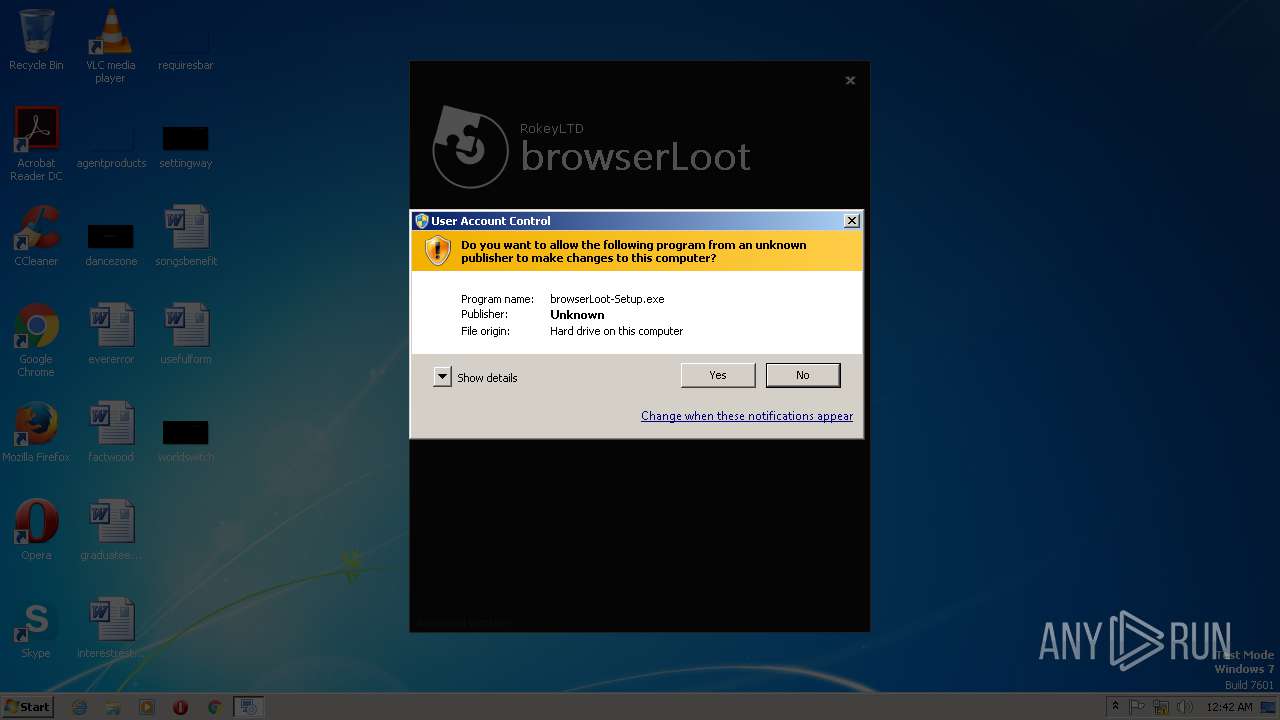
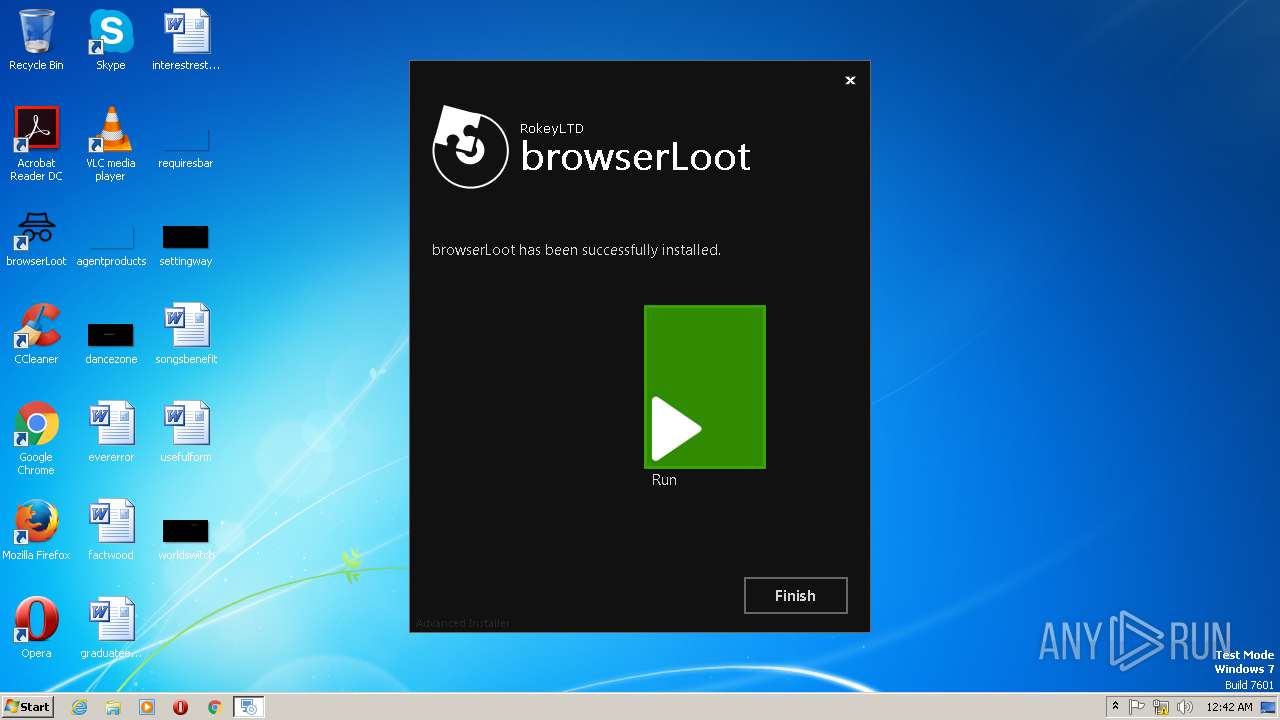
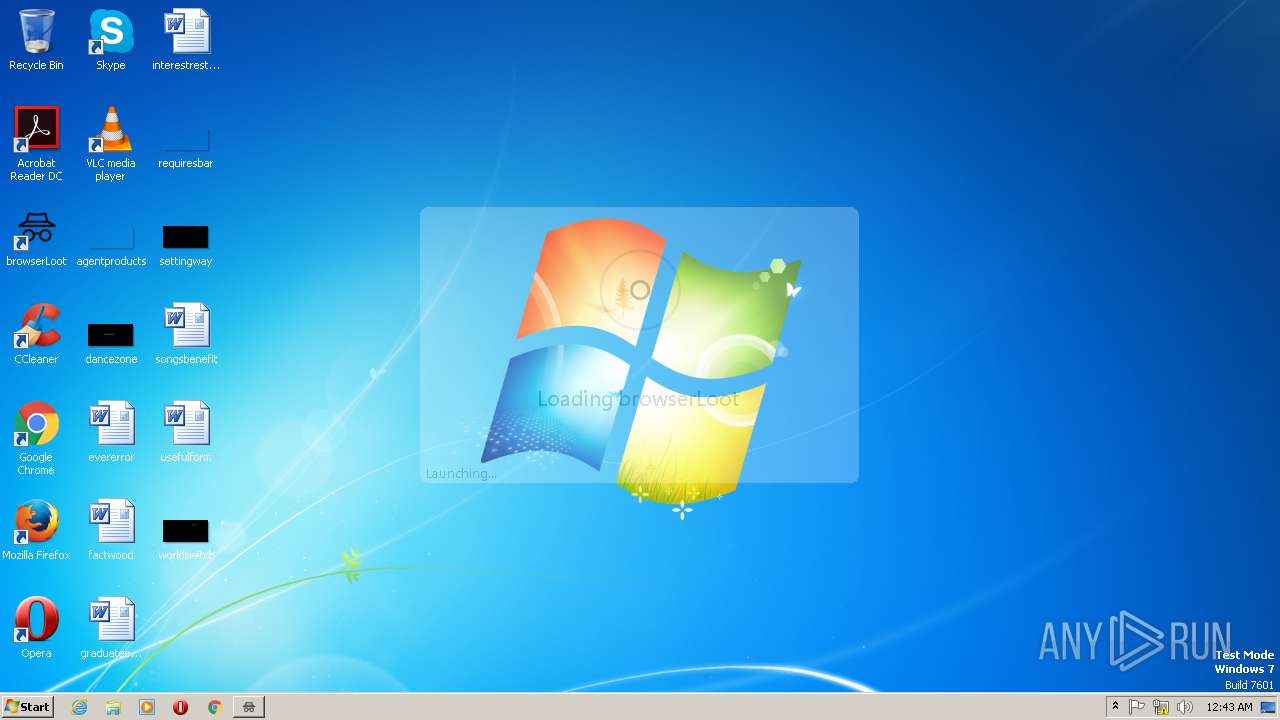
| File name: | browserLoot-Setup.exe |
| Full analysis: | https://app.any.run/tasks/921ef36d-be63-4429-bdad-d1343df56c75 |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | February 19, 2019, 00:41:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D0A9670753528654D5D5858F4929CF8D |
| SHA1: | BC480A94BE9BE4613A4ACF767136838CC7A6372B |
| SHA256: | B0E68E0D779E618F397DD424FD625CC0F3EEBC036A8864C61590F1DB25314573 |
| SSDEEP: | 786432:mbSjP4SRz9uokXh+8ktRxBM8DDs6TUHG4z57Q:mGj4SRzU/Xh+jRxB3DYQaGOG |
MALICIOUS
No malicious indicators.SUSPICIOUS
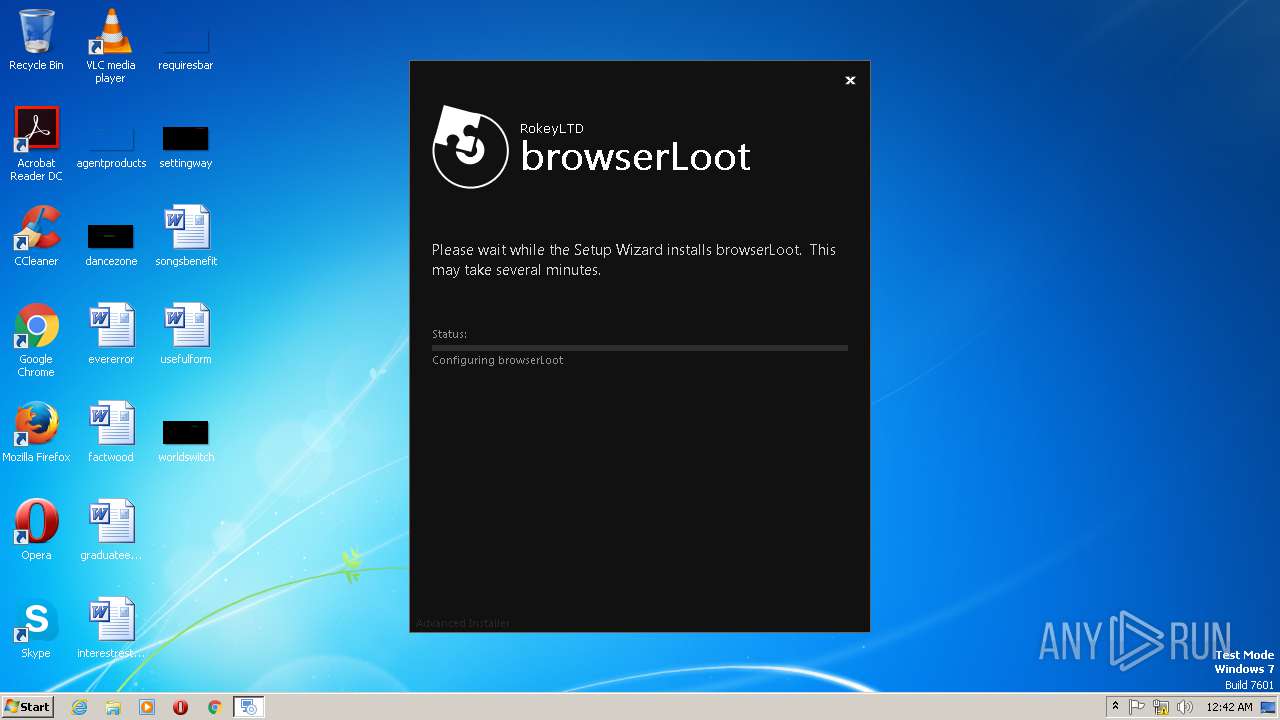
Executable content was dropped or overwritten
- browserLoot-Setup.exe (PID: 2124)
- browserLoot-Setup.exe (PID: 3056)
- msiexec.exe (PID: 2628)
Reads the machine GUID from the registry
- msiexec.exe (PID: 2628)
- vssvc.exe (PID: 3060)
Application launched itself
- browserLoot-Setup.exe (PID: 2124)
INFO
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2952)
Searches for installed software
- msiexec.exe (PID: 2628)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3060)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 2628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (3.6) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:03:07 10:57:40+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.12 |
| CodeSize: | 1201152 |
| InitializedDataSize: | 532992 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xdb1fa |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
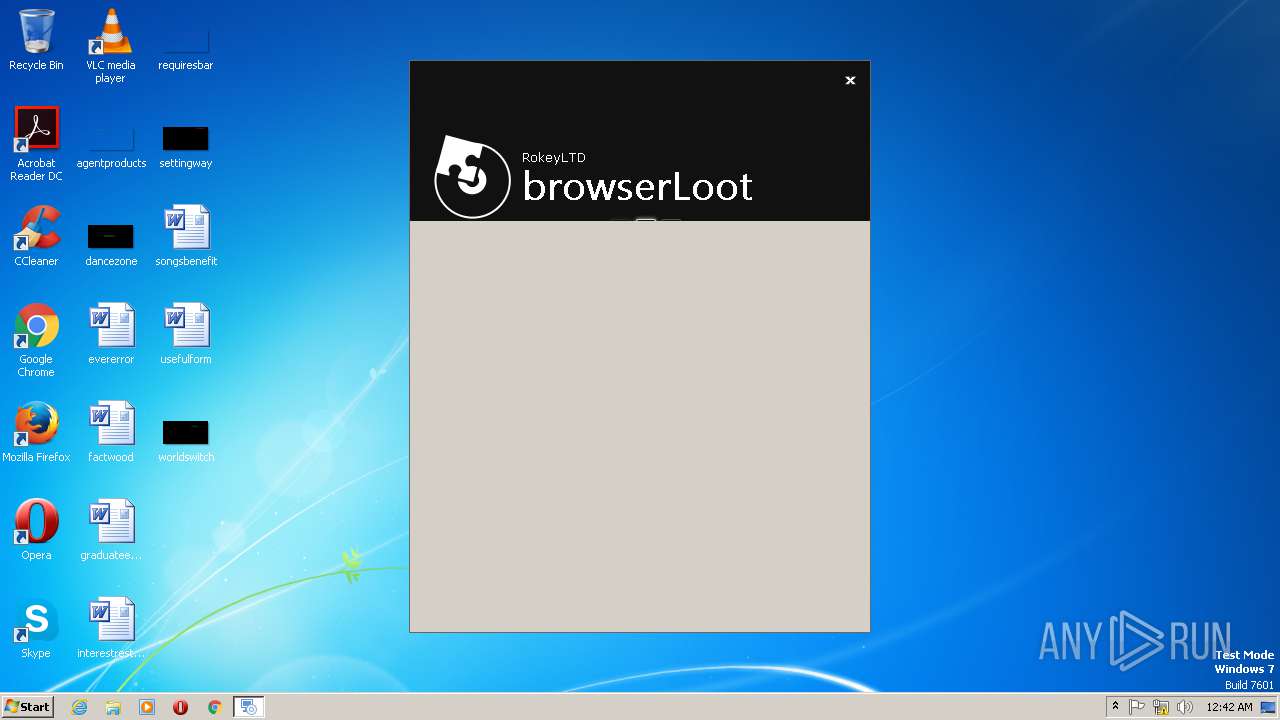
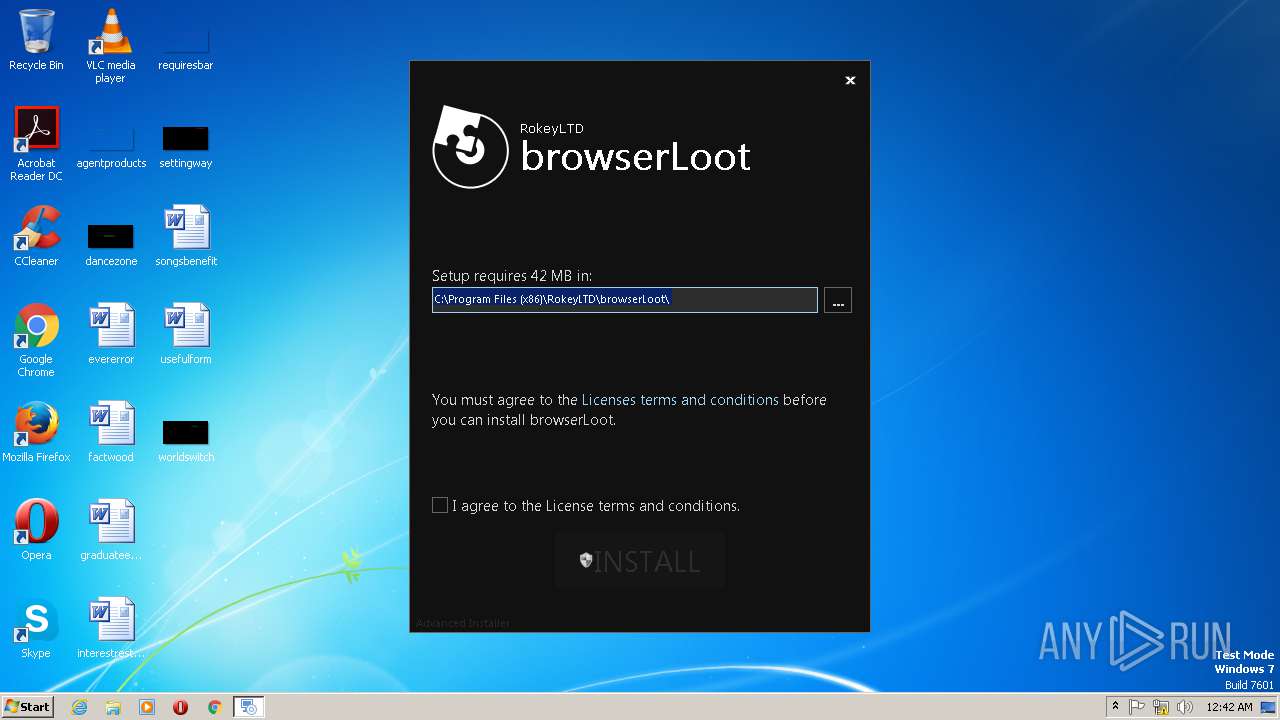
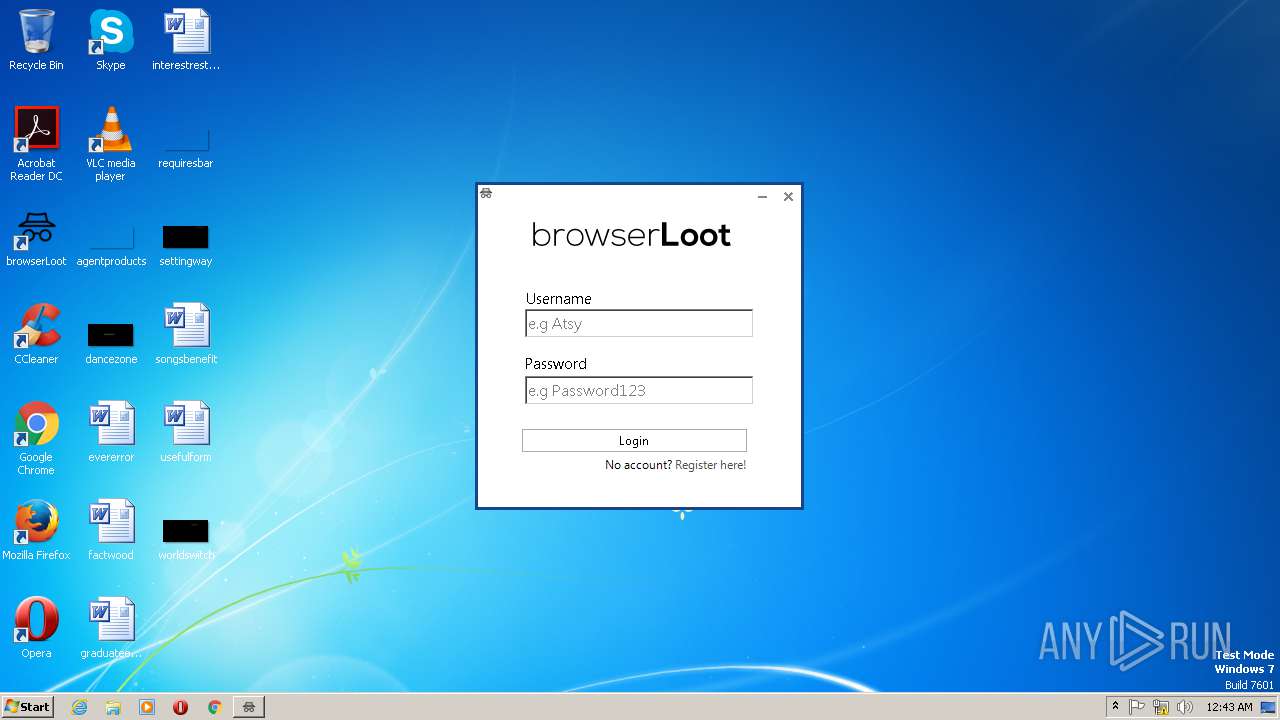
| CompanyName: | RokeyLTD |
| FileDescription: | browserLoot Installer |
| FileVersion: | 1.0.0 |
| InternalName: | browserLoot |
| LegalCopyright: | Copyright (C) 2018 RokeyLTD |
| OriginalFileName: | browserLoot.exe |
| ProductName: | browserLoot |
| ProductVersion: | 1.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Mar-2018 09:57:40 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | RokeyLTD |
| FileDescription: | browserLoot Installer |
| FileVersion: | 1.0.0 |
| InternalName: | browserLoot |
| LegalCopyright: | Copyright (C) 2018 RokeyLTD |
| OriginalFileName: | browserLoot.exe |
| ProductName: | browserLoot |
| ProductVersion: | 1.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 07-Mar-2018 09:57:40 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0012536D | 0x00125400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.65483 |
.rdata | 0x00127000 | 0x00055584 | 0x00055600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.57057 |
.data | 0x0017D000 | 0x00007164 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.18299 |
.rsrc | 0x00185000 | 0x0001528C | 0x00015400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.36213 |
.reloc | 0x0019B000 | 0x00015340 | 0x00015400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.58351 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.18236 | 1872 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.1591 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.46873 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.54157 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.01317 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.37783 | 1116 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 3.35254 | 1888 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.31743 | 760 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 3.23118 | 1432 | Latin 1 / Western European | English - United States | RT_STRING |
13 | 3.35766 | 820 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
msi.dll (delay-loaded) |
Total processes
41
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
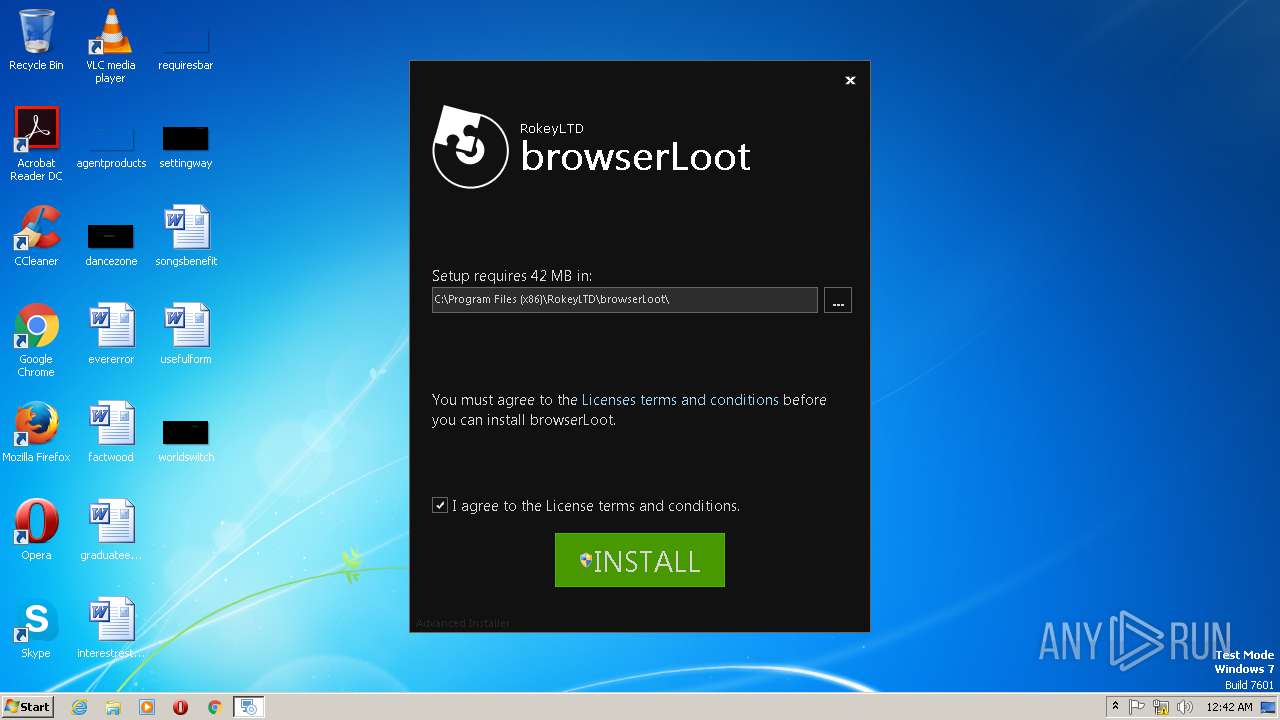
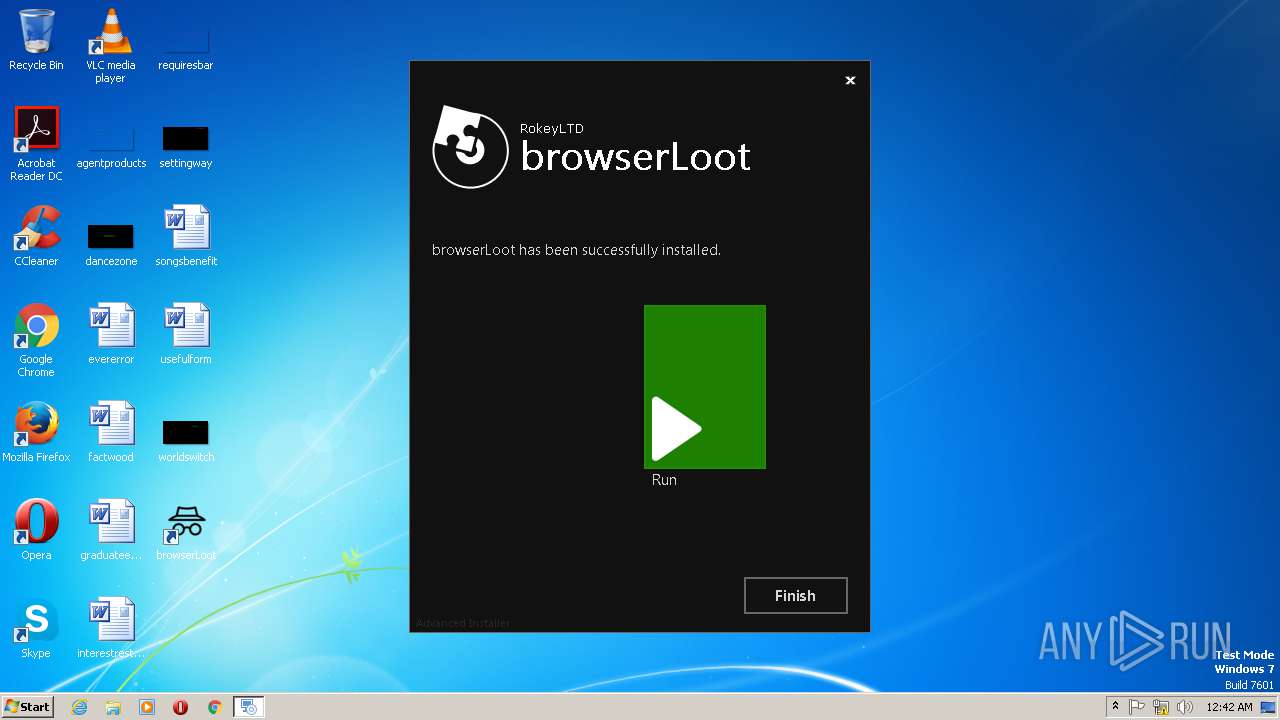
| 2124 | "C:\Users\admin\AppData\Local\Temp\browserLoot-Setup.exe" | C:\Users\admin\AppData\Local\Temp\browserLoot-Setup.exe | explorer.exe | ||||||||||||
User: admin Company: RokeyLTD Integrity Level: MEDIUM Description: browserLoot Installer Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
| 2628 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2952 | C:\Windows\syswow64\MsiExec.exe -Embedding E1C051FC03D0A12E8581B7C1DCB2D709 C | C:\Windows\syswow64\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3056 | "C:\Users\admin\AppData\Local\Temp\browserLoot-Setup.exe" /i C:\Users\admin\AppData\Local\Temp\{B308F405-DA45-4CFD-974D-EA94A7BC709A}\browserLoot.msi AI_EUIMSI=1 SHORTCUTDIR="C:\ProgramData\Microsoft\Windows\Start Menu\Programs\browserLoot" APPDIR="C:\Program Files (x86)\RokeyLTD\browserLoot" CLIENTPROCESSID="2124" SECONDSEQUENCE="1" CHAINERUIPROCESSID="2124Chainer" ACTION="INSTALL" EXECUTEACTION="INSTALL" CLIENTUILEVEL="0" ADDLOCAL="MainFeature" AGREE_CHECKBOX="Yes" PRIMARYFOLDER="APPDIR" ROOTDRIVE="C:\" AI_FOUND_PREREQS=".NET Framework 4.5.2" AI_DETECTED_DOTNET_VERSION="4.6.1" AI_SETUPEXEPATH="C:\Users\admin\AppData\Local\Temp\browserLoot-Setup.exe" SETUPEXEDIR="C:\Users\admin\AppData\Local\Temp\" EXE_CMD_LINE="/exenoupdates " TARGETDIR="C:\" AI_INSTALL="1" AI_SETUPEXEPATH_ORIGINAL="C:\Users\admin\AppData\Local\Temp\browserLoot-Setup.exe" | C:\Users\admin\AppData\Local\Temp\browserLoot-Setup.exe | browserLoot-Setup.exe | ||||||||||||
User: admin Company: RokeyLTD Integrity Level: HIGH Description: browserLoot Installer Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
| 3060 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
498
Read events
381
Write events
117
Delete events
0
Modification events
| (PID) Process: | (2124) browserLoot-Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2124) browserLoot-Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2124) browserLoot-Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2124) browserLoot-Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2628) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 48000000000000005326A3F4EBC7D401440A0000840A0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2628) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000005326A3F4EBC7D401440A0000840A0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2628) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 28 | |||
| (PID) Process: | (2628) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 48000000000000002BE8E5F4EBC7D401440A0000840A0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2628) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000002BE8E5F4EBC7D401440A00000C0B0000E803000001000000000000000000000038DC428B2F7F5242B57C041BEE87B47F00000000000000000000000000000000 | |||
| (PID) Process: | (3060) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000A198F6F4EBC7D401F40B0000D40B0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
48
Suspicious files
6
Text files
62
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2124 | browserLoot-Setup.exe | C:\Users\admin\AppData\Local\Temp\{B308F405-DA45-4CFD-974D-EA94A7BC709A}\holder0.aiph | — | |
MD5:— | SHA256:— | |||
| 2124 | browserLoot-Setup.exe | C:\Users\admin\AppData\Local\Temp\MSI358F.tmp | — | |
MD5:— | SHA256:— | |||
| 2124 | browserLoot-Setup.exe | C:\Users\admin\AppData\Local\Temp\MSI3590.tmp | — | |
MD5:— | SHA256:— | |||
| 2124 | browserLoot-Setup.exe | C:\Users\admin\AppData\Local\Temp\{B308F405-DA45-4CFD-974D-EA94A7BC709A}\browserLoot.aiui | executable | |
MD5:— | SHA256:— | |||
| 2124 | browserLoot-Setup.exe | C:\Users\admin\AppData\Local\Temp\{B308F405-DA45-4CFD-974D-EA94A7BC709A}\browserLoot.msi | executable | |
MD5:— | SHA256:— | |||
| 2124 | browserLoot-Setup.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_2124\printico | image | |
MD5:BDC280616F9670F41C57C16BF08E8387 | SHA256:6E5C2E9E923569F943E9F8A86EE5023034B3DB1F6434118A0D95F429F90FFBE7 | |||
| 2124 | browserLoot-Setup.exe | C:\Users\admin\AppData\Local\Temp\MSI34D3.tmp | executable | |
MD5:D261A064A6612A2B5F8774E55D49E8BB | SHA256:83A68300F22FA9F45FEA46E16AADA7887C3B8B09CEF3FAF098C30B428E6A4629 | |||
| 2124 | browserLoot-Setup.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_2124\repairic | image | |
MD5:2ED3D45BC22B79DB09136513AED402DD | SHA256:4A8FA6335720D3E4F464AF244364923E741605B8AD3E1E28411F494E95EC11E4 | |||
| 2124 | browserLoot-Setup.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_2124\frame_top_left_inactive.bmp | image | |
MD5:1966F4308086A013B8837DDDF88F67AD | SHA256:17B5CD496D98DB14E7C9757E38892883C7B378407E1F136889A9921ABE040741 | |||
| 2124 | browserLoot-Setup.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_2124\frame_bottom_left_inactive.bmp | image | |
MD5:821930553EF406B0C82D9420D3351C78 | SHA256:D5E9F3533CB7D727611AAFAA5AF22FA07EFEAEC0391A011ECF9803BED867DE7A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
6
DNS requests
2
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
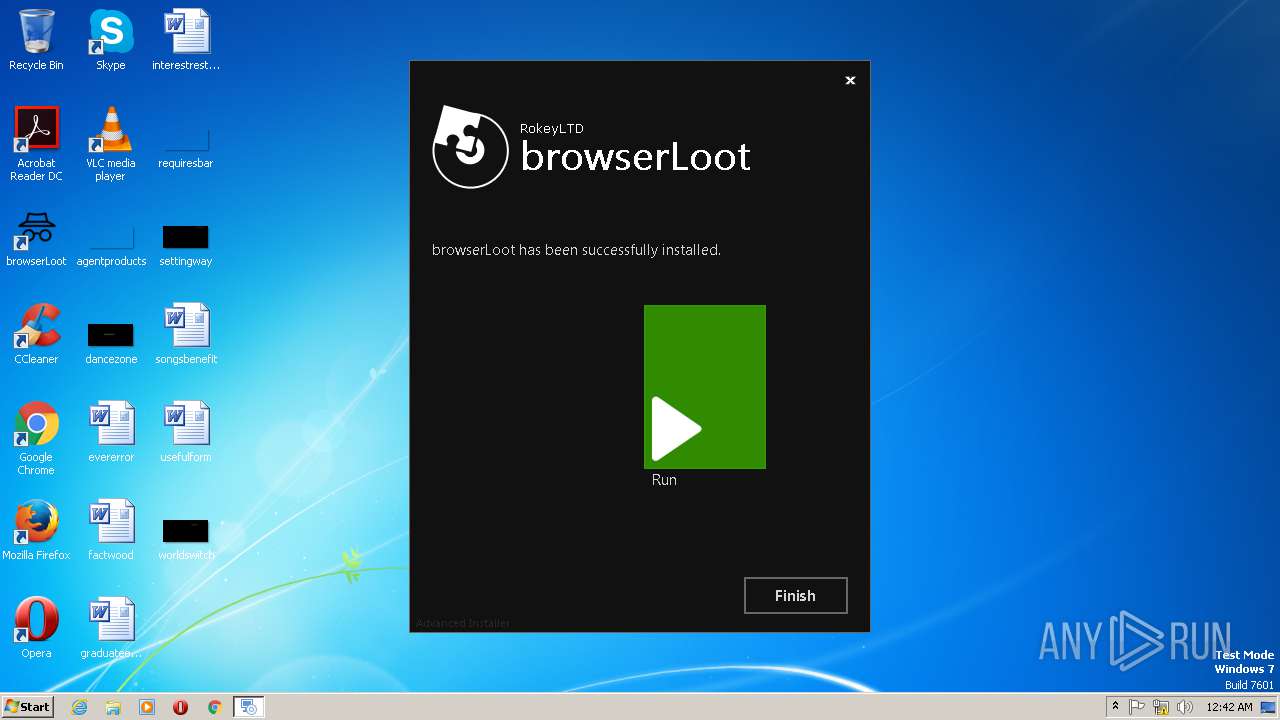
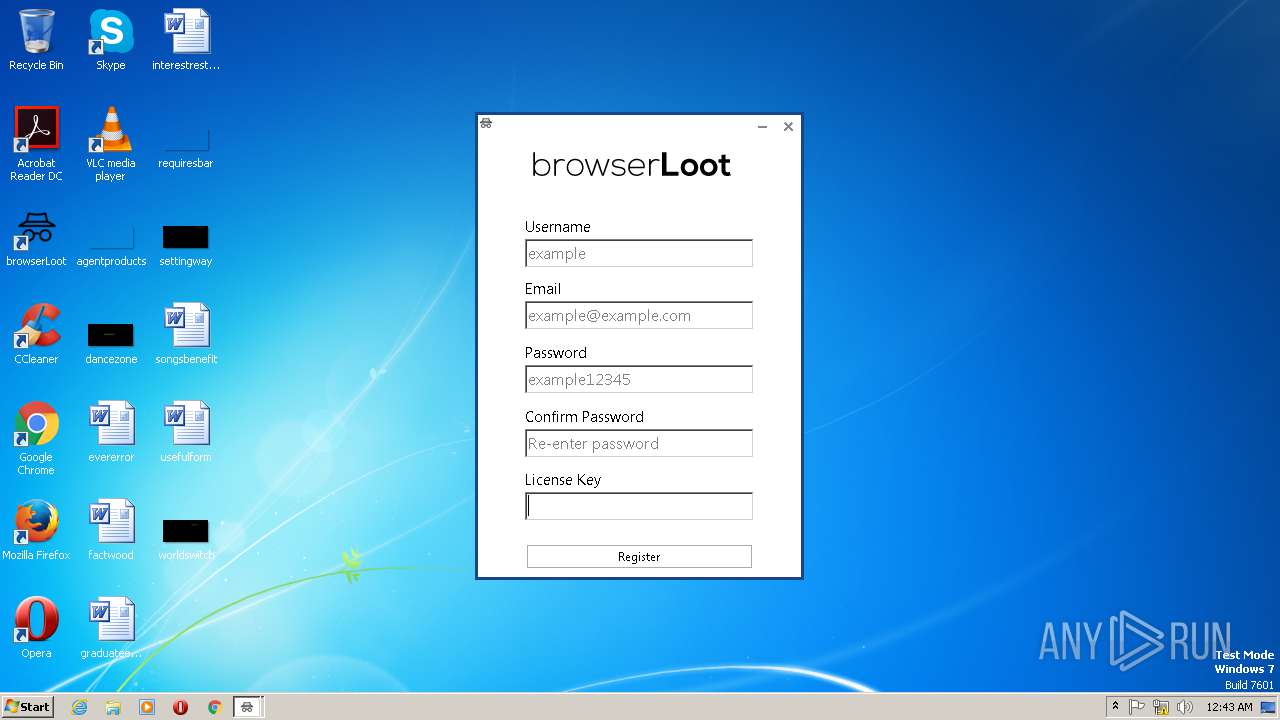
— | — | GET | 301 | 104.31.76.103:80 | http://browserloot.rokey.xyz/api/versions/1.1/ | US | — | — | malicious |
— | — | GET | 204 | 216.58.208.46:80 | http://clients3.google.com/generate_204 | US | — | — | whitelisted |
— | — | GET | 204 | 216.58.208.46:80 | http://clients3.google.com/generate_204 | US | — | — | whitelisted |
— | — | GET | 301 | 104.31.76.103:80 | http://browserloot.rokey.xyz/api/versions/1.1/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 104.31.76.103:443 | browserloot.rokey.xyz | Cloudflare Inc | US | shared |
— | — | 104.31.76.103:80 | browserloot.rokey.xyz | Cloudflare Inc | US | shared |
— | — | 216.58.208.46:80 | clients3.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
browserloot.rokey.xyz |
| malicious |
clients3.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | A Network Trojan was detected | MALWARE [PTsecurity] BrowserLoot Stealer |
— | — | A Network Trojan was detected | MALWARE [PTsecurity] BrowserLoot Stealer |
2 ETPRO signatures available at the full report