| File name: | Endermanch@Cerber5.exe |
| Full analysis: | https://app.any.run/tasks/3f616d0d-4b4c-4d03-9185-4c0c3134e8cb |
| Verdict: | Malicious activity |
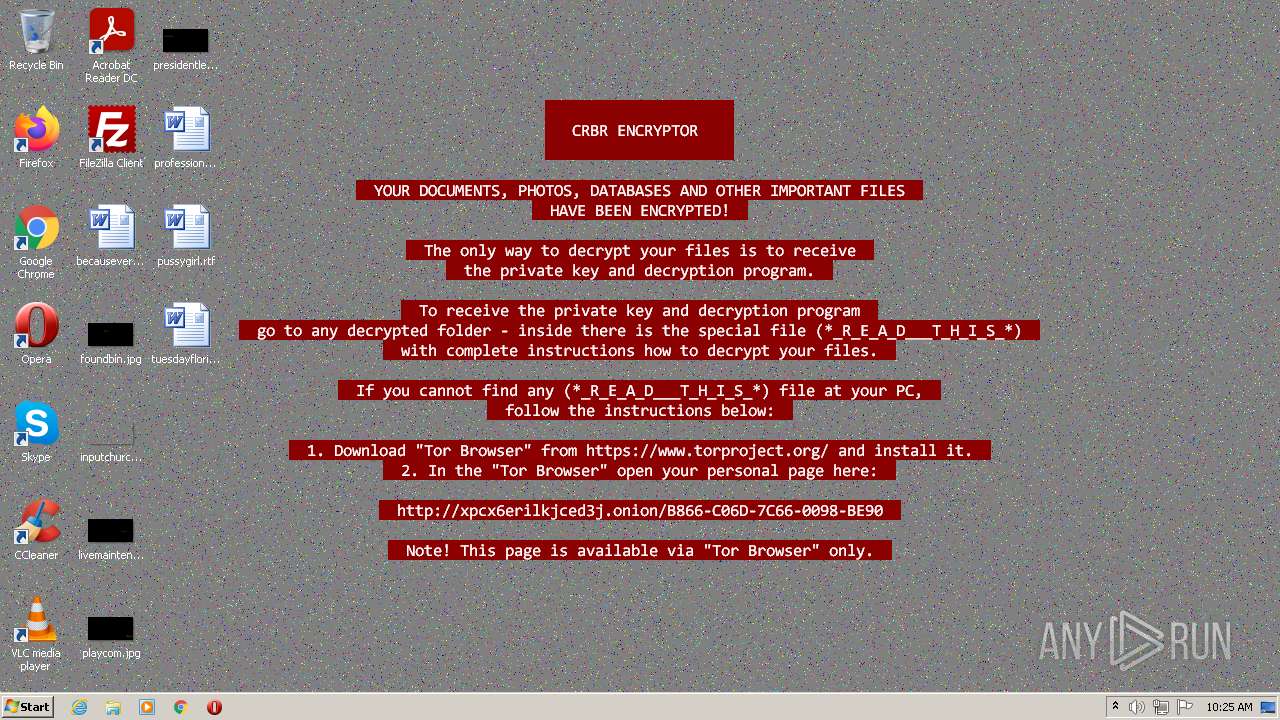
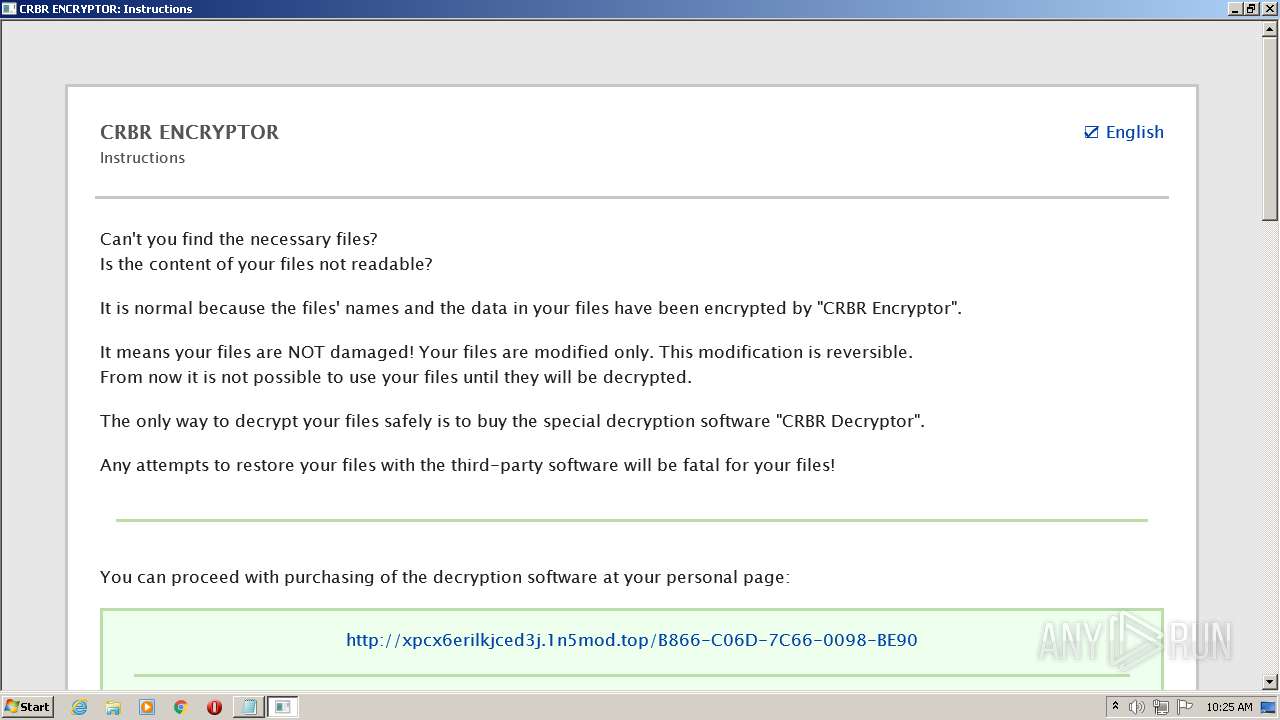
| Threats: | Cerber is a Ransomware-as-a-Service (RaaS) that appeared in 2016, spread quickly and has been evolving since. It became well-known for its file encryption, offline capabilities, and sophisticated evasion techniques. It primarily targets enterprises, financial institutions, and government entities, encrypting their data and demanding ransom payments in Bitcoin. It also targets everyday users encrypting personal files (photos, documents) with the risk of their permanent loss. |
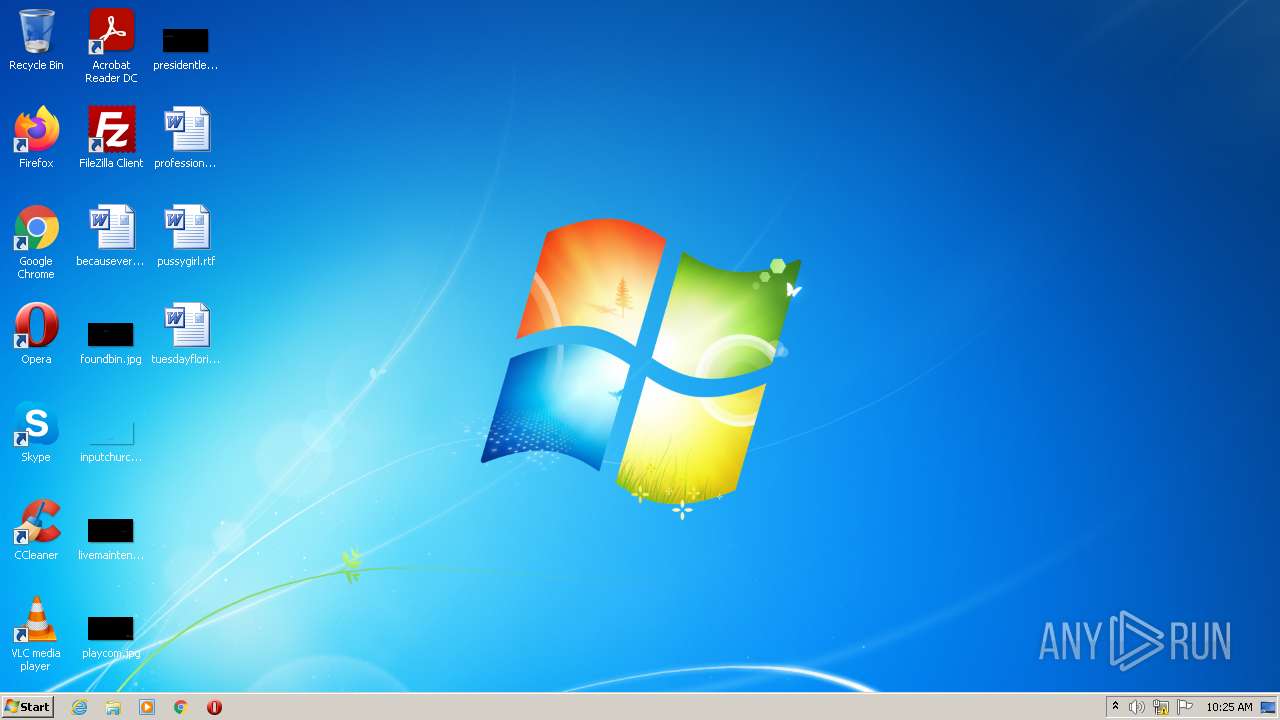
| Analysis date: | February 05, 2022, 10:25:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FE1BC60A95B2C2D77CD5D232296A7FA4 |
| SHA1: | C07DFDEA8DA2DA5BAD036E7C2F5D37582E1CF684 |
| SHA256: | B3E1E9D97D74C416C2A30DD11858789AF5554CF2DE62F577C13944A19623777D |
| SSDEEP: | 6144:nl578cxdGY87FohbnmM2i8ito7wTmCbL94KCT3OAmK:nl59zH8MiM2z+NLQBN |
MALICIOUS
CERBER was detected
- Endermanch@Cerber5.exe (PID: 2988)
Actions looks like stealing of personal data
- Endermanch@Cerber5.exe (PID: 2988)
Connects to CnC server
- Endermanch@Cerber5.exe (PID: 2988)
Dropped file may contain instructions of ransomware
- Endermanch@Cerber5.exe (PID: 2988)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 440)
SUSPICIOUS
Reads the computer name
- Endermanch@Cerber5.exe (PID: 2988)
- mshta.exe (PID: 1168)
Checks supported languages
- Endermanch@Cerber5.exe (PID: 2988)
- mshta.exe (PID: 1168)
- cmd.exe (PID: 440)
Creates files in the user directory
- Endermanch@Cerber5.exe (PID: 2988)
Creates files like Ransomware instruction
- Endermanch@Cerber5.exe (PID: 2988)
Starts MSHTA.EXE for opening HTA or HTMLS files
- Endermanch@Cerber5.exe (PID: 2988)
Reads Microsoft Outlook installation path
- mshta.exe (PID: 1168)
Starts CMD.EXE for self-deleting
- Endermanch@Cerber5.exe (PID: 2988)
Starts CMD.EXE for commands execution
- Endermanch@Cerber5.exe (PID: 2988)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 440)
INFO
Dropped object may contain Bitcoin addresses
- Endermanch@Cerber5.exe (PID: 2988)
- mshta.exe (PID: 1168)
Checks supported languages
- NOTEPAD.EXE (PID: 2292)
- taskkill.exe (PID: 3344)
- PING.EXE (PID: 2452)
Dropped object may contain TOR URL's
- Endermanch@Cerber5.exe (PID: 2988)
Dropped object may contain URL to Tor Browser
- Endermanch@Cerber5.exe (PID: 2988)
Reads internet explorer settings
- mshta.exe (PID: 1168)
Reads the computer name
- taskkill.exe (PID: 3344)
- PING.EXE (PID: 2452)
Checks Windows Trust Settings
- mshta.exe (PID: 1168)
Reads settings of System Certificates
- mshta.exe (PID: 1168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| ProductVersion: | 2, 7, 0, 1 |
|---|---|
| ProductName: | PDF Writer Application |
| OriginalFileName: | PDFWriter.EXE |
| LegalTrademarks: | PDF Writer |
| LegalCopyright: | Copyright © 2010 by Acro Software Inc., All Rights Reserved |
| InternalName: | PDF Writer |
| FileVersion: | 2, 7, 7, 1 |
| FileDescription: | PDF Writer Application |
| CompanyName: | Acro Software Inc. |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 2.7.0.1 |
| FileVersionNumber: | 2.7.7.1 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x497a0 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 14336 |
| CodeSize: | 300032 |
| LinkerVersion: | 9 |
| PEType: | PE32 |
| TimeStamp: | 2017:07:22 11:03:05+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Jul-2017 09:03:05 |
| Detected languages: |
|
| CompanyName: | Acro Software Inc. |
| FileDescription: | PDF Writer Application |
| FileVersion: | 2, 7, 7, 1 |
| InternalName: | PDF Writer |
| LegalCopyright: | Copyright © 2010 by Acro Software Inc., All Rights Reserved |
| LegalTrademarks: | PDF Writer |
| OriginalFilename: | PDFWriter.EXE |
| ProductName: | PDF Writer Application |
| ProductVersion: | 2, 7, 0, 1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 22-Jul-2017 09:03:05 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000493E5 | 0x00049400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.29041 |
.rdata | 0x0004B000 | 0x0000291E | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.6835 |
.data | 0x0004E000 | 0x000001A8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.70459 |
.rsrc | 0x0004F000 | 0x00000B30 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.6284 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.42914 | 920 | UNKNOWN | English - United States | RT_VERSION |
2 | 3.43321 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 3.20549 | 506 | UNKNOWN | English - United States | RT_DIALOG |
128 | 2.22208 | 34 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
msvcrt.dll |
Total processes
44
Monitored processes
6
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | "C:\Windows\system32\cmd.exe" /d /c taskkill /f /im "E" > NUL & ping -n 1 127.0.0.1 > NUL & del "C" > NUL && exit | C:\Windows\system32\cmd.exe | — | Endermanch@Cerber5.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1168 | "C:\Windows\System32\mshta.exe" "C:\Users\admin\Desktop\_R_E_A_D___T_H_I_S___QYVLV17J_.hta" | C:\Windows\System32\mshta.exe | Endermanch@Cerber5.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2292 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\_R_E_A_D___T_H_I_S___LGQC36_.txt | C:\Windows\system32\NOTEPAD.EXE | — | Endermanch@Cerber5.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2452 | ping -n 1 127.0.0.1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2988 | "C:\Users\admin\AppData\Local\Temp\Endermanch@Cerber5.exe" | C:\Users\admin\AppData\Local\Temp\Endermanch@Cerber5.exe | Explorer.EXE | ||||||||||||
User: admin Company: Acro Software Inc. Integrity Level: MEDIUM Description: PDF Writer Application Exit code: 0 Version: 2, 7, 7, 1 Modules
| |||||||||||||||
| 3344 | taskkill /f /im "E" | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 822
Read events
5 765
Write events
57
Delete events
0
Modification events
| (PID) Process: | (2988) Endermanch@Cerber5.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2988) Endermanch@Cerber5.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @"C:\Windows\system32\windowspowershell\v1.0\powershell.exe",-103 |
Value: Windows PowerShell Script | |||
| (PID) Process: | (2988) Endermanch@Cerber5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2988) Endermanch@Cerber5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2988) Endermanch@Cerber5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2988) Endermanch@Cerber5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1168) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1168) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1168) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1168) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
15
Text files
46
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2988 | Endermanch@Cerber5.exe | C:\Users\admin\AppData\Local\Temp\90059c37\41a4.tmp | text | |
MD5:B866C06D7C660FEF48ECBED9E71E685E | SHA256:AC7D23D62D491B9C6B5E22DEE90184B3EEB99140A540AA9B0B68CE58E47D19C9 | |||
| 2988 | Endermanch@Cerber5.exe | C:\Users\admin\AppData\Local\Temp\90059c37\1320.tmp | binary | |
MD5:263D8D9045EC7E9CF4140F2D1008A3D3 | SHA256:22ECE275E0A467C31C75F42A91AFB42D32BE2DC4AAF25B1D17D678E05DC2E76C | |||
| 2988 | Endermanch@Cerber5.exe | C:\users\admin\appdata\roaming\microsoft\onenote\14.0\_R_E_A_D___T_H_I_S___NMWB_.hta | html | |
MD5:88F22D35F877E78D4DEFC3697B585D74 | SHA256:F95406887F8E69779CD7B2A105286314C9E1EE9A9FFDCF45275F8E13E6C996B6 | |||
| 2988 | Endermanch@Cerber5.exe | C:\users\admin\appdata\roaming\microsoft\onenote\14.0\_R_E_A_D___T_H_I_S___YG1U0_.txt | text | |
MD5:BBFC57E80D5159BB625DF6F40C9E7CA3 | SHA256:4F3F2A84F0BF1716EF943636A092A5835F6E50B57BE0C7BD14900D97C81027A0 | |||
| 2988 | Endermanch@Cerber5.exe | C:\users\admin\appdata\roaming\microsoft\onenote\14.0\preferences.dat | binary | |
MD5:9A9A9691232C1C223D23ED617F9F8F70 | SHA256:3A7D4DB8021BD3116F5412EED5679569A8F8ABA24B7824173931D240E849B0DA | |||
| 2988 | Endermanch@Cerber5.exe | C:\users\admin\documents\creditmaps.rtf | text | |
MD5:3F183BA53C87DFC46C785DE3BF067FBD | SHA256:E65BA61E216C4A7073C238D8BB9531EDDAED380F2C3A59A7764393BE59090C7B | |||
| 2988 | Endermanch@Cerber5.exe | C:\users\admin\appdata\roaming\microsoft\outlook\_R_E_A_D___T_H_I_S___0XW969_.txt | text | |
MD5:BBFC57E80D5159BB625DF6F40C9E7CA3 | SHA256:4F3F2A84F0BF1716EF943636A092A5835F6E50B57BE0C7BD14900D97C81027A0 | |||
| 2988 | Endermanch@Cerber5.exe | C:\Users\admin\AppData\Roaming\Microsoft\OneNote\14.0\kR1PCR6ljc.b58d | binary | |
MD5:9A9A9691232C1C223D23ED617F9F8F70 | SHA256:3A7D4DB8021BD3116F5412EED5679569A8F8ABA24B7824173931D240E849B0DA | |||
| 2988 | Endermanch@Cerber5.exe | C:\users\admin\appdata\roaming\microsoft\outlook\outlook.srs | binary | |
MD5:36AB8473CEE3F7B23ABBA45F3EED13F4 | SHA256:6EF4ED2D377C43B988EA2EAD395C52E6C6396B1C86F79C85748DA2C8DA5E05A7 | |||
| 2988 | Endermanch@Cerber5.exe | C:\users\admin\appdata\roaming\microsoft\outlook\test.xml | xml | |
MD5:505EC07DFCC2B511477935539CE86981 | SHA256:941AC818AC3479AAFB75D0725BD43D9E0FC40819076F3DEE1F18294FA0EF05B1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
8
DNS requests
10
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1168 | mshta.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
1168 | mshta.exe | GET | 200 | 104.20.21.251:80 | http://api.blockcypher.com/v1/btc/main/addrs/1CMRScsrxPe2N4HwPpNKcHUhfCJXUm2Cx6?_=1644056726397 | US | compressed | 4.14 Kb | malicious |
1168 | mshta.exe | GET | 200 | 104.20.21.251:80 | http://api.blockcypher.com/v1/btc/main/txs/995afab49dc5a2f77a46f58a9ed65702cf0277f913cfe964b5e756fbc69ea816?_=1644056726710 | US | binary | 755 b | malicious |
1168 | mshta.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEAKRhgUjCVlX4eVtTfjYz8Q%3D | US | der | 278 b | whitelisted |
1168 | mshta.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/rootr1/MEwwSjBIMEYwRDAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCCwQAAAAAAURO8DYx | US | der | 1.41 Kb | whitelisted |
1168 | mshta.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/gsalphasha2g2/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBSE1Wv4CYvTB7dm2OHrrWWWqmtnYQQU9c3VPAhQ%2BWpPOreX2laD5mnSaPcCDGSMnAbUH8%2F7LNnhbA%3D%3D | US | der | 1.40 Kb | whitelisted |
1168 | mshta.exe | GET | 200 | 67.26.83.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6b298cdcaec23998 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1168 | mshta.exe | 178.128.255.179:443 | bitaps.com | Forthnet | GR | malicious |
1168 | mshta.exe | 104.18.20.226:80 | ocsp.globalsign.com | Cloudflare Inc | US | shared |
1168 | mshta.exe | 67.26.83.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | malicious |
1168 | mshta.exe | 172.66.41.18:443 | chain.so | — | US | malicious |
1168 | mshta.exe | 104.20.21.251:80 | api.blockcypher.com | Cloudflare Inc | US | shared |
1168 | mshta.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.blockcypher.com |
| malicious |
btc.blockr.io |
| unknown |
bitaps.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
chain.so |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
xpcx6erilkjced3j.14pxvn.top |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2988 | Endermanch@Cerber5.exe | A Network Trojan was detected | ET TROJAN Ransomware/Cerber Checkin M3 (12) |
— | — | A Network Trojan was detected | ET TROJAN ABUSE.CH Ransomware/Cerber Onion Domain Lookup |
— | — | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
1 ETPRO signatures available at the full report