| File name: | bk_0.1.4.7.exe |
| Full analysis: | https://app.any.run/tasks/ee2f39d0-3679-4a3f-a116-48e52ff1406c |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | May 23, 2025, 13:41:56 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 6C0511FAEA7AD1018EF12EE991D8827C |
| SHA1: | 28837640C9069C6A546C7828490C6D8260DE124C |
| SHA256: | B2E715AC8EF0723EE6D28AAEF075B1ABAAB46F0CD6D953C95C6C39F397A4FA65 |
| SSDEEP: | 49152:8s7SbMdBO9Ev+Uvy6x/HQQ9MgwhdM/p2ocNDdWXujlbBME0HD/0Jfy+K:8seYPO6Xv1Q3gwhUcNDdWXMBOH49LK |
MALICIOUS
Changes the login/logoff helper path in the registry
- reg.exe (PID: 8140)
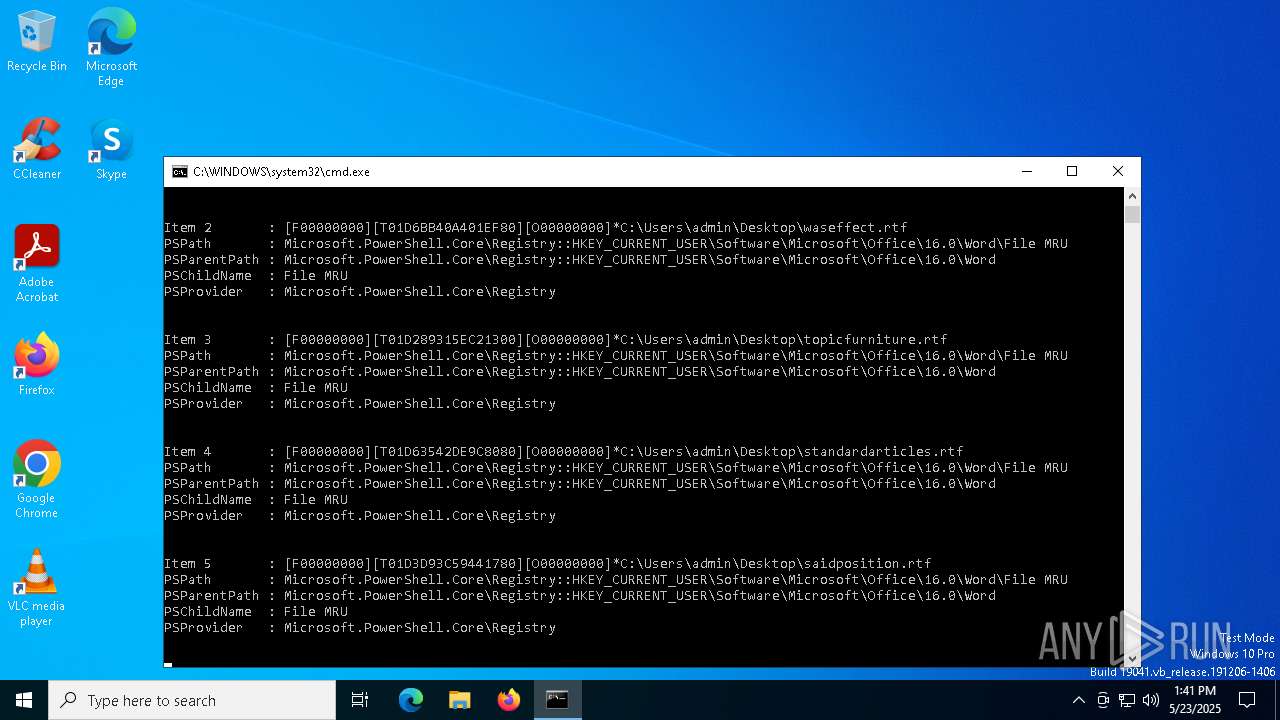
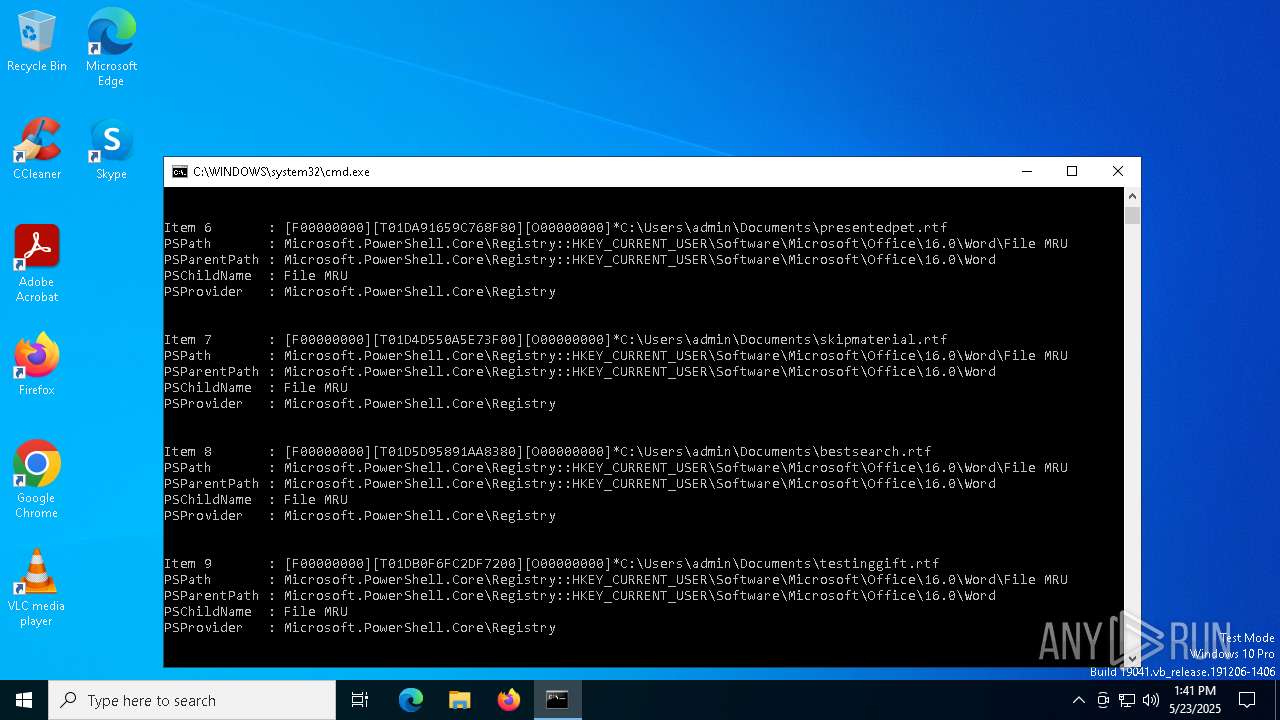
Steals credentials from Web Browsers
- AddInProcess32.exe (PID: 2904)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
- AddInProcess32.exe (PID: 2904)
Connects to the CnC server
- svchost.exe (PID: 2196)
LUMMA mutex has been found
- AddInProcess32.exe (PID: 2904)
Actions looks like stealing of personal data
- AddInProcess32.exe (PID: 2904)
SUSPICIOUS
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 8088)
Starts CMD.EXE for commands execution
- bk_0.1.4.7.exe (PID: 7700)
Executable content was dropped or overwritten
- bk_0.1.4.7.exe (PID: 7700)
Reads security settings of Internet Explorer
- bk_0.1.4.7.exe (PID: 7700)
Connects to unusual port
- InstallUtil.exe (PID: 7268)
Starts itself from another location
- bk_0.1.4.7.exe (PID: 7700)
Contacting a server suspected of hosting an CnC
- AddInProcess32.exe (PID: 2904)
- svchost.exe (PID: 2196)
INFO
Disables trace logs
- bk_0.1.4.7.exe (PID: 7700)
- InstallUtil.exe (PID: 8180)
- InstallUtil.exe (PID: 7268)
Checks supported languages
- bk_0.1.4.7.exe (PID: 7700)
- InstallUtil.exe (PID: 8180)
- InstallUtil.exe (PID: 7268)
- AddInProcess32.exe (PID: 2904)
Reads the machine GUID from the registry
- bk_0.1.4.7.exe (PID: 7700)
- InstallUtil.exe (PID: 8180)
- InstallUtil.exe (PID: 7268)
- AddInProcess32.exe (PID: 2904)
Reads the computer name
- bk_0.1.4.7.exe (PID: 7700)
- InstallUtil.exe (PID: 8180)
- InstallUtil.exe (PID: 7268)
- AddInProcess32.exe (PID: 2904)
Checks proxy server information
- bk_0.1.4.7.exe (PID: 7700)
- InstallUtil.exe (PID: 8180)
- slui.exe (PID: 7224)
- InstallUtil.exe (PID: 7268)
Reads the software policy settings
- bk_0.1.4.7.exe (PID: 7700)
- InstallUtil.exe (PID: 8180)
- InstallUtil.exe (PID: 7268)
- slui.exe (PID: 7224)
- AddInProcess32.exe (PID: 2904)
HTTPDEBUGGER has been detected
- bk_0.1.4.7.exe (PID: 7700)
- InstallUtil.exe (PID: 8180)
Creates files or folders in the user directory
- bk_0.1.4.7.exe (PID: 7700)
Process checks computer location settings
- bk_0.1.4.7.exe (PID: 7700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:02:20 03:09:11+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 1221120 |
| InitializedDataSize: | 17408 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x12c02e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.3.277.63586 |
| ProductVersionNumber: | 1.3.277.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Greenshot |
| FileDescription: | Greenshot |
| FileVersion: | 1.3.277.63586 |
| InternalName: | Greenshot.exe |
| LegalCopyright: | Copyright © Greenshot 2004-2022 |
| OriginalFileName: | Greenshot.exe |
| ProductName: | Greenshot |
| ProductVersion: | 1.3.277+f862e79485 |
| AssemblyVersion: | 1.3.0.0 |
Total processes
134
Monitored processes
12
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2904 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe | InstallUtil.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AddInProcess.exe Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 5428 | "C:\Users\admin\AppData\Local\update.exe" | C:\Users\admin\AppData\Local\update.exe | — | bk_0.1.4.7.exe | |||||||||||
User: admin Company: Greenshot Integrity Level: MEDIUM Description: Greenshot Exit code: 3221226540 Version: 1.3.277.63586 Modules
| |||||||||||||||
| 6388 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe | — | InstallUtil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AddInProcess.exe Exit code: 4294967295 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 7224 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7268 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | bk_0.1.4.7.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 7340 | "C:\Users\admin\AppData\Local\update.exe" | C:\Users\admin\AppData\Local\update.exe | — | bk_0.1.4.7.exe | |||||||||||
User: admin Company: Greenshot Integrity Level: MEDIUM Description: Greenshot Exit code: 3221226540 Version: 1.3.277.63586 Modules
| |||||||||||||||
| 7700 | "C:\Users\admin\Desktop\bk_0.1.4.7.exe" | C:\Users\admin\Desktop\bk_0.1.4.7.exe | explorer.exe | ||||||||||||
User: admin Company: Greenshot Integrity Level: MEDIUM Description: Greenshot Exit code: 0 Version: 1.3.277.63586 Modules
| |||||||||||||||
| 8088 | "cmd.exe" /c REG ADD "HKCU\Software\Microsoft\Windows NT\CurrentVersion\Winlogon" /f /v "Shell" /t REG_SZ /d "explorer.exe,C:\Users\admin\AppData\Local\update.exe," | C:\Windows\SysWOW64\cmd.exe | — | bk_0.1.4.7.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8096 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
18 578
Read events
18 549
Write events
29
Delete events
0
Modification events
| (PID) Process: | (7700) bk_0.1.4.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\bk_0_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7700) bk_0.1.4.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\bk_0_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7700) bk_0.1.4.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\bk_0_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (7700) bk_0.1.4.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\bk_0_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (7700) bk_0.1.4.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\bk_0_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (7700) bk_0.1.4.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\bk_0_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (7700) bk_0.1.4.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\bk_0_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (7700) bk_0.1.4.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\bk_0_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7700) bk_0.1.4.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\bk_0_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7700) bk_0.1.4.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\bk_0_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7700 | bk_0.1.4.7.exe | C:\Users\admin\AppData\Local\update.exe | executable | |
MD5:6C0511FAEA7AD1018EF12EE991D8827C | SHA256:B2E715AC8EF0723EE6D28AAEF075B1ABAAB46F0CD6D953C95C6C39F397A4FA65 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
30
DNS requests
12
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 104.21.32.1:443 | https://i.ibb.co/GvNXNdqD/shiauxc-alvia-first-lookuracship.webp | unknown | image | 3.61 Mb | whitelisted |
2104 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | GET | 200 | 104.21.80.1:443 | https://i.ibb.co/GvNXNdqD/shiauxc-alvia-first-lookuracship.webp | unknown | image | 3.61 Mb | whitelisted |
— | — | POST | 200 | 172.67.222.194:443 | https://narrathfpt.top/tekq | unknown | binary | 32.7 Kb | unknown |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 403 | 104.21.83.105:443 | https://narrathfpt.top/tekq | unknown | html | 4.79 Kb | unknown |
— | — | GET | 200 | 104.22.68.199:443 | https://pastebin.com/raw/Ld9GfkdJ | unknown | text | 13 b | whitelisted |
— | — | POST | 200 | 104.21.83.105:443 | https://narrathfpt.top/tekq | unknown | binary | 69 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7700 | bk_0.1.4.7.exe | 108.181.22.211:443 | i.ibb.co | TELUS Communications | CA | shared |
7556 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8180 | InstallUtil.exe | 108.181.22.211:443 | i.ibb.co | TELUS Communications | CA | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
i.ibb.co |
| shared |
activation-v2.sls.microsoft.com |
| whitelisted |
maxmtsq.bet |
| unknown |
narrathfpt.top |
| unknown |
pastebin.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7700 | bk_0.1.4.7.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image hosting service ImgBB |
8180 | InstallUtil.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image hosting service ImgBB |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
— | — | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (narrathfpt .top) |
2904 | AddInProcess32.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (narrathfpt .top) in TLS SNI |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (maxmtsq .bet) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
2904 | AddInProcess32.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (narrathfpt .top) in TLS SNI |
2904 | AddInProcess32.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (narrathfpt .top) in TLS SNI |