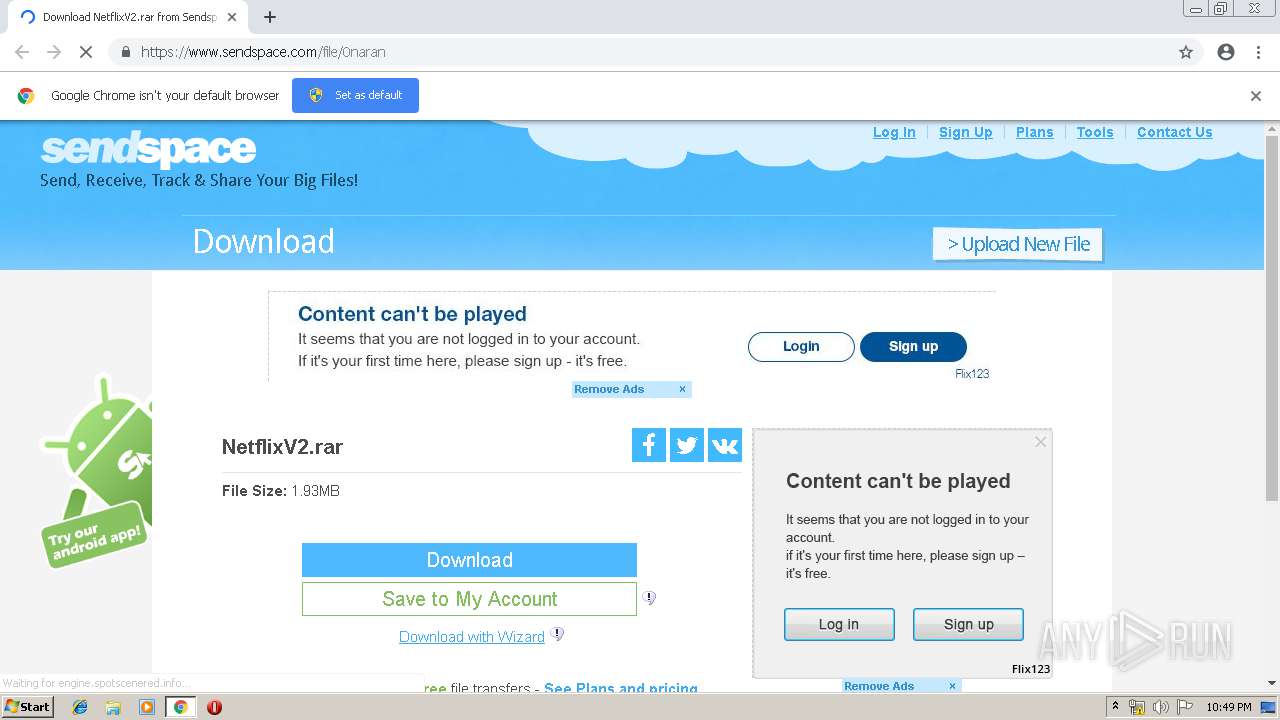
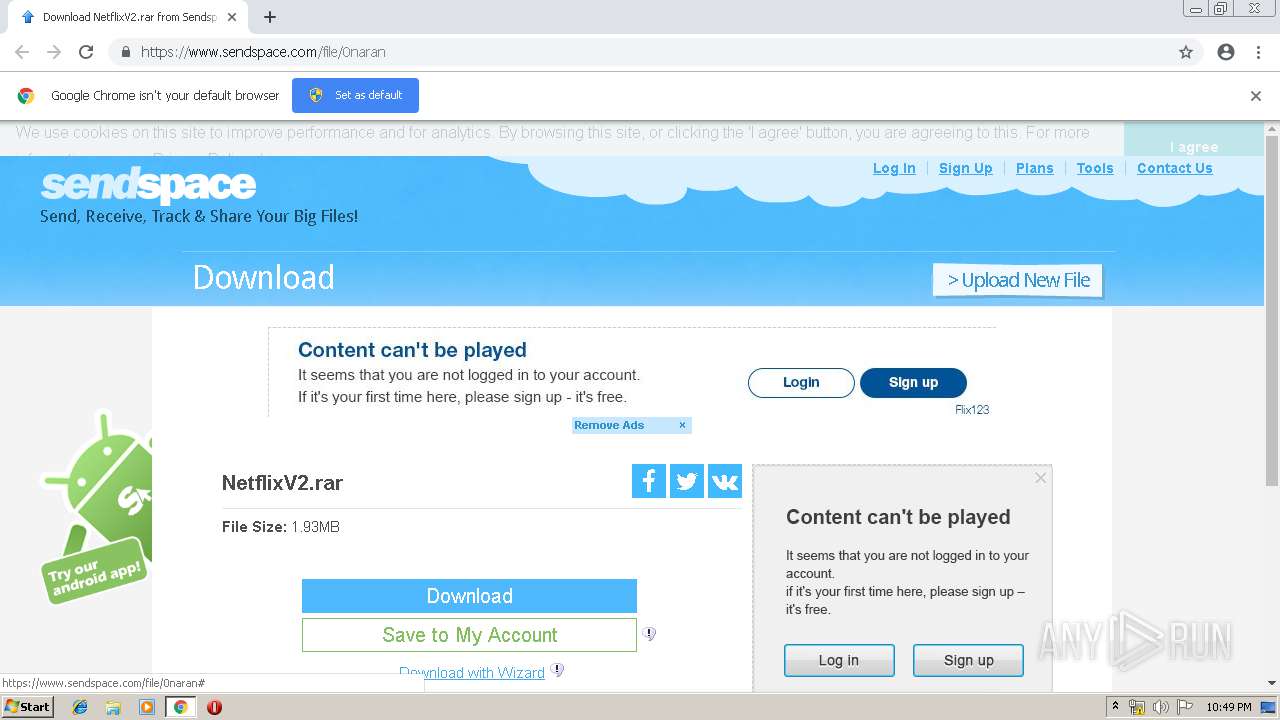
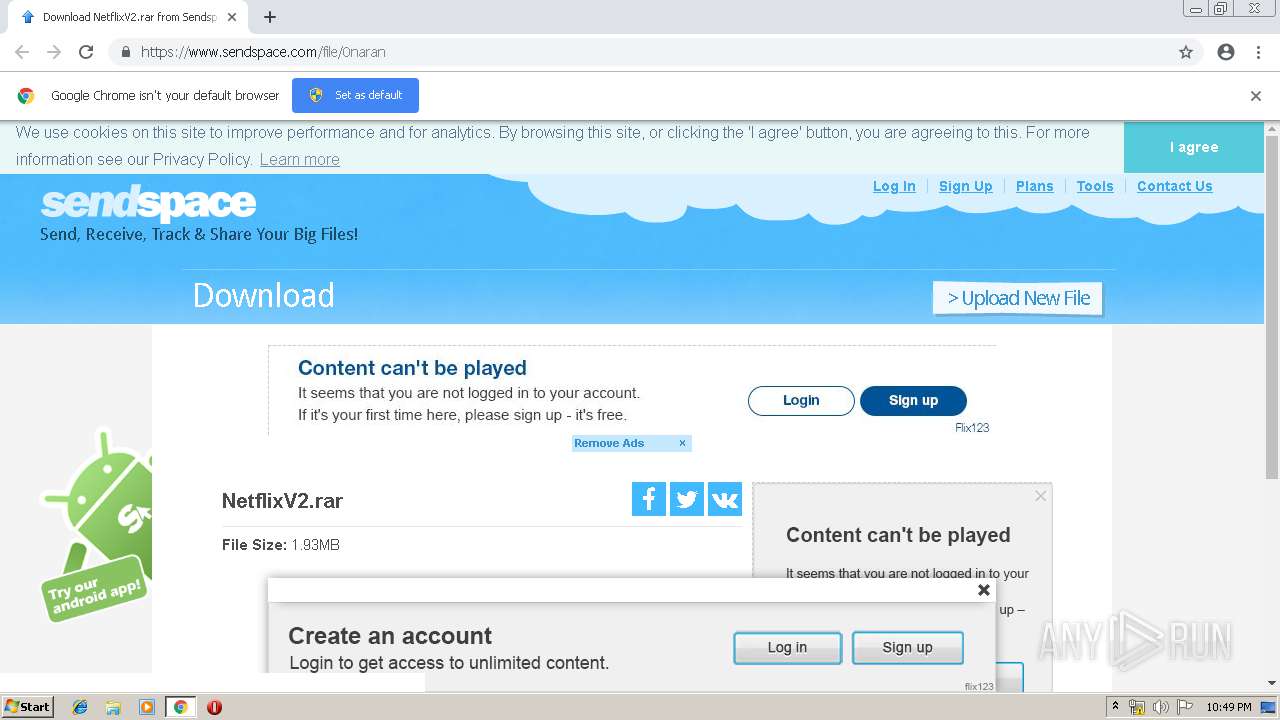
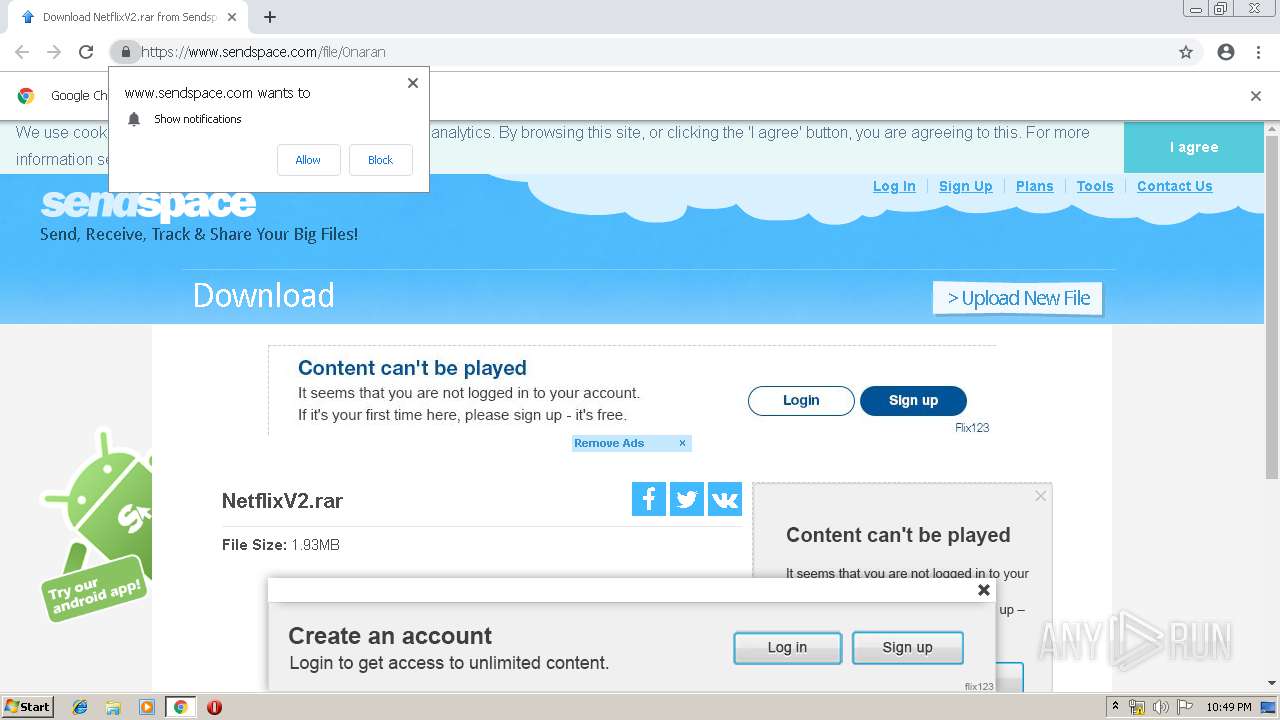
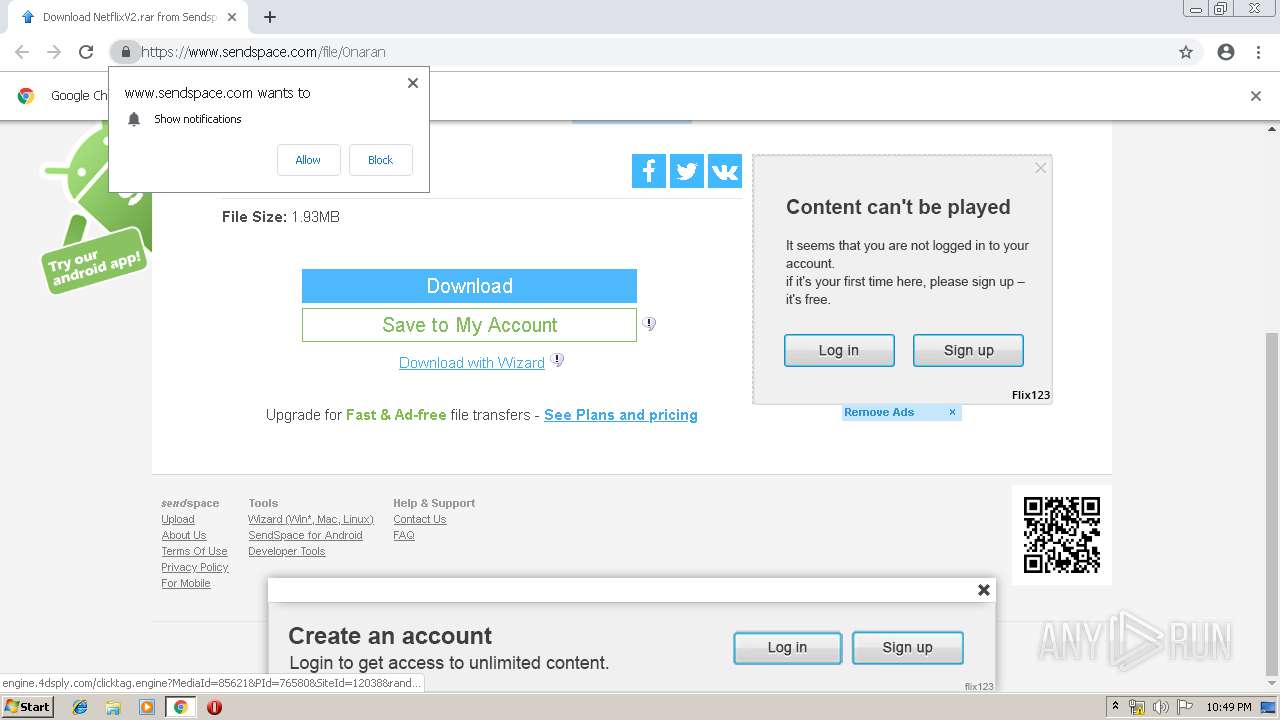
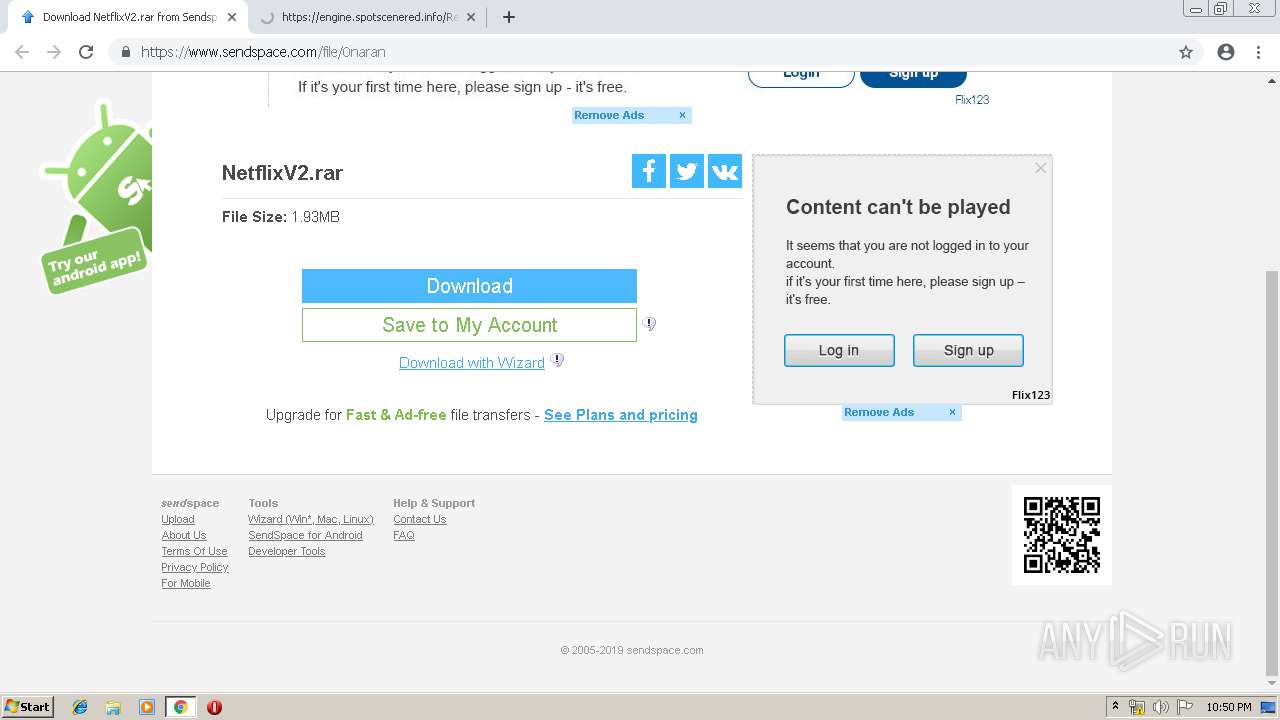
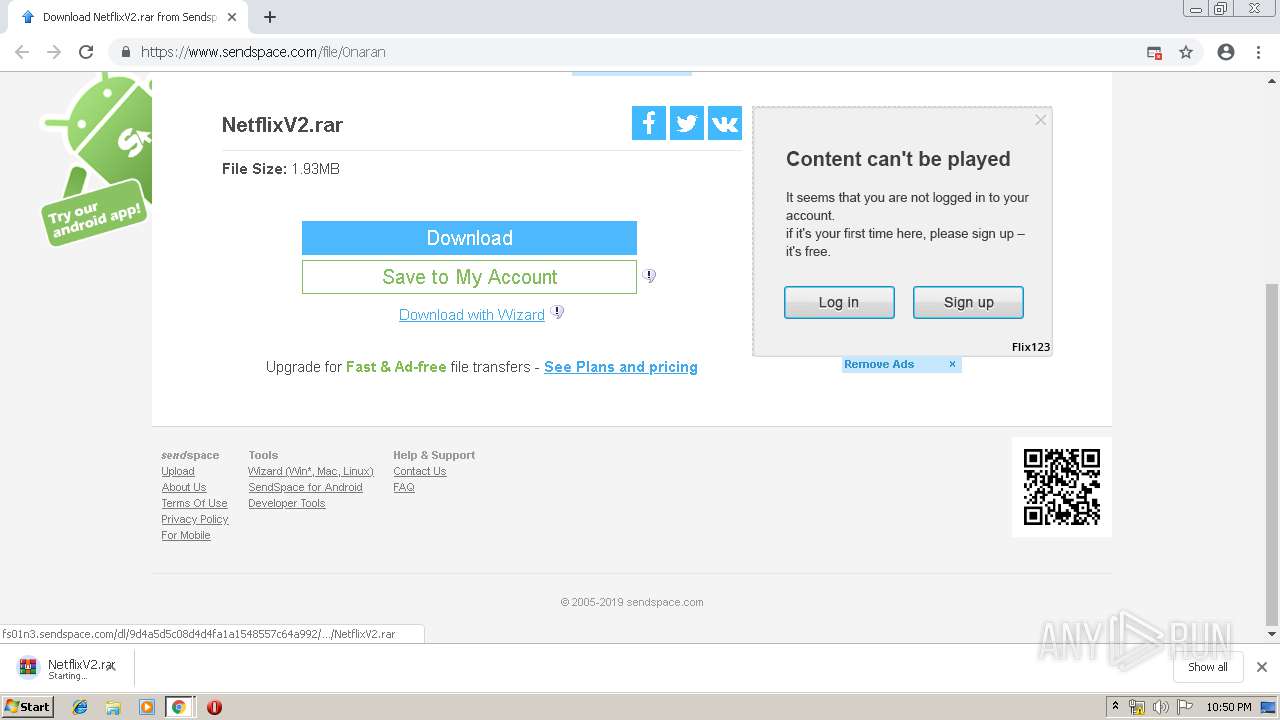
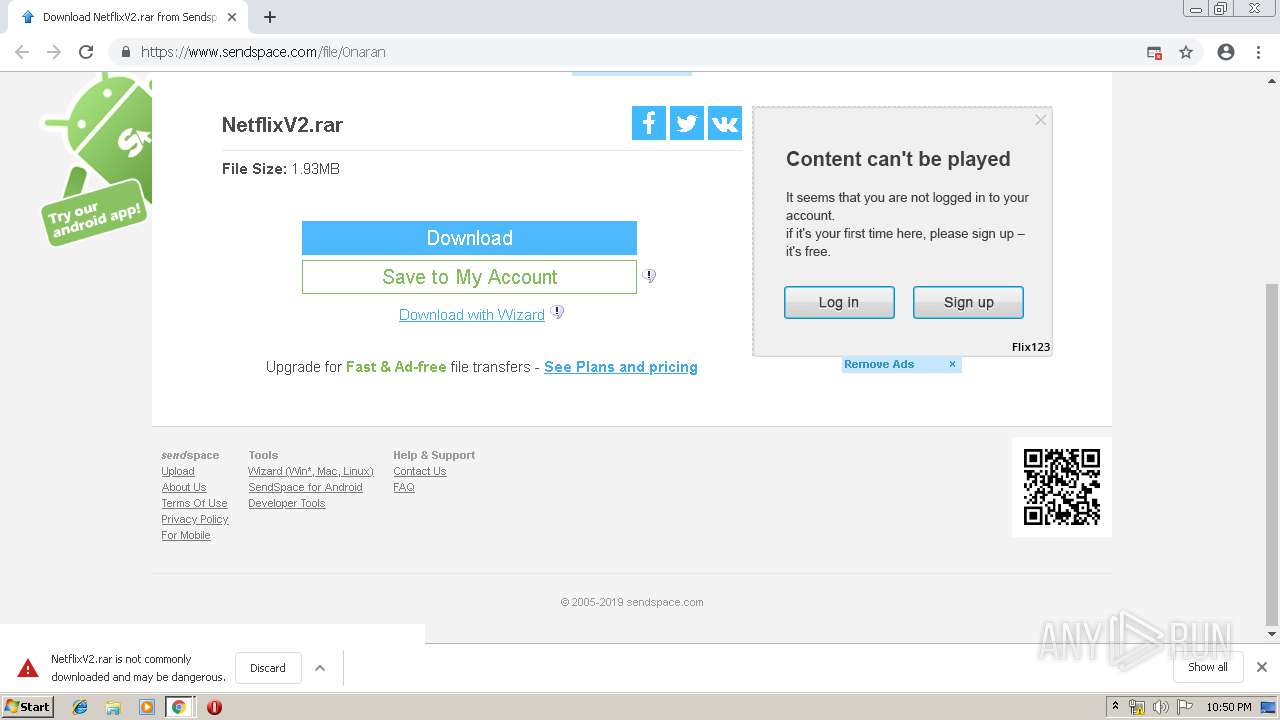
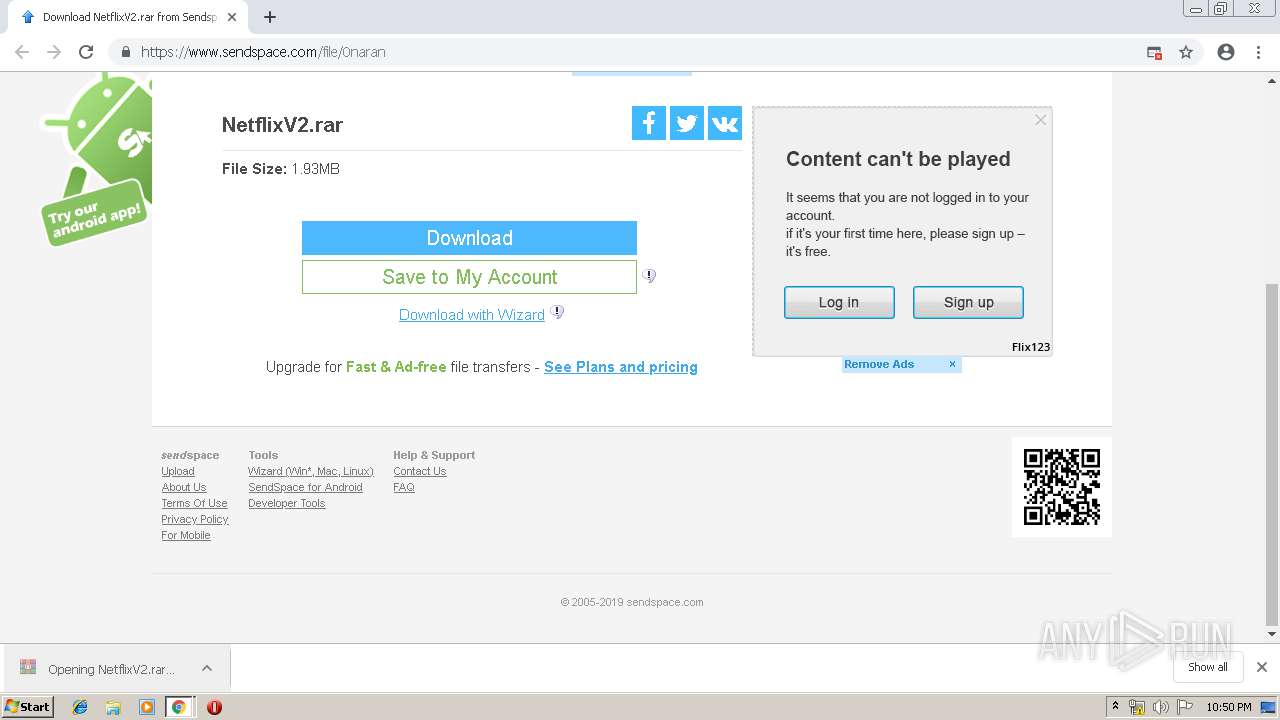
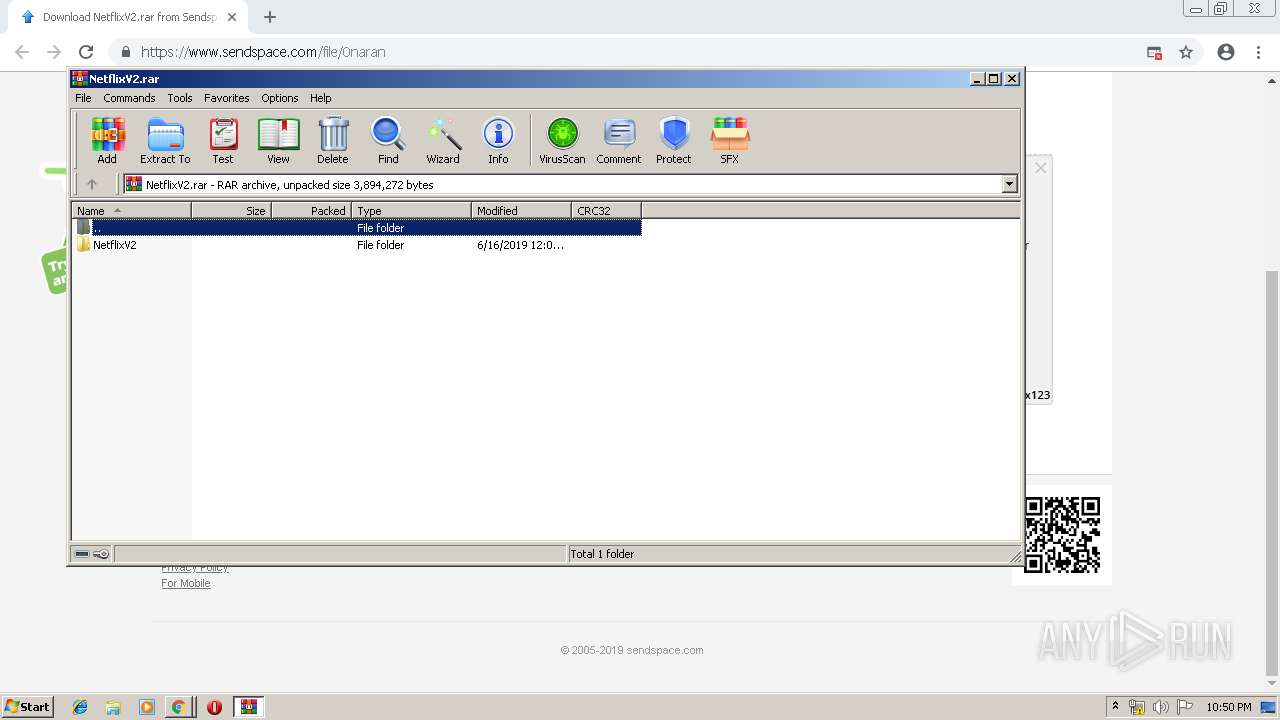
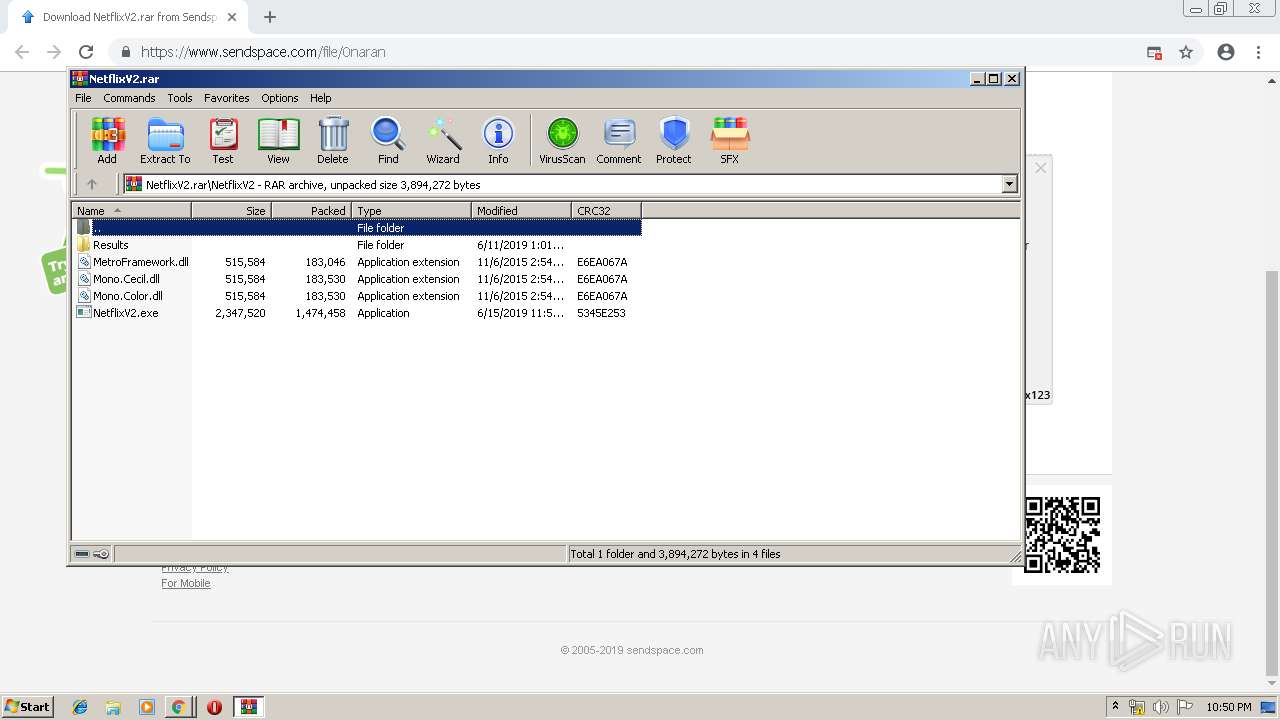
| URL: | https://www.sendspace.com/file/0naran |
| Full analysis: | https://app.any.run/tasks/65b465b3-181d-42f9-aad9-6b68238a7abe |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | June 16, 2019, 21:49:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2BBA9226A9B2E686DC049F40C487EB2E |
| SHA1: | 12FD0E802BFC43C75C5A8FB47E85FFB9513F641C |
| SHA256: | B652B061C4D077E3A3850B8B43FA468BF031D657DC50E67119F0A3DD718EFA12 |
| SSDEEP: | 3:N8DSLEvuGTYoVii:2OL0uKFL |
MALICIOUS
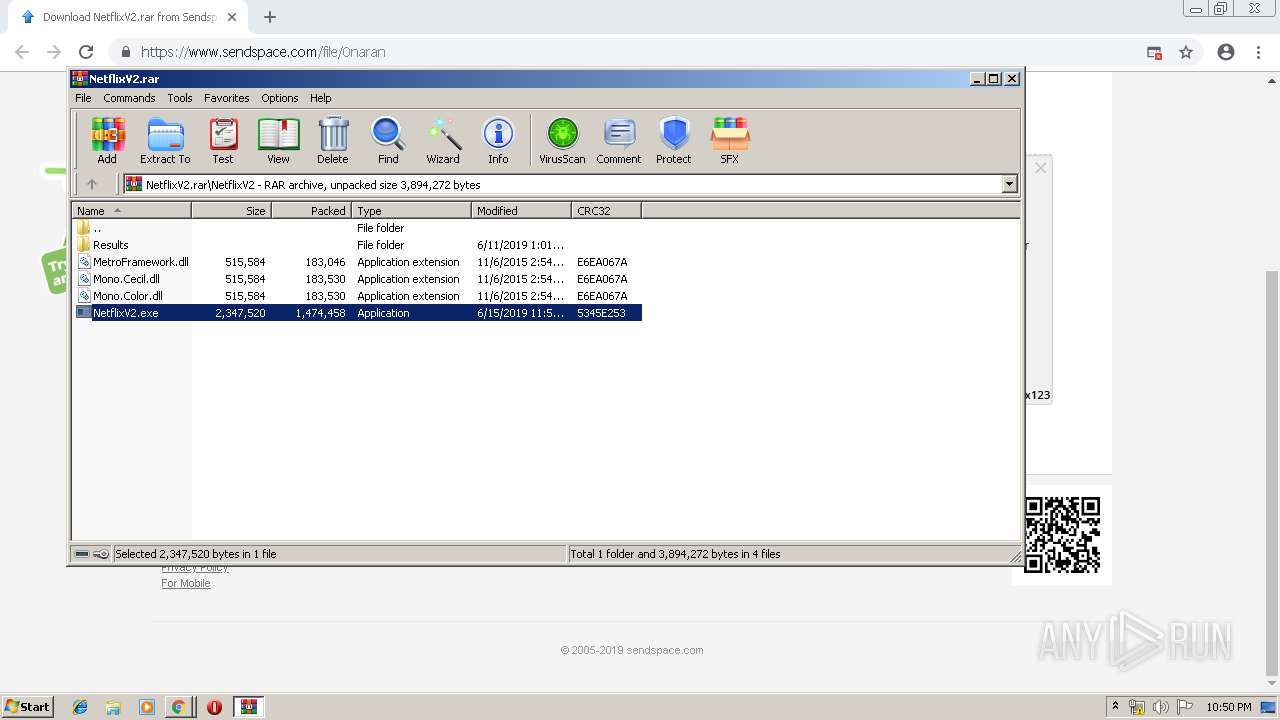
Application was dropped or rewritten from another process
- NetflixV2.exe (PID: 2548)
Changes the autorun value in the registry
- NetflixV2.exe (PID: 2548)
QUASAR was detected
- RegAsm.exe (PID: 2532)
- RegAsm.exe (PID: 3812)
Actions looks like stealing of personal data
- RegAsm.exe (PID: 2532)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 2160)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3372)
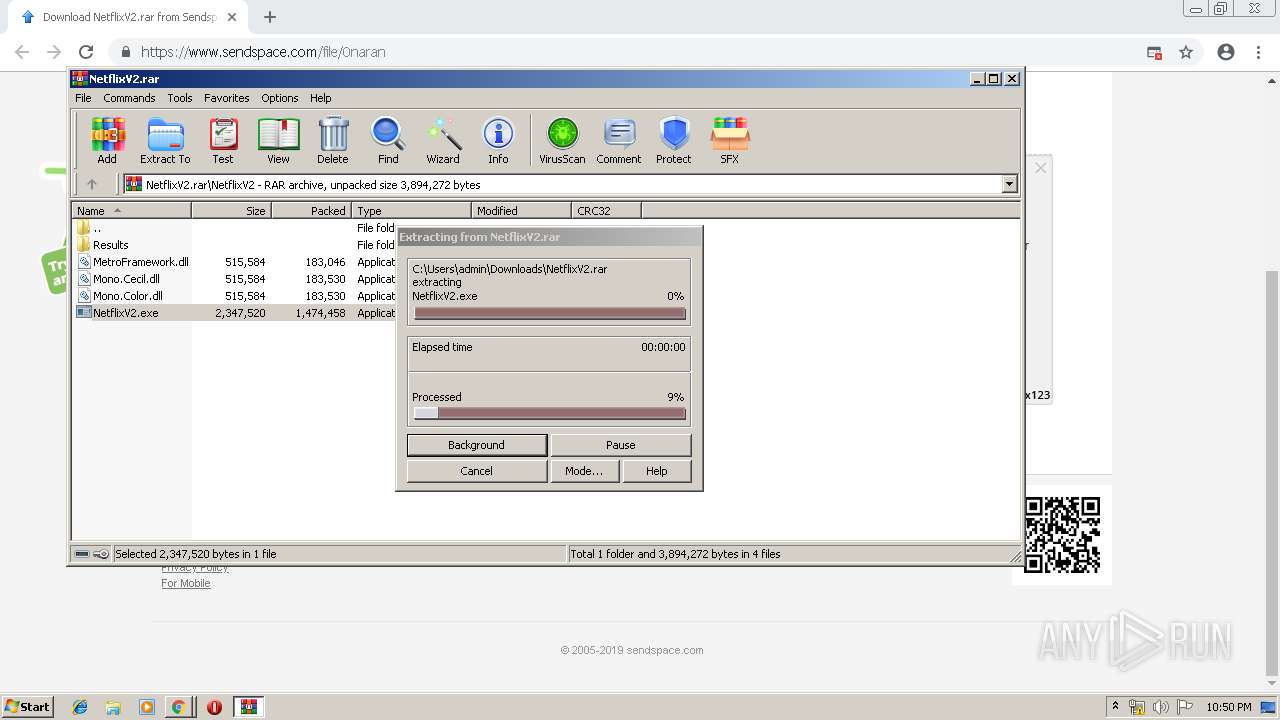
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3412)
- NetflixV2.exe (PID: 2548)
Creates files in the user directory
- RegAsm.exe (PID: 2532)
- RegAsm.exe (PID: 3812)
- NetflixV2.exe (PID: 2548)
Reads Internet Cache Settings
- RegAsm.exe (PID: 2532)
Checks for external IP
- RegAsm.exe (PID: 2532)
- RegAsm.exe (PID: 3812)
Starts CMD.EXE for commands execution
- RegAsm.exe (PID: 2532)
Starts application with an unusual extension
- cmd.exe (PID: 2160)
Loads DLL from Mozilla Firefox
- RegAsm.exe (PID: 2532)
INFO
Modifies the open verb of a shell class
- chrome.exe (PID: 3372)
Reads Internet Cache Settings
- chrome.exe (PID: 3372)
Application launched itself
- chrome.exe (PID: 3372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
63
Monitored processes
31
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8085138030993092555 --mojo-platform-channel-handle=2904 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7895136893860027957 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7895136893860027957 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3784 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7947892985299664486 --mojo-platform-channel-handle=4684 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15993887591204934790 --mojo-platform-channel-handle=4316 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3376 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --service-pipe-token=13461074370225948206 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13461074370225948206 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2056 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10102152477128796129 --mojo-platform-channel-handle=4900 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10037924409315195530 --mojo-platform-channel-handle=4508 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2160 | cmd /c ""C:\Users\admin\AppData\Local\Temp\DYmXM1Hy7ctr.bat" " | C:\Windows\system32\cmd.exe | — | RegAsm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=893356164246810009 --mojo-platform-channel-handle=4564 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
1 909
Read events
1 747
Write events
156
Delete events
6
Modification events
| (PID) Process: | (3372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3372-13205195385427000 |
Value: 259 | |||
| (PID) Process: | (3372) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
5
Suspicious files
96
Text files
204
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\326d552d-6ebc-4dcc-a4ca-f4772b2d6eb8.tmp | — | |
MD5:— | SHA256:— | |||
| 3372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
62
DNS requests
43
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3372 | chrome.exe | GET | 302 | 45.79.134.162:80 | http://runslin.com/?a_aid=m85230&data1=802136&data2=&data3=9eab7547-814e-45f6-b061-163727186fde&data4=3591499&a_aid=M85230&a_bid=0ecf847d&abopt=das2779jf2 | US | — | — | unknown |
3372 | chrome.exe | GET | 302 | 45.56.106.23:80 | http://myhithub.com/?a_aid=M85230&data1=802136&data2=&data3=9eab7547-814e-45f6-b061-163727186fde&data4=3591499&a_bid=0ecf847d&abopt=das2779jf2 | US | — | — | unknown |
3372 | chrome.exe | GET | 200 | 173.194.135.106:80 | http://r5---sn-aigzrn7z.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=109.169.22.99&mm=28&mn=sn-aigzrn7z&ms=nvh&mt=1560721020&mv=u&pl=22&shardbypass=yes | US | crx | 842 Kb | whitelisted |
3372 | chrome.exe | GET | 302 | 216.58.205.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 504 b | whitelisted |
3812 | RegAsm.exe | GET | 200 | 185.194.141.58:80 | http://ip-api.com/json/ | DE | text | 321 b | malicious |
3372 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.2 Kb | whitelisted |
3372 | chrome.exe | GET | 301 | 50.116.55.233:80 | http://bookvus.com/?a_aid=M85230&data1=802136&data2=&data3=9eab7547-814e-45f6-b061-163727186fde&data4=3591499&a_bid=0ecf847d&abopt=das2779jf2 | US | html | 194 b | unknown |
2532 | RegAsm.exe | GET | 200 | 185.194.141.58:80 | http://ip-api.com/json/ | DE | text | 321 b | malicious |
3372 | chrome.exe | GET | 200 | 13.32.42.105:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
3372 | chrome.exe | GET | 200 | 13.32.42.196:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3372 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3372 | chrome.exe | 69.31.136.5:443 | www.sendspace.com | GTT Communications Inc. | US | suspicious |
3372 | chrome.exe | 172.217.18.110:443 | apis.google.com | Google Inc. | US | whitelisted |
3372 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
3372 | chrome.exe | 216.58.207.74:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3372 | chrome.exe | 205.185.216.10:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3372 | chrome.exe | 13.32.42.105:80 | x.ss2.us | — | US | unknown |
3372 | chrome.exe | 13.32.42.196:80 | x.ss2.us | — | US | unknown |
3372 | chrome.exe | 69.89.74.102:443 | engine.spotscenered.info | Net Data Centers, Inc. | US | unknown |
3372 | chrome.exe | 172.217.22.78:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.sendspace.com |
| shared |
accounts.google.com |
| shared |
apis.google.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
t.mdn2015x4.com |
| whitelisted |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
engine.spotscenered.info |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2532 | RegAsm.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
2532 | RegAsm.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
2532 | RegAsm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Quasar 1.3 RAT IP Lookup ip-api.com (HTTP headeer) |
1056 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
2532 | RegAsm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Quasar RAT |
3812 | RegAsm.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
3812 | RegAsm.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
3812 | RegAsm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Quasar 1.3 RAT IP Lookup ip-api.com (HTTP headeer) |
3812 | RegAsm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Quasar RAT |
2 ETPRO signatures available at the full report