| File name: | file.exe |
| Full analysis: | https://app.any.run/tasks/a1175f37-e0a7-433c-b235-0e5e413c3f77 |
| Verdict: | Malicious activity |
| Threats: | WarZone RAT is a remote access trojan, which is written in C++ and offered as a malware-as-a-service. It packs a wide range of capabilities, from stealing victims’ files and passwords to capturing desktop activities. WarZone RAT is primarily distributed via phishing emails and receives regular updates from its C2. |
| Analysis date: | September 30, 2020, 09:42:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | EE30419ED7499C224DDED63416F5E70F |
| SHA1: | 85519BF70E7E05C7F3D74DC38154934834F0CCA2 |
| SHA256: | B09BA0422073D096874E13104B4709F379468DD324EB85DCB84CD112A6609F1B |
| SSDEEP: | 24576:ymMTGeriBlWM0oSyEboy970e+y2/Vb0Amexia:9MTGeriBlWM0oSyEboy970e+y2/Vb0AZ |
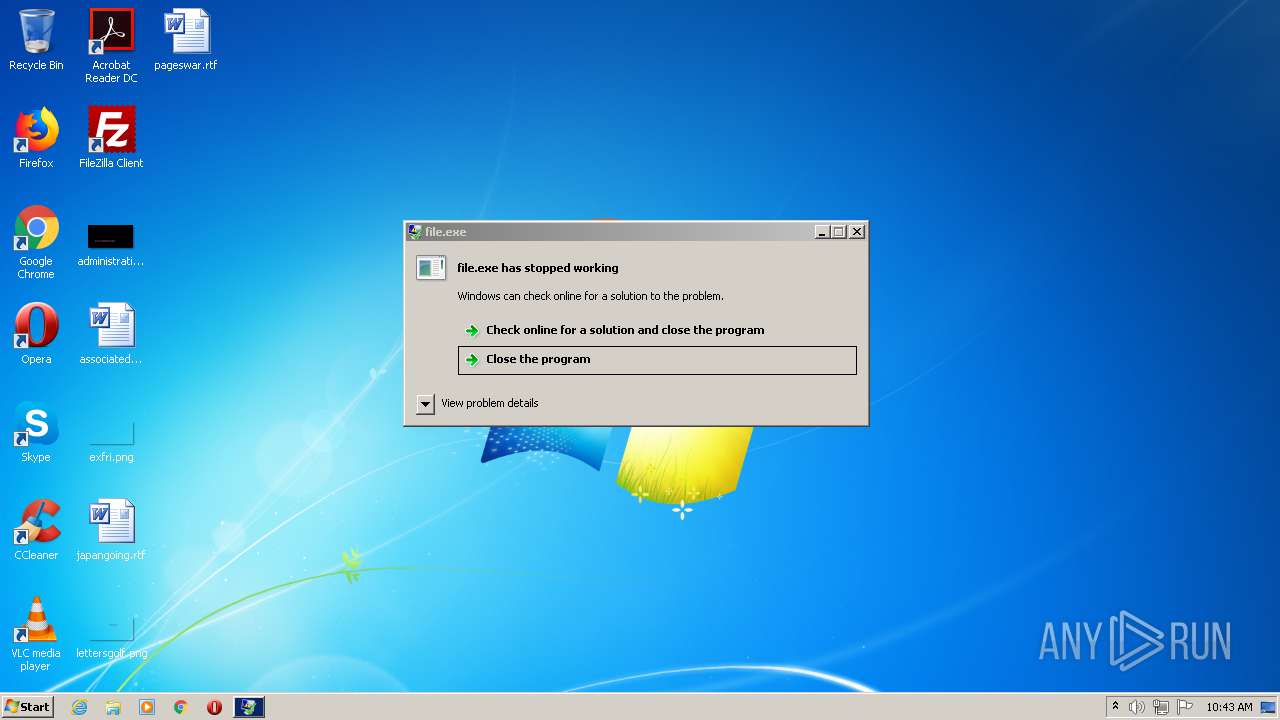
MALICIOUS
AVEMARIA was detected
- file.exe (PID: 2808)
- images.exe (PID: 1864)
- file.exe (PID: 1556)
- images.exe (PID: 2380)
Changes the autorun value in the registry
- file.exe (PID: 2808)
Runs app for hidden code execution
- file.exe (PID: 2808)
- images.exe (PID: 1864)
Actions looks like stealing of personal data
- images.exe (PID: 1864)
Loads dropped or rewritten executable
- dism.exe (PID: 3332)
- dism.exe (PID: 612)
Connects to CnC server
- images.exe (PID: 1864)
- images.exe (PID: 2380)
- file.exe (PID: 1556)
SUSPICIOUS
Starts CMD.EXE for commands execution
- file.exe (PID: 2808)
- images.exe (PID: 1864)
Reads Internet Cache Settings
- file.exe (PID: 2808)
- file.exe (PID: 1556)
- images.exe (PID: 1864)
- images.exe (PID: 2380)
Starts itself from another location
- file.exe (PID: 2808)
Executable content was dropped or overwritten
- cmd.exe (PID: 1972)
- file.exe (PID: 2808)
- DllHost.exe (PID: 2312)
- cmd.exe (PID: 2740)
- DllHost.exe (PID: 2896)
Creates files in the user directory
- file.exe (PID: 2808)
- images.exe (PID: 1864)
- powershell.exe (PID: 2664)
- powershell.exe (PID: 2980)
Executed via COM
- DllHost.exe (PID: 2312)
- DllHost.exe (PID: 2896)
Executes PowerShell scripts
- file.exe (PID: 1556)
- images.exe (PID: 2380)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:09:27 17:31:18+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 114688 |
| InitializedDataSize: | 757760 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6410 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 27-Sep-2020 15:31:18 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 27-Sep-2020 15:31:18 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001BE0D | 0x0001C000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.61947 |
.rdata | 0x0001D000 | 0x0000F1D2 | 0x0000F200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.29567 |
.data | 0x0002D000 | 0x000A7A10 | 0x000A6C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.84608 |
.rsrc | 0x000D5000 | 0x000001E0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.70286 |
.reloc | 0x000D6000 | 0x00001FF0 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.57021 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
KERNEL32.dll |
USER32.dll |
WININET.dll |
ole32.dll |
Total processes
68
Monitored processes
16
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 612 | "C:\Windows\system32\dism.exe" /online /norestart /apply-unattend:"C:\Users\admin\AppData\Local\Temp\ellocnak.xml" | C:\Windows\system32\dism.exe | — | pkgmgr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Image Servicing Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1556 | "C:\Users\admin\AppData\Local\Temp\file.exe" | C:\Users\admin\AppData\Local\Temp\file.exe | dism.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225477 Modules
| |||||||||||||||
| 1864 | "C:\Users\admin\AppData\Roaming\images.exe" | C:\Users\admin\AppData\Roaming\images.exe | file.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1972 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | file.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2312 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2380 | "C:\Users\admin\AppData\Roaming\images.exe" | C:\Users\admin\AppData\Roaming\images.exe | dism.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2664 | powershell Add-MpPreference -ExclusionPath C:\ | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | file.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2740 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | images.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2808 | "C:\Users\admin\AppData\Local\Temp\file.exe" | C:\Users\admin\AppData\Local\Temp\file.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2872 | "C:\Windows\system32\pkgmgr.exe" /n:%temp%\ellocnak.xml | C:\Windows\system32\pkgmgr.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Package Manager Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 379
Read events
1 245
Write events
134
Delete events
0
Modification events
| (PID) Process: | (2808) file.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPer1_0Server |
Value: 10 | |||
| (PID) Process: | (2808) file.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPerServer |
Value: 10 | |||
| (PID) Process: | (2808) file.exe | Key: | HKEY_CURRENT_USER\Software\_rptls |
| Operation: | write | Name: | Install |
Value: C:\Users\admin\AppData\Local\Temp\file.exe | |||
| (PID) Process: | (2808) file.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\3BP2YKUVKV |
| Operation: | write | Name: | inst |
Value: BEE3DBE35B86A904412120789915F2E23516794512D5E92902212EE9309B61C40AEC266291F6645D8BDDB623B37E5082368622F7506B83B8CD395BE70F871858CB9CFA81CD938AB89419389C9BDE664944F3F1C9 | |||
| (PID) Process: | (2808) file.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Images |
Value: C:\Users\admin\AppData\Roaming\images.exe | |||
| (PID) Process: | (1972) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1972) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1864) images.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPer1_0Server |
Value: 10 | |||
| (PID) Process: | (1864) images.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPerServer |
Value: 10 | |||
| (PID) Process: | (1864) images.exe | Key: | HKEY_CURRENT_USER\Software\_rptls |
| Operation: | write | Name: | Install |
Value: C:\Users\admin\AppData\Roaming\images.exe | |||
Executable files
5
Suspicious files
4
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1864 | images.exe | C:\Users\admin\AppData\Roaming\mpFFeE..tmp | — | |
MD5:— | SHA256:— | |||
| 1864 | images.exe | C:\Users\admin\AppData\Roaming\CvEvIcb.tmp | — | |
MD5:— | SHA256:— | |||
| 2664 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\UVRH6ZUHKPQLY54DQ48A.temp | — | |
MD5:— | SHA256:— | |||
| 2980 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\WDFELGNM0XI2YSHFI8V5.temp | — | |
MD5:— | SHA256:— | |||
| 2808 | file.exe | C:\Users\admin\AppData\Roaming\images.exe | executable | |
MD5:— | SHA256:— | |||
| 2872 | pkgmgr.exe | C:\Windows\Logs\CBS\CBS.log | text | |
MD5:— | SHA256:— | |||
| 2980 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF234b37.TMP | binary | |
MD5:— | SHA256:— | |||
| 2664 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2664 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF23071a.TMP | binary | |
MD5:— | SHA256:— | |||
| 2980 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
153
DNS requests
2
Threats
19
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2808 | file.exe | 69.171.242.11:80 | facebook.pt | Facebook, Inc. | US | unknown |
1864 | images.exe | 69.171.242.11:80 | facebook.pt | Facebook, Inc. | US | unknown |
1864 | images.exe | 193.169.253.181:5200 | minekroft.duckdns.org | — | UA | malicious |
1556 | file.exe | 69.171.242.11:80 | facebook.pt | Facebook, Inc. | US | unknown |
1556 | file.exe | 193.169.253.181:5200 | minekroft.duckdns.org | — | UA | malicious |
— | — | 69.171.242.11:80 | facebook.pt | Facebook, Inc. | US | unknown |
2380 | images.exe | 69.171.242.11:80 | facebook.pt | Facebook, Inc. | US | unknown |
2380 | images.exe | 193.169.253.181:5200 | minekroft.duckdns.org | — | UA | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
facebook.pt |
| unknown |
minekroft.duckdns.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1864 | images.exe | A Network Trojan was detected | AV TROJAN Ave Maria RAT CnC Response |
1864 | images.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Encrypted Checkin |
1864 | images.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Connection |
1556 | file.exe | A Network Trojan was detected | AV TROJAN Ave Maria RAT CnC Response |
1556 | file.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Encrypted Checkin |
1556 | file.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Connection |
1556 | file.exe | A Network Trojan was detected | AV TROJAN Ave Maria RAT CnC Response |
1556 | file.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Encrypted Checkin |
1556 | file.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Connection |
5 ETPRO signatures available at the full report