| File name: | upx.exe |
| Full analysis: | https://app.any.run/tasks/07e86311-afb2-4bf7-ae92-78755760f296 |
| Verdict: | Malicious activity |
| Threats: | Ramnit is a highly modular banking trojan and worm that evolved from a file-infecting virus into a powerful cybercrime tool. It specializes in financial fraud, credential theft, remote access, and malware delivery, being a serious threat to businesses and individuals. First spotted in 2010, Ramnit became popular after the 2014 takedown of the GameOver Zeus botnet, as cybercriminals sought alternatives for banking fraud. |
| Analysis date: | August 01, 2024, 14:48:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
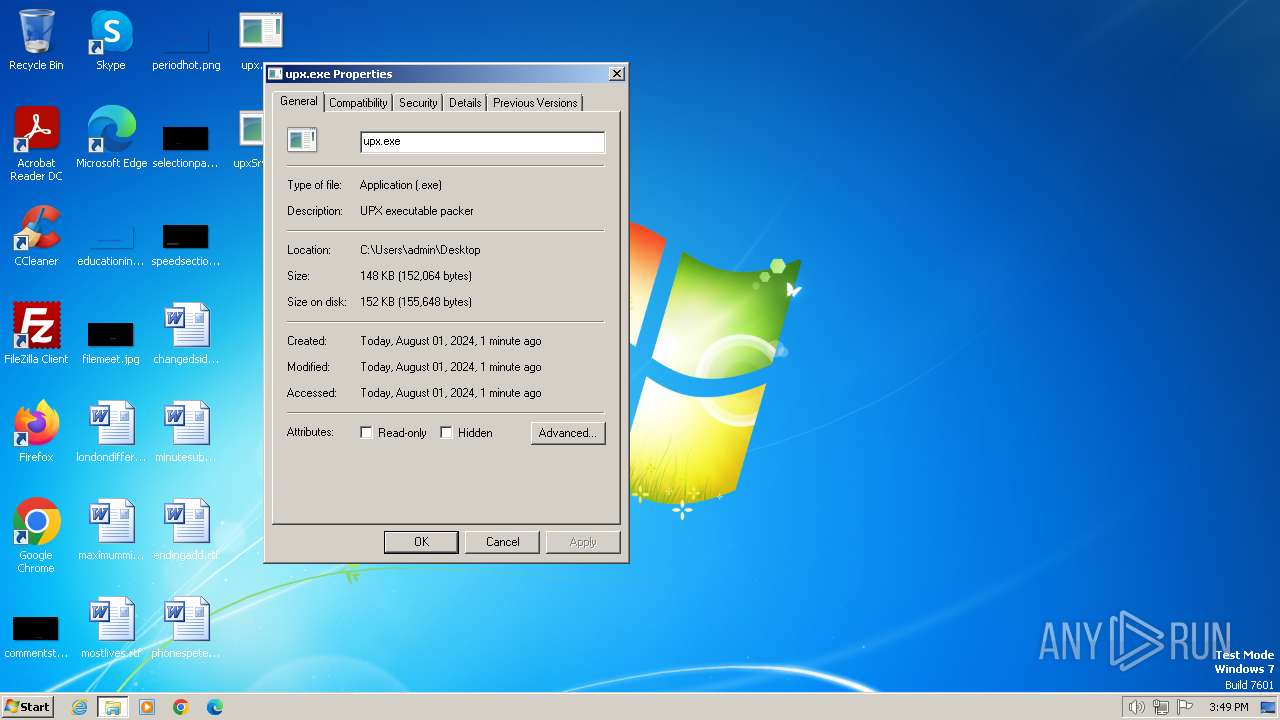
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 16282F2A1AFDAC0E8388FBD310844877 |
| SHA1: | 5197E2895C5C536869CB15478DA3D2B00236ABB6 |
| SHA256: | B1F445EF77C23029736B474730E7D884585AF928150AF8C4A0CAE108D0A3E33C |
| SSDEEP: | 3072:nO34RxTxabGp61CnKOw76G1y6lYuI+BpWIvStKb5QaXP3BLmpR9KJQKVXRxZKY18:n1taCo1CnZwr1RYf+rvSOQ0e9wn5BdC |
MALICIOUS
Drops the executable file immediately after the start
- upx.exe (PID: 2780)
Signature: RAMNIT has been detected
- upxSrv.exe (PID: 2712)
- DesktopLayer.exe (PID: 1488)
- upx.exe (PID: 2780)
- iexplore.exe (PID: 2472)
Connects to the CnC server
- svchost.exe (PID: 1060)
- iexplore.exe (PID: 2472)
RAMNIT has been detected (SURICATA)
- iexplore.exe (PID: 2472)
Changes the login/logoff helper path in the registry
- iexplore.exe (PID: 2472)
SUSPICIOUS
Executable content was dropped or overwritten
- upx.exe (PID: 2780)
- upxSrv.exe (PID: 2712)
Starts itself from another location
- upxSrv.exe (PID: 2712)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 1060)
- iexplore.exe (PID: 2472)
INFO
Checks supported languages
- upxSrv.exe (PID: 2712)
- upx.exe (PID: 2780)
- DesktopLayer.exe (PID: 1488)
- wmpnscfg.exe (PID: 3636)
Reads the computer name
- wmpnscfg.exe (PID: 3636)
Manual execution by a user
- wmpnscfg.exe (PID: 3636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (28.6) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (28) |
| .exe | | | Win32 EXE Yoda's Crypter (27.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (6.8) |
| .exe | | | Win32 Executable (generic) (4.6) |
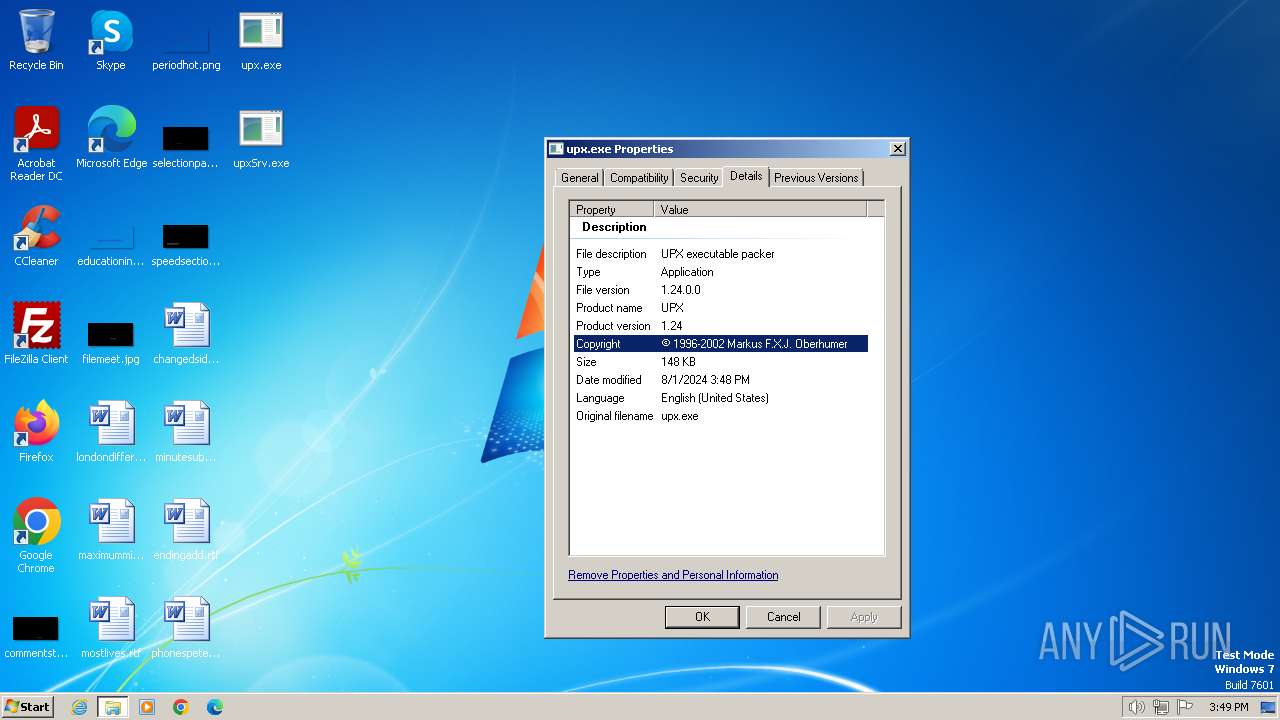
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2002:11:07 13:13:18+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 94208 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 135168 |
| EntryPoint: | 0x3a000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.24.0.0 |
| ProductVersionNumber: | 1.24.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
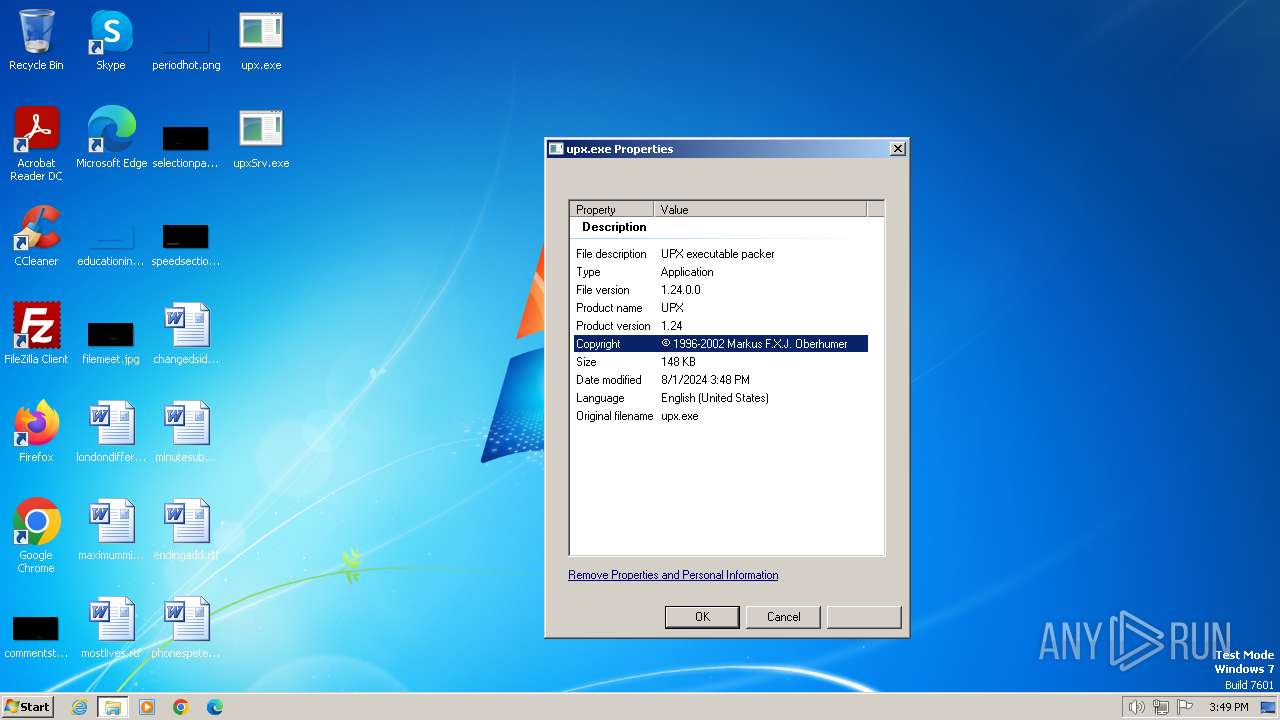
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | The UPX Team http://upx.sf.net |
| FileDescription: | UPX executable packer |
| FileVersion: | 1.24 |
| InternalName: | upx.exe |
| LegalCopyright: | © 1996-2002 Markus F.X.J. Oberhumer |
| OriginalFileName: | upx.exe |
| ProductName: | UPX |
| ProductVersion: | 1.24 |
Total processes
42
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1060 | C:\Windows\system32\svchost.exe -k NetworkService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1488 | C:\Users\admin\Microsoft\DesktopLayer.exe | C:\Users\admin\Microsoft\DesktopLayer.exe | — | upxSrv.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2472 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | DesktopLayer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2712 | C:\Users\admin\Desktop\upxSrv.exe | C:\Users\admin\Desktop\upxSrv.exe | upx.exe | ||||||||||||
User: admin Company: SOFTWIN S.R.L. Integrity Level: MEDIUM Description: BitDefender Management Console Exit code: 0 Version: 106.42.73.61 Modules
| |||||||||||||||
| 2780 | "C:\Users\admin\Desktop\upx.exe" | C:\Users\admin\Desktop\upx.exe | explorer.exe | ||||||||||||
User: admin Company: The UPX Team http://upx.sf.net Integrity Level: MEDIUM Description: UPX executable packer Exit code: 1 Version: 1.24 Modules
| |||||||||||||||
| 3636 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
881
Read events
804
Write events
77
Delete events
0
Modification events
| (PID) Process: | (2472) iexplore.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Userinit |
Value: c:\windows\system32\userinit.exe,,c:\users\admin\microsoft\desktoplayer.exe | |||
| (PID) Process: | (1060) svchost.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\SystemCertificates\AuthRoot\AutoUpdate |
| Operation: | write | Name: | DisallowedCertLastSyncTime |
Value: C4613DF621E4DA01 | |||
| (PID) Process: | (1060) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\AutoUpdate |
| Operation: | write | Name: | DisallowedCertLastSyncTime |
Value: 0AC8420822E4DA01 | |||
Executable files
2
Suspicious files
3
Text files
3
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1060 | svchost.exe | C:\Windows\ServiceProfiles\NetworkService\AppData\Local\Temp\Tar6482.tmp | cat | |
MD5:78785956AB4E54D6116D673C3491EDFF | SHA256:C514DBDBB13632CBB378C59086C1EBB0BC9B25FFB0A349F2B052B065C0D913E6 | |||
| 2780 | upx.exe | C:\Users\admin\Desktop\upxSrv.exe | executable | |
MD5:FF5E1F27193CE51EEC318714EF038BEF | SHA256:FD6C69C345F1E32924F0A5BB7393E191B393A78D58E2C6413B03CED7482F2320 | |||
| 2472 | iexplore.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\WebResources\Resource1\index.html | html | |
MD5:89BB70E172DD1DE12EF92A3CFC7DB945 | SHA256:E4B98A2E87231D00E3B91926F2FB531CEF9A3D8F2908F940E3442CB278DCA5F4 | |||
| 1060 | svchost.exe | C:\Windows\ServiceProfiles\NetworkService\AppData\Local\Temp\Cab6481.tmp | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 1060 | svchost.exe | C:\Windows\ServiceProfiles\NetworkService\AppData\Local\Temp\CabDAAD.tmp | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 2712 | upxSrv.exe | C:\Users\admin\Microsoft\DesktopLayer.exe | executable | |
MD5:FF5E1F27193CE51EEC318714EF038BEF | SHA256:FD6C69C345F1E32924F0A5BB7393E191B393A78D58E2C6413B03CED7482F2320 | |||
| 1060 | svchost.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:BB305D504B172EAA1A256EBC48997940 | SHA256:— | |||
| 1060 | svchost.exe | C:\Windows\ServiceProfiles\NetworkService\AppData\Local\Temp\TarDAAE.tmp | cat | |
MD5:78785956AB4E54D6116D673C3491EDFF | SHA256:C514DBDBB13632CBB378C59086C1EBB0BC9B25FFB0A349F2B052B065C0D913E6 | |||
| 2472 | iexplore.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\Legal\ENU\license.html | html | |
MD5:A0AAB44EBA2F0AD61CA7A7B72CDA4932 | SHA256:E284BF88F5AFD72C7ADFEF90607659B19F3EEEF34718D4138D83A0D15B9892B6 | |||
| 2472 | iexplore.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\ngl_resources\resources\ui\index.html | html | |
MD5:C96625984CD3CF51A3DB24CC0E6EAB89 | SHA256:9595AC02CFC7172BCD46F8F6021E8F61B899F51A05A7CB5B6549B20E6AA91296 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
16
DNS requests
7
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 304 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | whitelisted |
1060 | svchost.exe | GET | 304 | 217.20.57.19:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?8f69642324cc87bd | unknown | — | — | whitelisted |
1372 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1372 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | unknown |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
— | — | 239.255.255.250:3702 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
1372 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2472 | iexplore.exe | 34.253.216.9:443 | fget-career.com | AMAZON-02 | IE | unknown |
2472 | iexplore.exe | 142.250.184.238:80 | google.com | GOOGLE | US | unknown |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1372 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
1372 | svchost.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| unknown |
fget-career.com |
| unknown |
settings-win.data.microsoft.com |
| unknown |
ctldl.windowsupdate.com |
| unknown |
crl.microsoft.com |
| unknown |
www.microsoft.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2472 | iexplore.exe | Malware Command and Control Activity Detected | ET MALWARE Win32/Ramnit Checkin |
2472 | iexplore.exe | Malware Command and Control Activity Detected | ET MALWARE Win32/Ramnit Checkin |
1 ETPRO signatures available at the full report