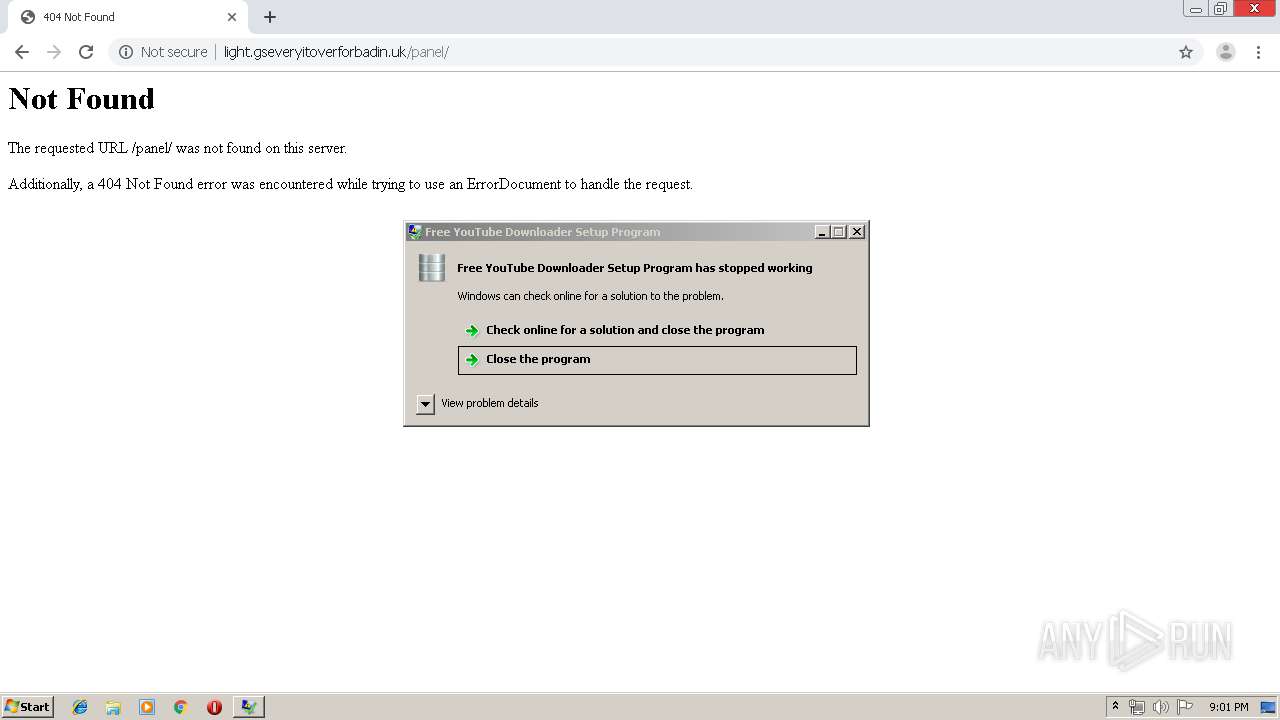
| URL: | http://light.gseveryitoverforbadin.uk |
| Full analysis: | https://app.any.run/tasks/1c12a5da-c9ff-4d98-8e91-ae902365d77d |
| Verdict: | Malicious activity |
| Threats: | WarZone RAT is a remote access trojan, which is written in C++ and offered as a malware-as-a-service. It packs a wide range of capabilities, from stealing victims’ files and passwords to capturing desktop activities. WarZone RAT is primarily distributed via phishing emails and receives regular updates from its C2. |
| Analysis date: | July 11, 2019, 20:00:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 27927A8739AA4573096BFBE06E3E86E8 |
| SHA1: | 7D5824BFDACFD95023A877B0CB065EC6CDA40B47 |
| SHA256: | B7CB1FBC1ACCDD0CC83A3D38540EF9A6A0A7C80D79D5F065C7288EC6295EF3CF |
| SSDEEP: | 3:N1KSM0dNy/x/bn:CS7QB |
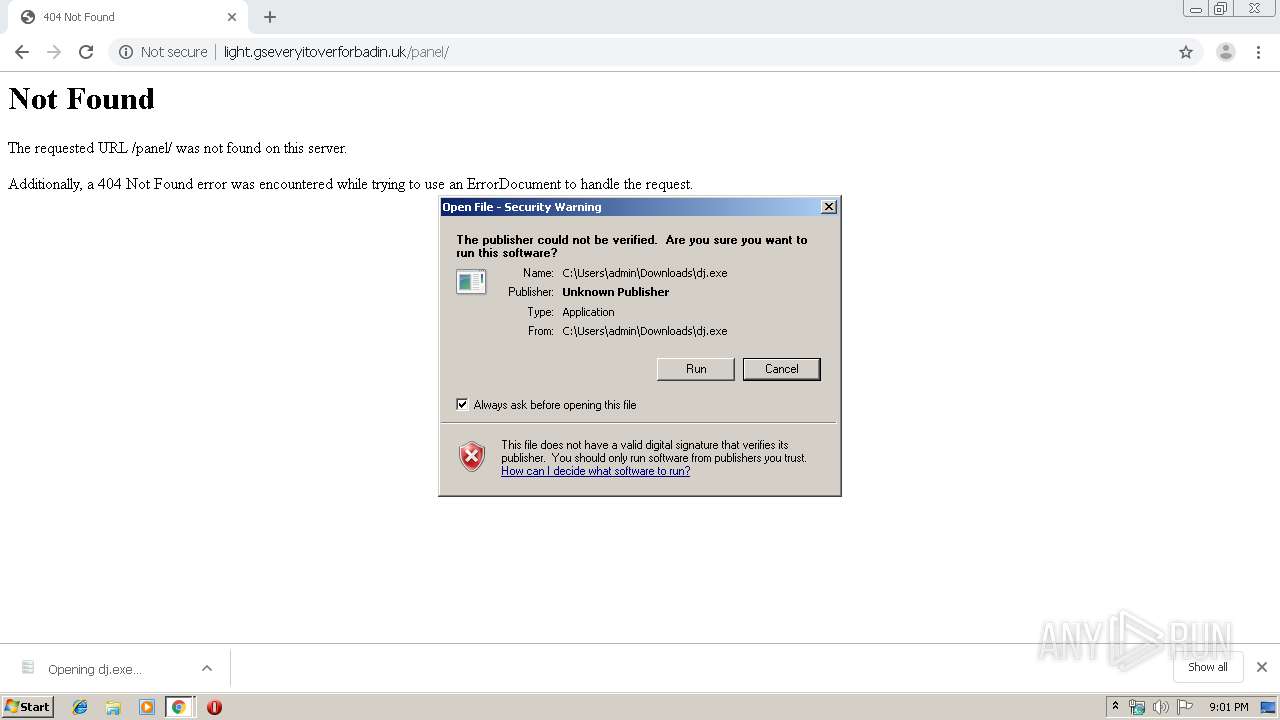
MALICIOUS
Application was dropped or rewritten from another process
- dj.exe (PID: 452)
- dj.exe (PID: 4068)
- images.exe (PID: 2932)
- images.exe (PID: 2496)
- dj.exe (PID: 2948)
- images.exe (PID: 3552)
- images.exe (PID: 2176)
- dj.exe (PID: 1952)
Changes the autorun value in the registry
- dj.exe (PID: 452)
- dj.exe (PID: 4068)
- images.exe (PID: 2932)
Connects to CnC server
- images.exe (PID: 2496)
- dj.exe (PID: 2948)
- images.exe (PID: 3552)
- images.exe (PID: 2176)
- dj.exe (PID: 1952)
AVEMARIA was detected
- images.exe (PID: 3552)
- images.exe (PID: 2496)
- dj.exe (PID: 2948)
- images.exe (PID: 2176)
- dj.exe (PID: 1952)
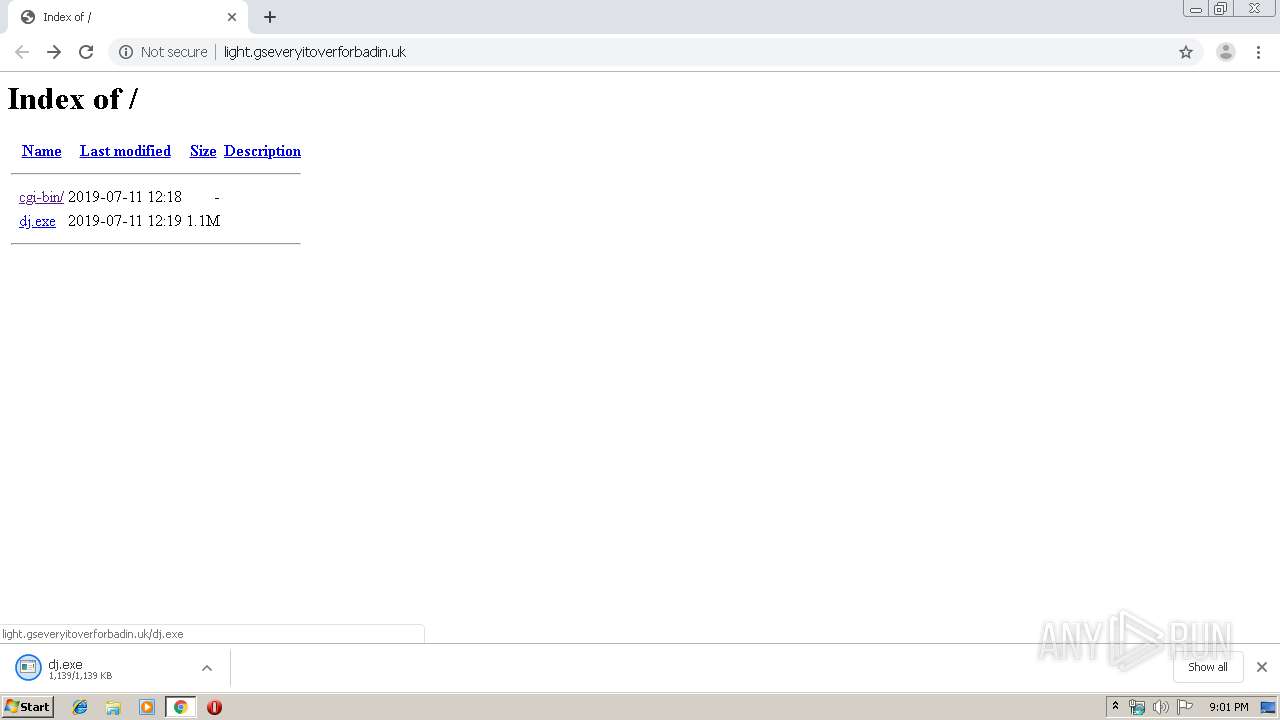
Downloads executable files from the Internet
- chrome.exe (PID: 2548)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2548)
- chrome.exe (PID: 3108)
- dj.exe (PID: 452)
- dj.exe (PID: 4068)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3108)
Suspicious files were dropped or overwritten
- dj.exe (PID: 452)
Application launched itself
- dj.exe (PID: 452)
- images.exe (PID: 2932)
Creates files in the user directory
- dj.exe (PID: 4068)
Cleans NTFS data-stream (Zone Identifier)
- dj.exe (PID: 4068)
Starts itself from another location
- dj.exe (PID: 4068)
Reads the machine GUID from the registry
- dj.exe (PID: 2948)
- images.exe (PID: 2496)
- images.exe (PID: 3552)
- images.exe (PID: 2176)
- dj.exe (PID: 1952)
INFO
Application launched itself
- chrome.exe (PID: 3108)
Reads Internet Cache Settings
- chrome.exe (PID: 3108)
Creates files in the user directory
- chrome.exe (PID: 3108)
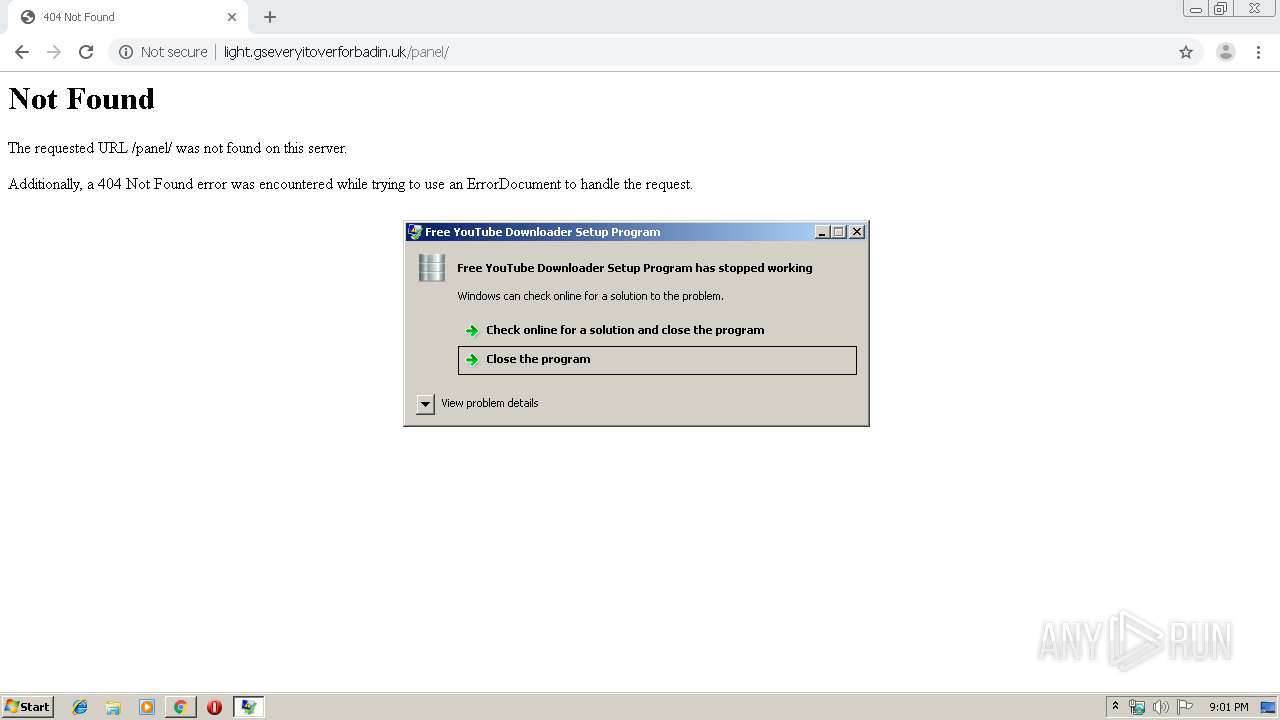
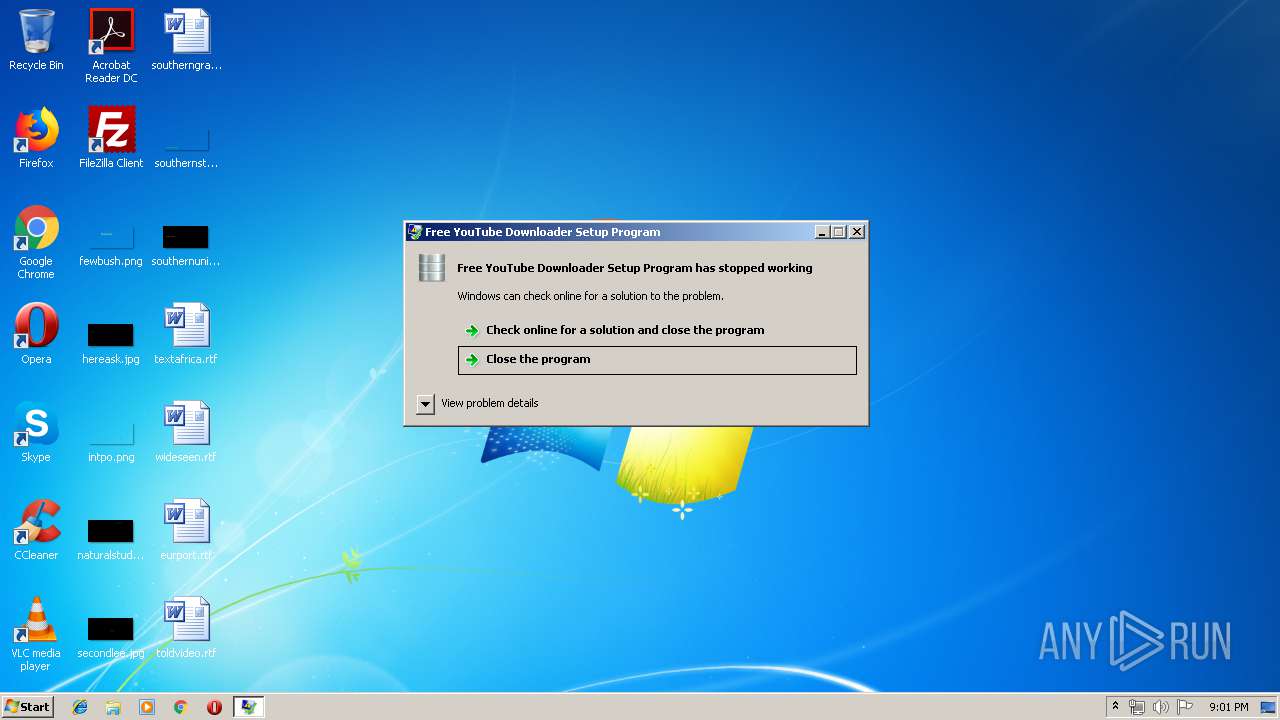
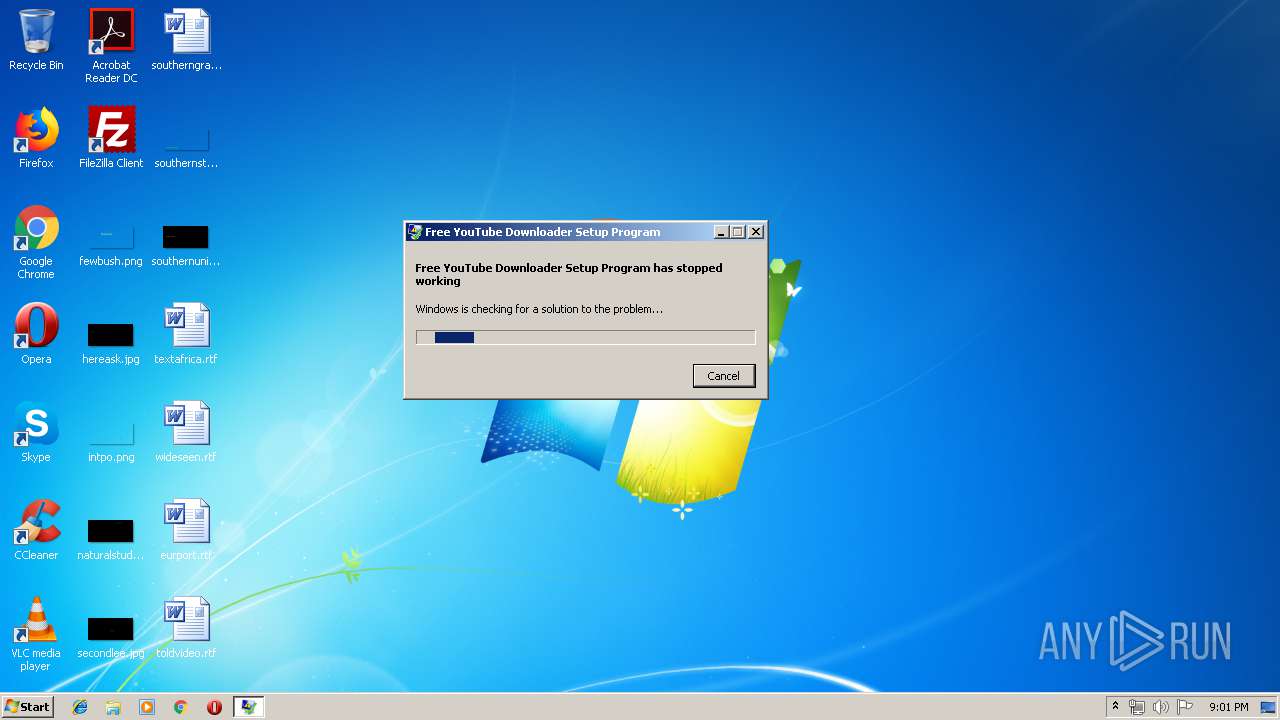
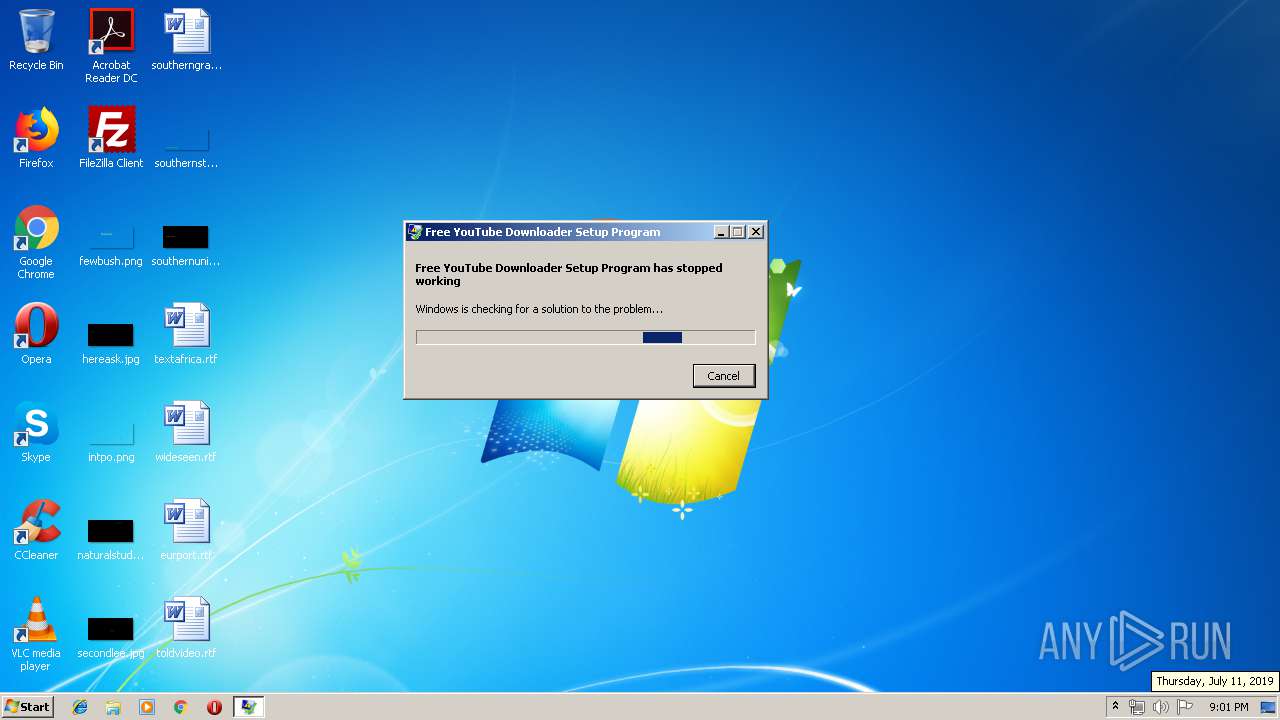
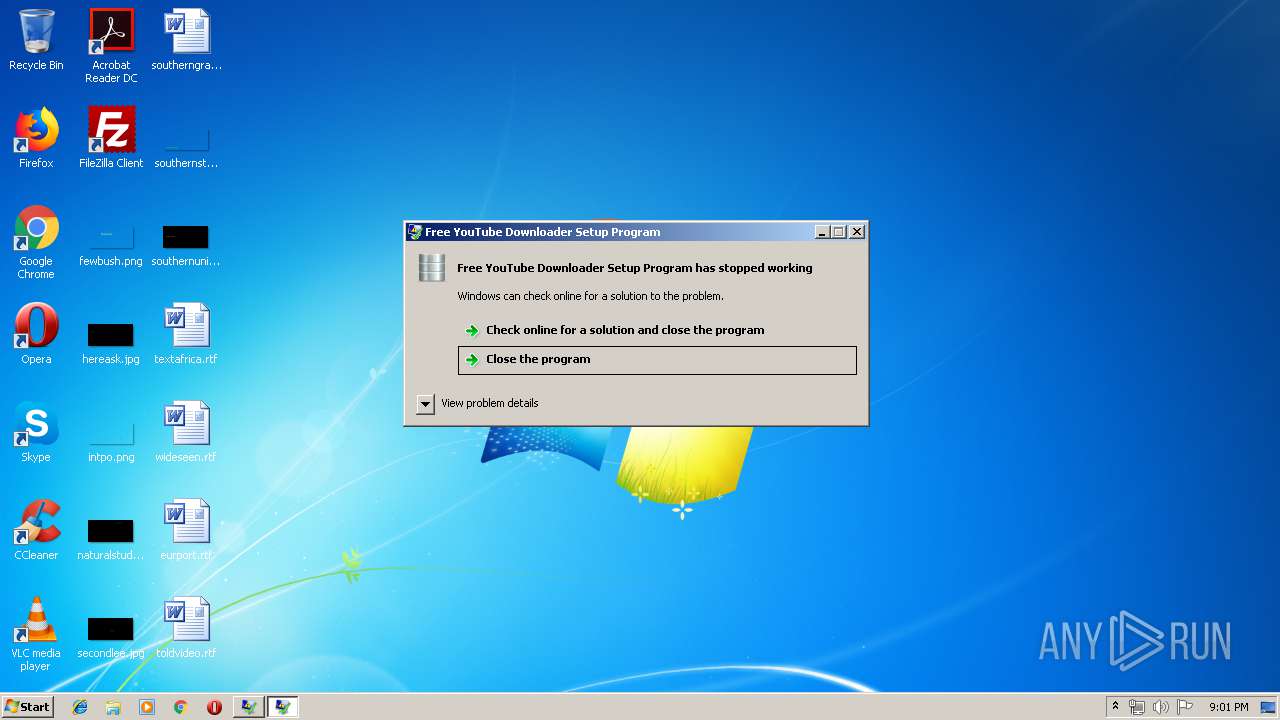
Application was crashed
- images.exe (PID: 2496)
- dj.exe (PID: 2948)
- images.exe (PID: 3552)
- images.exe (PID: 2176)
- dj.exe (PID: 1952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
70
Monitored processes
28
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 452 | "C:\Users\admin\Downloads\dj.exe" | C:\Users\admin\Downloads\dj.exe | chrome.exe | ||||||||||||
User: admin Company: How, Inc Integrity Level: MEDIUM Description: Free YouTube Downloader Setup Program Exit code: 0 Version: 201.564.879.536 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,8692131613813955740,11896911989967356214,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2305295732283950215 --mojo-platform-channel-handle=3760 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1952 | "C:\Users\admin\Downloads\dj.exe" | C:\Users\admin\Downloads\dj.exe | dj.exe | ||||||||||||
User: admin Company: How, Inc Integrity Level: MEDIUM Description: Free YouTube Downloader Setup Program Exit code: 0 Version: 201.564.879.536 Modules
| |||||||||||||||
| 2176 | "C:\Users\admin\AppData\Roaming\images.exe" | C:\Users\admin\AppData\Roaming\images.exe | images.exe | ||||||||||||
User: admin Company: How, Inc Integrity Level: MEDIUM Description: Free YouTube Downloader Setup Program Exit code: 0 Version: 201.564.879.536 Modules
| |||||||||||||||
| 2324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,8692131613813955740,11896911989967356214,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=14448356049234591077 --mojo-platform-channel-handle=1028 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,8692131613813955740,11896911989967356214,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17513574322880910625 --mojo-platform-channel-handle=3660 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2496 | "C:\Users\admin\AppData\Roaming\images.exe" | C:\Users\admin\AppData\Roaming\images.exe | images.exe | ||||||||||||
User: admin Company: How, Inc Integrity Level: MEDIUM Description: Free YouTube Downloader Setup Program Exit code: 3221225477 Version: 201.564.879.536 Modules
| |||||||||||||||
| 2508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,8692131613813955740,11896911989967356214,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=13767893519693968898 --mojo-platform-channel-handle=3224 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,8692131613813955740,11896911989967356214,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=10982735286747324601 --mojo-platform-channel-handle=1532 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,8692131613813955740,11896911989967356214,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17243911883227024123 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 098
Read events
984
Write events
109
Delete events
5
Modification events
| (PID) Process: | (3108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3108-13207348850223750 |
Value: 259 | |||
| (PID) Process: | (3108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3108) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
6
Suspicious files
28
Text files
195
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f21a2df8-2da7-4b55-9ace-57527e97ab07.tmp | — | |
MD5:— | SHA256:— | |||
| 3108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF100c94.TMP | text | |
MD5:— | SHA256:— | |||
| 3108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF100c27.TMP | text | |
MD5:— | SHA256:— | |||
| 3108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF100c08.TMP | text | |
MD5:— | SHA256:— | |||
| 3108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF100bd9.TMP | text | |
MD5:— | SHA256:— | |||
| 3108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
25
DNS requests
14
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3248 | WerFault.exe | GET | — | 51.143.111.81:80 | http://watson.microsoft.com/StageOne/Generic/BEX/dj_exe/1_0_0_0/5d15dfda/StackHash_0a9e/0_0_0_0/00000000/00000000/c0000005/00000008.htm?LCID=1033&OS=6.1.7601.2.00010100.1.0.48.17514&SM=DELL&SPN=DELL&BV=DELL&MID=3ADE2C42-4AB9-49B7-B142-BE9AEEA69063 | US | — | — | whitelisted |
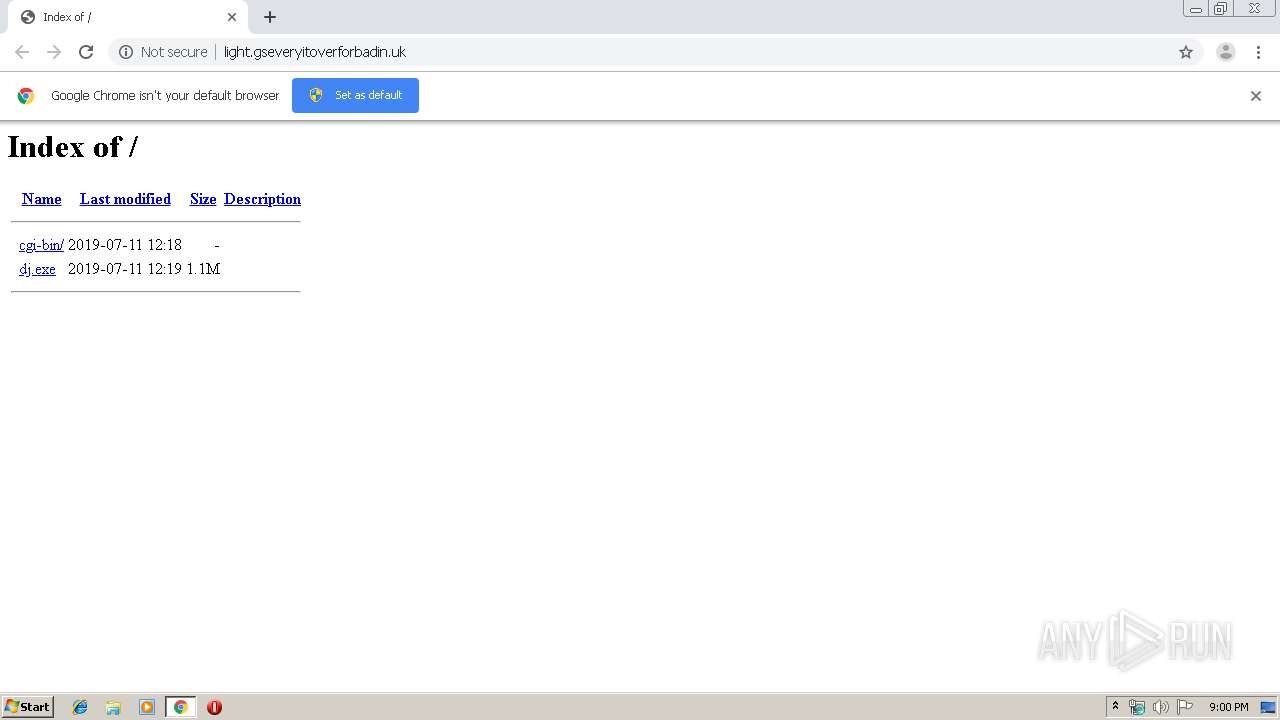
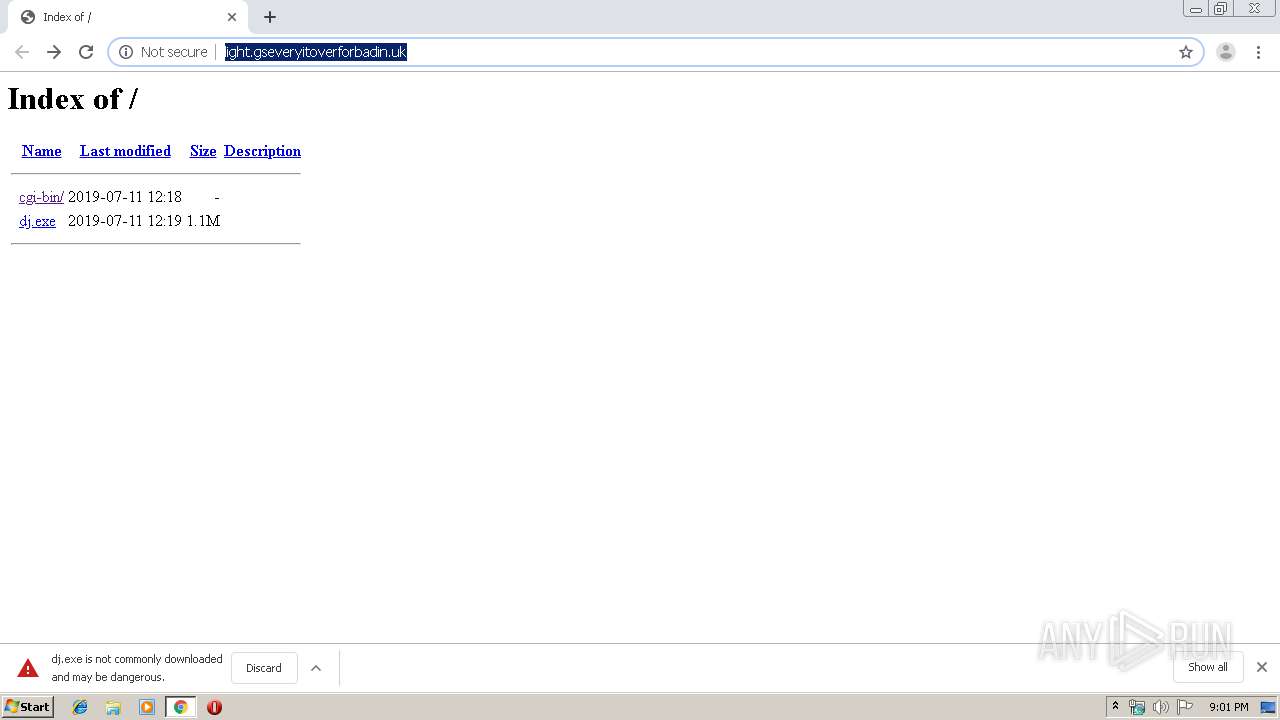
2548 | chrome.exe | GET | 200 | 51.77.151.60:80 | http://light.gseveryitoverforbadin.uk/ | GB | html | 797 b | suspicious |
2548 | chrome.exe | GET | 200 | 51.77.151.60:80 | http://light.gseveryitoverforbadin.uk/dj.exe | GB | executable | 1.11 Mb | suspicious |
2548 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
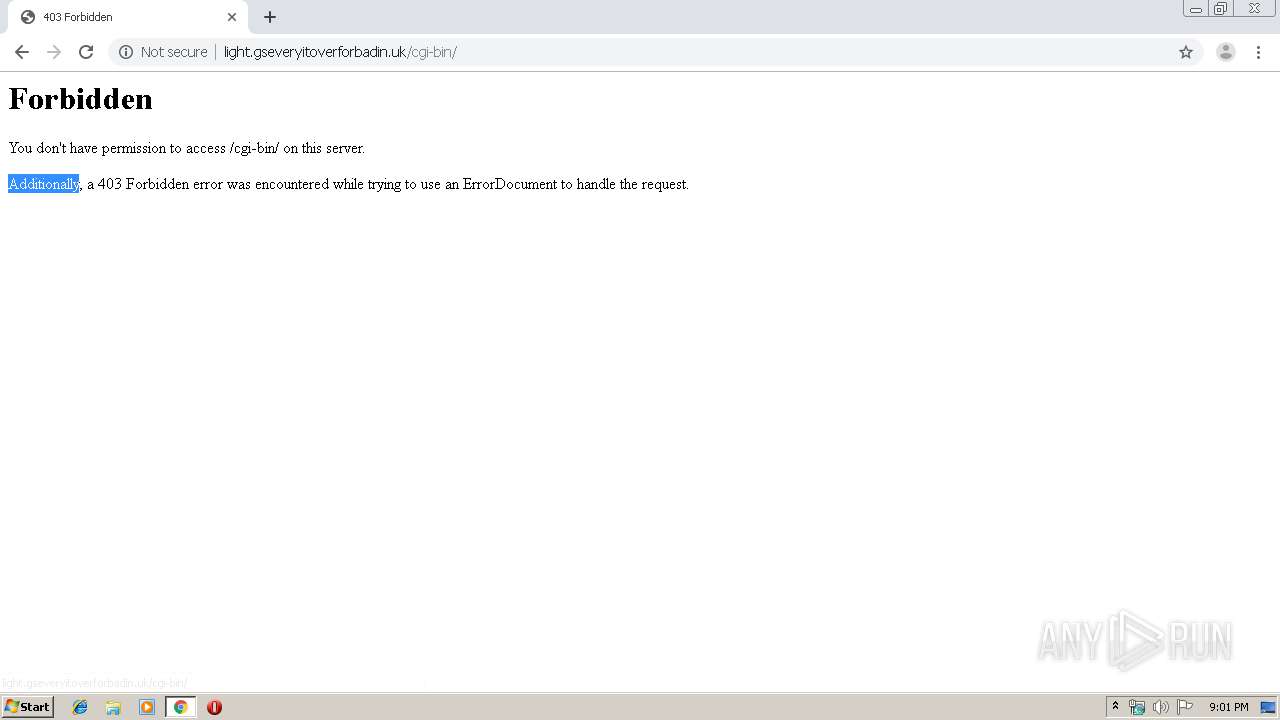
2548 | chrome.exe | GET | 403 | 51.77.151.60:80 | http://light.gseveryitoverforbadin.uk/cgi-bin/ | GB | html | 336 b | suspicious |
2548 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
2548 | chrome.exe | GET | 404 | 51.77.151.60:80 | http://light.gseveryitoverforbadin.uk/favicon.ico | GB | html | 328 b | suspicious |
2548 | chrome.exe | GET | 200 | 74.125.173.170:80 | http://r5---sn-1gieen7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.212.170.83&mm=28&mn=sn-1gieen7e&ms=nvh&mt=1562875159&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
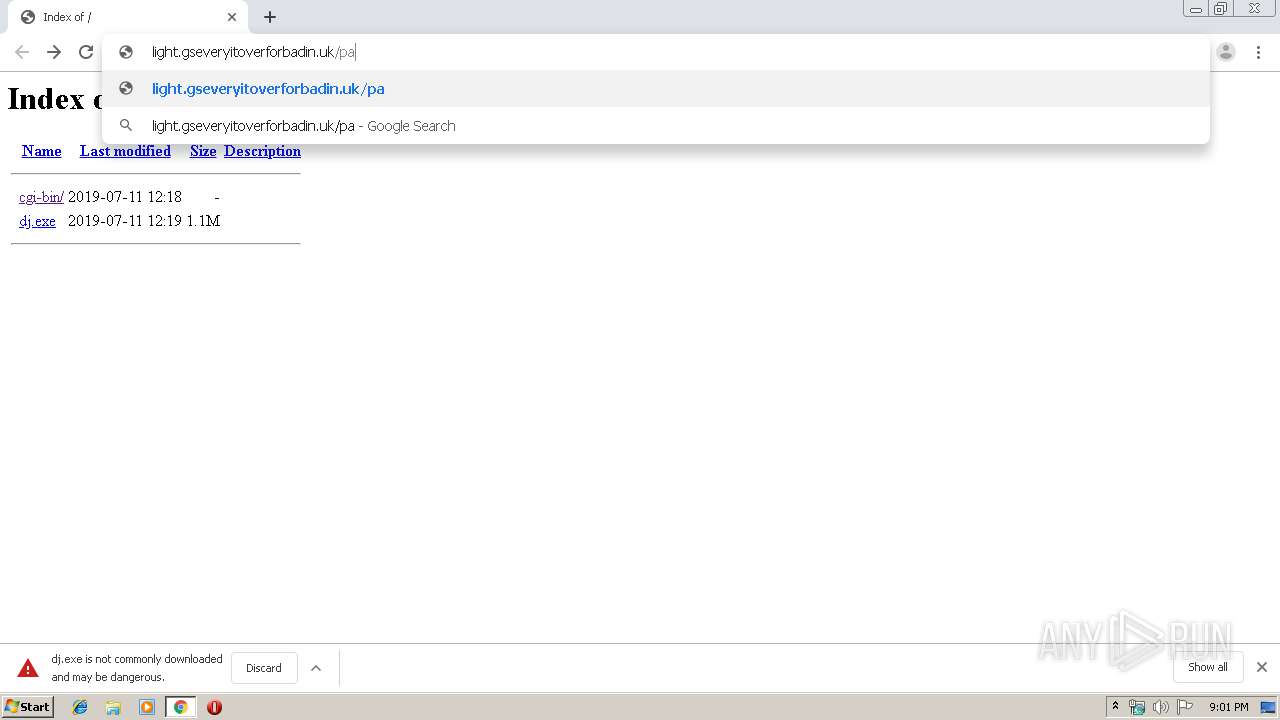
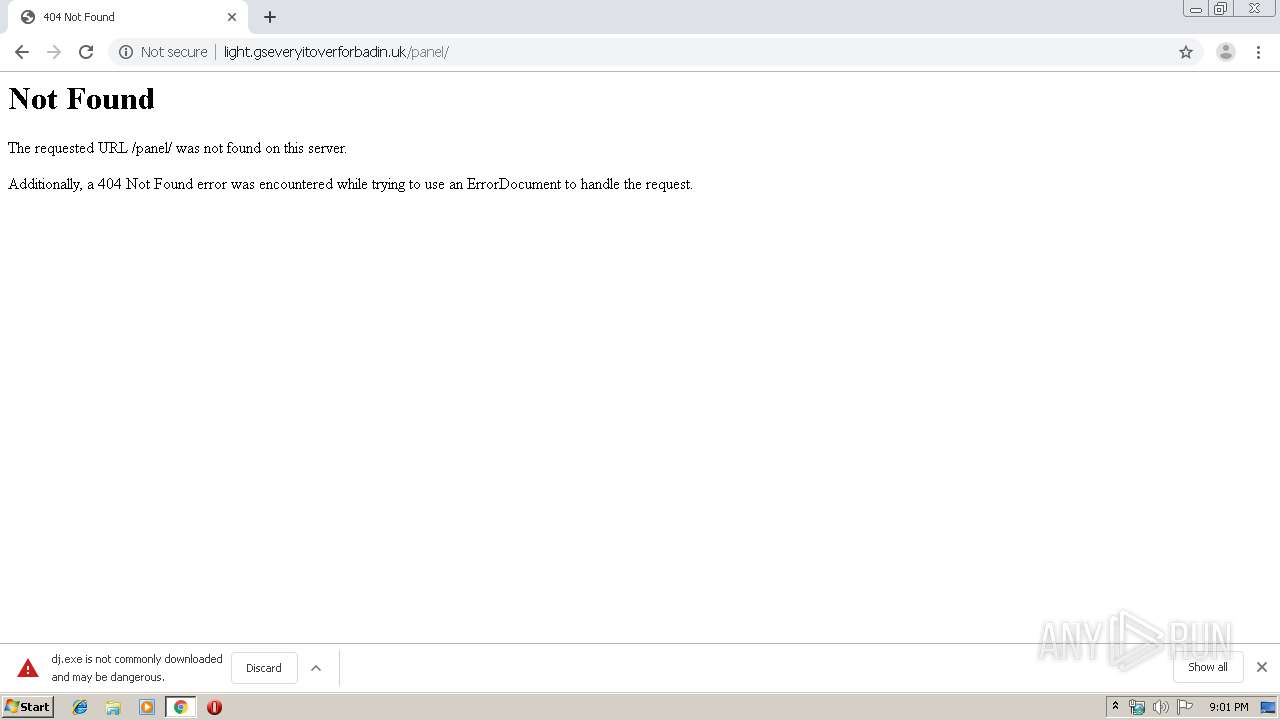
2548 | chrome.exe | GET | 404 | 51.77.151.60:80 | http://light.gseveryitoverforbadin.uk/panel/ | GB | html | 323 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2548 | chrome.exe | 74.125.173.170:80 | r5---sn-1gieen7e.gvt1.com | Google Inc. | US | whitelisted |
2548 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2548 | chrome.exe | 51.77.151.60:80 | light.gseveryitoverforbadin.uk | — | GB | suspicious |
2548 | chrome.exe | 172.217.22.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
2548 | chrome.exe | 172.217.22.1:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2548 | chrome.exe | 172.217.18.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2548 | chrome.exe | 172.217.22.4:443 | www.google.com | Google Inc. | US | whitelisted |
2548 | chrome.exe | 172.217.21.238:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2548 | chrome.exe | 172.217.21.227:443 | www.google.ch | Google Inc. | US | whitelisted |
2548 | chrome.exe | 216.58.205.238:443 | safebrowsing.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
light.gseveryitoverforbadin.uk |
| suspicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
www.google.com |
| malicious |
redirector.gvt1.com |
| whitelisted |
r5---sn-1gieen7e.gvt1.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2548 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2496 | images.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Encrypted Checkin |
2948 | dj.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Encrypted Checkin |
3552 | images.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Encrypted Checkin |
2176 | images.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Encrypted Checkin |
3248 | WerFault.exe | Potential Corporate Privacy Violation | ET POLICY Application Crash Report Sent to Microsoft |
3248 | WerFault.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
1952 | dj.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Encrypted Checkin |
2 ETPRO signatures available at the full report