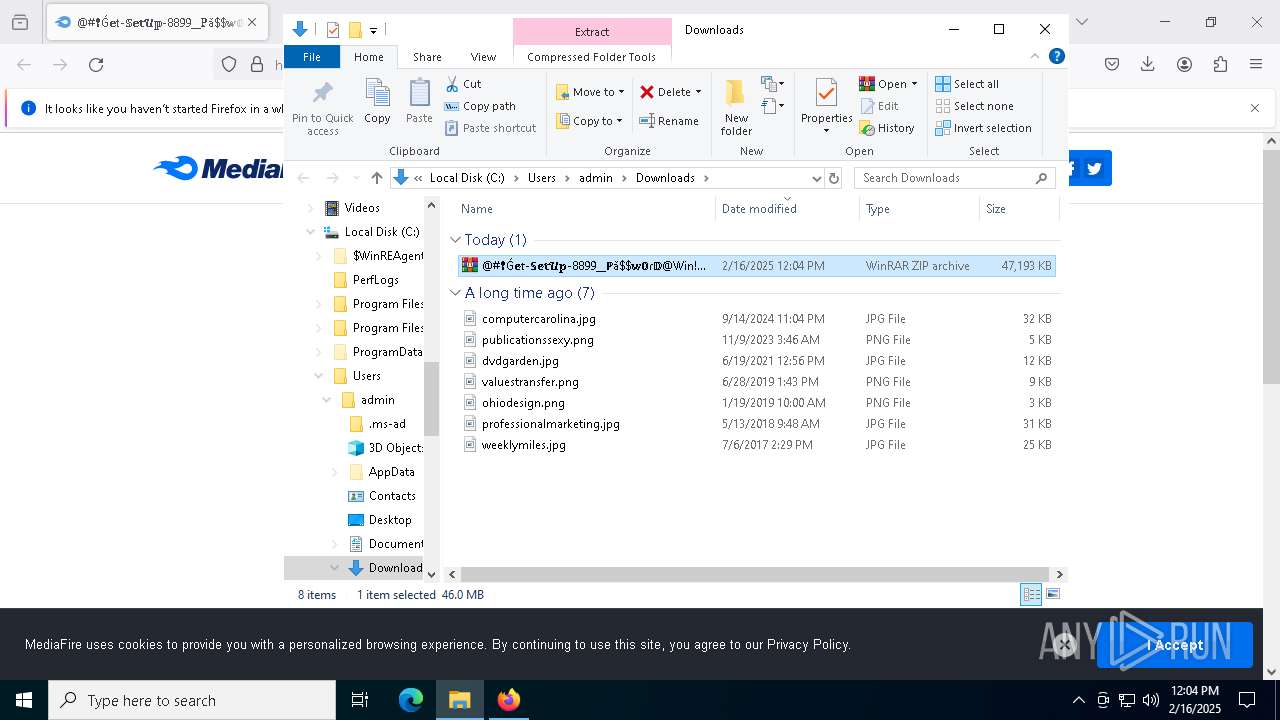
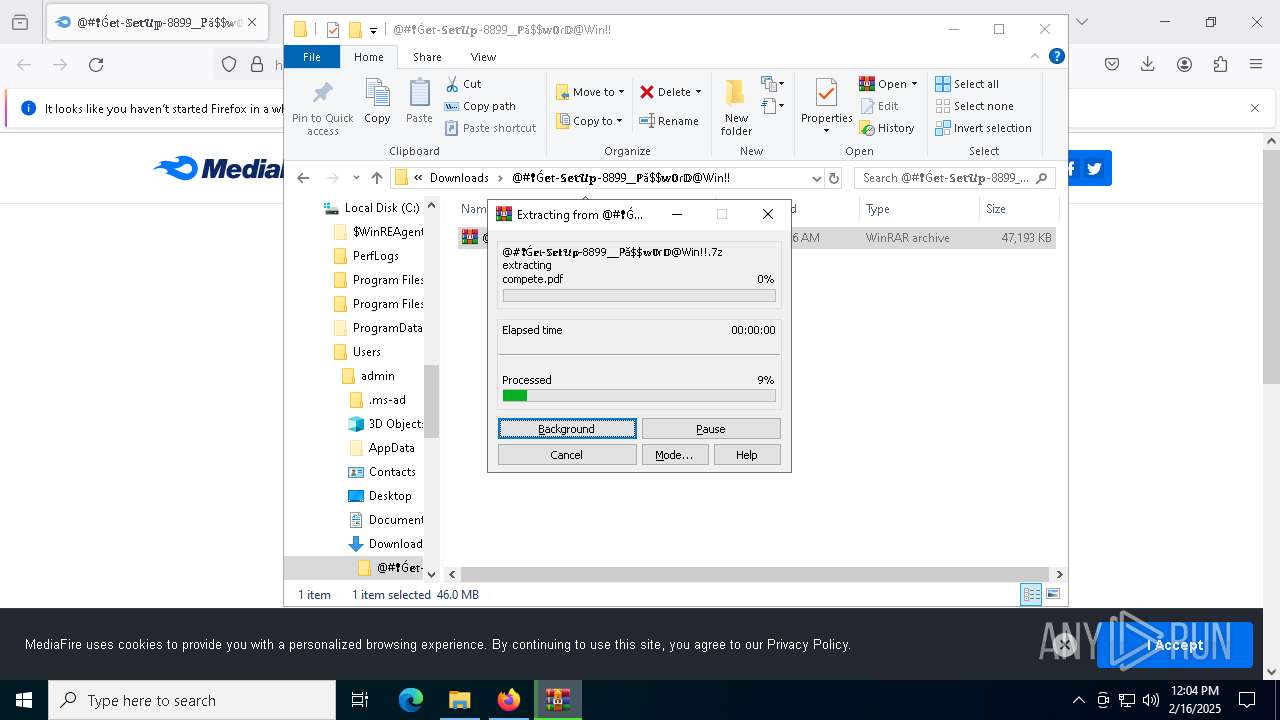
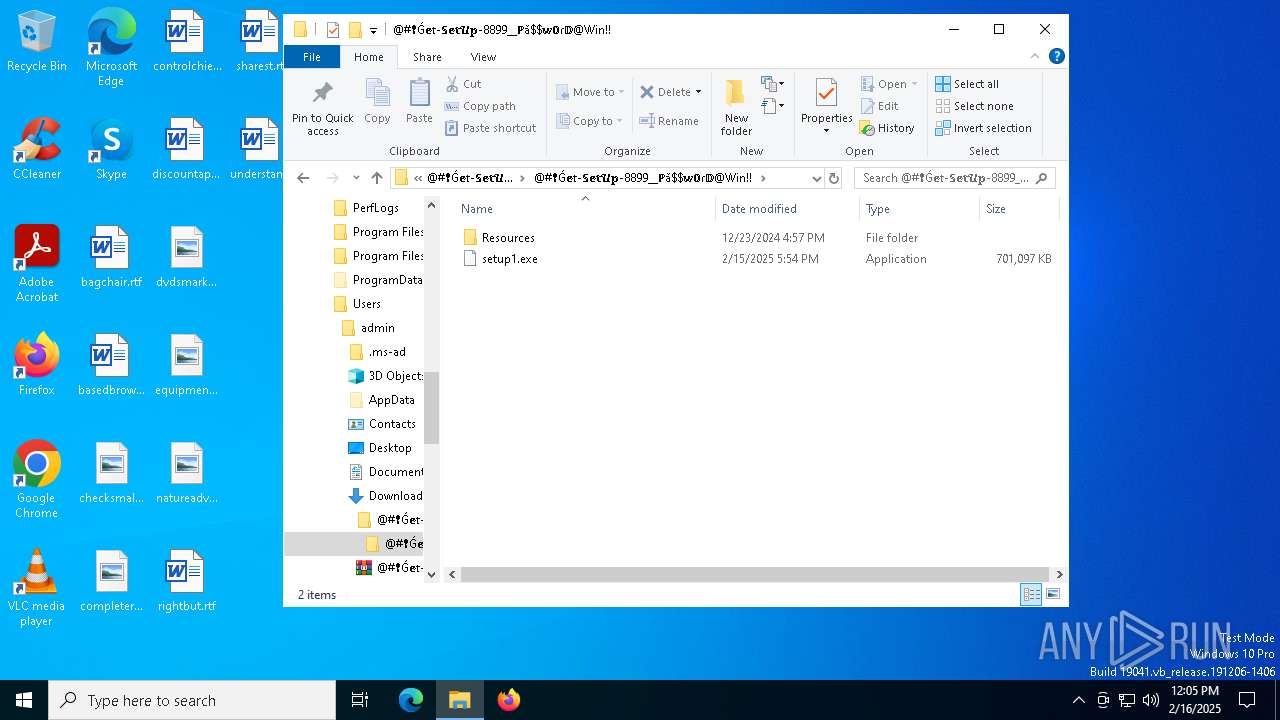
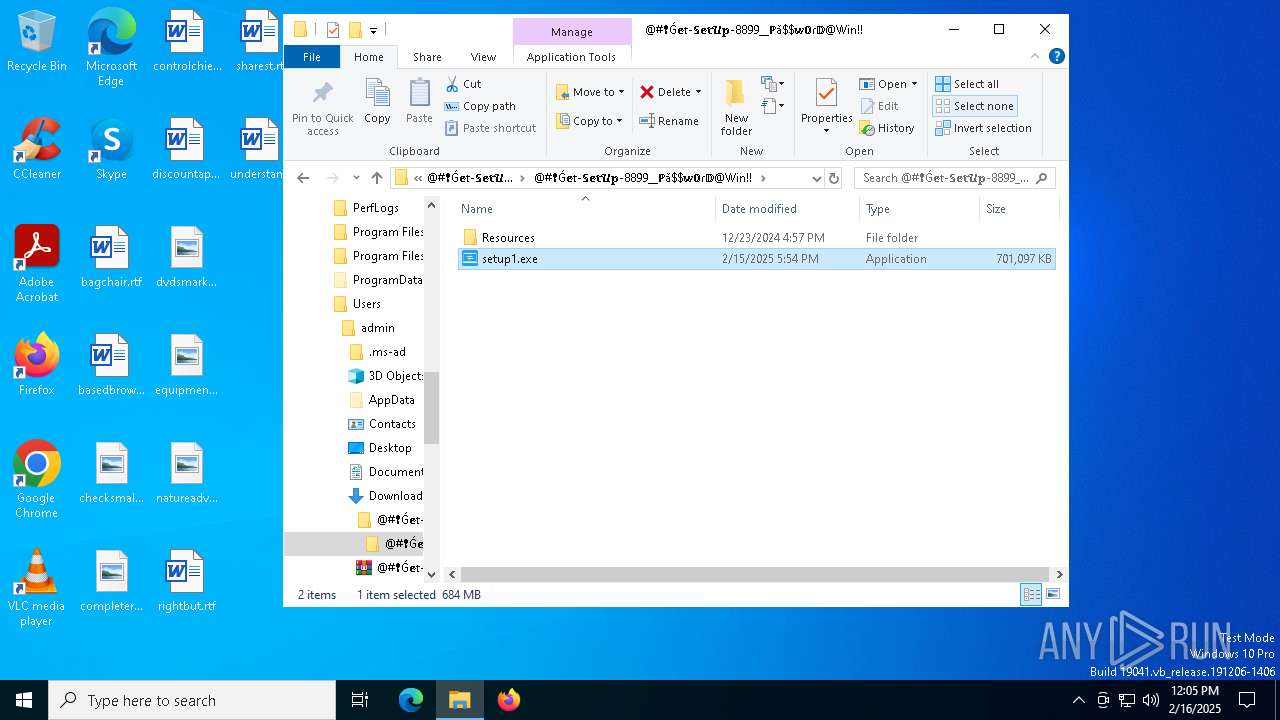
| URL: | https://www.mediafire.com/file/pn92ib6v7qrpcq6/@#%E2%9D%A2%C7%B4%F0%9D%95%96%F0%9D%94%B1-%F0%9D%95%8A%F0%9D%95%96%F0%9D%95%A5%F0%9D%93%A4%F0%9D%95%A1-8899__%E2%84%99%C7%8E$%F0%9D%95%A8%F0%9D%9F%98%C9%BE%F0%9D%94%BB@Win!!.zip/file |
| Full analysis: | https://app.any.run/tasks/9a6be9c1-46b5-44e1-9fb3-e946f2d91a11 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | February 16, 2025, 12:04:14 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6AA9FADDA5A4A6C2739B5FEED5EBA862 |
| SHA1: | ADA7A9CE63111A05965F8D94FF7841CC1F627975 |
| SHA256: | B883E2DE55744D4A0420626E49687AB2B022B3F5DAF242CAEBC37C4BC5808A9C |
| SSDEEP: | 6:2OLw3eG3JOP0D2rnbx0D2enbERAjb+YmM4D8cGMbmv:273eODUn2DTMWmMjcGhv |
MALICIOUS
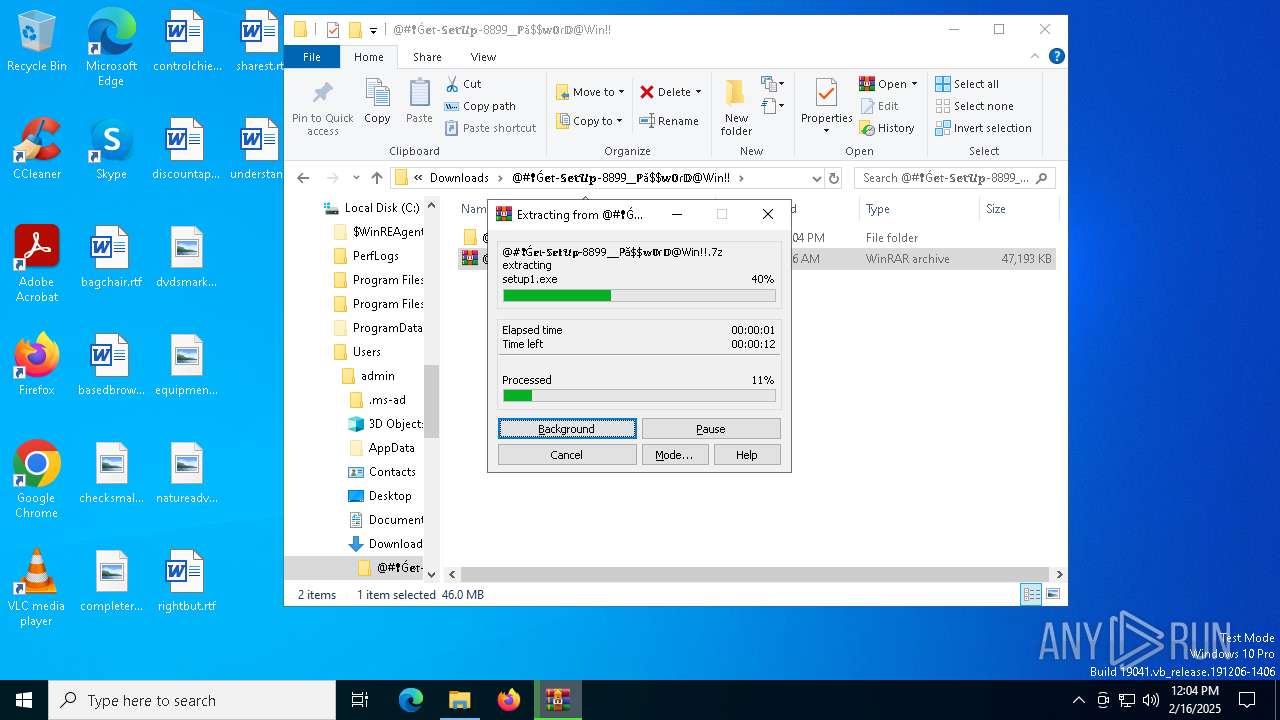
Executing a file with an untrusted certificate
- setup1.exe (PID: 5696)
Connects to the CnC server
- svchost.exe (PID: 2192)
Actions looks like stealing of personal data
- setup1.exe (PID: 5696)
LUMMA mutex has been found
- setup1.exe (PID: 5696)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2192)
- setup1.exe (PID: 5696)
Steals credentials from Web Browsers
- setup1.exe (PID: 5696)
Changes powershell execution policy (Bypass)
- setup1.exe (PID: 5696)
Bypass execution policy to execute commands
- powershell.exe (PID: 5244)
- powershell.exe (PID: 2736)
SUSPICIOUS
Possibly a phishing URL contains email has been detected
- firefox.exe (PID: 1344)
- firefox.exe (PID: 6032)
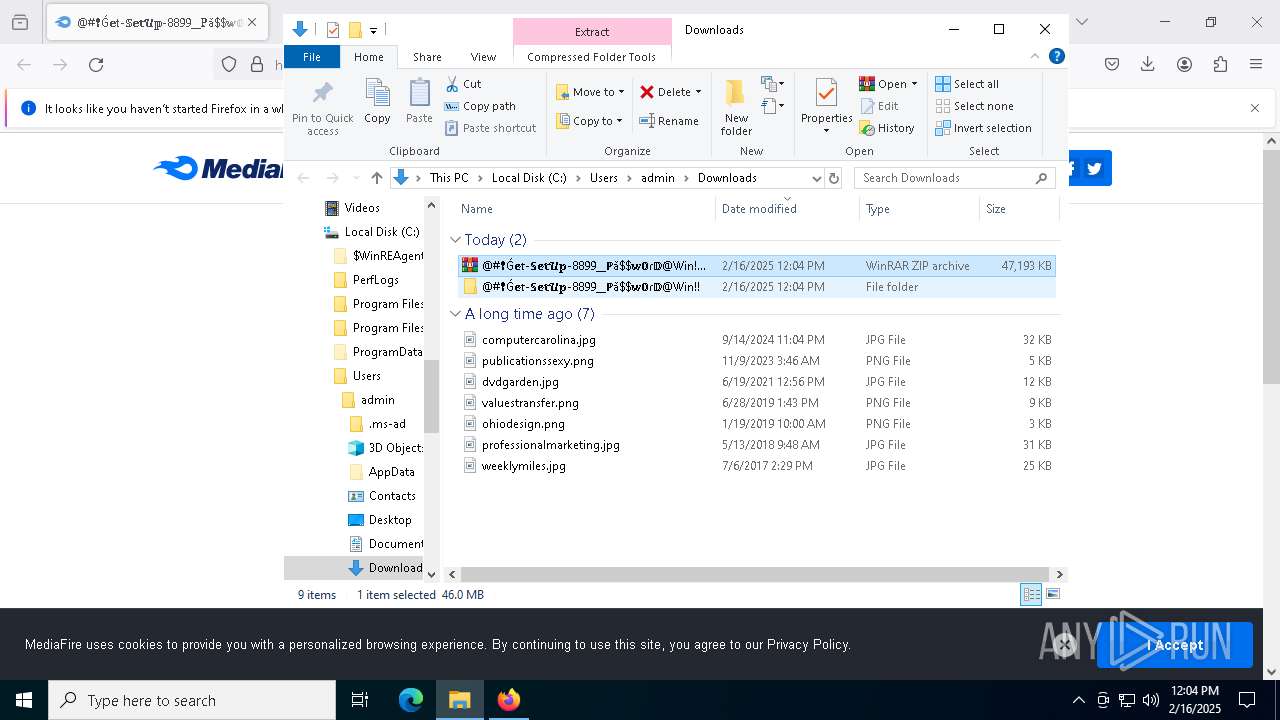
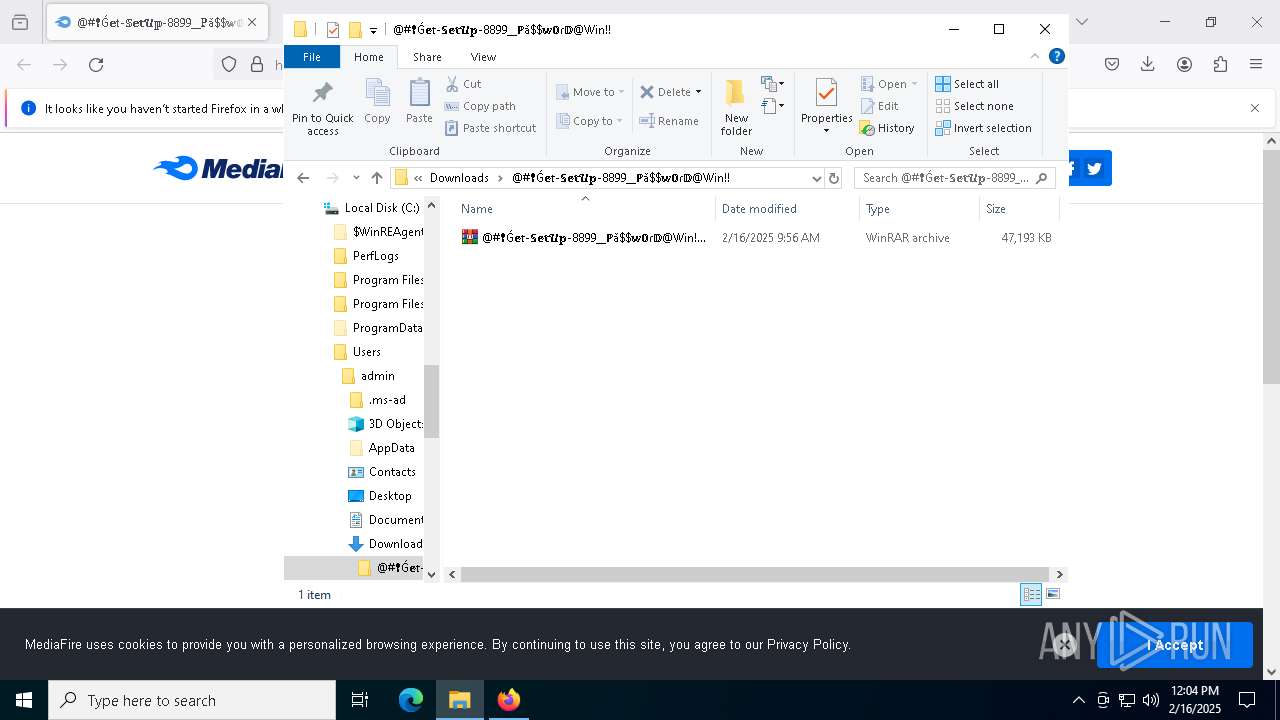
The process creates files with name similar to system file names
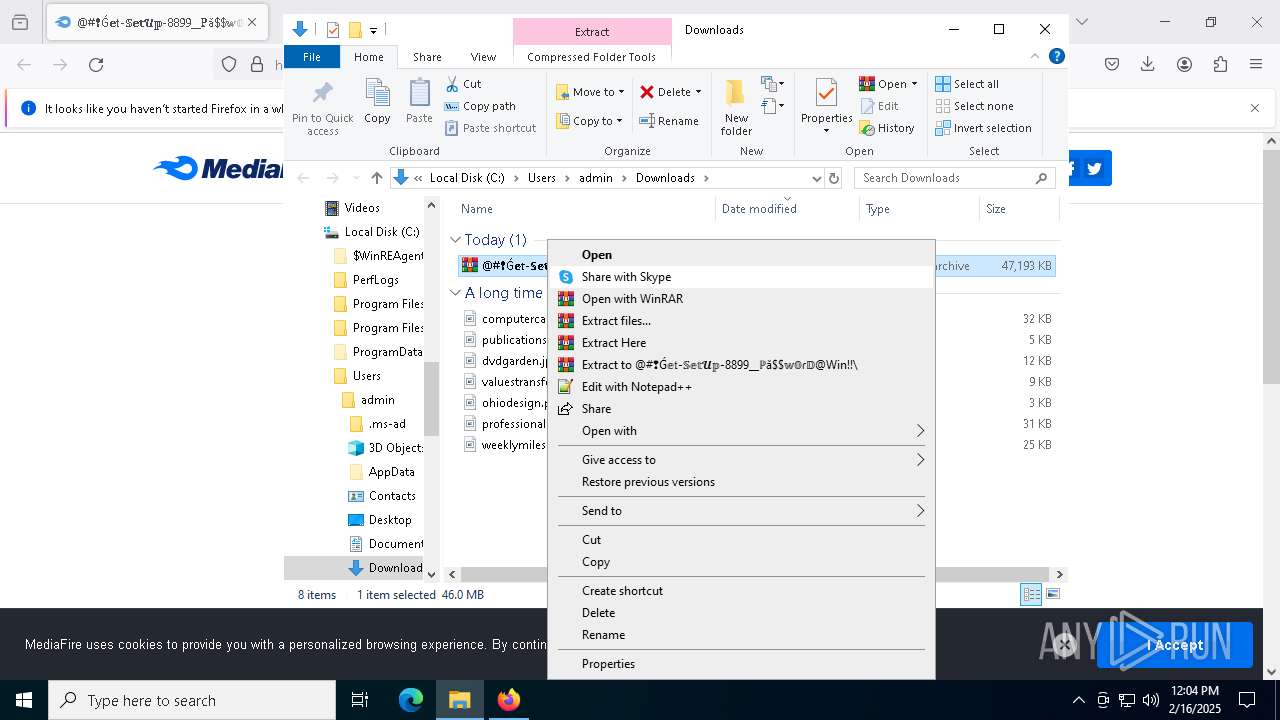
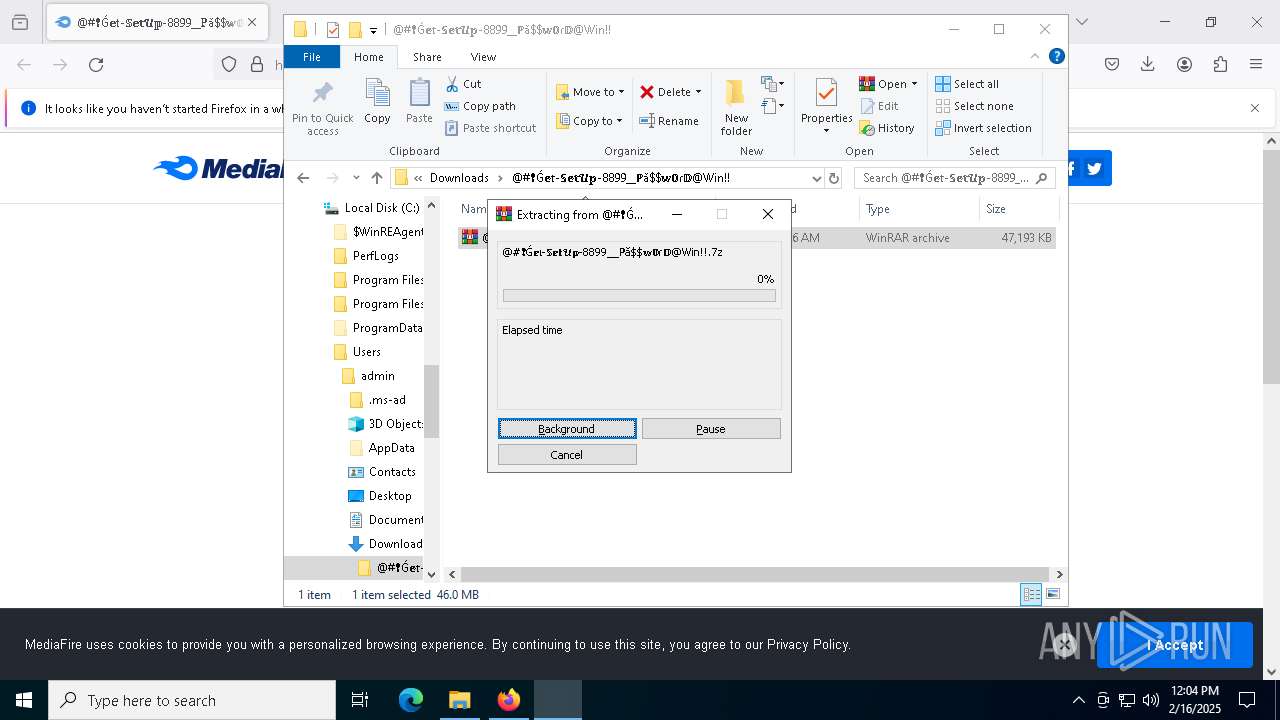
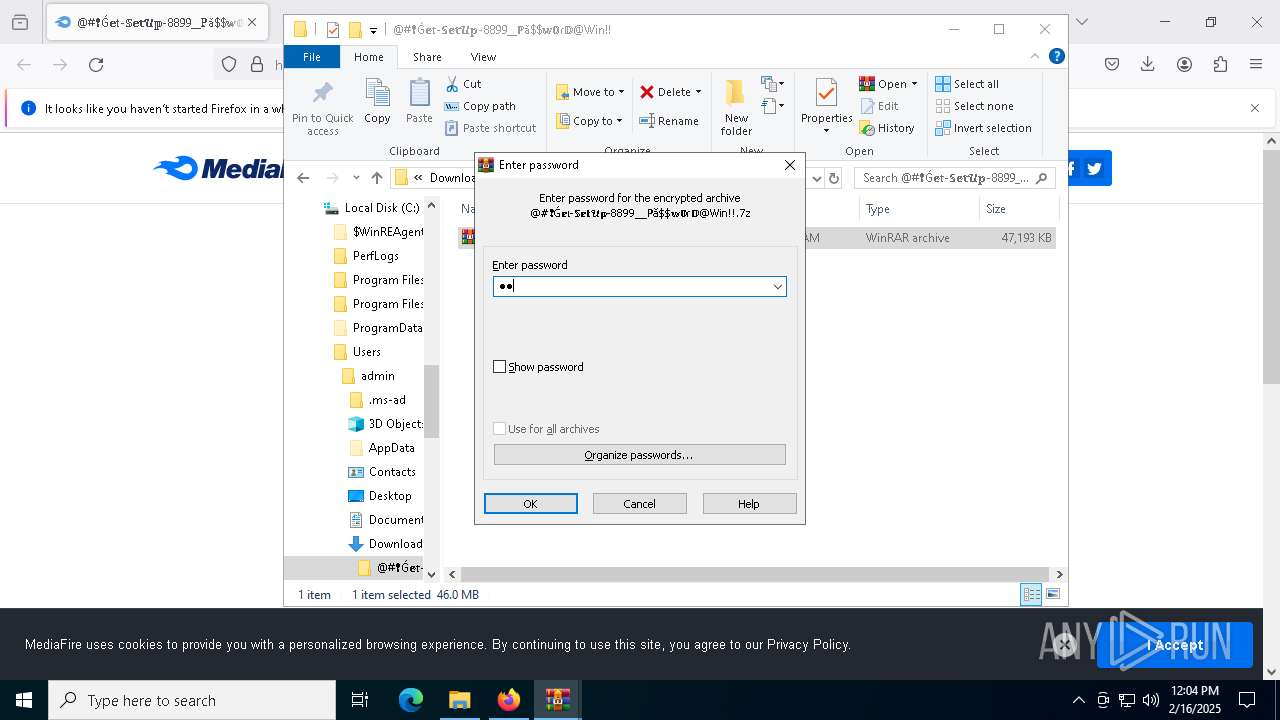
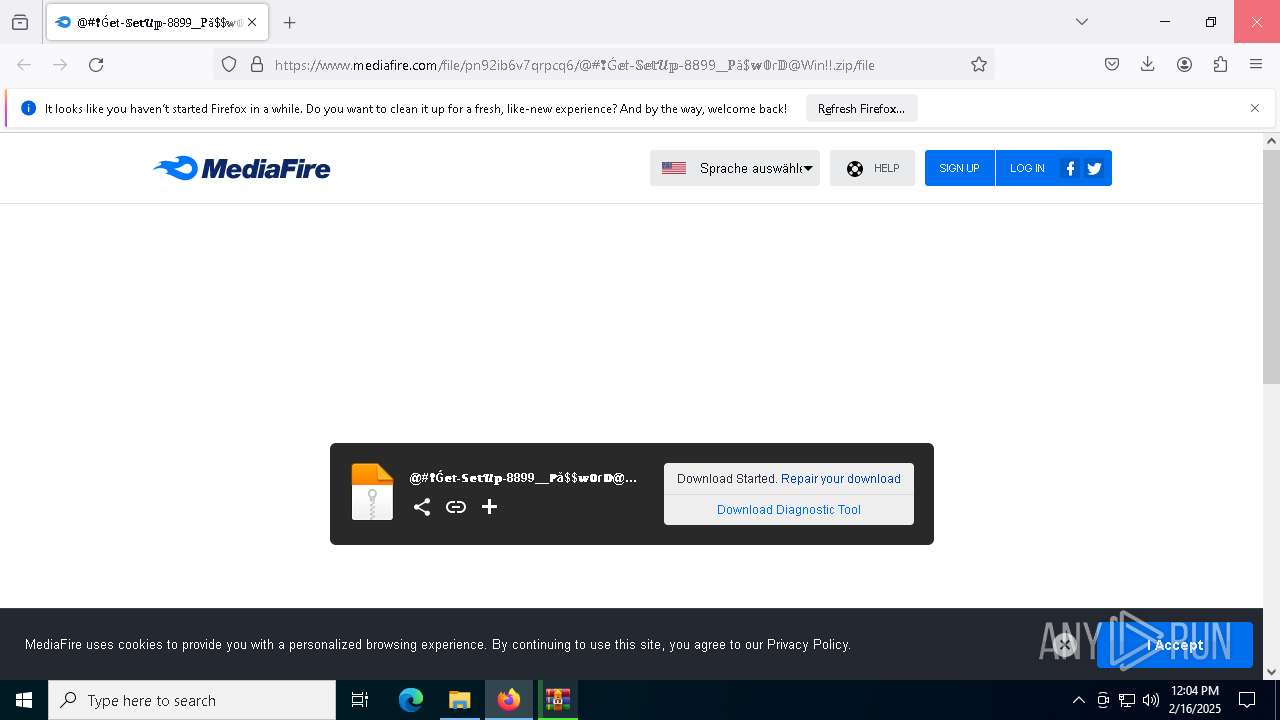
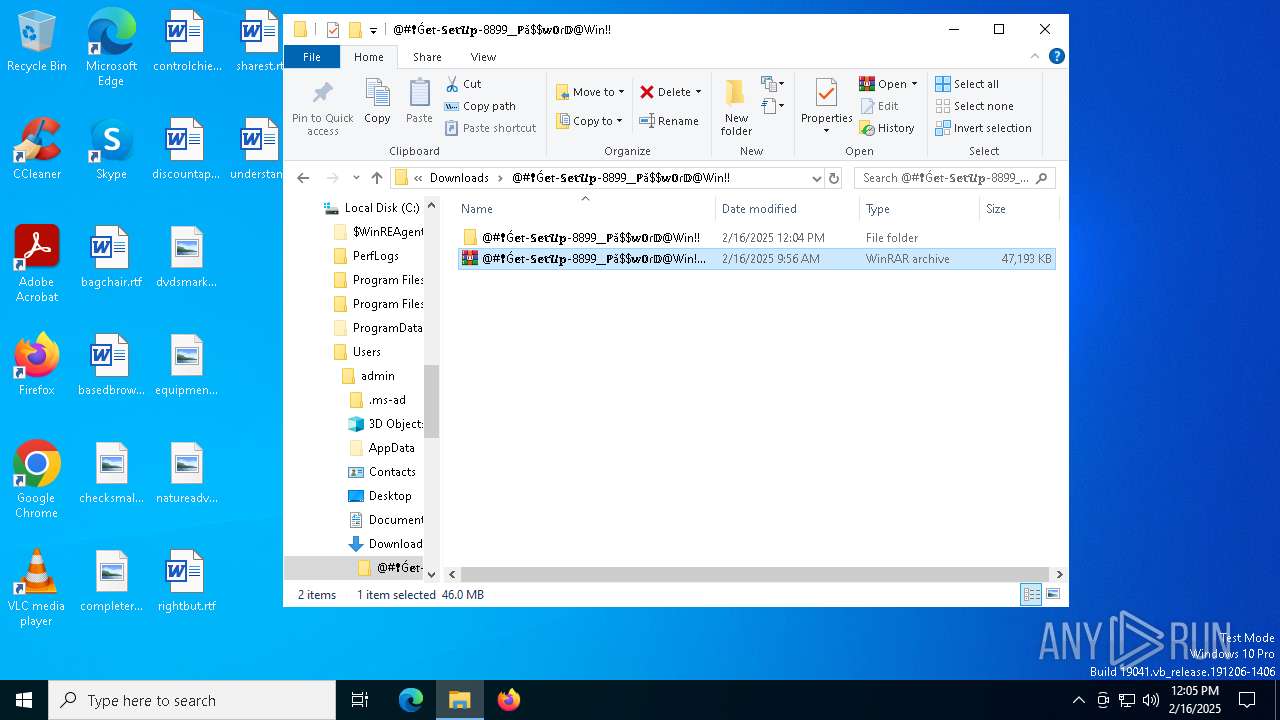
- WinRAR.exe (PID: 8160)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2192)
- setup1.exe (PID: 5696)
Process drops legitimate windows executable
- WinRAR.exe (PID: 8160)
Searches for installed software
- setup1.exe (PID: 5696)
The process executes Powershell scripts
- setup1.exe (PID: 5696)
Starts POWERSHELL.EXE for commands execution
- setup1.exe (PID: 5696)
INFO
Application launched itself
- firefox.exe (PID: 6032)
- firefox.exe (PID: 1344)
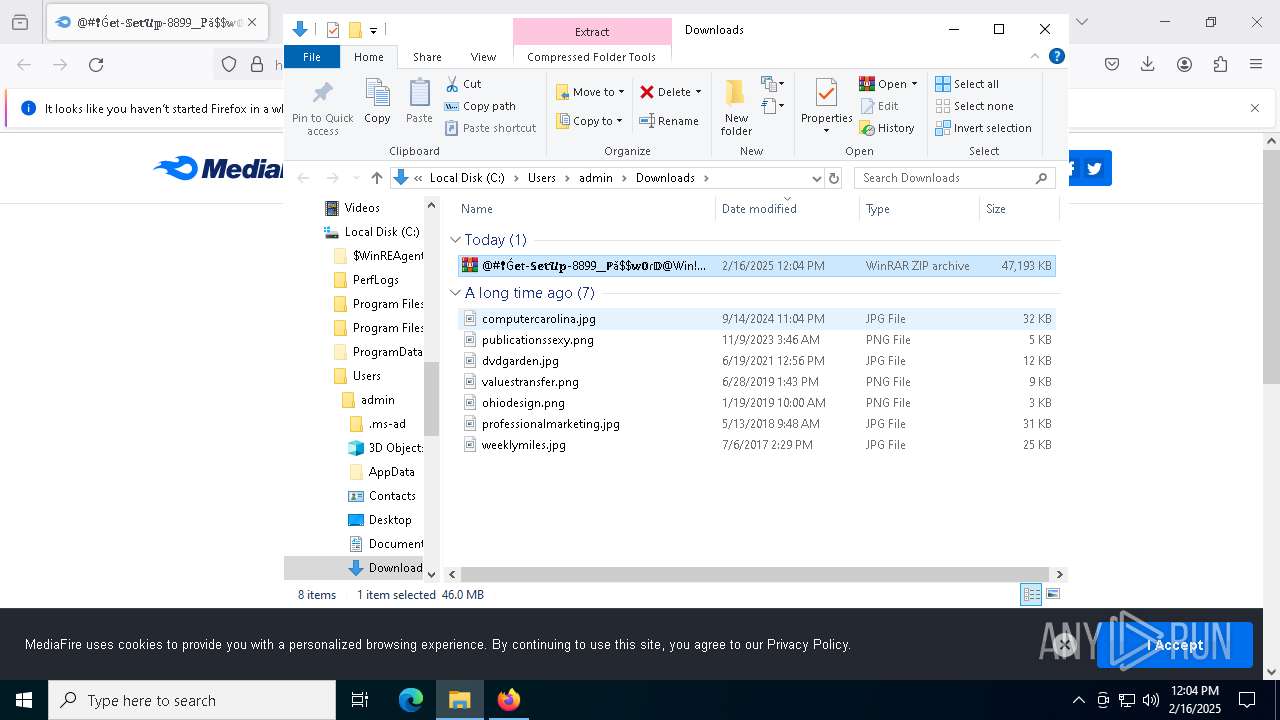
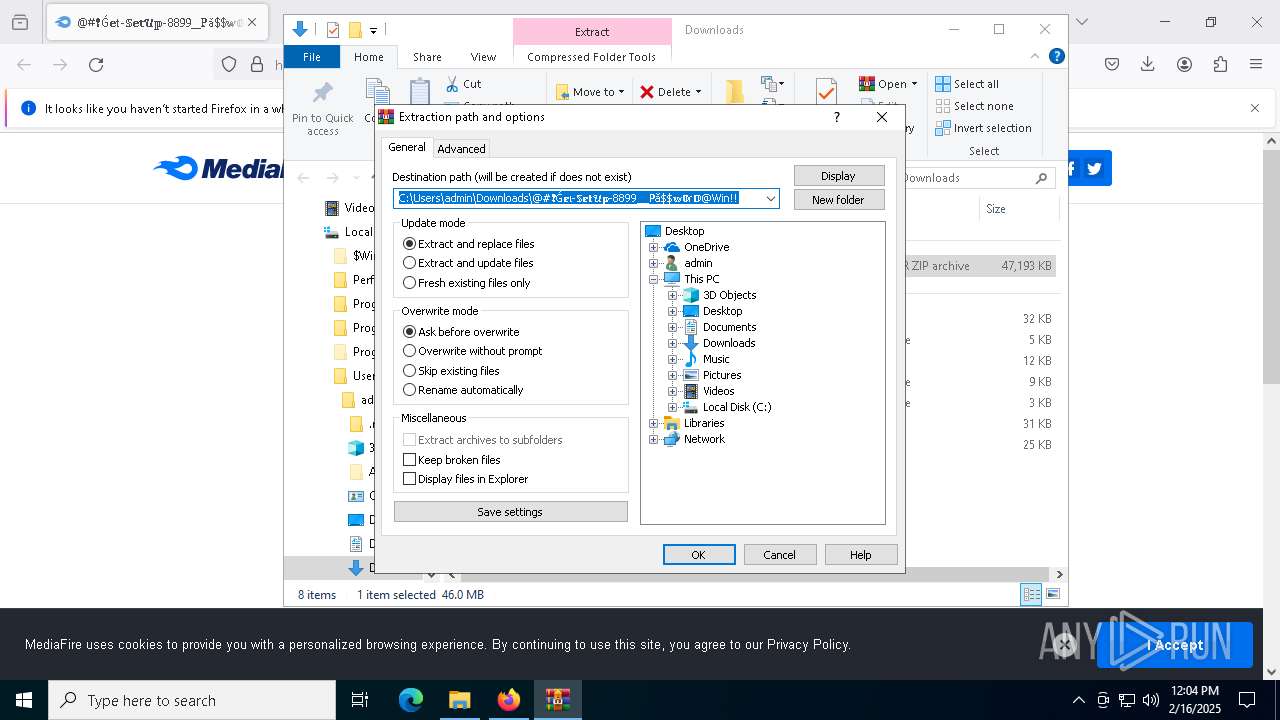
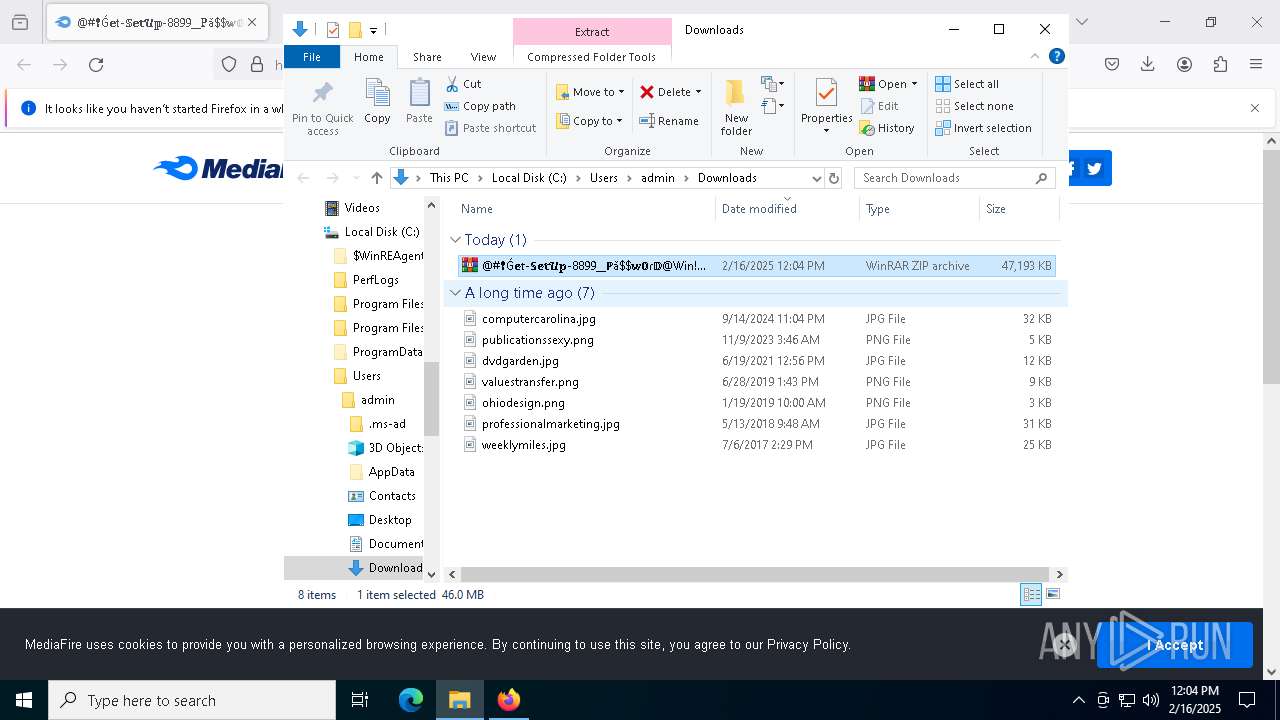
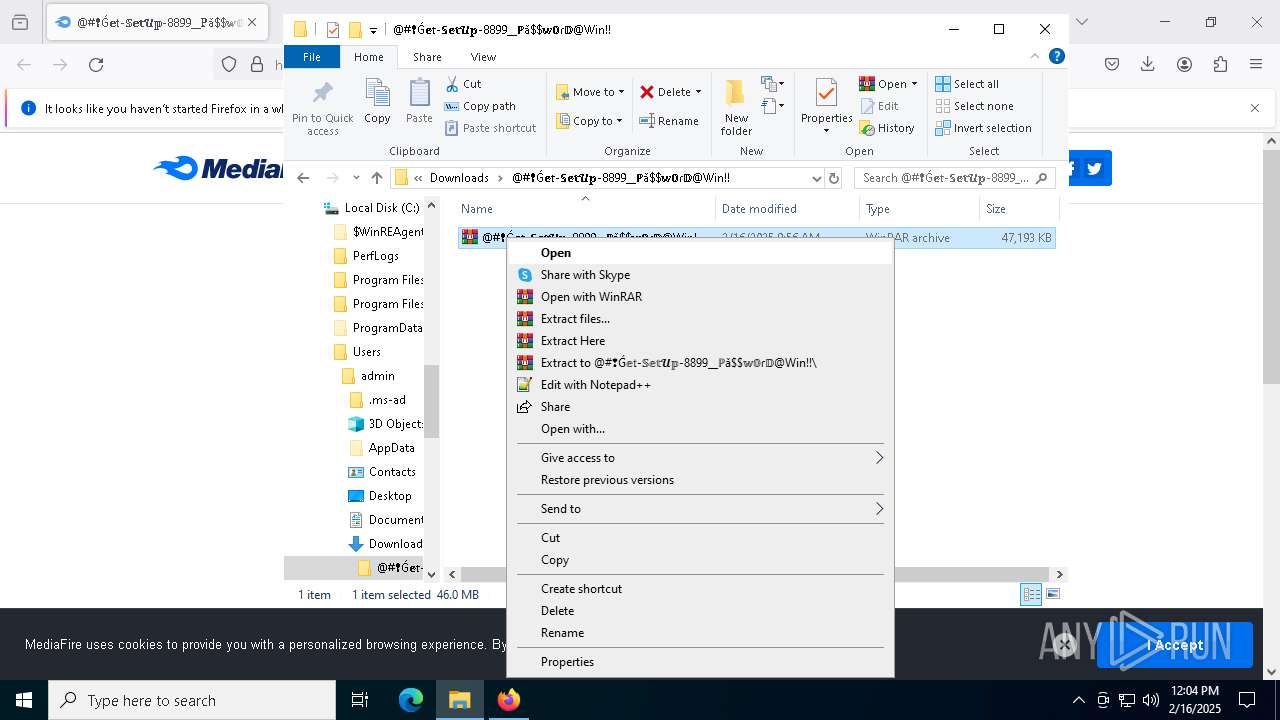
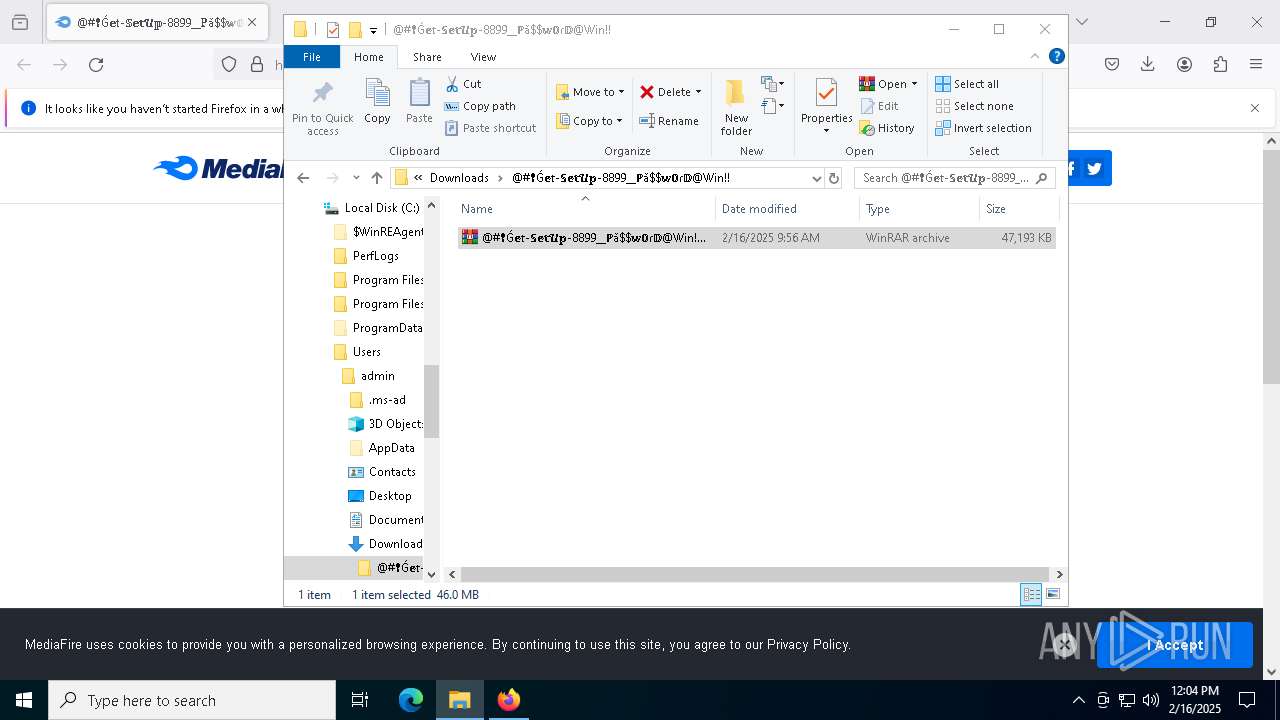
Manual execution by a user
- WinRAR.exe (PID: 8160)
- WinRAR.exe (PID: 7800)
- setup1.exe (PID: 5696)
The sample compiled with english language support
- WinRAR.exe (PID: 8160)
Checks supported languages
- setup1.exe (PID: 5696)
Reads the computer name
- setup1.exe (PID: 5696)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8160)
Reads the software policy settings
- setup1.exe (PID: 5696)
Create files in a temporary directory
- setup1.exe (PID: 5696)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2736)
- powershell.exe (PID: 5244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
145
Monitored processes
20
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1344 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://www.mediafire.com/file/pn92ib6v7qrpcq6/@#%E2%9D%A2%C7%B4%F0%9D%95%96%F0%9D%94%B1-%F0%9D%95%8A%F0%9D%95%96%F0%9D%95%A5%F0%9D%93%A4%F0%9D%95%A1-8899__%E2%84%99%C7%8E$%F0%9D%95%A8%F0%9D%9F%98%C9%BE%F0%9D%94%BB@Win!!.zip/file | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5380 -childID 6 -isForBrowser -prefsHandle 5300 -prefMapHandle 5304 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1308 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {89c7377d-7fae-4d29-9756-4d0e33ea5ced} 1344 "\\.\pipe\gecko-crash-server-pipe.1344" 1a4bced1a10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2424 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1916 -parentBuildID 20240213221259 -prefsHandle 1844 -prefMapHandle 1840 -prefsLen 31031 -prefMapSize 244583 -appDir "C:\Program Files\Mozilla Firefox\browser" - {ad285f42-1145-409b-a1d8-b6879d6848f0} 1344 "\\.\pipe\gecko-crash-server-pipe.1344" 1a4b3cbe610 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
| 2676 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2736 | powershell -exec bypass -f "C:\Users\admin\AppData\Local\Temp\RU03SJBIOJ1QRHG0IV1CL.ps1" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | setup1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3700 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3796 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2152 -parentBuildID 20240213221259 -prefsHandle 2144 -prefMapHandle 2140 -prefsLen 31031 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {fe1a44a1-6947-4bc5-95da-1578ff468a25} 1344 "\\.\pipe\gecko-crash-server-pipe.1344" 1a4a6d87d10 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 3876 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5148 -childID 4 -isForBrowser -prefsHandle 5136 -prefMapHandle 5132 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1308 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {91b96ed2-168e-497d-afda-215b8e1f89cb} 1344 "\\.\pipe\gecko-crash-server-pipe.1344" 1a4bced1310 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 5244 | powershell -exec bypass -f "C:\Users\admin\AppData\Local\Temp\ATUW8FAVOQ225E0LXEYPELZXSVAK.ps1" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | setup1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
24 671
Read events
24 629
Write events
17
Delete events
25
Modification events
| (PID) Process: | (1344) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (7800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\ext | |||
| (PID) Process: | (7800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\@#❢Ǵ𝕖𝔱-𝕊𝕖𝕥𝓤𝕡-8899__ℙǎ$𝕨𝟘ɾ𝔻@Win!! | |||
| (PID) Process: | (7800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (7800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
| (PID) Process: | (7800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 13 |
Value: | |||
| (PID) Process: | (7800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 12 |
Value: | |||
Executable files
12
Suspicious files
206
Text files
94
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1344 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 1344 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 1344 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 1344 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1344 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 1344 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 1344 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 1344 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1344 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1344 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
138
DNS requests
164
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1344 | firefox.exe | POST | — | 142.250.185.195:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.167:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5892 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5892 | svchost.exe | GET | 200 | 23.48.23.167:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1344 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
1344 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
1344 | firefox.exe | POST | 200 | 184.24.77.44:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
1344 | firefox.exe | POST | 200 | 184.24.77.45:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
1344 | firefox.exe | POST | 200 | 142.250.185.195:80 | http://o.pki.goog/s/wr3/jLM | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
712 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.167:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5892 | svchost.exe | 23.48.23.167:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5892 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.179:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
www.mediafire.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
2192 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
2192 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
2192 | svchost.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
2192 | svchost.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
2192 | svchost.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (shiningrstars .help) |
5696 | setup1.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (shiningrstars .help in TLS SNI) |
5696 | setup1.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (shiningrstars .help in TLS SNI) |
5696 | setup1.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (shiningrstars .help in TLS SNI) |