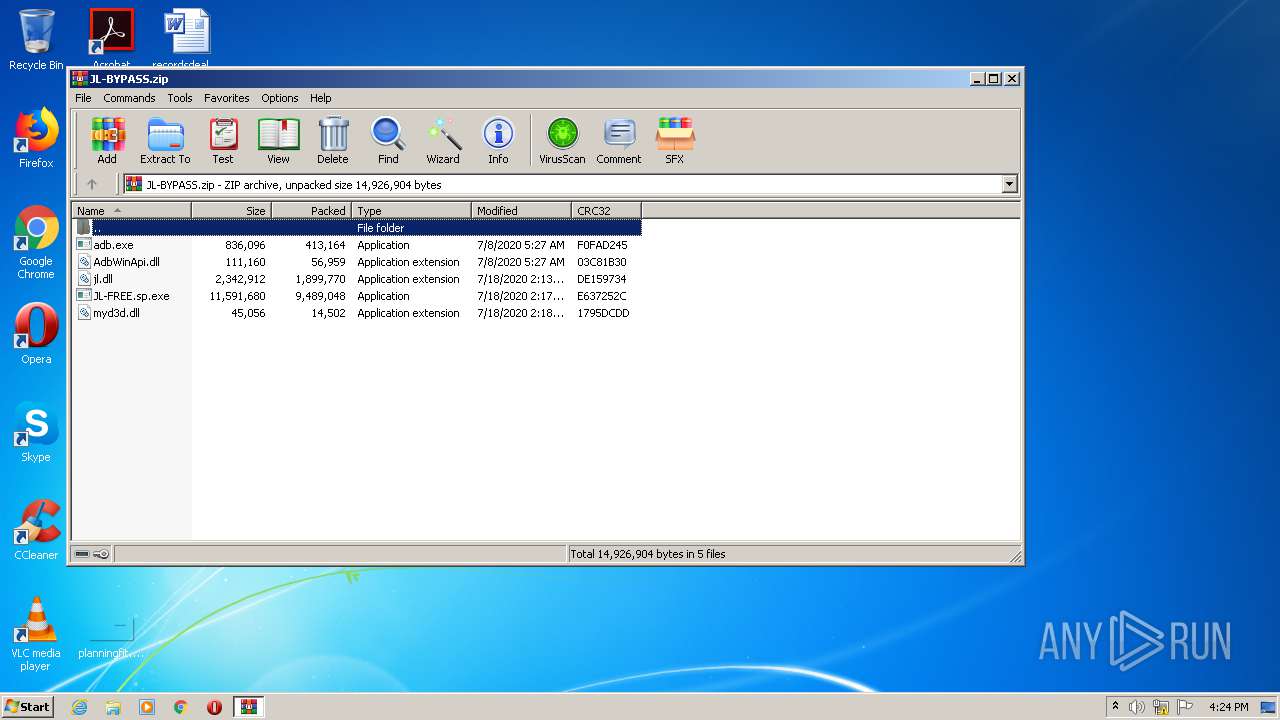
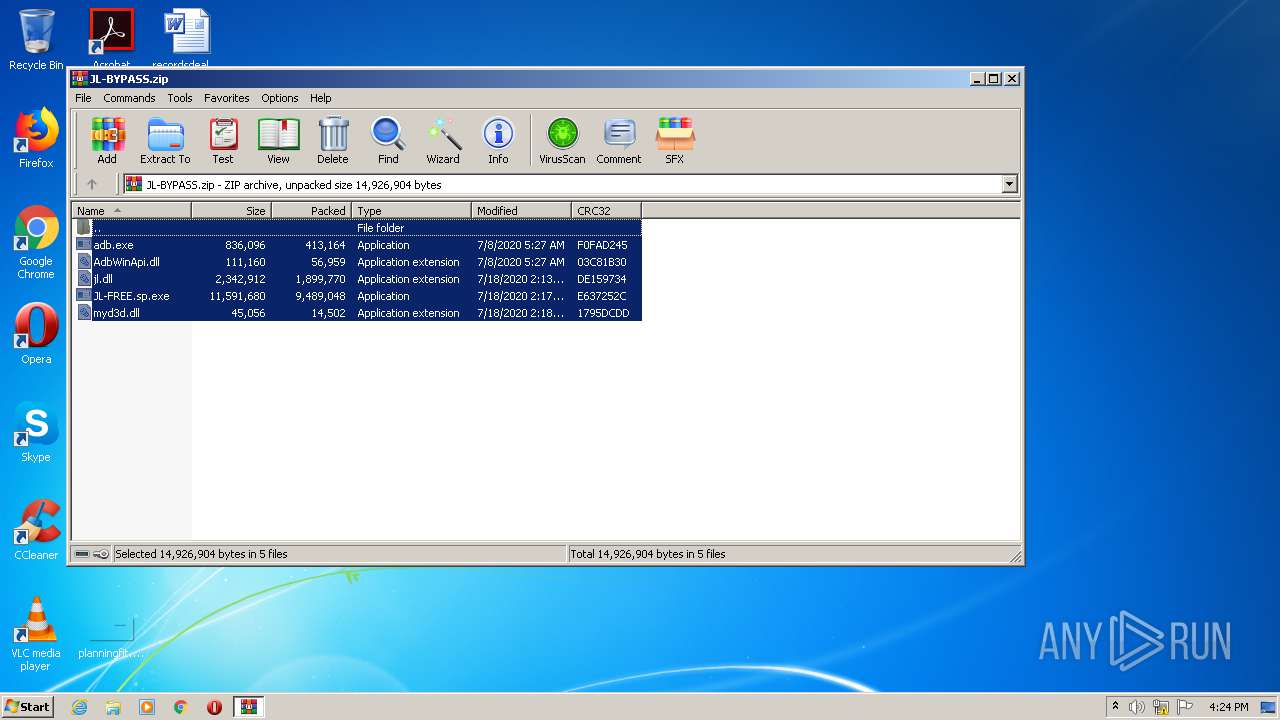
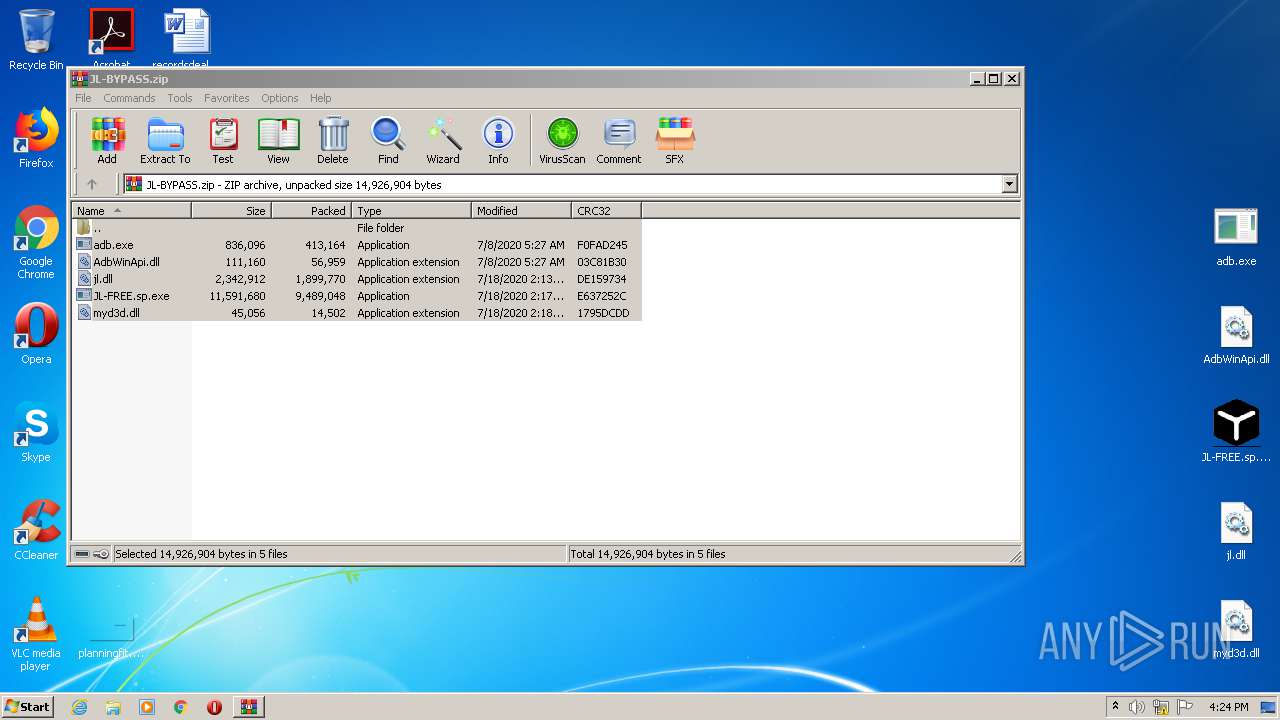
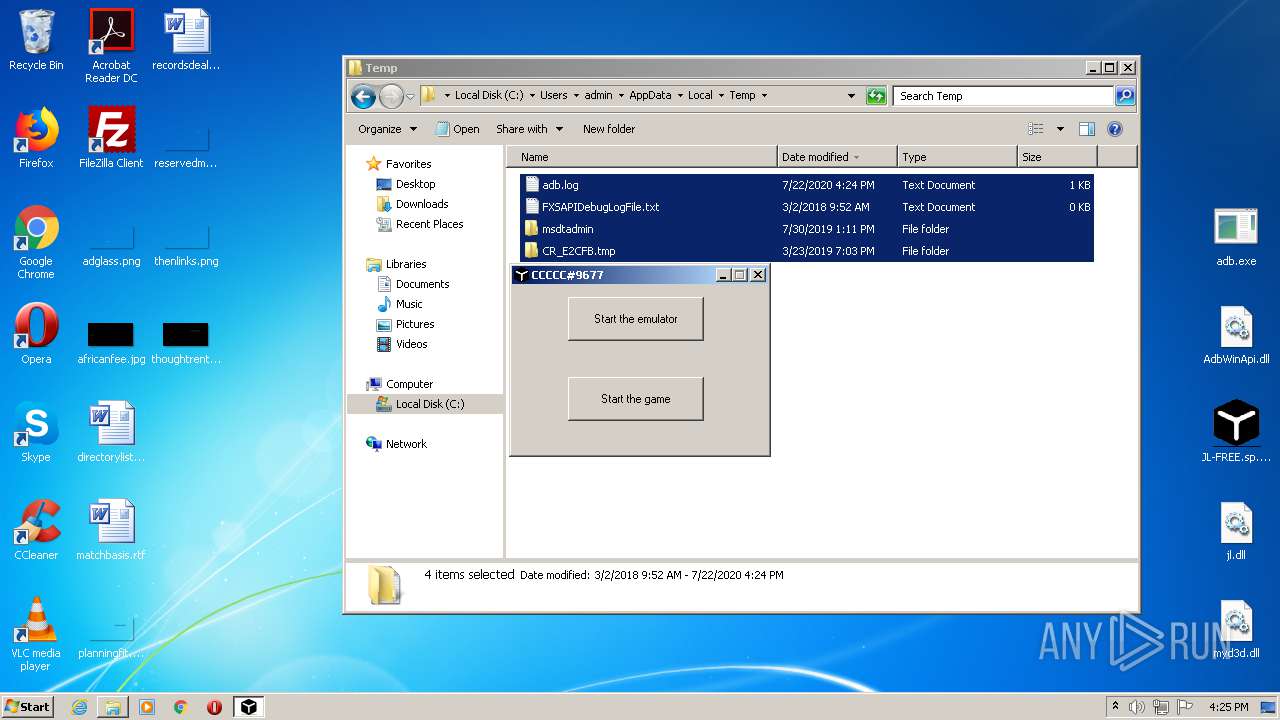
| File name: | JL-BYPASS.zip |
| Full analysis: | https://app.any.run/tasks/1cf73d91-7be6-46c7-a4b5-443dc72348e0 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | July 22, 2020, 15:23:31 |
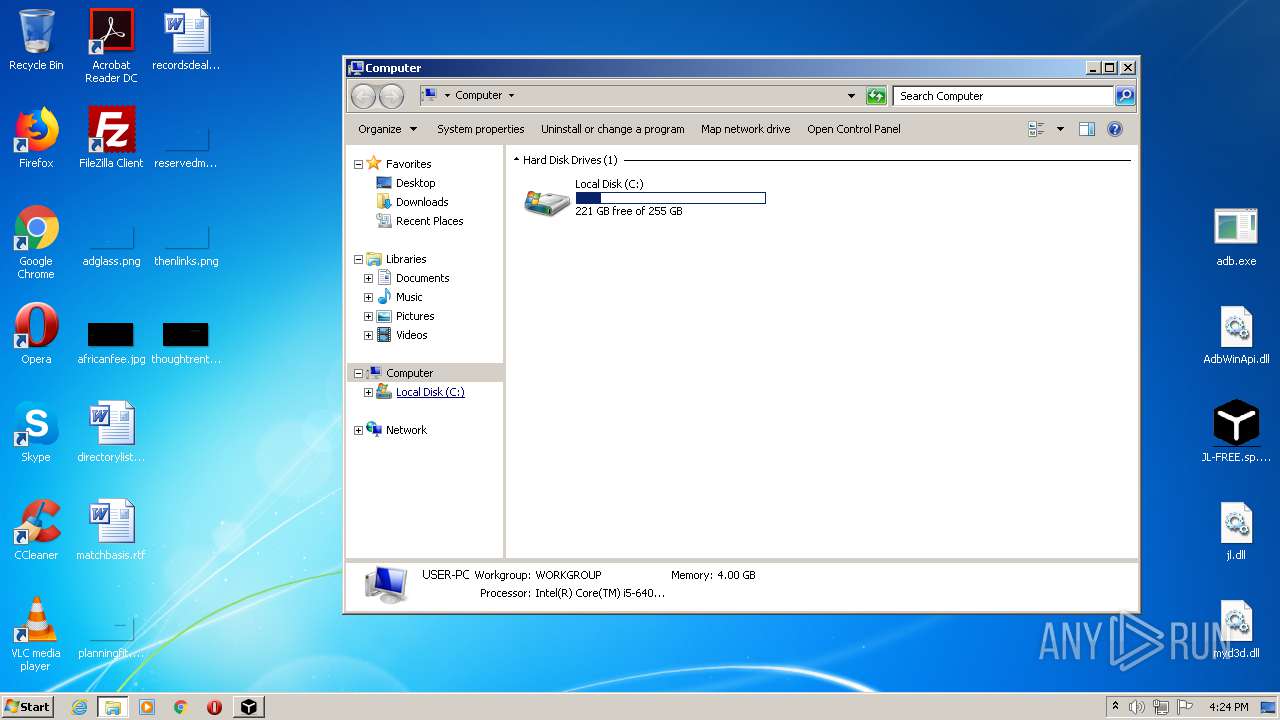
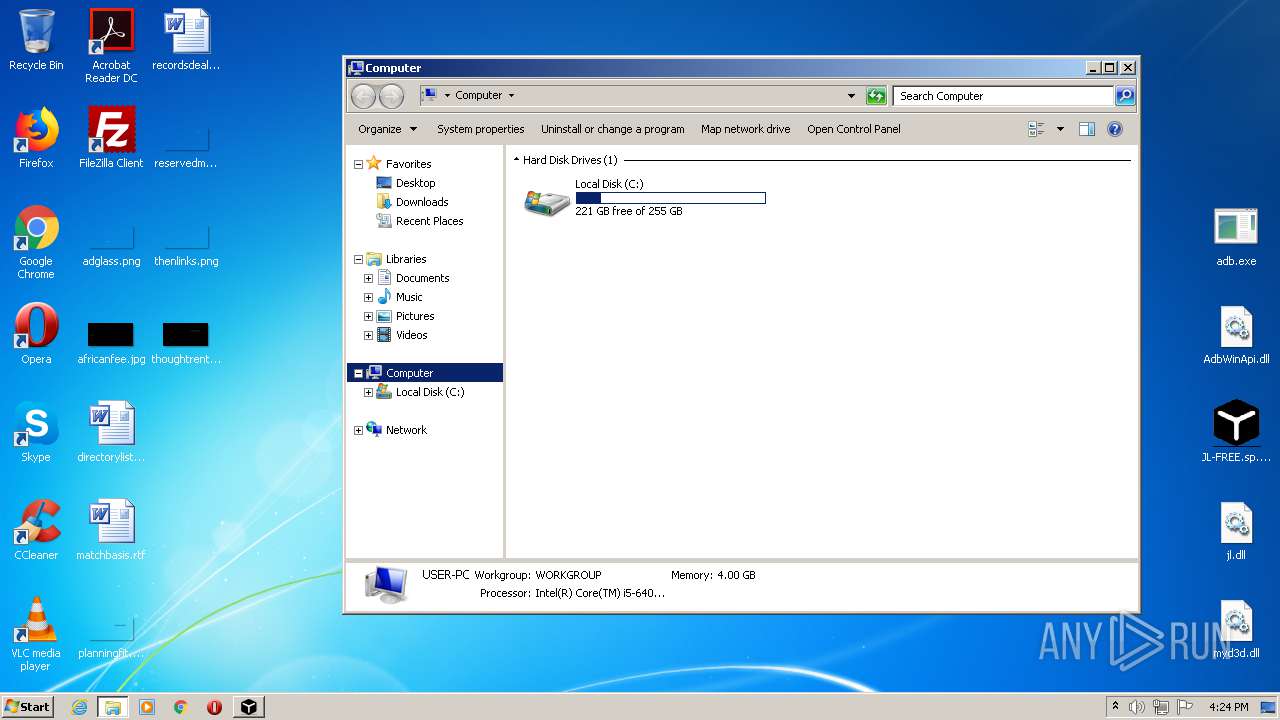
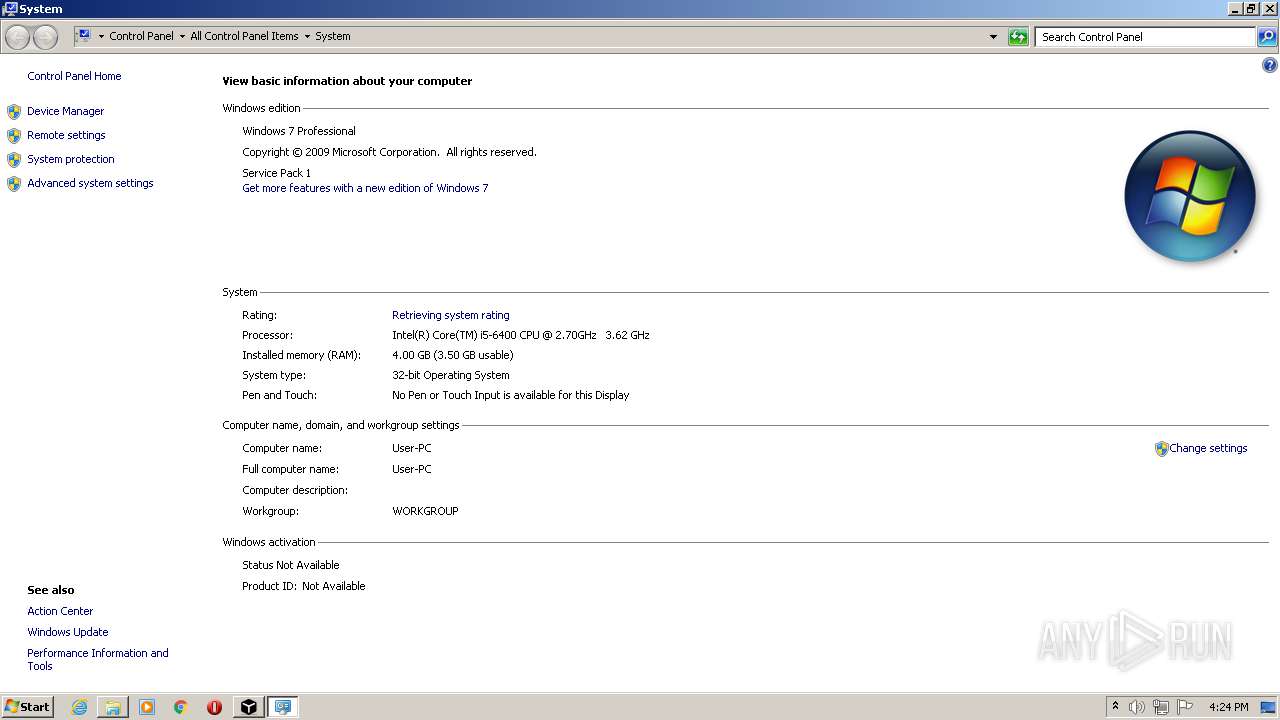
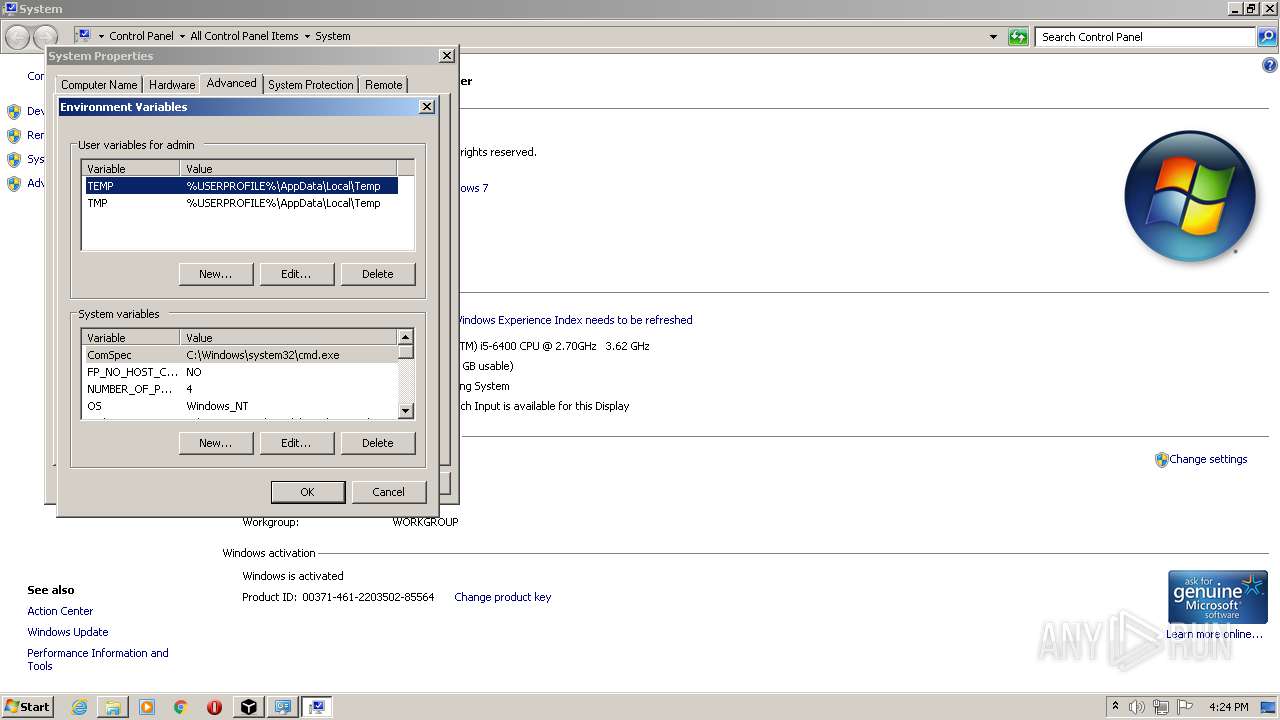
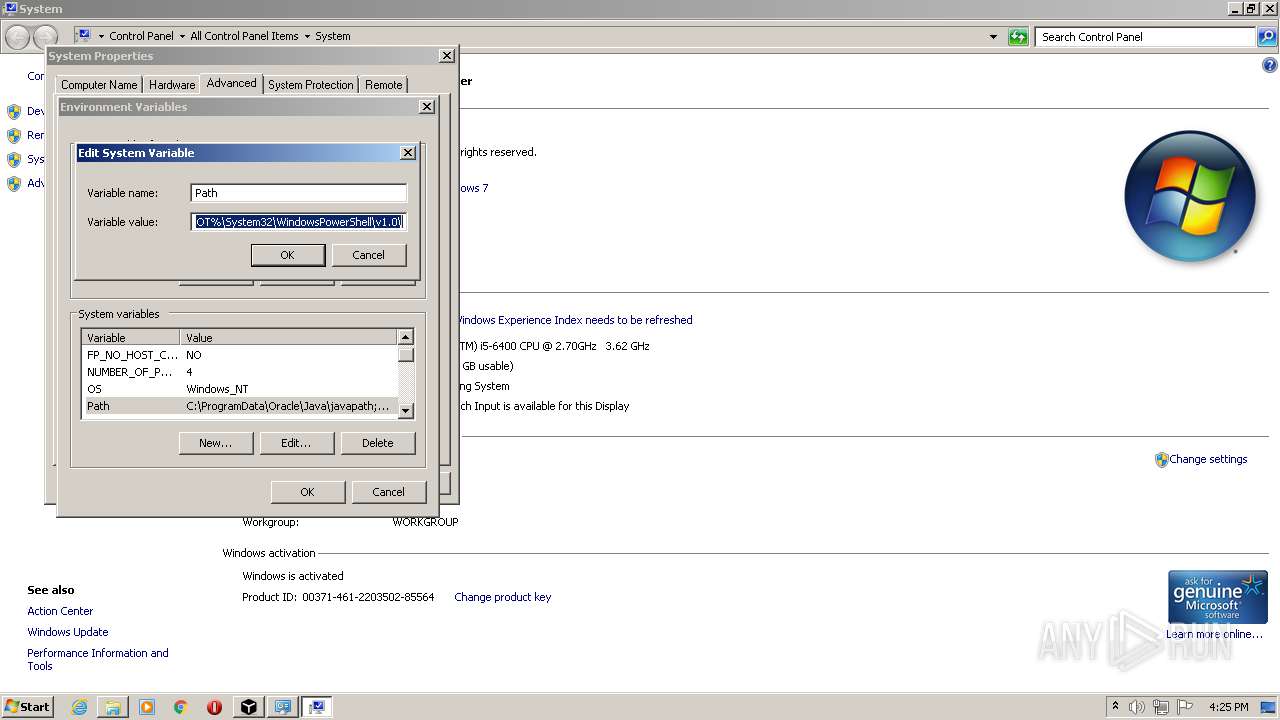
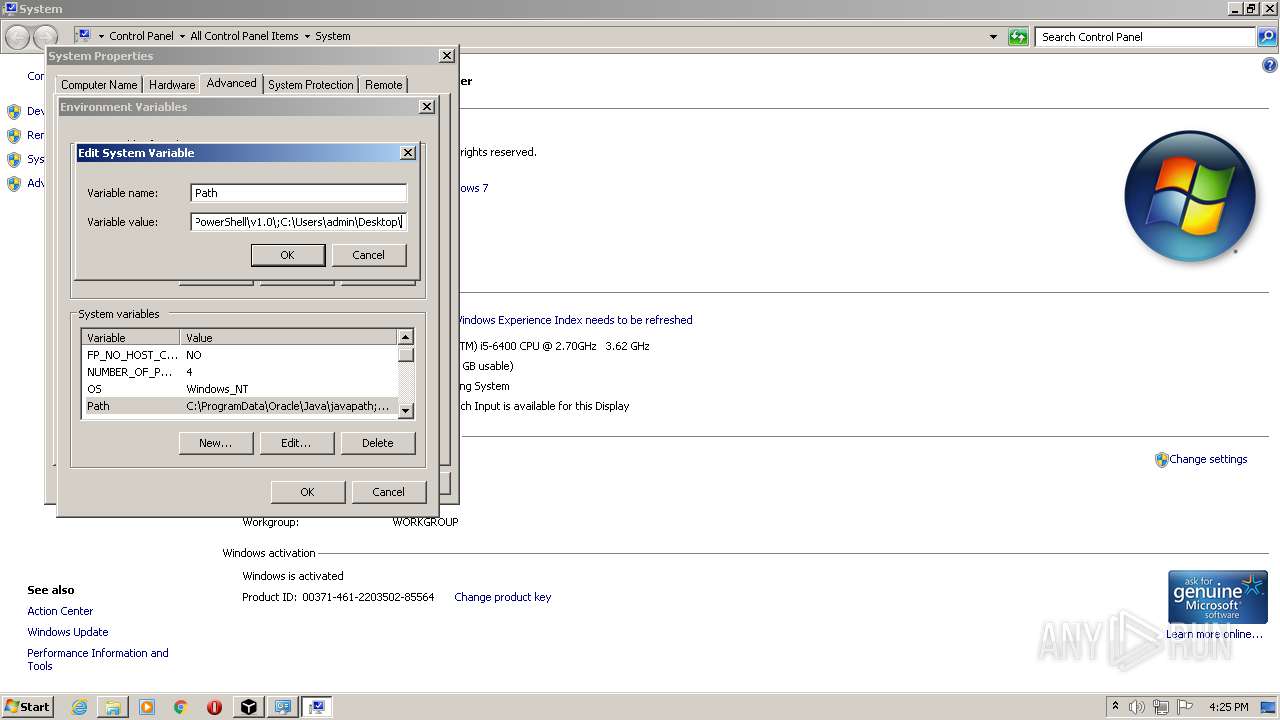
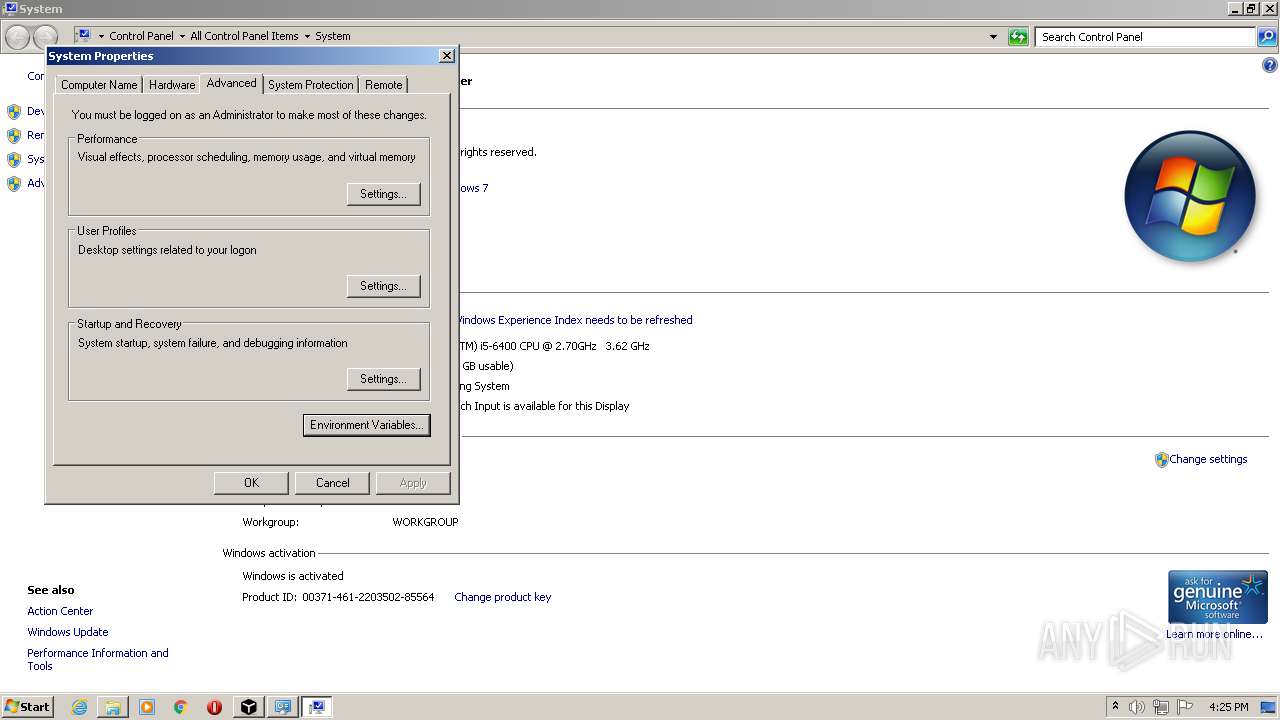
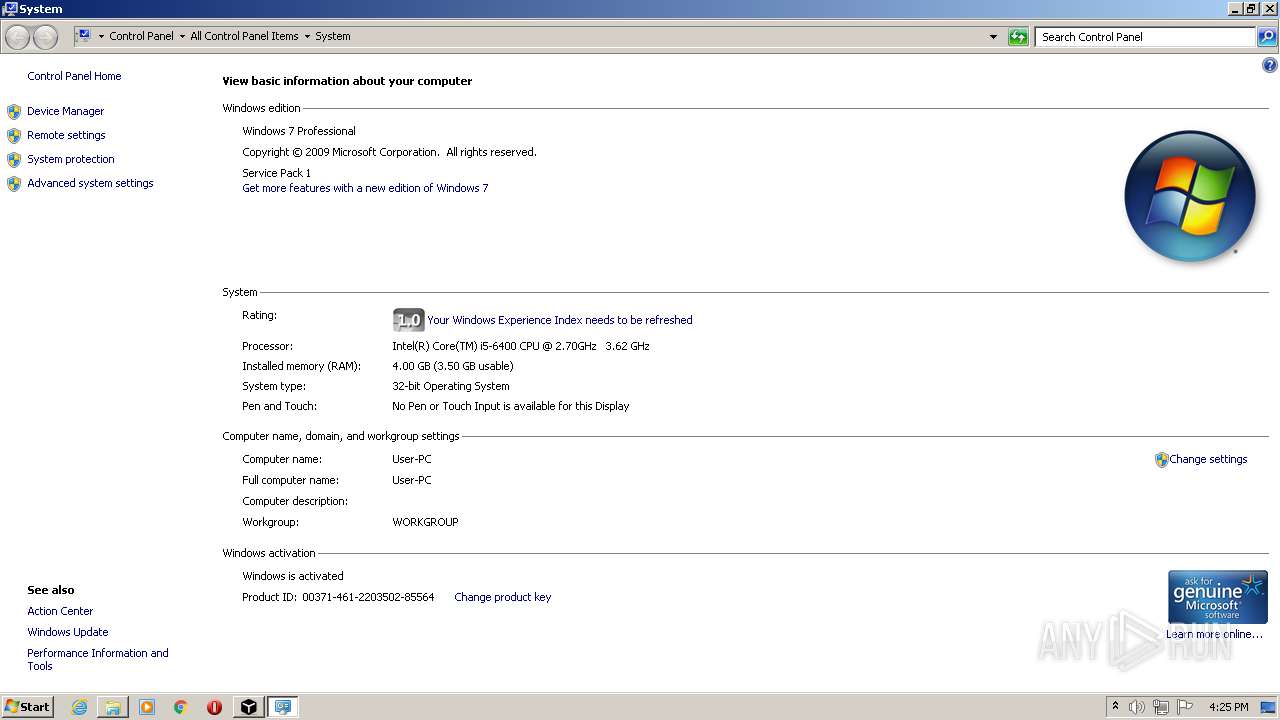
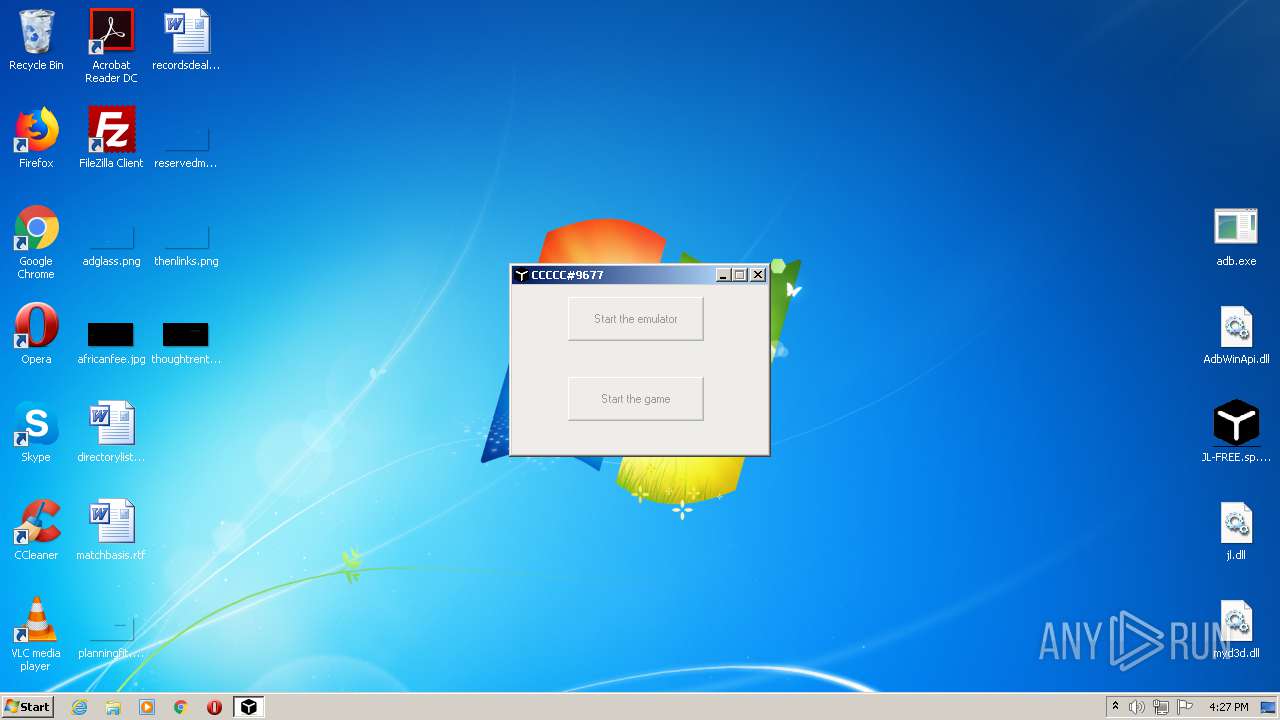
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | B7CB8ACBCE87AD53EA0E43246508CC1D |
| SHA1: | D6D2A4510367A5B49F53C764C3A33133C6CF4955 |
| SHA256: | B704016773C976B53C6A8B57C183FC8D5254BFB4E8D597C1E87C89C980F8D8B1 |
| SSDEEP: | 196608:38HTnY3vl1rIgAi0iza/v0/RJnnd0YXiKp3TwQDGxNZFVaqZ1n3vkd9GG:38H7Y3N1cziq/vSvnd0YSK9Tc9FVau8x |
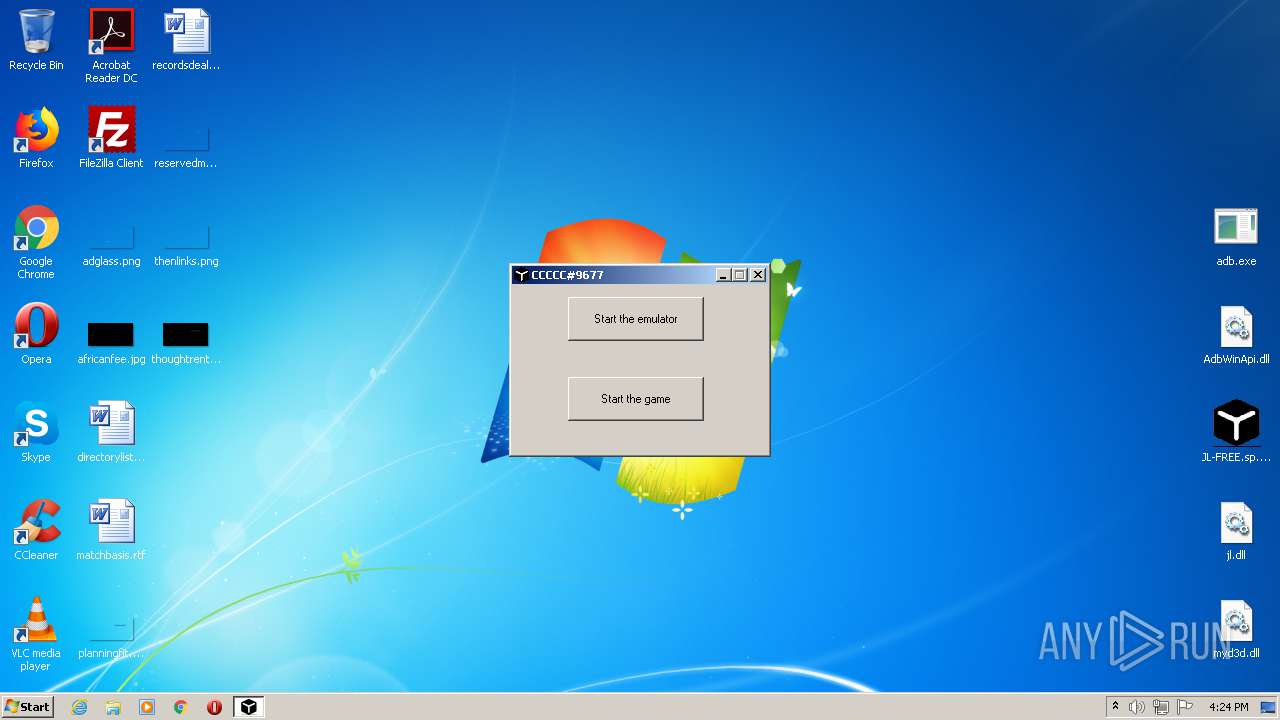
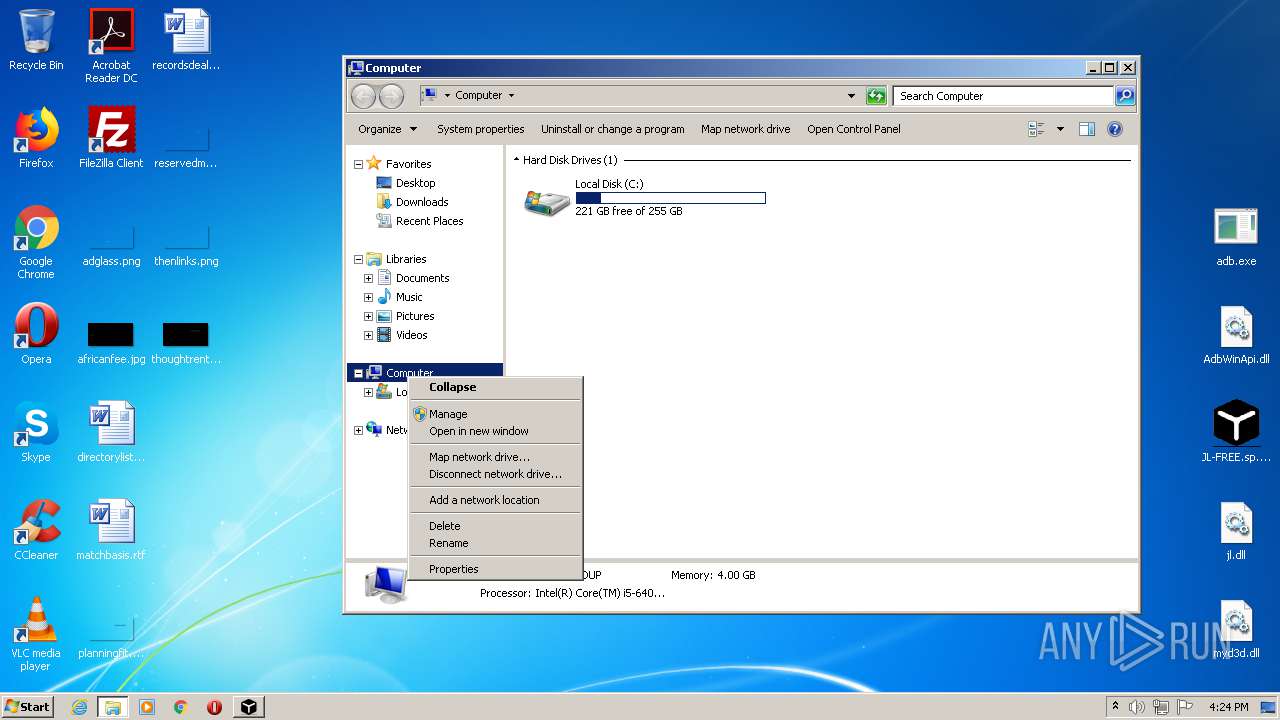
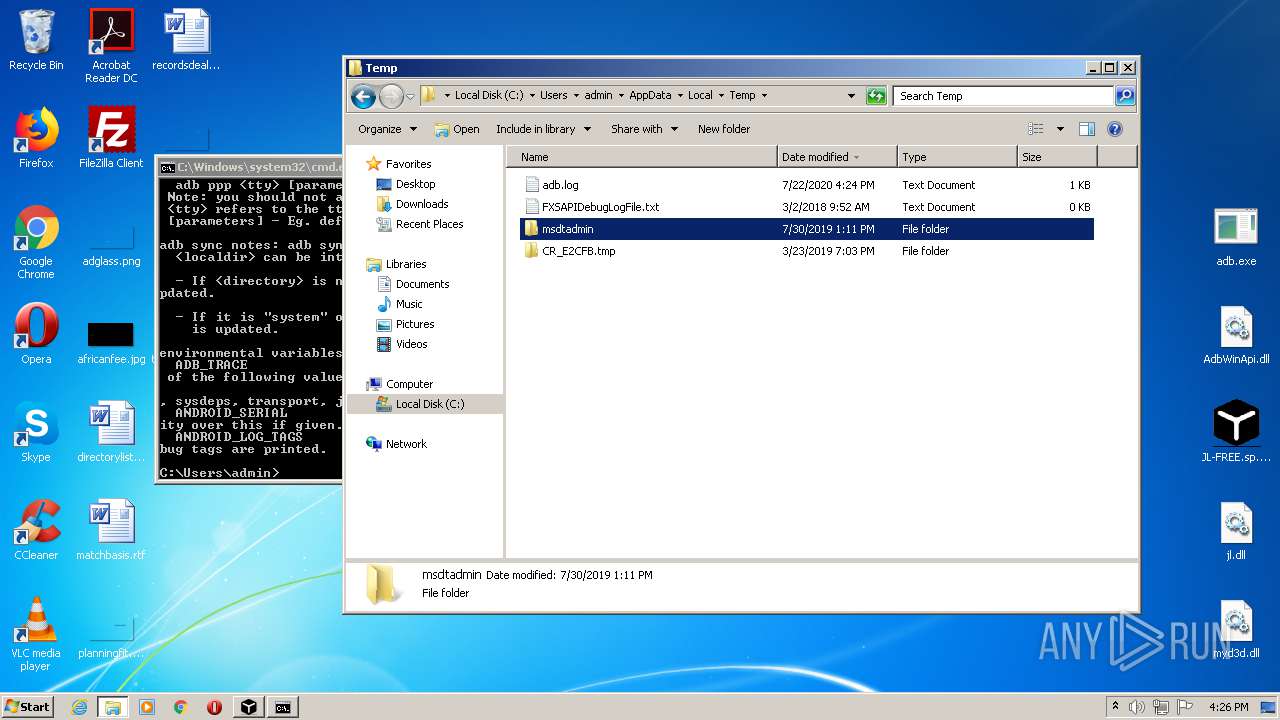
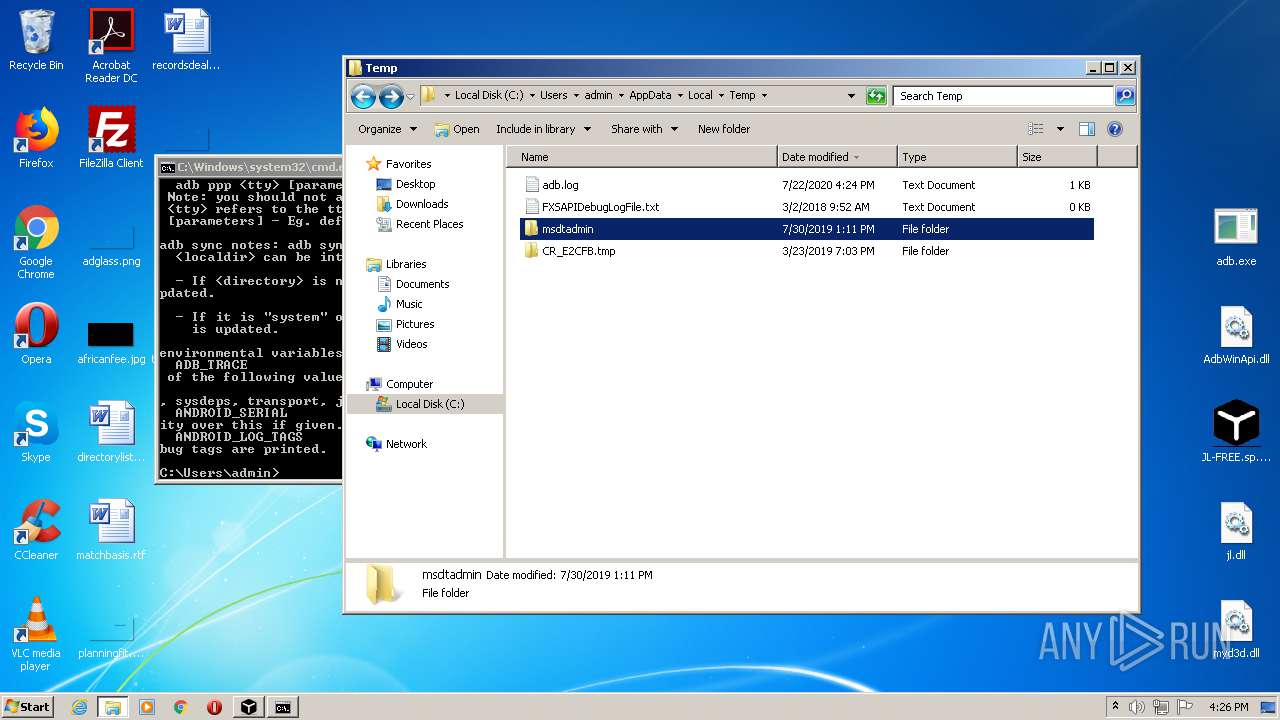
MALICIOUS
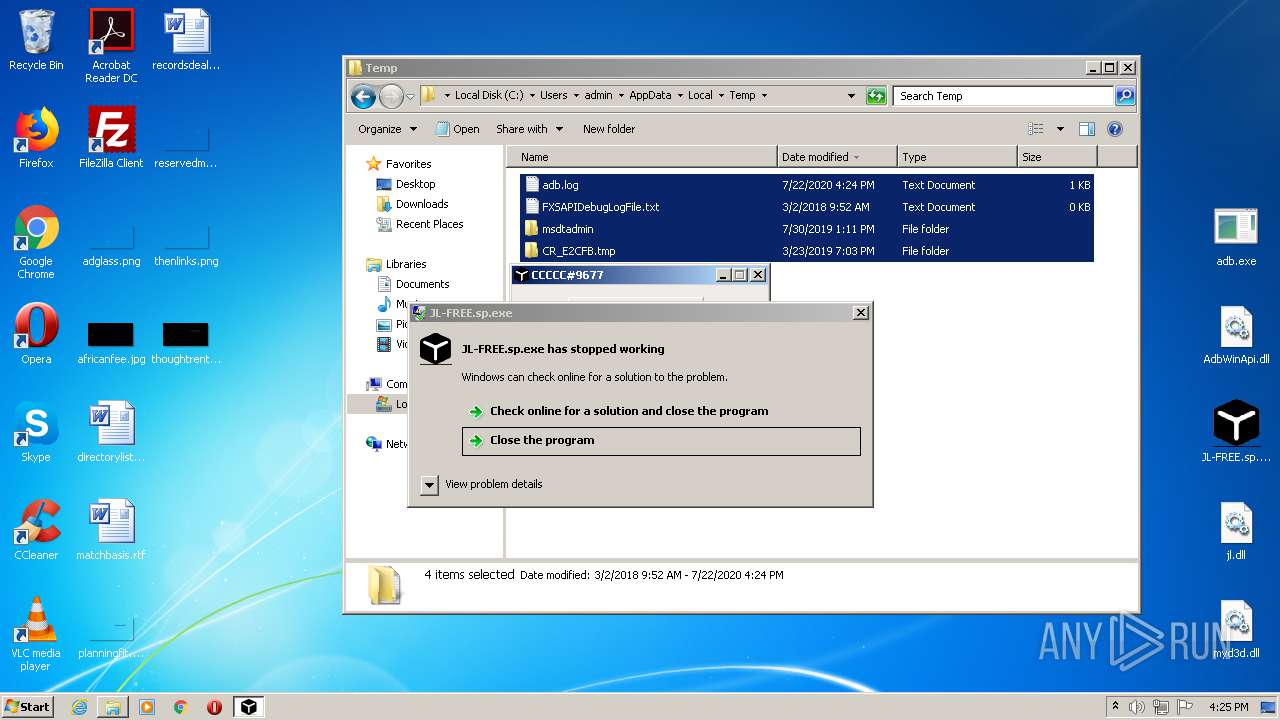
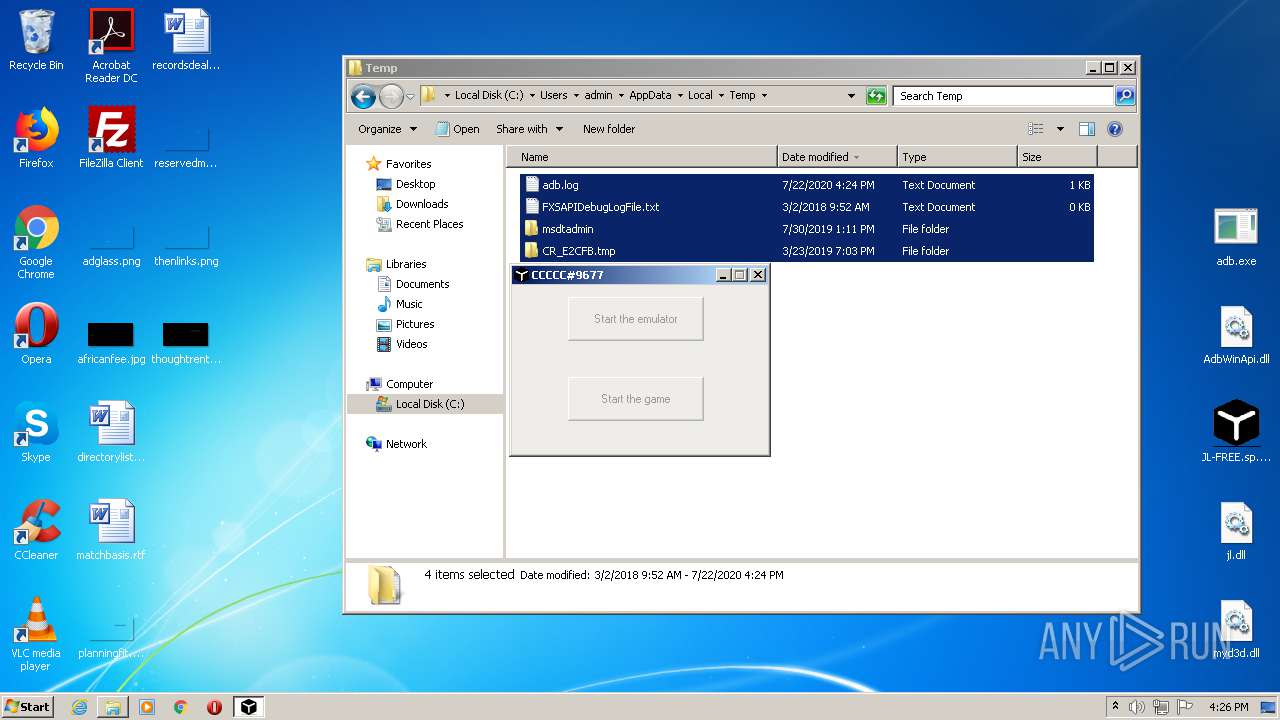
Application was dropped or rewritten from another process
- JL-FREE.sp.exe (PID: 2104)
- msm.exe (PID: 3012)
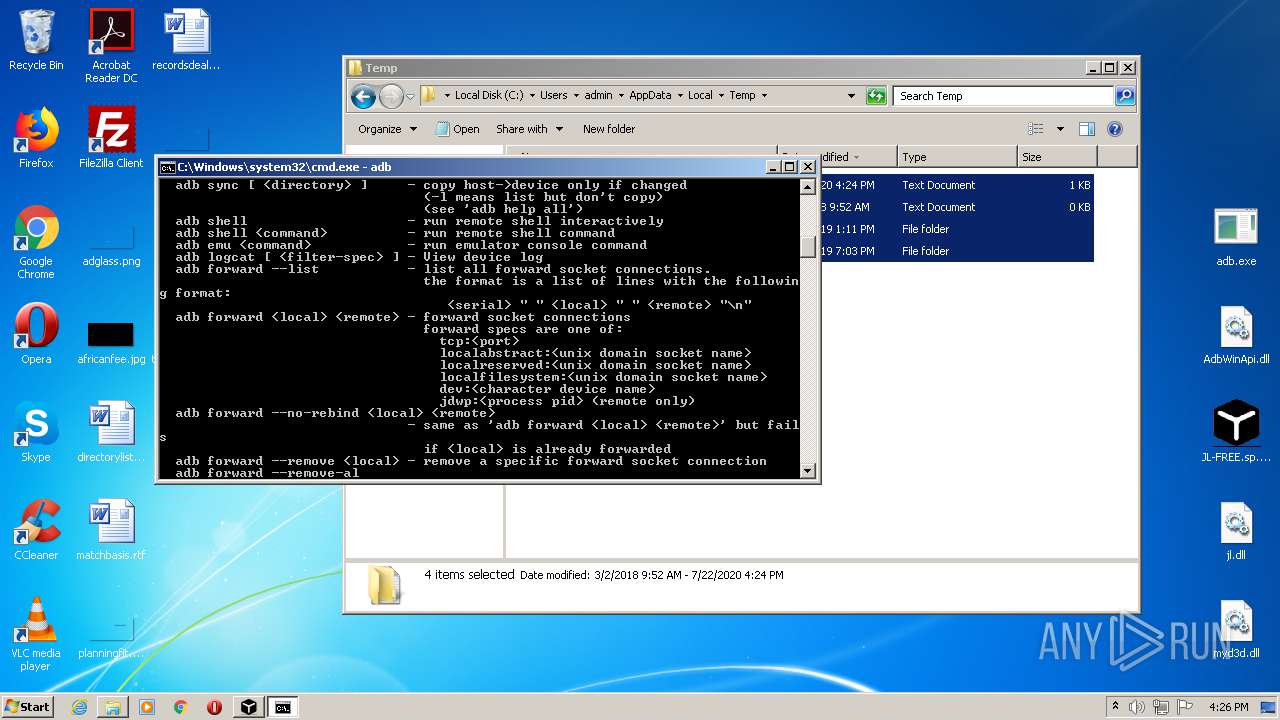
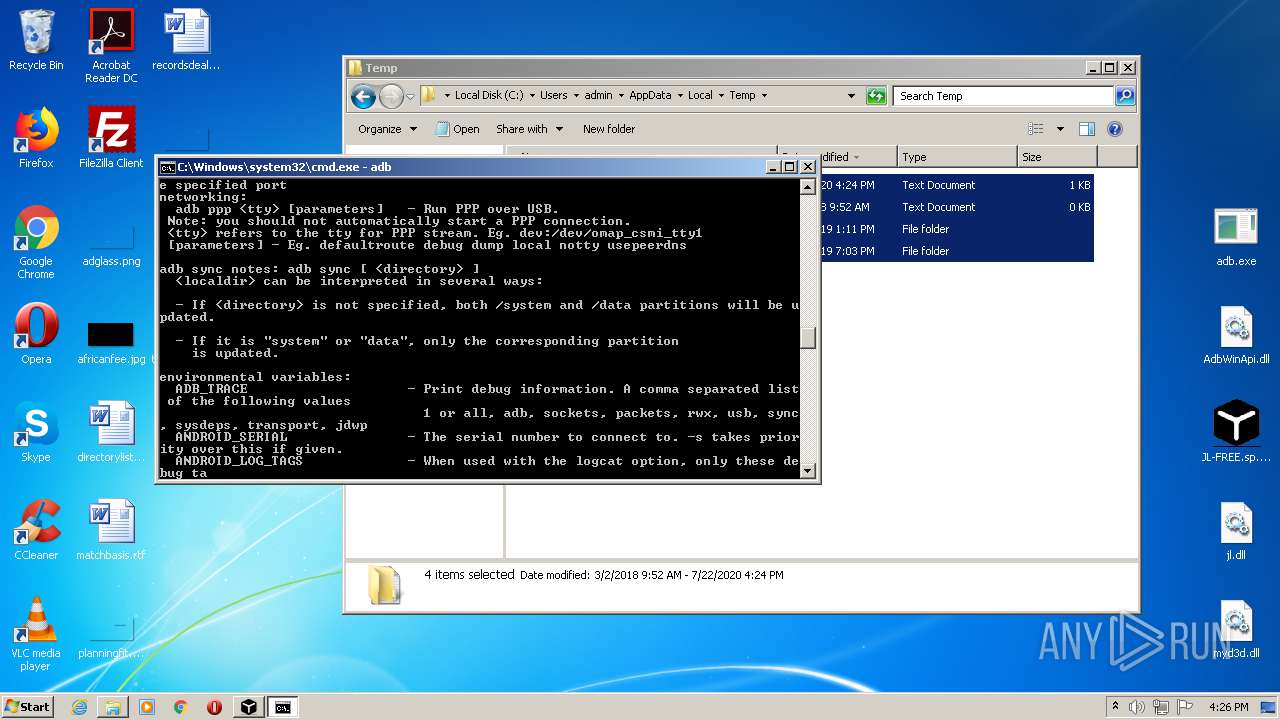
- adb.exe (PID: 2400)
- hxQzrZ.exe (PID: 3124)
- adb.exe (PID: 1844)
- hxQzrZ.exe (PID: 3236)
- adb.exe (PID: 3392)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3928)
- JL-FREE.sp.exe (PID: 2104)
- explorer.exe (PID: 392)
- adb.exe (PID: 2400)
- adb.exe (PID: 1844)
- adb.exe (PID: 3392)
Connects to CnC server
- wuapp.exe (PID: 2540)
- wuapp.exe (PID: 2716)
MINER was detected
- wuapp.exe (PID: 2540)
- wuapp.exe (PID: 2716)
Writes to a start menu file
- wscript.exe (PID: 2784)
Runs app for hidden code execution
- explorer.exe (PID: 392)
Actions looks like stealing of personal data
- explorer.exe (PID: 392)
SUSPICIOUS
Executable content was dropped or overwritten
- explorer.exe (PID: 392)
- WinRAR.exe (PID: 2856)
- JL-FREE.sp.exe (PID: 2104)
- adb.exe (PID: 2400)
- msm.exe (PID: 3012)
- adb.exe (PID: 1844)
Reads Internet Cache Settings
- msm.exe (PID: 3012)
- hxQzrZ.exe (PID: 3124)
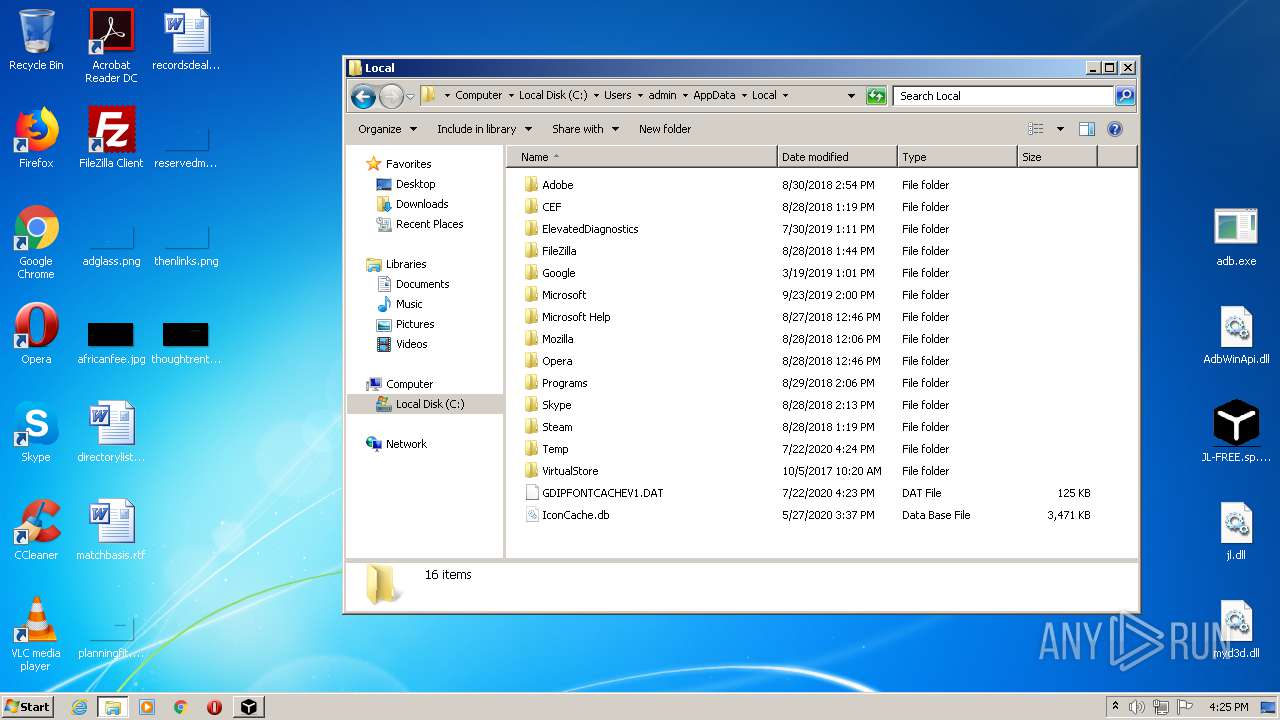
Creates files in the program directory
- msm.exe (PID: 3012)
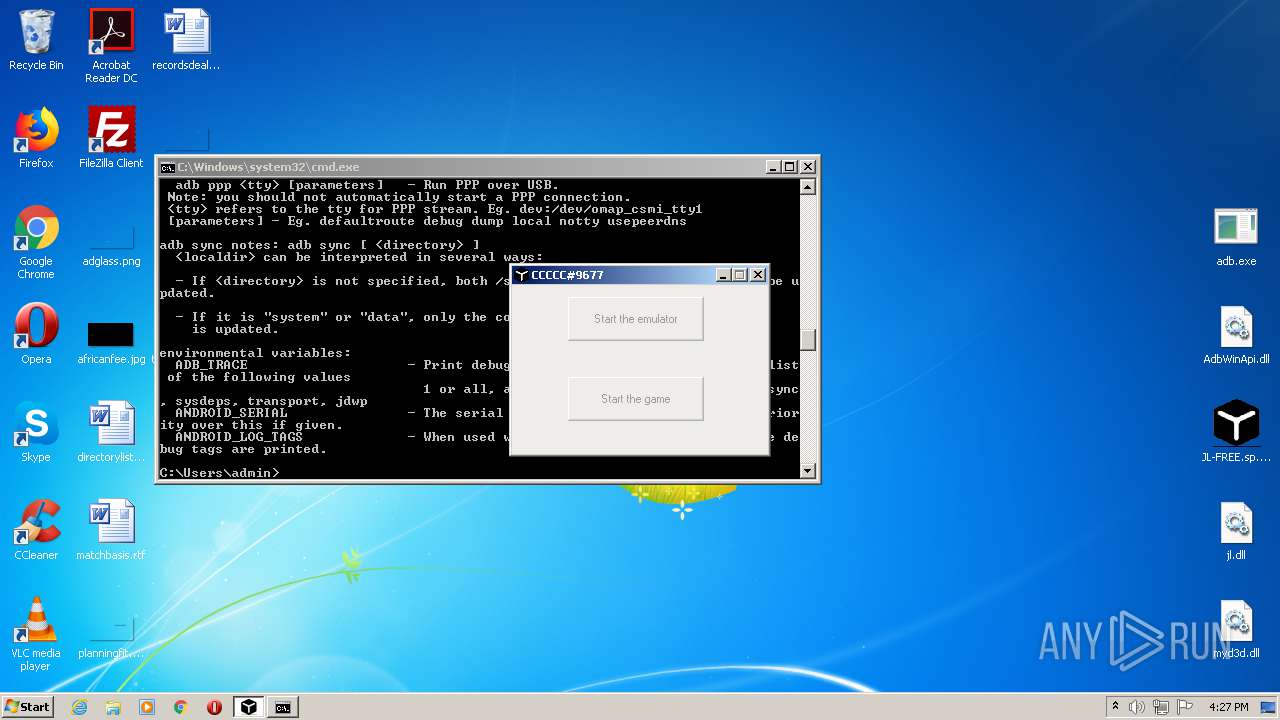
Application launched itself
- adb.exe (PID: 2400)
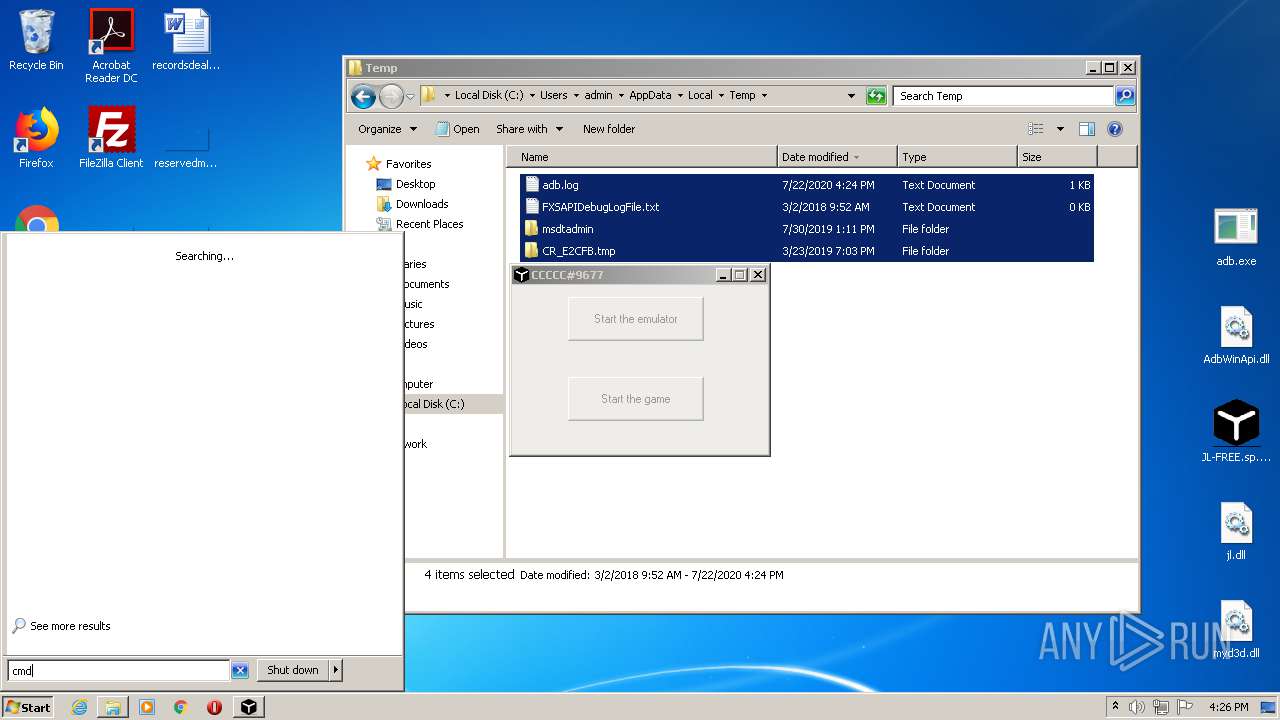
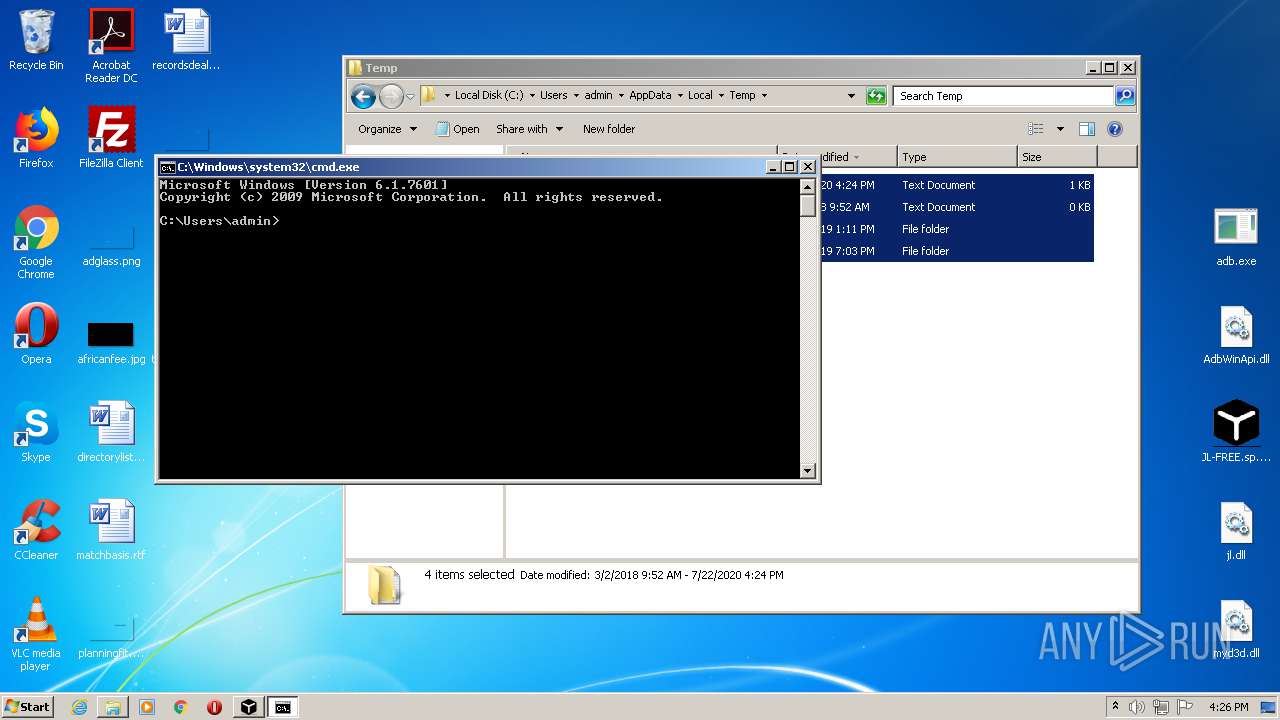
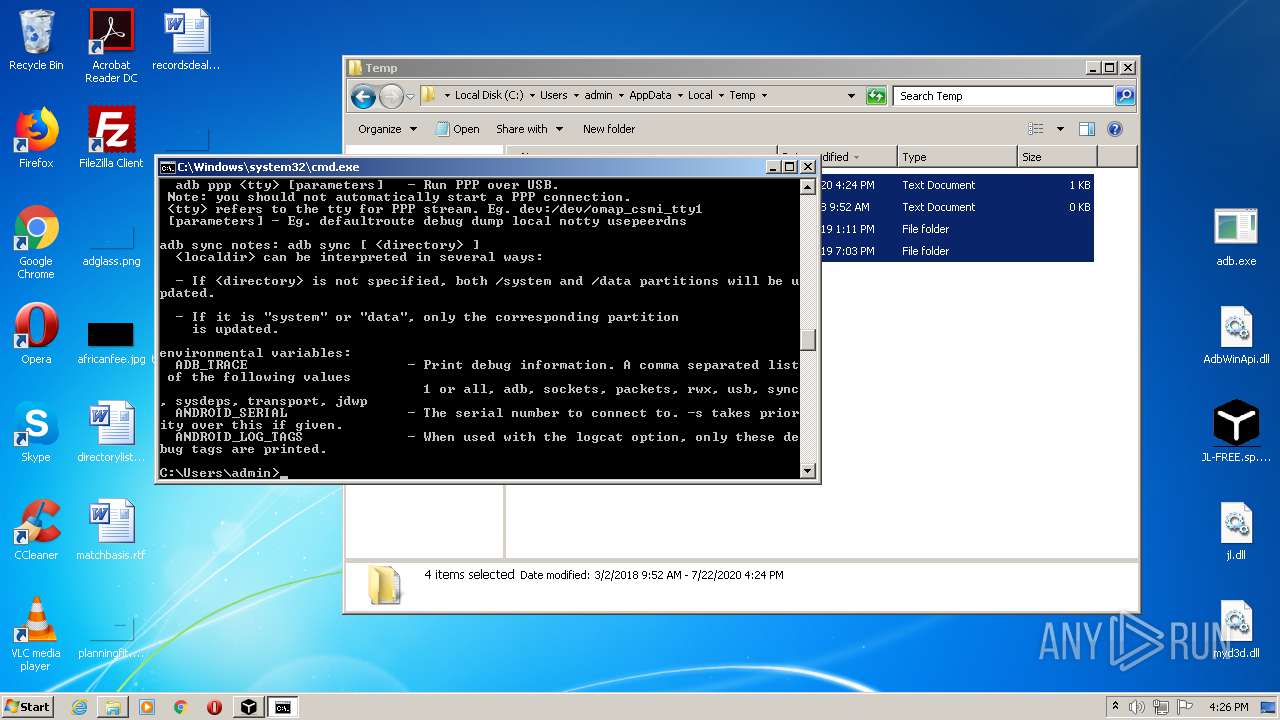
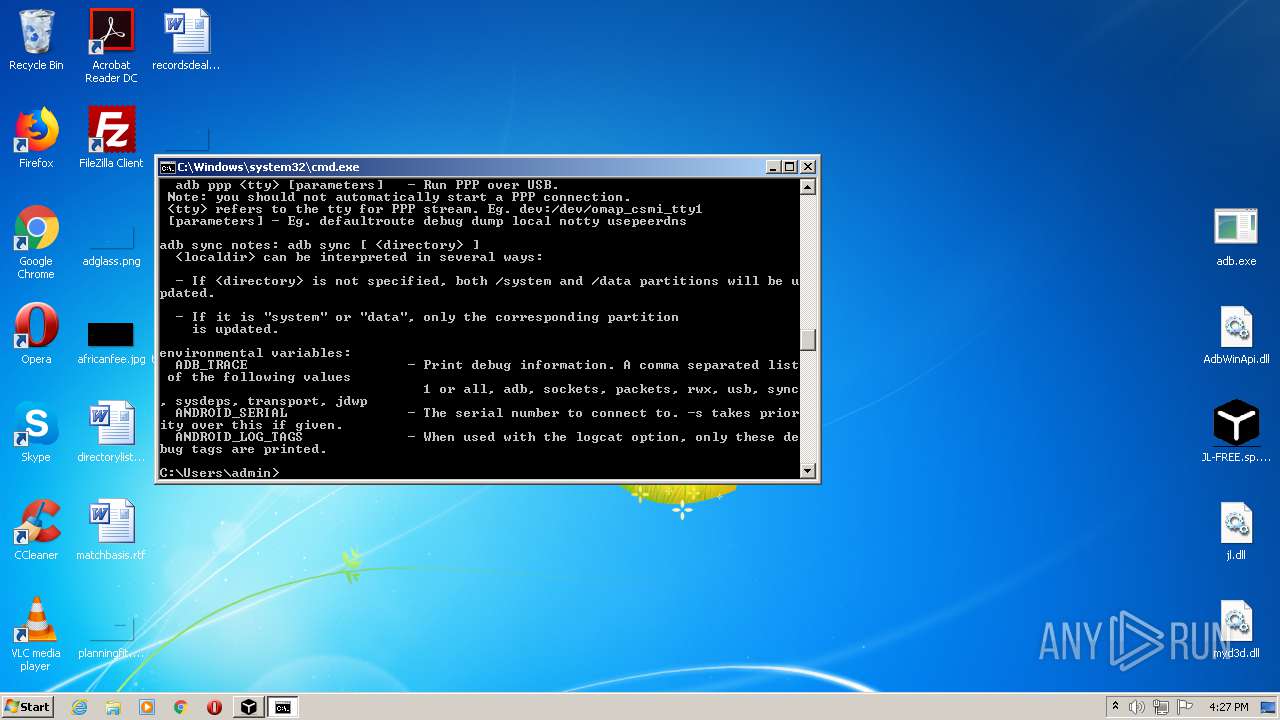
Starts CMD.EXE for commands execution
- hxQzrZ.exe (PID: 3124)
- msm.exe (PID: 3012)
- explorer.exe (PID: 392)
- JL-FREE.sp.exe (PID: 2104)
- hxQzrZ.exe (PID: 3236)
Executes scripts
- cmd.exe (PID: 1848)
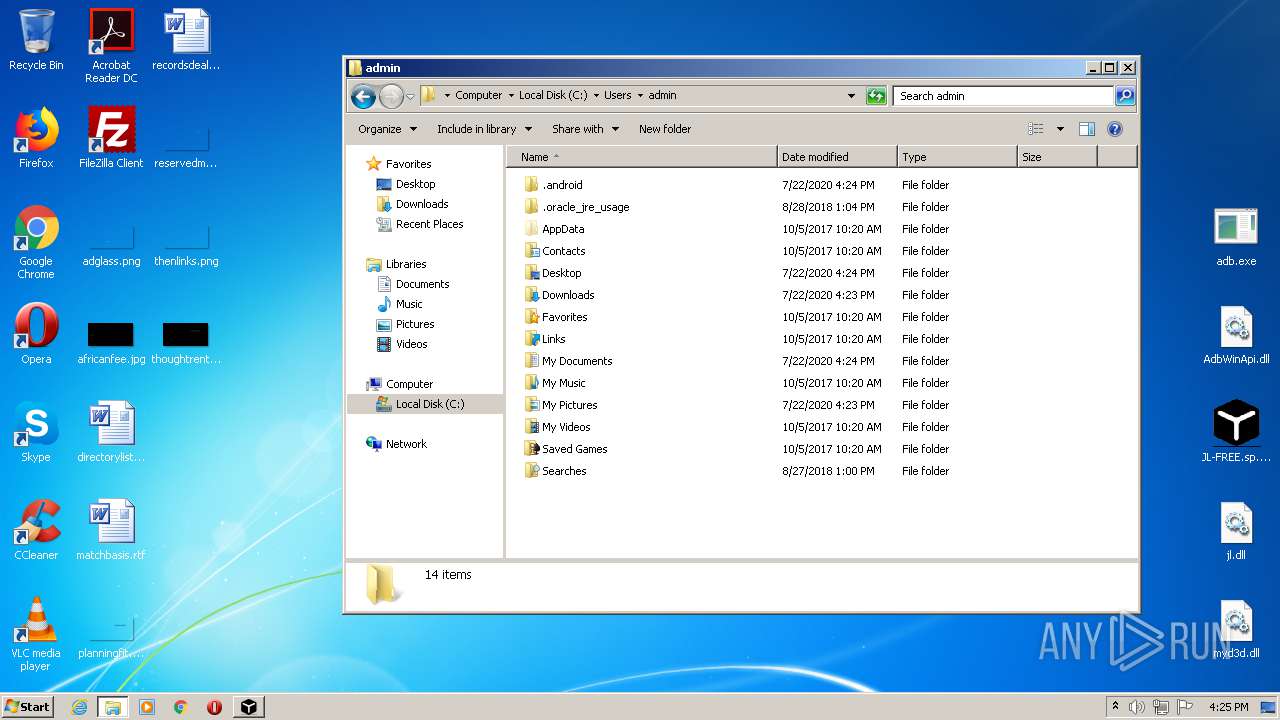
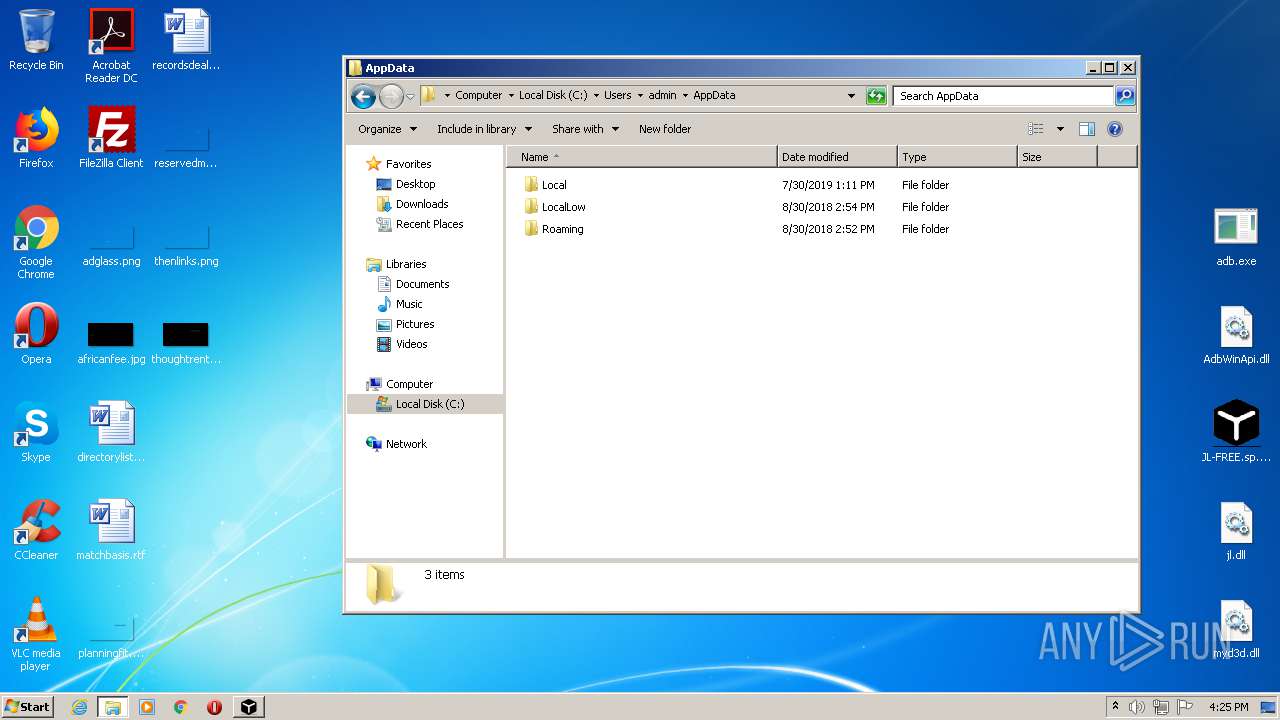
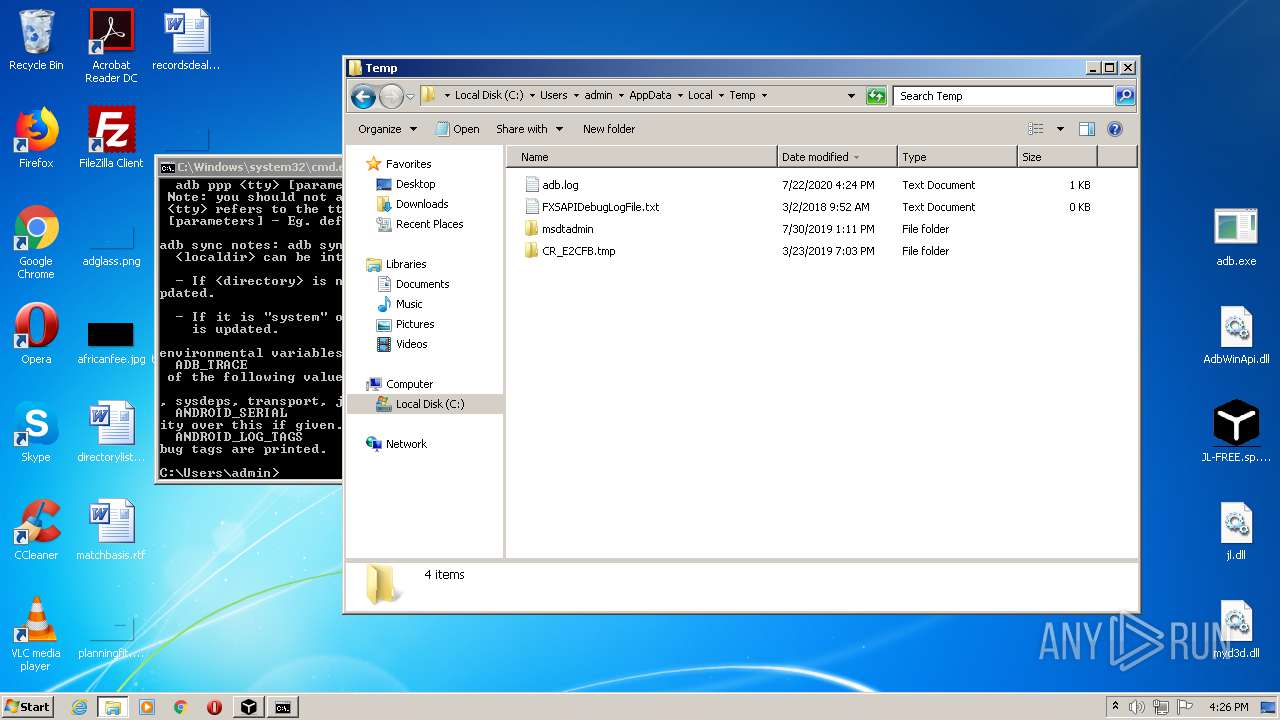
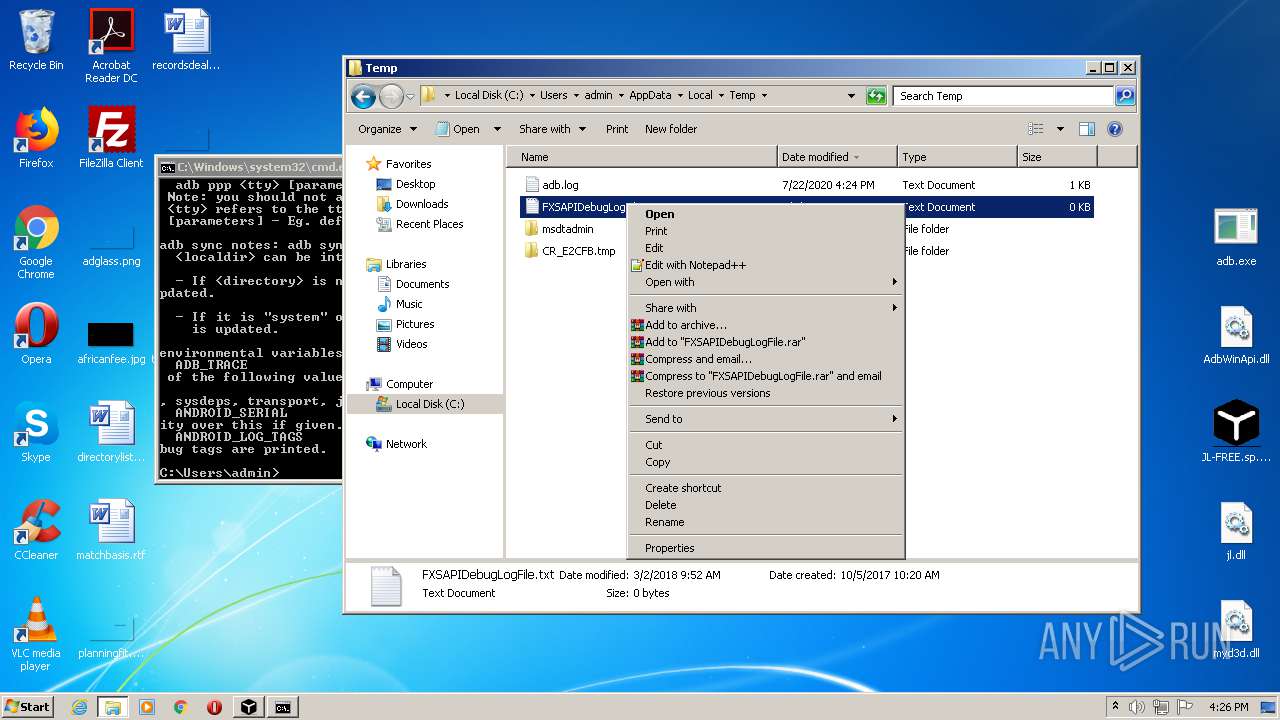
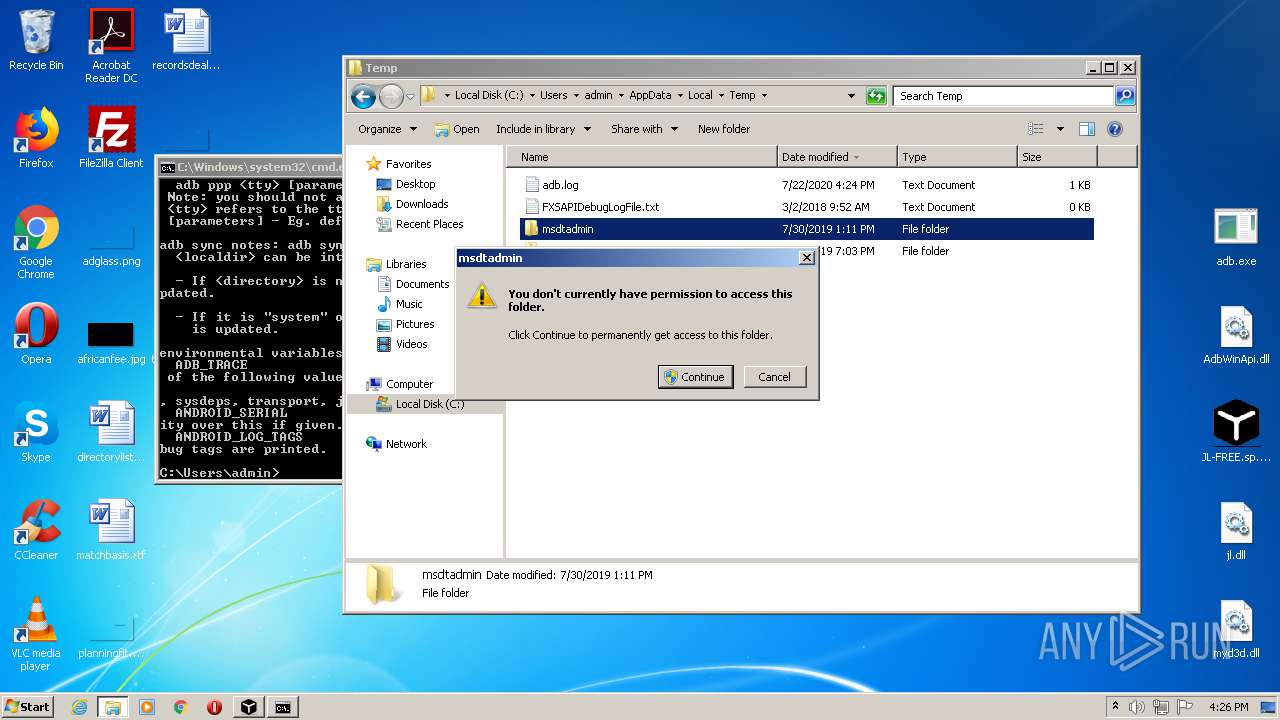
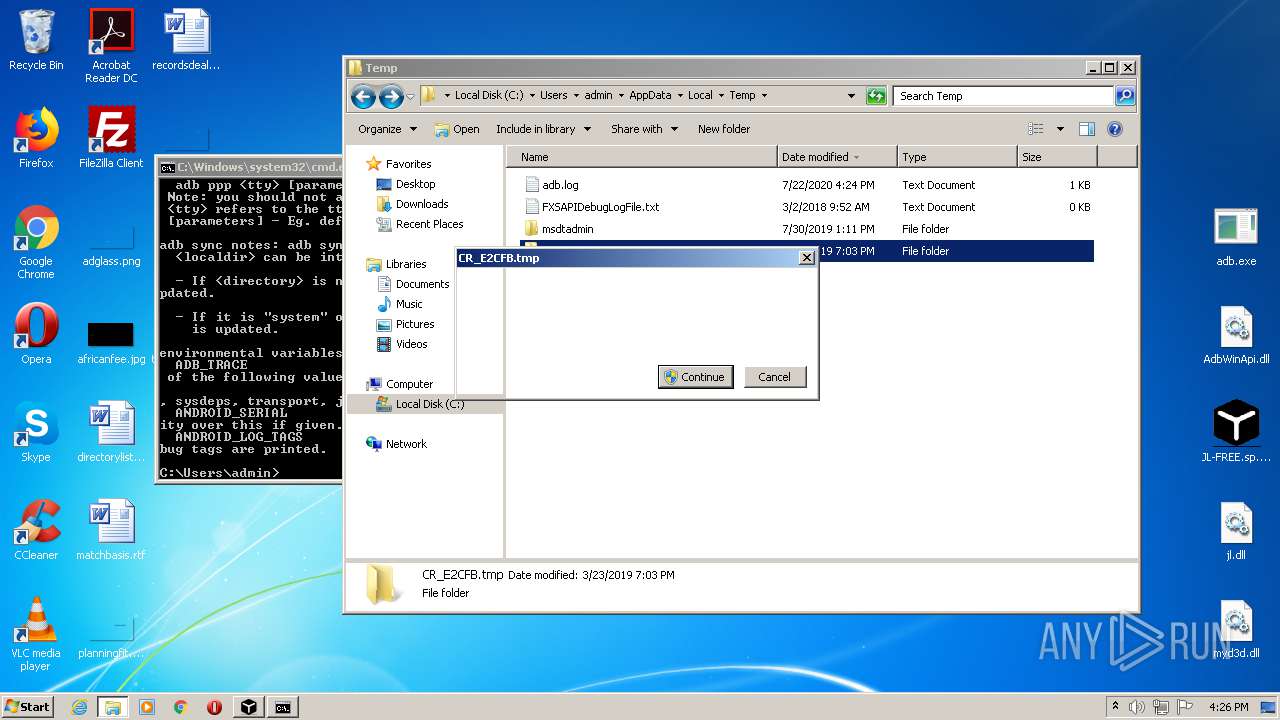
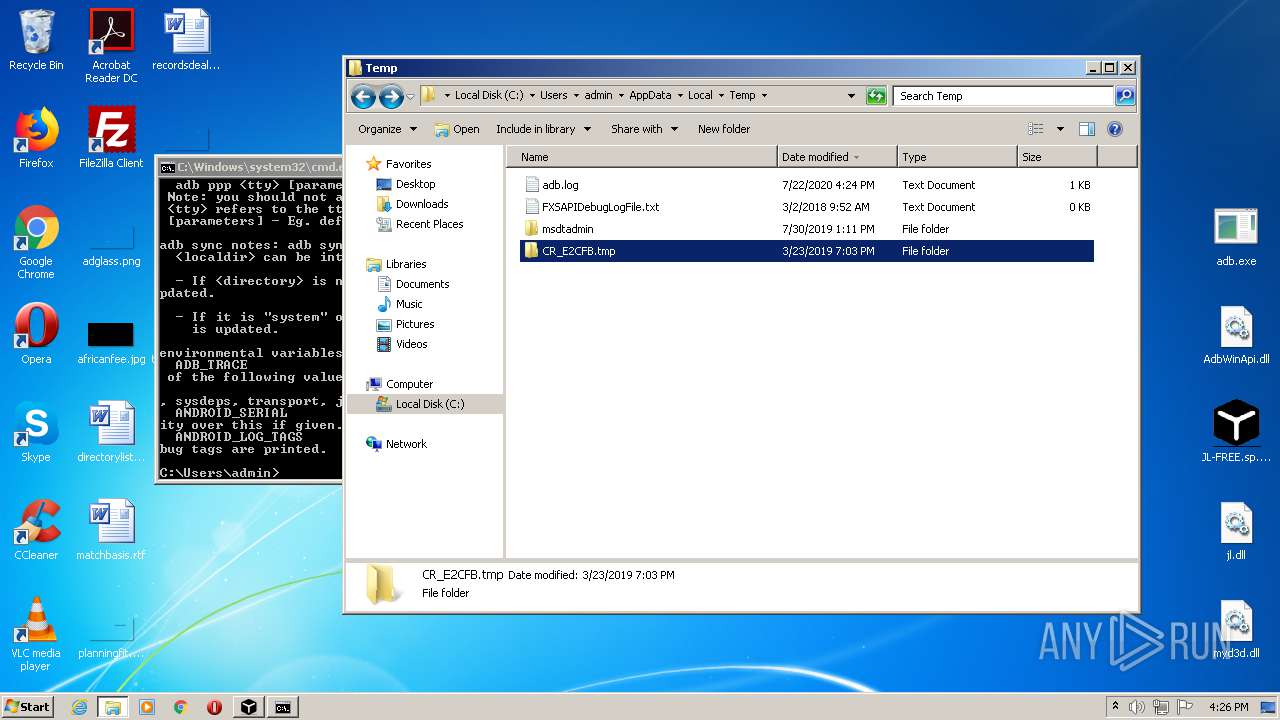
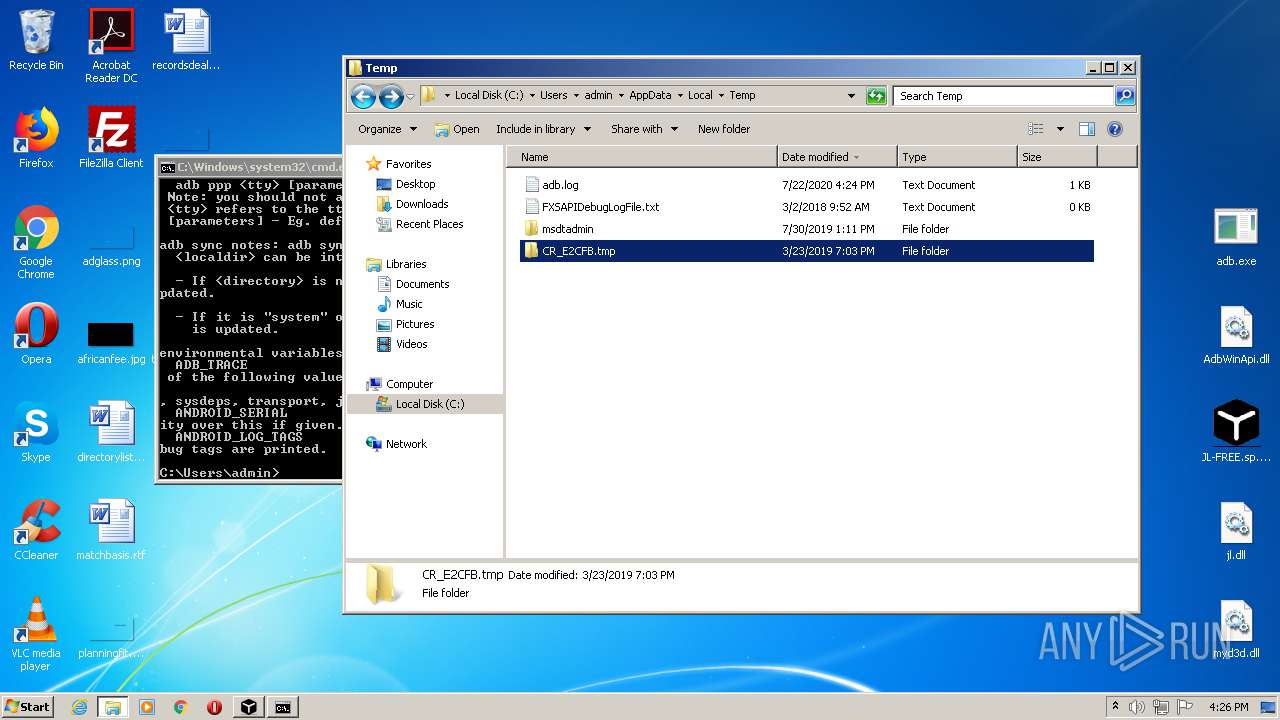
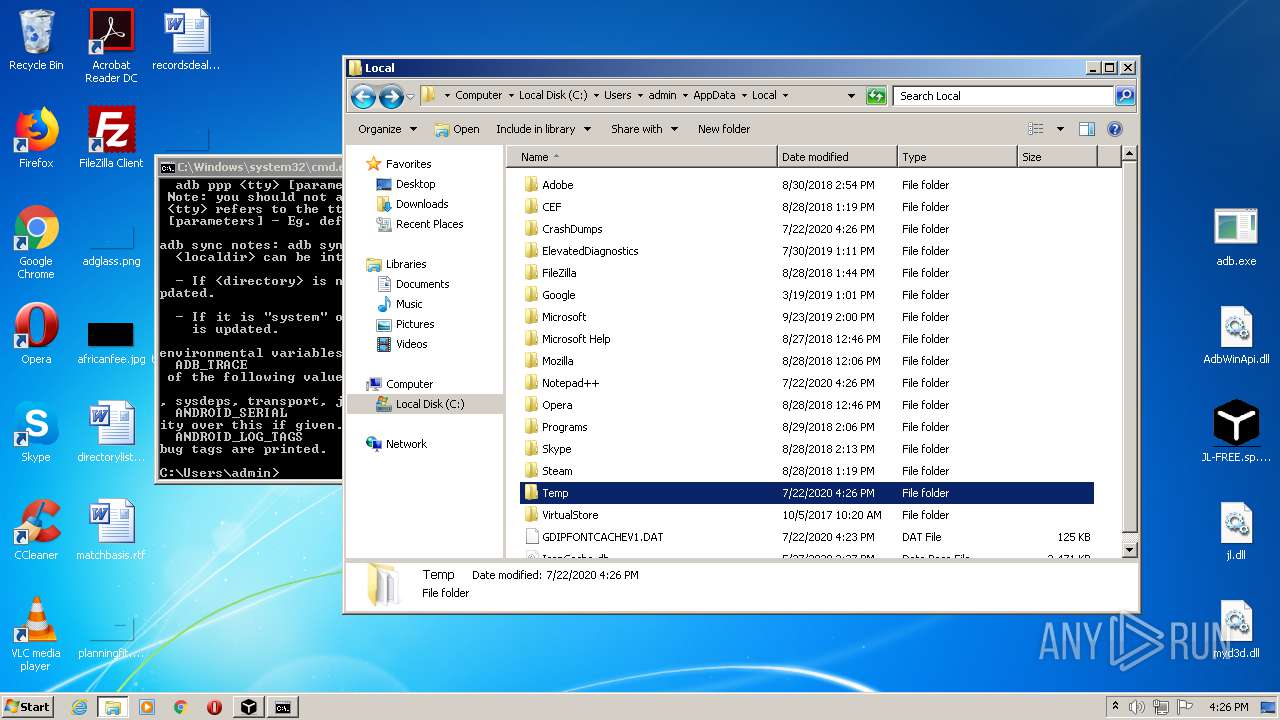
Creates files in the user directory
- explorer.exe (PID: 392)
- wscript.exe (PID: 2784)
- notepad++.exe (PID: 1004)
Executed via COM
- DllHost.exe (PID: 3852)
- DllHost.exe (PID: 3964)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:07:18 18:47:18 |
| ZipCRC: | 0xe637252c |
| ZipCompressedSize: | 9489048 |
| ZipUncompressedSize: | 11591680 |
| ZipFileName: | JL-FREE.sp.exe |
Total processes
83
Monitored processes
28
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
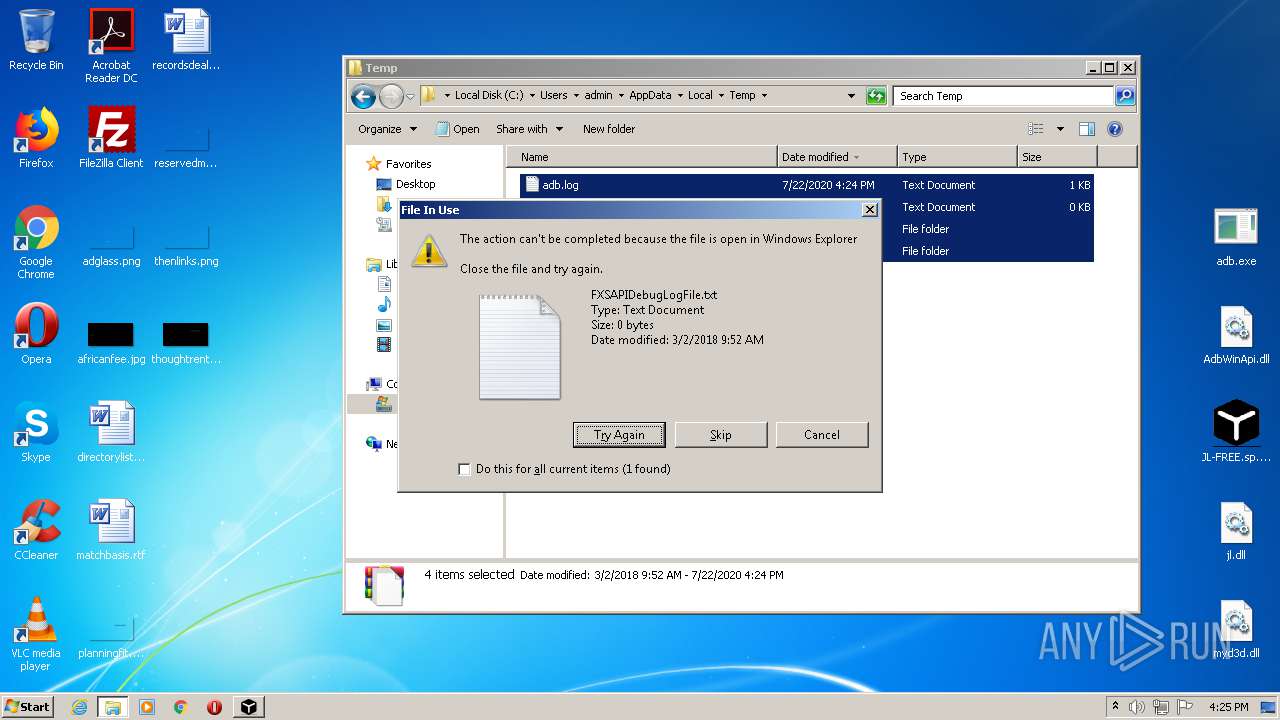
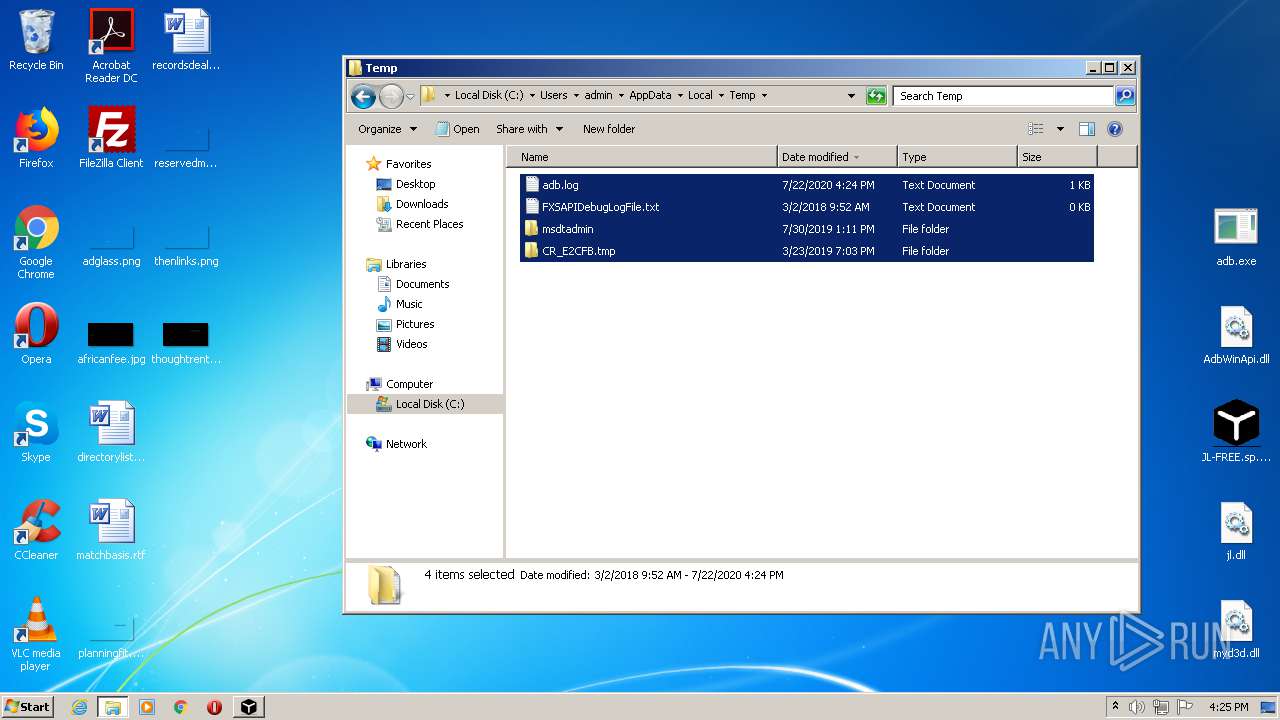
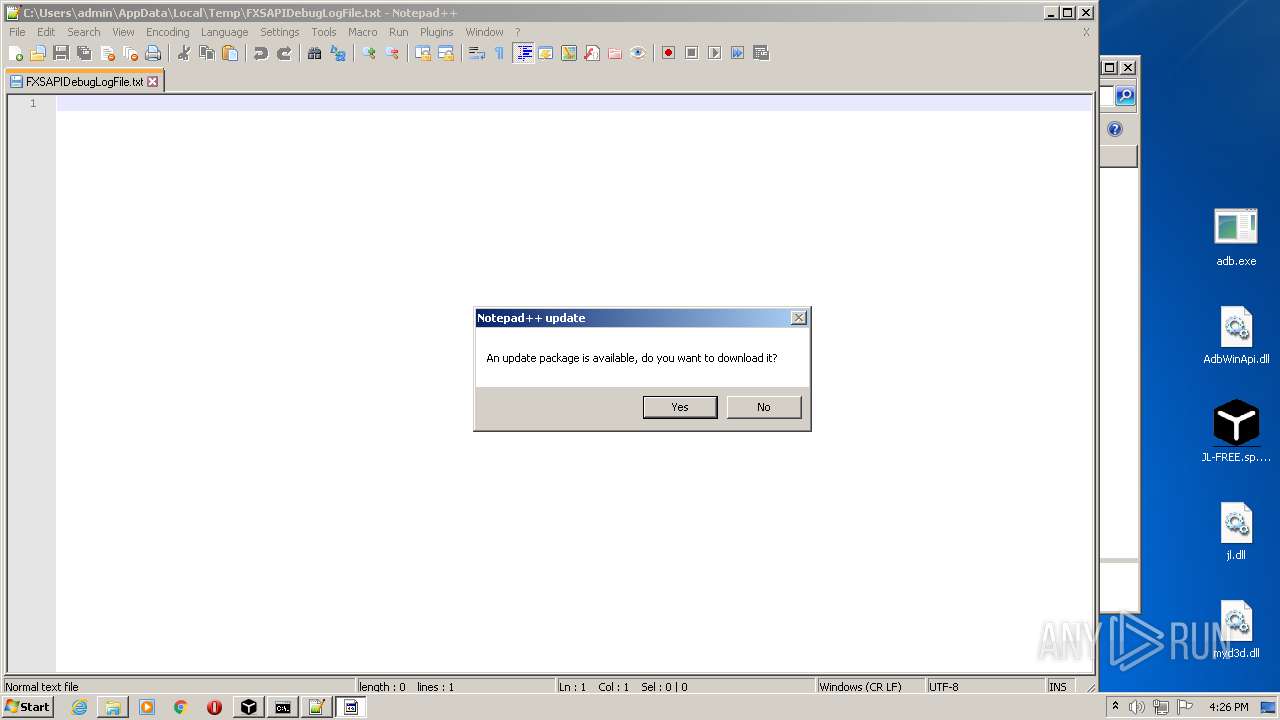
| 1004 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\AppData\Local\Temp\FXSAPIDebugLogFile.txt" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
| 1384 | cmd.exe /c cd/d""&& adb kill-server | C:\Windows\system32\cmd.exe | — | JL-FREE.sp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
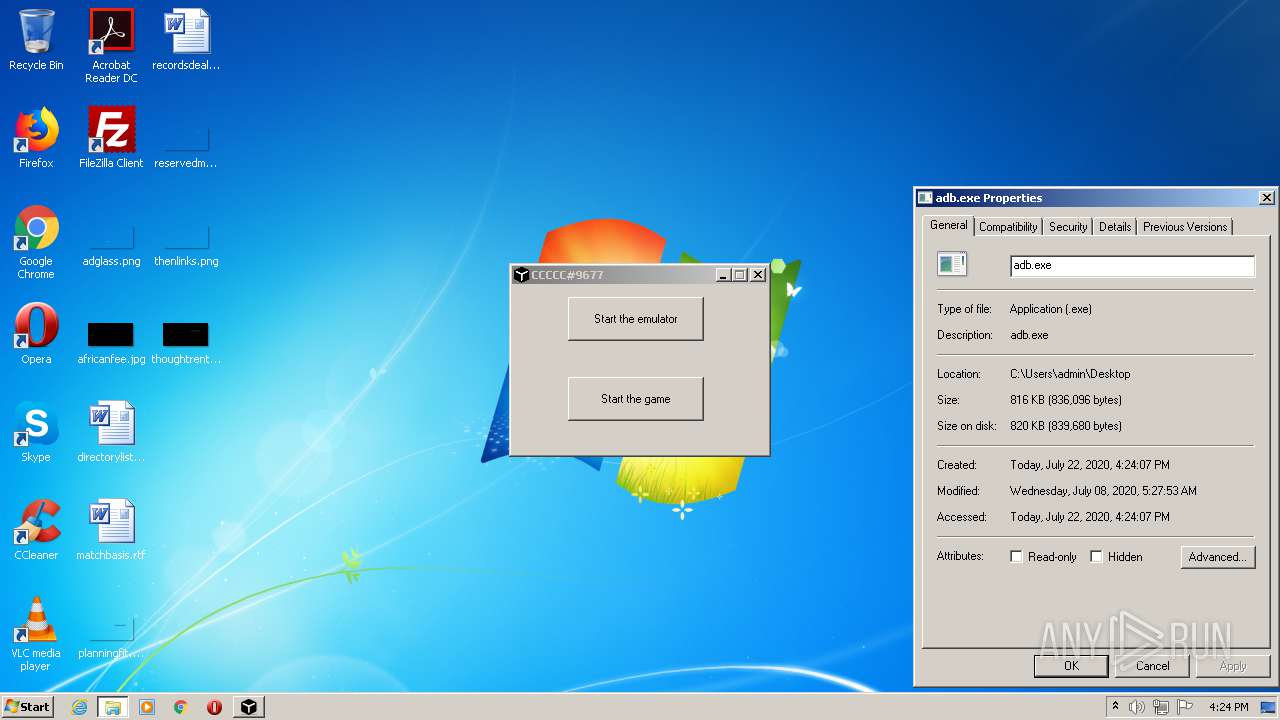
| 1844 | adb | C:\Users\admin\Desktop\adb.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 1848 | cmd.exe /C WScript "C:\ProgramData\YHKVPDcWfD\r.vbs" | C:\Windows\system32\cmd.exe | — | msm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2104 | "C:\Users\admin\Desktop\JL-FREE.sp.exe" | C:\Users\admin\Desktop\JL-FREE.sp.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2400 | adb start-server | C:\Users\admin\Desktop\adb.exe | JL-FREE.sp.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2424 | cmd /c ""C:\Users\admin\AppData\Local\Temp\1a984ec2.bat" " | C:\Windows\system32\cmd.exe | — | hxQzrZ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2492 | "C:\Windows\System32\control.exe" SYSTEM | C:\Windows\System32\control.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Control Panel Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2540 | "C:\Windows\System32\wuapp.exe" -c "C:\ProgramData\YHKVPDcWfD\cfg" | C:\Windows\System32\wuapp.exe | msm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Application Launcher Exit code: 0 Version: 7.5.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
6 509
Read events
5 593
Write events
888
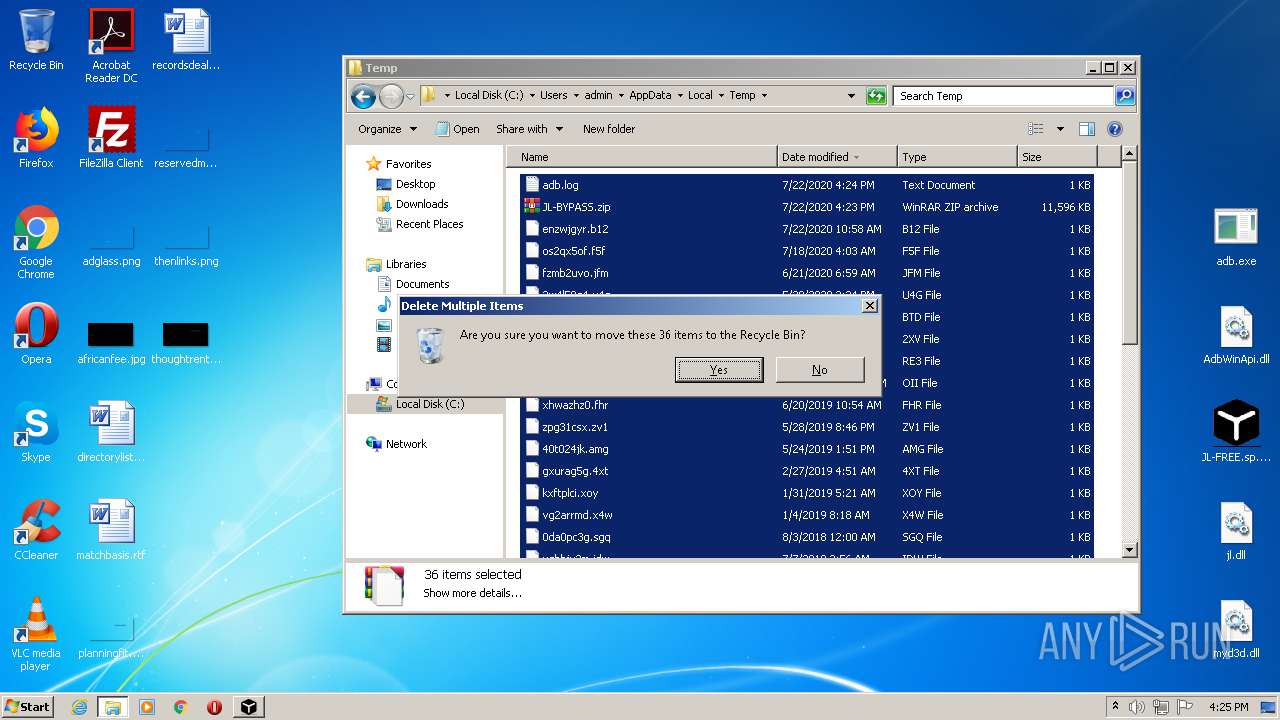
Delete events
28
Modification events
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\132\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\JL-BYPASS.zip | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (392) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (392) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
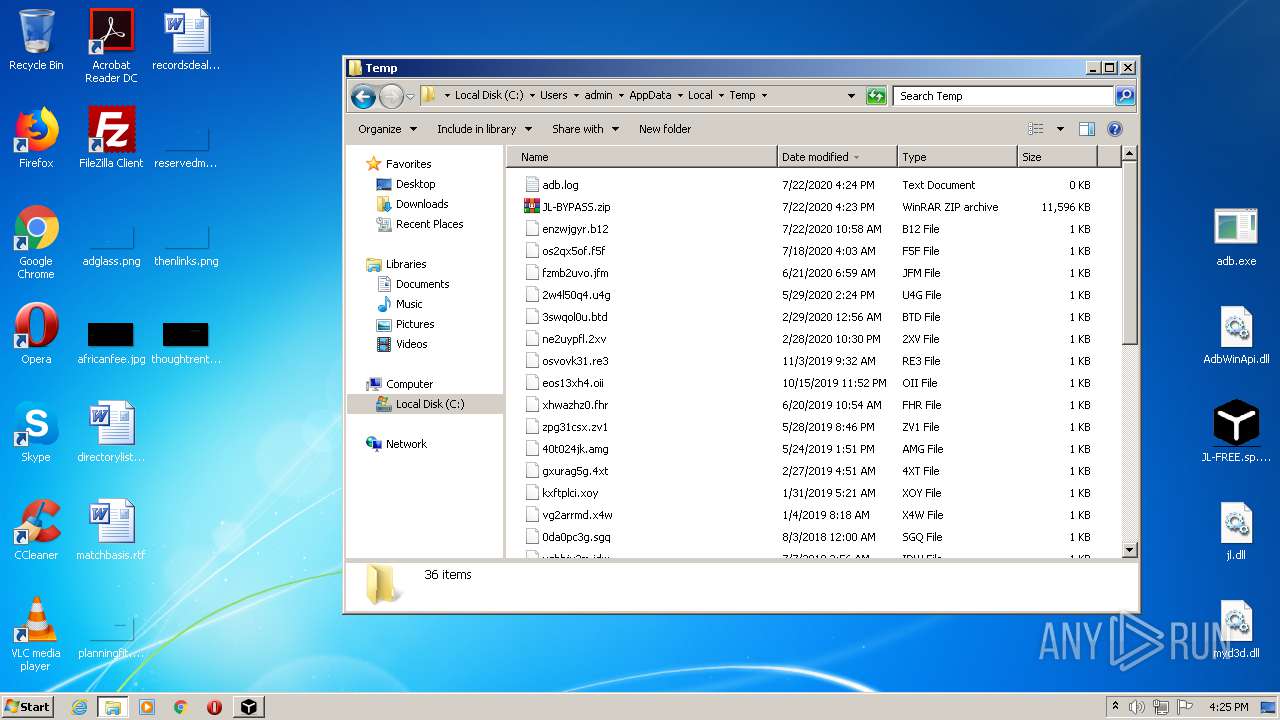
Executable files
14
Suspicious files
60
Text files
14
Unknown types
5
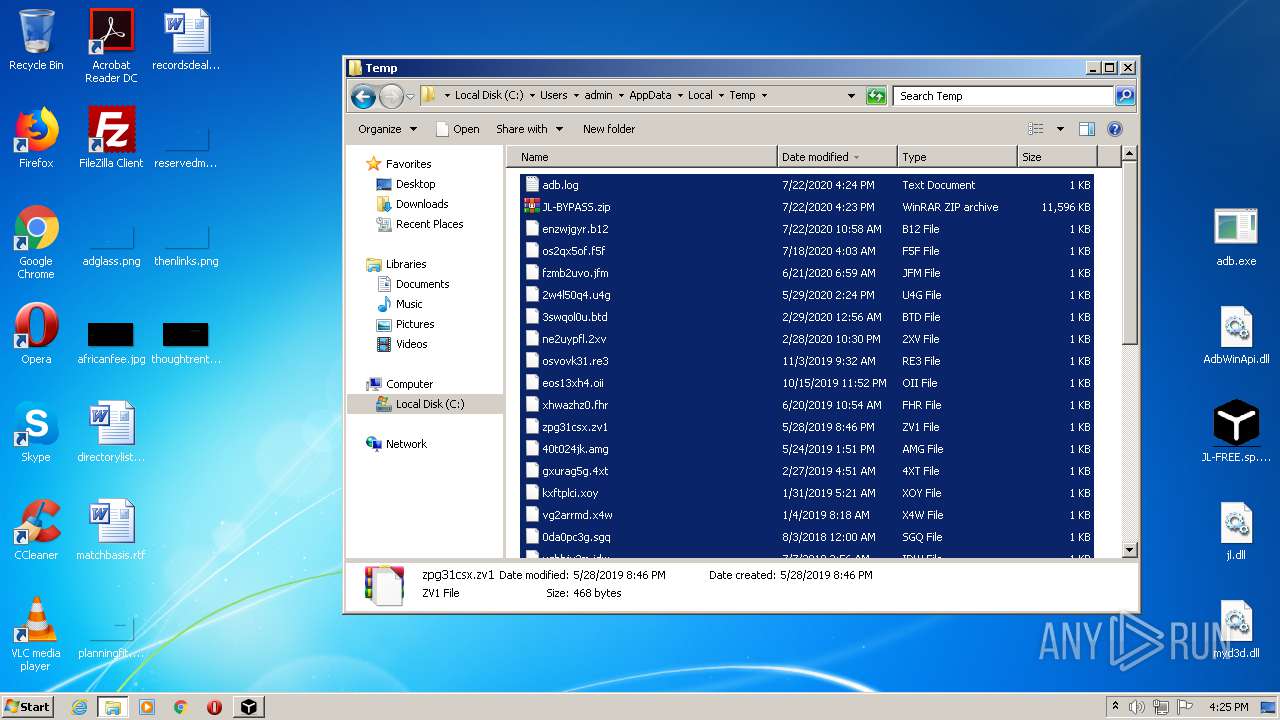
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3012 | msm.exe | C:\ProgramData\YHKVPDcWfD\41f43142c9_3.0.0 | — | |
MD5:— | SHA256:— | |||
| 3124 | hxQzrZ.exe | C:\Users\admin\AppData\Local\Temp\08f55ecc.exe | — | |
MD5:— | SHA256:— | |||
| 2104 | JL-FREE.sp.exe | C:\Users\admin\Documents\msm.exe | executable | |
MD5:— | SHA256:— | |||
| 3012 | msm.exe | C:\ProgramData\YHKVPDcWfD\ie.exe | — | |
MD5:— | SHA256:— | |||
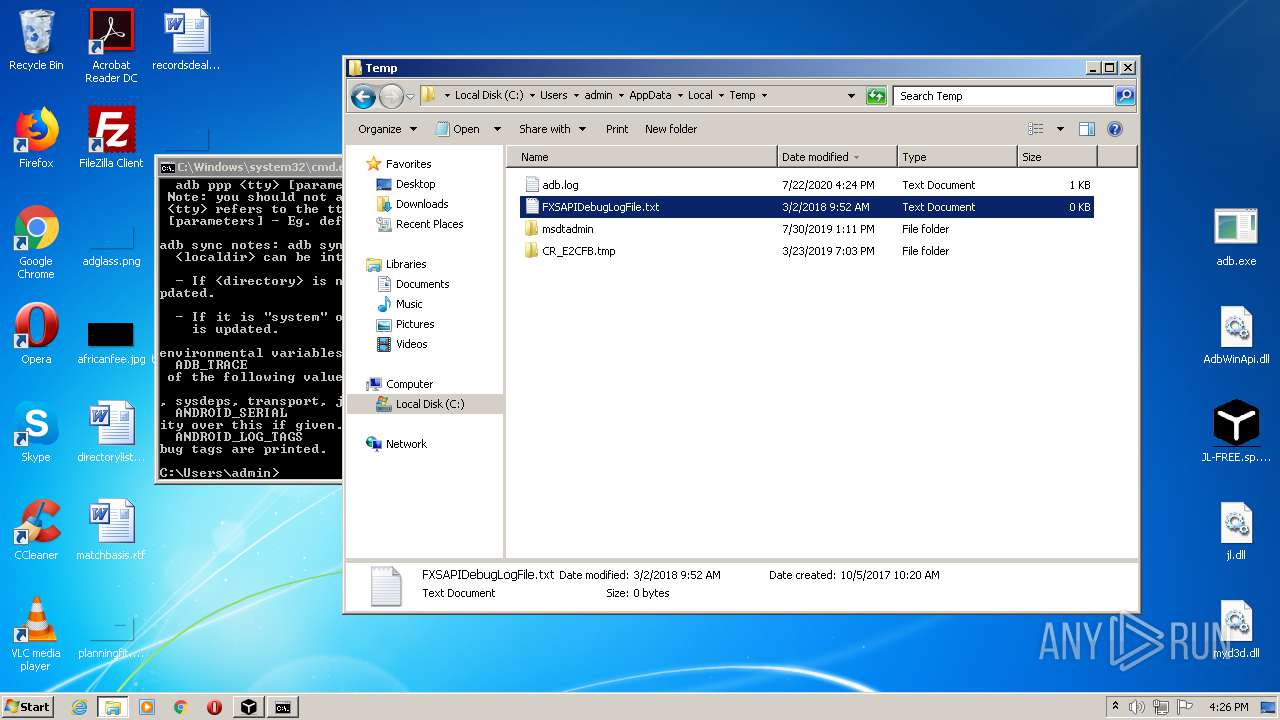
| 2856 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2856.27588\jl.dll | executable | |
MD5:— | SHA256:— | |||
| 2856 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2856.27588\adb.exe | executable | |
MD5:— | SHA256:— | |||
| 392 | explorer.exe | C:\Users\admin\Desktop\adb.exe | executable | |
MD5:— | SHA256:— | |||
| 392 | explorer.exe | C:\Users\admin\Desktop\AdbWinApi.dll | executable | |
MD5:— | SHA256:— | |||
| 392 | explorer.exe | C:\Users\admin\Desktop\JL-FREE.sp.exe | executable | |
MD5:— | SHA256:— | |||
| 392 | explorer.exe | C:\Users\admin\Desktop\jl.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
7
DNS requests
5
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3012 | msm.exe | GET | 200 | 23.225.140.58:80 | http://shadowgamer.vip/bigxmr.txt | US | text | 279 b | malicious |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2540 | wuapp.exe | 107.191.99.95:2222 | monerohash.com | RamNode LLC | US | malicious |
3012 | msm.exe | 23.225.140.58:80 | shadowgamer.vip | CNSERVERS LLC | US | malicious |
2104 | JL-FREE.sp.exe | 23.225.140.58:9000 | shadowgamer.vip | CNSERVERS LLC | US | malicious |
2716 | wuapp.exe | 107.191.99.95:2222 | monerohash.com | RamNode LLC | US | malicious |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3096 | gup.exe | 104.31.88.28:443 | notepad-plus-plus.org | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
shadowgamer.vip |
| malicious |
monerohash.com |
| unknown |
ddos.dnsnb8.net |
| malicious |
notepad-plus-plus.org |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2540 | wuapp.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
2540 | wuapp.exe | Misc activity | MINER [PTsecurity] CoinMiner CryptoNight XMRig JSON_RPC Client Login |
2540 | wuapp.exe | Misc activity | MINER [PTsecurity] Riskware/CoinMiner JSON_RPC Response |
3012 | msm.exe | A Network Trojan was detected | MINER [PTsecurity] Phorpiex Config |
2540 | wuapp.exe | Misc activity | MINER [PTsecurity] CoinMiner CryptoNight XMRig JSON_RPC Client Login |
2716 | wuapp.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
2716 | wuapp.exe | Misc activity | MINER [PTsecurity] CoinMiner CryptoNight XMRig JSON_RPC Client Login |
2716 | wuapp.exe | Misc activity | MINER [PTsecurity] Riskware/CoinMiner JSON_RPC Response |
5 ETPRO signatures available at the full report
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|