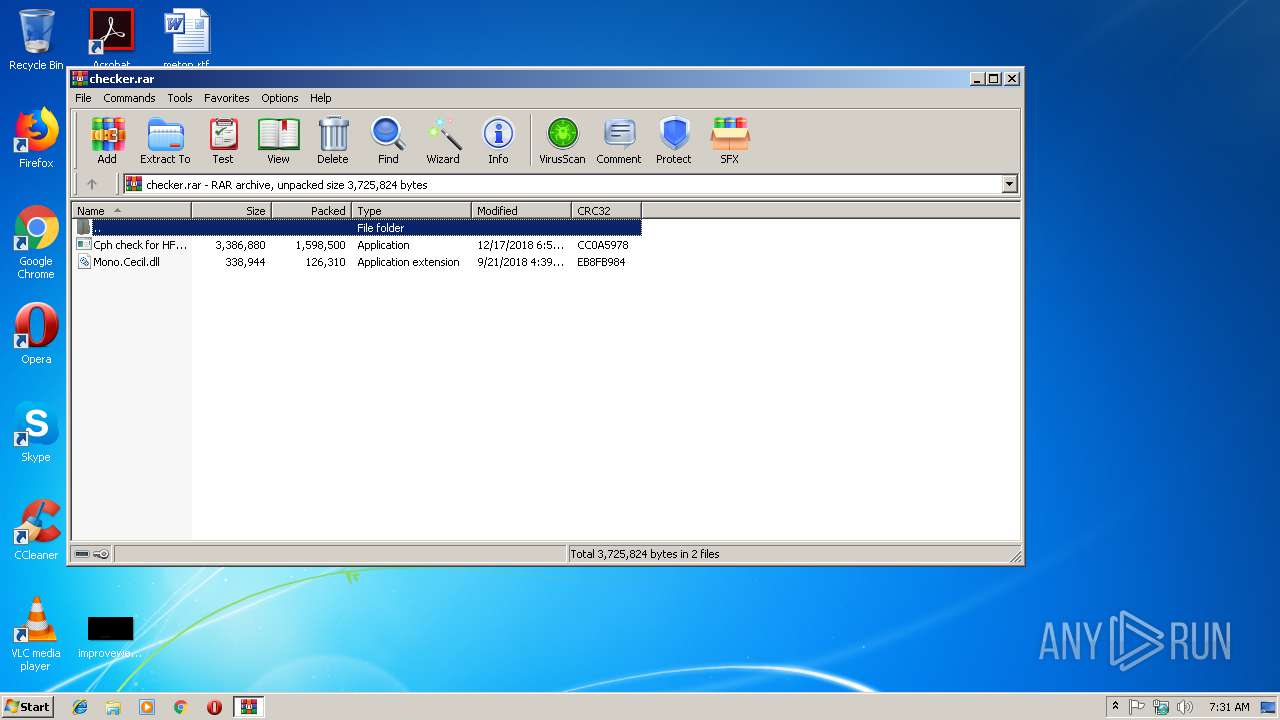
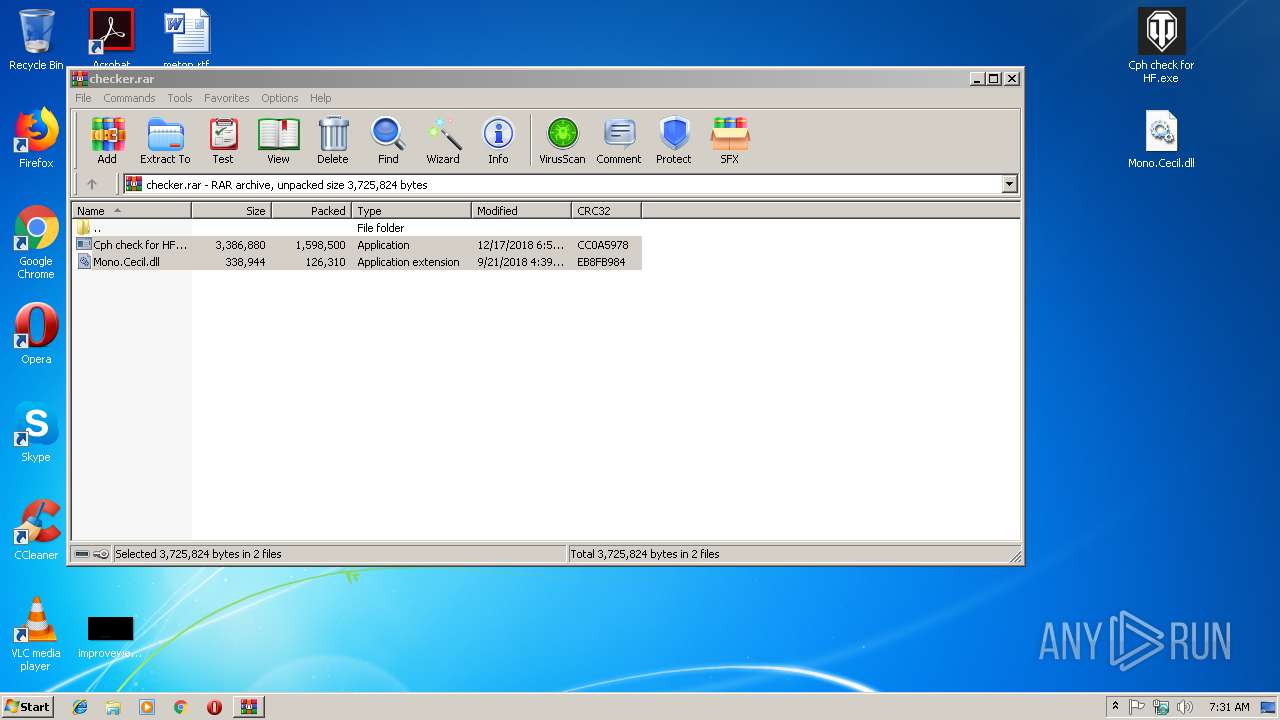
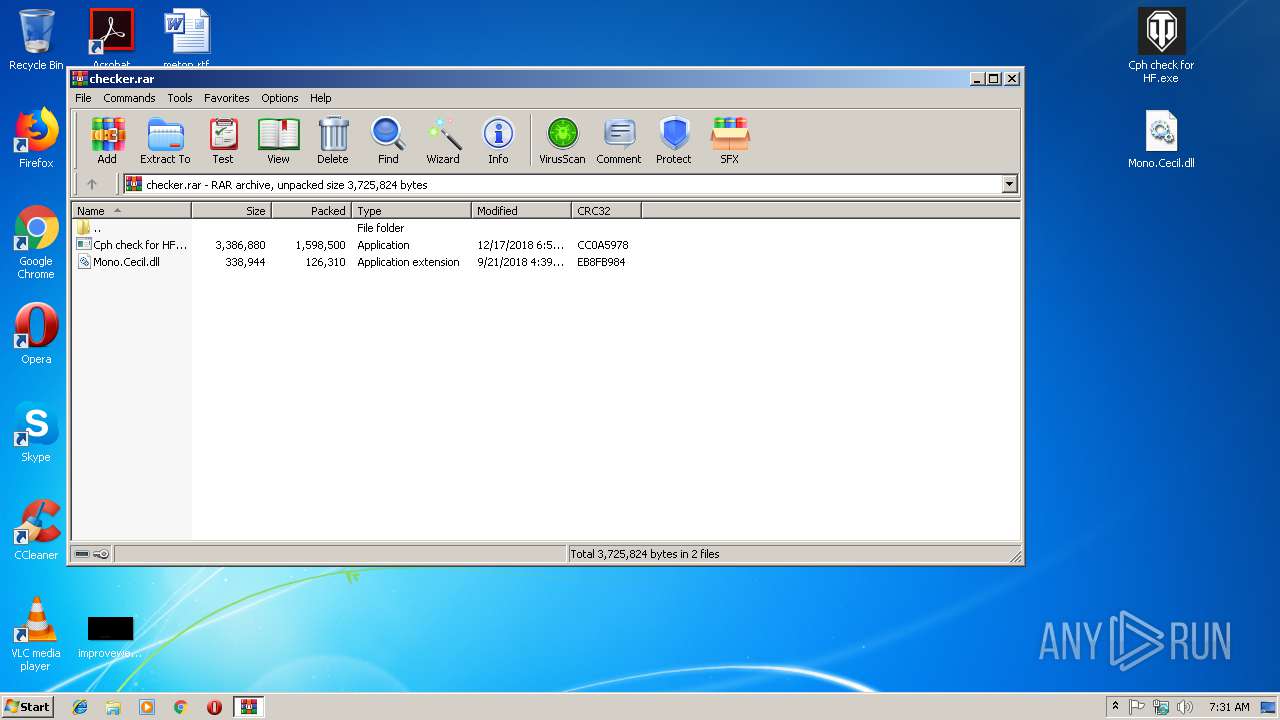
| File name: | checker.rar |
| Full analysis: | https://app.any.run/tasks/9218936d-82e4-46ad-b718-8570554909ab |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
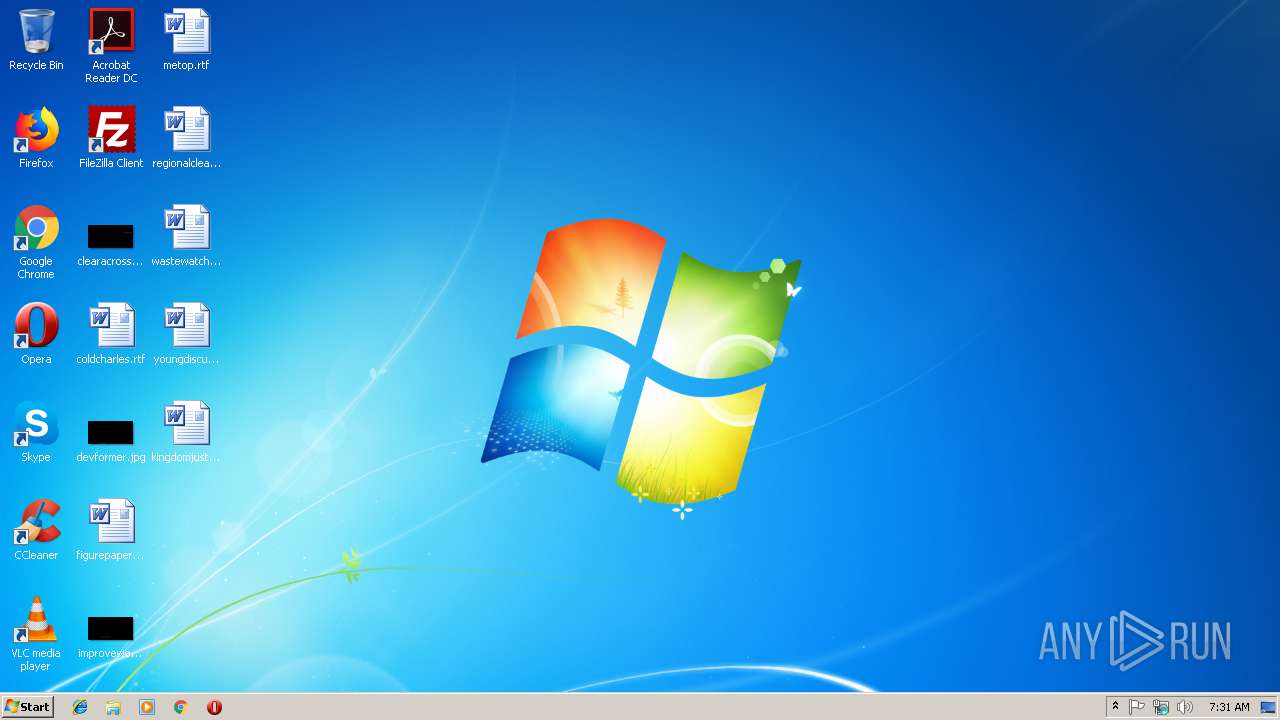
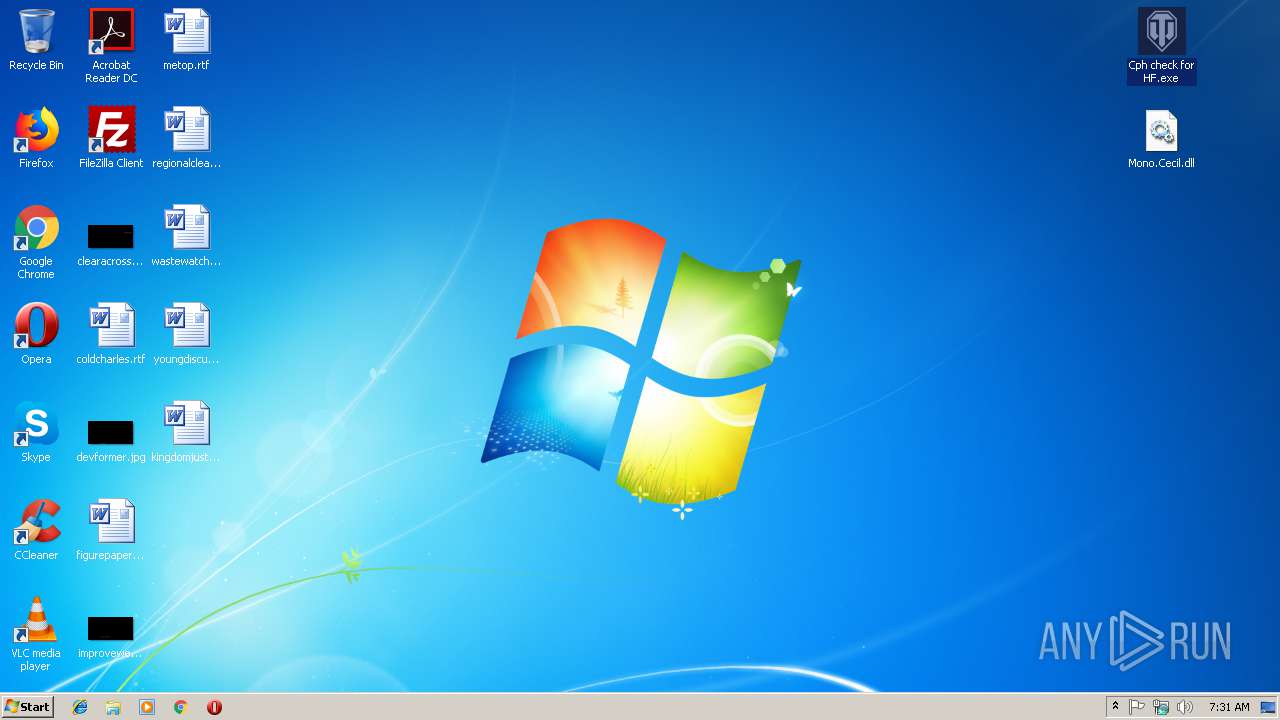
| Analysis date: | December 18, 2018, 07:31:21 |
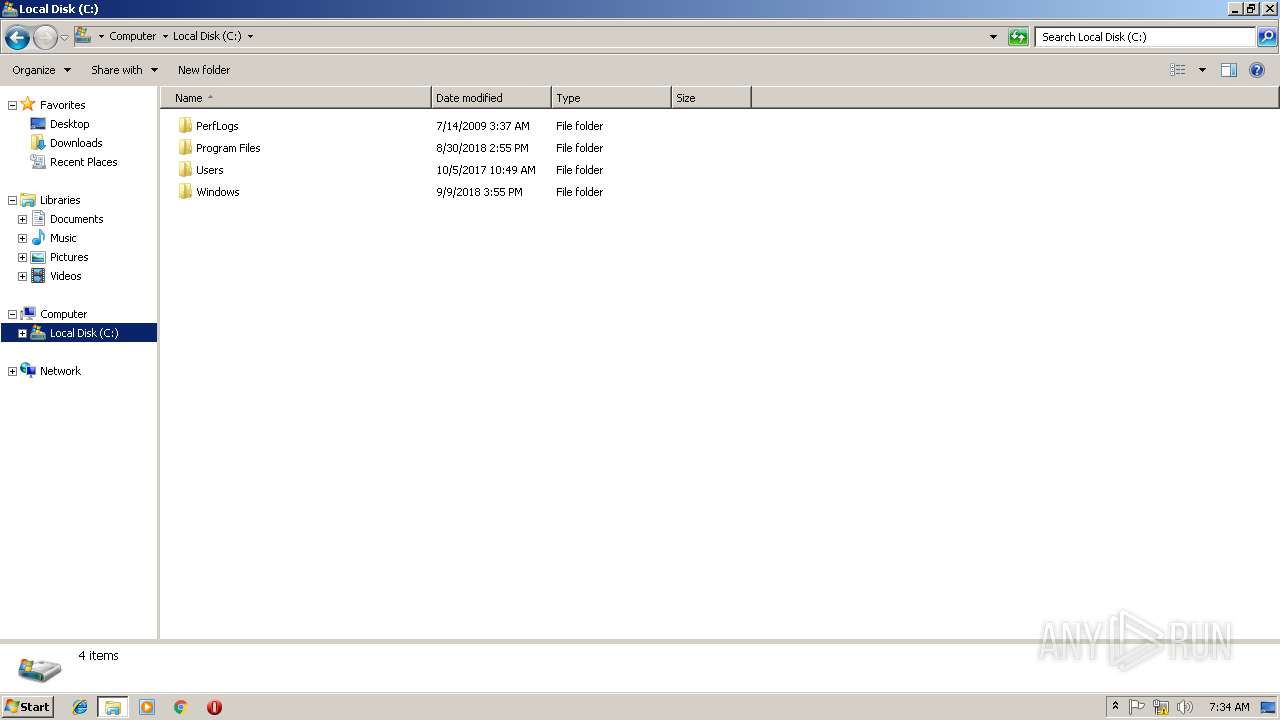
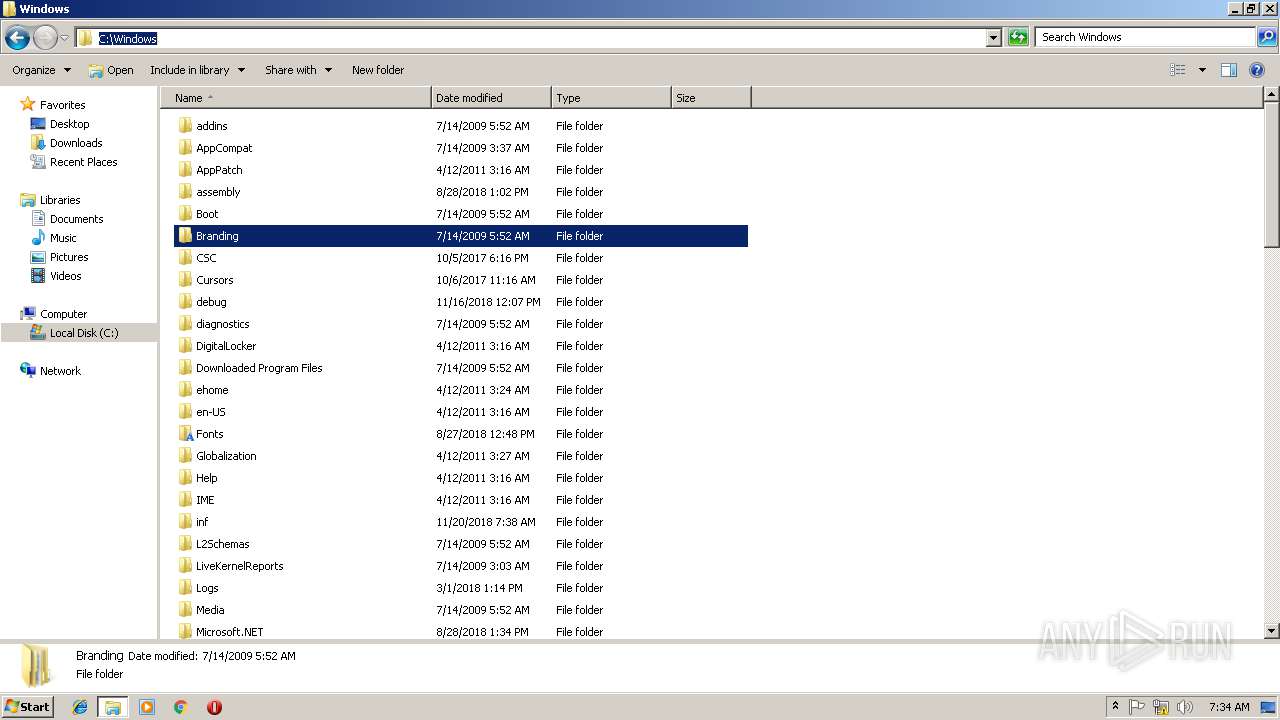
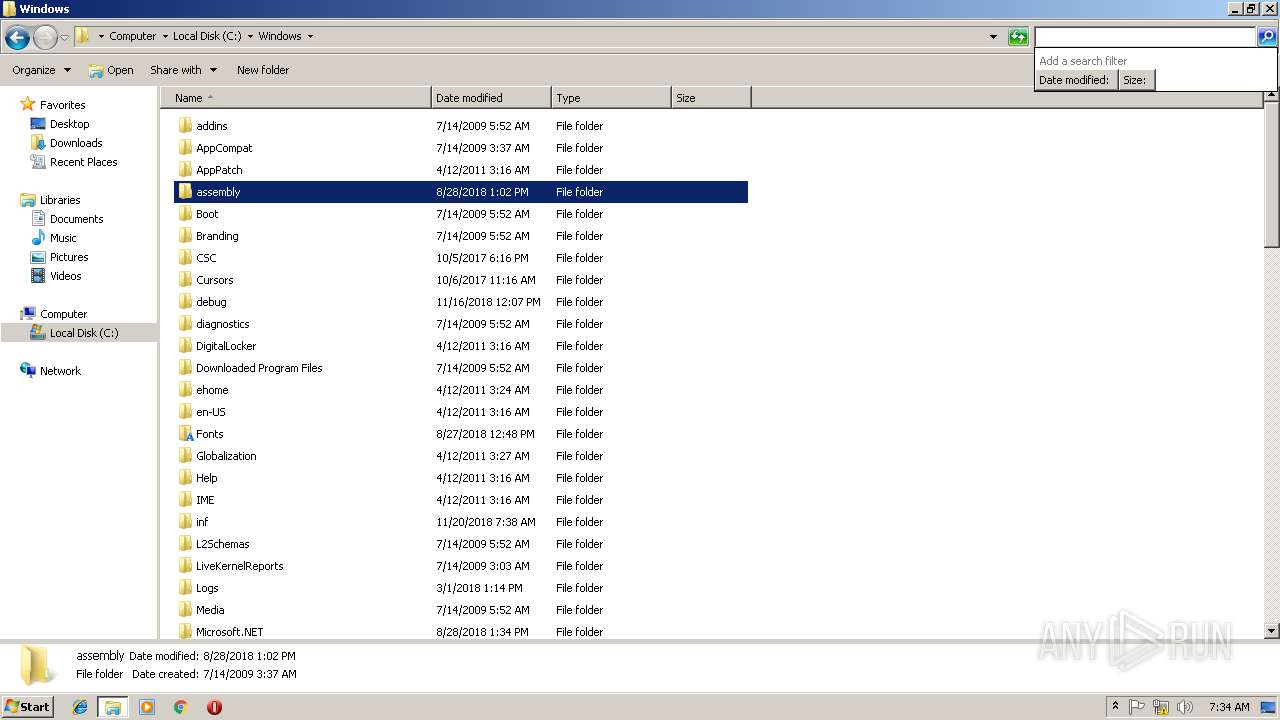
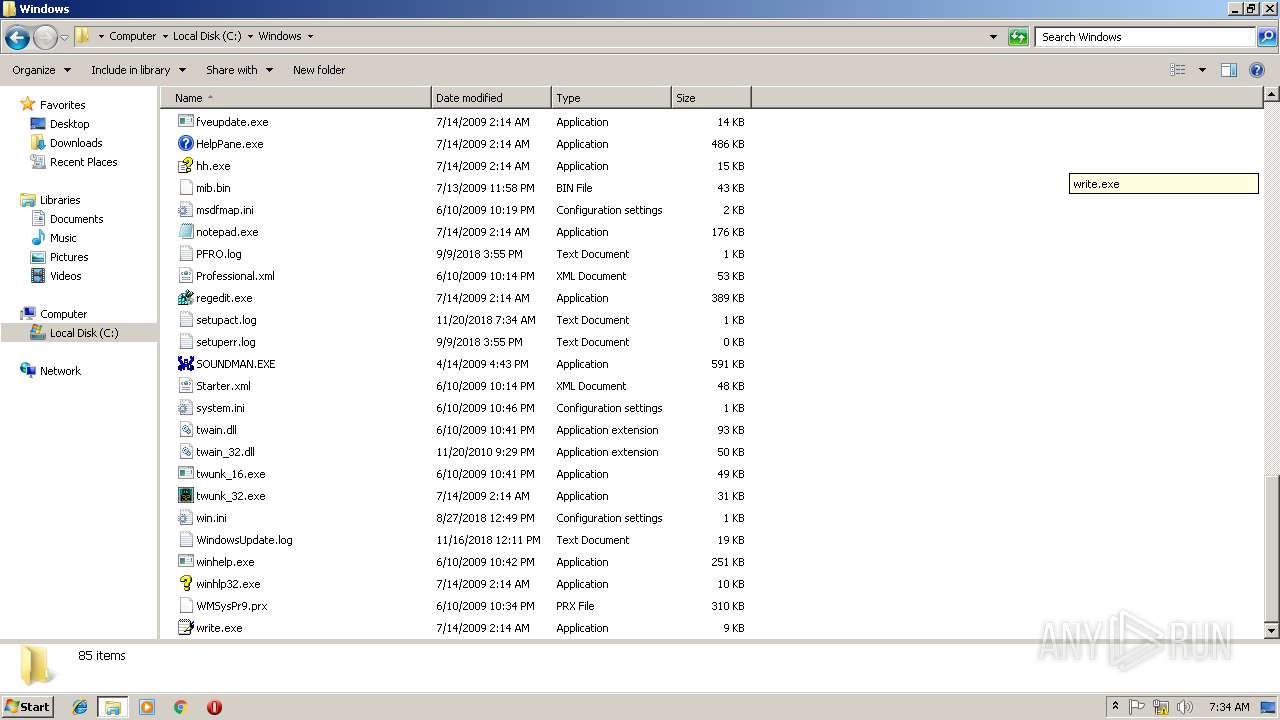
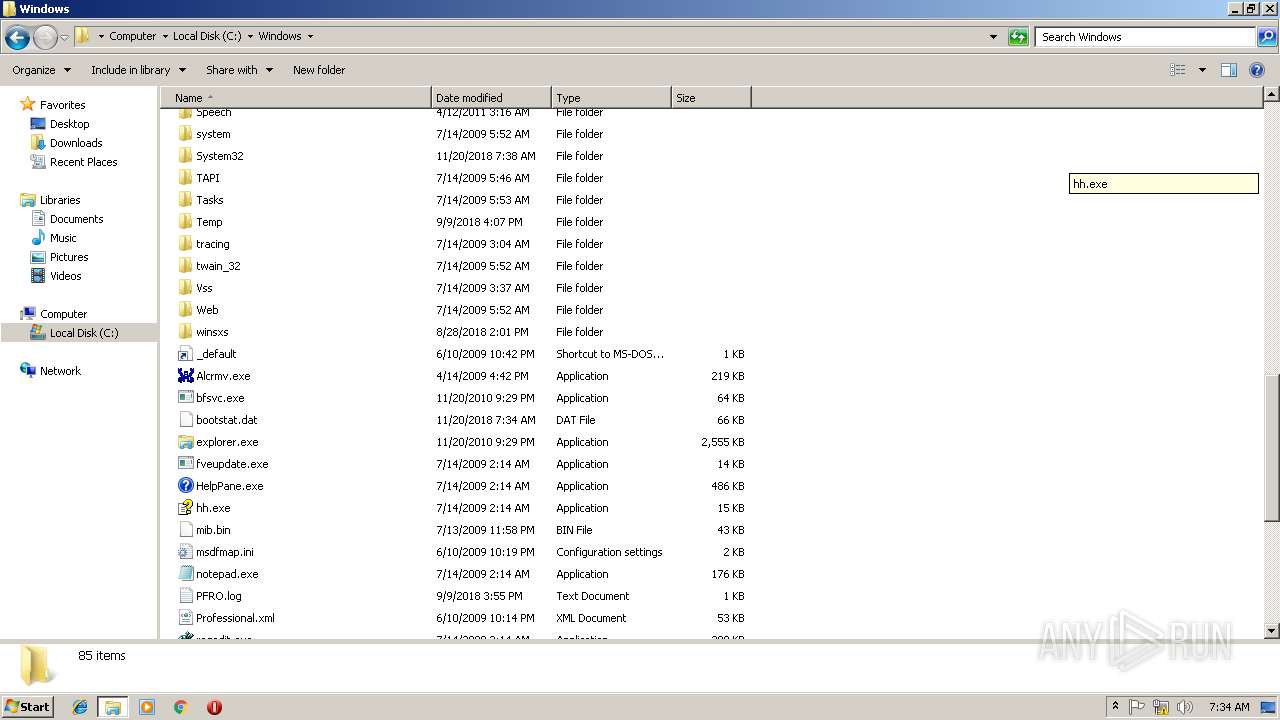
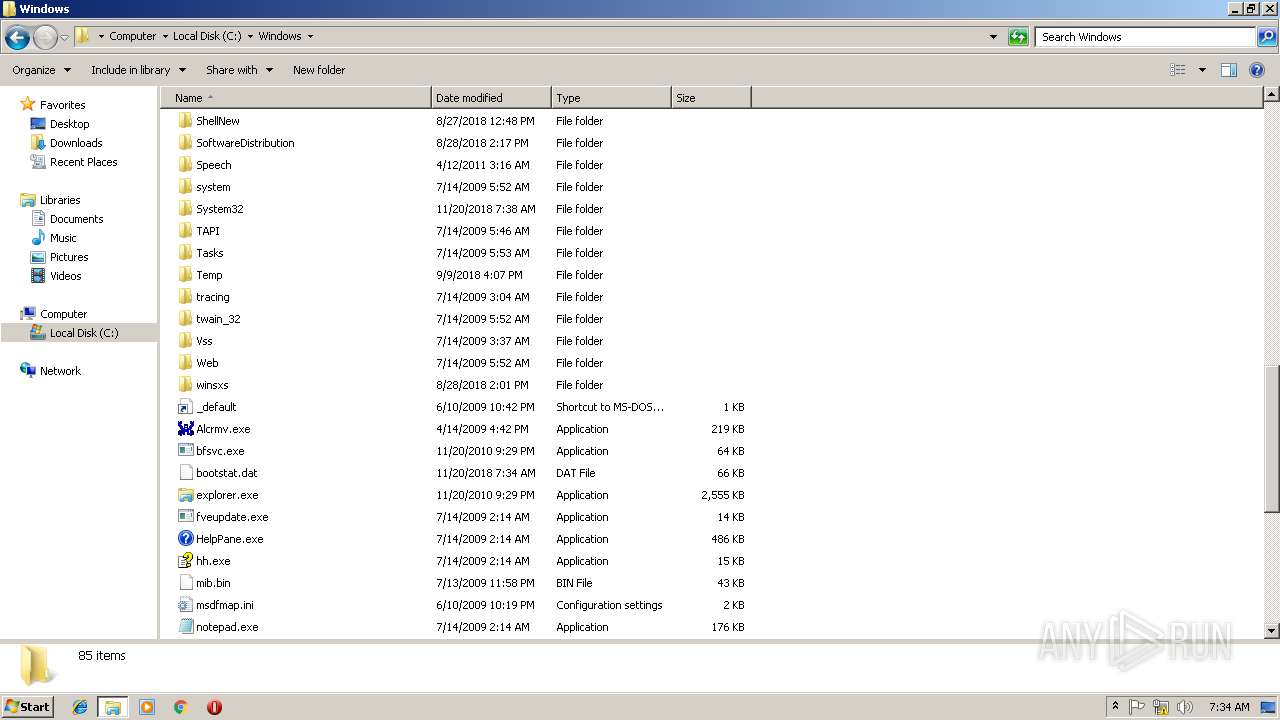
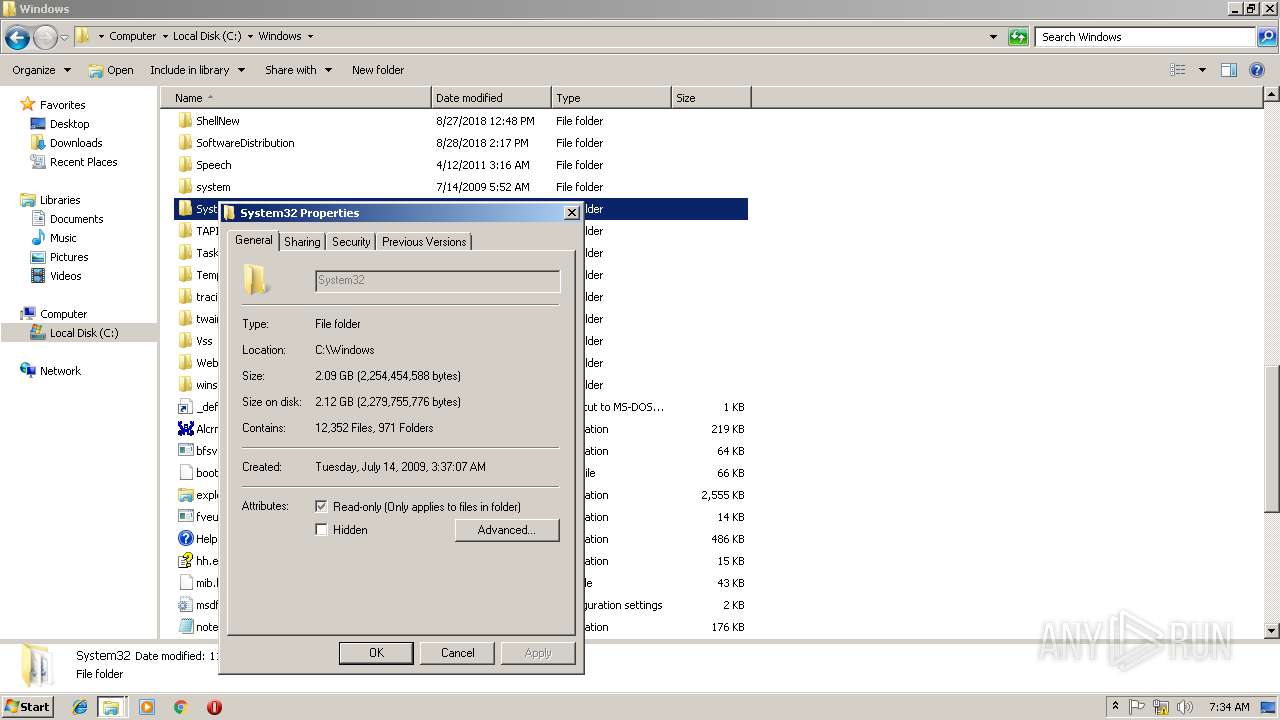
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 9AF6E91BF19AE7B4E92A3701ABD01299 |
| SHA1: | D28196297FD55010DB94A3C234A75766A9787F75 |
| SHA256: | B7997BD6F01D5CB7496C4746CC449573082BFF8E727EF8FDD6CC3393A5BAE363 |
| SSDEEP: | 49152:ncGSlbcIZl2WatdpLm3+iLP00h54wcvWSQL:ncnCIn2WSpLM354YL |
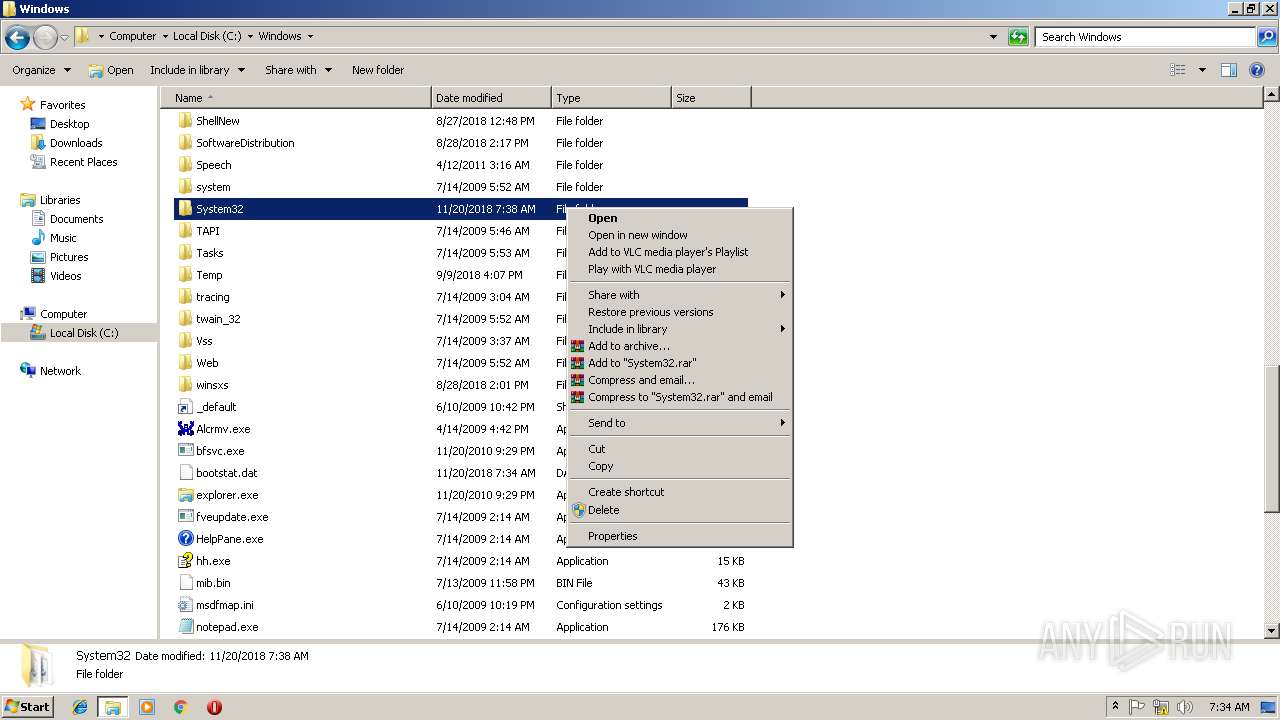
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 612)
Application was dropped or rewritten from another process
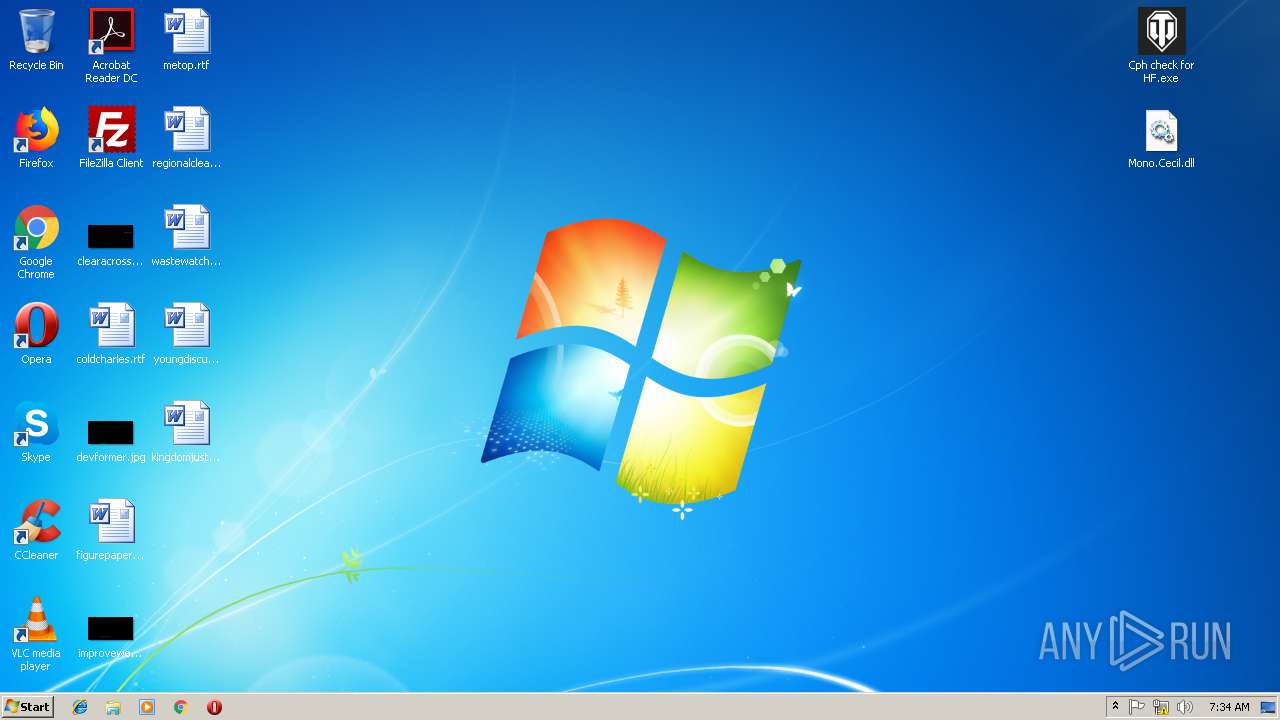
- Cph check for HF.exe (PID: 2388)
- Adobe.exe (PID: 2284)
QUASAR was detected
- Regasm.exe (PID: 3968)
SUSPICIOUS
Creates files in the user directory
- Regasm.exe (PID: 3968)
- Cph check for HF.exe (PID: 2388)
Checks for external IP
- Regasm.exe (PID: 3968)
Connects to unusual port
- Regasm.exe (PID: 3968)
Starts itself from another location
- Cph check for HF.exe (PID: 2388)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3016)
- Cph check for HF.exe (PID: 2388)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
43
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 612 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe6_ Global\UsGthrCtrlFltPipeMssGthrPipe6 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
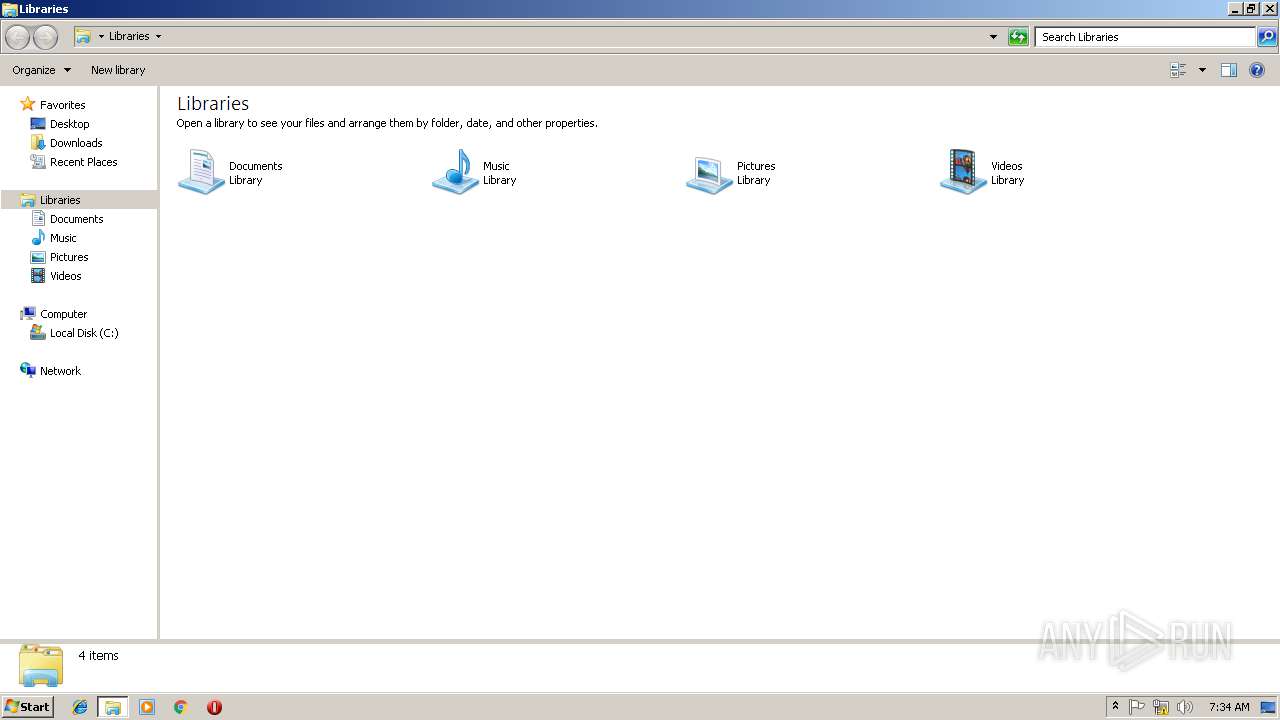
| 1092 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2284 | "C:\Users\admin\AppData\Roaming\Adobe.exe" | C:\Users\admin\AppData\Roaming\Adobe.exe | — | Cph check for HF.exe | |||||||||||
User: admin Company: VLC media player Integrity Level: HIGH Description: vlc Exit code: 0 Version: 3.0.3.0 Modules
| |||||||||||||||
| 2388 | "C:\Users\admin\Desktop\Cph check for HF.exe" | C:\Users\admin\Desktop\Cph check for HF.exe | explorer.exe | ||||||||||||
User: admin Company: VLC media player Integrity Level: HIGH Description: vlc Exit code: 0 Version: 3.0.3.0 Modules
| |||||||||||||||
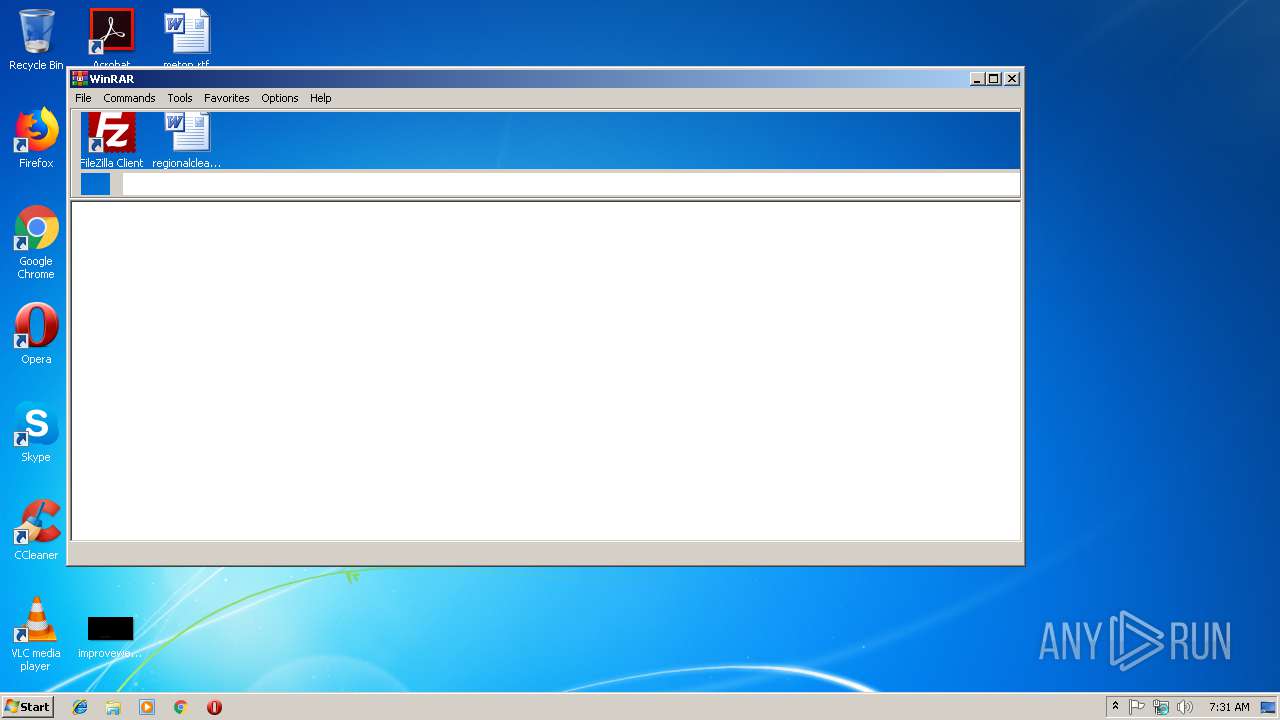
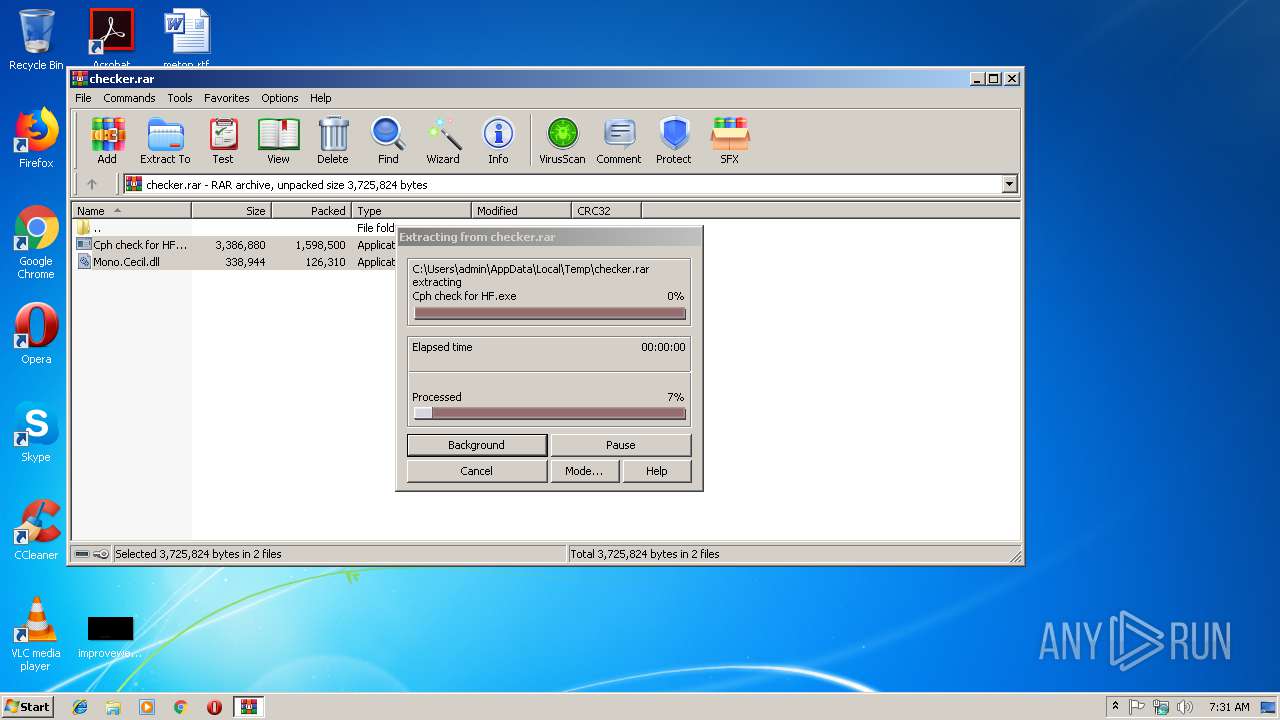
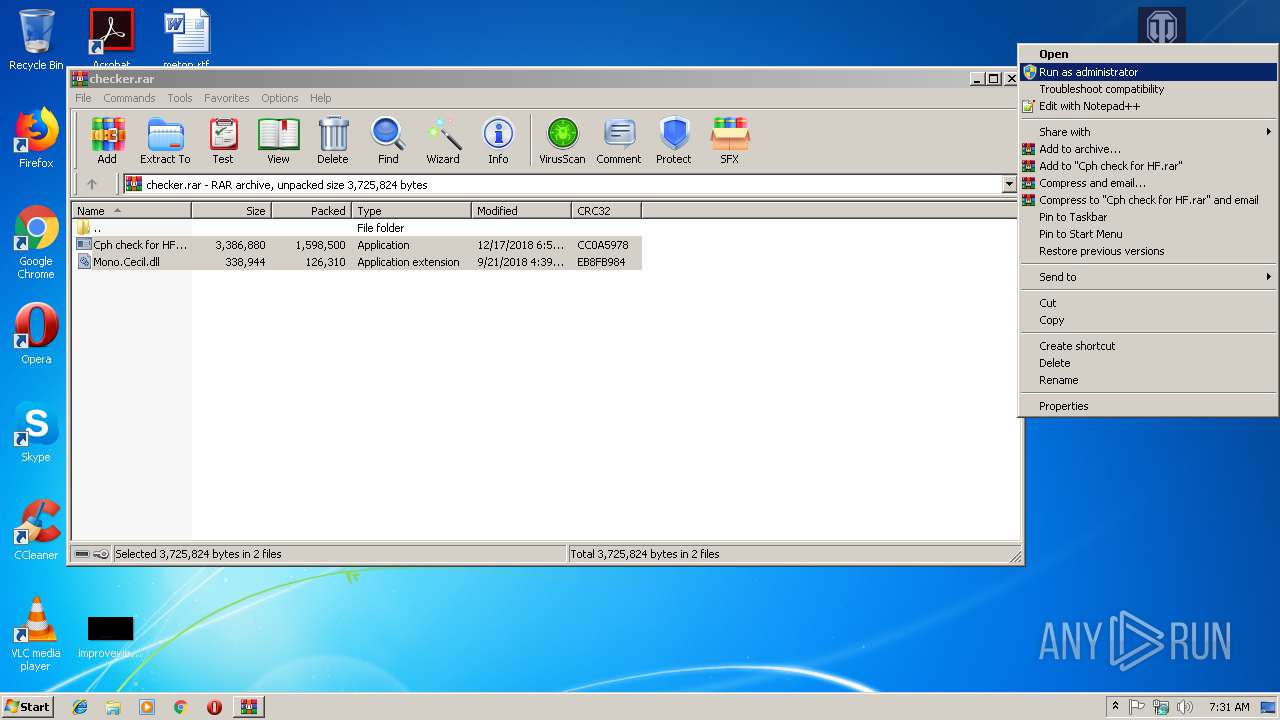
| 3016 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\checker.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3968 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe | Adobe.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
Total events
870
Read events
834
Write events
36
Delete events
0
Modification events
| (PID) Process: | (3016) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3016) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3016) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3016) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\checker.rar | |||
| (PID) Process: | (3016) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3016) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3016) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3016) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2388) Cph check for HF.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\Run\CurrentVersion |
| Operation: | write | Name: | Adobe.exe |
Value: C:\Users\admin\AppData\Roaming\Adobe.exe | |||
| (PID) Process: | (2388) Cph check for HF.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
3
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3968 | Regasm.exe | C:\Users\admin\AppData\Roaming\Logs\12-18-2018 | binary | |
MD5:— | SHA256:— | |||
| 2388 | Cph check for HF.exe | C:\Users\admin\AppData\Roaming\Adobe.exe | executable | |
MD5:— | SHA256:— | |||
| 3016 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3016.30939\Cph check for HF.exe | executable | |
MD5:— | SHA256:— | |||
| 3016 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3016.30939\Mono.Cecil.dll | executable | |
MD5:8152E9D15C022E601EFA9DA3A3BEFD71 | SHA256:4457EF2BA0D3B802CDC5384F044C9CBDDAB6FC8B25AAD794B4BCE3249D106054 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
5
DNS requests
5
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3968 | Regasm.exe | GET | 200 | 185.194.141.58:80 | http://ip-api.com/json/ | DE | text | 255 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3968 | Regasm.exe | 185.194.141.58:80 | ip-api.com | netcup GmbH | DE | unknown |
3968 | Regasm.exe | 217.12.210.23:4782 | cphdnstest.hopto.org | ITL Company | UA | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ip-api.com |
| malicious |
cphdnstest.hopto.org |
| malicious |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3968 | Regasm.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
3968 | Regasm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Quasar 1.3 RAT IP Lookup ip-api.com (HTTP headeer) |
1 ETPRO signatures available at the full report