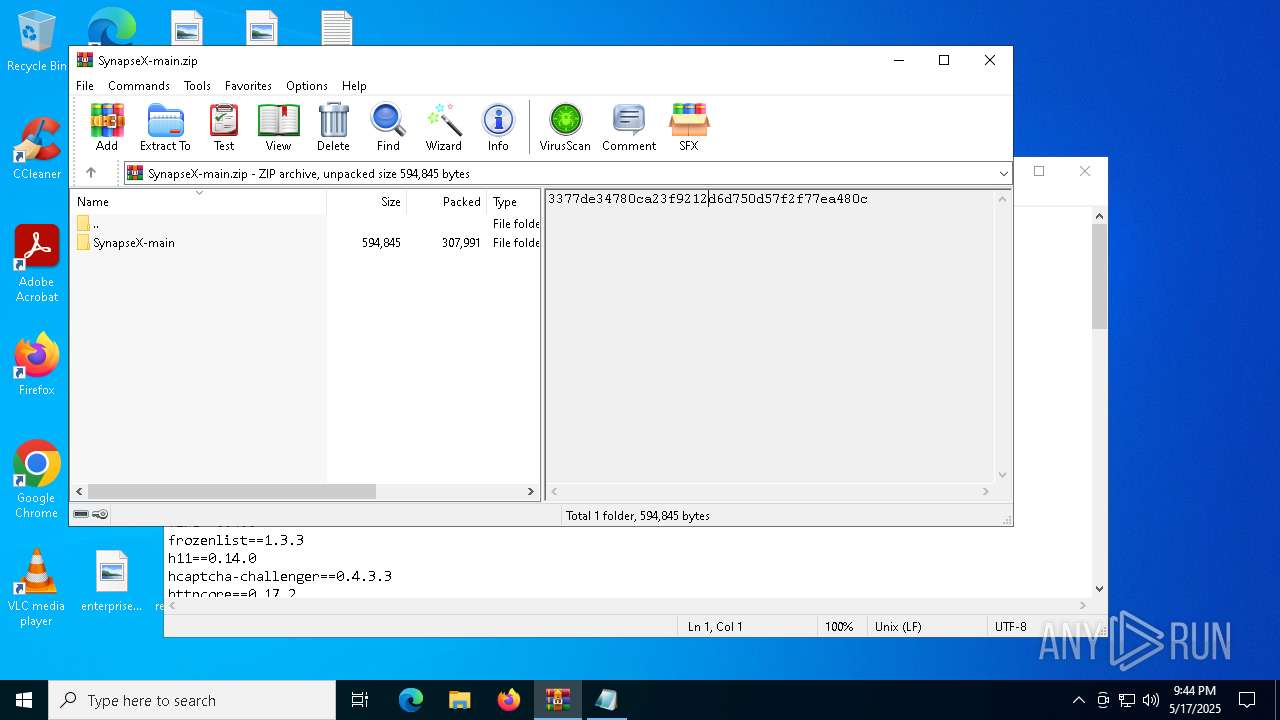
| File name: | SynapseX-main.zip |
| Full analysis: | https://app.any.run/tasks/6bc3aeb8-175b-4884-ab7e-6d3a2f7c743b |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | May 17, 2025, 21:43:53 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | DB76BED0BCB58EC7F089CC6414B39683 |
| SHA1: | 262B4F1C5EA161E9535A0B46E4CD7C6846EB5884 |
| SHA256: | B2D0E3F171A30769D7F5C84749FDA37B3FCCFFAE53CB39EA8378573FCE43161A |
| SSDEEP: | 12288:OWpyaTGNnt5TkCMykHoVO7U/u1x0In3dSaytKU:OWwmGNnt5TkQaql/u1x1NSaytKU |
MALICIOUS
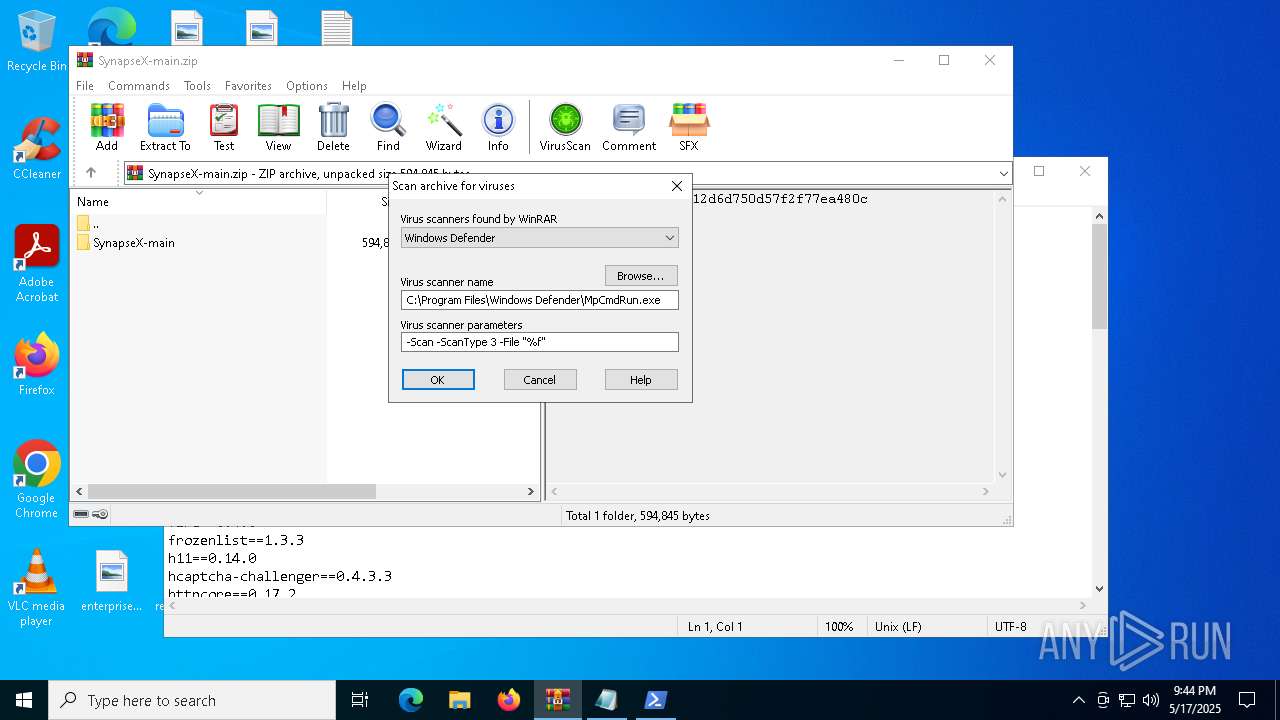
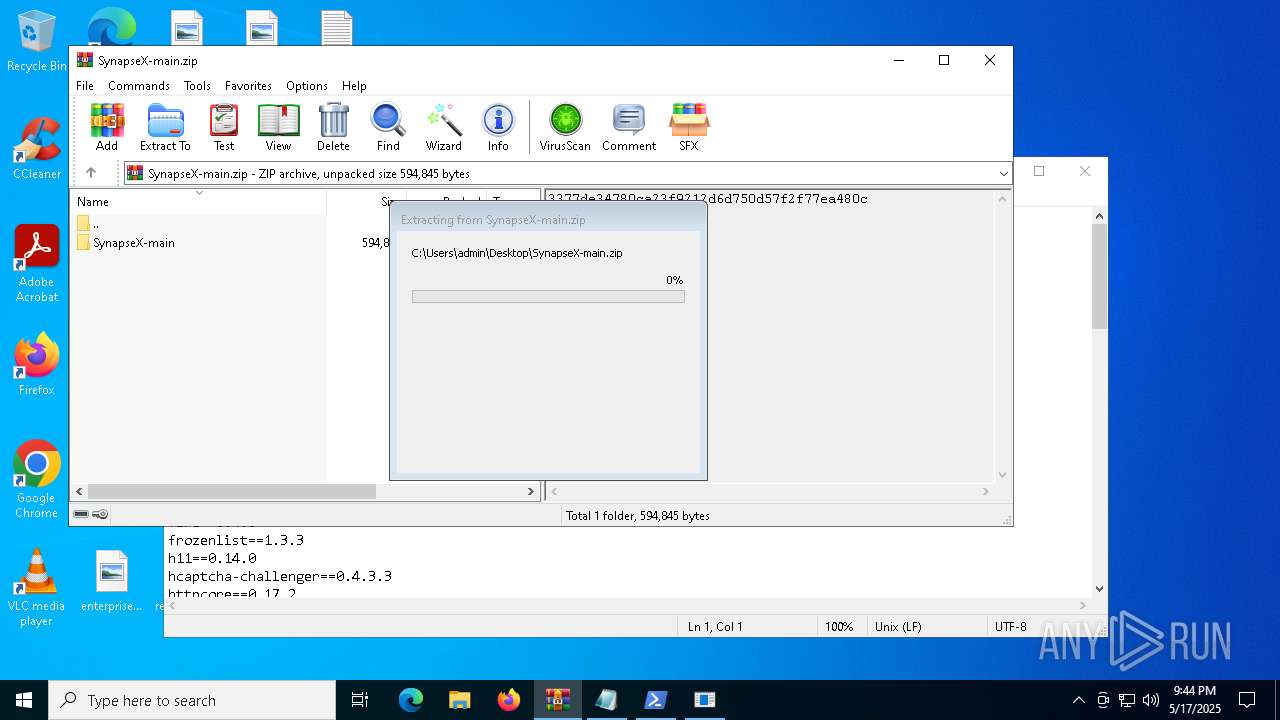
Generic archive extractor
- WinRAR.exe (PID: 7420)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 7820)
STEALER has been found (auto)
- WinRAR.exe (PID: 7420)
Connects to the CnC server
- svchost.exe (PID: 2196)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
- MSBuild.exe (PID: 672)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 7820)
Steals credentials from Web Browsers
- MSBuild.exe (PID: 672)
LUMMA mutex has been found
- MSBuild.exe (PID: 672)
Actions looks like stealing of personal data
- MSBuild.exe (PID: 672)
SUSPICIOUS
Reads security settings of Internet Explorer
- Loader.exe (PID: 7536)
- WinRAR.exe (PID: 7420)
Base64-obfuscated command line is found
- Loader.exe (PID: 7536)
BASE64 encoded PowerShell command has been detected
- Loader.exe (PID: 7536)
Starts POWERSHELL.EXE for commands execution
- Loader.exe (PID: 7536)
- powershell.exe (PID: 7820)
Application launched itself
- powershell.exe (PID: 7820)
Executable content was dropped or overwritten
- powershell.exe (PID: 7820)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- MSBuild.exe (PID: 672)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
- MSBuild.exe (PID: 672)
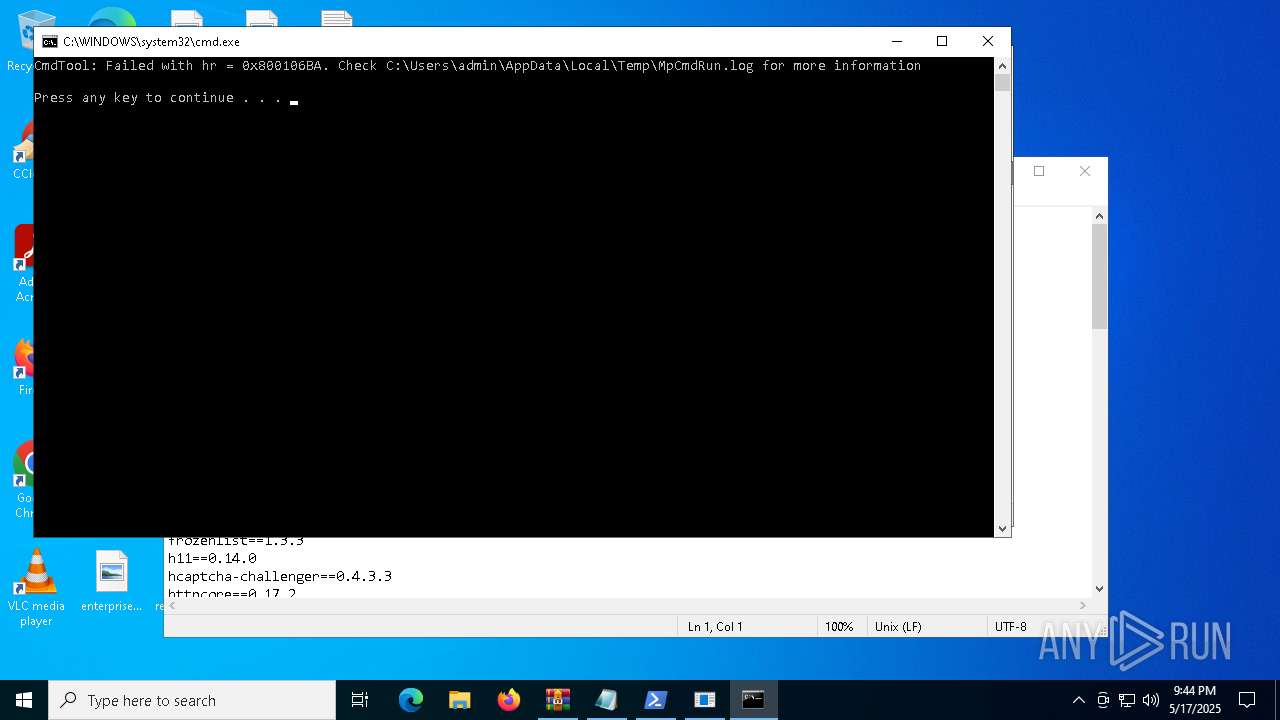
Executing commands from a ".bat" file
- WinRAR.exe (PID: 7420)
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 7420)
Searches for installed software
- MSBuild.exe (PID: 672)
INFO
Create files in a temporary directory
- Loader.exe (PID: 7536)
- powershell.exe (PID: 8084)
- MpCmdRun.exe (PID: 7156)
Reads the computer name
- Loader.exe (PID: 7536)
- MSBuild.exe (PID: 672)
- MpCmdRun.exe (PID: 7156)
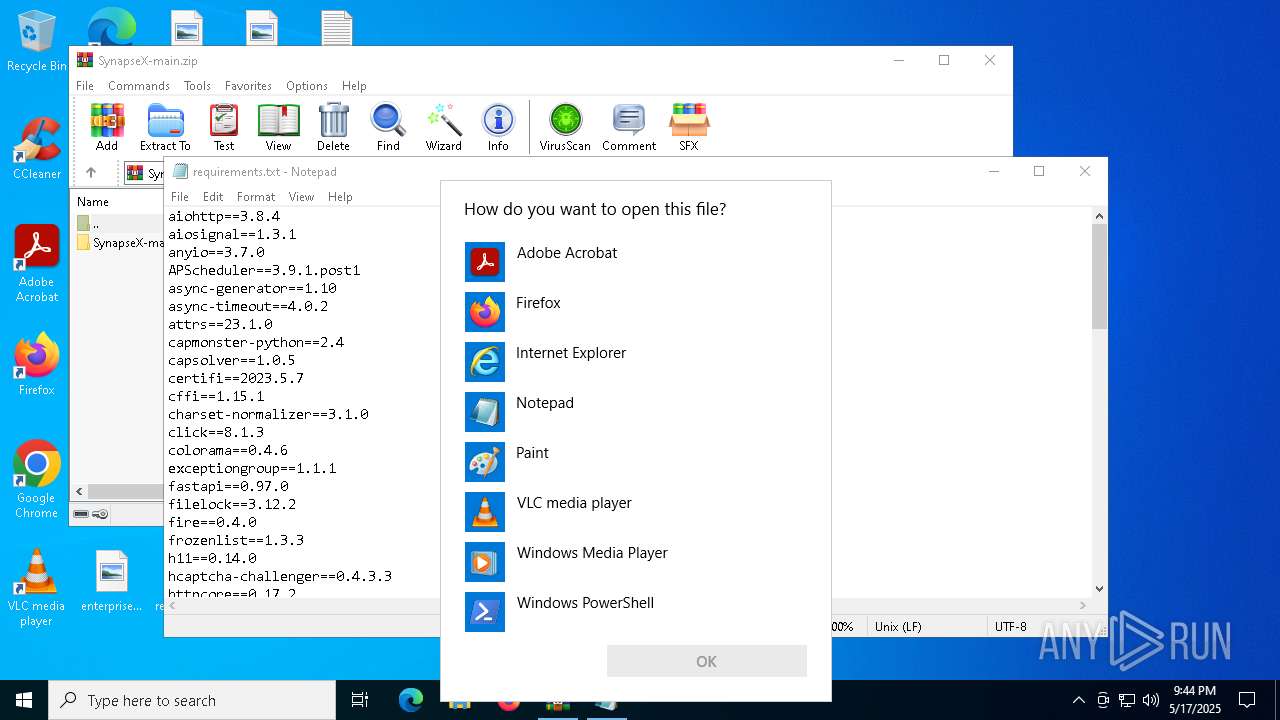
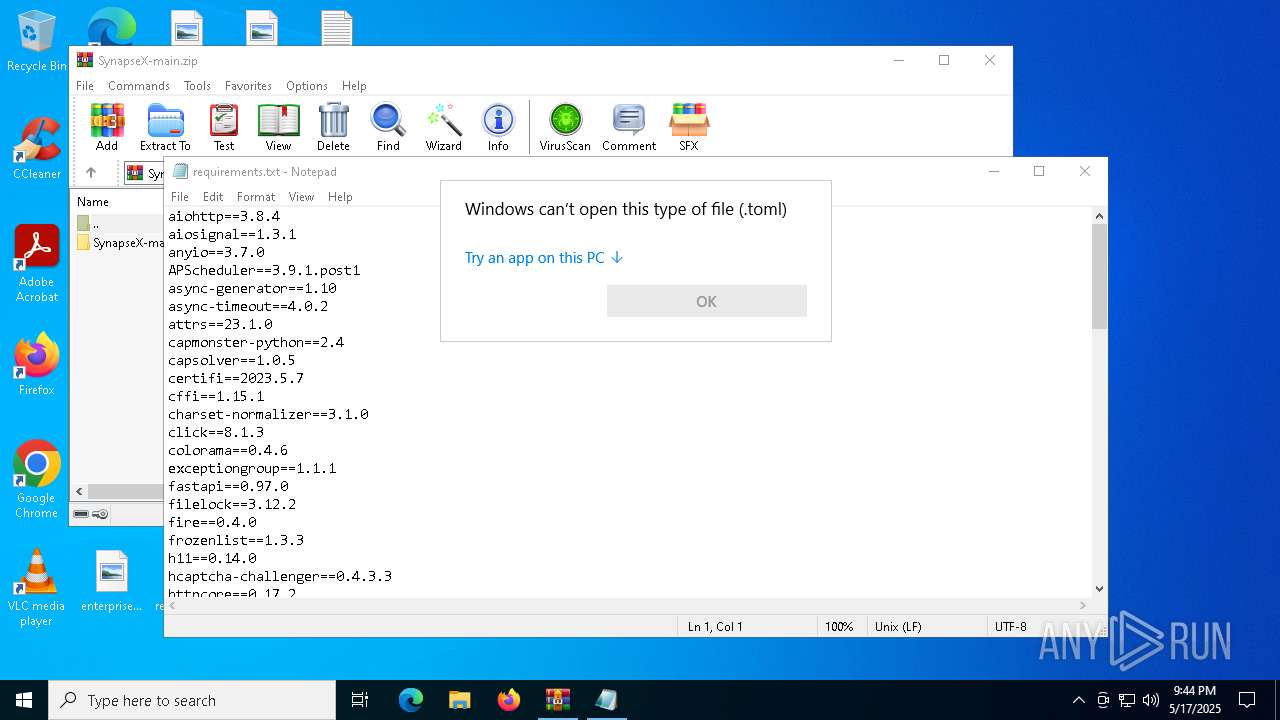
Manual execution by a user
- Loader.exe (PID: 7536)
- notepad.exe (PID: 7580)
- OpenWith.exe (PID: 7644)
- OpenWith.exe (PID: 7776)
- OpenWith.exe (PID: 7928)
- OpenWith.exe (PID: 8008)
Reads the machine GUID from the registry
- Loader.exe (PID: 7536)
- MSBuild.exe (PID: 672)
Reads security settings of Internet Explorer
- notepad.exe (PID: 7580)
- powershell.exe (PID: 8084)
Reads Environment values
- Loader.exe (PID: 7536)
Checks supported languages
- Loader.exe (PID: 7536)
- MpCmdRun.exe (PID: 7156)
- w33j4spl.vxe0.exe (PID: 5164)
- MSBuild.exe (PID: 672)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 7644)
- OpenWith.exe (PID: 7776)
- OpenWith.exe (PID: 7928)
- OpenWith.exe (PID: 8008)
Reads the software policy settings
- powershell.exe (PID: 8084)
- MSBuild.exe (PID: 672)
- slui.exe (PID: 7348)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7820)
Found Base64 encoded access to Windows Defender via PowerShell (YARA)
- Loader.exe (PID: 7536)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7820)
Found Base64 encoded reflection usage via PowerShell (YARA)
- Loader.exe (PID: 7536)
Found Base64 encoded file access via PowerShell (YARA)
- Loader.exe (PID: 7536)
Disables trace logs
- powershell.exe (PID: 7820)
Checks proxy server information
- powershell.exe (PID: 7820)
- slui.exe (PID: 7348)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7820)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7420)
The sample compiled with english language support
- WinRAR.exe (PID: 7420)
The executable file from the user directory is run by the Powershell process
- w33j4spl.vxe0.exe (PID: 5164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:05:09 23:32:24 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | SynapseX-main/ |
Total processes
139
Monitored processes
19
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 672 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | w33j4spl.vxe0.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4452 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5116 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | — | w33j4spl.vxe0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 5164 | "C:\Users\admin\AppData\Roaming\w33j4spl.vxe0.exe" | C:\Users\admin\AppData\Roaming\w33j4spl.vxe0.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5608 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$VR7420.8115\Rar$Scan27106.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7156 | "C:\Program Files\Windows Defender\MpCmdRun.exe" -Scan -ScanType 3 -File "C:\Users\admin\AppData\Local\Temp\Rar$VR7420.8115" | C:\Program Files\Windows Defender\MpCmdRun.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Malware Protection Command Line Utility Exit code: 2 Version: 4.18.1909.6 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7348 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7420 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\SynapseX-main.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7536 | "C:\Users\admin\Desktop\Loader.exe" | C:\Users\admin\Desktop\Loader.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Version: 0.0.0.0 Modules
| |||||||||||||||
Total events
22 334
Read events
22 324
Write events
10
Delete events
0
Modification events
| (PID) Process: | (7420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\SynapseX-main.zip | |||
| (PID) Process: | (7420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList |
| Operation: | write | Name: | ArcSort |
Value: 32 | |||
| (PID) Process: | (7420) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\VirusScan |
| Operation: | write | Name: | DefScanner |
Value: Windows Defender | |||
Executable files
3
Suspicious files
2
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7536 | Loader.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ooitbjeo.5iw.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7536 | Loader.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ixkgwbla.ugd.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7420 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7420.8115\SynapseX-main.zip\SynapseX-main\Makefile | text | |
MD5:F540DEC20889A7DCB32E6AECA5885109 | SHA256:AEF2D0EEF89302D1117707BADC975D6C63EE40DF2D27AE4F198BB25138201F46 | |||
| 7820 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:EC005B31E31CD6D085CBDA52E729891C | SHA256:72D3E03647E7E767EFACAA650353D3D88DFEA14CB424AE6F706CFC6ABFE7A531 | |||
| 7420 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7420.8115\SynapseX-main.zip\SynapseX-main\Loader.exe | executable | |
MD5:65D53D68126B91CDCABBFFB58ED3C66C | SHA256:479B3C923BE6125530E99F24E611547AA5D8861D1E88B75A03CE5527A2052213 | |||
| 7420 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7420.8115\SynapseX-main.zip\SynapseX-main\README.md | text | |
MD5:E6133D19006BB1CC7AADB52F97F1FAF5 | SHA256:6DEEBC0AD3EA0B8C9C7376F9EC965F3A69E8E15C57478B036A94E44160465734 | |||
| 7420 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7420.8115\SynapseX-main.zip\SynapseX-main\libcurl.dll | executable | |
MD5:8DA7E810E0F12B16FE6087AADDA7A69C | SHA256:79F567797066F6206EA870FFDA11CF92612AEA0EE3A26582BE38DDD0FD51FA53 | |||
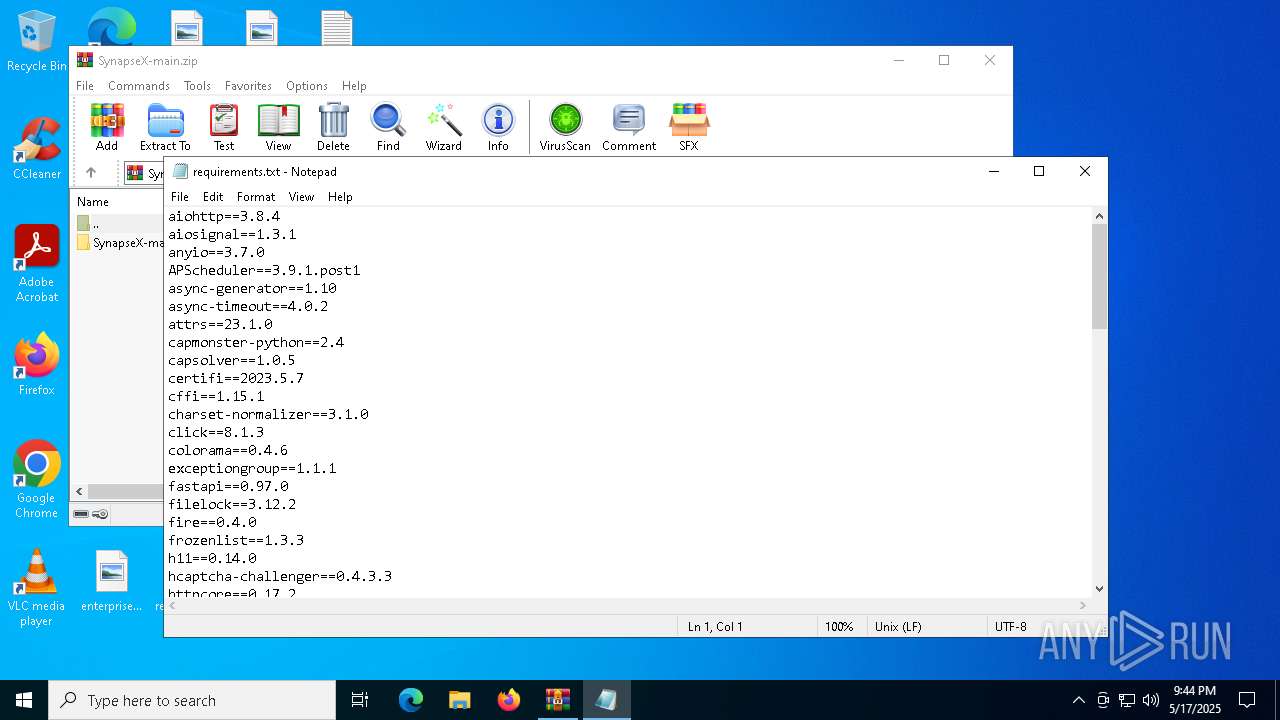
| 7420 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7420.8115\SynapseX-main.zip\SynapseX-main\requirements.txt | text | |
MD5:84E1021A2F9073DBACAD1349B6C9E4D3 | SHA256:1EAE2E450EEAC1C395F714F2639F09AE83CB959AC09A596151E4CABB9225939E | |||
| 7420 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR7420.8115\SynapseX-main.zip\SynapseX-main\config.toml | text | |
MD5:D2FD712EB5EB2CBA945D93680208E954 | SHA256:8DC716F57504B1A81D926C4793CCFA143A2D83337AE4C4BCB8DA106BA90188B0 | |||
| 8084 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ky0ytkvp.4ny.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
37
DNS requests
13
Threats
24
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7820 | powershell.exe | 104.22.69.199:443 | pastebin.com | CLOUDFLARENET | — | whitelisted |
7820 | powershell.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
7820 | powershell.exe | 185.199.108.133:443 | raw.githubusercontent.com | FASTLY | US | whitelisted |
672 | MSBuild.exe | 149.154.167.99:443 | t.me | Telegram Messenger Inc | GB | whitelisted |
672 | MSBuild.exe | 40.91.108.115:443 | flowerexju.bet | MICROSOFT-CORP-MSN-AS-BLOCK | US | malicious |
672 | MSBuild.exe | 172.67.150.184:443 | overcovtcg.top | CLOUDFLARENET | US | malicious |
7200 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
pastebin.com |
| whitelisted |
github.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
t.me |
| whitelisted |
searchilyo.run |
| unknown |
flowerexju.bet |
| malicious |
testcawepr.run |
| unknown |
easterxeen.run |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | Misc activity | ET INFO Packed Executable Download |
— | — | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
— | — | Misc activity | ET HUNTING EXE Downloaded from Github |
672 | MSBuild.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (flowerexju .bet) |
672 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (flowerexju .bet) in TLS SNI |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (testcawepr .run) |