| File name: | 123.exe |
| Full analysis: | https://app.any.run/tasks/860f539e-8c33-42a6-9843-220bb9c23392 |
| Verdict: | Malicious activity |
| Threats: | Orcus is a modular Remote Access Trojan with some unusual functions. This RAT enables attackers to create plugins using a custom development library and offers a robust core feature set that makes it one of the most dangerous malicious programs in its class. |
| Analysis date: | April 01, 2023, 13:13:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 8CE35F432328FB6434AE7CF8DF4E0CFA |
| SHA1: | 72F6F75E369C35E9ACCEE972ABCDD287609897DE |
| SHA256: | B45A27DF015D267370061BD31378EB681DD2812C73F73A7BD07B15770FAA170E |
| SSDEEP: | 24576:ZiC4MROxnFgjsyrrcI0AilFEvxHP47oob:ZuMiZyrrcI0AilFEvxHP |
MALICIOUS
Orcus is detected
- 123.exe (PID: 2696)
- 123.exe (PID: 3728)
- Orcus.exe (PID: 2964)
ORCUS was detected
- Orcus.exe (PID: 2964)
ORCUS detected by memory dumps
- Orcus.exe (PID: 2964)
Loads dropped or rewritten executable
- Orcus.exe (PID: 2964)
SUSPICIOUS
Reads the Internet Settings
- 123.exe (PID: 2696)
- eventvwr.exe (PID: 3724)
- 123.exe (PID: 3728)
- Orcus.exe (PID: 2964)
Executable content was dropped or overwritten
- 123.exe (PID: 3728)
- Orcus.exe (PID: 2964)
Starts itself from another location
- 123.exe (PID: 3728)
Connects to unusual port
- Orcus.exe (PID: 2964)
Reads settings of System Certificates
- Orcus.exe (PID: 2964)
Reads the Windows owner or organization settings
- Orcus.exe (PID: 2964)
INFO
Reads the computer name
- 123.exe (PID: 2696)
- 123.exe (PID: 3728)
- Orcus.exe (PID: 2964)
- wmpnscfg.exe (PID: 3700)
Checks supported languages
- 123.exe (PID: 2696)
- 123.exe (PID: 3728)
- wmpnscfg.exe (PID: 3700)
- Orcus.exe (PID: 2964)
The process checks LSA protection
- 123.exe (PID: 2696)
- eventvwr.exe (PID: 3724)
- 123.exe (PID: 3728)
- Orcus.exe (PID: 2964)
- wmpnscfg.exe (PID: 3700)
- dllhost.exe (PID: 1296)
Reads the machine GUID from the registry
- 123.exe (PID: 2696)
- 123.exe (PID: 3728)
- Orcus.exe (PID: 2964)
- wmpnscfg.exe (PID: 3700)
Reads Environment values
- 123.exe (PID: 3728)
- Orcus.exe (PID: 2964)
Creates files or folders in the user directory
- 123.exe (PID: 3728)
- Orcus.exe (PID: 2964)
Creates files in the program directory
- 123.exe (PID: 3728)
Manual execution by a user
- wmpnscfg.exe (PID: 3700)
- WINWORD.EXE (PID: 1584)
Create files in a temporary directory
- Orcus.exe (PID: 2964)
Reads CPU info
- Orcus.exe (PID: 2964)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Orcus
(PID) Process(2964) Orcus.exe
C2 (2)192.168.0.200:1604
212.ip.ply.gg:21954
Keys
AES51aa23aac719275b34e333d8fdfdcac25967d4101ad3406c1ac9769bd1835d9a
Salt
Options
AutostartBuilderProperty
AutostartMethodDisable
TaskSchedulerTaskNameOrcus
TaskHighestPrivilegestrue
RegistryHiddenStarttrue
RegistryKeyNameOrcus
TryAllAutostartMethodsOnFailtrue
ChangeAssemblyInformationBuilderProperty
ChangeAssemblyInformationfalse
AssemblyTitlenull
AssemblyDescriptionnull
AssemblyCompanyNamenull
AssemblyProductNamenull
AssemblyCopyrightnull
AssemblyTrademarksnull
AssemblyProductVersion1.0.0.0
AssemblyFileVersion1.0.0.0
ChangeCreationDateBuilderProperty
IsEnabledfalse
NewCreationDate2023-04-01T16:06:15
ChangeIconBuilderProperty
ChangeIconfalse
IconPathnull
ClientTagBuilderProperty
ClientTagHacked
DataFolderBuilderProperty
Path%appdata%\Orcus
DefaultPrivilegesBuilderProperty
RequireAdministratorRightsfalse
DisableInstallationPromptBuilderProperty
IsDisabledtrue
FrameworkVersionBuilderProperty
FrameworkVersionNET45
HideFileBuilderProperty
HideFilefalse
InstallationLocationBuilderProperty
Path%programfiles%\Orcus\Orcus.exe
InstallBuilderProperty
Installtrue
KeyloggerBuilderProperty
IsEnabledfalse
MutexBuilderProperty
Mutex3a123d24fb5344d1b5cc1b33b628bfec
ProxyBuilderProperty
ProxyOptionNone
ProxyAddressnull
ProxyPort1080
ProxyType2
ReconnectDelayProperty
Delay10000
RequireAdministratorPrivilegesInstallerBuilderProperty
RequireAdministratorPrivilegestrue
RespawnTaskBuilderProperty
IsEnabledfalse
TaskNameOrcus Respawner
ServiceBuilderProperty
Installfalse
SetRunProgramAsAdminFlagBuilderProperty
SetFlagfalse
WatchdogBuilderProperty
IsEnabledfalse
NameOrcusWatchdog.exe
WatchdogLocationAppData
PreventFileDeletionfalse
Plugins
PluginNameBSoD Protection
PluginVersion2.0
ResourceName99a6eab2959b4562bcd38daf7e585440
ResourceTypeClientPlugin
Guiddccbc1db-f7d1-413d-bba4-72611d485d3a
PluginNameDisable Webcam Lights
PluginVersion1.0
ResourceName79dac1b2990f47e9801c721d46d68608
ResourceTypeClientPlugin
Guide6ee5674-bb94-46c7-8bbc-5729af6e2c28
PluginNameSilent Elevation
PluginVersion1.5
ResourceName91e9f74edfb14dd1852a51ea9c3ae62b
ResourceTypeClientPlugin
Guid0a189c79-87ca-4d8d-bfb5-fac811f4048e
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| AssemblyVersion: | 1.0.0.0 |
|---|---|
| ProductVersion: | 1.0.0.0 |
| ProductName: | - |
| OriginalFileName: | Orcus.exe |
| LegalTrademarks: | - |
| LegalCopyright: | - |
| InternalName: | Orcus.exe |
| FileVersion: | 1.0.0.0 |
| FileDescription: | - |
| CompanyName: | - |
| Comments: | - |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0xe504e |
| UninitializedDataSize: | - |
| InitializedDataSize: | 4608 |
| CodeSize: | 930304 |
| LinkerVersion: | 8 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2023:04:01 13:07:12+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Apr-2023 13:07:12 |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| InternalName: | Orcus.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | Orcus.exe |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 01-Apr-2023 13:07:12 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000E3054 | 0x000E3200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.15618 |
.rsrc | 0x000E6000 | 0x00001000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.99406 |
.reloc | 0x000E8000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0980042 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.99793 | 3128 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
54
Monitored processes
8
Malicious processes
4
Suspicious processes
0
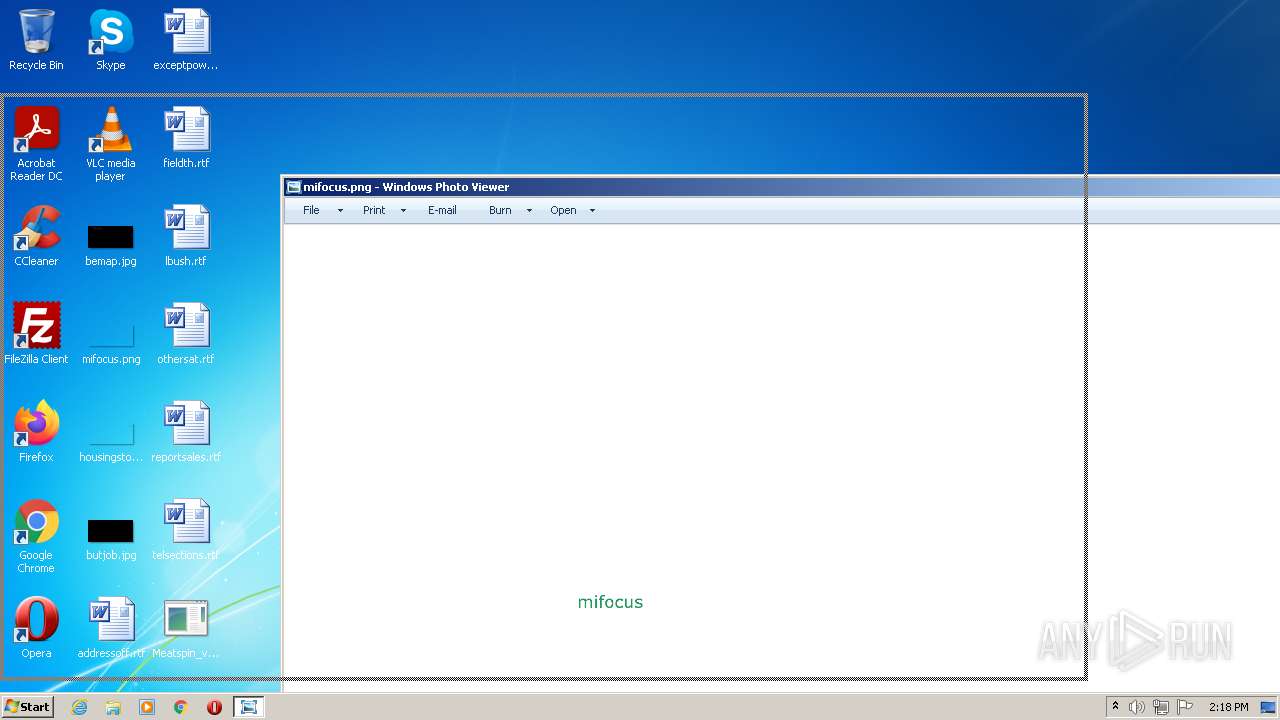
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1296 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1584 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\lbush.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2696 | "C:\Users\admin\AppData\Local\Temp\123.exe" | C:\Users\admin\AppData\Local\Temp\123.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2964 | "C:\Program Files\Orcus\Orcus.exe" | C:\Program Files\Orcus\Orcus.exe | 123.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
Orcus(PID) Process(2964) Orcus.exe C2 (2)192.168.0.200:1604 212.ip.ply.gg:21954 Keys AES51aa23aac719275b34e333d8fdfdcac25967d4101ad3406c1ac9769bd1835d9a Salt Options AutostartBuilderProperty AutostartMethodDisable TaskSchedulerTaskNameOrcus TaskHighestPrivilegestrue RegistryHiddenStarttrue RegistryKeyNameOrcus TryAllAutostartMethodsOnFailtrue ChangeAssemblyInformationBuilderProperty ChangeAssemblyInformationfalse AssemblyTitlenull AssemblyDescriptionnull AssemblyCompanyNamenull AssemblyProductNamenull AssemblyCopyrightnull AssemblyTrademarksnull AssemblyProductVersion1.0.0.0 AssemblyFileVersion1.0.0.0 ChangeCreationDateBuilderProperty IsEnabledfalse NewCreationDate2023-04-01T16:06:15 ChangeIconBuilderProperty ChangeIconfalse IconPathnull ClientTagBuilderProperty ClientTagHacked DataFolderBuilderProperty Path%appdata%\Orcus DefaultPrivilegesBuilderProperty RequireAdministratorRightsfalse DisableInstallationPromptBuilderProperty IsDisabledtrue FrameworkVersionBuilderProperty FrameworkVersionNET45 HideFileBuilderProperty HideFilefalse InstallationLocationBuilderProperty Path%programfiles%\Orcus\Orcus.exe InstallBuilderProperty Installtrue KeyloggerBuilderProperty IsEnabledfalse MutexBuilderProperty Mutex3a123d24fb5344d1b5cc1b33b628bfec ProxyBuilderProperty ProxyOptionNone ProxyAddressnull ProxyPort1080 ProxyType2 ReconnectDelayProperty Delay10000 RequireAdministratorPrivilegesInstallerBuilderProperty RequireAdministratorPrivilegestrue RespawnTaskBuilderProperty IsEnabledfalse TaskNameOrcus Respawner ServiceBuilderProperty Installfalse SetRunProgramAsAdminFlagBuilderProperty SetFlagfalse WatchdogBuilderProperty IsEnabledfalse NameOrcusWatchdog.exe WatchdogLocationAppData PreventFileDeletionfalse Plugins PluginNameBSoD Protection PluginVersion2.0 ResourceName99a6eab2959b4562bcd38daf7e585440 ResourceTypeClientPlugin Guiddccbc1db-f7d1-413d-bba4-72611d485d3a PluginNameDisable Webcam Lights PluginVersion1.0 ResourceName79dac1b2990f47e9801c721d46d68608 ResourceTypeClientPlugin Guide6ee5674-bb94-46c7-8bbc-5729af6e2c28 PluginNameSilent Elevation PluginVersion1.5 ResourceName91e9f74edfb14dd1852a51ea9c3ae62b ResourceTypeClientPlugin Guid0a189c79-87ca-4d8d-bfb5-fac811f4048e | |||||||||||||||
| 3108 | "C:\Windows\System32\eventvwr.exe" | C:\Windows\System32\eventvwr.exe | — | 123.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Event Viewer Snapin Launcher Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3700 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3724 | "C:\Windows\System32\eventvwr.exe" | C:\Windows\System32\eventvwr.exe | 123.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Event Viewer Snapin Launcher Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3728 | "C:\Users\admin\AppData\Local\Temp\123.exe" | C:\Users\admin\AppData\Local\Temp\123.exe | eventvwr.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
18 856
Read events
18 388
Write events
170
Delete events
298
Modification events
| (PID) Process: | (2696) 123.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2696) 123.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2696) 123.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2696) 123.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3724) eventvwr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3724) eventvwr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3724) eventvwr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3724) eventvwr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3728) 123.exe | Key: | HKEY_CLASSES_ROOT\mscfile\shell\open\command |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3728) 123.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
22
Suspicious files
12
Text files
16
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1584 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6038.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3728 | 123.exe | C:\Users\admin\AppData\Roaming\Orcus\err_3a123d24fb5344d1b5cc1b33b628bfec.dat | text | |
MD5:— | SHA256:— | |||
| 2964 | Orcus.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 3728 | 123.exe | C:\Program Files\Orcus\Orcus.exe | executable | |
MD5:— | SHA256:— | |||
| 2964 | Orcus.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:E71C8443AE0BC2E282C73FAEAD0A6DD3 | SHA256:95B0A5ACC5BF70D3ABDFD091D0C9F9063AA4FDE65BD34DBF16786082E1992E72 | |||
| 2964 | Orcus.exe | C:\Users\admin\AppData\Roaming\Orcus\plg_3a123d24fb5344d1b5cc1b33b628bfec\7e3ec7eec72244d8ab73154728e6c00f_1.2 | compressed | |
MD5:DF0D0B4BD309E9E55F4710C60D103630 | SHA256:FCD4FBEC90CCE3171FB725B6F048CC88C8F9CE4EFA5244E81383E1C425C275EB | |||
| 2964 | Orcus.exe | C:\Users\admin\AppData\Roaming\Orcus\lib_3a123d24fb5344d1b5cc1b33b628bfec\SharpDX.Direct3D11.dll | executable | |
MD5:98EB5BA5871ACDEAEBF3A3B0F64BE449 | SHA256:D7617D926648849CBFEF450B8F48E458EE52E2793FB2251A30094B778AA8848C | |||
| 2964 | Orcus.exe | C:\Users\admin\AppData\Roaming\Orcus\lib_3a123d24fb5344d1b5cc1b33b628bfec\SharpDX.DXGI.dll | executable | |
MD5:2B44C70C49B70D797FBB748158B5D9BB | SHA256:3762D43C83AF69CD38C9341A927CA6BD00F6BAE8217C874D693047D6DF4705BF | |||
| 2964 | Orcus.exe | C:\Users\admin\AppData\Roaming\Orcus\lib_3a123d24fb5344d1b5cc1b33b628bfec\TurboJpegWrapper.dll | executable | |
MD5:AC6ACC235EBEF6374BED71B37E322874 | SHA256:047B042CEBF4C851F0D14F85F16CE952F03E48C20362D4ED9390875D4900FE96 | |||
| 2964 | Orcus.exe | C:\Users\admin\AppData\Roaming\Orcus\lib_3a123d24fb5344d1b5cc1b33b628bfec\SharpDX.Direct3D9.dll | executable | |
MD5:934DA0E49208D0881C44FE19D5033840 | SHA256:02DA4AF8CD4A8DE19D816000CAAAE885E676B9E52F136FF071A279C2B8AD34C7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
5
DNS requests
3
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2964 | Orcus.exe | GET | 200 | 67.27.233.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?c6d9b27f0051f5d0 | US | compressed | 61.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2964 | Orcus.exe | 209.25.141.212:21954 | 212.ip.ply.gg | PLAYIT-GG | US | malicious |
2964 | Orcus.exe | 67.27.233.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
— | — | 192.168.100.37:49174 | — | — | — | malicious |
— | — | 192.168.100.37:49313 | — | — | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dl.n1ckna.me |
| unknown |
212.ip.ply.gg |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2964 | Orcus.exe | Generic Protocol Command Decode | SURICATA STREAM bad window update |
2964 | Orcus.exe | Generic Protocol Command Decode | SURICATA STREAM bad window update |
1 ETPRO signatures available at the full report