| File name: | QHAVFT.EXE |
| Full analysis: | https://app.any.run/tasks/a3a123ae-a180-43d0-8c8f-bb9632899c25 |
| Verdict: | Malicious activity |
| Threats: | Cobalt Strike is a legitimate penetration software toolkit developed by Forta. But its cracked versions are widely adopted by bad actors, who use it as a C2 system of choice for targeted attacks. |
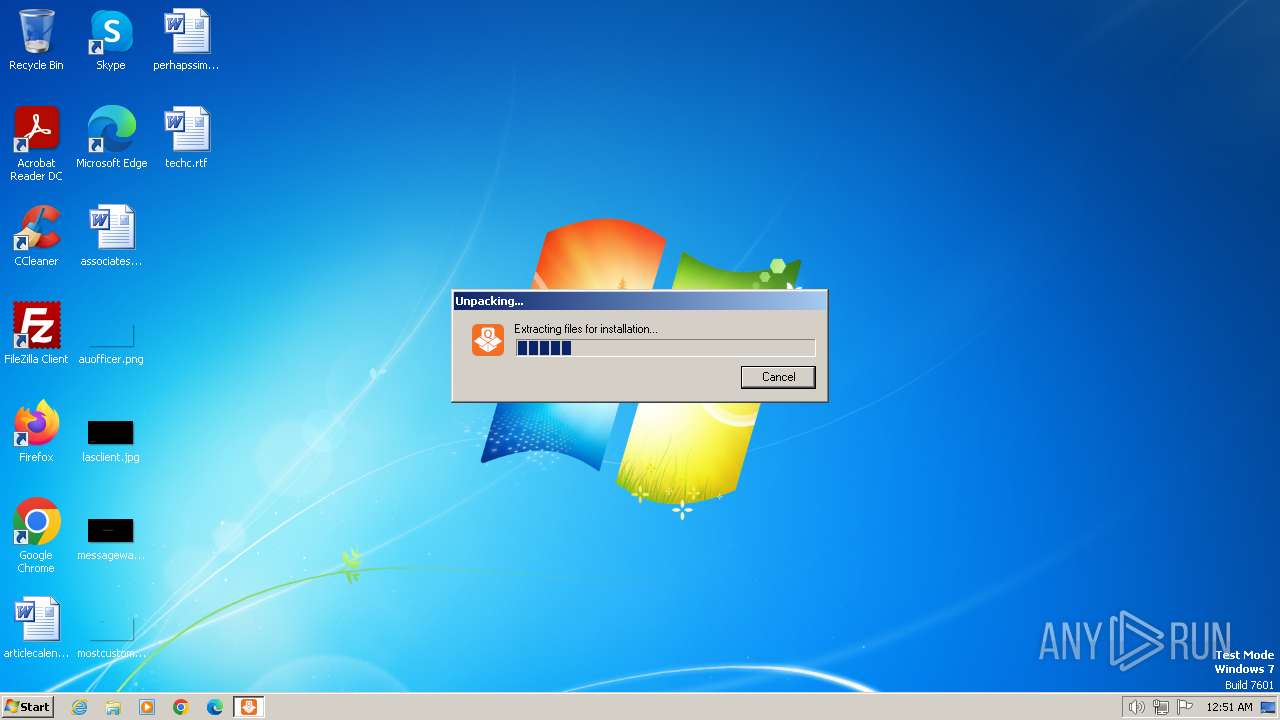
| Analysis date: | February 13, 2024, 00:51:37 |
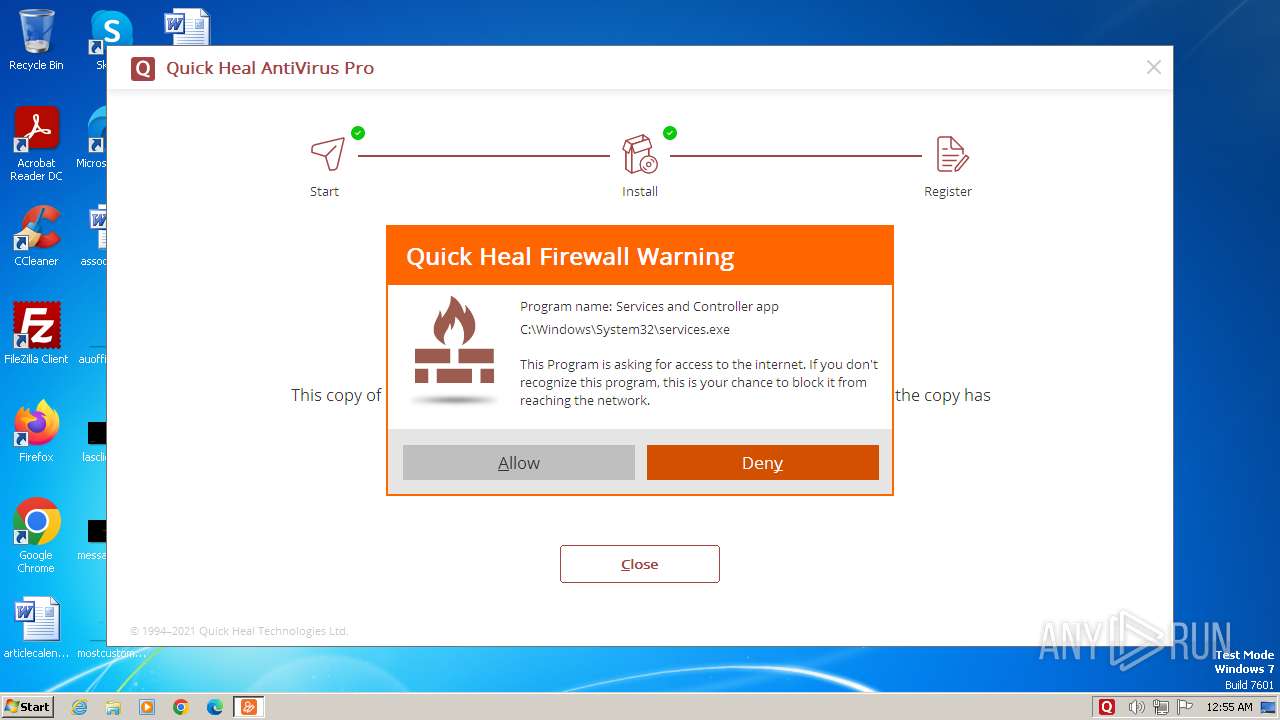
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2A26198809FFA6433C314F4A7B83173A |
| SHA1: | 6655DB3096F145C4D2DB3AF625AD3C9BA085CDF7 |
| SHA256: | B19D2DBB66FA025D9D8CDEA6F01A58A71FAD7877A225CA1B286FCEE4D9B472DB |
| SSDEEP: | 98304:rd8j7v4InohbhOWfXtwawco+R/aoA0QJiw/pvusuGczFd3Uk/xCmgTWc4UxI/DLx:yv6TgwukYmvQdKRBhR |
MALICIOUS
Changes the autorun value in the registry
- INST.EXE (PID: 2844)
Drops the executable file immediately after the start
- QHAVFT.EXE.exe (PID: 3708)
- INST.EXE (PID: 2844)
- drvinst.exe (PID: 3924)
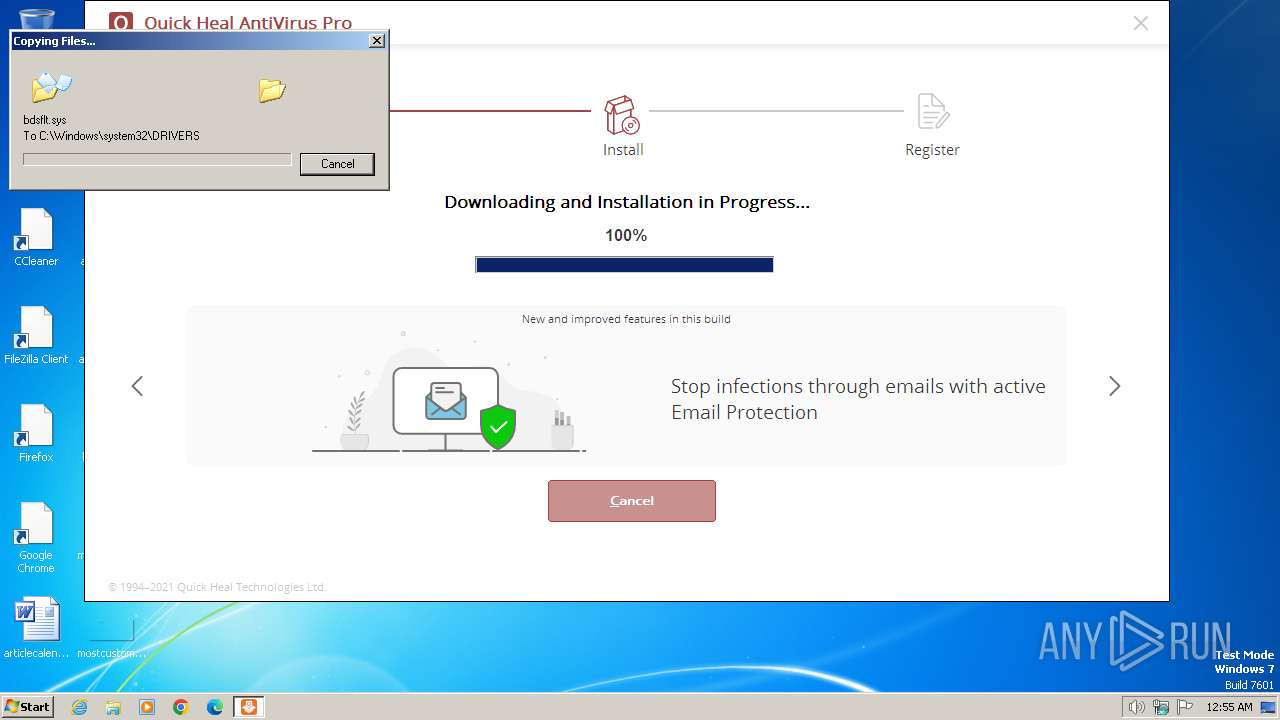
Creates a writable file in the system directory
- INST.EXE (PID: 2844)
- drvinst.exe (PID: 3924)
- ARWSRVC.EXE (PID: 3892)
- BDSSVC.EXE (PID: 752)
SODINOKIBI has been detected (YARA)
- SAPISSVC.EXE (PID: 3468)
COBALTSTRIKE has been detected (YARA)
- SAPISSVC.EXE (PID: 3468)
CVE-2022-30190 detected
- SAPISSVC.EXE (PID: 3468)
Application was injected by another process
- svchost.exe (PID: 596)
Runs injected code in another process
- BDSSVC.EXE (PID: 752)
DARKGATE has been detected (YARA)
- SAPISSVC.EXE (PID: 3468)
SUSPICIOUS
The process drops C-runtime libraries
- QHAVFT.EXE.exe (PID: 3708)
- expand.exe (PID: 1112)
- expand.exe (PID: 2248)
Process drops legitimate windows executable
- QHAVFT.EXE.exe (PID: 3708)
- expand.exe (PID: 1112)
- expand.exe (PID: 2248)
Executable content was dropped or overwritten
- QHAVFT.EXE.exe (PID: 3708)
- expand.exe (PID: 1112)
- INST.EXE (PID: 2844)
- expand.exe (PID: 2248)
- drvinst.exe (PID: 3924)
Reads the Internet Settings
- INST.EXE (PID: 2844)
- runonce.exe (PID: 2592)
- runonce.exe (PID: 3112)
- runonce.exe (PID: 2032)
- runonce.exe (PID: 2492)
- runonce.exe (PID: 3692)
- runonce.exe (PID: 2592)
- runonce.exe (PID: 2060)
- runonce.exe (PID: 3920)
- runonce.exe (PID: 3348)
- ONLINENT.EXE (PID: 3112)
- ACTIVATE.EXE (PID: 3760)
- QUICKUP.EXE (PID: 2928)
Reads security settings of Internet Explorer
- INST.EXE (PID: 2844)
- QHAVFT32.EXE (PID: 3308)
- QUICKUP.EXE (PID: 2928)
- ACTIVATE.EXE (PID: 3760)
Process requests binary or script from the Internet
- INST.EXE (PID: 2844)
Checks Windows Trust Settings
- QHAVFT32.EXE (PID: 3308)
- ARWSRVC.EXE (PID: 3892)
- drvinst.exe (PID: 3924)
- BDSSVC.EXE (PID: 752)
- ACTIVATE.EXE (PID: 3760)
- EMLPROXY.EXE (PID: 2588)
Reads settings of System Certificates
- QHAVFT32.EXE (PID: 3308)
- ACTIVATE.EXE (PID: 3760)
Drops a system driver (possible attempt to evade defenses)
- INST.EXE (PID: 2844)
- expand.exe (PID: 1112)
- drvinst.exe (PID: 3924)
Searches for installed software
- INST.EXE (PID: 2844)
Reads the Windows owner or organization settings
- INST.EXE (PID: 2844)
The process verifies whether the antivirus software is installed
- SCANWSCS.EXE (PID: 2640)
- INST.EXE (PID: 2844)
- SAPISSVC.EXE (PID: 920)
- SAPISSVC.EXE (PID: 2736)
- SCANWSCS.EXE (PID: 3252)
- SCSECSVC.EXE (PID: 3396)
- QHPISVR.EXE (PID: 1424)
- SCSECSVC.EXE (PID: 1388)
- ARWSRVC.EXE (PID: 3348)
- ARWSRVC.EXE (PID: 3892)
- SAPISSVC.EXE (PID: 3468)
- SCANWSCS.EXE (PID: 3820)
- OPSSVC.EXE (PID: 3852)
- OPSSVC.EXE (PID: 1972)
- OPSSVC.EXE (PID: 2384)
- OPSSVC.EXE (PID: 1888)
- EMLPROXY.EXE (PID: 1036)
- BDSSVC.EXE (PID: 920)
- OPSSVC.EXE (PID: 844)
- EMLPROUI.EXE (PID: 1932)
- ONLINENT.EXE (PID: 3112)
- EMLPROXY.EXE (PID: 2820)
- EMLPROUI.EXE (PID: 604)
- EMLPROXY.EXE (PID: 3768)
- REPRSVC.EXE (PID: 2860)
- EMLPROXY.EXE (PID: 2232)
- REPRSVC.EXE (PID: 1216)
- REPRSVC.EXE (PID: 2016)
- EMLPROUI.EXE (PID: 3324)
- EMLPROXY.EXE (PID: 3896)
- EMLPROXY.EXE (PID: 2588)
- BDSSVC.EXE (PID: 3492)
- BDSSVC.EXE (PID: 3396)
- QUHLPSVC.EXE (PID: 2568)
- QUHLPSVC.EXE (PID: 3156)
- ONLINENT.EXE (PID: 3416)
- QUICKUP.EXE (PID: 3504)
- SCANNER.EXE (PID: 2108)
- ACTIVATE.EXE (PID: 3760)
- BDSSVC.EXE (PID: 752)
- QUICKUP.EXE (PID: 2928)
Creates files in the driver directory
- INST.EXE (PID: 2844)
- drvinst.exe (PID: 3924)
Executes as Windows Service
- SAPISSVC.EXE (PID: 3468)
- SCANWSCS.EXE (PID: 3252)
- SCSECSVC.EXE (PID: 1388)
- ARWSRVC.EXE (PID: 3892)
- OPSSVC.EXE (PID: 1888)
- REPRSVC.EXE (PID: 1216)
- EMLPROXY.EXE (PID: 2588)
- QUHLPSVC.EXE (PID: 3156)
- BDSSVC.EXE (PID: 752)
Creates or modifies Windows services
- SCSECSVC.EXE (PID: 3396)
Creates/Modifies COM task schedule object
- INST.EXE (PID: 2844)
Application launched itself
- QUICKUP.EXE (PID: 3504)
Adds/modifies Windows certificates
- BDSSVC.EXE (PID: 752)
INFO
Checks supported languages
- QHAVFT.EXE.exe (PID: 3708)
- INST.EXE (PID: 2844)
- QHAVFT32.EXE (PID: 3308)
- qhclean.exe (PID: 2336)
- SCANWSCS.EXE (PID: 2640)
- SAPISSVC.EXE (PID: 920)
- SCANWSCS.EXE (PID: 3252)
- SAPISSVC.EXE (PID: 3468)
- SCSECSVC.EXE (PID: 3396)
- SAPISSVC.EXE (PID: 2736)
- QHPISVR.EXE (PID: 1424)
- SCSECSVC.EXE (PID: 1388)
- ARWSRVC.EXE (PID: 3348)
- drvinst.exe (PID: 3924)
- ARWSRVC.EXE (PID: 3892)
- SCANWSCS.EXE (PID: 3820)
- OPSSVC.EXE (PID: 3852)
- OPSSVC.EXE (PID: 1972)
- OPSSVC.EXE (PID: 2384)
- OPSSVC.EXE (PID: 1888)
- EMLPROXY.EXE (PID: 1036)
- BDSSVC.EXE (PID: 920)
- OPSSVC.EXE (PID: 844)
- ONLINENT.EXE (PID: 3112)
- EMLPROUI.EXE (PID: 1932)
- EMLPROXY.EXE (PID: 3768)
- EMLPROUI.EXE (PID: 604)
- EMLPROXY.EXE (PID: 2820)
- EMLPROXY.EXE (PID: 2232)
- REPRSVC.EXE (PID: 1216)
- wmpnscfg.exe (PID: 3120)
- REPRSVC.EXE (PID: 2016)
- REPRSVC.EXE (PID: 2860)
- EMLPROXY.EXE (PID: 3896)
- QUHLPSVC.EXE (PID: 1972)
- EMLPROXY.EXE (PID: 2588)
- QUHLPSVC.EXE (PID: 2568)
- EMLPROUI.EXE (PID: 3324)
- QUHLPSVC.EXE (PID: 3156)
- BDSSVC.EXE (PID: 3492)
- wmpnscfg.exe (PID: 3540)
- BDSSVC.EXE (PID: 752)
- ONLINENT.EXE (PID: 3416)
- BDSSVC.EXE (PID: 3396)
- QUICKUP.EXE (PID: 3504)
- ACTIVATE.EXE (PID: 3760)
- SCANNER.EXE (PID: 2108)
- QUICKUP.EXE (PID: 2928)
Create files in a temporary directory
- QHAVFT.EXE.exe (PID: 3708)
- INST.EXE (PID: 2844)
- QHAVFT32.EXE (PID: 3308)
- expand.exe (PID: 1112)
- expand.exe (PID: 2060)
- expand.exe (PID: 2248)
Reads the computer name
- INST.EXE (PID: 2844)
- QHAVFT32.EXE (PID: 3308)
- qhclean.exe (PID: 2336)
- SCANWSCS.EXE (PID: 2640)
- SCANWSCS.EXE (PID: 3252)
- SAPISSVC.EXE (PID: 2736)
- SAPISSVC.EXE (PID: 920)
- SAPISSVC.EXE (PID: 3468)
- QHPISVR.EXE (PID: 1424)
- SCSECSVC.EXE (PID: 3396)
- SCSECSVC.EXE (PID: 1388)
- ARWSRVC.EXE (PID: 3348)
- drvinst.exe (PID: 3924)
- ARWSRVC.EXE (PID: 3892)
- SCANWSCS.EXE (PID: 3820)
- OPSSVC.EXE (PID: 3852)
- OPSSVC.EXE (PID: 1972)
- OPSSVC.EXE (PID: 844)
- OPSSVC.EXE (PID: 1888)
- ONLINENT.EXE (PID: 3112)
- BDSSVC.EXE (PID: 920)
- EMLPROXY.EXE (PID: 1036)
- OPSSVC.EXE (PID: 2384)
- EMLPROXY.EXE (PID: 3768)
- EMLPROXY.EXE (PID: 2820)
- REPRSVC.EXE (PID: 2860)
- EMLPROXY.EXE (PID: 2232)
- REPRSVC.EXE (PID: 2016)
- EMLPROXY.EXE (PID: 3896)
- QUHLPSVC.EXE (PID: 1972)
- EMLPROXY.EXE (PID: 2588)
- wmpnscfg.exe (PID: 3120)
- BDSSVC.EXE (PID: 3492)
- QUHLPSVC.EXE (PID: 3156)
- BDSSVC.EXE (PID: 3396)
- QUHLPSVC.EXE (PID: 2568)
- wmpnscfg.exe (PID: 3540)
- BDSSVC.EXE (PID: 752)
- ONLINENT.EXE (PID: 3416)
- QUICKUP.EXE (PID: 3504)
- ACTIVATE.EXE (PID: 3760)
- QUICKUP.EXE (PID: 2928)
- REPRSVC.EXE (PID: 1216)
Reads the machine GUID from the registry
- INST.EXE (PID: 2844)
- QHAVFT32.EXE (PID: 3308)
- SCANWSCS.EXE (PID: 3252)
- SCANWSCS.EXE (PID: 2640)
- QHPISVR.EXE (PID: 1424)
- SAPISSVC.EXE (PID: 3468)
- drvinst.exe (PID: 3924)
- ONLINENT.EXE (PID: 3112)
- BDSSVC.EXE (PID: 752)
- ACTIVATE.EXE (PID: 3760)
- QUICKUP.EXE (PID: 2928)
- EMLPROXY.EXE (PID: 2588)
- ARWSRVC.EXE (PID: 3892)
Checks proxy server information
- INST.EXE (PID: 2844)
- ONLINENT.EXE (PID: 3112)
- ACTIVATE.EXE (PID: 3760)
- QUICKUP.EXE (PID: 2928)
Reads the software policy settings
- QHAVFT32.EXE (PID: 3308)
- ARWSRVC.EXE (PID: 3892)
- drvinst.exe (PID: 3924)
- BDSSVC.EXE (PID: 752)
- EMLPROXY.EXE (PID: 2588)
- ACTIVATE.EXE (PID: 3760)
Creates files in the program directory
- INST.EXE (PID: 2844)
- SCANWSCS.EXE (PID: 2640)
- QHPISVR.EXE (PID: 1424)
- SCSECSVC.EXE (PID: 3396)
- SAPISSVC.EXE (PID: 3468)
- ARWSRVC.EXE (PID: 3892)
- OPSSVC.EXE (PID: 1888)
- ONLINENT.EXE (PID: 3112)
- BDSSVC.EXE (PID: 752)
- QUICKUP.EXE (PID: 3504)
- ACTIVATE.EXE (PID: 3760)
- SCANNER.EXE (PID: 2108)
- EMLPROXY.EXE (PID: 2588)
Drops the executable file immediately after the start
- expand.exe (PID: 1112)
- expand.exe (PID: 2248)
Reads the time zone
- runonce.exe (PID: 2592)
- runonce.exe (PID: 3112)
- runonce.exe (PID: 2492)
- runonce.exe (PID: 2032)
- runonce.exe (PID: 3692)
- runonce.exe (PID: 2060)
- runonce.exe (PID: 2592)
- runonce.exe (PID: 3920)
- runonce.exe (PID: 3348)
Reads security settings of Internet Explorer
- runonce.exe (PID: 2592)
- runonce.exe (PID: 3112)
- runonce.exe (PID: 2492)
- runonce.exe (PID: 2032)
- runonce.exe (PID: 3692)
- runonce.exe (PID: 2592)
- runonce.exe (PID: 2060)
- runonce.exe (PID: 3920)
- runonce.exe (PID: 3348)
Manual execution by a user
- wmpnscfg.exe (PID: 3120)
- wmpnscfg.exe (PID: 3540)
- taskmgr.exe (PID: 4624)
Creates files or folders in the user directory
- EMLPROXY.EXE (PID: 2588)
- QUICKUP.EXE (PID: 2928)
- ACTIVATE.EXE (PID: 3760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:07:23 07:20:46+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 176128 |
| InitializedDataSize: | 167936 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x186b6 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 13.1.0.1 |
| ProductVersionNumber: | 22.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
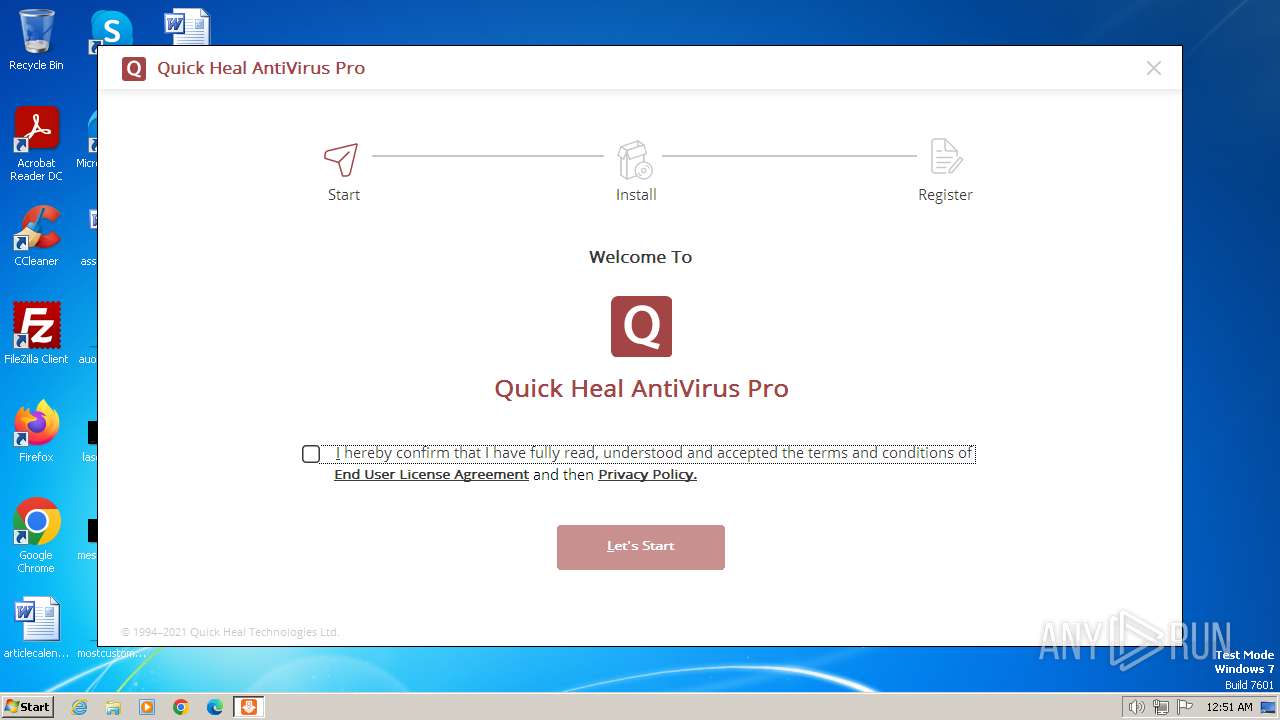
| CompanyName: | Quick Heal Technologies Ltd. |
| FileDescription: | qhunpack.exe |
| FileVersion: | 13.1.0.1 |
| LegalCopyright: | © Quick Heal Technologies Ltd. All rights reserved. |
| OriginalFileName: | qhunpack.exe |
| ProductName: | Quick Heal Unpacker |
| ProductVersion: | 22 |
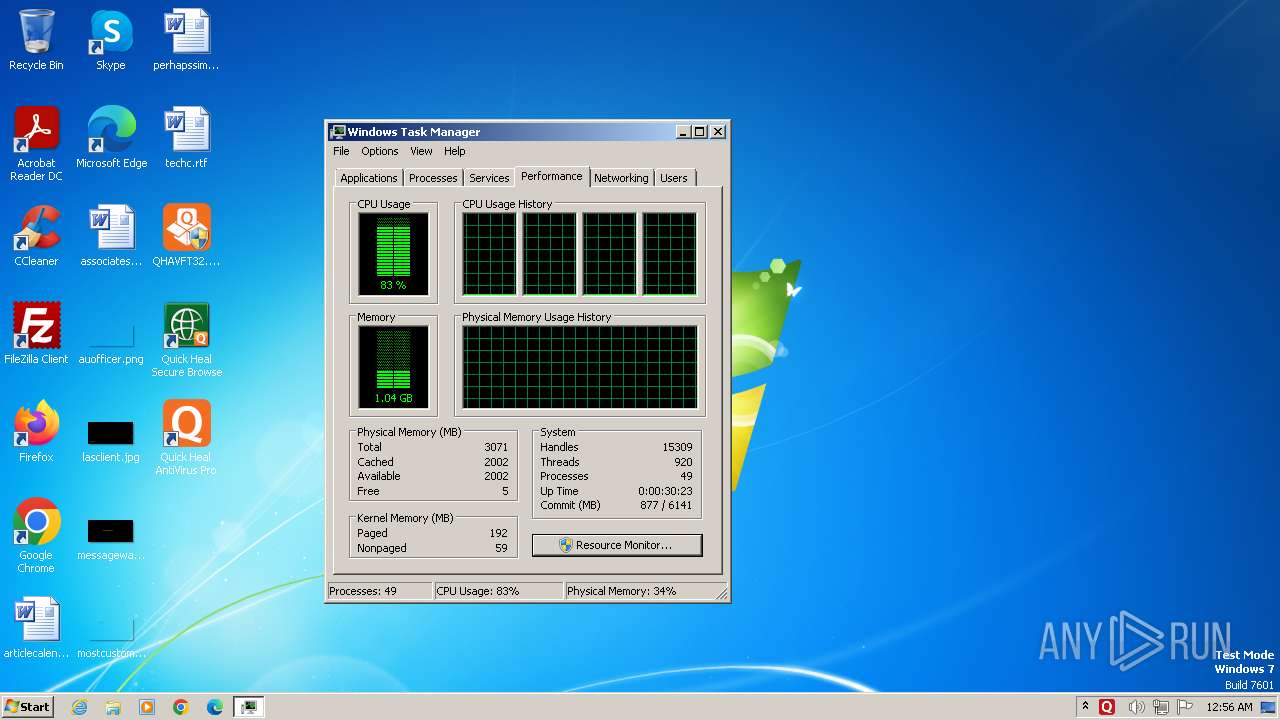
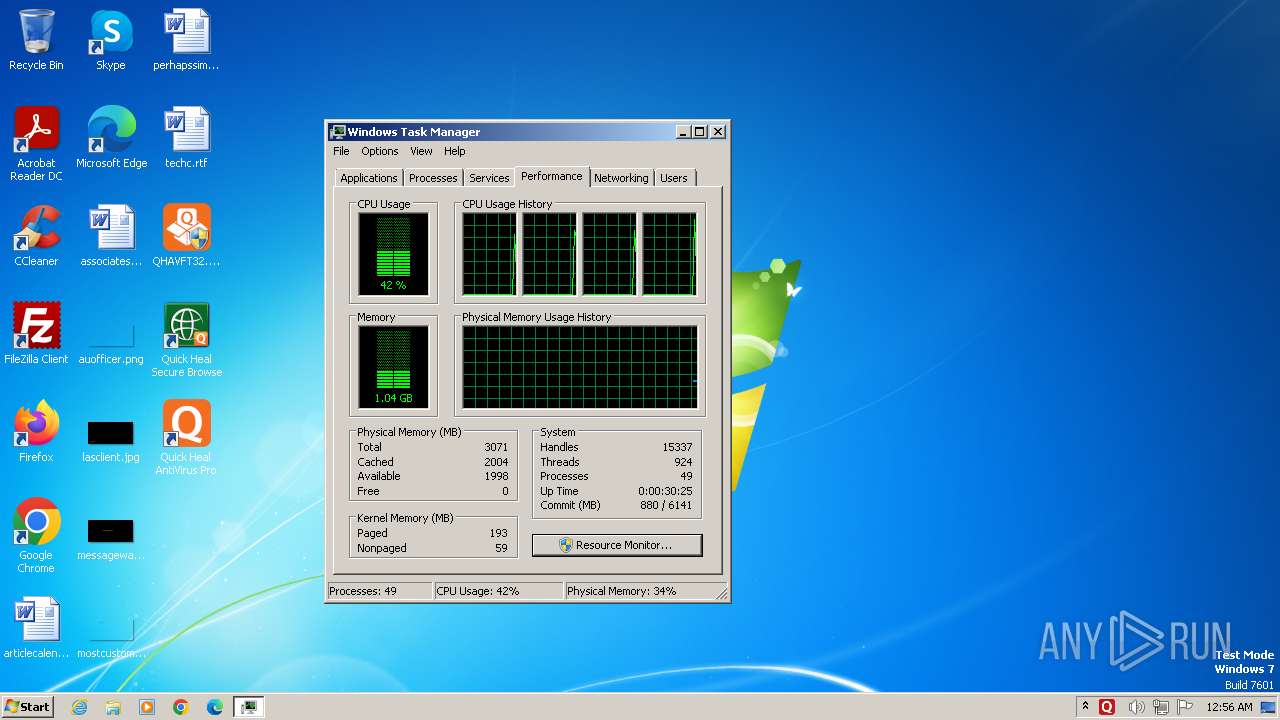
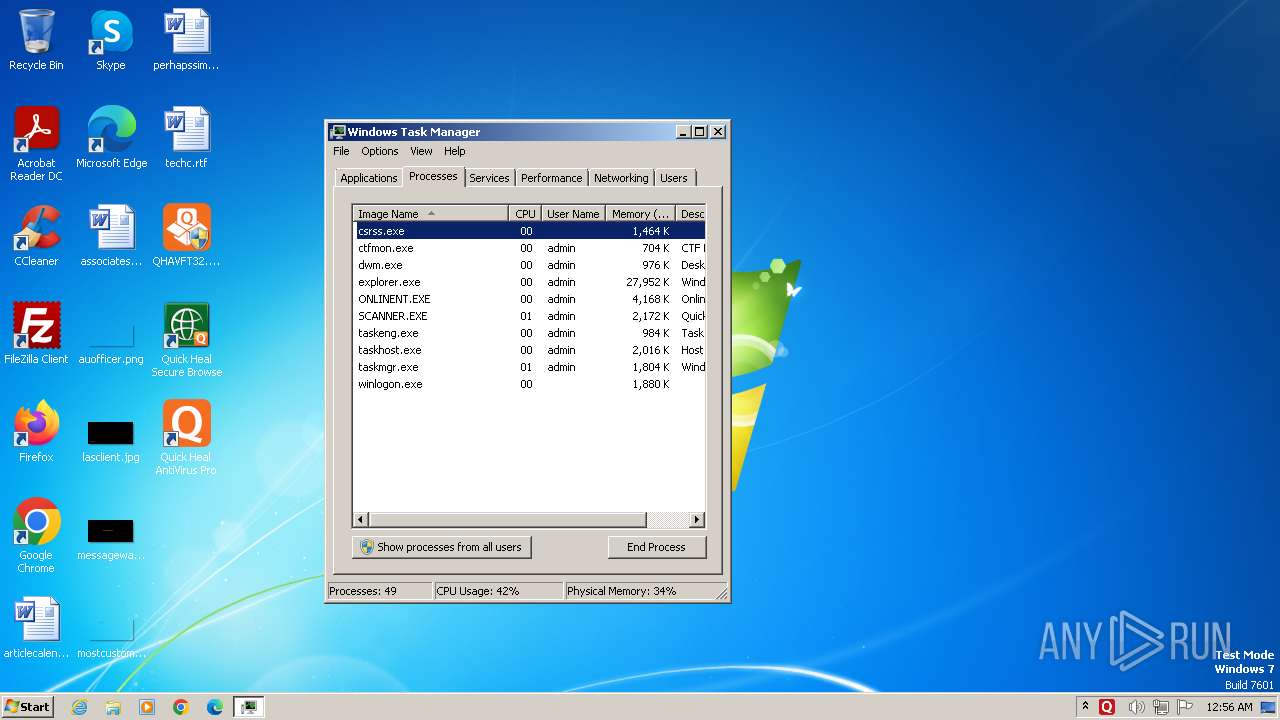
Total processes
148
Monitored processes
72
Malicious processes
32
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 596 | C:\Windows\system32\svchost.exe -k DcomLaunch | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 604 | "C:\Program Files\Quick Heal\Quick Heal AntiVirus Pro\emlproui.exe" | C:\Program Files\Quick Heal\Quick Heal AntiVirus Pro\EMLPROUI.EXE | — | INST.EXE | |||||||||||
User: admin Company: Quick Heal Technologies Ltd. Integrity Level: HIGH Description: Email Protection Exit code: 0 Version: 13.1.0.2 Modules
| |||||||||||||||
| 752 | "C:\Program Files\Quick Heal\Quick Heal AntiVirus Pro\bdssvc.exe" | C:\Program Files\Quick Heal\Quick Heal AntiVirus Pro\BDSSVC.EXE | services.exe | ||||||||||||
User: SYSTEM Company: Quick Heal Technologies Ltd. Integrity Level: SYSTEM Description: BDS Service Application Exit code: 0 Version: 11.1.90.29 Modules
| |||||||||||||||
| 844 | "C:\Program Files\Quick Heal\Quick Heal AntiVirus Pro\opssvc.exe" -start | C:\Program Files\Quick Heal\Quick Heal AntiVirus Pro\OPSSVC.EXE | — | INST.EXE | |||||||||||
User: admin Company: Quick Heal Technologies Ltd. Integrity Level: HIGH Description: Online Protection System Service Exit code: 0 Version: 13.1.0.2 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Quick Heal\Quick Heal AntiVirus Pro\SAPISSVC.EXE" -install | C:\Program Files\Quick Heal\Quick Heal AntiVirus Pro\SAPISSVC.EXE | — | INST.EXE | |||||||||||
User: admin Company: Quick Heal Technologies Ltd. Integrity Level: HIGH Description: Antimalware Scan Service Exit code: 0 Version: 11.1.0.1 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Quick Heal\Quick Heal AntiVirus Pro\bdssvc.exe" -uninstall | C:\Program Files\Quick Heal\Quick Heal AntiVirus Pro\BDSSVC.EXE | — | INST.EXE | |||||||||||
User: admin Company: Quick Heal Technologies Ltd. Integrity Level: HIGH Description: BDS Service Application Exit code: 0 Version: 11.1.90.29 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Quick Heal\Quick Heal AntiVirus Pro\EmlProxy.exe" -start | C:\Program Files\Quick Heal\Quick Heal AntiVirus Pro\EMLPROXY.EXE | — | INST.EXE | |||||||||||
User: admin Company: Quick Heal Technologies Ltd. Integrity Level: HIGH Description: Mail Protection Service Exit code: 0 Version: 13.1.0.2 Modules
| |||||||||||||||
| 1112 | "C:\Windows\system32\expand.exe" "C:\Users\admin\AppData\Local\Temp\QH8474.ins\init.cab" -F:* "C:\Users\admin\AppData\Local\Temp\QH8474.ins" | C:\Windows\System32\expand.exe | QHAVFT32.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: LZ Expansion Utility Exit code: 1 Version: 6.1.7601.24535 (win7sp1_ldr_escrow.191105-1059) Modules
| |||||||||||||||
| 1216 | "C:\Program Files\Quick Heal\Quick Heal AntiVirus Pro\reprsvc.exe" | C:\Program Files\Quick Heal\Quick Heal AntiVirus Pro\REPRSVC.EXE | — | services.exe | |||||||||||
User: SYSTEM Company: Quick Heal Technologies Ltd. Integrity Level: SYSTEM Description: Repair Service Exit code: 0 Version: 13.1.0.2 Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Quick Heal\Quick Heal AntiVirus Pro\ScSecSvc.exe" | C:\Program Files\Quick Heal\Quick Heal AntiVirus Pro\SCSECSVC.EXE | services.exe | ||||||||||||
User: SYSTEM Company: Quick Heal Technologies Ltd. Integrity Level: SYSTEM Description: Browser Sandbox Safe Browsing Security Service Exit code: 0 Version: 3.0.1.29 Modules
| |||||||||||||||
Total events
87 739
Read events
86 648
Write events
1 000
Delete events
91
Modification events
| (PID) Process: | (2844) INST.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2844) INST.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2844) INST.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2844) INST.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2844) INST.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
| (PID) Process: | (2844) INST.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyOverride |
Value: | |||
| (PID) Process: | (2844) INST.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoConfigURL |
Value: | |||
| (PID) Process: | (2844) INST.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoDetect |
Value: | |||
| (PID) Process: | (2844) INST.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005C010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2844) INST.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
233
Suspicious files
757
Text files
60
Unknown types
274
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3708 | QHAVFT.EXE.exe | C:\Users\admin\AppData\Local\Temp\QH8474.ins\QHDATA.ARJ | — | |
MD5:— | SHA256:— | |||
| 3708 | QHAVFT.EXE.exe | C:\Users\admin\AppData\Local\Temp\QH8474.ins\INST_32.DLL | binary | |
MD5:DA6CE791A2204B8F834D5C89038B3ECC | SHA256:67F88FCA7064FECB2CD8416B321873111B9DE002310C799BD3D2336B9EACEC13 | |||
| 3708 | QHAVFT.EXE.exe | C:\Users\admin\AppData\Local\Temp\QH8474.ins\MFC90_32.DLL | executable | |
MD5:79BF45E2AD6BCF754D35DA012C1B164B | SHA256:22418C87915E5A0E9679C48050F95D835CF6EA59BE67923743F581F6C71B9C7D | |||
| 3708 | QHAVFT.EXE.exe | C:\Users\admin\AppData\Local\Temp\QH8474.ins\CTR_32.DLL | executable | |
MD5:1C9EB4A40DB69671CFA021E22EAD59B6 | SHA256:E8C34C18DAB603FA555A12FAA4C8F9073EAEBEDD7362C4F09F442DD524FB6D49 | |||
| 3708 | QHAVFT.EXE.exe | C:\Users\admin\AppData\Local\Temp\QH8474.ins\MSICONF.DAT | csp | |
MD5:22A6D730804E564476BCDE9E55CAF3AE | SHA256:15459C75C82F609B62338D418BB33D17BFC585273ACF8FE2B663BDEBFB0ACFDA | |||
| 3708 | QHAVFT.EXE.exe | C:\Users\admin\AppData\Local\Temp\QH8474.ins\SETPDN.DAT | binary | |
MD5:9069682DC2B4C26C0E9D8E0D3E9FEA6E | SHA256:B63131973052C59B875C0760518F8AE14F70F1CFDCB57E7C25ADB7A5FCDDA27E | |||
| 3708 | QHAVFT.EXE.exe | C:\Users\admin\AppData\Local\Temp\QH8474.ins\CTR_64.DLL | executable | |
MD5:D10DA3CF888F9197A5206766BAF96245 | SHA256:30C48B13D0DC5D2261D6058DA3D8808FE6D768860CD0F29DB85BD9C4D25EBD08 | |||
| 3708 | QHAVFT.EXE.exe | C:\Users\admin\AppData\Local\Temp\QH8474.ins\SLIDERSE.INI | ini | |
MD5:7CE048B8DD506F92940E45E232C88601 | SHA256:D6B5C24E7A87F021712A263629E43E6781273665AAC919D72840ECD04058E7B0 | |||
| 3708 | QHAVFT.EXE.exe | C:\Users\admin\AppData\Local\Temp\QH8474.ins\INFOEML.DAT | binary | |
MD5:C09ECF5FB3532C2448E47CCFB3539EAA | SHA256:7CECF49C339A578E91C91A0F35FE408BCAFC1813FAA0E1523ACD352C6F7957AB | |||
| 3708 | QHAVFT.EXE.exe | C:\Users\admin\AppData\Local\Temp\QH8474.ins\MFC_32.MAN | xml | |
MD5:CE3AB3BD3FF80FCE88DCB0EA3D48A0C9 | SHA256:F7205C5C0A629D0CC60E30E288E339F08616BE67B55757D4A403A2B54E23922B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
31
DNS requests
10
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2844 | INST.EXE | GET | 200 | 64.185.181.238:80 | http://dlupdate.quickheal.com/builds/2200/eval/av/CONFIG.DAT | unknown | binary | 14.3 Kb | unknown |
2844 | INST.EXE | GET | — | 64.185.181.238:80 | http://dlupdate.quickheal.com/builds/2200/eval/av/QHAVFT32.EXE | unknown | — | — | unknown |
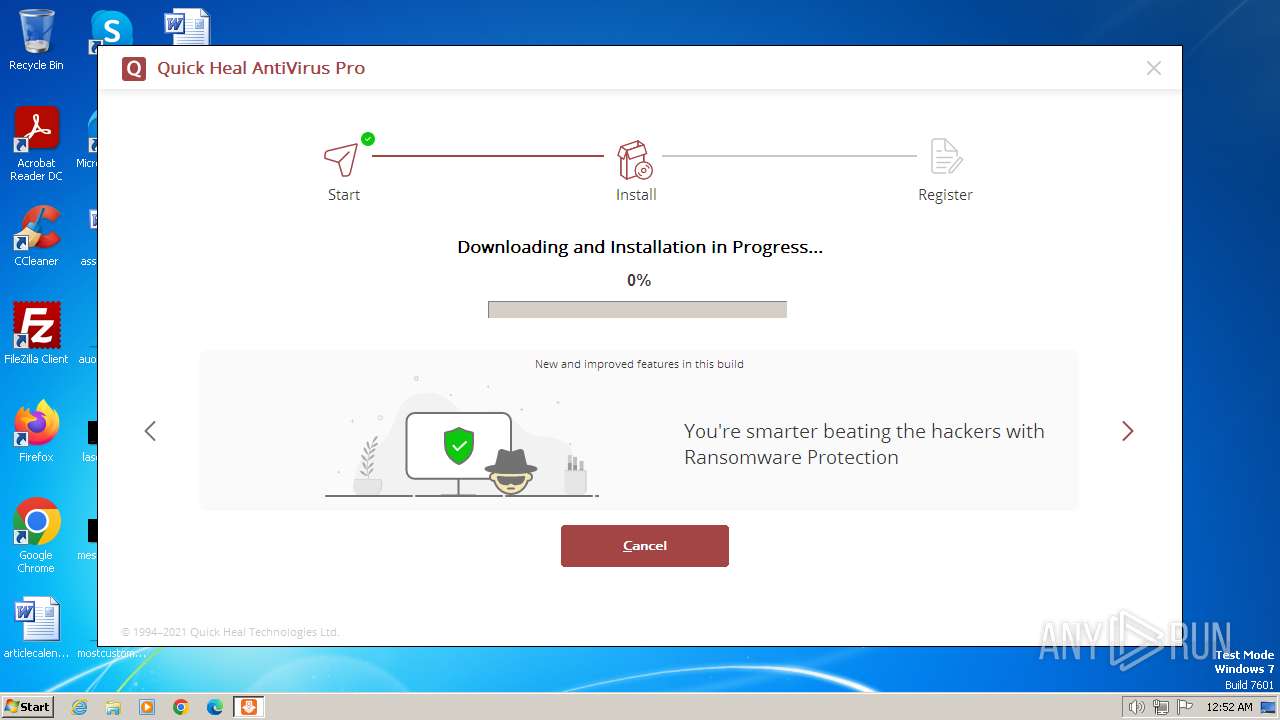
2844 | INST.EXE | GET | 200 | 64.185.181.238:80 | http://dlupdate.quickheal.com/builds/2200/eval/av/QHAVFT32.EXE | unknown | executable | 133 Mb | unknown |
3892 | ARWSRVC.EXE | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?647fd33e0fc40b53 | unknown | — | — | unknown |
3892 | ARWSRVC.EXE | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | binary | 767 b | unknown |
3892 | ARWSRVC.EXE | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/WinPCA.crl | unknown | binary | 530 b | unknown |
752 | BDSSVC.EXE | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | binary | 824 b | unknown |
2928 | QUICKUP.EXE | GET | 200 | 52.117.209.10:80 | http://virusmap.quickheal.com/msg32.htm | unknown | binary | 1 b | unknown |
752 | BDSSVC.EXE | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | binary | 519 b | unknown |
2928 | QUICKUP.EXE | GET | 200 | 52.117.209.10:80 | http://virusmap.quickheal.com/worldmap/detectinfo.php?data=7%2C0%2C0%2C20%2C0%2C1816837%2C2%2C0%2C6667C6F%2C22.00%2C0%2C0%2C0%2C0%2C0 | unknown | binary | 1 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2844 | INST.EXE | 64.185.181.238:80 | dlupdate.quickheal.com | BITGRAVITY | US | unknown |
3892 | ARWSRVC.EXE | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3892 | ARWSRVC.EXE | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | unknown |
752 | BDSSVC.EXE | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | unknown |
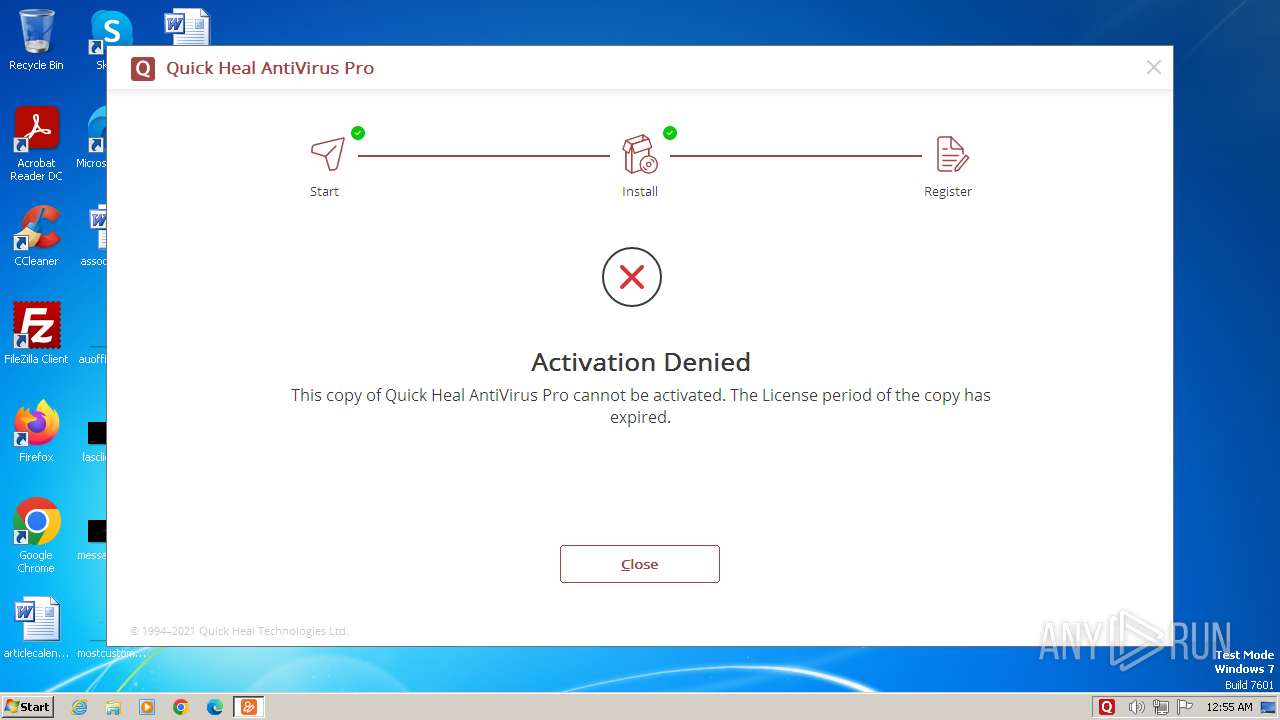
3760 | ACTIVATE.EXE | 13.233.240.42:443 | license1.quickheal.com | AMAZON-02 | IN | unknown |
2928 | QUICKUP.EXE | 52.117.209.10:80 | virusmap.quickheal.com | SOFTLAYER | US | unknown |
752 | BDSSVC.EXE | 104.79.89.142:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dlupdate.quickheal.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
license1.quickheal.com |
| unknown |
virusmap.quickheal.com |
| unknown |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
status.rapidssl.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2844 | INST.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2844 | INST.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
QHAVFT.EXE.exe | ExtractFilesToFolder |
QHAVFT.EXE.exe | Calling MoveFileAndAddDelTmpExeEntryToRunOnce(): FALSE == m_bSilentMode |
QHAVFT.EXE.exe | Start MoveFileAndAddDelTmpExeEntryToRunOnce(): C:\Users\admin\AppData\Local\Temp\QH8474.ins\ |
QHAVFT.EXE.exe | MoveFileAndAddDelTmpExeEntryToRunOnce::CopyFail FAIL: C:\Users\admin\AppData\Local\Temp\QH8474.ins\QHDELTMP.EXE and C:\Users\admin\AppData\Local\Temp\QHDELTMP.EXE |
QHAVFT.EXE.exe | SUCCESS ExtractFilesToFolder for ROOT.ARJ |
QHAVFT.EXE.exe | Calling MoveFileAndAddDelTmpExeEntryToRunOnce if m_bSilentMode = FALSE |
QHAVFT.EXE.exe | Start MoveFileAndAddDelTmpExeEntryToRunOnce(): C:\Users\admin\AppData\Local\Temp\QH8474.ins\ |
QHAVFT.EXE.exe | MoveFileAndAddDelTmpExeEntryToRunOnce::CopyFail FAIL: C:\Users\admin\AppData\Local\Temp\QH8474.ins\QHDELTMP.EXE and C:\Users\admin\AppData\Local\Temp\QHDELTMP.EXE |
QHAVFT.EXE.exe | PerformRenameOperation() Start |
QHAVFT.EXE.exe | C:\Users\admin\AppData\Local\Temp\QH8474.ins\\RenFile.ini |