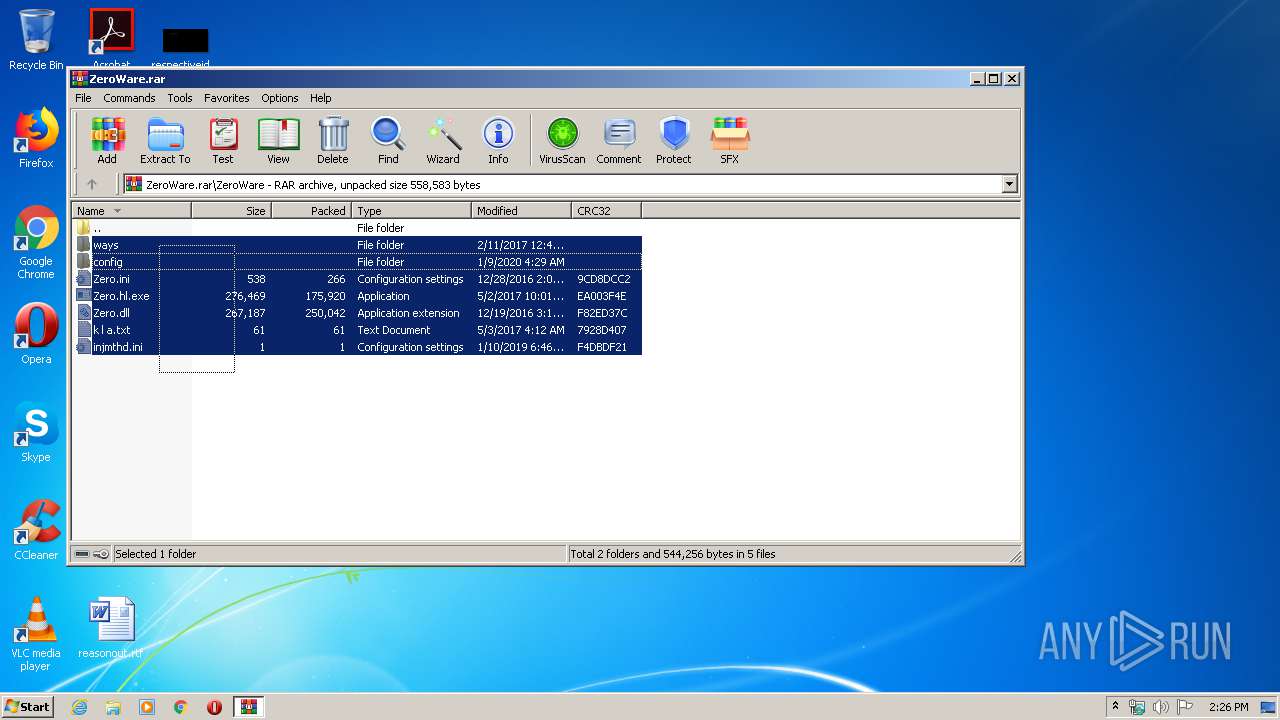
| File name: | ZeroWare.rar |
| Full analysis: | https://app.any.run/tasks/87def657-4f64-4f28-8f88-c2975b7de982 |
| Verdict: | Malicious activity |
| Threats: | Ramnit is a highly modular banking trojan and worm that evolved from a file-infecting virus into a powerful cybercrime tool. It specializes in financial fraud, credential theft, remote access, and malware delivery, being a serious threat to businesses and individuals. First spotted in 2010, Ramnit became popular after the 2014 takedown of the GameOver Zeus botnet, as cybercriminals sought alternatives for banking fraud. |
| Analysis date: | April 21, 2020, 13:25:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
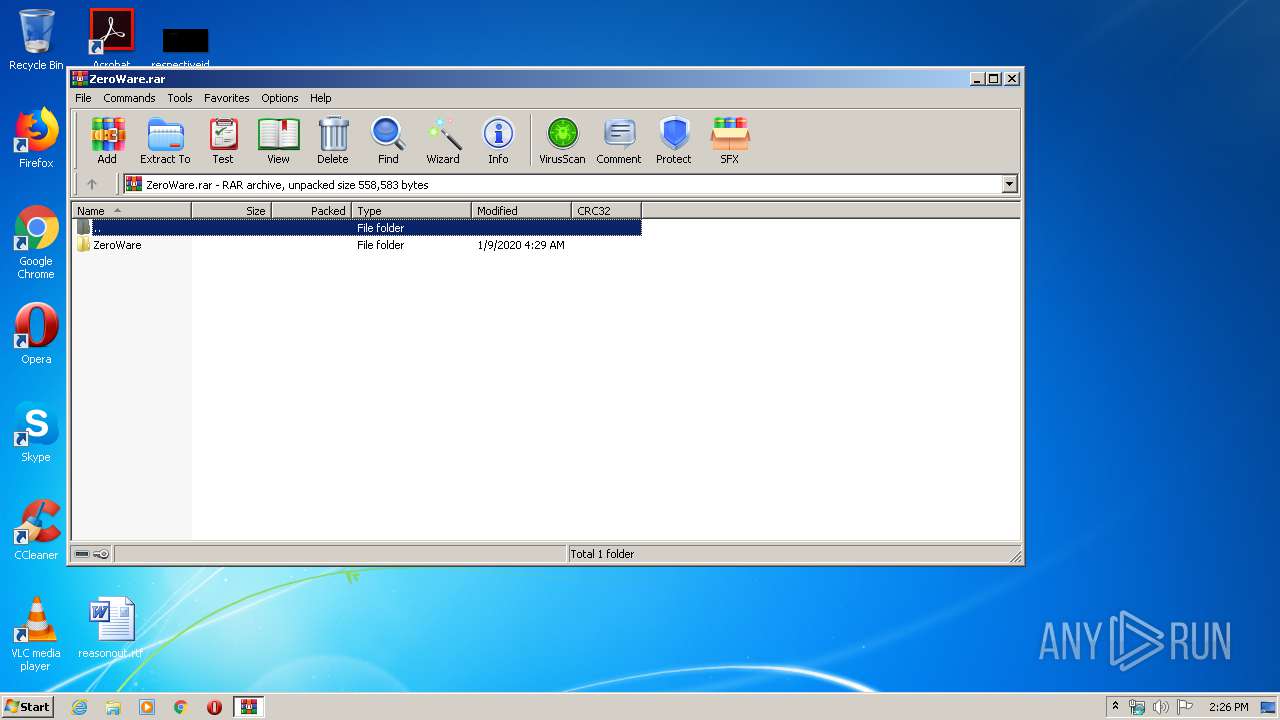
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | EF9BD5E9AB2AC737F7415FA60FC52023 |
| SHA1: | AB3550B6E49FFB8F3E61C086CBD436C56A52FB1C |
| SHA256: | B11811BD7F5029EDF98A1923212AA3160EFDE5FAFFE7DC52AAB33AB4199B1124 |
| SSDEEP: | 12288:QD/q2VxGJ1Y2BzRFixe9SSG3WSdvt86Rd:QzLb2BzziCSSSdvtZj |
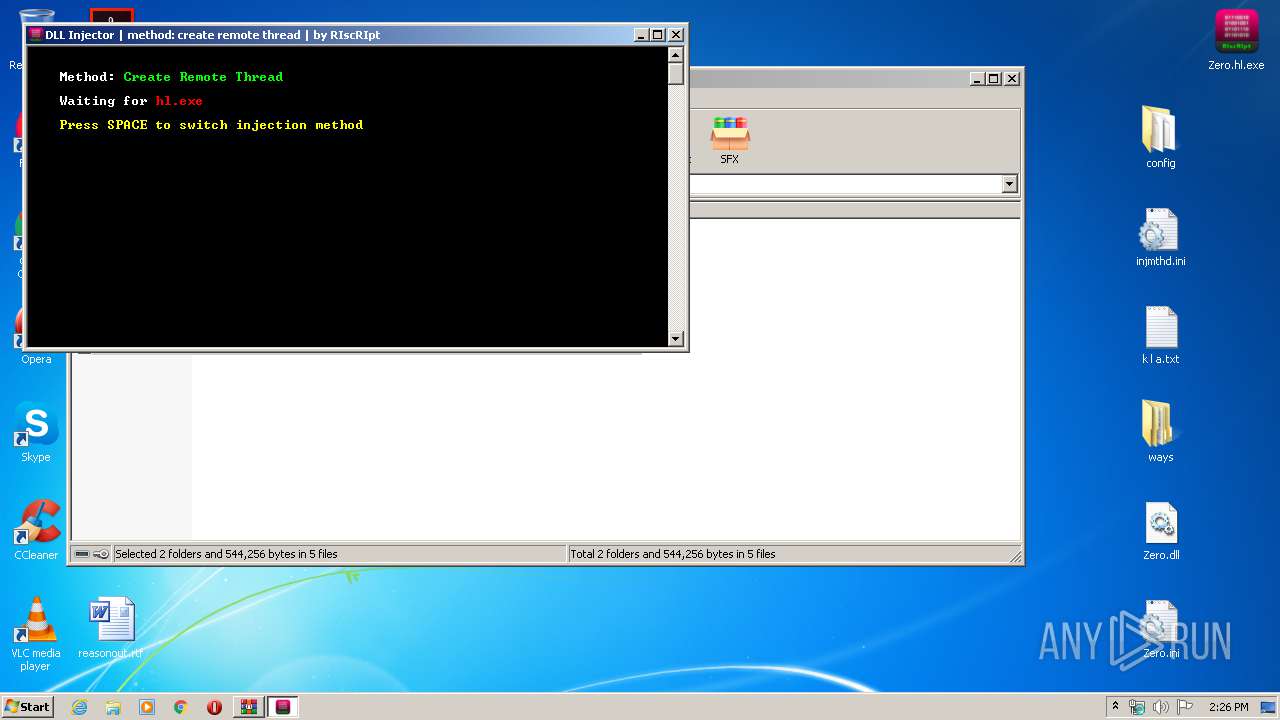
MALICIOUS
Application was dropped or rewritten from another process
- Zero.hl.exe (PID: 440)
- Zero.hlmgr.exe (PID: 2576)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2460)
Writes to a start menu file
- iexplore.exe (PID: 3668)
Connects to CnC server
- iexplore.exe (PID: 3668)
RAMNIT was detected
- iexplore.exe (PID: 3668)
SUSPICIOUS
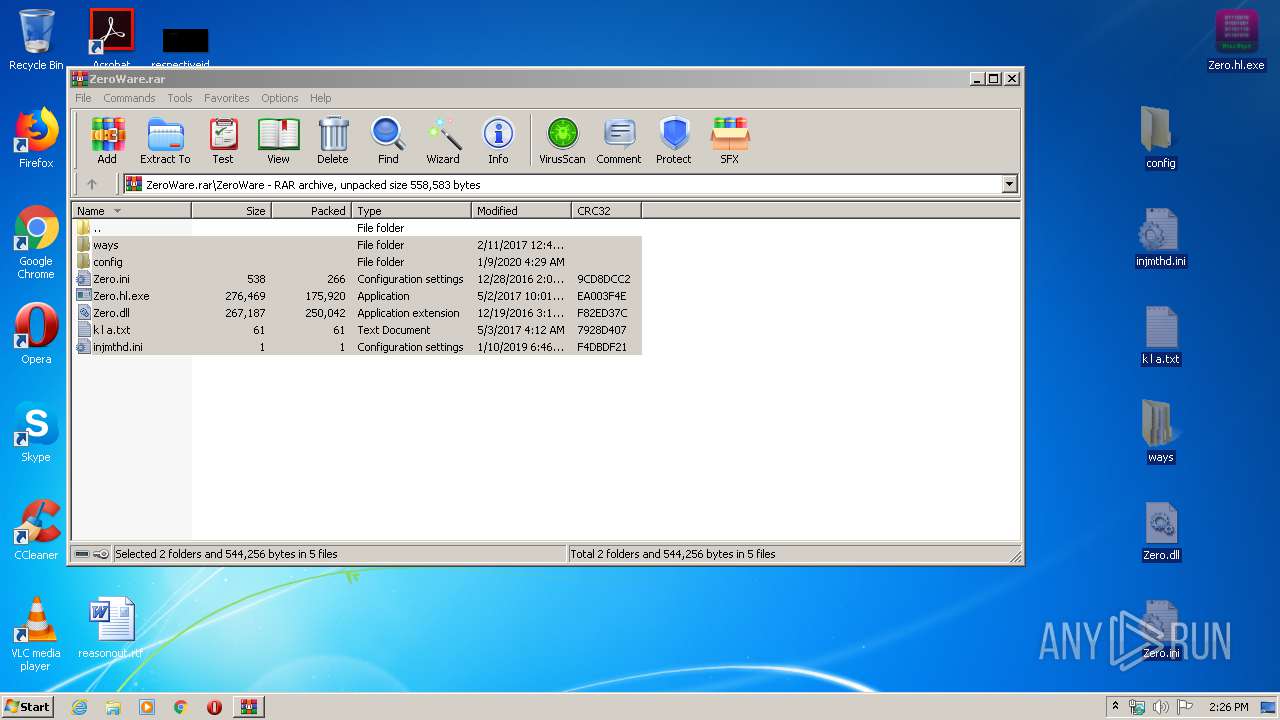
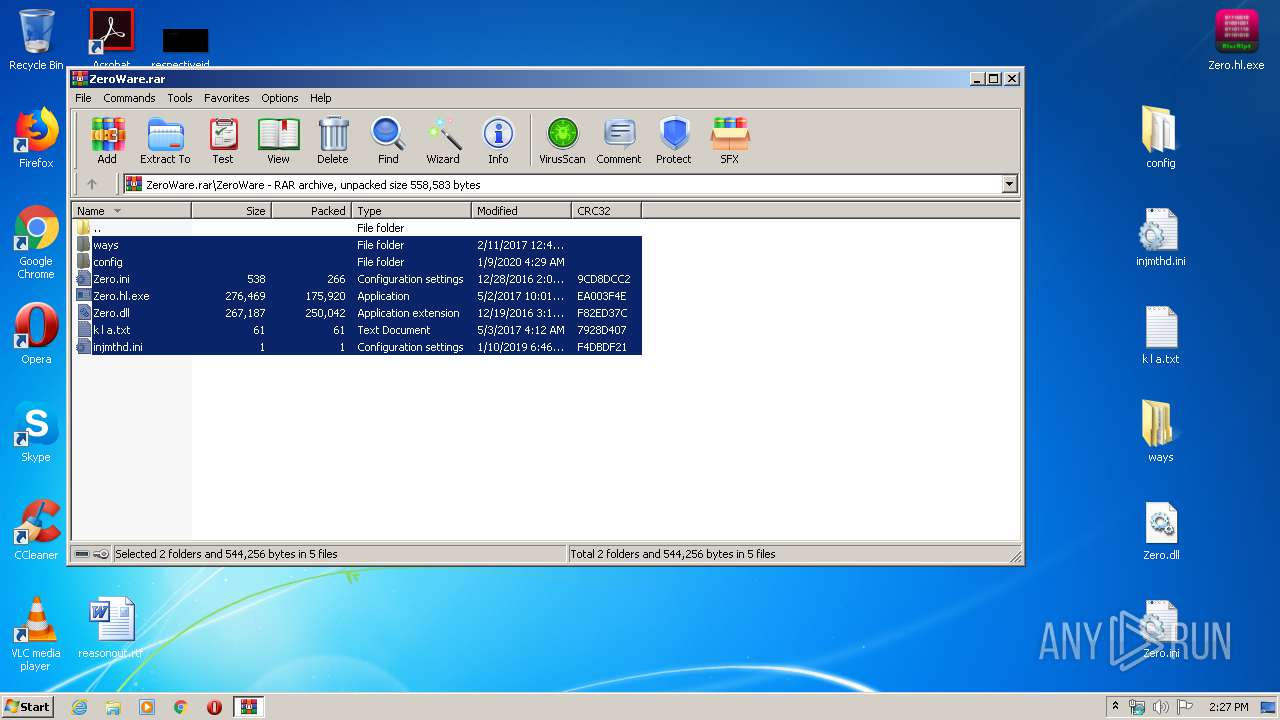
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3312)
- Zero.hl.exe (PID: 440)
Starts Internet Explorer
- Zero.hlmgr.exe (PID: 2576)
Creates files in the program directory
- iexplore.exe (PID: 3668)
INFO
Manual execution by user
- Zero.hl.exe (PID: 440)
Creates files in the user directory
- iexplore.exe (PID: 3668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
41
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | "C:\Users\admin\Desktop\Zero.hl.exe" | C:\Users\admin\Desktop\Zero.hl.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225547 Modules
| |||||||||||||||
| 2460 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2576 | C:\Users\admin\Desktop\Zero.hlmgr.exe | C:\Users\admin\Desktop\Zero.hlmgr.exe | — | Zero.hl.exe | |||||||||||
User: admin Company: Macromedia, Inc. Integrity Level: MEDIUM Description: Macromedia Flash Player 7.0 r14 Exit code: 0 Version: 7,0,14,0 Modules
| |||||||||||||||
| 3312 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\ZeroWare.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3668 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | Zero.hlmgr.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
779
Read events
767
Write events
12
Delete events
0
Modification events
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ZeroWare.rar | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList |
| Operation: | write | Name: | ArcSort |
Value: 32 | |||
| (PID) Process: | (2460) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
3
Suspicious files
2
Text files
66
Unknown types
75
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
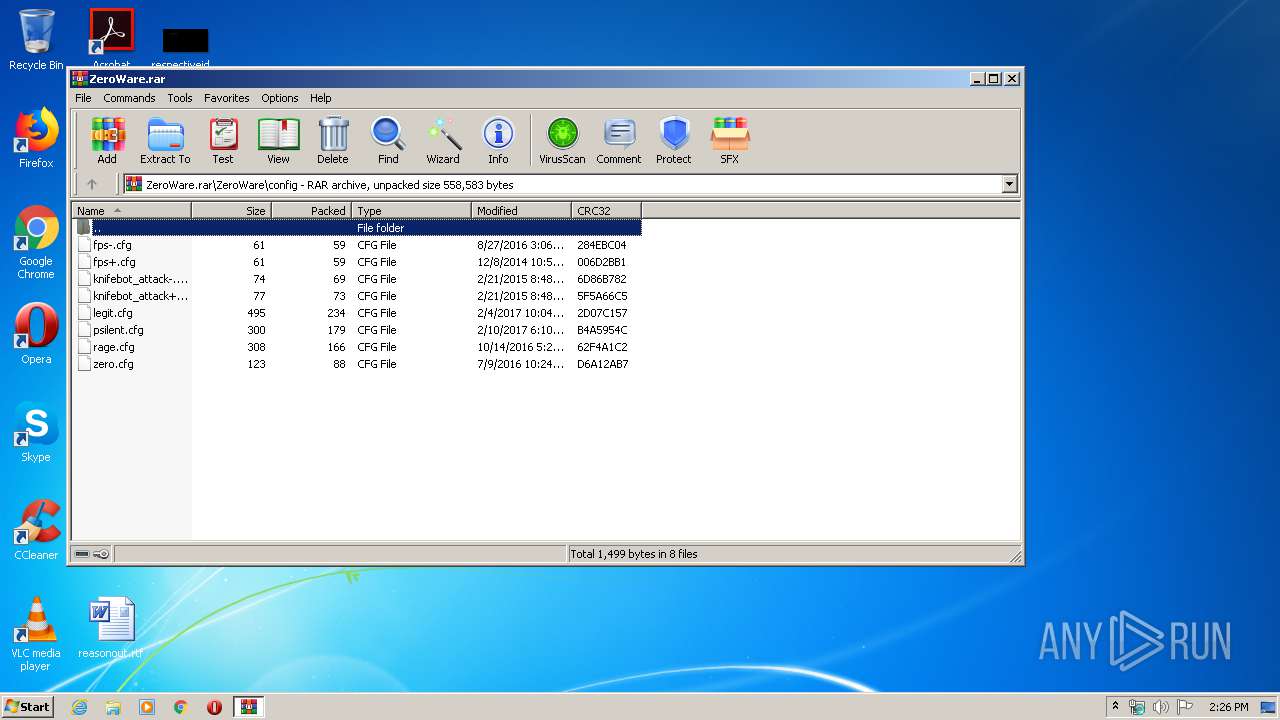
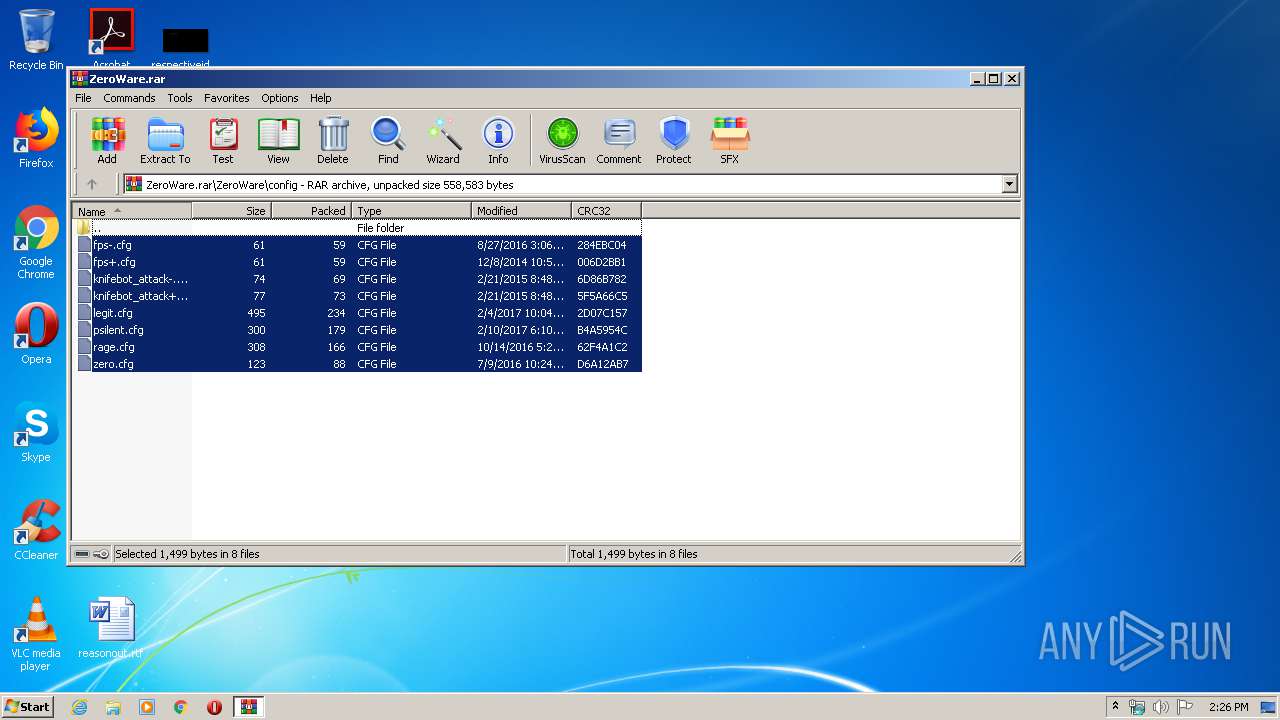
| 3312 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3312.41809\ZeroWare\config\legit.cfg | text | |
MD5:— | SHA256:— | |||
| 3312 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3312.41809\ZeroWare\config\psilent.cfg | text | |
MD5:— | SHA256:— | |||
| 3312 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3312.41809\ZeroWare\k l a.txt | text | |
MD5:— | SHA256:— | |||
| 3312 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3312.41809\ZeroWare\ways\$1000$\ct | text | |
MD5:CAC5E1365FD26391A6CACF4AD8F1723D | SHA256:B1187810AABD39DD2D00460118159A71A290649DAC7873C67AB4570CC217899F | |||
| 3312 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3312.41809\ZeroWare\injmthd.ini | binary | |
MD5:CFCD208495D565EF66E7DFF9F98764DA | SHA256:5FECEB66FFC86F38D952786C6D696C79C2DBC239DD4E91B46729D73A27FB57E9 | |||
| 3312 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3312.41809\ZeroWare\config\knifebot_attack-.cfg | text | |
MD5:F17568A7AEF82BA2289618D6F4BAB88E | SHA256:9E9804433CBFDE7CA8410197255A1E975FD9623D1F668429C67E18B87537330B | |||
| 3312 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3312.41809\ZeroWare\config\fps-.cfg | text | |
MD5:076966AF9A0E5A2F87DA064EC5B78F98 | SHA256:430C2D211A7746ABE65984FC31C2E71499B685FFD1240CDE309E704D5C95F8C3 | |||
| 3312 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3312.41809\ZeroWare\ways\$1000$\t | text | |
MD5:962B77D2EEBC5EBADEA54FFB90AD907D | SHA256:869A634814813A29B82B3D5318C563966878498939B5BCF0139ED33B2A1D7C4B | |||
| 3312 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3312.41809\ZeroWare\config\rage.cfg | text | |
MD5:BDAF02BD5E9E6E5E4F7EF53FCED9650C | SHA256:9012D90E2CCCCDE02D34A503CF99FADA024194C9F6D4D7312DF700CCF59689C5 | |||
| 3312 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3312.41809\ZeroWare\config\zero.cfg | text | |
MD5:73EA1FB2DE2DB4799FF7BA8717B82467 | SHA256:4E8A1BCC754FFE86399EA441496151E48C2D616B0BEB5B796DE146FD2C495529 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
2
Threats
4
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3668 | iexplore.exe | 216.58.210.14:80 | google.com | Google Inc. | US | whitelisted |
3668 | iexplore.exe | 82.112.184.197:443 | poopthree.com | Vysokie tehnologii Limited Liability Company | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| malicious |
poopthree.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3668 | iexplore.exe | A Network Trojan was detected | ET TROJAN Win32/Ramnit Checkin |
3668 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Ramnit Checkin |
3668 | iexplore.exe | A Network Trojan was detected | ET TROJAN Win32/Ramnit Checkin |
3668 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Ramnit Checkin |