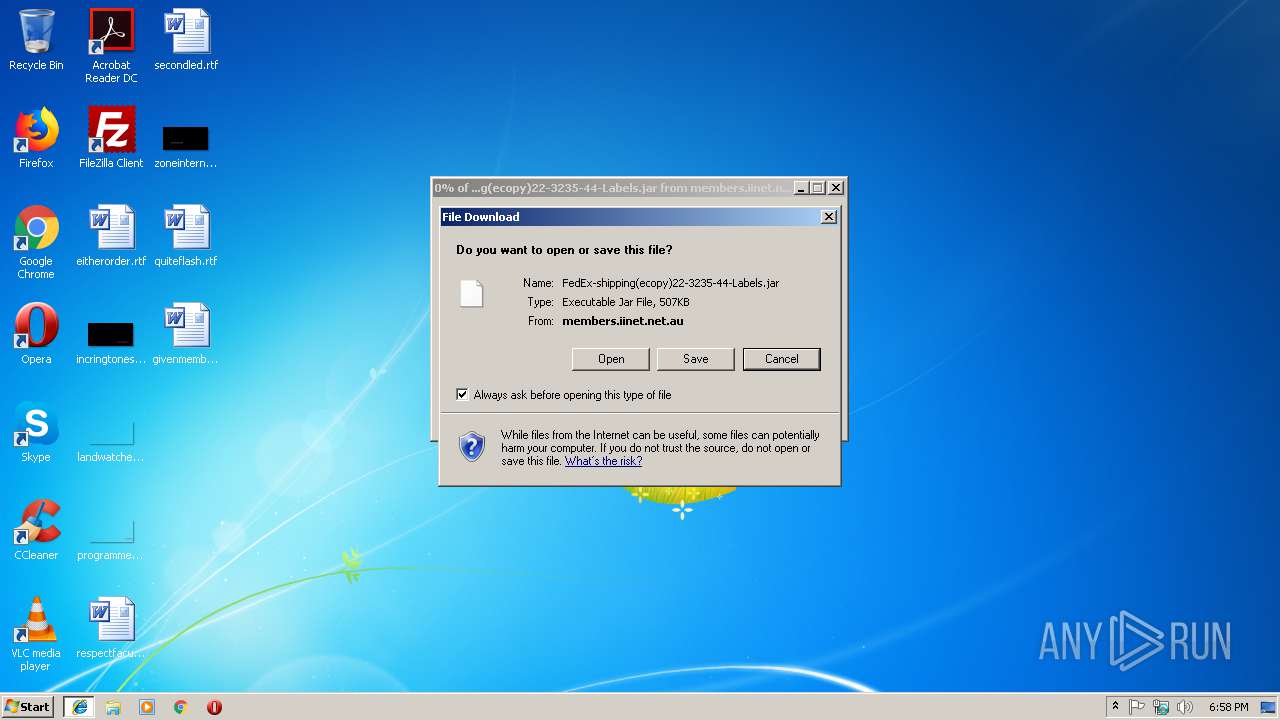
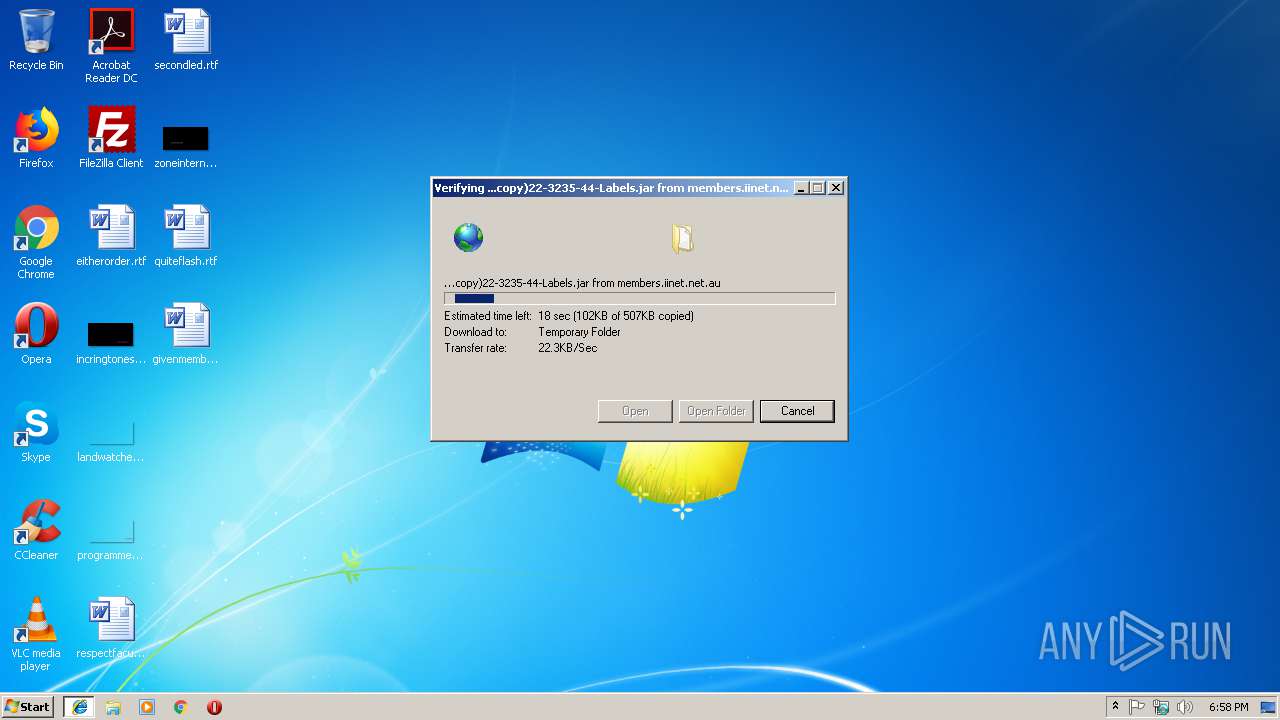
| URL: | http://members.iinet.net.au/~sambo75/FedEx-shipping(ecopy)22-3235-44-Labels.jar |
| Full analysis: | https://app.any.run/tasks/0a044bac-86f0-4061-b5da-e736f64ca2db |
| Verdict: | Malicious activity |
| Threats: | Adwind RAT, sometimes also called Unrecom, Sockrat, Frutas, jRat, and JSocket, is a Malware As A Service Remote Access Trojan that attackers can use to collect information from infected machines. It was one of the most popular RATs in the market in 2015. |
| Analysis date: | December 14, 2018, 18:58:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C56EF284916710CB1B7F0DA78A5CED02 |
| SHA1: | 34399ADF088FBF25A71DE948BC483802B87BFB93 |
| SHA256: | B767A69FFC8FA192D2304B85B46F04CB2C46AC1B84B85590706D107CAC9841BC |
| SSDEEP: | 3:N1KTXm0LEQV1jpcmLCN2rXXIWGQI3dg4+:Ch9LVHI36Z |
MALICIOUS
AdWind was detected
- java.exe (PID: 3148)
- java.exe (PID: 2728)
Loads dropped or rewritten executable
- iexplore.exe (PID: 3228)
- javaw.exe (PID: 2764)
- java.exe (PID: 3148)
- iexplore.exe (PID: 2944)
- javaw.exe (PID: 2332)
- java.exe (PID: 2728)
Application was dropped or rewritten from another process
- java.exe (PID: 3148)
- javaw.exe (PID: 2764)
- javaw.exe (PID: 2332)
- java.exe (PID: 2728)
Changes the autorun value in the registry
- reg.exe (PID: 2452)
ADWIND was detected
- javaw.exe (PID: 2332)
SUSPICIOUS
Creates files in the user directory
- javaw.exe (PID: 2764)
- xcopy.exe (PID: 3968)
Starts CMD.EXE for commands execution
- javaw.exe (PID: 2764)
- java.exe (PID: 3148)
- java.exe (PID: 2728)
- javaw.exe (PID: 2332)
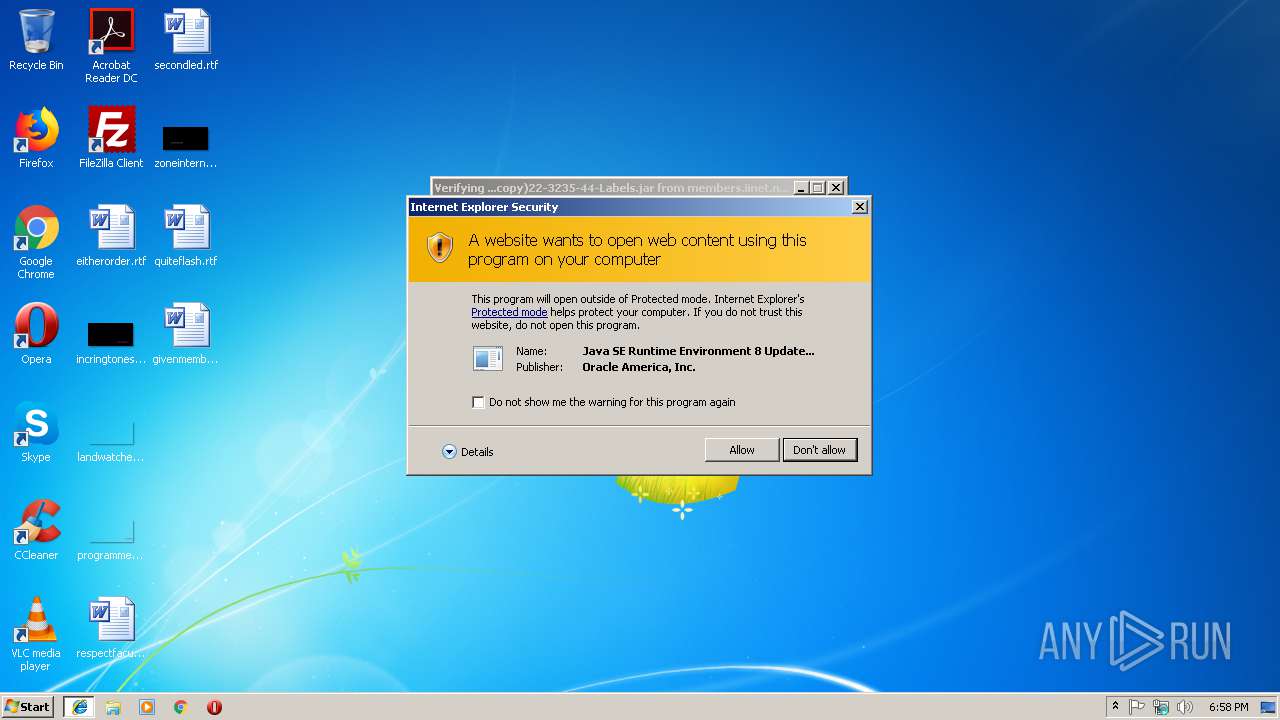
Executes JAVA applets
- javaw.exe (PID: 2764)
- iexplore.exe (PID: 2944)
Executes scripts
- cmd.exe (PID: 4040)
- cmd.exe (PID: 2176)
- cmd.exe (PID: 2824)
- cmd.exe (PID: 3676)
- cmd.exe (PID: 2620)
- cmd.exe (PID: 2612)
- cmd.exe (PID: 2660)
- cmd.exe (PID: 2800)
Executable content was dropped or overwritten
- xcopy.exe (PID: 3968)
- javaw.exe (PID: 2332)
Uses ATTRIB.EXE to modify file attributes
- javaw.exe (PID: 2764)
Starts itself from another location
- javaw.exe (PID: 2764)
Uses REG.EXE to modify Windows registry
- javaw.exe (PID: 2764)
Connects to unusual port
- javaw.exe (PID: 2332)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2944)
Reads settings of System Certificates
- iexplore.exe (PID: 2944)
Reads Internet Cache Settings
- iexplore.exe (PID: 3228)
- iexplore.exe (PID: 2944)
Application launched itself
- iexplore.exe (PID: 2944)
Creates files in the user directory
- iexplore.exe (PID: 3228)
- iexplore.exe (PID: 2944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
72
Monitored processes
27
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2176 | cmd.exe /C cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive5102215968150116583.vbs | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2316 | cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive4205122069500729217.vbs | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2332 | C:\Users\admin\AppData\Roaming\Oracle\bin\javaw.exe -jar C:\Users\admin\OFSjRiXdnZC\KtqtPnJOfkG.wRYYfN | C:\Users\admin\AppData\Roaming\Oracle\bin\javaw.exe | javaw.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2452 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Run /v noZEbihAfjf /t REG_EXPAND_SZ /d "\"C:\Users\admin\AppData\Roaming\Oracle\bin\javaw.exe\" -jar \"C:\Users\admin\OFSjRiXdnZC\KtqtPnJOfkG.wRYYfN\"" /f | C:\Windows\system32\reg.exe | javaw.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2604 | attrib +h "C:\Users\admin\OFSjRiXdnZC\*.*" | C:\Windows\system32\attrib.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2612 | cmd.exe /C cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive429920747253108235.vbs | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2620 | cmd.exe /C cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive3872764485955992321.vbs | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2640 | cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive8817750696798682258.vbs | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2660 | cmd.exe /C cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive2916085115602438210.vbs | C:\Windows\system32\cmd.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2708 | cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive5102215968150116583.vbs | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
932
Read events
868
Write events
60
Delete events
4
Modification events
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {4461DA61-FFD2-11E8-BAD8-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070C0005000E0012003A0028004E02 | |||
Executable files
109
Suspicious files
13
Text files
78
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2944 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFEDDD03F487A8285E.TMP | — | |
MD5:— | SHA256:— | |||
| 2944 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2944 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2944 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF28D876B3D9F1F0A3.TMP | — | |
MD5:— | SHA256:— | |||
| 2944 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{4461DA61-FFD2-11E8-BAD8-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2764 | javaw.exe | C:\Users\admin\AppData\Local\Temp\Retrive8817750696798682258.vbs | — | |
MD5:— | SHA256:— | |||
| 3228 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\MSHist012018121420181215\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2764 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 2944 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012018121420181215\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2944 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{4461DA62-FFD2-11E8-BAD8-5254004A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
2
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3228 | iexplore.exe | GET | 200 | 203.0.178.90:80 | http://members.iinet.net.au/~sambo75/FedEx-shipping(ecopy)22-3235-44-Labels.jar | AU | compressed | 507 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2944 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3228 | iexplore.exe | 203.0.178.90:80 | members.iinet.net.au | Internode Pty Ltd | AU | malicious |
2332 | javaw.exe | 212.73.150.132:1010 | — | BelCloud Hosting Corporation | BG | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
members.iinet.net.au |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2332 | javaw.exe | A Network Trojan was detected | ET TROJAN Possible Adwind SSL Cert (assylias.Inc) |