| URL: | https://clearsxperts.com/ |
| Full analysis: | https://app.any.run/tasks/069b8780-dafe-467a-9b46-b6f3b5818bfd |
| Verdict: | Malicious activity |
| Threats: | EvilProxy is a phishing-as-a-service (PhaaS) platform that enables cybercriminals to bypass multi-factor authentication (MFA) and hijack user sessions. It leverages reverse proxy techniques to harvest credentials and session cookies, posing a serious threat to both individuals and enterprises. |
| Analysis date: | February 20, 2026, 15:27:27 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 72205C6FA9F143E3FE5F5D97095BE937 |
| SHA1: | 00B54AD19B6C8D954777786591E78AFF1B1512E4 |
| SHA256: | B23AC0F8309F20CF84695A812739607F84AFDC2C1F9AF69CA2B3C547AFC0D234 |
| SSDEEP: | 3:N8UBWXCq3n:2UgXCq3 |
MALICIOUS
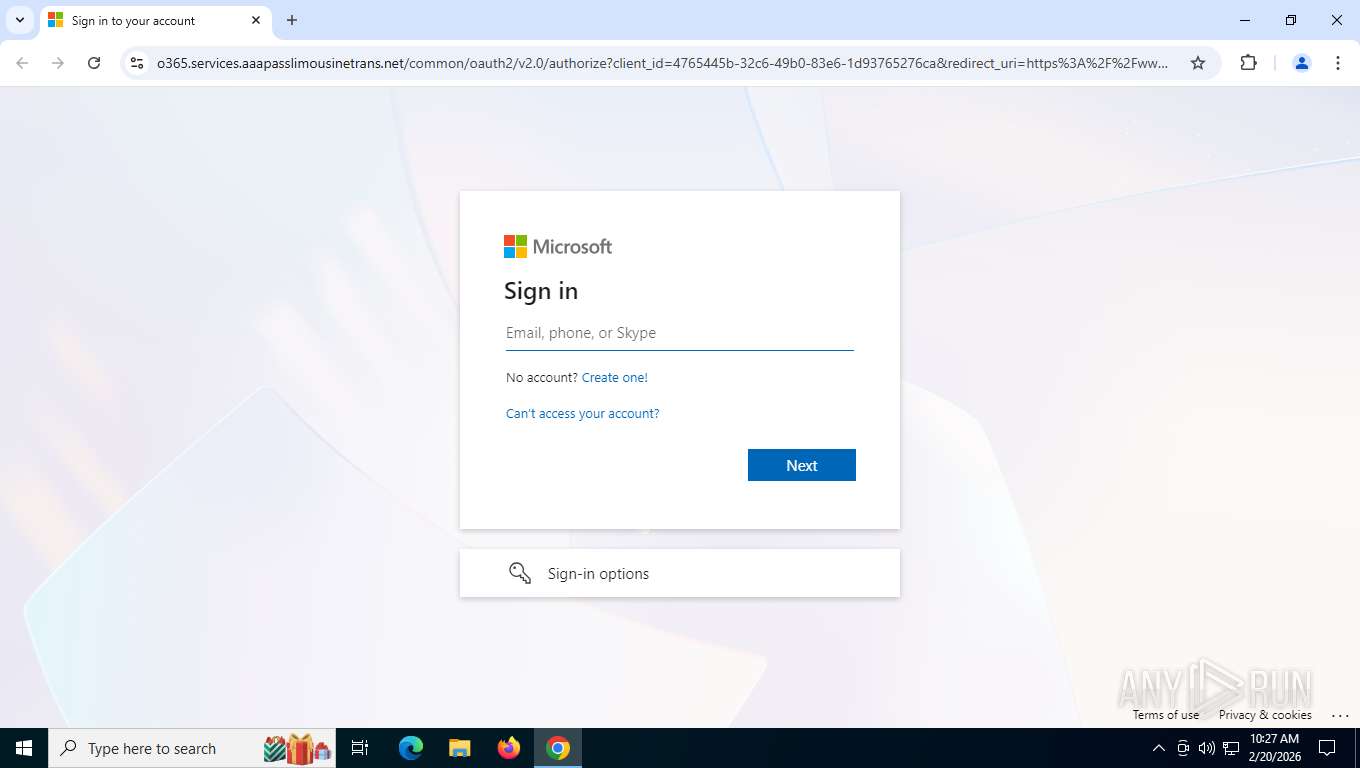
PHISHING has been detected (ML)
- chrome.exe (PID: 6504)
Fake Microsoft Authentication Page has been detected
- chrome.exe (PID: 6504)
MS auth config detected on a non-Microsoft site
- chrome.exe (PID: 6504)
PHISHING has been detected (SURICATA)
- chrome.exe (PID: 8120)
SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 6504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
177
Monitored processes
29
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5220,i,1888446452845659916,11221799798982662281,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=6056 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5980,i,1888446452845659916,11221799798982662281,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5204 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=4124,i,1888446452845659916,11221799798982662281,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5828 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --field-trial-handle=3164,i,1888446452845659916,11221799798982662281,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=3460 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2148 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5984,i,1888446452845659916,11221799798982662281,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5972 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=3320,i,1888446452845659916,11221799798982662281,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5796 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5732,i,1888446452845659916,11221799798982662281,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5860 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=6036,i,1888446452845659916,11221799798982662281,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=4664 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 4644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5812,i,1888446452845659916,11221799798982662281,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5808 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
220
Read events
220
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
42
Text files
17
Unknown types
67
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF1e5448.TMP | — | |
MD5:— | SHA256:— | |||
| 6504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF1e5457.TMP | — | |
MD5:— | SHA256:— | |||
| 6504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF1e5457.TMP | — | |
MD5:— | SHA256:— | |||
| 6504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF1e5457.TMP | — | |
MD5:— | SHA256:— | |||
| 6504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF1e5457.TMP | — | |
MD5:— | SHA256:— | |||
| 6504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1e5467.TMP | — | |
MD5:— | SHA256:— | |||
| 6504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
93
TCP/UDP connections
81
DNS requests
61
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8120 | chrome.exe | GET | 301 | 188.114.97.3:443 | https://clearsxperts.com/ | unknown | — | — | unknown |
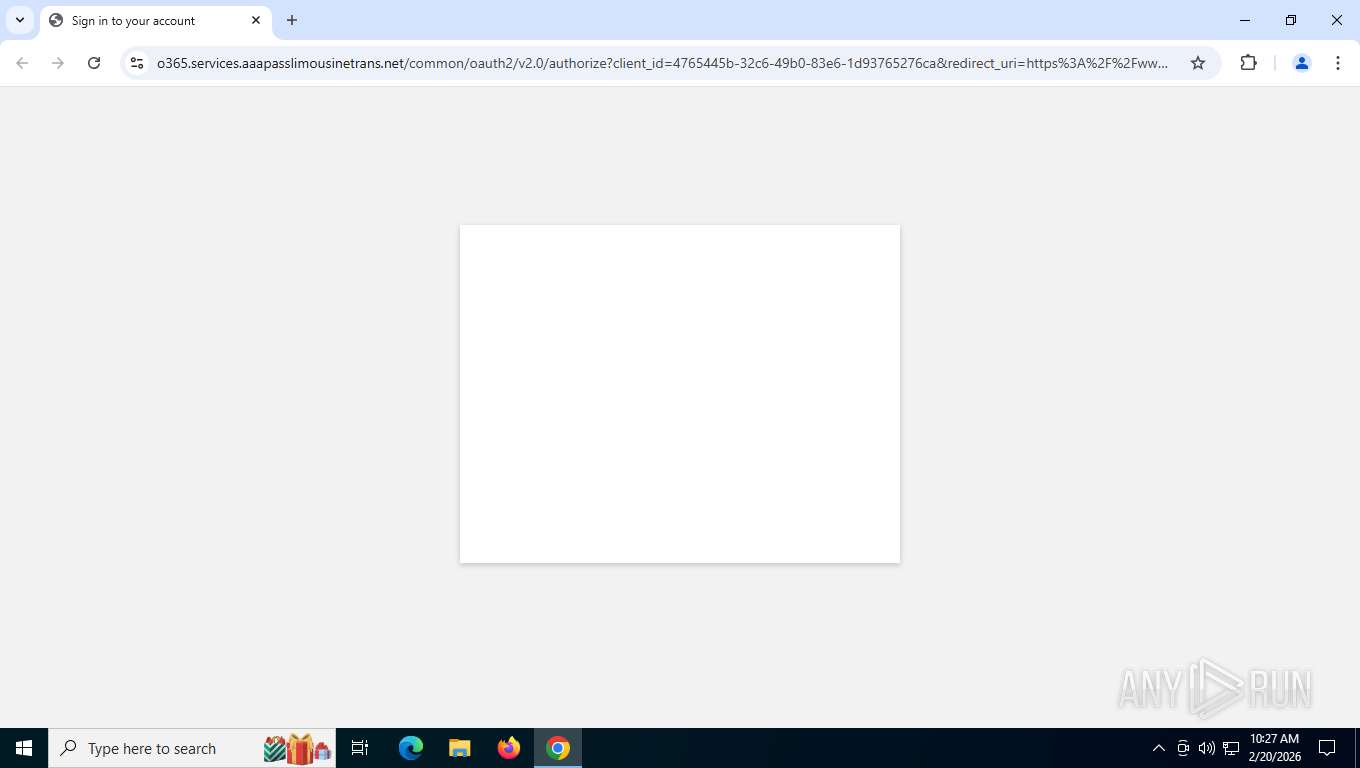
8120 | chrome.exe | GET | 302 | 51.161.207.169:443 | https://helpdesk.services.aaapasslimousinetrans.net/s/OMWLjwpsfLWYU | unknown | — | — | unknown |
8120 | chrome.exe | GET | 302 | 51.161.207.169:443 | https://gatezp5xu8guomwki23kgcjrbswjs5.services.aaapasslimousinetrans.net/login | unknown | — | — | unknown |
8120 | chrome.exe | GET | 200 | 51.161.207.169:443 | https://o365.services.aaapasslimousinetrans.net/s/bd6f25bc0834e39d8f5570fcfb20abfa017f98a1fd27bdc723295b3f283154b9.js | unknown | — | — | unknown |
8120 | chrome.exe | POST | 200 | 142.250.201.67:443 | https://update.googleapis.com/service/update2/json?cup2key=14:KmAUKorMSO7nk-6jO6YX_9tWdJyq6bswNGGsDJ2XSsw&cup2hreq=23480dc031f01fc9cb6cc907ff674e1836db9f1056ca580077e5b1380601df76 | unknown | binary | 289 b | whitelisted |
8120 | chrome.exe | GET | 200 | 51.161.207.169:443 | https://o365.services.aaapasslimousinetrans.net/common/oauth2/v2.0/authorize?client_id=4765445b-32c6-49b0-83e6-1d93765276ca&redirect_uri=https%3A%2F%2Fwww.office.com%2Flandingv2&response_type=code%20id_token&scope=openid%20profile%20https%3A%2F%2Fwww.office.com%2Fv2%2FOfficeHome.All&response_mode=form_post&nonce=639071980586003481.MDA0YzVmYzEtZmNkNi00MDVmLWE4OTYtN2JhZmFjMDEwNDEyNTAwNTYzZjctZGI5My00OGZiLTgzZDMtYzVlMTM1MWY0NzM4&ui_locales=en-US&mkt=en-US&client-request-id=71c390bf-04af-4e8c-bc1b-fd78e5beeec7&state=brWTSms39UmONaR_lofqnZHX_N5kxfDhcf7SlIZofjJgI-187OFkKjnVB6c34dLrKglZ5yoXAbnXxcIDmPGZZiLYJLdIXB8fTngjdyv855QFGEVL60UdxKuL4Hqd9qfe0ZJ0bJU-1W975pDPaD-x1CXjE-_jsiQ1wRTfoi8G3v3_e3tPOqj-aryTG7aDG8ssEFsW7Dj4cvGju0e0iuA-iGIhXz1jxnkJqFcdW3OlNMYpz2N6zu5JYAA099JTXfmn12kUFxHm3VTsiB1X1qv25MfWN8hU1vlLDbLI45qMlro&x-client-SKU=ID_NET8_0&x-client-ver=8.5.0.0 | unknown | binary | 26.7 Kb | malicious |
356 | svchost.exe | POST | 200 | 20.190.160.128:443 | https://login.live.com/RST2.srf | unknown | binary | 11.1 Kb | whitelisted |
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | unknown | — | — | whitelisted |
8120 | chrome.exe | GET | 200 | 142.251.208.10:443 | https://safebrowsingohttpgateway.googleapis.com/v1/ohttp/hpkekeyconfig?key=AIzaSyA2KlwBX3mkFo30om9LUFYQhpqLoa_BNhE | unknown | image | 41 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5660 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4256 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 92.123.104.31:443 | th.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 92.123.104.18:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8120 | chrome.exe | 142.251.208.10:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8120 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain identified as Suspicious |
8120 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Gabagool Phishing-Kit Domain (o365) |
8120 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Gabagool Phishing-Kit Domain (o365) |
8120 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain identified as Suspicious |
8120 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
8120 | chrome.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Possible Fake Microsoft Sign-in domain chain (authisnotlogin) |
8120 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
8120 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Microsoft Authorization URL Observed on Fake Domain (/common/oauth2/) |
8120 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
8120 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |