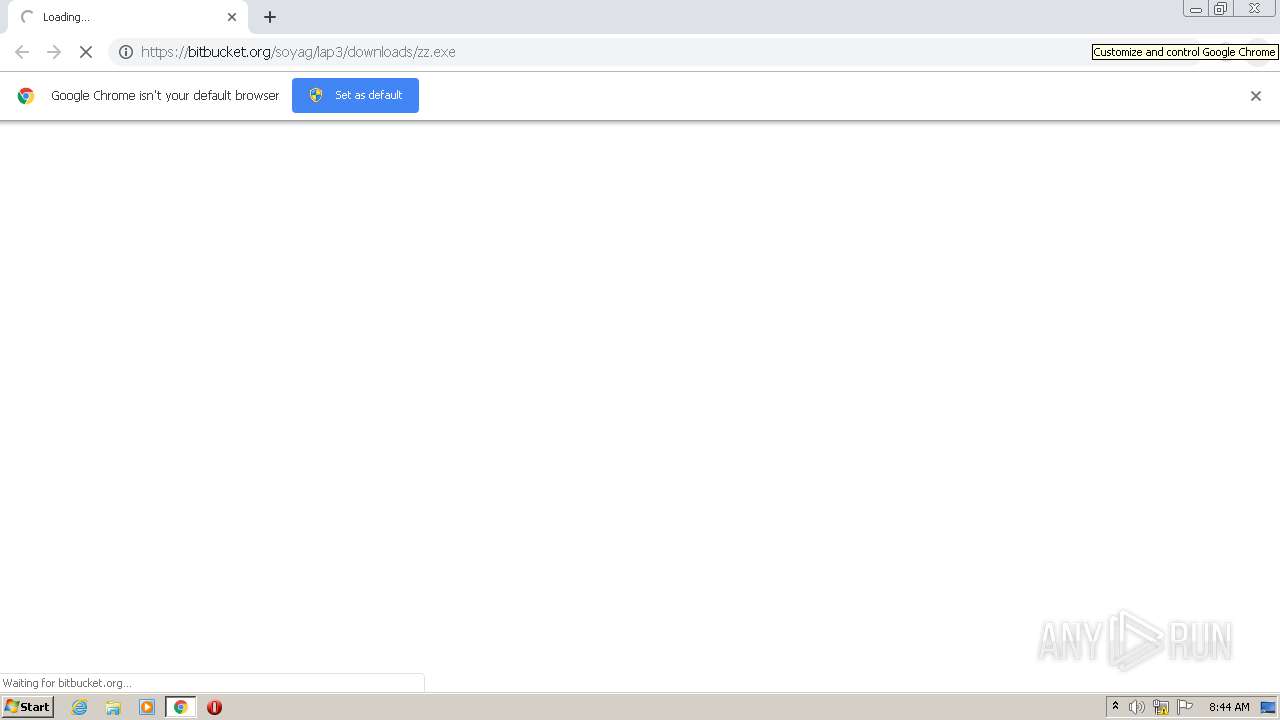
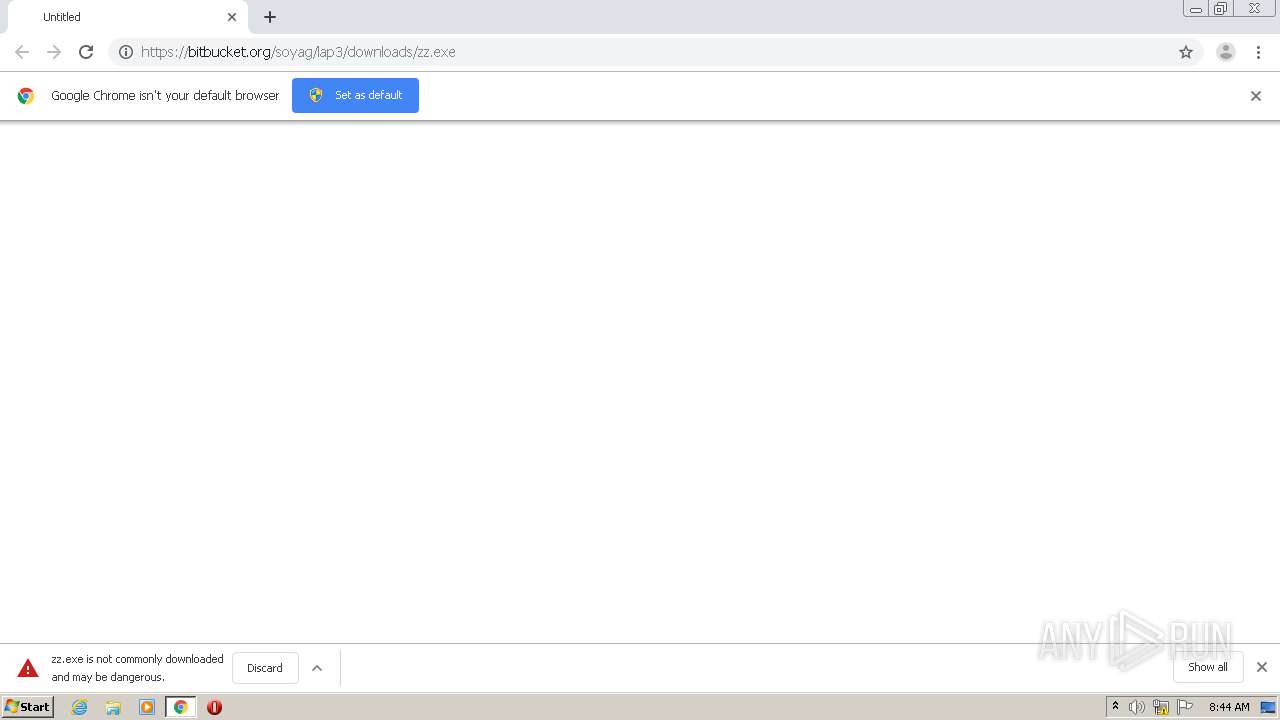
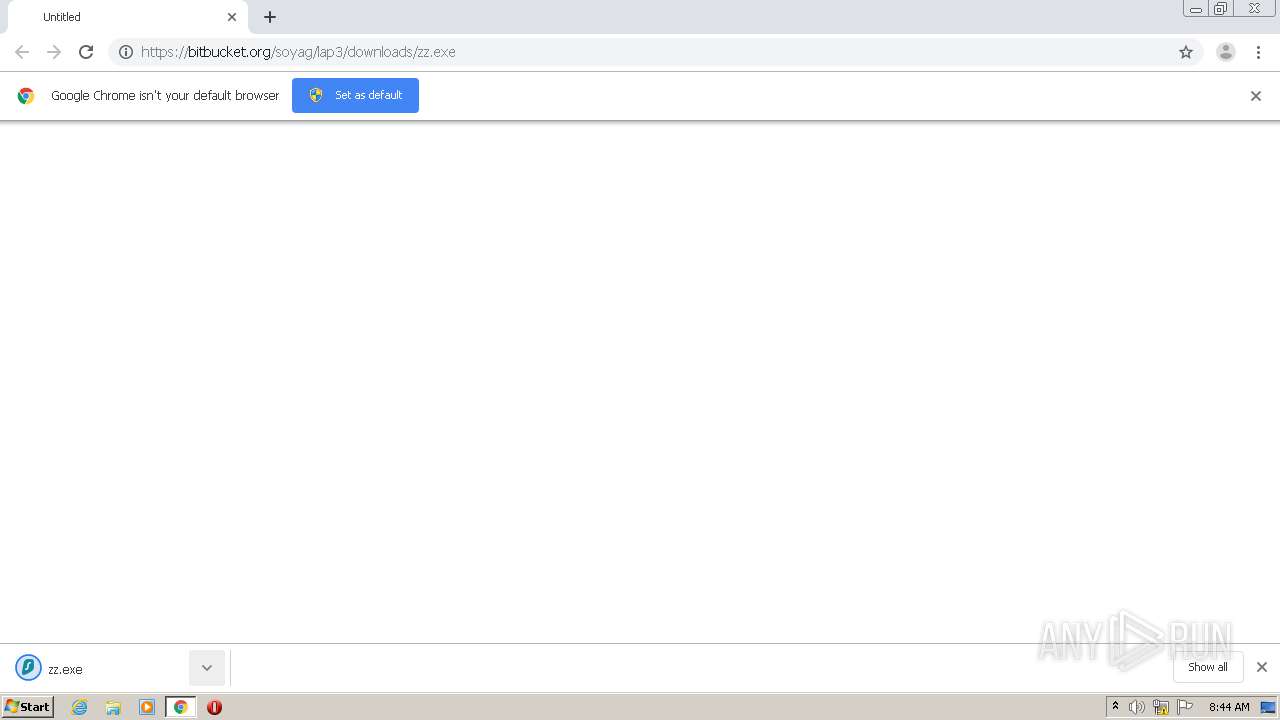
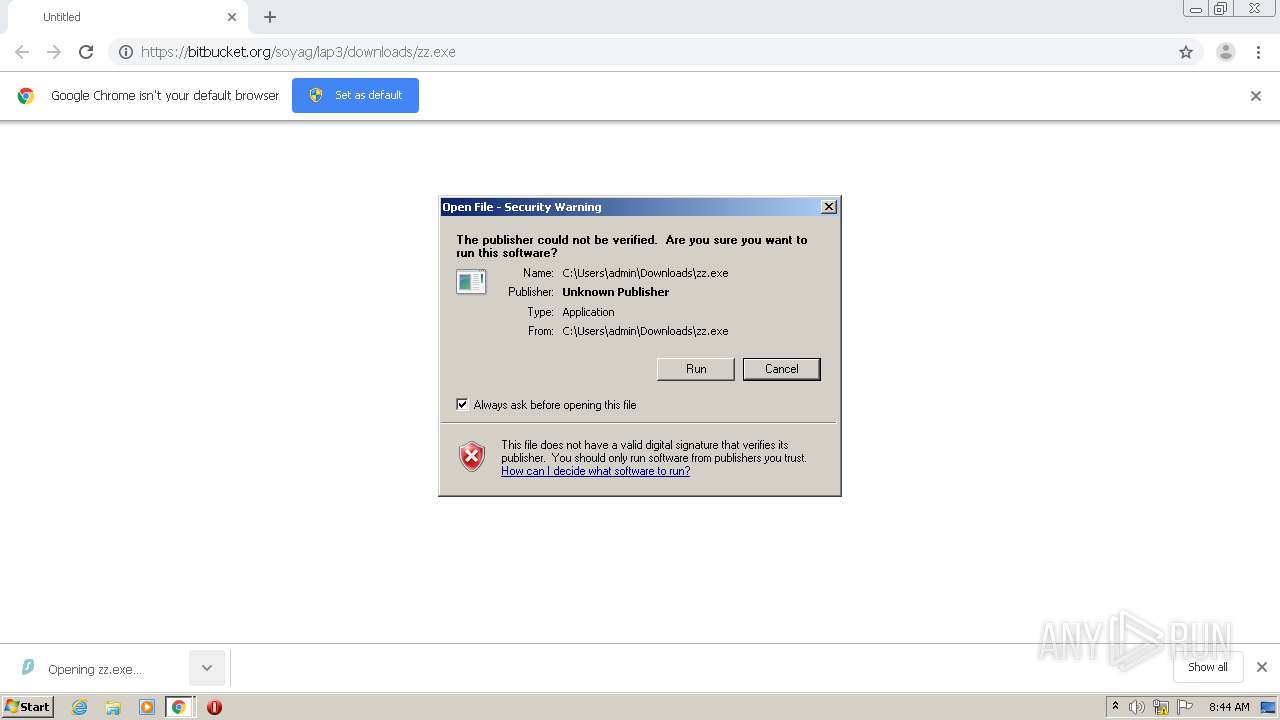
| URL: | https://bitbucket.org/soyag/lap3/downloads/zz.exe |
| Full analysis: | https://app.any.run/tasks/a559e0fc-f1cf-40f9-b29e-3bb1c5b5f610 |
| Verdict: | Malicious activity |
| Threats: | Pony is a malware with two main functions — stealing information and dropping other viruses with different tasks on infected machines. It has been around since 2011, and it still actively attacks users in Europe and America. |
| Analysis date: | October 13, 2020, 07:43:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8B4F1EDB7EDF86A709C33CD9B28805A8 |
| SHA1: | 317D222ECEE1B5D3A5BE9F2A22FD1CC46D540A53 |
| SHA256: | B12AE18D8D124BE45D7BB380B20DA1562C07E0A0F2FFBF437D03A53EF83DBB36 |
| SSDEEP: | 3:N8J+RoCS1K0A:2J+p5 |
MALICIOUS
Application was dropped or rewritten from another process
- zz.exe (PID: 3712)
Detected Pony/Fareit Trojan
- mscorsvw.exe (PID: 2844)
PONY was detected
- mscorsvw.exe (PID: 2844)
Connects to CnC server
- mscorsvw.exe (PID: 2844)
Actions looks like stealing of personal data
- mscorsvw.exe (PID: 2844)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2136)
- chrome.exe (PID: 2052)
Cleans NTFS data-stream (Zone Identifier)
- zz.exe (PID: 3712)
Starts CMD.EXE for commands execution
- mscorsvw.exe (PID: 2844)
INFO
Application launched itself
- chrome.exe (PID: 2136)
Reads the hosts file
- chrome.exe (PID: 2136)
- chrome.exe (PID: 2052)
Reads Internet Cache Settings
- chrome.exe (PID: 2136)
Manual execution by user
- WINWORD.EXE (PID: 2572)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2572)
Creates files in the user directory
- WINWORD.EXE (PID: 2572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
13
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,6326750272194098024,10623849703586548527,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5047552602867303248 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2220 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,6326750272194098024,10623849703586548527,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7033253448034735517 --mojo-platform-channel-handle=3820 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,6326750272194098024,10623849703586548527,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=14186958405871837801 --mojo-platform-channel-handle=1592 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://bitbucket.org/soyag/lap3/downloads/zz.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,6326750272194098024,10623849703586548527,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=726914407250041228 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2480 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2572 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\workpeter.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6c57a9d0,0x6c57a9e0,0x6c57a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2844 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | zz.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 3252 | cmd /c ""C:\Users\admin\AppData\Local\Temp\2989843.bat" "C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe" " | C:\Windows\system32\cmd.exe | — | mscorsvw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,6326750272194098024,10623849703586548527,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3533941930533339917 --mojo-platform-channel-handle=1008 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 037
Read events
1 683
Write events
210
Delete events
144
Modification events
| (PID) Process: | (2136) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2136) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2136) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2136) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2136-13247048650604625 |
Value: 259 | |||
| (PID) Process: | (2136) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2136) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2136) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2136) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2136) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2136-13247048650604625 |
Value: 259 | |||
Executable files
4
Suspicious files
24
Text files
90
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2136 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F855ACB-858.pma | — | |
MD5:— | SHA256:— | |||
| 2136 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2136 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2136 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF2d3f02.TMP | — | |
MD5:— | SHA256:— | |||
| 2136 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7907c1a3-cdbb-4414-bdca-1dd6ca77c327.tmp | — | |
MD5:— | SHA256:— | |||
| 2136 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2136 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2136 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF2d3f9e.TMP | text | |
MD5:— | SHA256:— | |||
| 2136 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF2d3fcd.TMP | text | |
MD5:— | SHA256:— | |||
| 2136 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF2d3fdc.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
18
DNS requests
10
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2844 | mscorsvw.exe | POST | 200 | 5.101.153.102:80 | http://gromitn5.beget.tech/panel/gate.php | RU | binary | 20 b | malicious |
2052 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2052 | chrome.exe | 172.217.16.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2052 | chrome.exe | 18.205.93.0:443 | bitbucket.org | — | US | malicious |
2052 | chrome.exe | 216.58.212.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2052 | chrome.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2052 | chrome.exe | 172.217.22.110:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2052 | chrome.exe | 172.217.18.110:443 | safebrowsing.google.com | Google Inc. | US | whitelisted |
2052 | chrome.exe | 172.217.21.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2052 | chrome.exe | 18.205.93.1:443 | bitbucket.org | — | US | malicious |
2844 | mscorsvw.exe | 5.101.153.102:80 | gromitn5.beget.tech | Beget Ltd | RU | malicious |
2052 | chrome.exe | 172.217.22.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bitbucket.org |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ocsp.digicert.com |
| whitelisted |
bbuseruploads.s3.amazonaws.com |
| shared |
sb-ssl.google.com |
| whitelisted |
safebrowsing.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
gromitn5.beget.tech |
| malicious |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2844 | mscorsvw.exe | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 2 |
2844 | mscorsvw.exe | A Network Trojan was detected | ET TROJAN Trojan Generic - POST To gate.php with no referer |
2844 | mscorsvw.exe | A Network Trojan was detected | LOADER [PTsecurity] Pony |
2844 | mscorsvw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Fareit/Pony CnC Server stdResponse |
4 ETPRO signatures available at the full report