| File name: | b71e94a993094d8ce5599f234ea57ad65f4d7336e7355d1aa29c0f3deff93976 |
| Full analysis: | https://app.any.run/tasks/2d642ca3-6e8e-4631-88e0-4691044aa9d7 |
| Verdict: | Malicious activity |
| Threats: | Cobalt Strike is a legitimate penetration software toolkit developed by Forta. But its cracked versions are widely adopted by bad actors, who use it as a C2 system of choice for targeted attacks. |
| Analysis date: | December 13, 2024, 20:47:58 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 17 sections |
| MD5: | CEBAE30FFFF7911C619B2F88ACECFE8C |
| SHA1: | C321C710C0A5AACFBA8884E8AB64F3D17B8CF667 |
| SHA256: | B71E94A993094D8CE5599F234EA57AD65F4D7336E7355D1AA29C0F3DEFF93976 |
| SSDEEP: | 1536:ENGoXbZwI+wCu4i6y8tSOPzgSQF+WSWAaKuVBIX0Bf5NhXMyp98kA:GSSZaiNhxp98kA |
MALICIOUS
COBALTSTRIKE has been detected (YARA)
- b71e94a993094d8ce5599f234ea57ad65f4d7336e7355d1aa29c0f3deff93976.exe (PID: 4504)
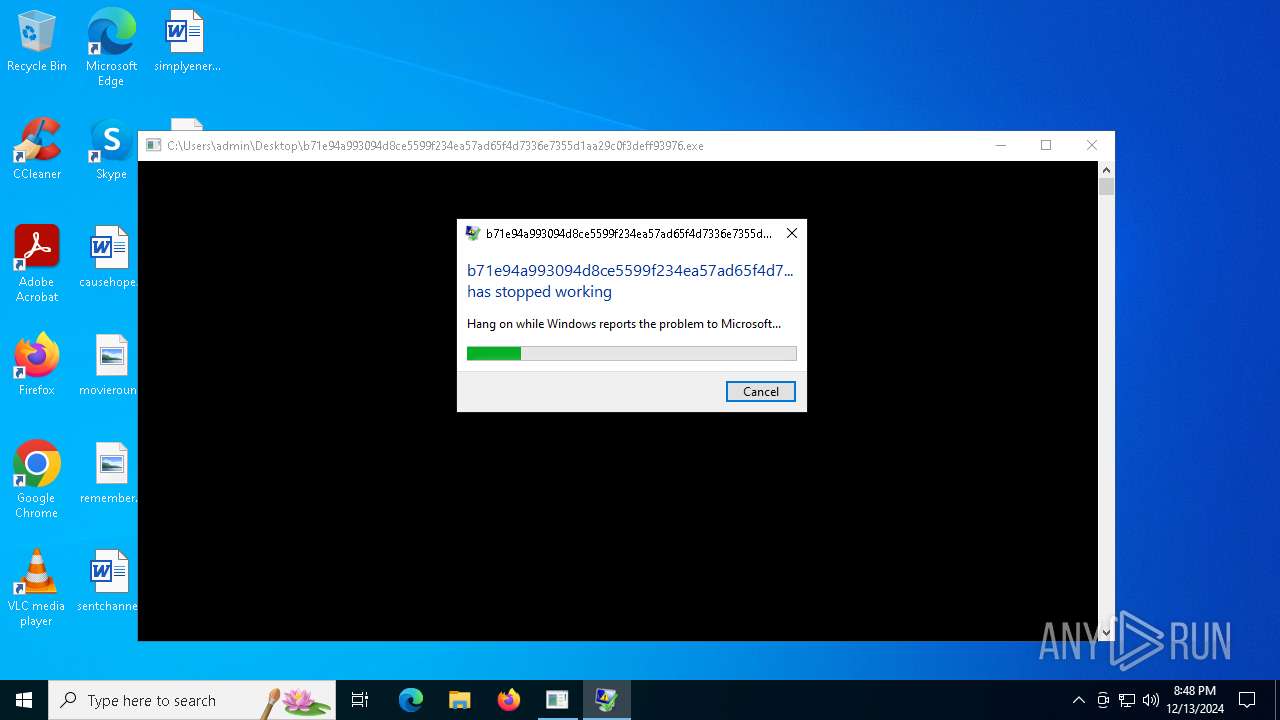
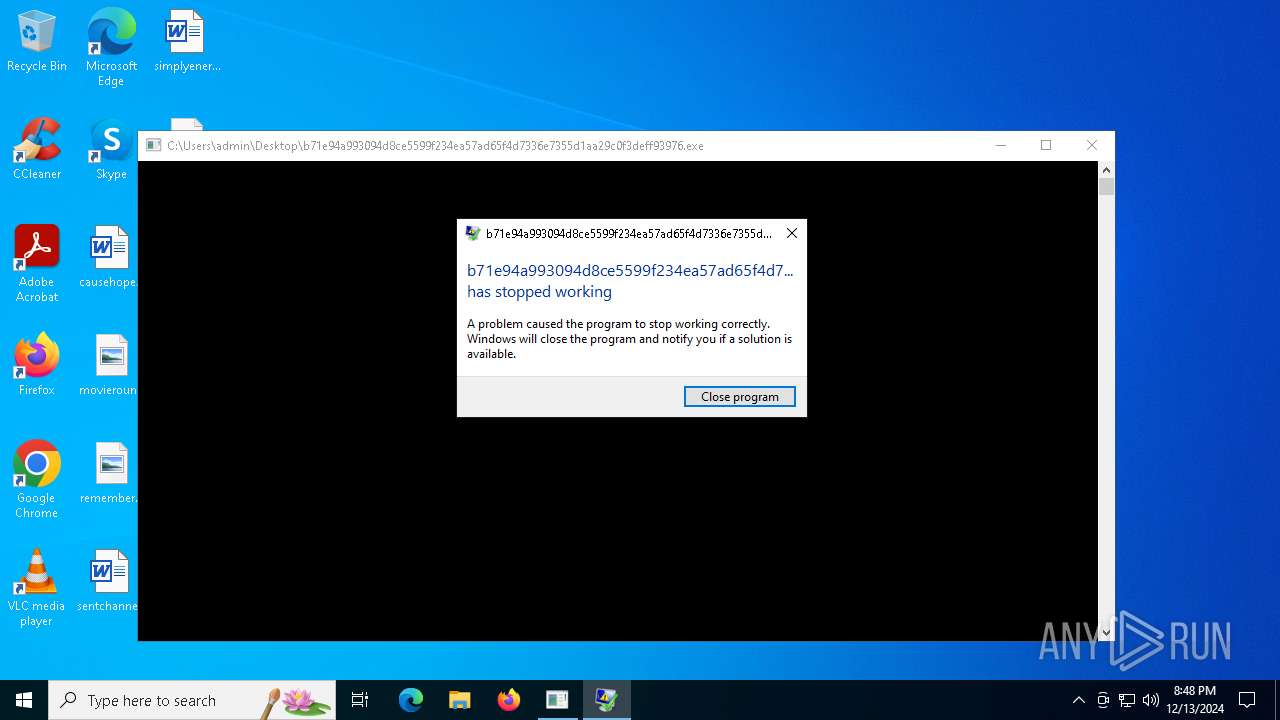
SUSPICIOUS
Executes application which crashes
- b71e94a993094d8ce5599f234ea57ad65f4d7336e7355d1aa29c0f3deff93976.exe (PID: 4504)
INFO
Checks supported languages
- b71e94a993094d8ce5599f234ea57ad65f4d7336e7355d1aa29c0f3deff93976.exe (PID: 4504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.2) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:12:11 13:22:40+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 2.24 |
| CodeSize: | 7680 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | 3072 |
| EntryPoint: | 0x1500 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
Total processes
121
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4504 | "C:\Users\admin\Desktop\b71e94a993094d8ce5599f234ea57ad65f4d7336e7355d1aa29c0f3deff93976.exe" | C:\Users\admin\Desktop\b71e94a993094d8ce5599f234ea57ad65f4d7336e7355d1aa29c0f3deff93976.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 4640 | C:\WINDOWS\system32\WerFault.exe -u -p 4504 -s 188 | C:\Windows\System32\WerFault.exe | b71e94a993094d8ce5599f234ea57ad65f4d7336e7355d1aa29c0f3deff93976.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4824 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | b71e94a993094d8ce5599f234ea57ad65f4d7336e7355d1aa29c0f3deff93976.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 741
Read events
6 741
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
1
Text files
2
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4640 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_b71e94a993094d8c_a1a2d8da604ed7f5c6533c47ea8e52ed201c163c_47fdc5b1_503e5e12-b7bd-41bf-bace-d7ca0163602b\Report.wer | — | |
MD5:— | SHA256:— | |||
| 4640 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER65E2.tmp.WERInternalMetadata.xml | xml | |
MD5:47CFF8A498621DED7CD98B91BAFE11E0 | SHA256:DDE0F66871B6CA211FD969B8C8FAA01C1AA33E917CBEDB81AD7807E72FF7F12A | |||
| 4640 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER6622.tmp.xml | xml | |
MD5:B8FC23B775C1E273171B0E4CD6B1D608 | SHA256:BB107DE942A96C7980E21A1CC2735E2F156B83AA380C32AD2077147CD9211596 | |||
| 4640 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\b71e94a993094d8ce5599f234ea57ad65f4d7336e7355d1aa29c0f3deff93976.exe.4504.dmp | dmp | |
MD5:C0637FF22E63A5D6A40455E48FC03A62 | SHA256:E16503AE67DAA0FF565D4D43AF598ED2AEB0D04E4931D946952773B6A1A9ADED | |||
| 4640 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER6593.tmp.dmp | dmp | |
MD5:C7FA0681E4F118A9E96F8C92AE7D0CA1 | SHA256:27BC3FCED01EA38E4A98AF5E65B45132296650683D1FFFD80EE26557B60BE06D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
21
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1596 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1596 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
1596 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4640 | WerFault.exe | 20.42.73.29:443 | watson.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1596 | svchost.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1596 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |