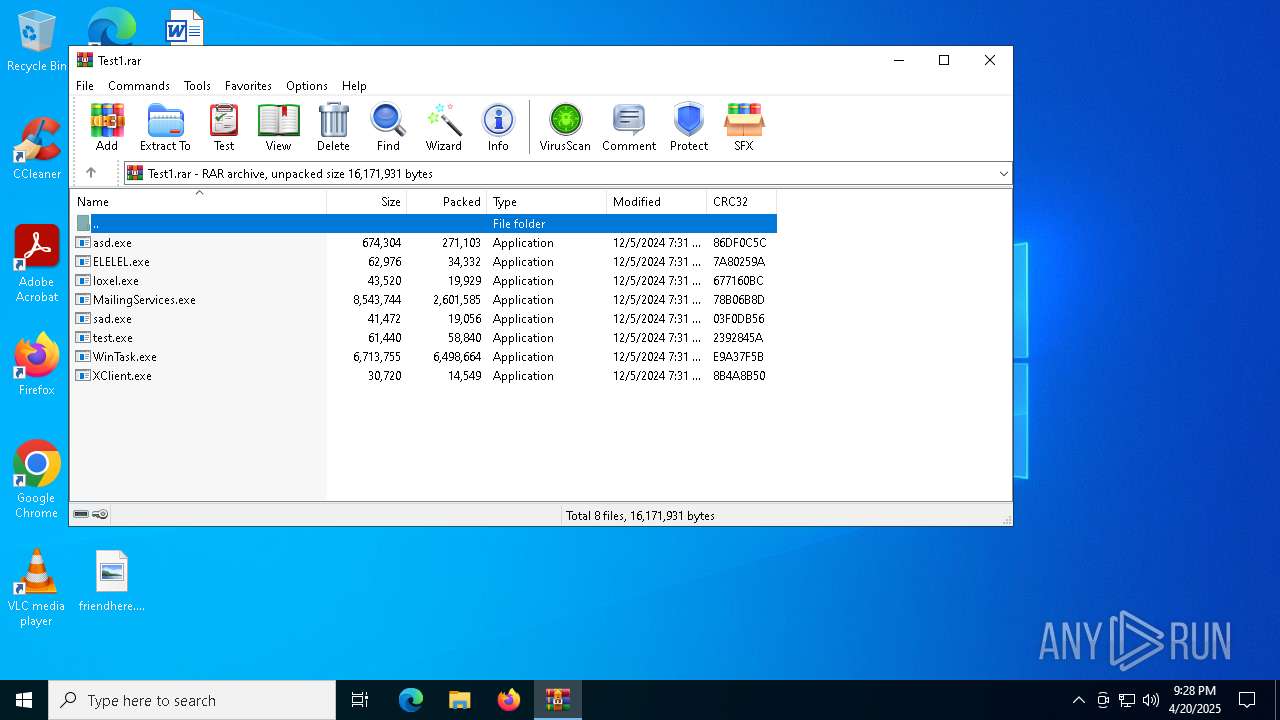
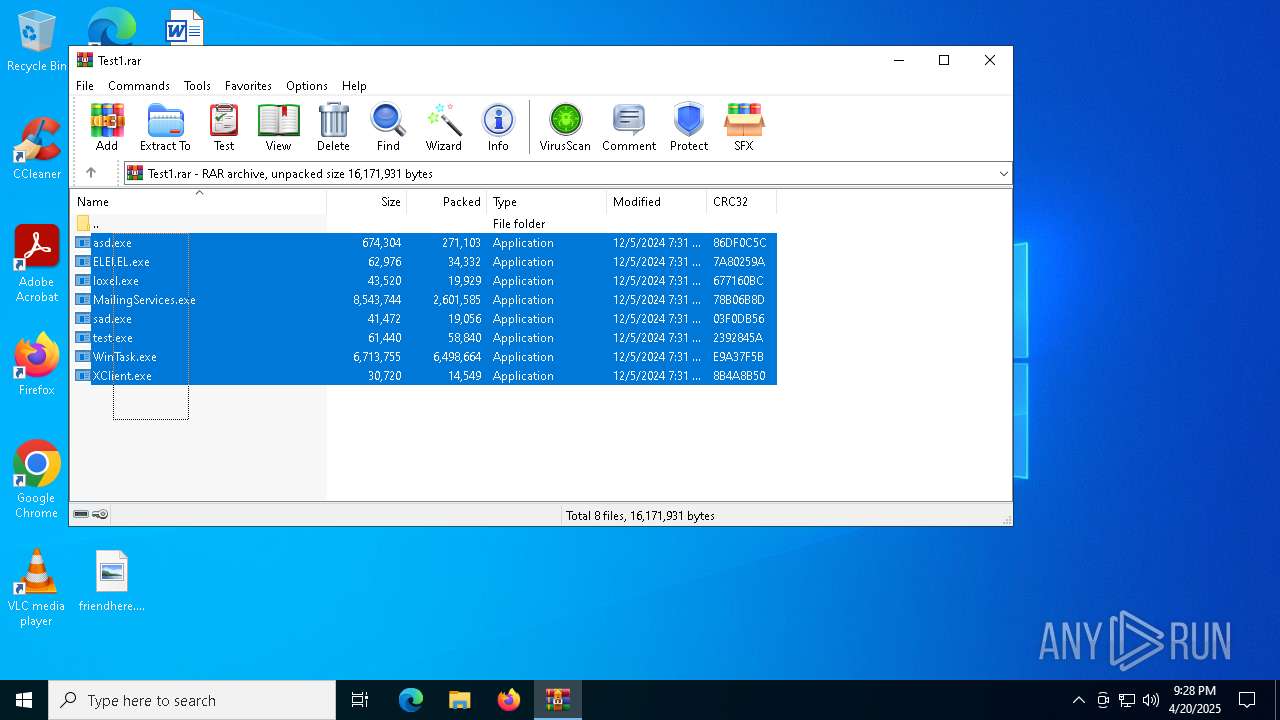
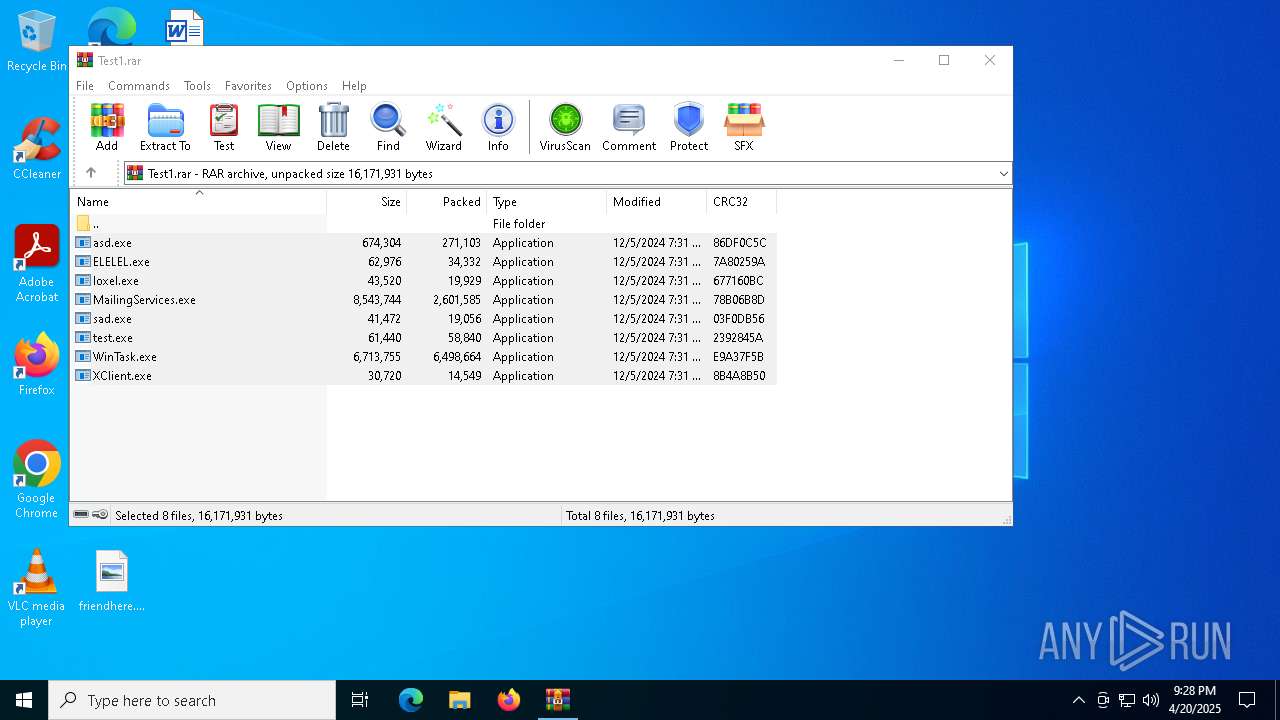
| File name: | Test1.rar |
| Full analysis: | https://app.any.run/tasks/14843d00-e759-4cbf-b88d-5c0754495258 |
| Verdict: | Malicious activity |
| Threats: | DarkComet RAT is a malicious program designed to remotely control or administer a victim's computer, steal private data and spy on the victim. |
| Analysis date: | April 20, 2025, 21:28:34 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | FA3CD4ABCEB2344F577937A0409E77E5 |
| SHA1: | 0622F0DC3101C1AA4F36C49D4FFF502821132E25 |
| SHA256: | B21F491FAD2E8F2D6F8C2C36EA1BAC9BC3E3E2E4F066A1BBD0DA1D94F7DCDE1B |
| SSDEEP: | 98304:x7aifdyi44ENlD4T/n/+HYg+g2cZgx1KBlxFptFn3OGzCvhxO6R9n+7PP4eGlAP5:L7f9GSggDz48oLh5Ihs+y |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 668)
Changes the autorun value in the registry
- asd.exe (PID: 7672)
- sad.exe (PID: 7792)
- msdcsc.exe (PID: 7304)
Changes the login/logoff helper path in the registry
- asd.exe (PID: 7672)
Uses Task Scheduler to run other applications
- sad.exe (PID: 7792)
DARKCOMET mutex has been found
- msdcsc.exe (PID: 7304)
- notepad.exe (PID: 7408)
XWORM has been detected (SURICATA)
- XClient.exe (PID: 7864)
- sad.exe (PID: 7792)
SUSPICIOUS
The process creates files with name similar to system file names
- WinRAR.exe (PID: 668)
The process checks if it is being run in the virtual environment
- WinRAR.exe (PID: 668)
Executable content was dropped or overwritten
- asd.exe (PID: 7672)
- sad.exe (PID: 7792)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 7952)
Reads security settings of Internet Explorer
- test.exe (PID: 7832)
- asd.exe (PID: 7672)
- sad.exe (PID: 7792)
Reads the date of Windows installation
- test.exe (PID: 7832)
- sad.exe (PID: 7792)
Executing commands from a ".bat" file
- test.exe (PID: 7832)
Starts CMD.EXE for commands execution
- test.exe (PID: 7832)
- asd.exe (PID: 7672)
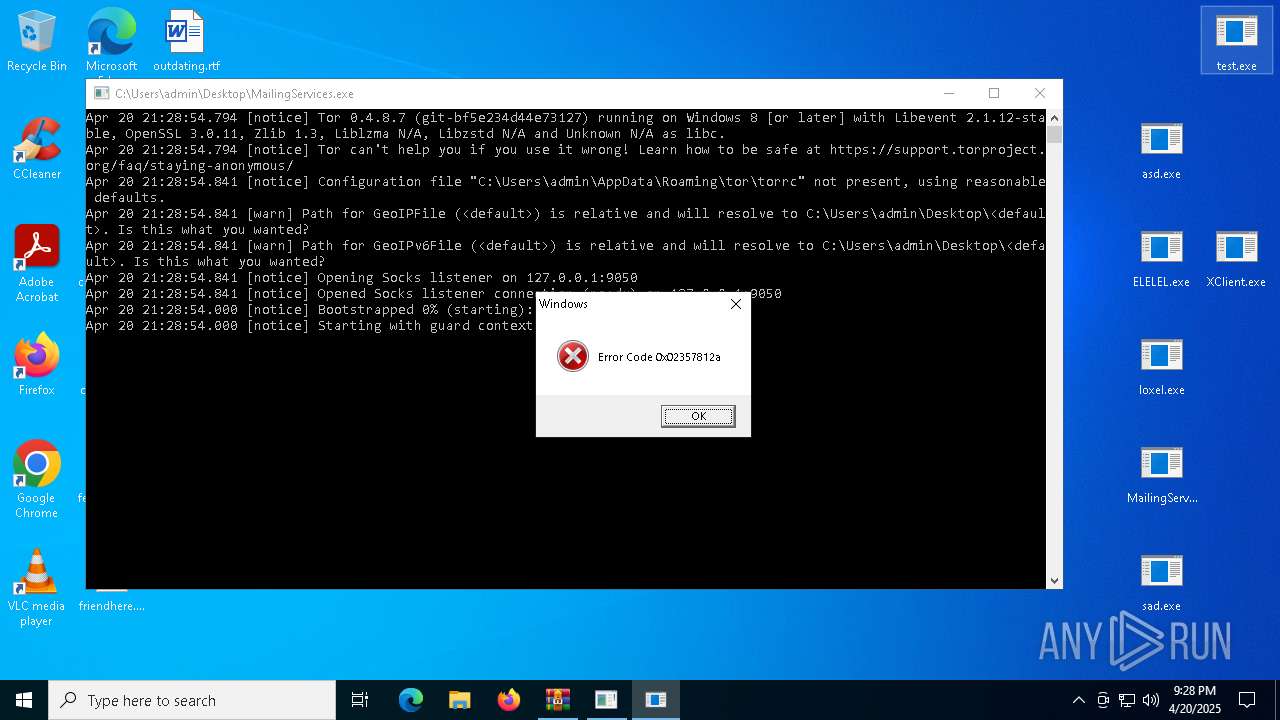
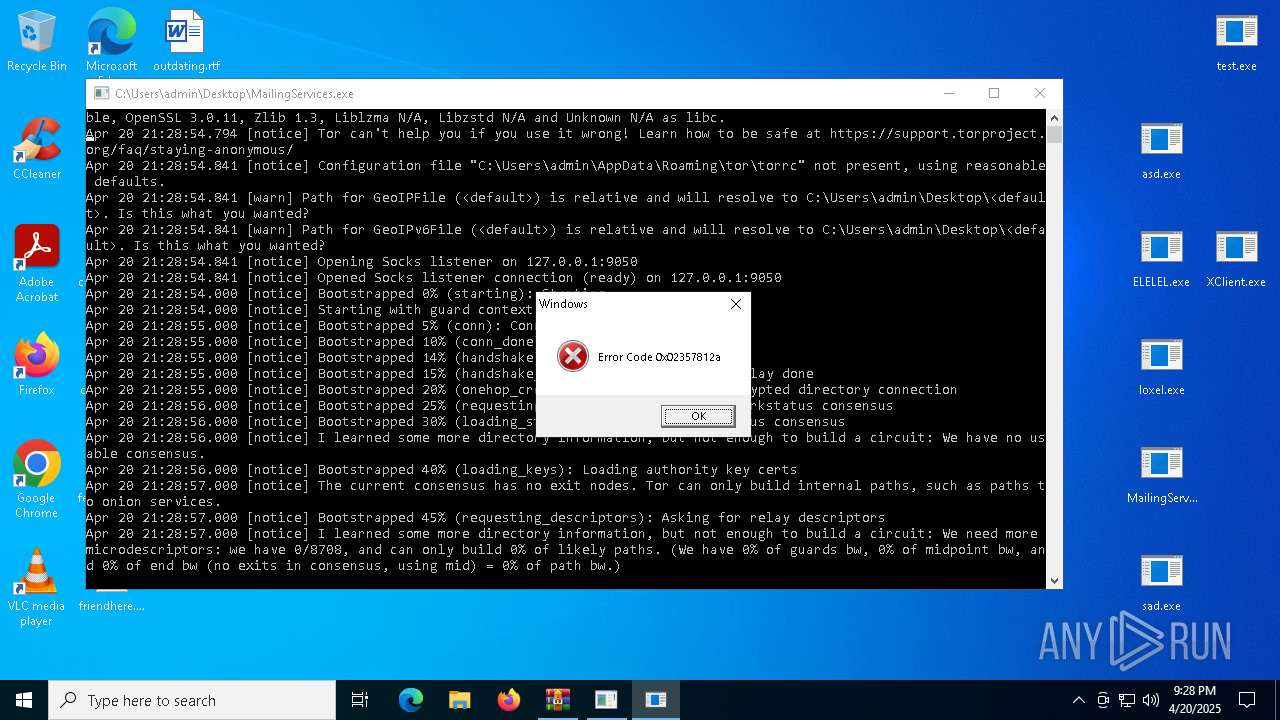
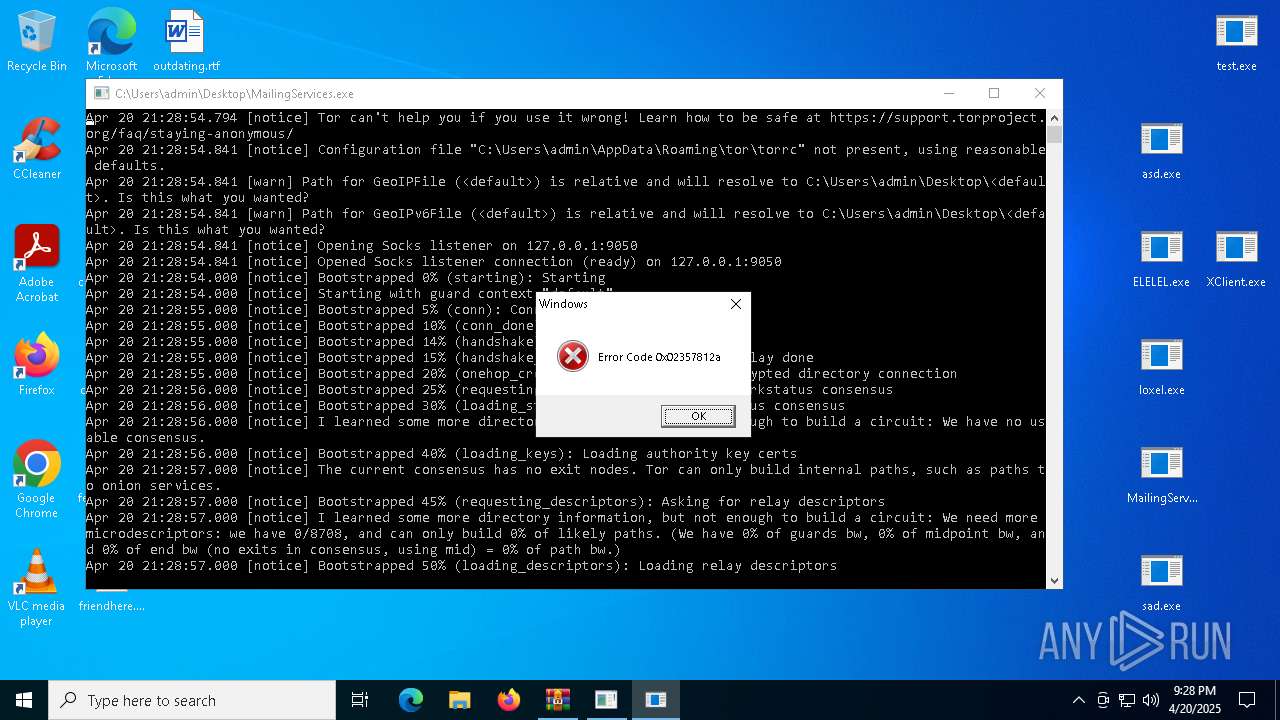
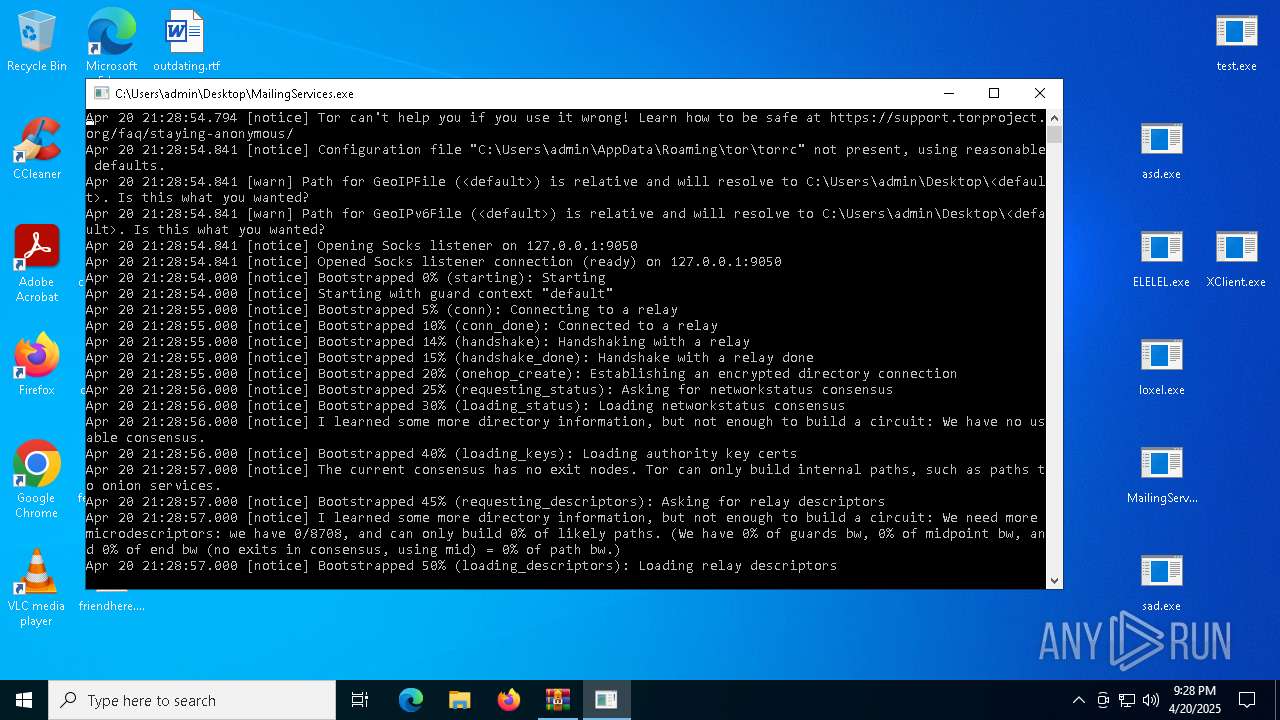
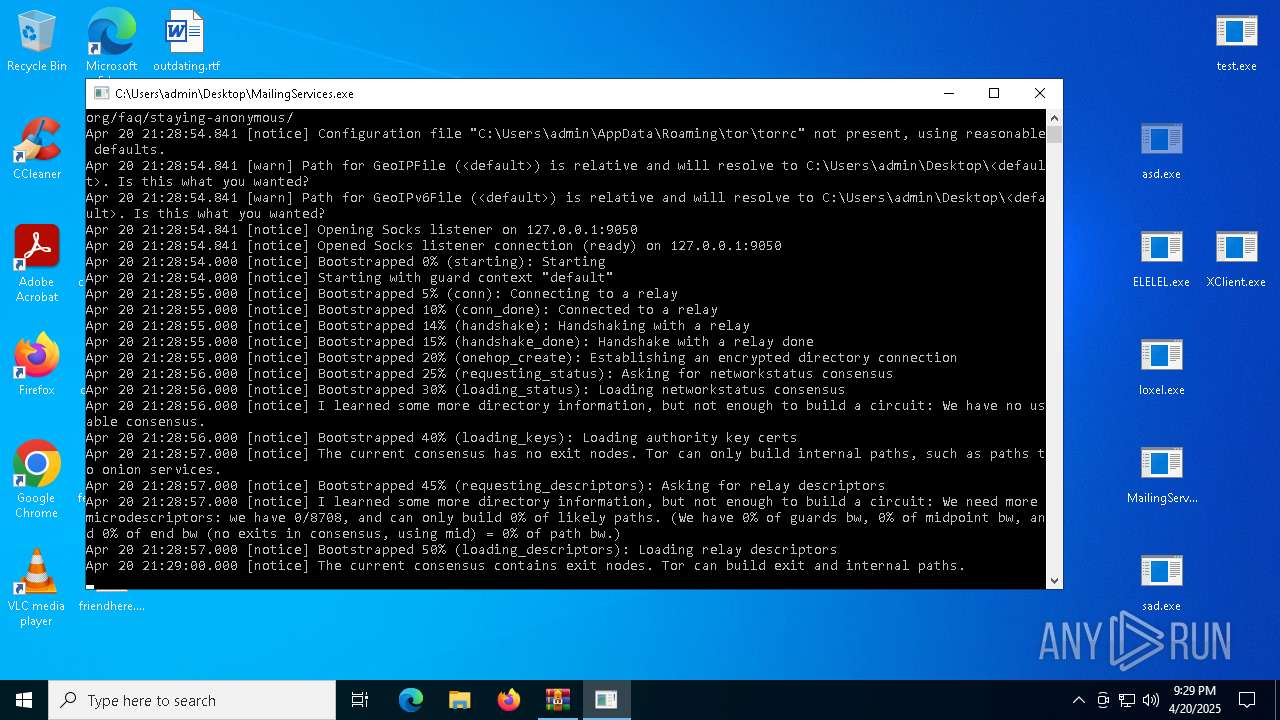
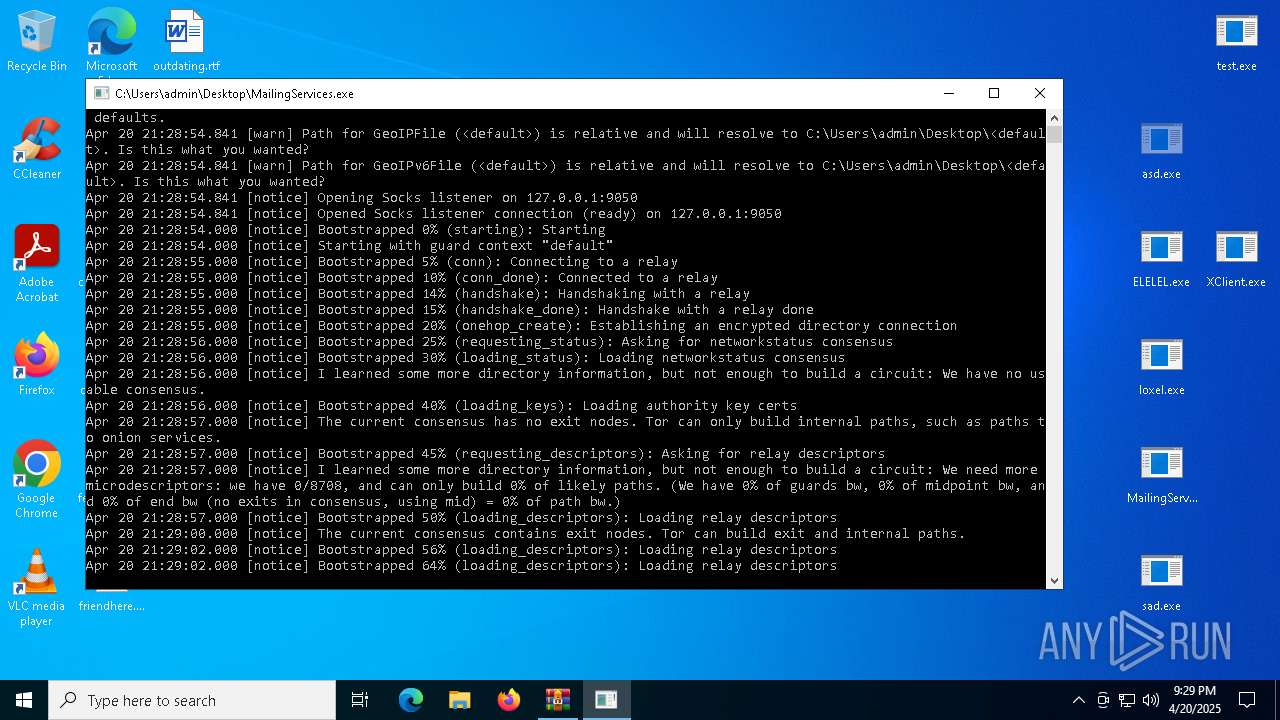
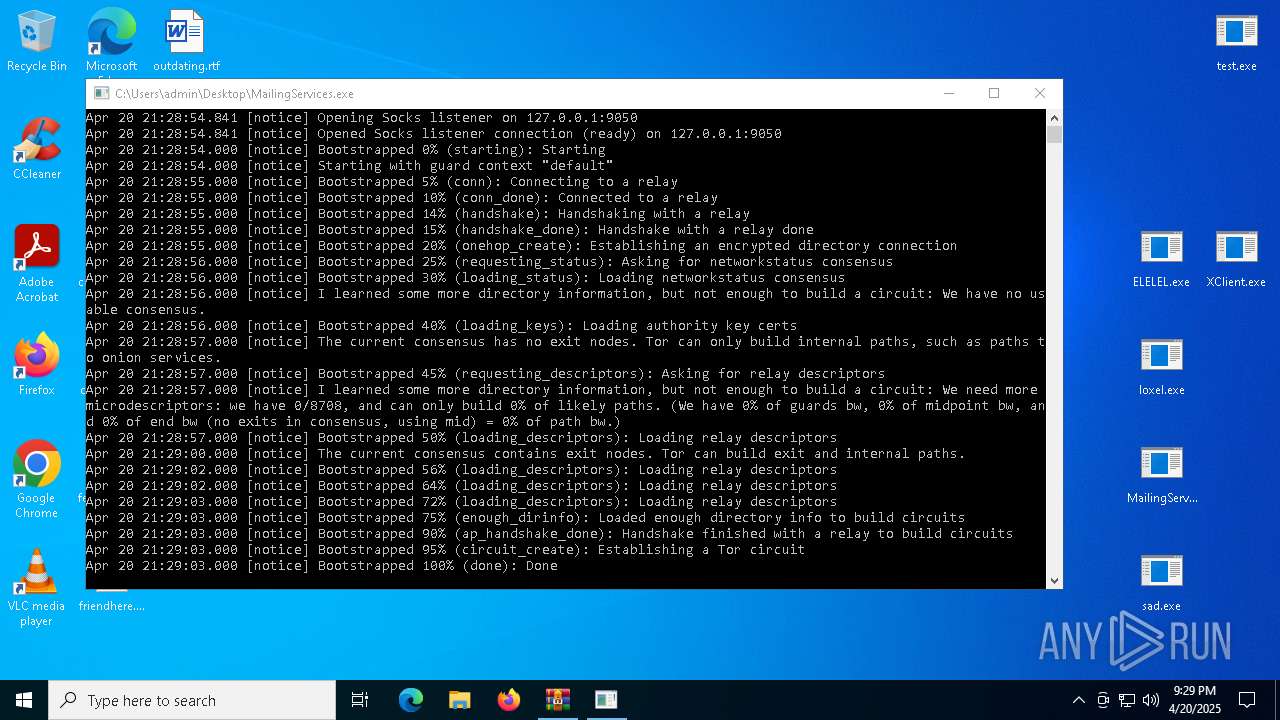
Connects to unusual port
- MailingServices.exe (PID: 7748)
- XClient.exe (PID: 7864)
- sad.exe (PID: 7792)
Checks for external IP
- loxel.exe (PID: 7708)
- svchost.exe (PID: 2196)
- ELELEL.exe (PID: 7692)
Executes application which crashes
- loxel.exe (PID: 7708)
- ELELEL.exe (PID: 7692)
Start notepad (likely ransomware note)
- asd.exe (PID: 7672)
- msdcsc.exe (PID: 7304)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 1628)
- cmd.exe (PID: 6540)
Starts itself from another location
- asd.exe (PID: 7672)
The process executes via Task Scheduler
- sad.exe (PID: 7440)
Contacting a server suspected of hosting an CnC
- sad.exe (PID: 7792)
- XClient.exe (PID: 7864)
INFO
Executable content was dropped or overwritten
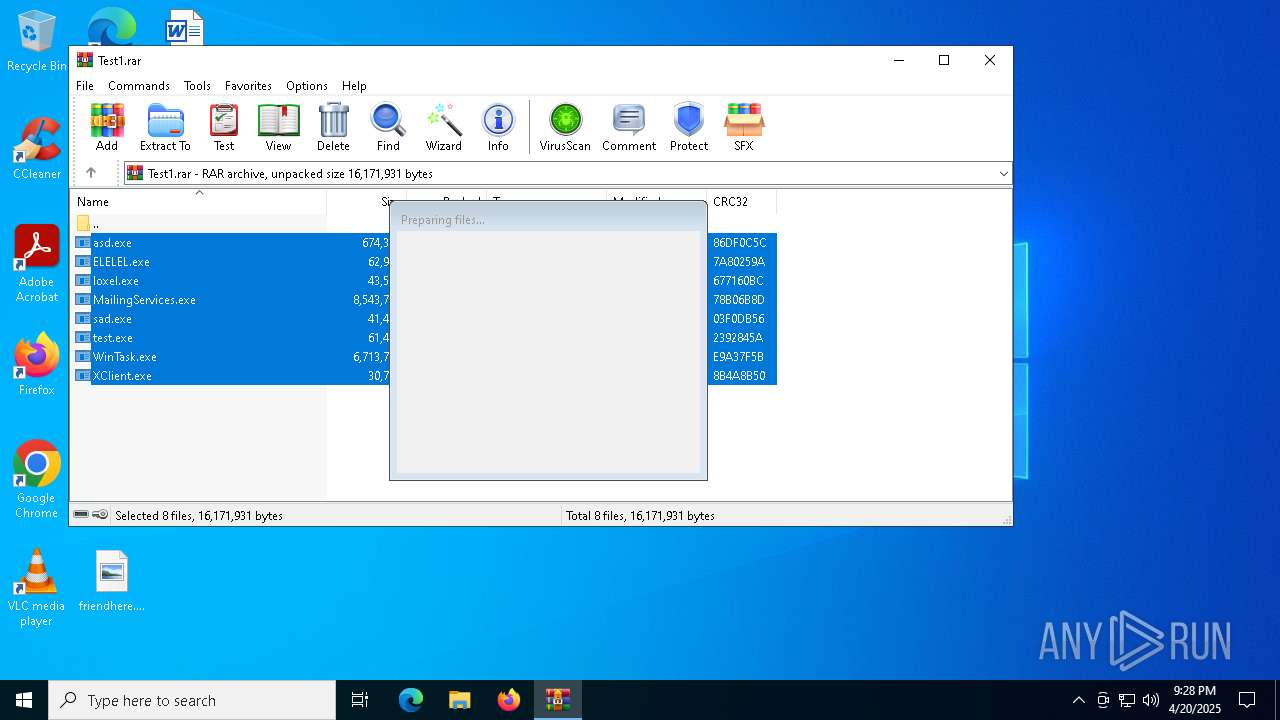
- WinRAR.exe (PID: 668)
Manual execution by a user
- ELELEL.exe (PID: 7692)
- loxel.exe (PID: 7708)
- asd.exe (PID: 7672)
- MailingServices.exe (PID: 7748)
- sad.exe (PID: 7792)
- test.exe (PID: 7832)
- XClient.exe (PID: 7864)
Checks supported languages
- loxel.exe (PID: 7708)
- MailingServices.exe (PID: 7748)
- sad.exe (PID: 7792)
- test.exe (PID: 7832)
- XClient.exe (PID: 7864)
- asd.exe (PID: 7672)
- ELELEL.exe (PID: 7692)
- msdcsc.exe (PID: 7304)
- sad.exe (PID: 7440)
The sample compiled with english language support
- WinRAR.exe (PID: 668)
- asd.exe (PID: 7672)
Reads the machine GUID from the registry
- ELELEL.exe (PID: 7692)
- sad.exe (PID: 7792)
- MailingServices.exe (PID: 7748)
- XClient.exe (PID: 7864)
- loxel.exe (PID: 7708)
- sad.exe (PID: 7440)
Create files in a temporary directory
- test.exe (PID: 7832)
Reads the computer name
- sad.exe (PID: 7792)
- XClient.exe (PID: 7864)
- test.exe (PID: 7832)
- MailingServices.exe (PID: 7748)
- msdcsc.exe (PID: 7304)
- sad.exe (PID: 7440)
- loxel.exe (PID: 7708)
- ELELEL.exe (PID: 7692)
- asd.exe (PID: 7672)
Process checks computer location settings
- test.exe (PID: 7832)
- sad.exe (PID: 7792)
- asd.exe (PID: 7672)
Creates files or folders in the user directory
- MailingServices.exe (PID: 7748)
- sad.exe (PID: 7792)
- WerFault.exe (PID: 6872)
- WerFault.exe (PID: 680)
Disables trace logs
- loxel.exe (PID: 7708)
- ELELEL.exe (PID: 7692)
Reads Environment values
- ELELEL.exe (PID: 7692)
- loxel.exe (PID: 7708)
Checks proxy server information
- loxel.exe (PID: 7708)
- ELELEL.exe (PID: 7692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 2601585 |
| UncompressedSize: | 8543744 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | MailingServices.exe |
Total processes
158
Monitored processes
29
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\Test1.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 680 | C:\WINDOWS\system32\WerFault.exe -u -p 7692 -s 1808 | C:\Windows\System32\WerFault.exe | — | ELELEL.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1532 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1628 | "C:\Windows\System32\cmd.exe" /k attrib "C:\Users\admin\Desktop" +s +h | C:\Windows\SysWOW64\cmd.exe | — | asd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3096 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4120 | "C:\Windows\System32\schtasks.exe" /create /f /sc minute /mo 1 /tn "sad" /tr "C:\Users\admin\AppData\Local\sad.exe" | C:\Windows\System32\schtasks.exe | — | sad.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5544 | attrib "C:\Users\admin\Desktop" +s +h | C:\Windows\SysWOW64\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5596 | notepad | C:\Windows\SysWOW64\notepad.exe | — | asd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 3473408 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5892 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 154
Read events
11 105
Write events
49
Delete events
0
Modification events
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Test1.rar | |||
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7672) asd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicroUpdate |
Value: C:\Users\admin\Documents\MSDCSC\msdcsc.exe | |||
| (PID) Process: | (7672) asd.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | UserInit |
Value: C:\Windows\system32\userinit.exe,C:\Users\admin\Documents\MSDCSC\msdcsc.exe | |||
Executable files
10
Suspicious files
4
Text files
15
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 668 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa668.33537\MailingServices.exe | executable | |
MD5:949EC877D89E04A29F4FEF5A5B8592D8 | SHA256:3B2B11C7E54FF4E46EACD35EB7184AFB6A064B5310DA1F8B4E8AEB832F3A1FF5 | |||
| 668 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa668.33537\XClient.exe | executable | |
MD5:076C086FBCAA2BBD3727F2F31E3B88D4 | SHA256:A0465041D47C8E5A47D5904F8D46CF4A8F204553916D1080532B235BBDCEC959 | |||
| 668 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa668.33537\test.exe | executable | |
MD5:4BA8C0A09979A2066987CF6381907157 | SHA256:B72522DCB86C42950F8795144167DB4BBFE26166A456A2616AC2A6EAB1FB1EF8 | |||
| 668 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa668.33537\WinTask.exe | executable | |
MD5:DDD814C5CE4BA7E52E772B8EDC1CFC3E | SHA256:F5E3CF2B0AB8CC4D77967039FC4D42B42DFC1A68A12B46E928DAE6B3D5CBB47A | |||
| 668 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa668.33537\loxel.exe | executable | |
MD5:12E327CF70F9B4DA265AE590A3C6FE75 | SHA256:05B30B7FBEFA1D435F695F4D72CA165820C52954DBB6403F33085E69A9E43135 | |||
| 668 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa668.33537\sad.exe | executable | |
MD5:D600597F342290D215082BCC32DBE01C | SHA256:464BE69C47FAF6DDCE748892C392A510C4ADDB093F7F000233DD6C29A1D591D3 | |||
| 7748 | MailingServices.exe | C:\Users\admin\AppData\Roaming\tor\cached-certs.tmp | text | |
MD5:F74AE693B0ACA37C6F9A6D524F9741E5 | SHA256:18C7059547FE112CF212D311E9267BC0139F2B93BE694636D245FA79428D71C9 | |||
| 7952 | cmd.exe | C:\Users\admin\AppData\Local\Temp\getadmin.vbs | text | |
MD5:D14A6C18536B08C2D91CC10129CEC2CA | SHA256:88F0E55BE41422957E8F4FEC8CAF0F9ED4E68D1F0290171BA8F4BD26C19FA17D | |||
| 6872 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_loxel.exe_7cae9510d57f12197cc57c4a19bca8615d283b_a39b6d4b_b15dffcb-ad2e-404b-ab15-198d8ee3f033\Report.wer | — | |
MD5:— | SHA256:— | |||
| 680 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_ELELEL.exe_79dab57064bed2788a72d7c99e4f53a3d682fd73_ea522115_bb97bff6-e554-45c9-bff7-54530d392e93\Report.wer | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
24
DNS requests
11
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7708 | loxel.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6132 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7692 | ELELEL.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
6132 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.216.77.42:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7748 | MailingServices.exe | 185.220.101.83:9000 | — | Zwiebelfreunde e.V. | DE | unknown |
7748 | MailingServices.exe | 192.42.113.102:9001 | — | SURF B.V. | NL | unknown |
7748 | MailingServices.exe | 49.12.224.203:8000 | — | Hetzner Online GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
ip-api.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7748 | MailingServices.exe | Misc Attack | ET TOR Known Tor Exit Node Traffic group 50 |
7748 | MailingServices.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 50 |
7748 | MailingServices.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 314 |
7748 | MailingServices.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 744 |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
7708 | loxel.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
7708 | loxel.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
7692 | ELELEL.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
7692 | ELELEL.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |