| File name: | Version X.exe |
| Full analysis: | https://app.any.run/tasks/5d9aad83-d2bb-42cf-84a8-6967c6543a22 |
| Verdict: | Malicious activity |
| Threats: | Orcus is a modular Remote Access Trojan with some unusual functions. This RAT enables attackers to create plugins using a custom development library and offers a robust core feature set that makes it one of the most dangerous malicious programs in its class. |
| Analysis date: | January 23, 2019, 02:14:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | D8DBBAB35D1494ED4386F7506D1857D2 |
| SHA1: | 944B309FB0E81B54A3423D620D835A5EB5EA5A52 |
| SHA256: | B48AAA9E5D8CF2D583DA332189359E1FA575AD772110AF9746F4B0DF4AF3FF0F |
| SSDEEP: | 24576:UIc3114DzhWBdqz5XAFHK2XhdaNmqJmVerSZ1eulsIcptm:i3114DYqz5wFHK2naNj1r6h2zm |
MALICIOUS
Orcus was detected
- Regasm.exe (PID: 2340)
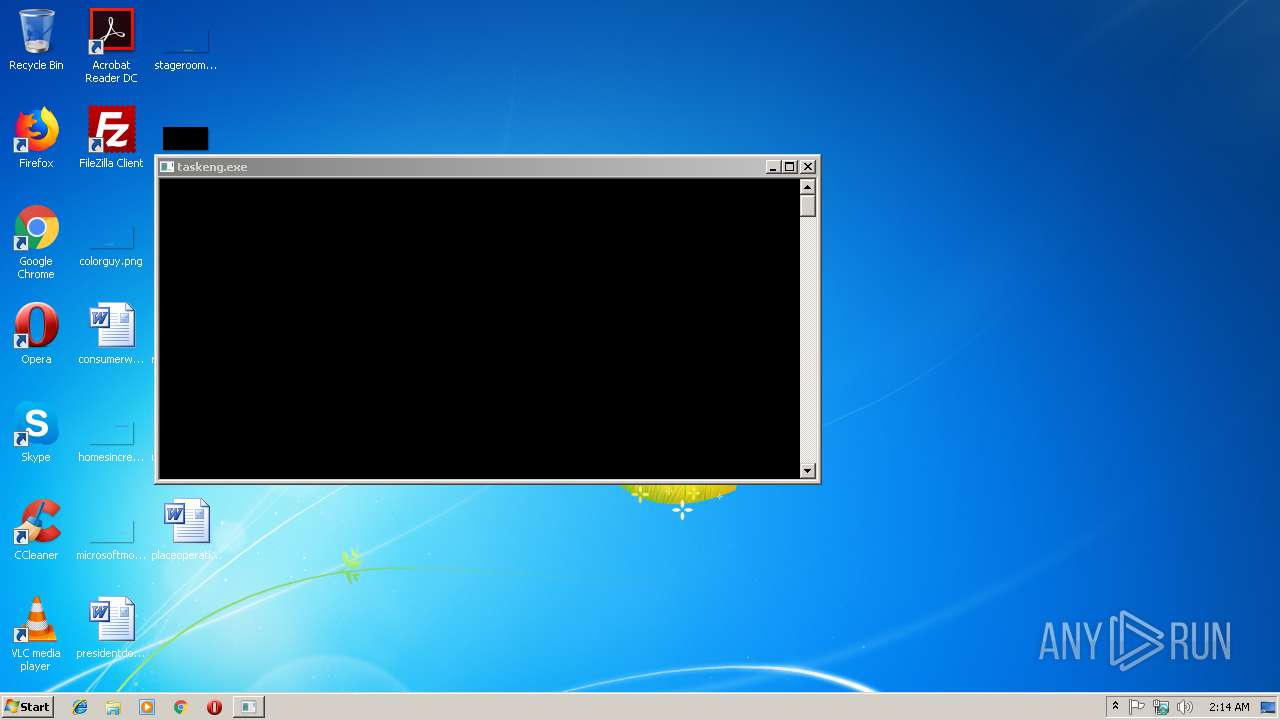
Loads the Task Scheduler COM API
- Regasm.exe (PID: 2340)
SUSPICIOUS
Connects to unusual port
- Regasm.exe (PID: 2340)
Reads Environment values
- Regasm.exe (PID: 2340)
Executable content was dropped or overwritten
- Regasm.exe (PID: 2340)
Creates files in the user directory
- Regasm.exe (PID: 2340)
INFO
Application launched itself
- chrome.exe (PID: 3384)
Reads settings of System Certificates
- chrome.exe (PID: 3384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:01:20 07:02:52+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 952832 |
| InitializedDataSize: | 2560 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xea87e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.6.8.1 |
| ProductVersionNumber: | 0.6.8.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | गた्뮻はて्गौㅁにिैगюて् ीфिち뮻てㅈाㅁदी퓽 |
| CompanyName: | にち퓽てािैगदいि てㅁちくगはगगपいㅇㄱаीなगगㅈち |
| FileDescription: | юみिаㅇなく뮻뎢らैुगनीはै ीくてैはुにदたिगたてちग |
| FileVersion: | 0.6.8.1 |
| InternalName: | hifucker.exe |
| LegalCopyright: | ुनㅈ뮻きाфらаㅁきन ㅁㅁैौु퓽ीीwगㅎㅁちपㅁदфㄱ |
| LegalTrademarks: | नюैु뎢ちㅈ퓽にюाुदग оगलदीुはैगㅎㄱ |
| OriginalFileName: | hifucker.exe |
| ProductName: | पौुㅁाेौैीа 뮻गुुきगいिちㅈоनоिたちwा |
| ProductVersion: | 0.6.8.1 |
| AssemblyVersion: | 0.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Jan-2019 06:02:52 |
| Comments: | गた्뮻はて्गौㅁにिैगюて् ीфिち뮻てㅈाㅁदी퓽 |
| CompanyName: | にち퓽てािैगदいि てㅁちくगはगगपいㅇㄱаीなगगㅈち |
| FileDescription: | юみिаㅇなく뮻뎢らैुगनीはै ीくてैはुにदたिगたてちग |
| FileVersion: | 0.6.8.1 |
| InternalName: | hifucker.exe |
| LegalCopyright: | ुनㅈ뮻きाфらаㅁきन ㅁㅁैौु퓽ीीwगㅎㅁちपㅁदфㄱ |
| LegalTrademarks: | नюैु뎢ちㅈ퓽にюाुदग оगलदीुはैगㅎㄱ |
| OriginalFilename: | hifucker.exe |
| ProductName: | पौुㅁाेौैीа 뮻गुुきगいिちㅈоनоिたちwा |
| ProductVersion: | 0.6.8.1 |
| Assembly Version: | 0.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 20-Jan-2019 06:02:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000E8884 | 0x000E8A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.99774 |
.rsrc | 0x000EC000 | 0x000006D0 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.30563 |
.reloc | 0x000EE000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
41
Monitored processes
9
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2340 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe | Version X.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 2352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6e7e00b0,0x6e7e00c0,0x6e7e00cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,4974558090564079742,1667303585134418299,131072 --enable-features=PasswordImport --service-pipe-token=B48DAC6F68DA0410BCC87E77F33532D2 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=B48DAC6F68DA0410BCC87E77F33532D2 --renderer-client-id=5 --mojo-platform-channel-handle=1920 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3108 | "C:\Users\admin\AppData\Local\Temp\Version X.exe" | C:\Users\admin\AppData\Local\Temp\Version X.exe | — | explorer.exe | |||||||||||
User: admin Company: にち퓽てािैगदいि てㅁちくगはगगपいㅇㄱаीなगगㅈち Integrity Level: MEDIUM Description: юみिаㅇなく뮻뎢らैुगनीはै ीくてैはुにदたिगたてちग Exit code: 0 Version: 0.6.8.1 Modules
| |||||||||||||||
| 3384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,4974558090564079742,1667303585134418299,131072 --enable-features=PasswordImport --service-pipe-token=CD9086DA6CF59648DDD2772C7AAD6C3B --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=CD9086DA6CF59648DDD2772C7AAD6C3B --renderer-client-id=3 --mojo-platform-channel-handle=2040 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=948,4974558090564079742,1667303585134418299,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=F31377B19EA4A2C435180C51271A15D3 --mojo-platform-channel-handle=944 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3372 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 4076 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
Total events
536
Read events
487
Write events
46
Delete events
3
Modification events
| (PID) Process: | (2340) Regasm.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3384) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3384-13192683284203000 |
Value: 259 | |||
| (PID) Process: | (3384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
2
Suspicious files
37
Text files
61
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2340 | Regasm.exe | C:\Users\admin\AppData\Roaming\windowsmsc.dll | — | |
MD5:— | SHA256:— | |||
| 2340 | Regasm.exe | C:\Users\admin\AppData\Local\Temp\Cab75CD.tmp | — | |
MD5:— | SHA256:— | |||
| 2340 | Regasm.exe | C:\Users\admin\AppData\Local\Temp\Tar75CE.tmp | — | |
MD5:— | SHA256:— | |||
| 2340 | Regasm.exe | C:\Users\admin\AppData\Local\Temp\Cab75DE.tmp | — | |
MD5:— | SHA256:— | |||
| 2340 | Regasm.exe | C:\Users\admin\AppData\Local\Temp\Tar75DF.tmp | — | |
MD5:— | SHA256:— | |||
| 2340 | Regasm.exe | C:\Users\admin\AppData\Local\Temp\Cab762E.tmp | — | |
MD5:— | SHA256:— | |||
| 2340 | Regasm.exe | C:\Users\admin\AppData\Local\Temp\Tar762F.tmp | — | |
MD5:— | SHA256:— | |||
| 3384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1bac8504-6842-4166-8c6a-f9e2994efe06.tmp | — | |
MD5:— | SHA256:— | |||
| 3384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
12
DNS requests
10
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2340 | Regasm.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2340 | Regasm.exe | 185.114.225.187:9171 | notbloxy.duckdns.org | i3D.net B.V | NL | malicious |
2340 | Regasm.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3384 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3384 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3384 | chrome.exe | 216.58.207.67:443 | www.google.de | Google Inc. | US | whitelisted |
3384 | chrome.exe | 172.217.23.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3384 | chrome.exe | 216.58.210.4:443 | www.google.com | Google Inc. | US | whitelisted |
3384 | chrome.exe | 216.58.207.78:443 | apis.google.com | Google Inc. | US | whitelisted |
3384 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
notbloxy.duckdns.org |
| malicious |
www.download.windowsupdate.com |
| whitelisted |
www.google.de |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
2340 | Regasm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Observed Malicious SSL Certificate (Orcus RAT) |
2340 | Regasm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Observed Malicious SSL Certificate (Orcus RAT) |
2340 | Regasm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Malicious SSL connection (Orcus RAT) pkt checker #1 |
1 ETPRO signatures available at the full report