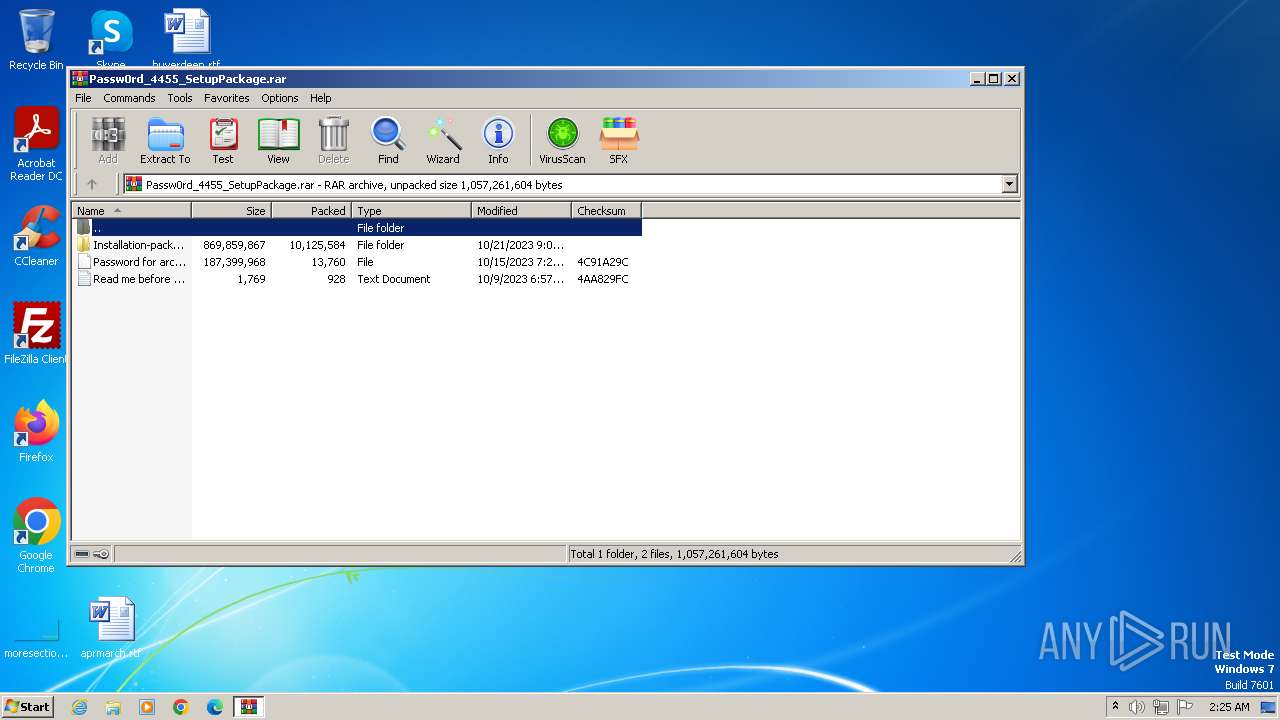
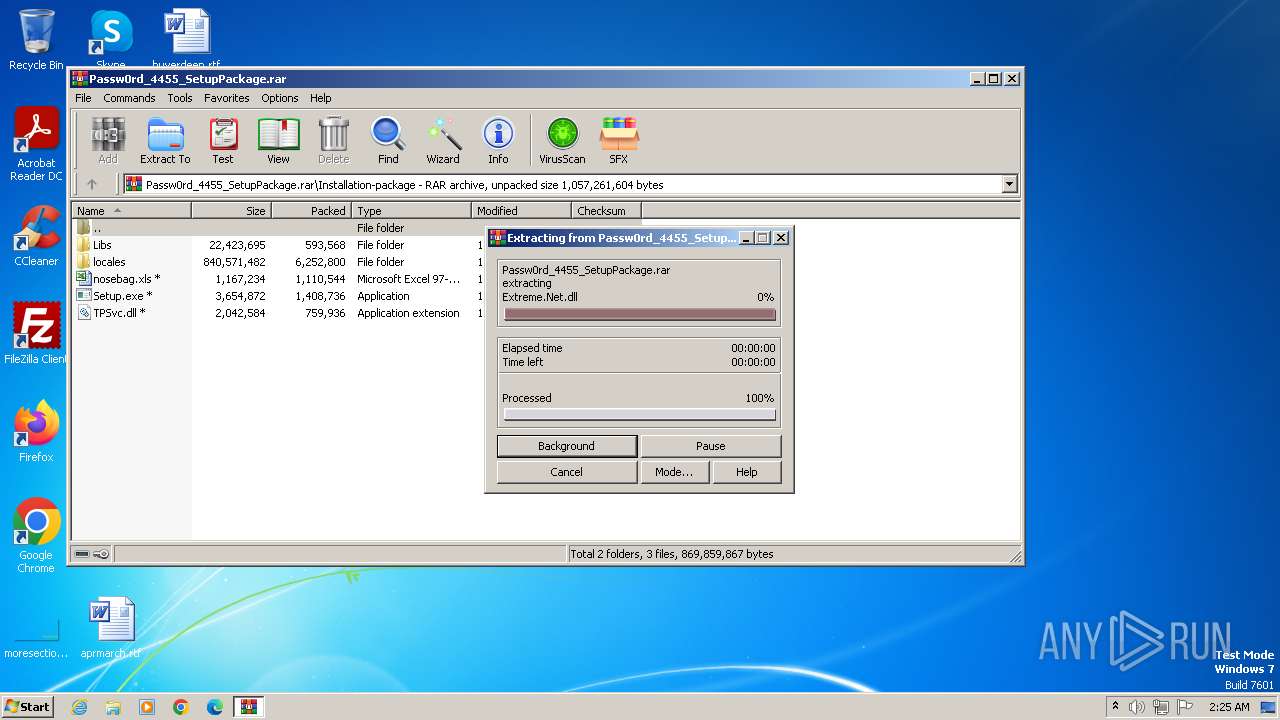
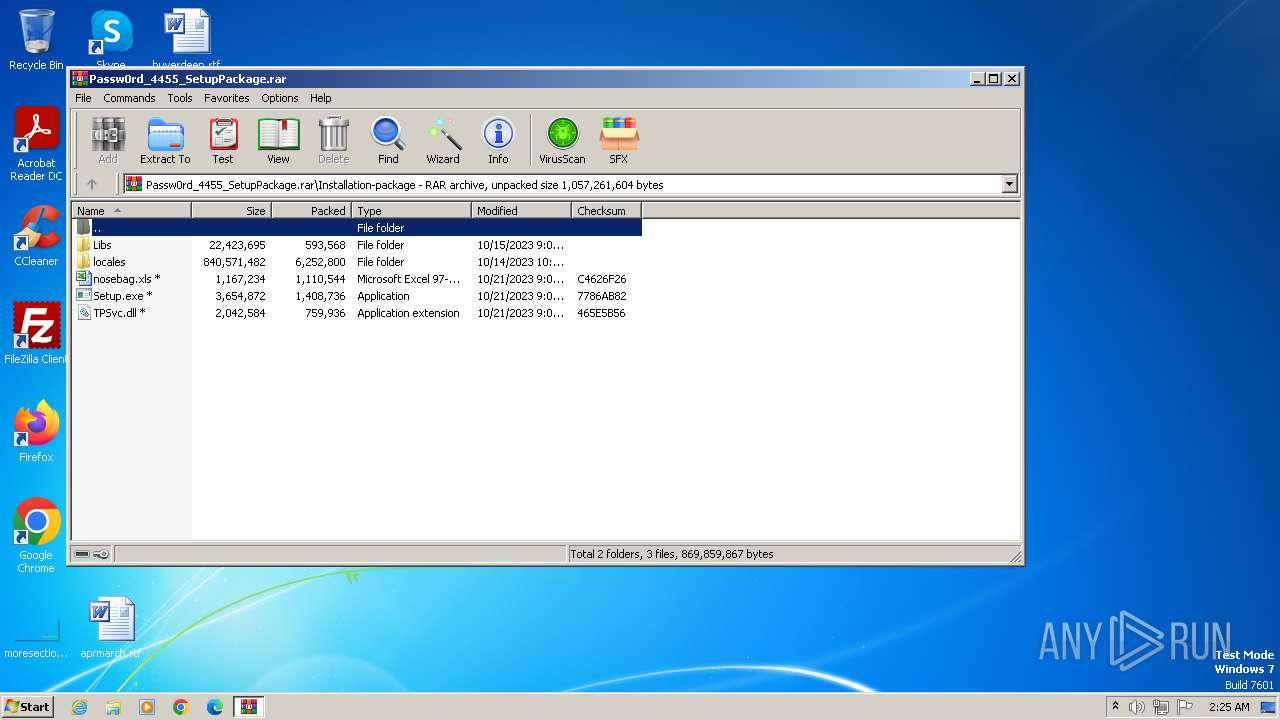
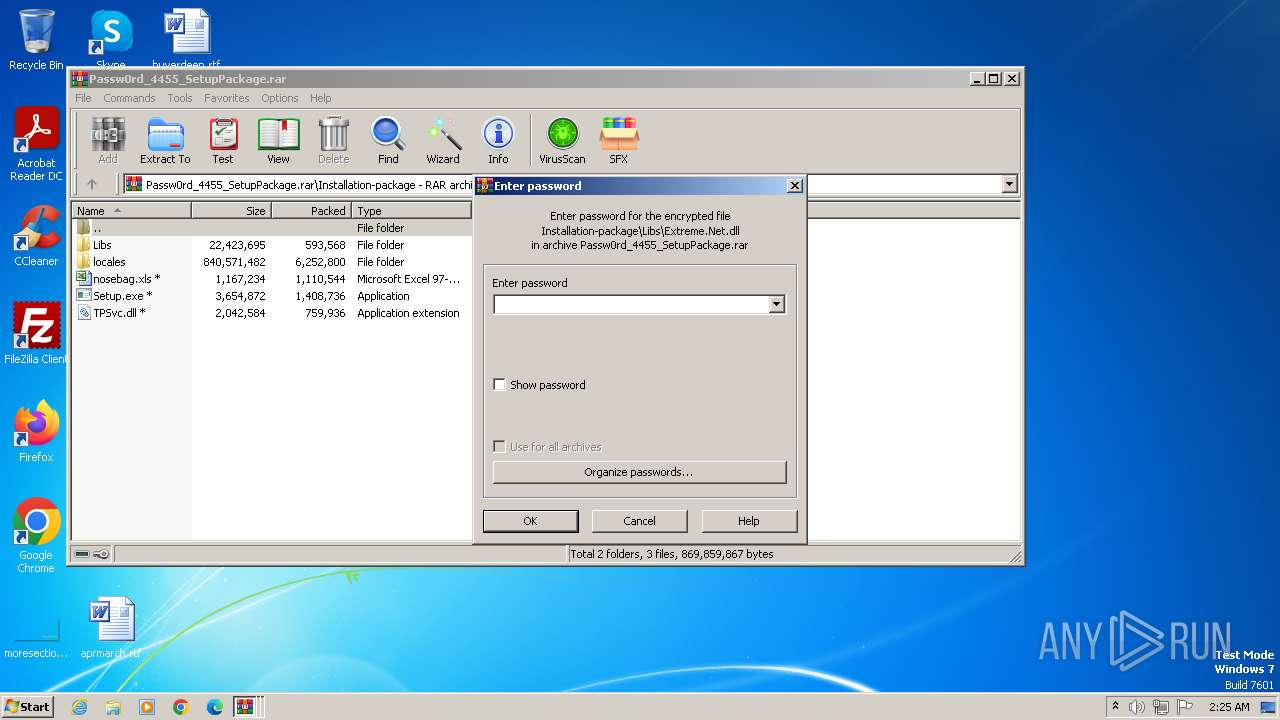
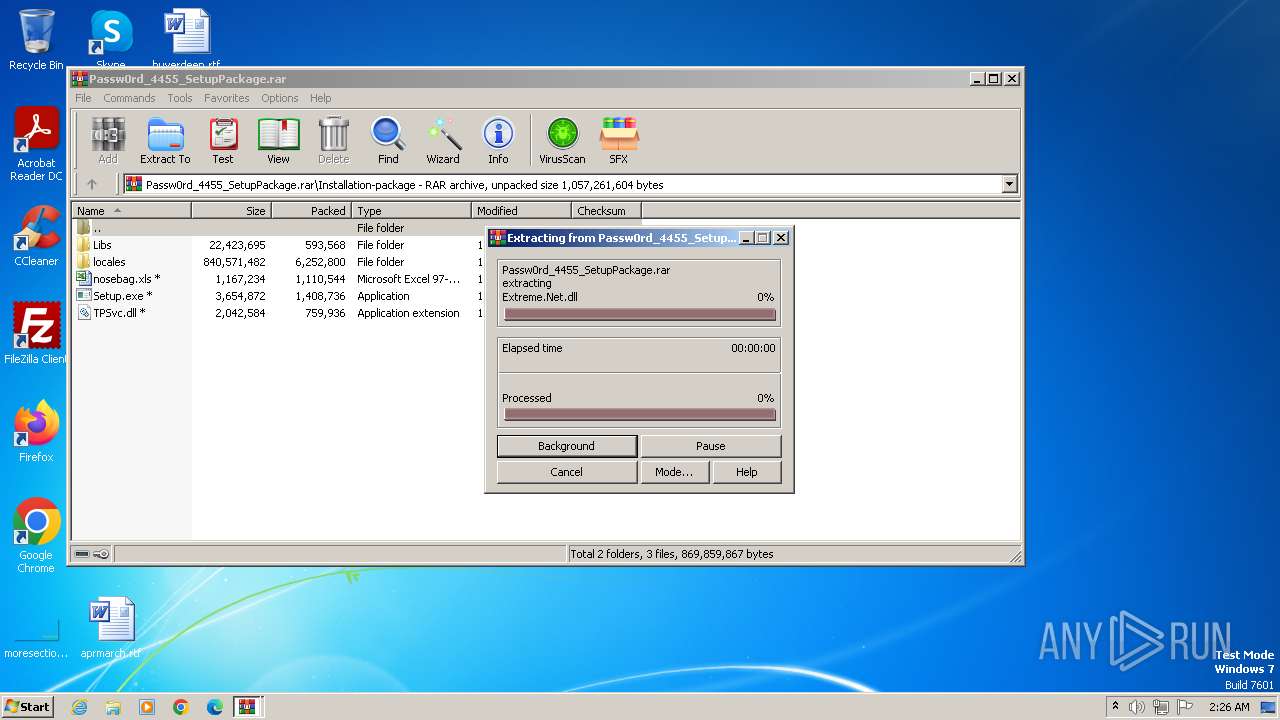
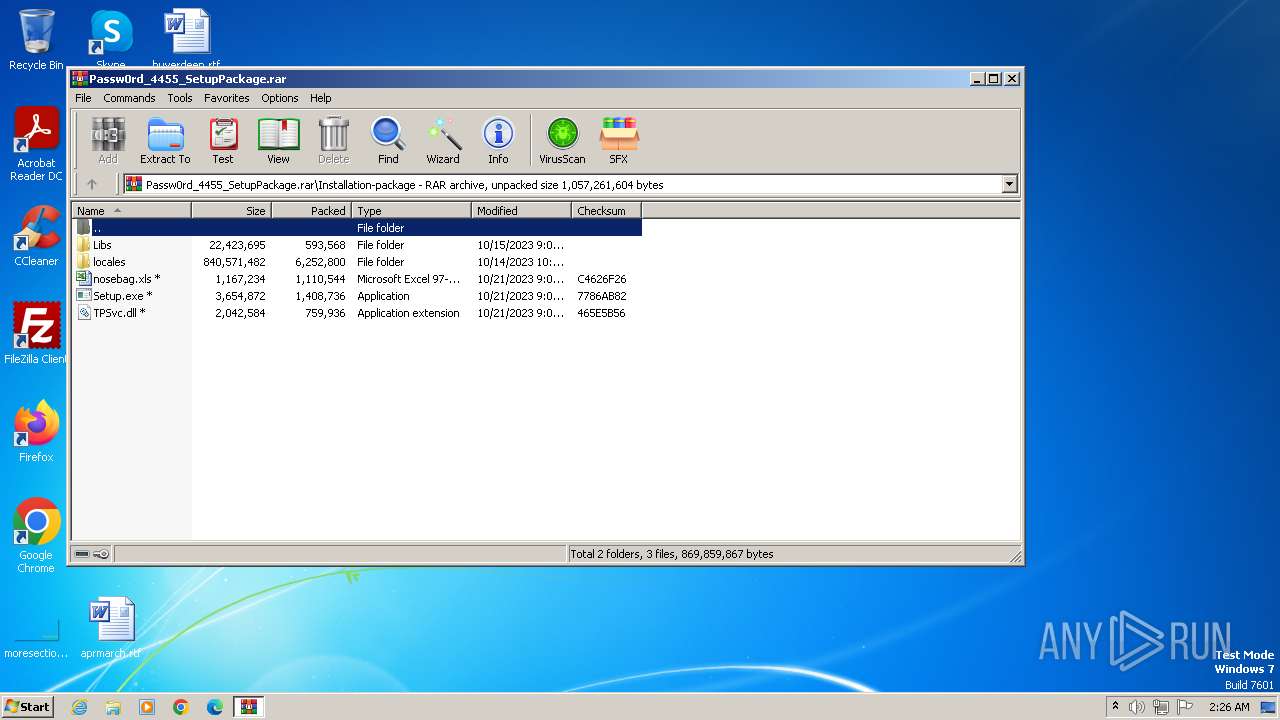
| File name: | Passw0rd_4455_SetupPackage.rar |
| Full analysis: | https://app.any.run/tasks/65ae9f31-068d-460d-9252-5cb9a5ddeee4 |
| Verdict: | Malicious activity |
| Threats: | HijackLoader is a modular malware acting as a vehicle for distributing different types of malicious software on compromised systems. It gained prominence during the summer of 2023 and has since been used in multiple attacks against organizations from various sectors, including hospitality businesses. |
| Analysis date: | October 22, 2023, 01:25:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | F90BA0B3A4B6249ECBB44CAAAA7AC9DC |
| SHA1: | 8E32AF6251408B9F1BA281007F009F0DA7364C2F |
| SHA256: | B149843765CC46B7AE72F3E9865DD7493FF5736766BB7C7924964CAD694F3ACA |
| SSDEEP: | 196608:LCyzNzVbWdIEl0Vr2sDbDNPK9t/AOSU+HzpoqWaB/Vig9yuIceLKiQQu8gT:LCyzNzvEl0V6sL3JTSE6g9yuIce8T |
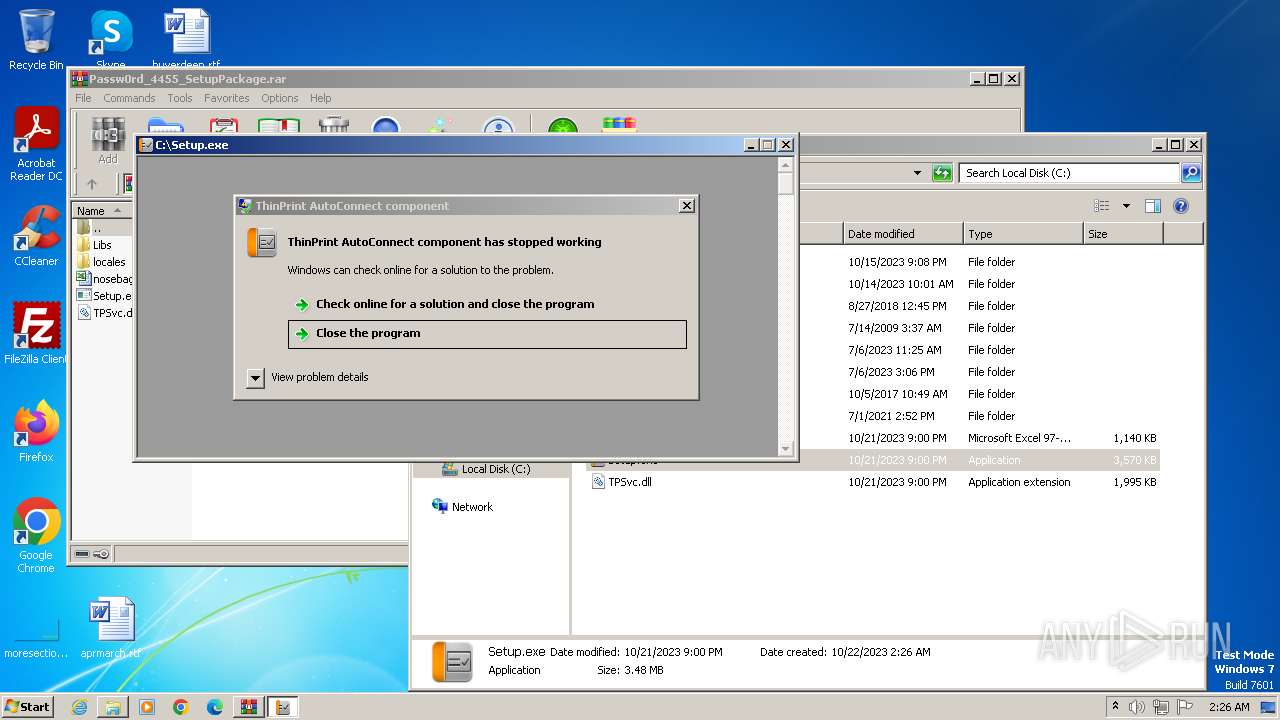
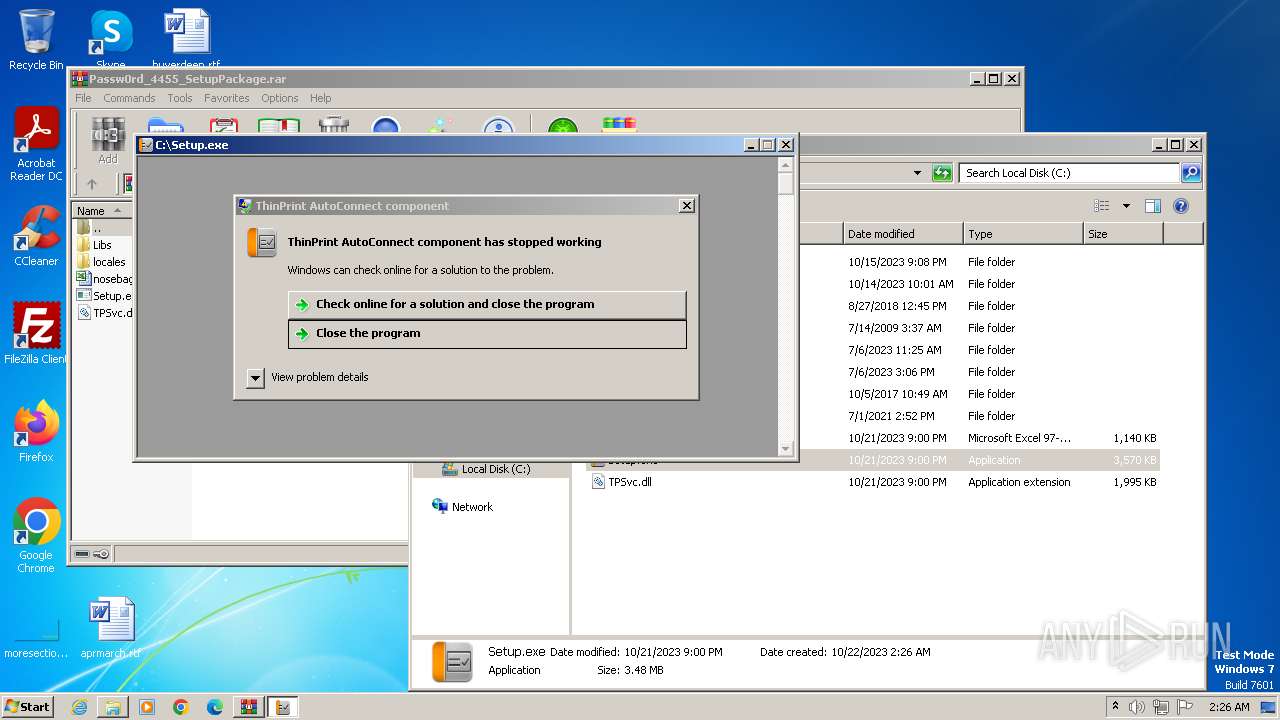
MALICIOUS
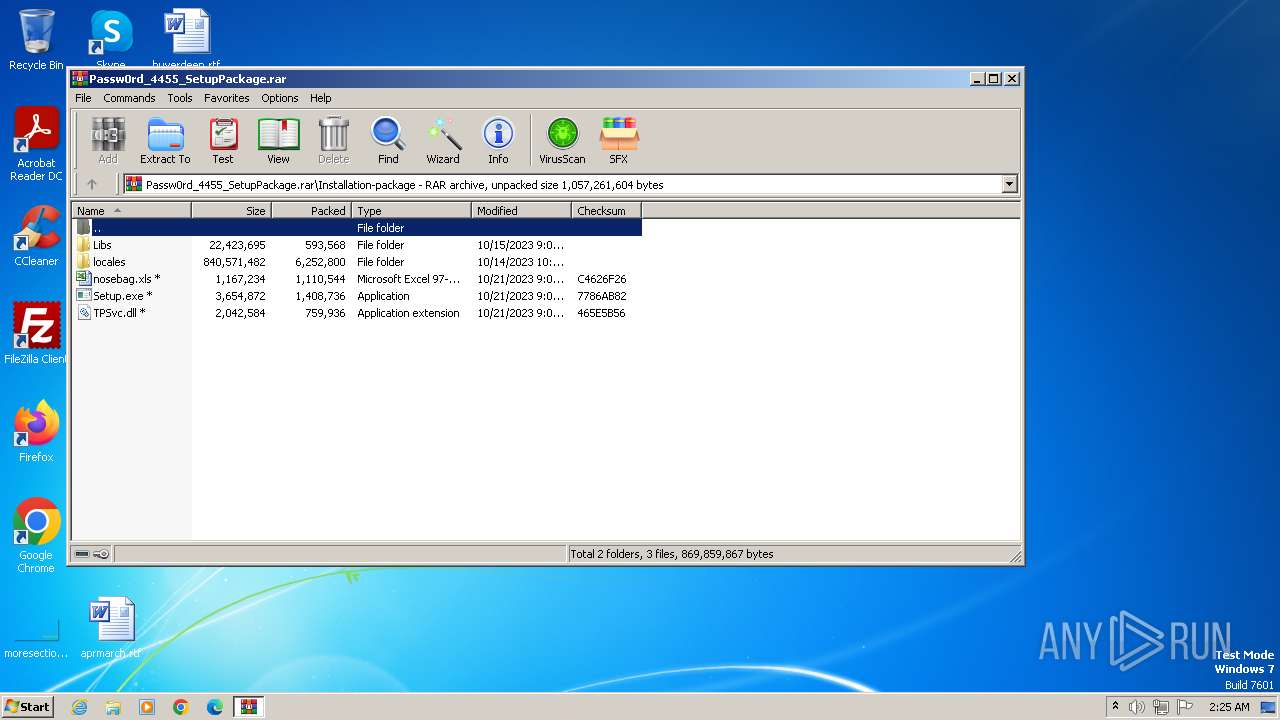
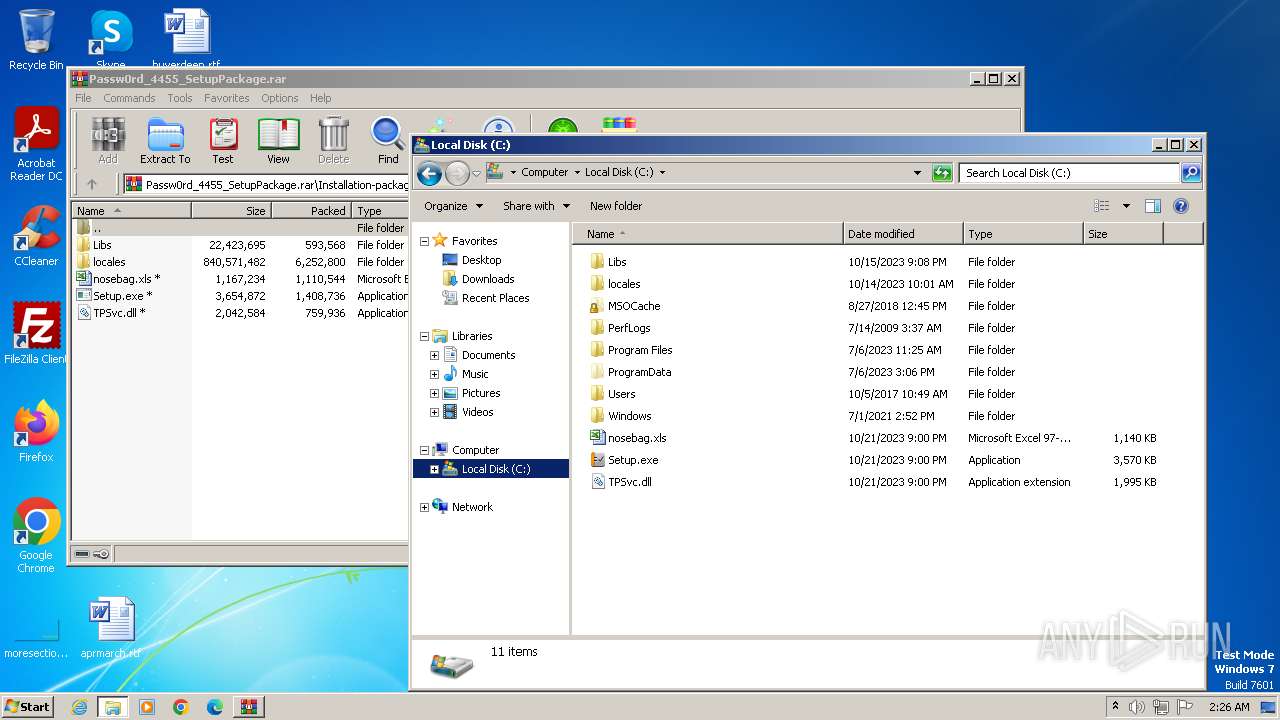
Application was dropped or rewritten from another process
- Setup.exe (PID: 2480)
Loads dropped or rewritten executable
- Setup.exe (PID: 2480)
Drops the executable file immediately after the start
- Setup.exe (PID: 2480)
HIJACKLOADER has been detected (YARA)
- Setup.exe (PID: 2480)
SUSPICIOUS
Application launched itself
- WinRAR.exe (PID: 1824)
INFO
Checks supported languages
- Setup.exe (PID: 2480)
Reads the computer name
- Setup.exe (PID: 2480)
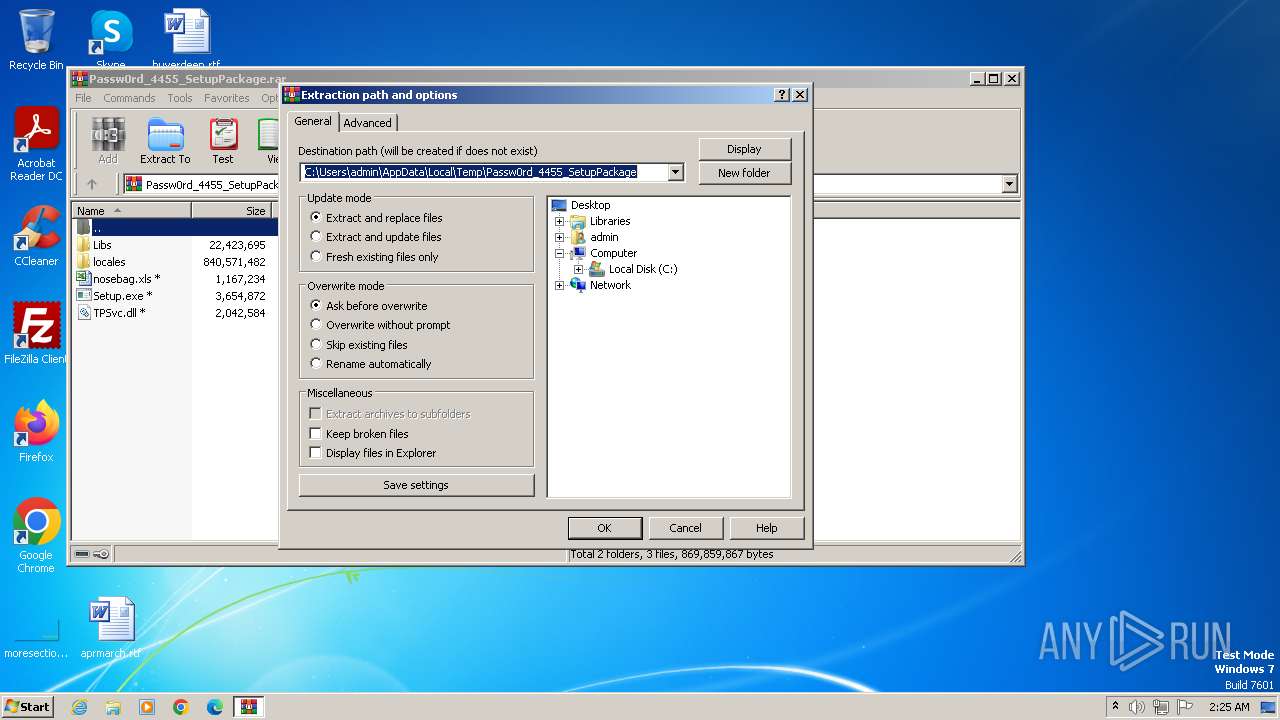
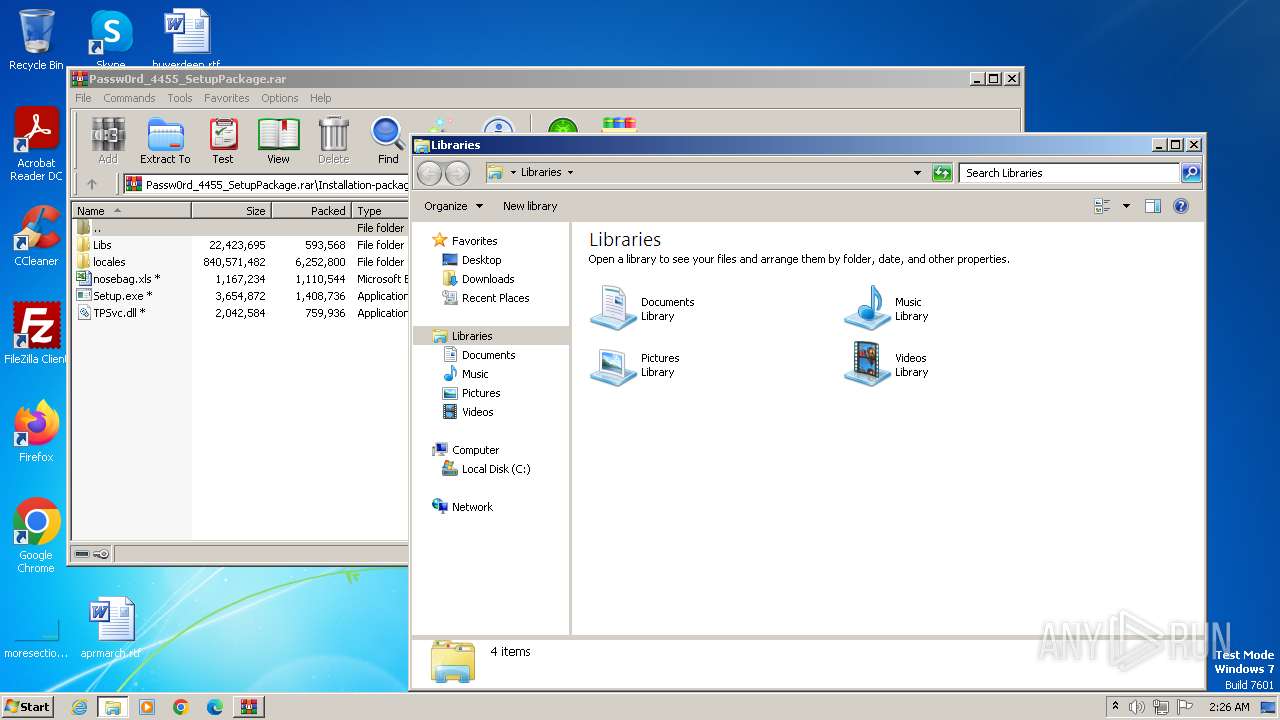
Manual execution by a user
- explorer.exe (PID: 1588)
- Setup.exe (PID: 2480)
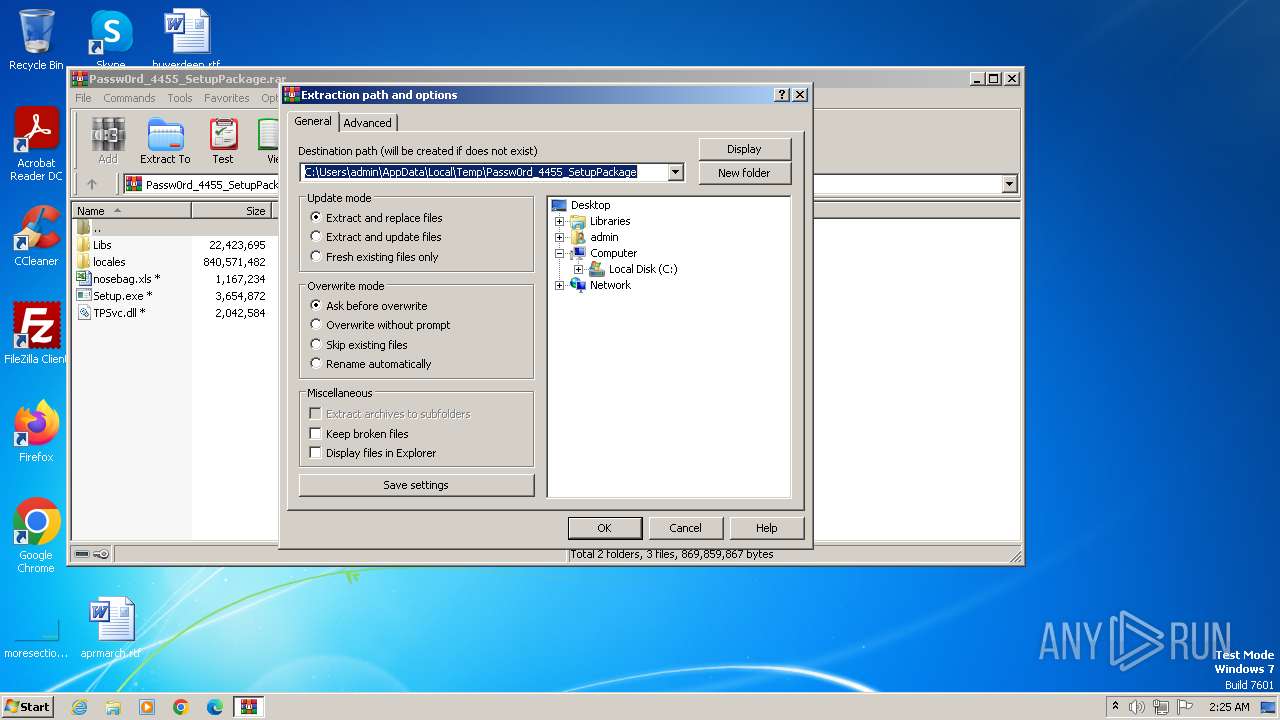
Creates files or folders in the user directory
- Setup.exe (PID: 2480)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
48
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
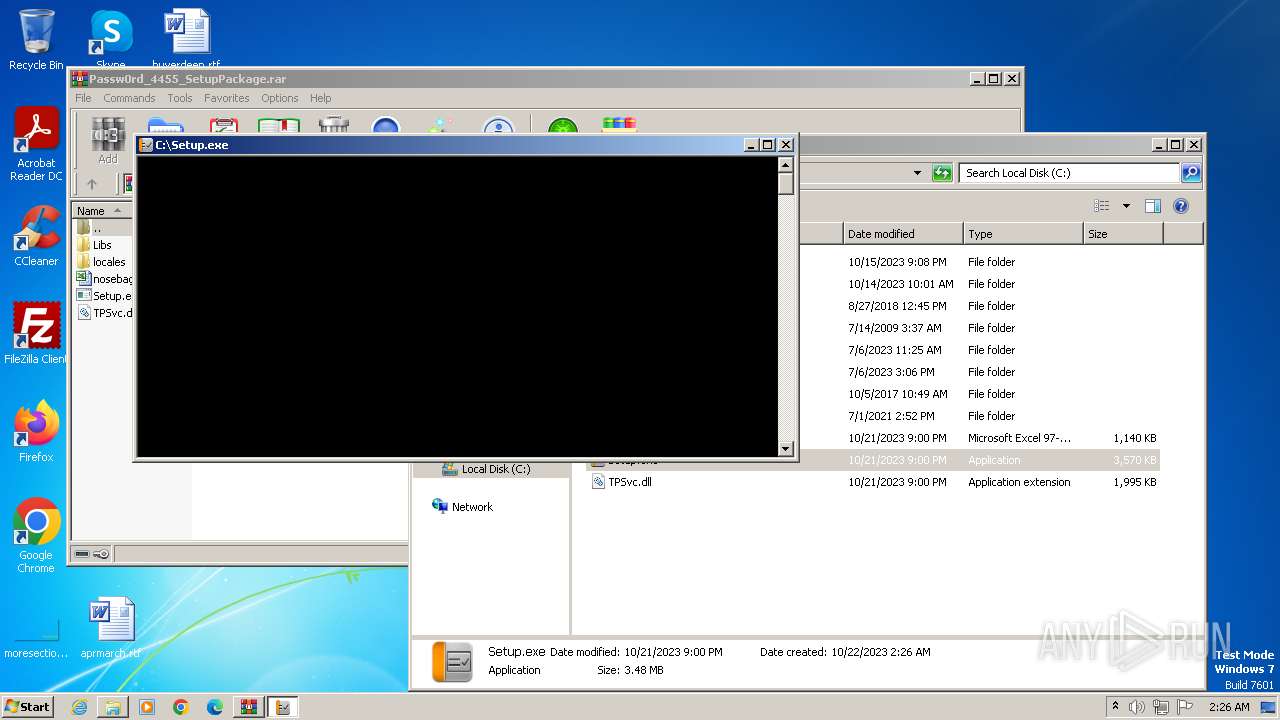
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Program Files\WinRAR\WinRAR.exe" -elevate1824 | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: WinRAR archiver Exit code: 10 Version: 5.91.0 Modules
| |||||||||||||||
| 1588 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1824 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Passw0rd_4455_SetupPackage.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2480 | "C:\Setup.exe" | C:\Setup.exe | explorer.exe | ||||||||||||
User: admin Company: ThinPrint GmbH Integrity Level: MEDIUM Description: ThinPrint AutoConnect component Exit code: 0 Version: 10,2,909,1 Modules
| |||||||||||||||
| 3640 | "C:\Program Files\WinRAR\WinRAR.exe" -elevate1824 | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
1 629
Read events
1 587
Write events
42
Delete events
0
Modification events
| (PID) Process: | (1824) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (1824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (1824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
14
Suspicious files
55
Text files
181
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3640 | WinRAR.exe | C:\Libs\opengl.sys | — | |
MD5:— | SHA256:— | |||
| 3640 | WinRAR.exe | C:\locales\af.pak | binary | |
MD5:C9312FF081E600E5FB4483B46DDD7C23 | SHA256:B1987CDCBB8D76598422AA1739A246ED6690DC1B211F950FCBF2F040491ED7A8 | |||
| 3640 | WinRAR.exe | C:\Libs\license | text | |
MD5:E6A600FD5E1D9CBDE2D983680233AD02 | SHA256:DA7EABB7BAFDF7D3AE5E9F223AA5BDC1EECE45AC569DC21B3B037520B4464768 | |||
| 3640 | WinRAR.exe | C:\Libs\NB_Support.dll | executable | |
MD5:8384F3BB0E807B2CCCD6B443E192B242 | SHA256:2720F4C9EE1331D35962F5BC35D589DBC3FAC1A8EB5A782589FC224DE34567F7 | |||
| 3640 | WinRAR.exe | C:\Libs\libEGL.dll | executable | |
MD5:3ABAA006E1842B5A3CBED2A41476CAE8 | SHA256:A96CDB651C862120489B30B40A716C3F20B772AC4BA8FC70AACCBB1A568005F2 | |||
| 3640 | WinRAR.exe | C:\locales\bg.pak | binary | |
MD5:96372403A9DED96F3A699262029A4580 | SHA256:6C10B64D31E0DC2C4BEFC6703AC17343CA473B4350CFB3C6E01833F505B69590 | |||
| 3640 | WinRAR.exe | C:\Libs\NahimicAPI.dll | executable | |
MD5:905E12FA14ADBD6EEE33E1EF9FBE5652 | SHA256:7434E6E74C537E097B93BC5291BDF89905FED240ACBE6ECF969F15E7C8E112CE | |||
| 3640 | WinRAR.exe | C:\locales\ca.pak | binary | |
MD5:DE21C7D001B771D4D59E2ACFDD67DD44 | SHA256:78BBEE9BF6C95D239418037FD4660D081EBC0F369E727E613B6B652E380E6DD0 | |||
| 3640 | WinRAR.exe | C:\Libs\libgcc_s_dw2-1.dll | executable | |
MD5:49E51045F2951FD248318AC9F1CCB18E | SHA256:73B563935D96D328D5E13D05DDC35F24B69237E4C4B7B183EE66AEEB3CCD9C16 | |||
| 3640 | WinRAR.exe | C:\locales\de.pak | binary | |
MD5:CFC9D90273C31CCF66D81739AA76306A | SHA256:8BD127D689BE65E45BB8D2A2FF66698200DA97835809C6B56EC9E2929B70618A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2656 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |