| File name: | Setup.exe |
| Full analysis: | https://app.any.run/tasks/b2af196c-438b-462a-b645-fc7f50b8f5a6 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | May 18, 2025, 19:56:09 |
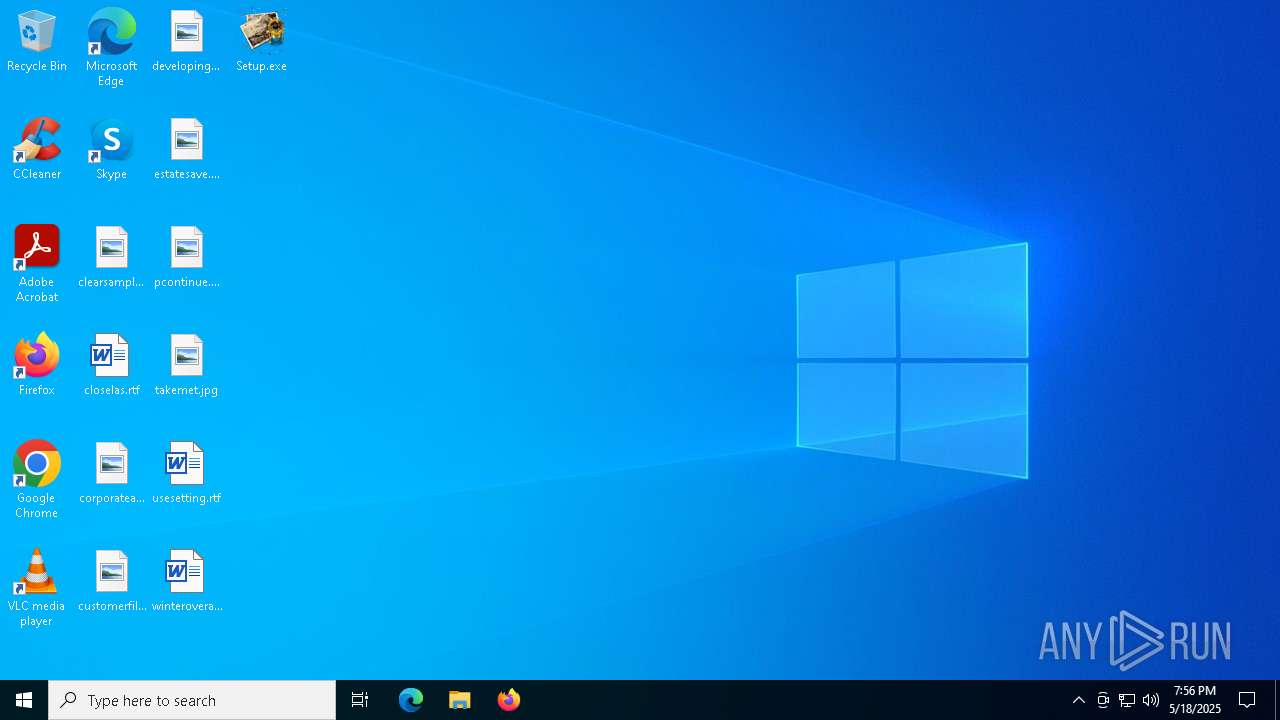
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | E010CD53F9377D356D547E3C4D298506 |
| SHA1: | 2409F485F42D285CD1157EE0EA6CA9881A90BEAB |
| SHA256: | B58EA28950BA3C0B5B67CF3B62A60C4BA8A2ADA384540CCD0D90C5D9A77EC230 |
| SSDEEP: | 98304:q6IenQfaamReZ0Epb3WrW3oZRftZK9tUfs71QFyik:q |
MALICIOUS
Executing a file with an untrusted certificate
- Setup.exe (PID: 7712)
AutoIt loader has been detected (YARA)
- Nine.com (PID: 8188)
Steals credentials from Web Browsers
- Nine.com (PID: 8188)
Actions looks like stealing of personal data
- Nine.com (PID: 8188)
LUMMA mutex has been found
- Nine.com (PID: 8188)
SUSPICIOUS
Reads the date of Windows installation
- Setup.exe (PID: 7712)
Application launched itself
- cmd.exe (PID: 7804)
Starts application with an unusual extension
- cmd.exe (PID: 7804)
Starts the AutoIt3 executable file
- cmd.exe (PID: 7804)
The executable file from the user directory is run by the CMD process
- Nine.com (PID: 8188)
There is functionality for taking screenshot (YARA)
- Setup.exe (PID: 7712)
- Nine.com (PID: 8188)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7804)
- Setup.exe (PID: 7712)
Searches for installed software
- Nine.com (PID: 8188)
Executing commands from a ".bat" file
- Setup.exe (PID: 7712)
Reads security settings of Internet Explorer
- Setup.exe (PID: 7712)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7804)
Get information on the list of running processes
- cmd.exe (PID: 7804)
INFO
Checks supported languages
- Setup.exe (PID: 7712)
- extrac32.exe (PID: 8112)
- Nine.com (PID: 8188)
Create files in a temporary directory
- Setup.exe (PID: 7712)
- extrac32.exe (PID: 8112)
- Nine.com (PID: 8188)
Reads the computer name
- Setup.exe (PID: 7712)
- extrac32.exe (PID: 8112)
- Nine.com (PID: 8188)
Creates a new folder
- cmd.exe (PID: 8088)
Reads mouse settings
- Nine.com (PID: 8188)
Reads the machine GUID from the registry
- Nine.com (PID: 8188)
Checks proxy server information
- slui.exe (PID: 5960)
Reads the software policy settings
- Nine.com (PID: 8188)
- slui.exe (PID: 5960)
Process checks computer location settings
- Setup.exe (PID: 7712)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:04:10 12:19:23+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 25600 |
| InitializedDataSize: | 431104 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x33e9 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Total processes
138
Monitored processes
15
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5960 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7204 | choice /d y /t 5 | C:\Windows\SysWOW64\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7712 | "C:\Users\admin\Desktop\Setup.exe" | C:\Users\admin\Desktop\Setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7804 | "C:\WINDOWS\System32\CMd.exe" /c copy Hearings.aifc Hearings.aifc.bat & Hearings.aifc.bat | C:\Windows\SysWOW64\cmd.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7812 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7888 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7908 | findstr /I "opssvc wrsa" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8032 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8040 | findstr "bdservicehost SophosHealth AvastUI AVGUI nsWscSvc ekrn" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 979
Read events
7 971
Write events
8
Delete events
0
Modification events
| (PID) Process: | (7712) Setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (7712) Setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (7712) Setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (7712) Setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
21
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7712 | Setup.exe | C:\Users\admin\AppData\Local\Temp\Subscriber.aifc | binary | |
MD5:7F3EAC07241DD012B3BC9D833E1B19A7 | SHA256:A9E137FE48A0A1A538E33DA686653C5A60A75BA32D5A506952CD3FF019C5D3A1 | |||
| 7712 | Setup.exe | C:\Users\admin\AppData\Local\Temp\Loops.aifc | binary | |
MD5:6996E5A280F6221D2C880D12A2877B96 | SHA256:0C7BBFAC1902CA77E89F2C1CDCBBA688BB2A8CE74056DBE6445A32284DC3E80A | |||
| 7712 | Setup.exe | C:\Users\admin\AppData\Local\Temp\Pocket.aifc | compressed | |
MD5:12592CC2C5AA803E51BBC449C3A9A3E7 | SHA256:FC7DE7EC45E4FAD1CE326DAA68CCDDE3C9108B61792B04965C322950B50E7099 | |||
| 7712 | Setup.exe | C:\Users\admin\AppData\Local\Temp\Og.aifc | binary | |
MD5:51D2E55A1FDF92D303ABF0348862D9A9 | SHA256:92AEE67AD0CAC6514583A59ABB8E6DAD13D61D9EDA8869A04DD11A289F3B8F44 | |||
| 7712 | Setup.exe | C:\Users\admin\AppData\Local\Temp\Tutorials.aifc | binary | |
MD5:0BAA8B80BFD199B5A9DC3608F6D4EF2D | SHA256:1FAA07435E9D7E913A842EAE914ADE487B04FCD3B01329E3BBC945A18E7223E4 | |||
| 7712 | Setup.exe | C:\Users\admin\AppData\Local\Temp\Pulling.aifc | binary | |
MD5:439EB449736FE70C8B0FF08F42286217 | SHA256:342B157566E5FC9E81DA425B49C2B3DA3234A6229D28460FFA9F136FA619029C | |||
| 7712 | Setup.exe | C:\Users\admin\AppData\Local\Temp\Talented.aifc | binary | |
MD5:EECD0914AA4E2895C8D65AB1A28E74CF | SHA256:C0262DB27F7BEAB938F873BFE21A004705EE84203A5C051B77FE66895748056D | |||
| 7712 | Setup.exe | C:\Users\admin\AppData\Local\Temp\Hearings.aifc | text | |
MD5:945A05710563D0544235367C3B2EF304 | SHA256:E5F4A86988507C7DF8DF97EF6F0AA1B51B57906F254585431D133006ADBA0E6E | |||
| 7712 | Setup.exe | C:\Users\admin\AppData\Local\Temp\Bracket.aifc | binary | |
MD5:A8D6AF02720F4267E56488FFC0E8F0C6 | SHA256:14BFE53F76D18008101C7ECE9C7CAC197FF4089E72E1A17E5B9779AE88C9460A | |||
| 8112 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Tried | binary | |
MD5:6C0B0F7F92DF97F2AF2960A32FE46399 | SHA256:477EB2228F9C7E4BB10D096B4704DE6F83A6556664A19FADA8B38B66F5C30D6F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
46
DNS requests
20
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4944 | RUXIMICS.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4944 | RUXIMICS.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7236 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
7236 | SIHClient.exe | GET | 200 | 23.48.23.169:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
7236 | SIHClient.exe | GET | 200 | 23.48.23.169:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
7236 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7236 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
7236 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
7236 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4944 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4944 | RUXIMICS.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4944 | RUXIMICS.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7236 | SIHClient.exe | 4.245.163.56:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7236 | SIHClient.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
WFfoWhHGBeMs.WFfoWhHGBeMs |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
narrathfpt.top |
| unknown |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
h1.jockstrapdisown.today |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |