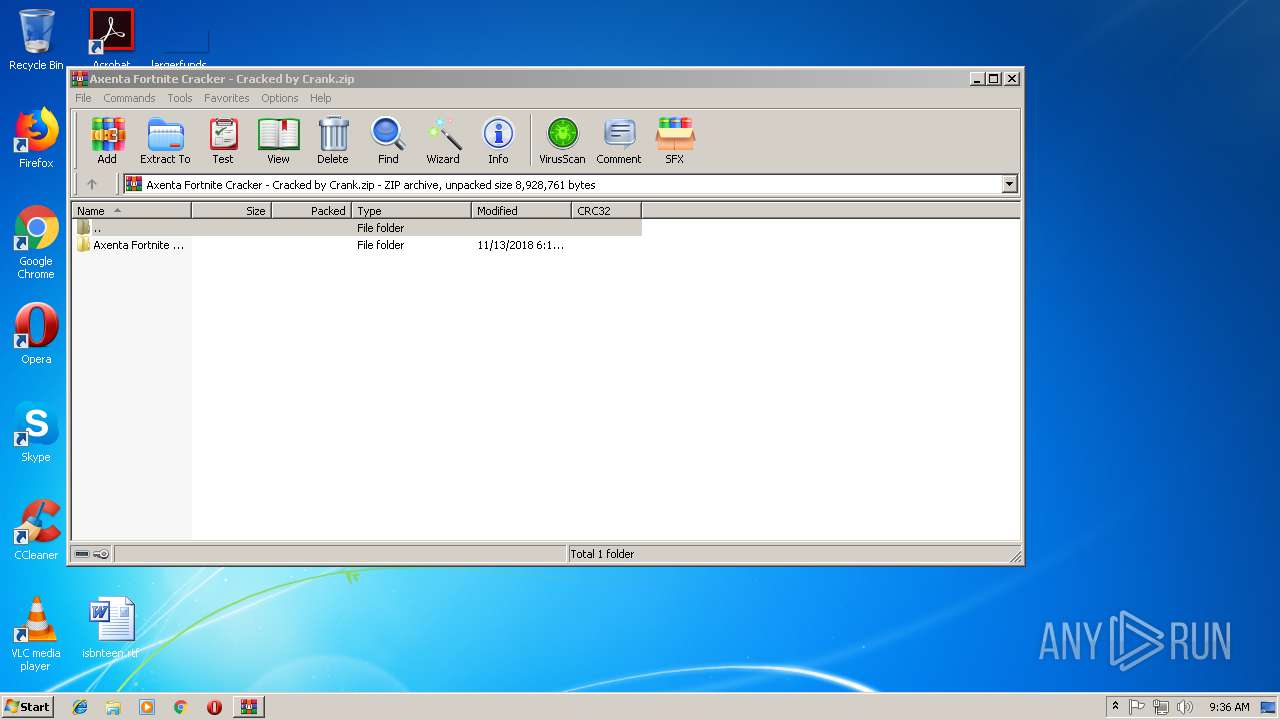
| File name: | Axenta Fortnite Cracker - Cracked by Crank.zip |
| Full analysis: | https://app.any.run/tasks/a1fc849b-fa91-426e-aa19-fb7f30011f18 |
| Verdict: | Malicious activity |
| Threats: | Arkei is a stealer type malware capable of collecting passwords, autosaved forms, cryptocurrency wallet credentials, and files. |
| Analysis date: | November 13, 2018, 09:36:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 9FD80D96BFE42C8B38819B73412EF228 |
| SHA1: | 9E0A17E395EB6E922350A782FC15544B6E22FFE2 |
| SHA256: | B103BBA9D8F10237E28AFA32C68A6B70D64049B8384FDA62D67A49F343BCA181 |
| SSDEEP: | 98304:EIi/0s4RO9CbTE95cyy5At0j6F9L17u4h4NfARzFc1Eal5:c/0ZkC895crAtTPCfNoRzFc1bl5 |
MALICIOUS
ARKEI was detected
- Axenta1.exe (PID: 936)
Stealing of credential data
- Axenta1.exe (PID: 936)
SUSPICIOUS
Loads DLL from Mozilla Firefox
- Axenta1.exe (PID: 936)
Executable content was dropped or overwritten
- Axenta1.exe (PID: 3800)
Application launched itself
- Axenta1.exe (PID: 3800)
Creates files in the user directory
- Axenta1.exe (PID: 936)
Creates files in the program directory
- Axenta1.exe (PID: 936)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:11:12 23:12:10 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Axenta Fortnite Cracker - Cracked by Crank/ |
Total processes
38
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
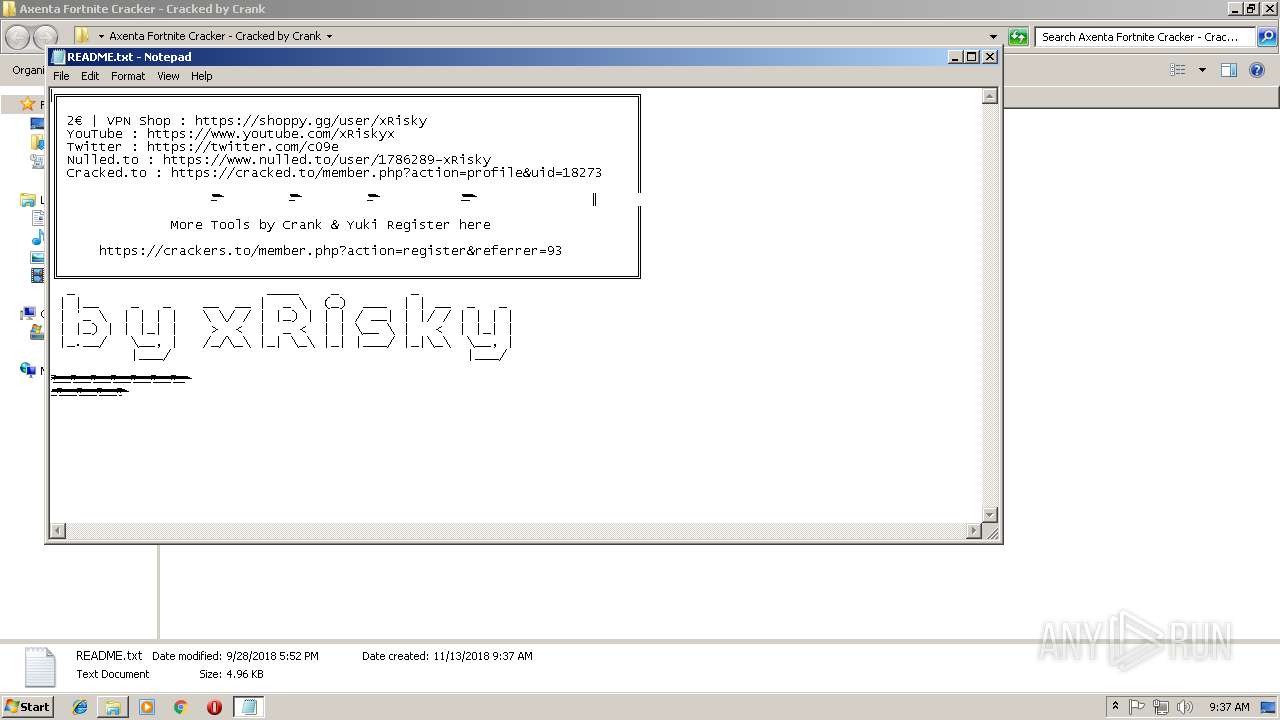
| 272 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Axenta Fortnite Cracker - Cracked by Crank\README.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
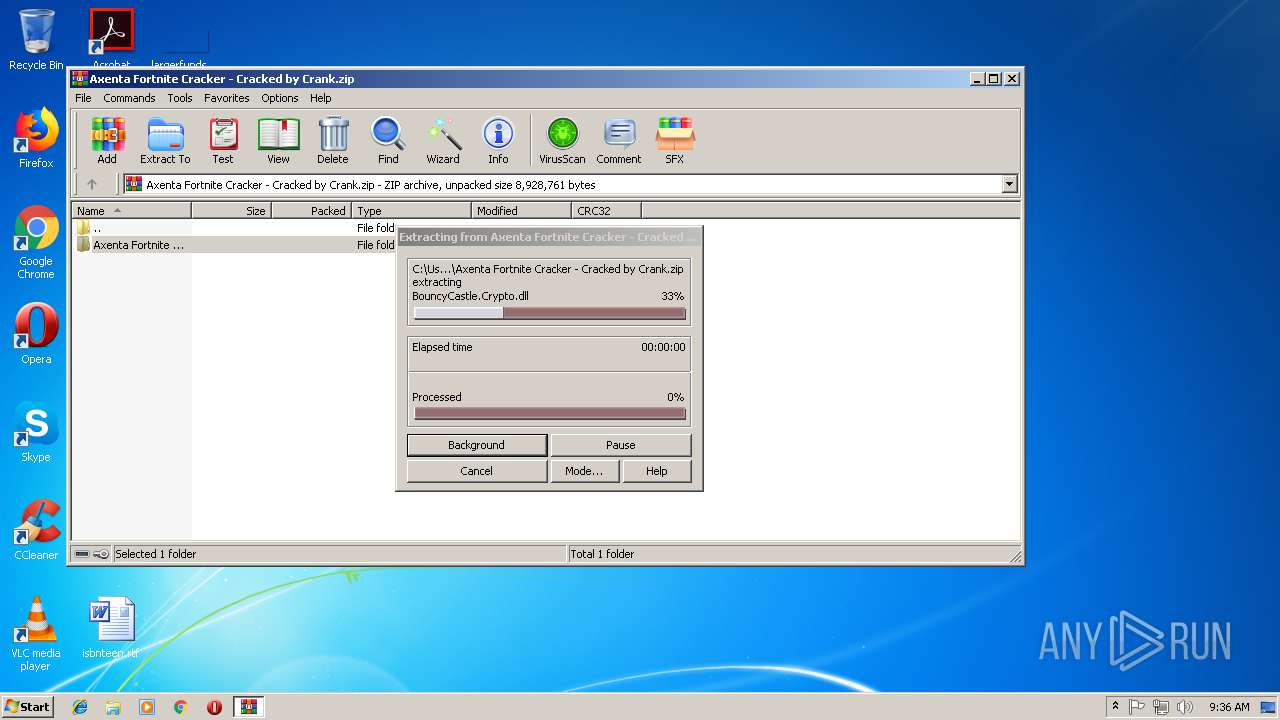
| 700 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Axenta Fortnite Cracker - Cracked by Crank.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
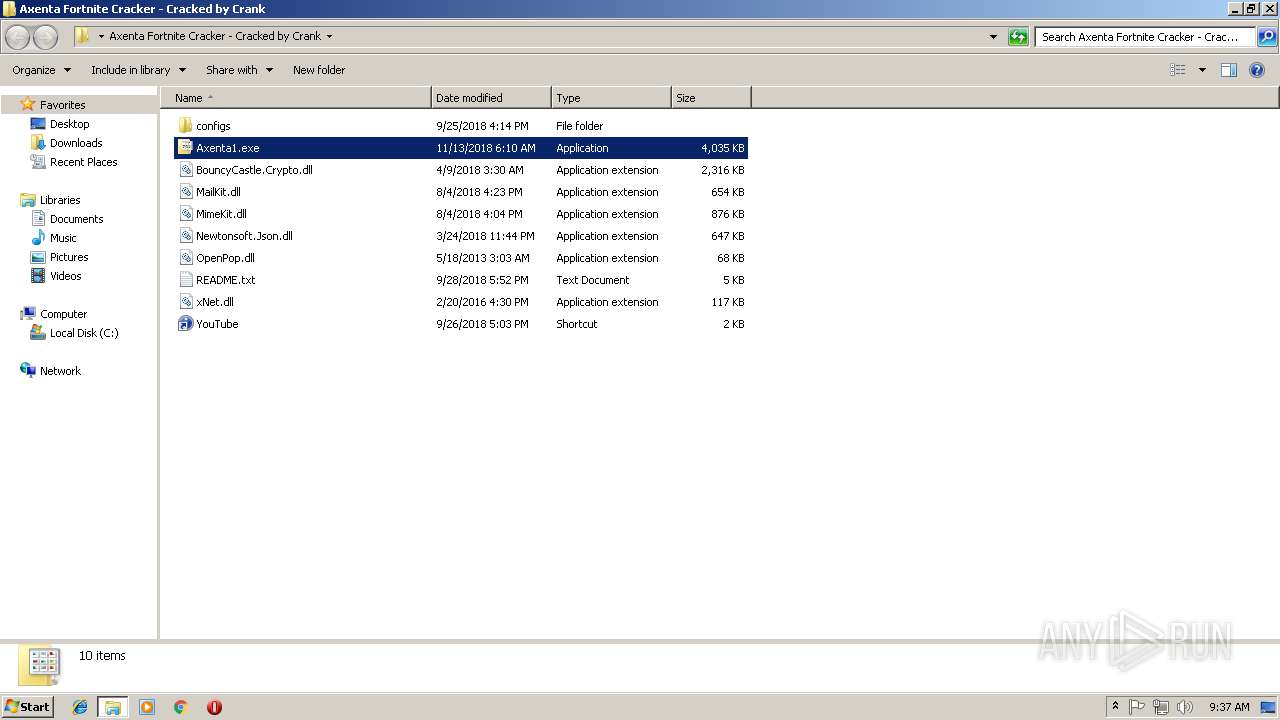
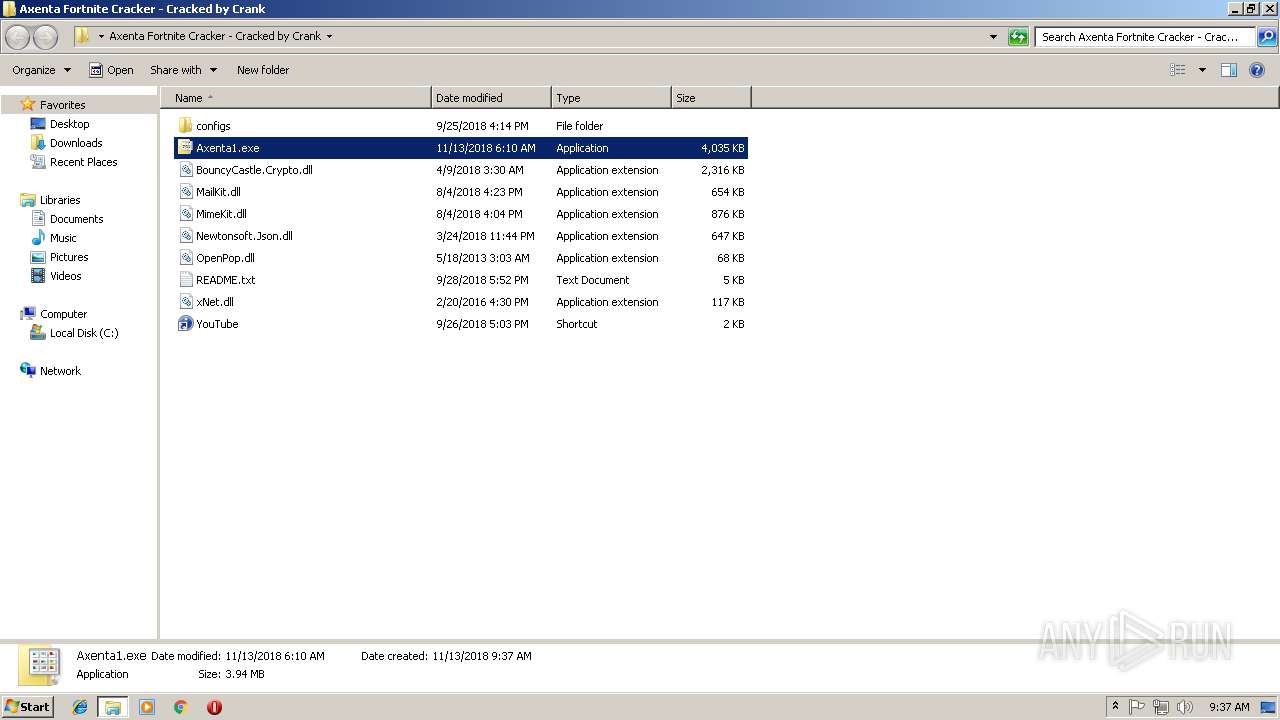
| 936 | "C:\Users\admin\Desktop\Axenta Fortnite Cracker - Cracked by Crank\Axenta1.exe" | C:\Users\admin\Desktop\Axenta Fortnite Cracker - Cracked by Crank\Axenta1.exe | Axenta1.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3800 | "C:\Users\admin\Desktop\Axenta Fortnite Cracker - Cracked by Crank\Axenta1.exe" | C:\Users\admin\Desktop\Axenta Fortnite Cracker - Cracked by Crank\Axenta1.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
825
Read events
780
Write events
45
Delete events
0
Modification events
| (PID) Process: | (700) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (700) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (700) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (700) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Axenta Fortnite Cracker - Cracked by Crank.zip | |||
| (PID) Process: | (700) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (700) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (700) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (700) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (700) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (700) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
1
Suspicious files
1
Text files
11
Unknown types
7
Dropped files
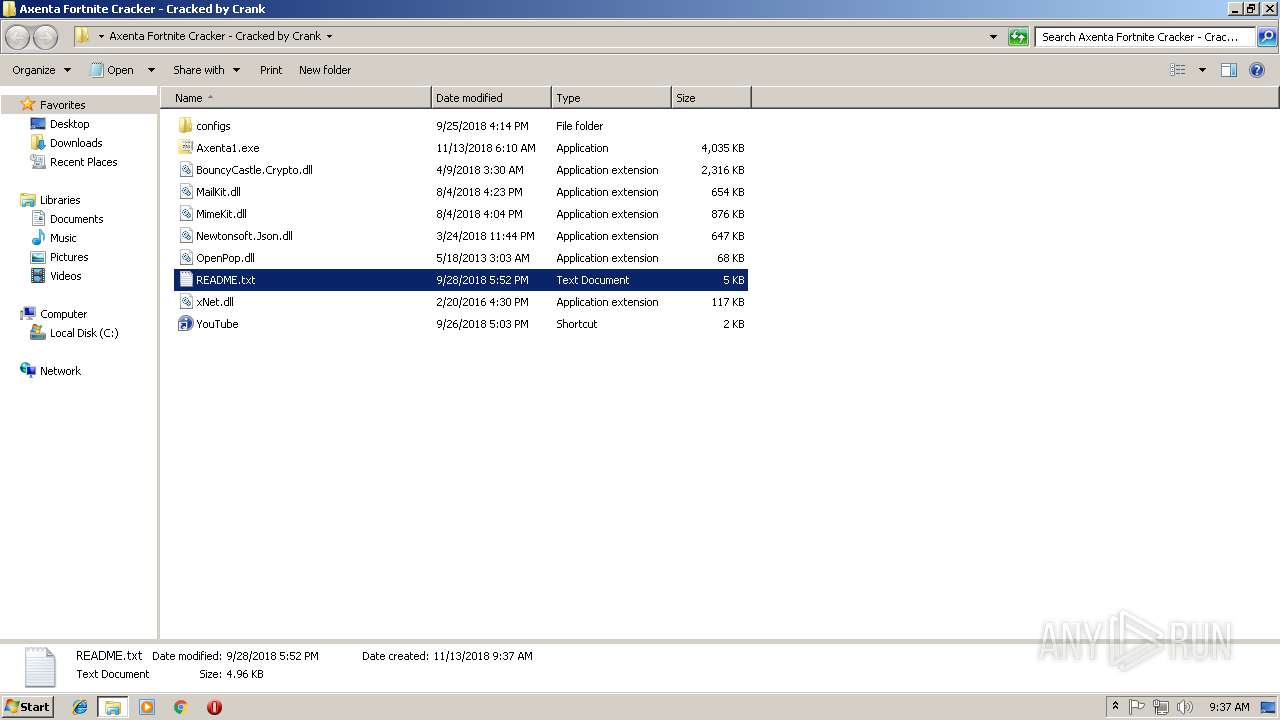
PID | Process | Filename | Type | |
|---|---|---|---|---|
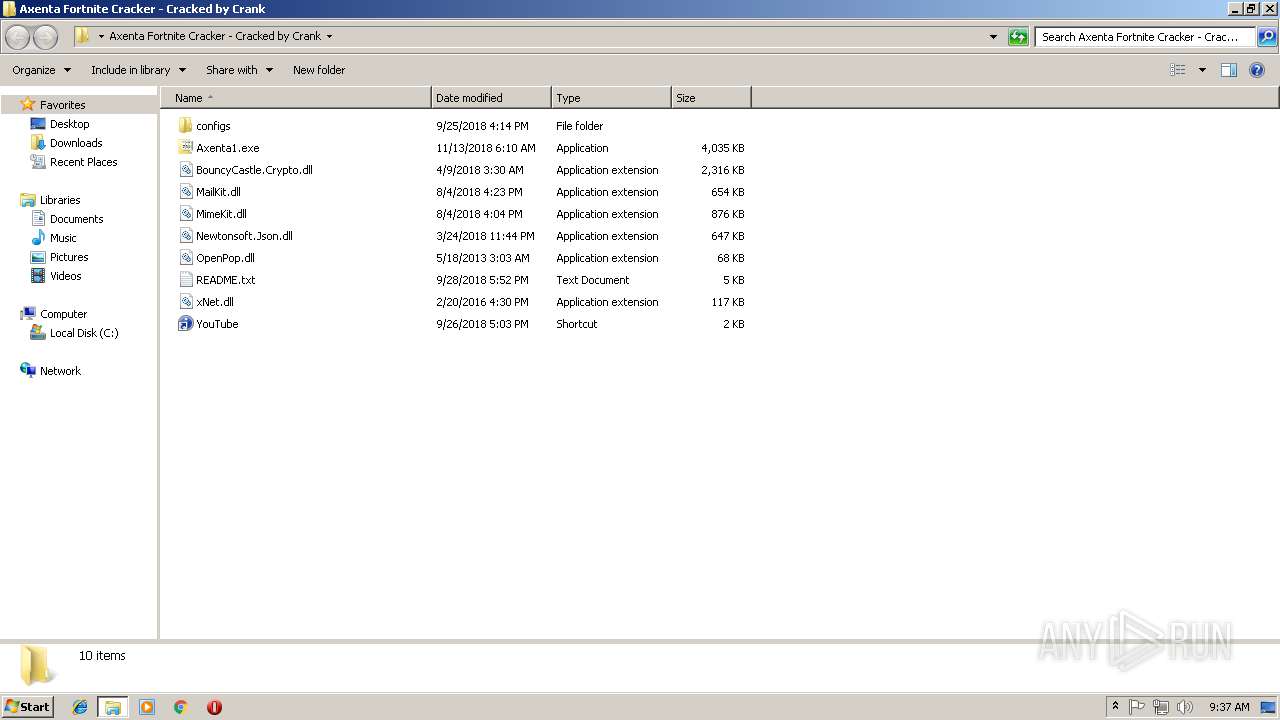
| 700 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa700.31955\Axenta Fortnite Cracker - Cracked by Crank\Axenta1.exe | — | |
MD5:— | SHA256:— | |||
| 700 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa700.31955\Axenta Fortnite Cracker - Cracked by Crank\BouncyCastle.Crypto.dll | — | |
MD5:— | SHA256:— | |||
| 700 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa700.31955\Axenta Fortnite Cracker - Cracked by Crank\configs\ddd.acf | — | |
MD5:— | SHA256:— | |||
| 700 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa700.31955\Axenta Fortnite Cracker - Cracked by Crank\MailKit.dll | — | |
MD5:— | SHA256:— | |||
| 700 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa700.31955\Axenta Fortnite Cracker - Cracked by Crank\MimeKit.dll | — | |
MD5:— | SHA256:— | |||
| 700 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa700.31955\Axenta Fortnite Cracker - Cracked by Crank\Newtonsoft.Json.dll | — | |
MD5:— | SHA256:— | |||
| 700 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa700.31955\Axenta Fortnite Cracker - Cracked by Crank\OpenPop.dll | — | |
MD5:— | SHA256:— | |||
| 700 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa700.31955\Axenta Fortnite Cracker - Cracked by Crank\README.txt | — | |
MD5:— | SHA256:— | |||
| 700 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa700.31955\Axenta Fortnite Cracker - Cracked by Crank\xNet.dll | — | |
MD5:— | SHA256:— | |||
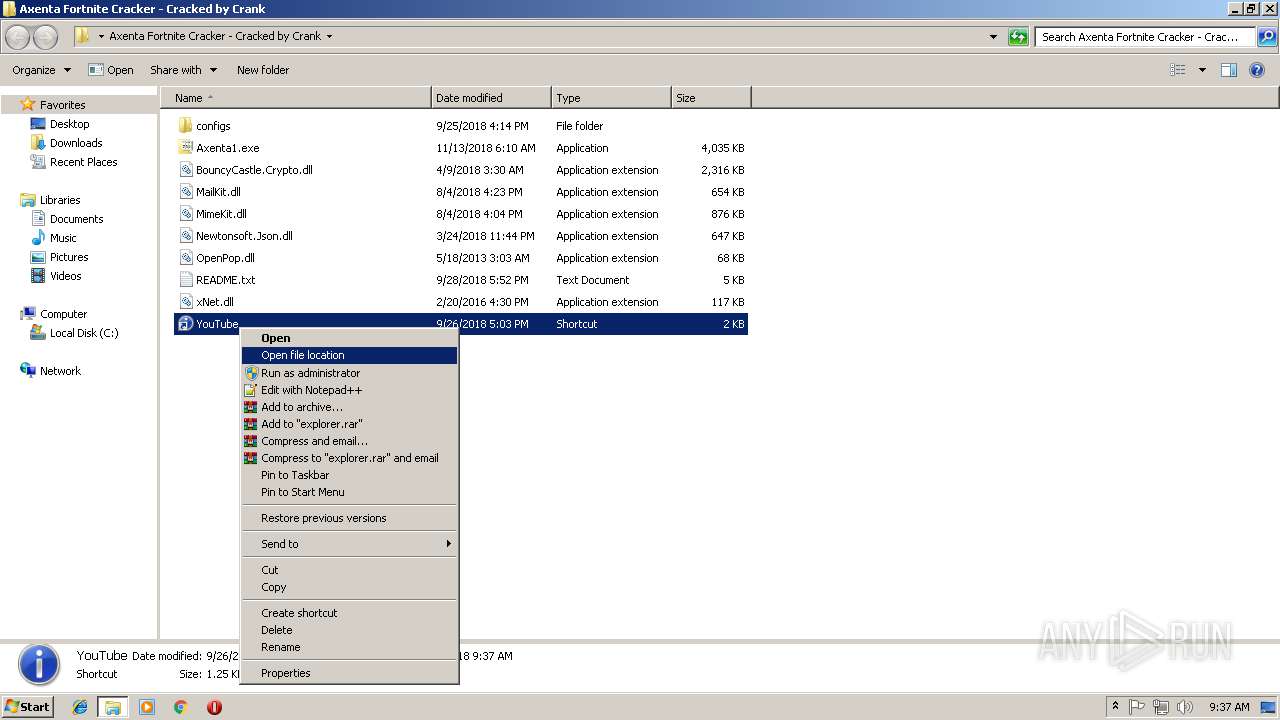
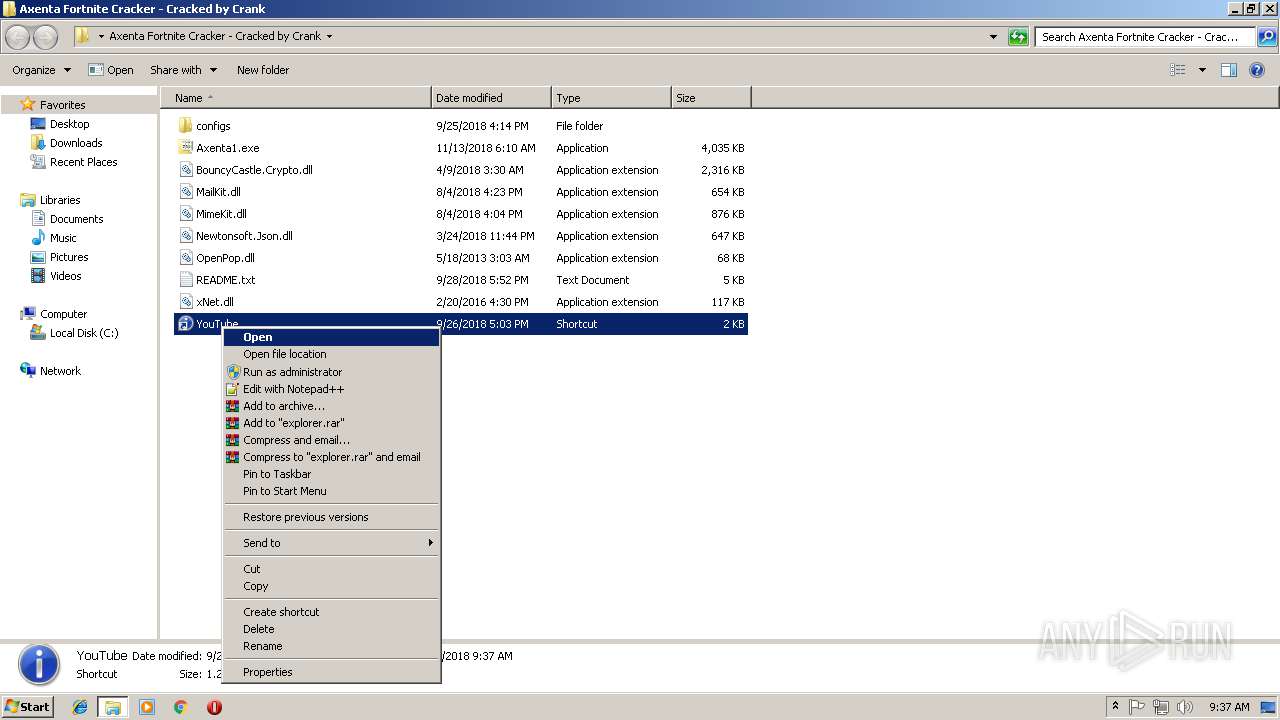
| 700 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa700.31955\Axenta Fortnite Cracker - Cracked by Crank\YouTube.lnk | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
2
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
936 | Axenta1.exe | POST | 200 | 185.212.130.15:80 | http://infek.tk/index.php | NL | text | 80 b | malicious |
— | — | POST | 200 | 185.194.141.58:80 | http://ip-api.com/line/ | DE | text | 206 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.194.141.58:80 | ip-api.com | netcup GmbH | DE | unknown |
936 | Axenta1.exe | 185.212.130.15:80 | infek.tk | Virtual Trade Ltd | NL | suspicious |
— | — | 216.58.215.238:80 | — | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
infek.tk |
| malicious |
ip-api.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
936 | Axenta1.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.PWS.Stealer.23869 (Arkei) |
936 | Axenta1.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
936 | Axenta1.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.PWS.Stealer.23869 (Arkei) |
936 | Axenta1.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
— | — | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
— | — | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.PWS.Stealer.23869 (Arkei) |
936 | Axenta1.exe | A Network Trojan was detected | ET CURRENT_EVENTS Possible Successful Phish to .tk domain Aug 26 2016 |
936 | Axenta1.exe | A Network Trojan was detected | ET TROJAN Arkei Stealer Client Data Upload |
936 | Axenta1.exe | A Network Trojan was detected | MALWARE [PTsecurity] Nocturnal Stealer |
936 | Axenta1.exe | A Network Trojan was detected | MALWARE [PTsecurity] Nocturnal Stealer |
3 ETPRO signatures available at the full report