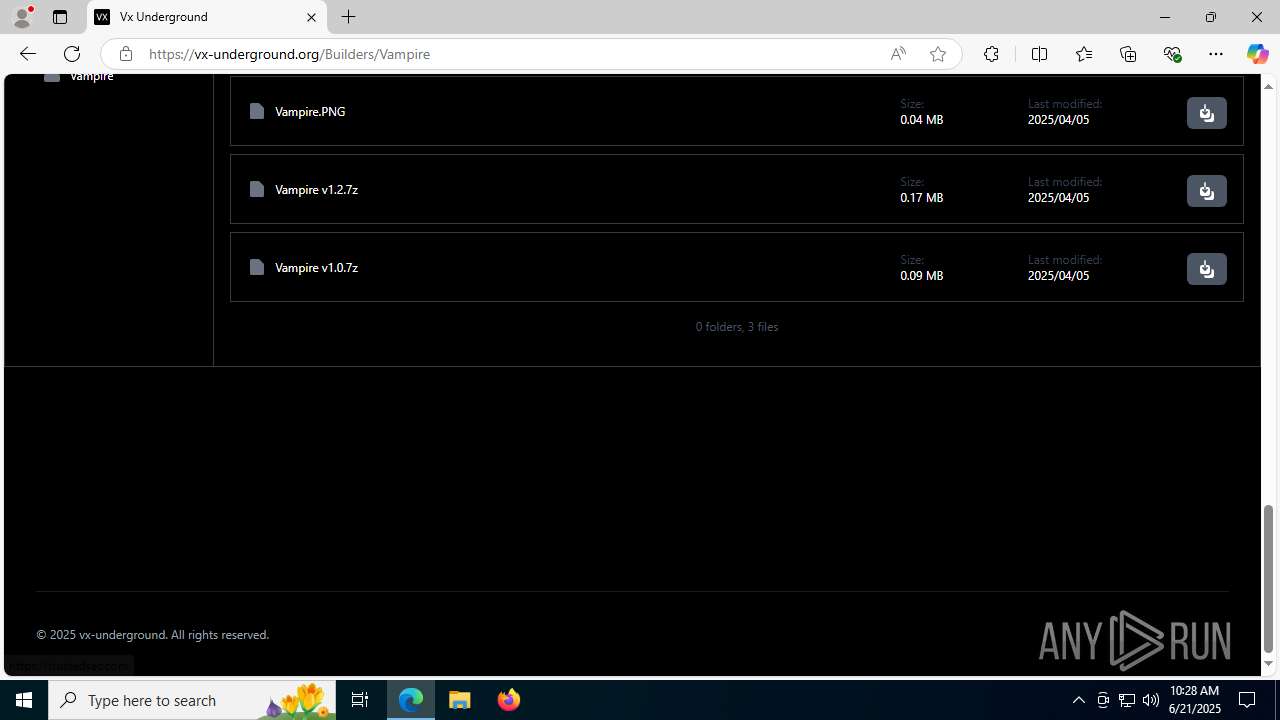
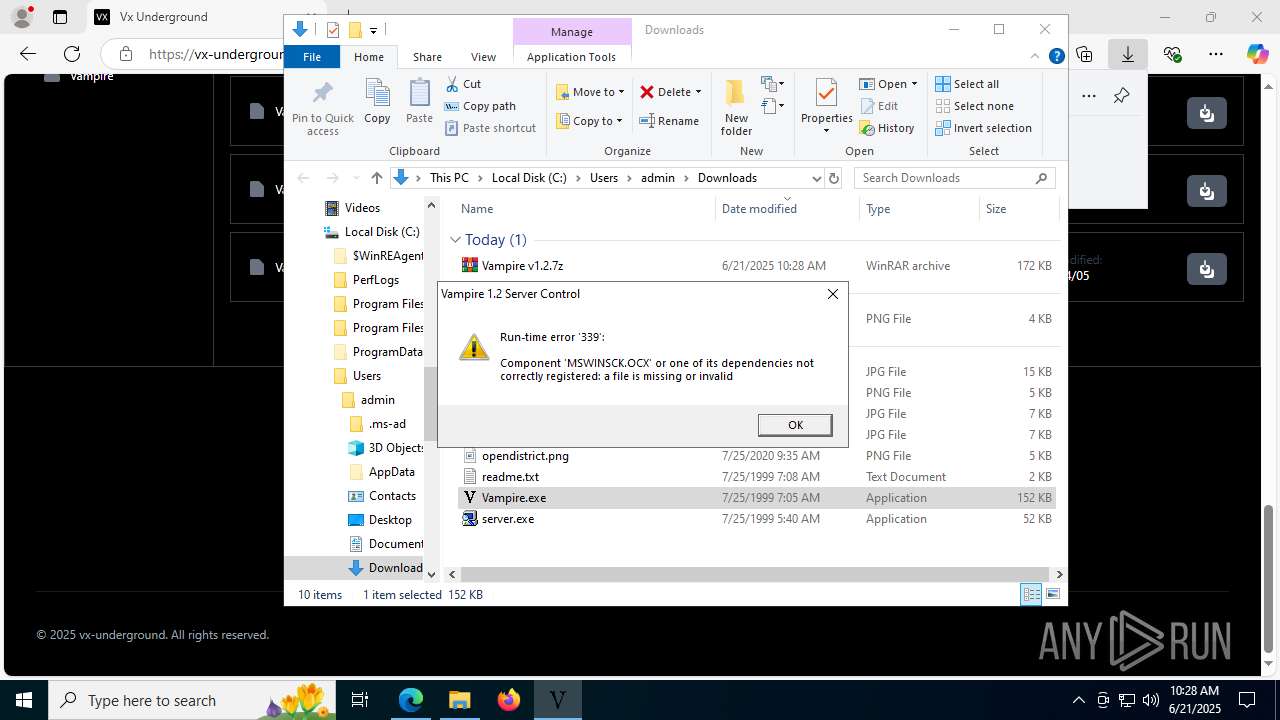
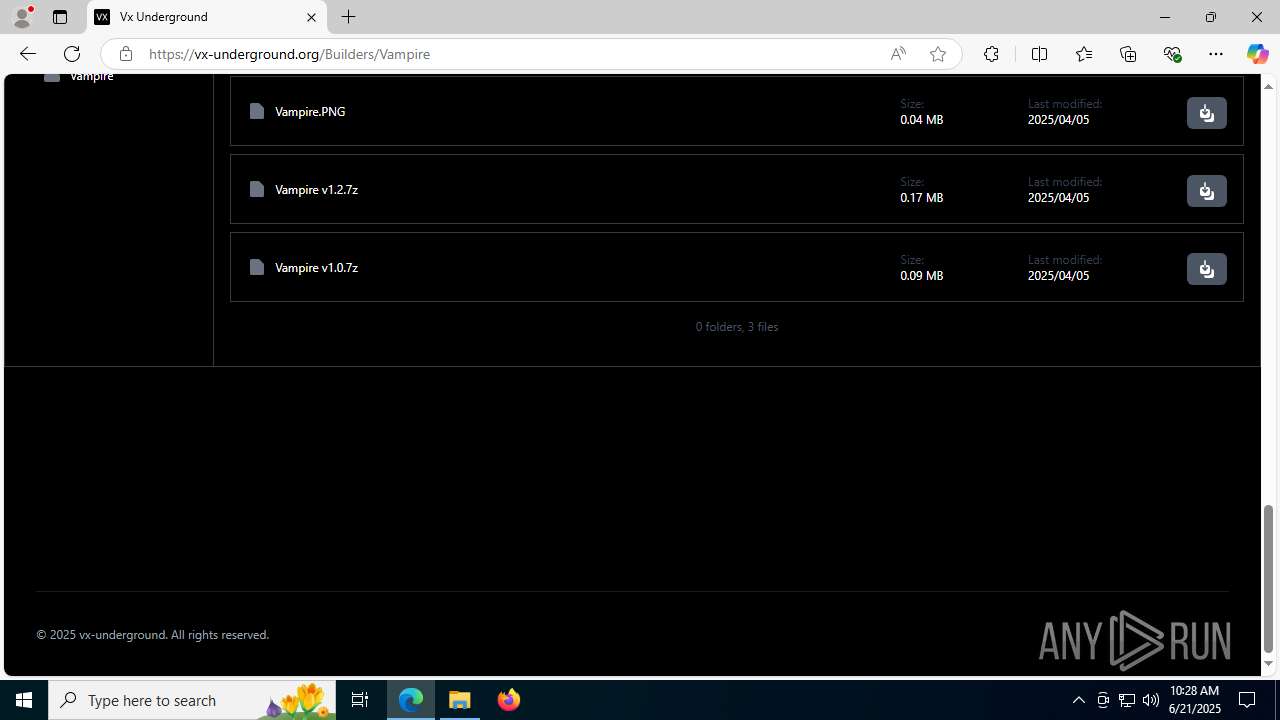
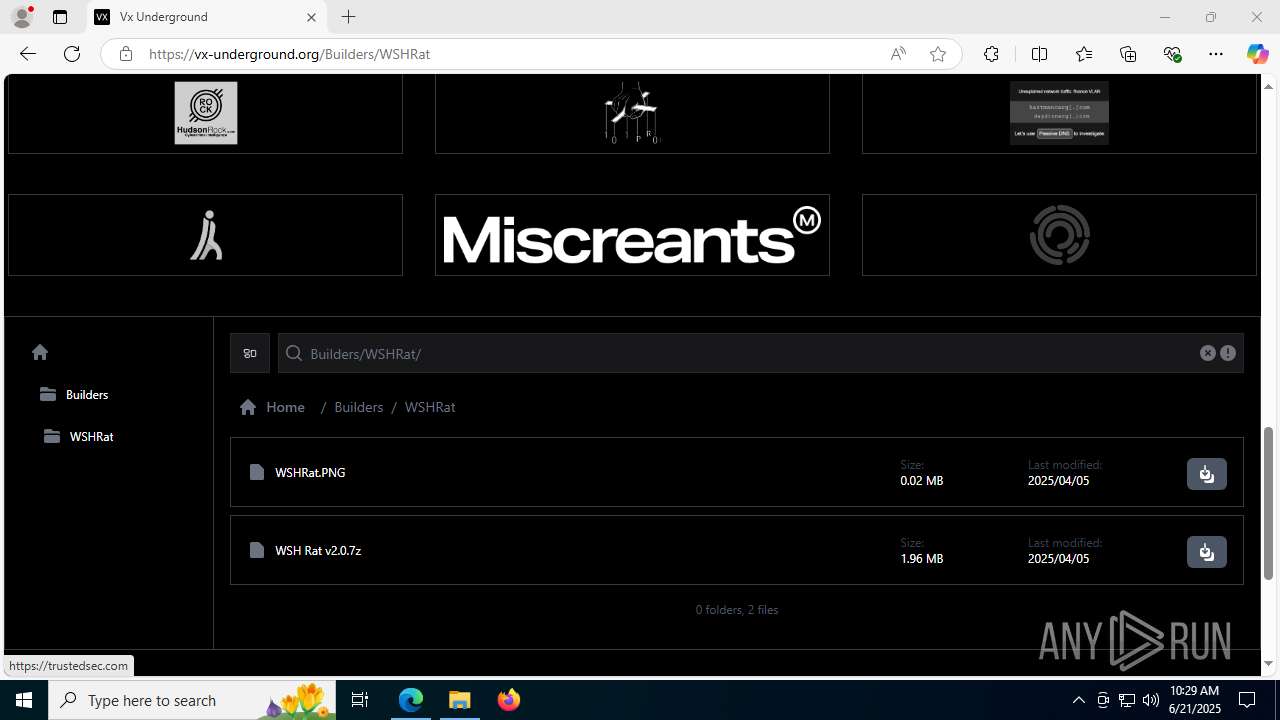
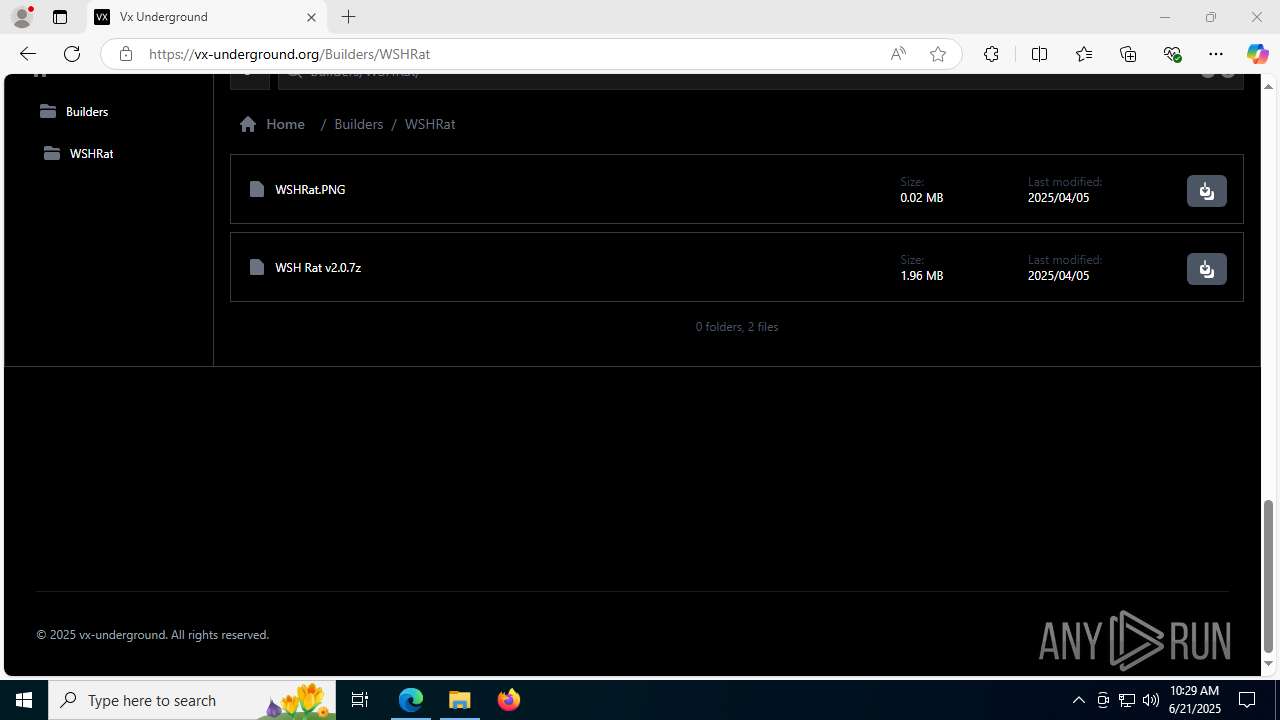
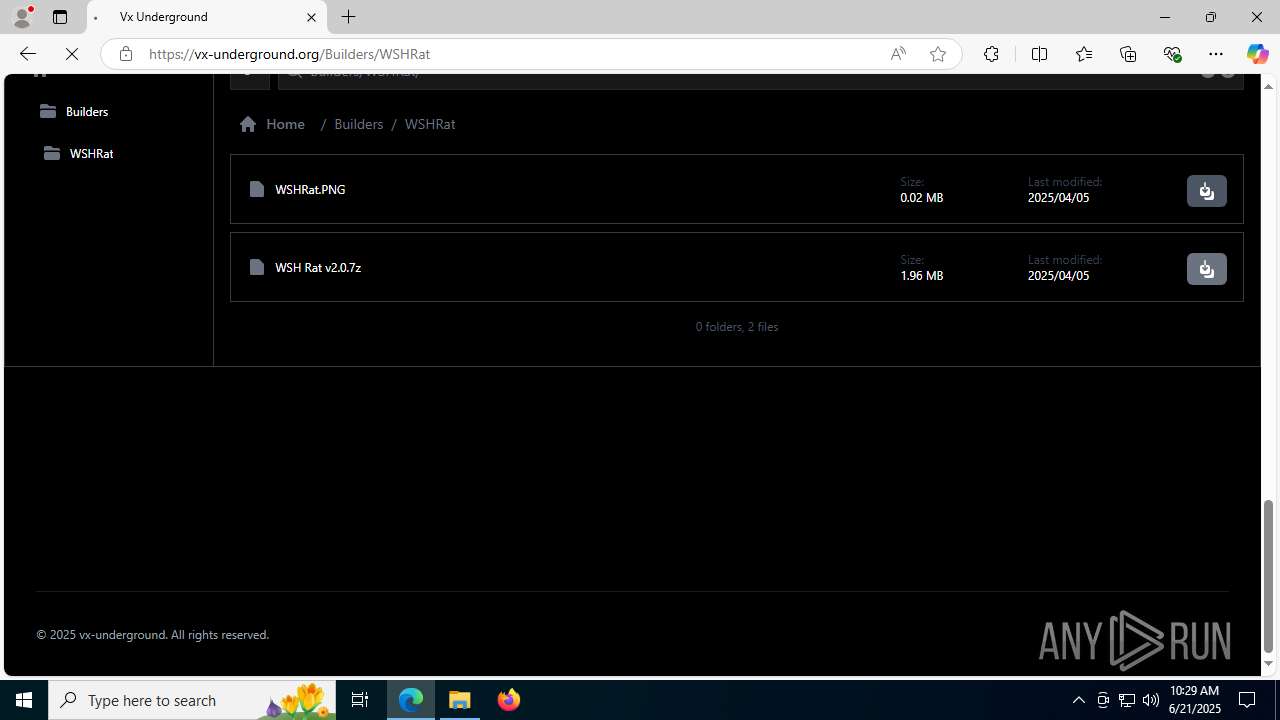
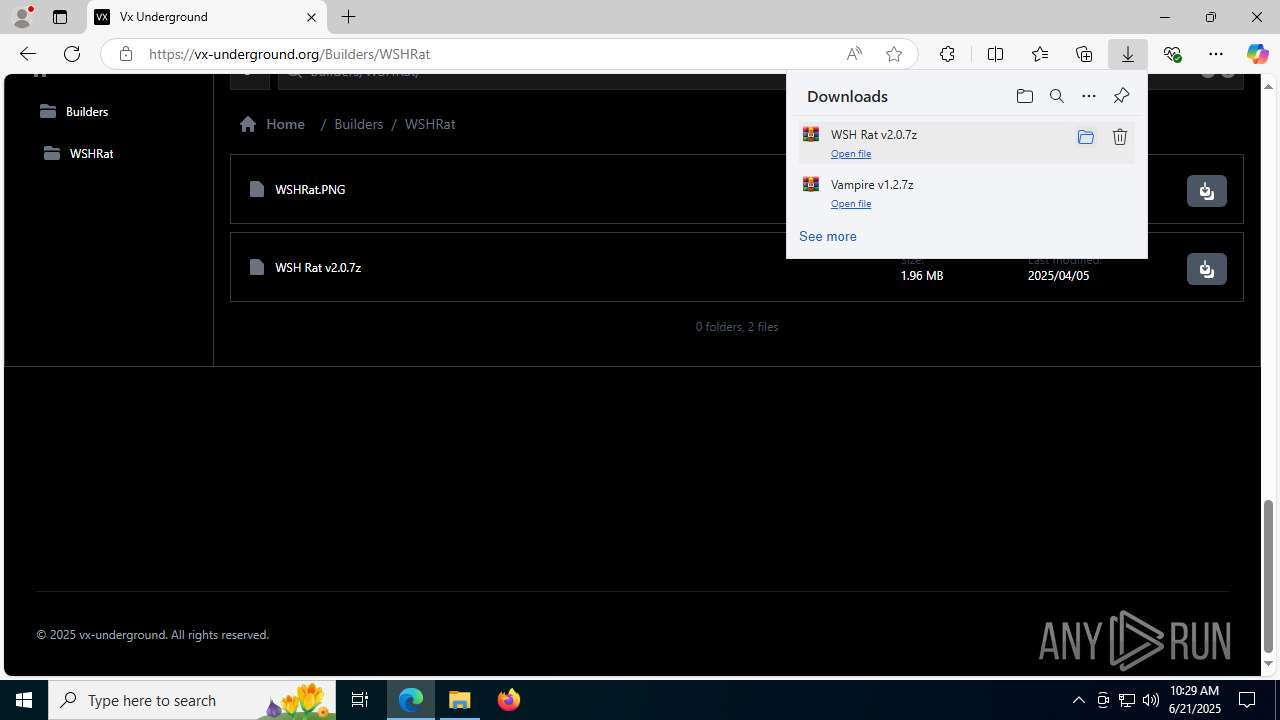
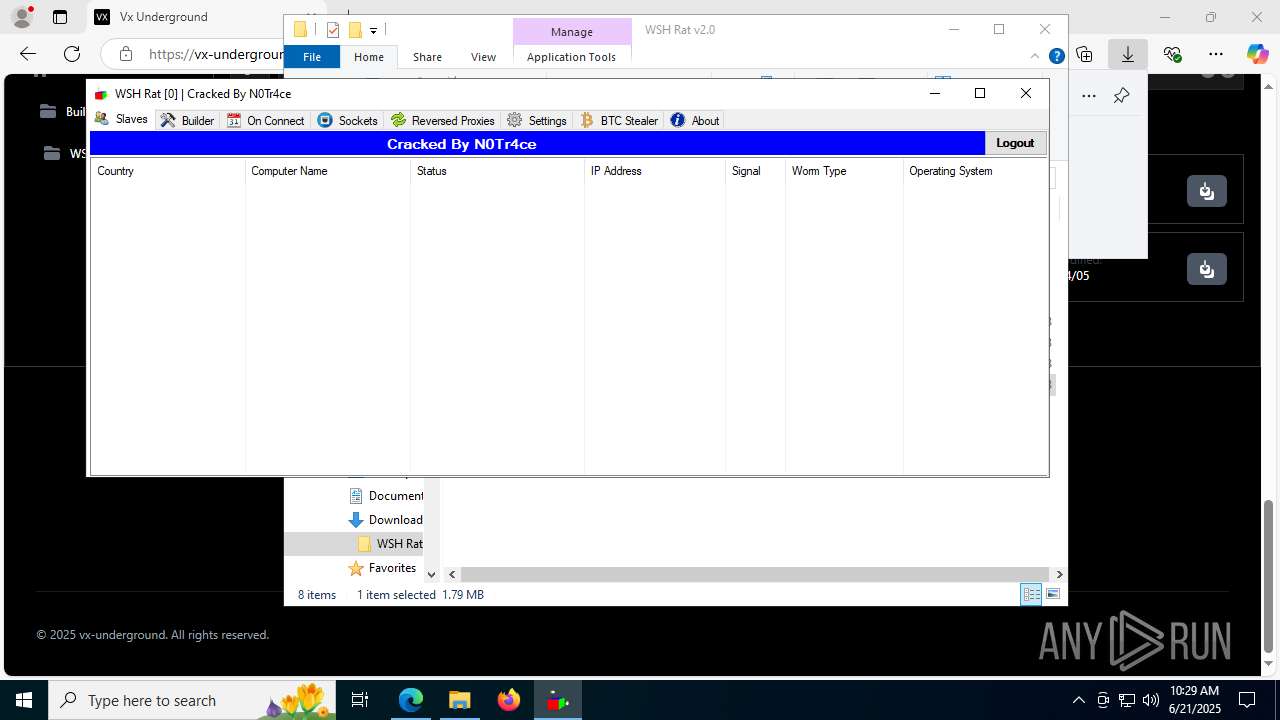
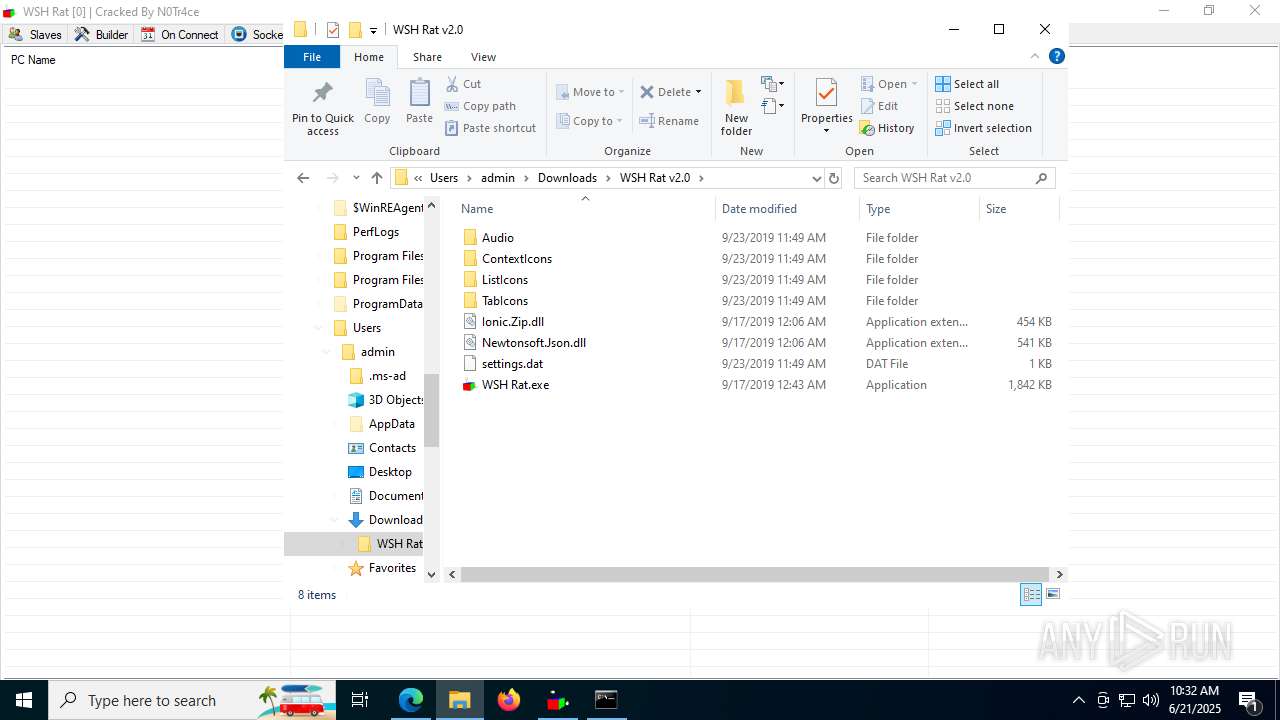
| URL: | https://vx-underground.org/Builders/Vampire |
| Full analysis: | https://app.any.run/tasks/895a2bf1-798d-479f-ab25-9710c66d2aa2 |
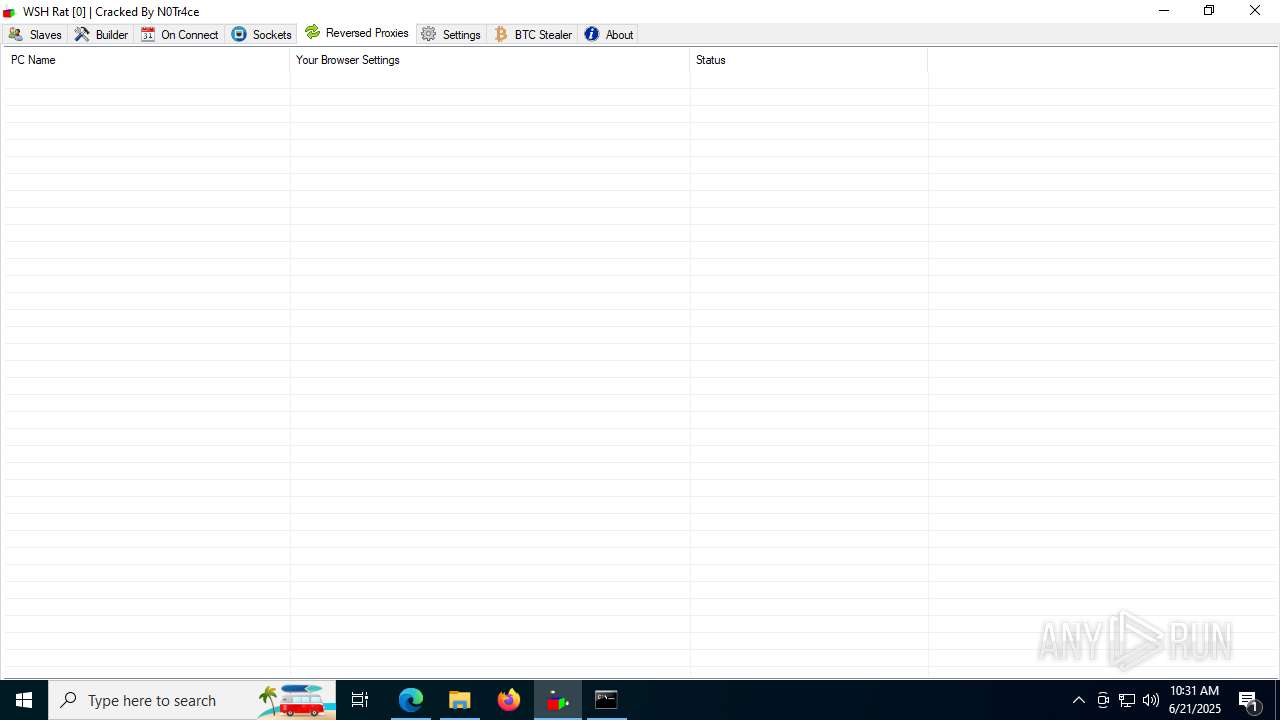
| Verdict: | Malicious activity |
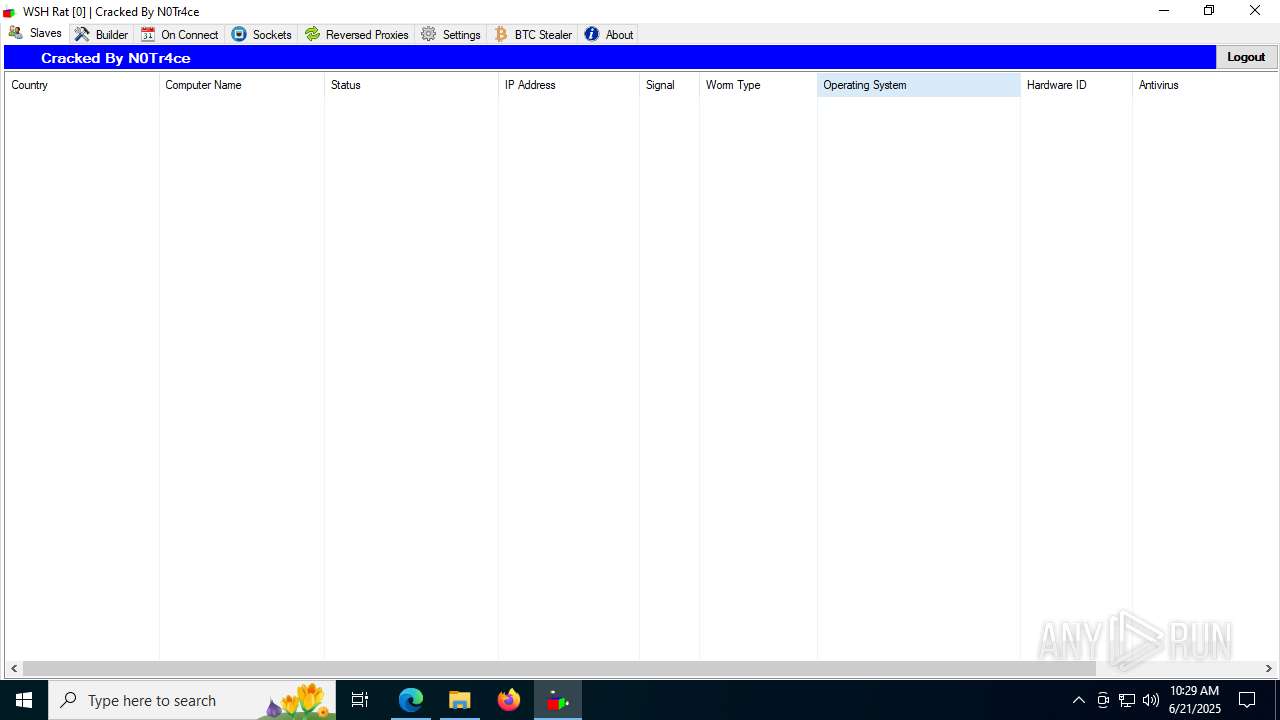
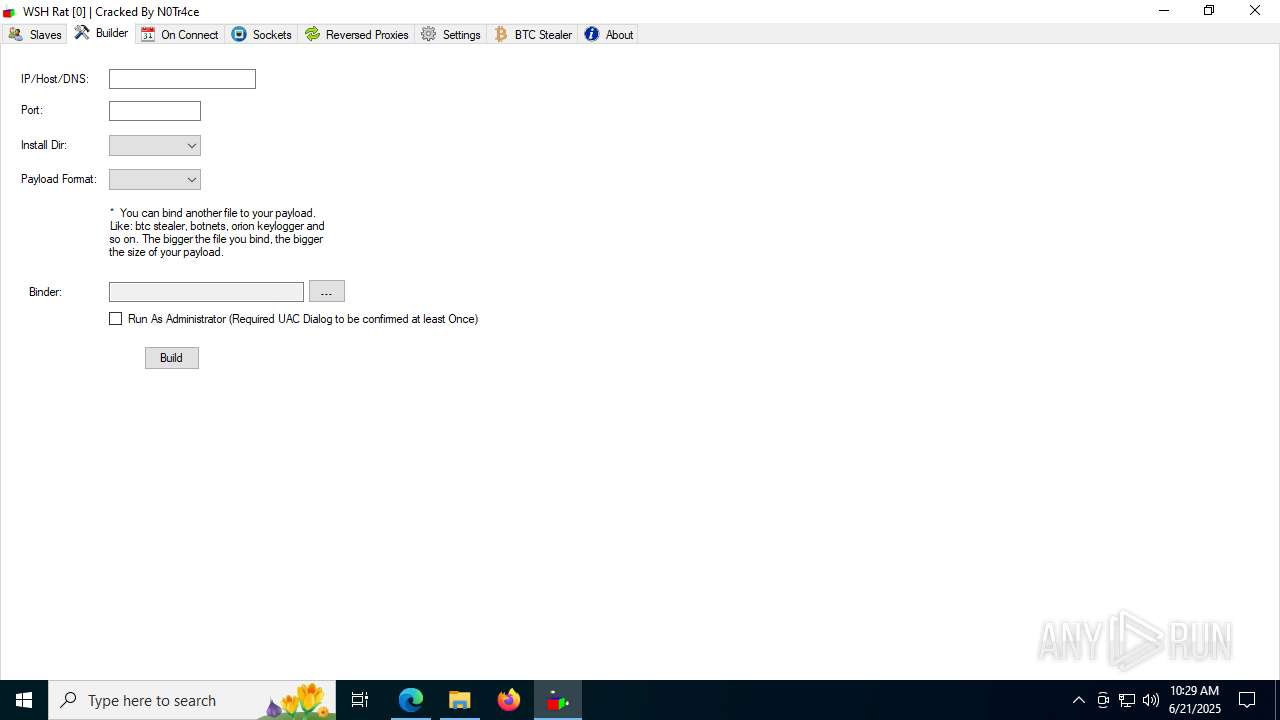
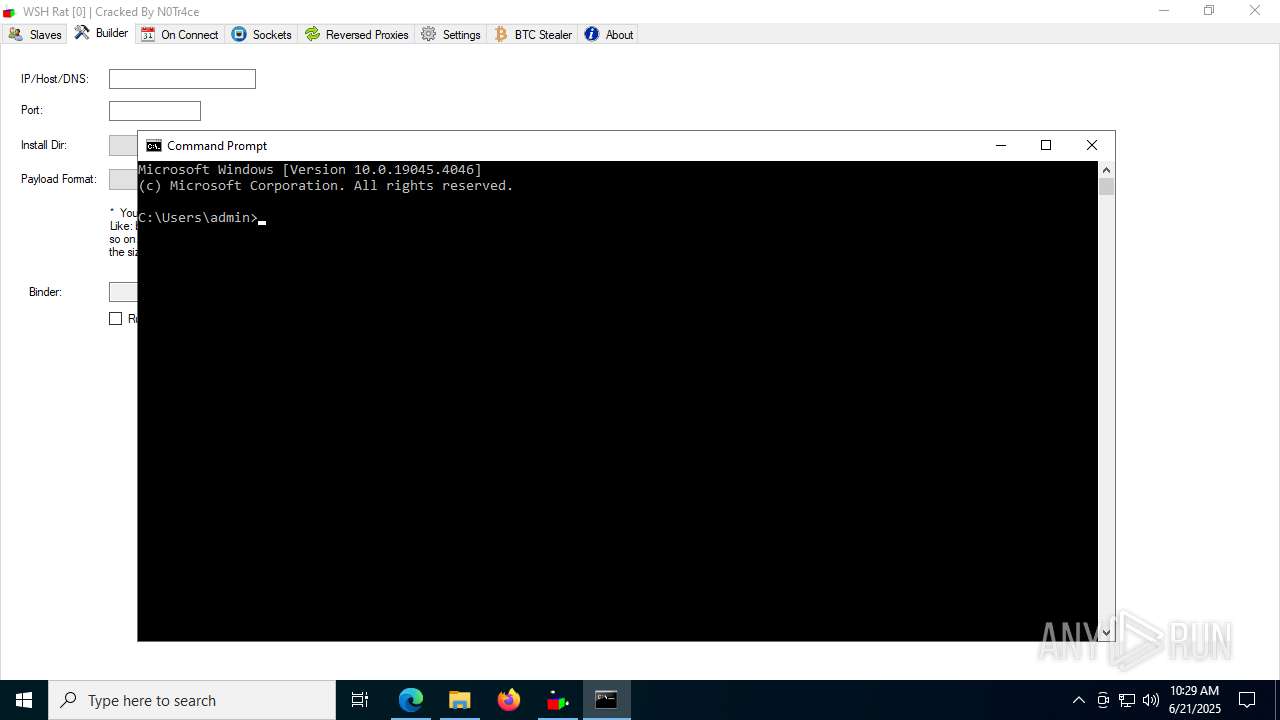
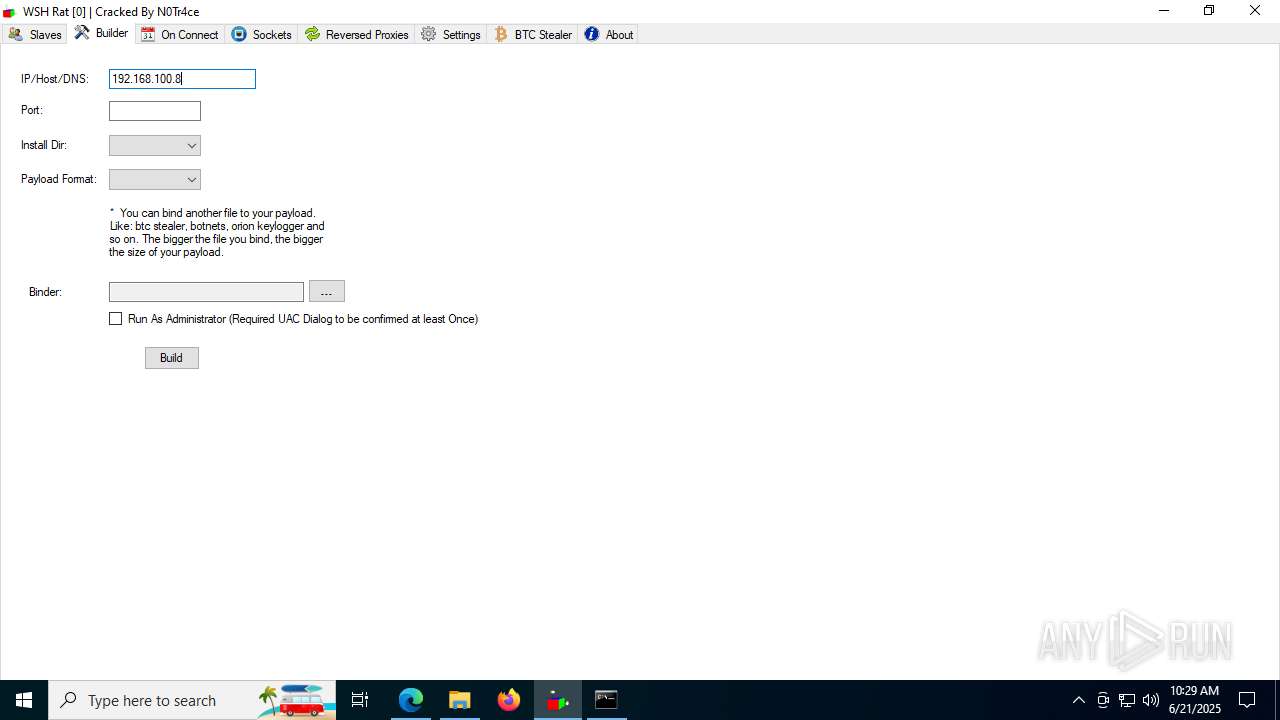
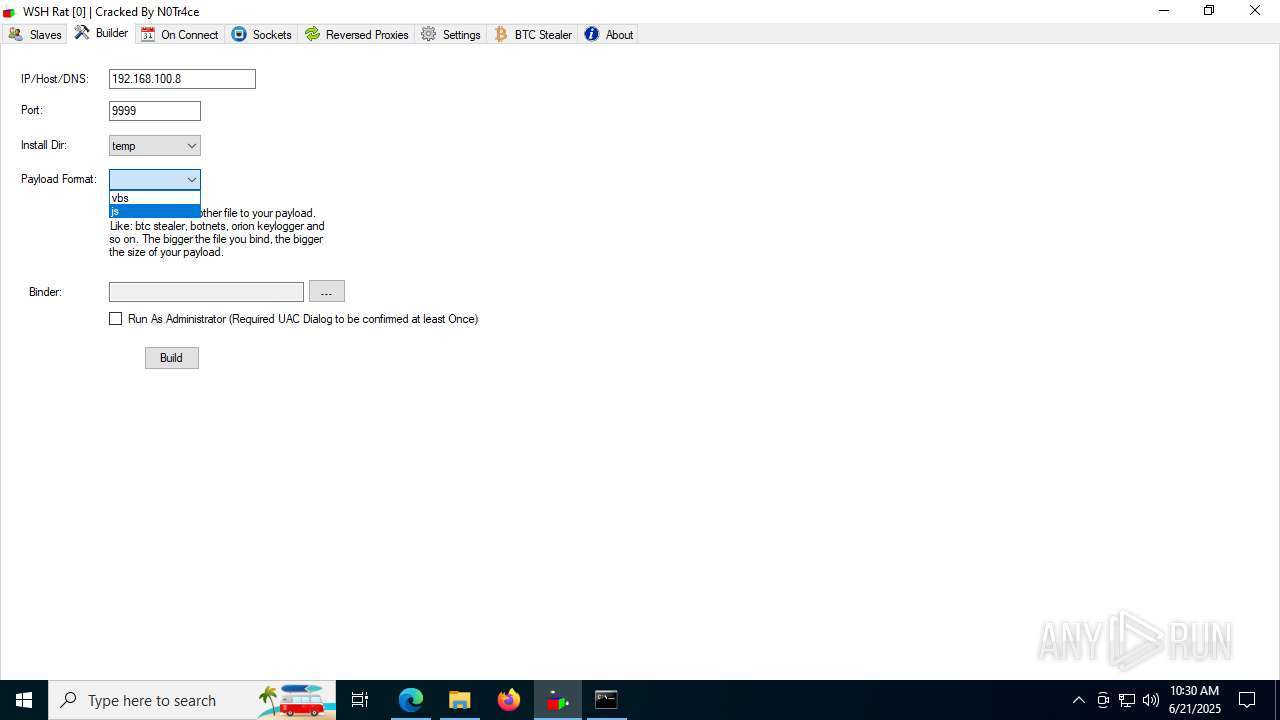
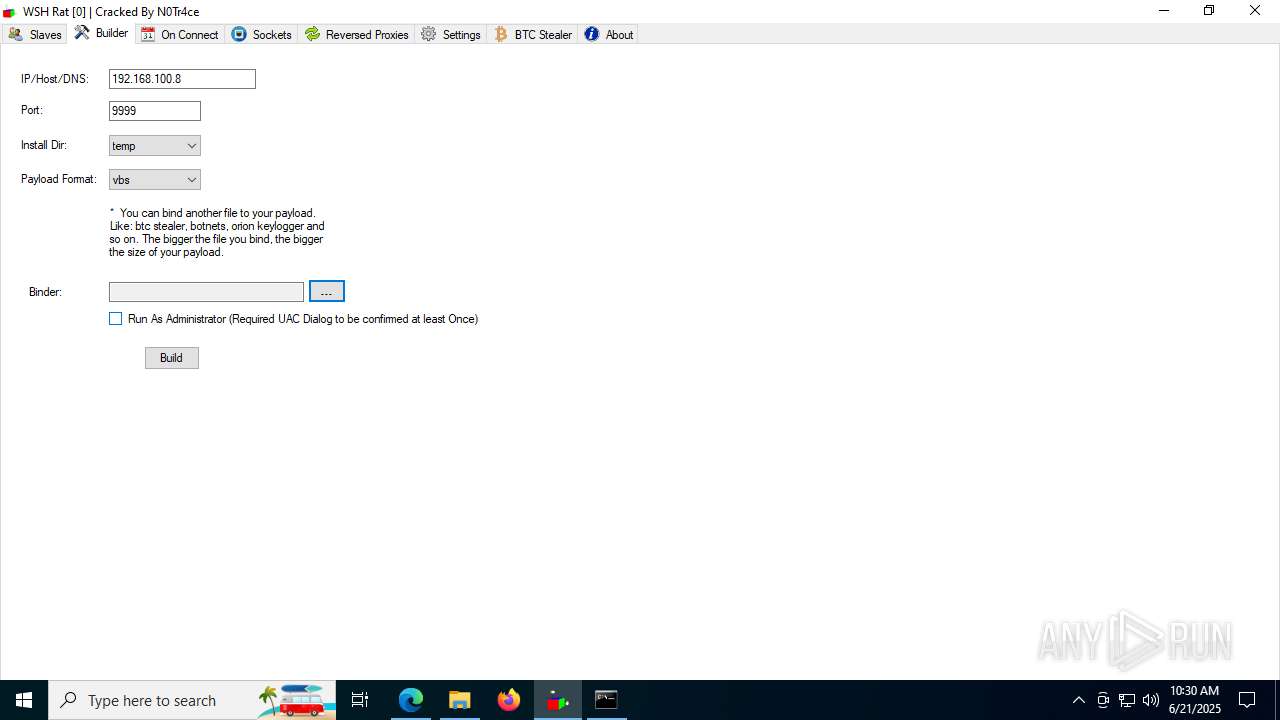
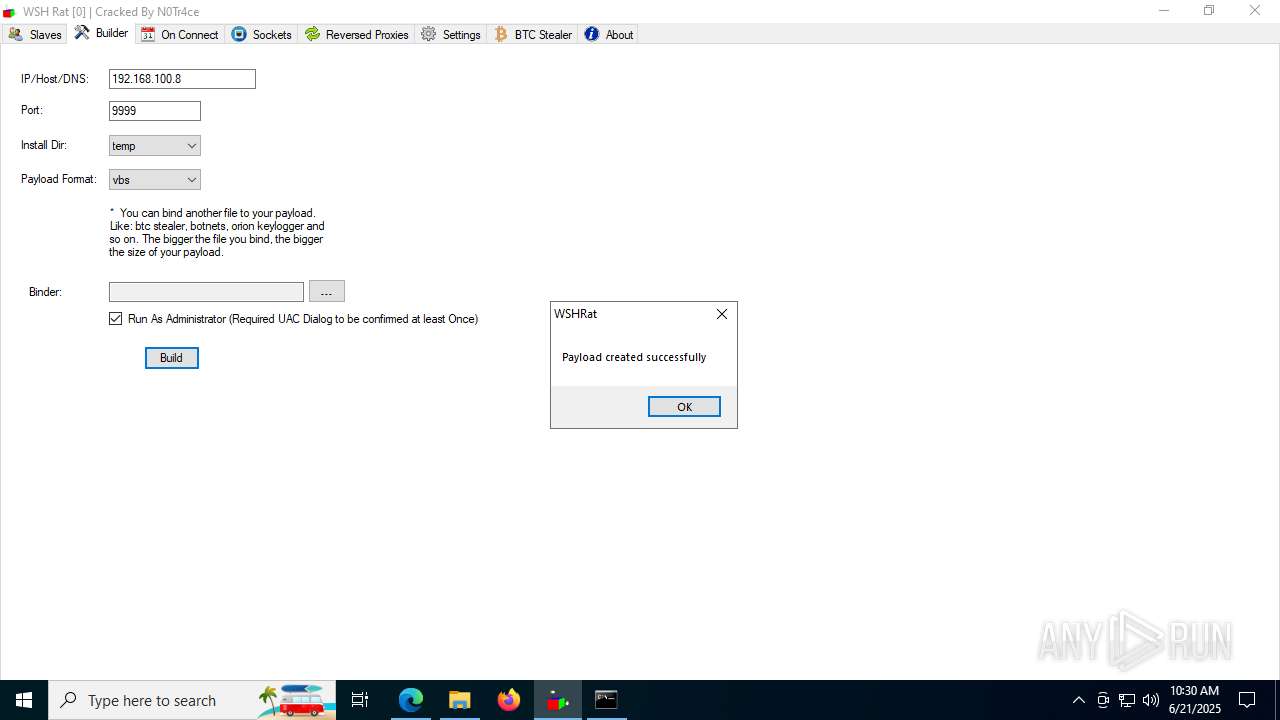
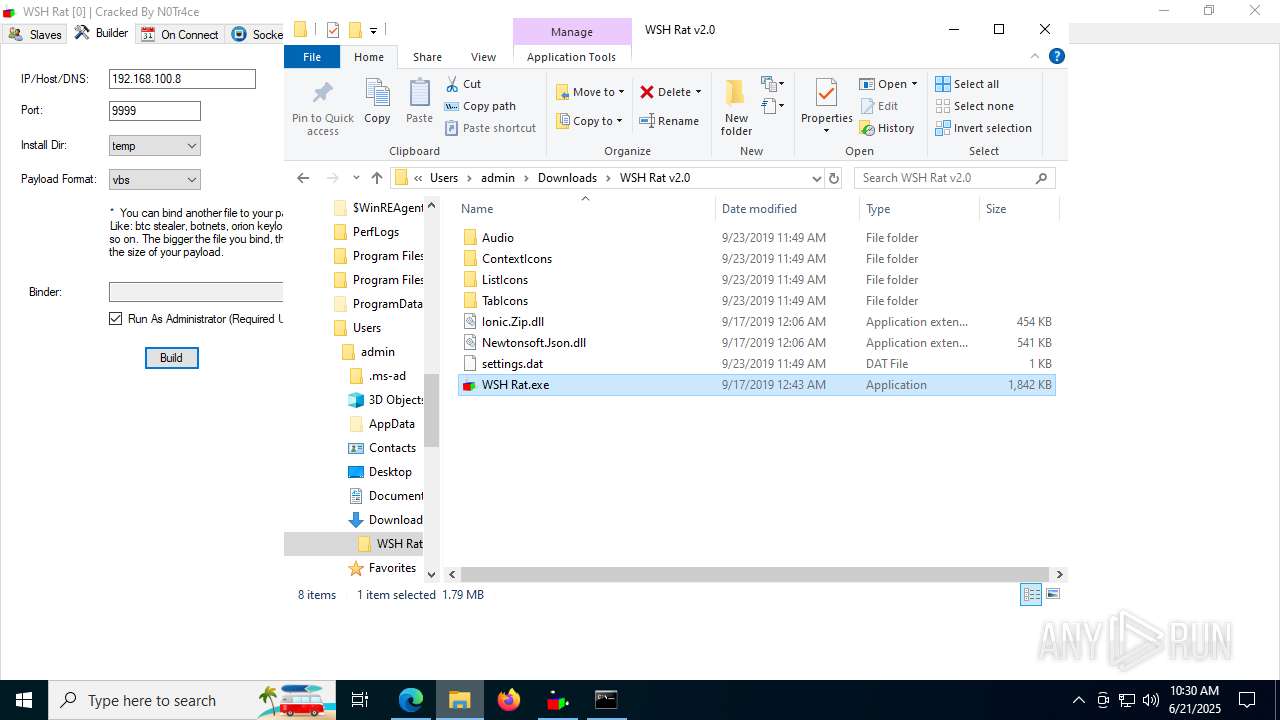
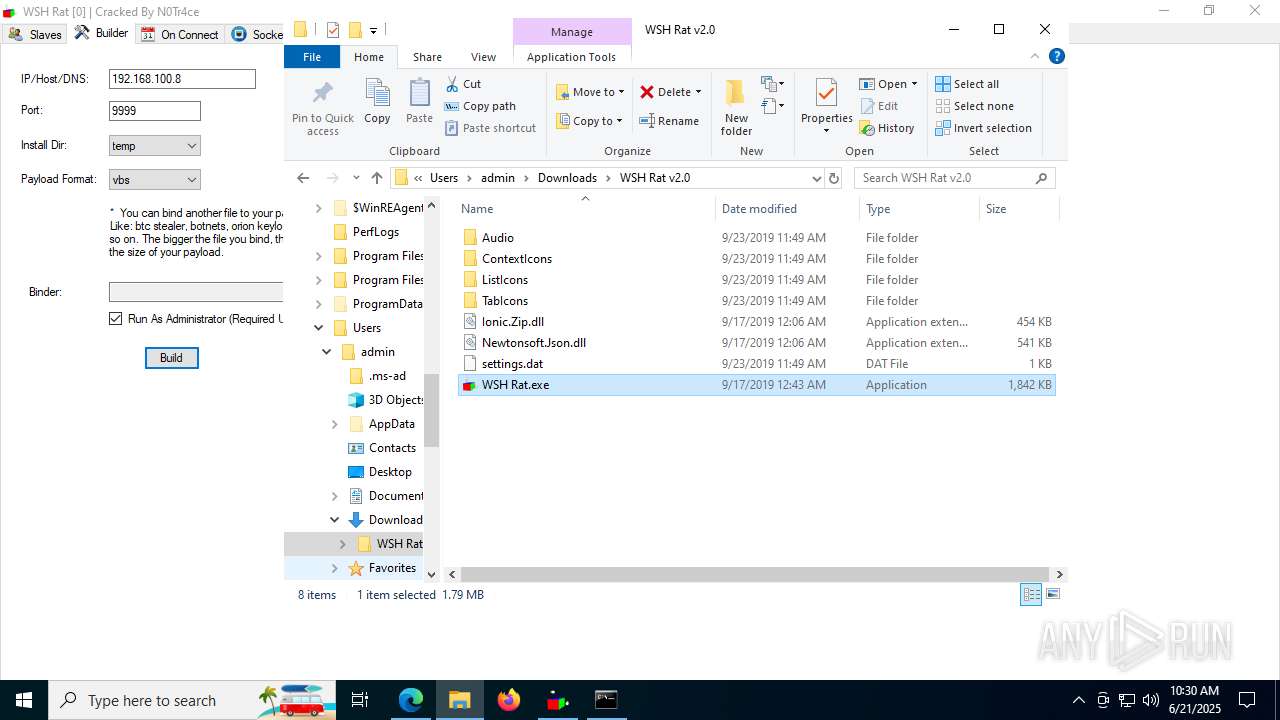
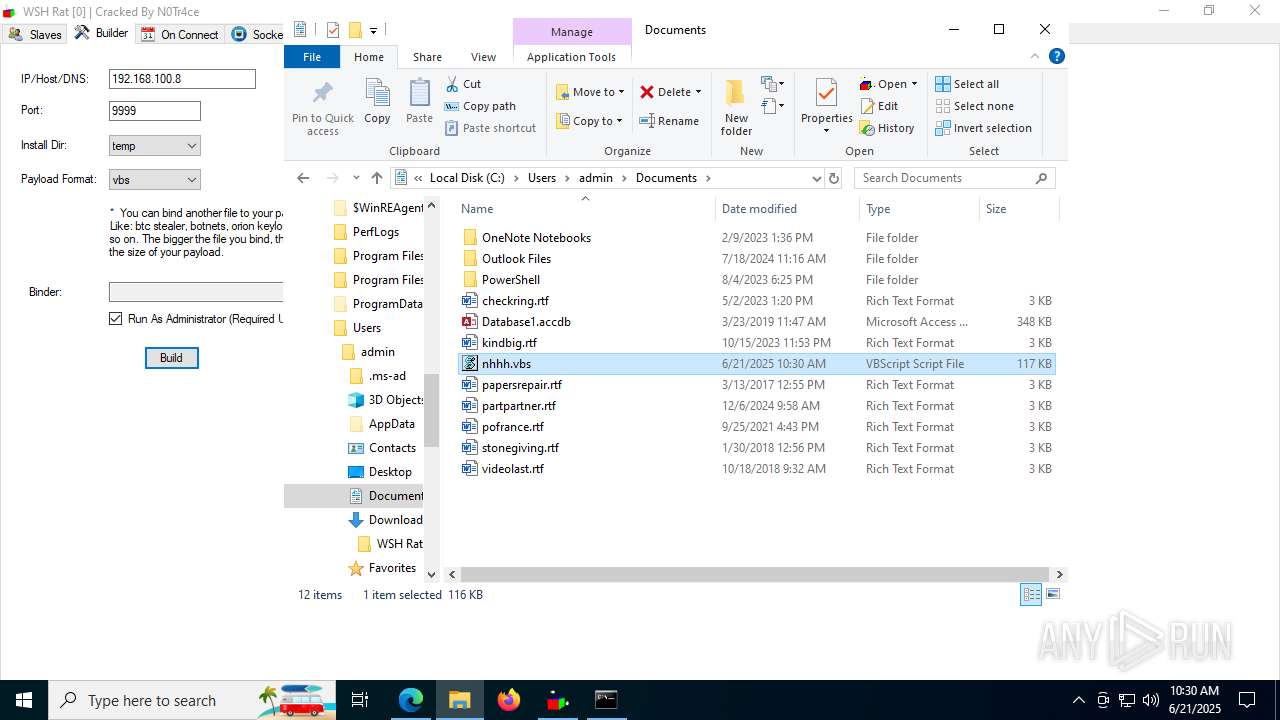
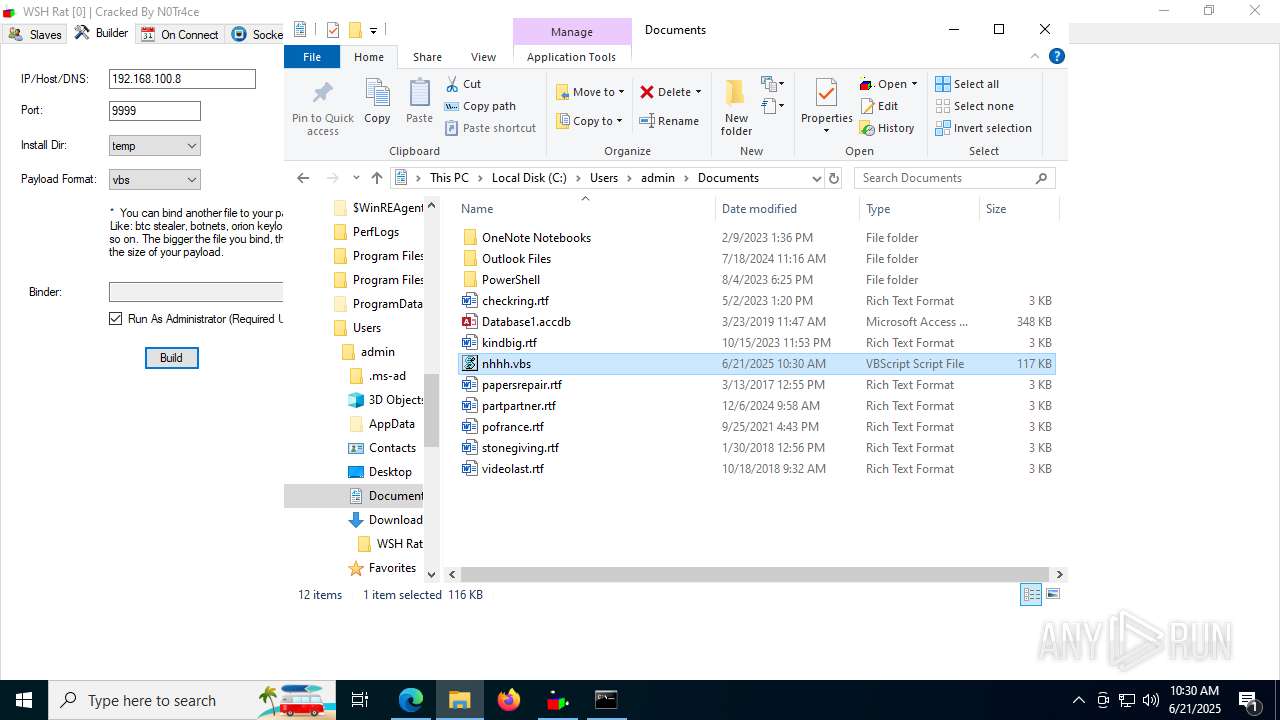
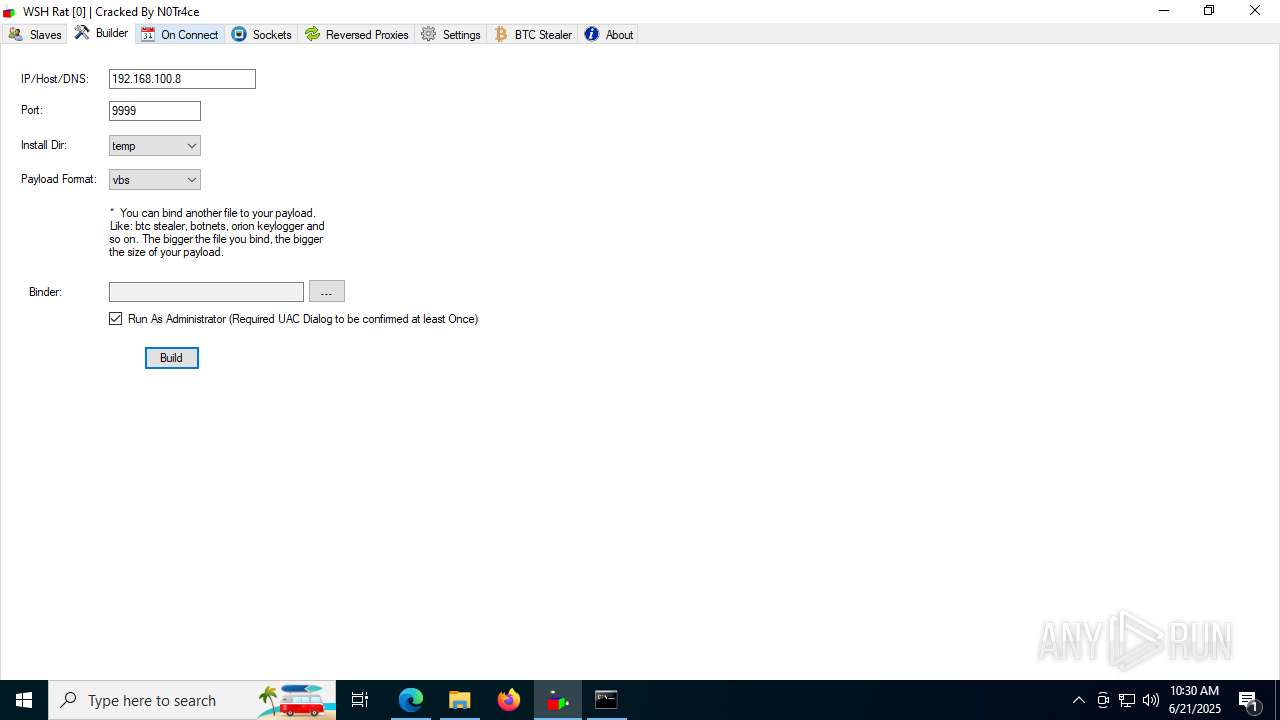
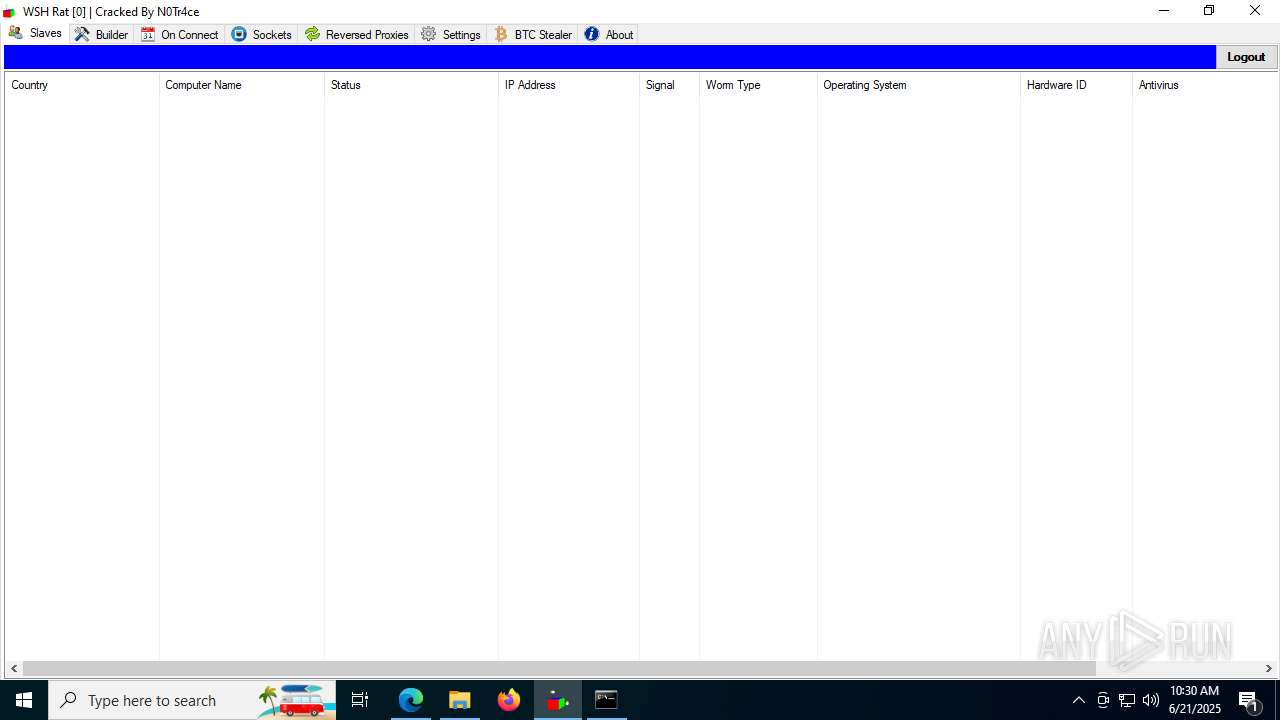
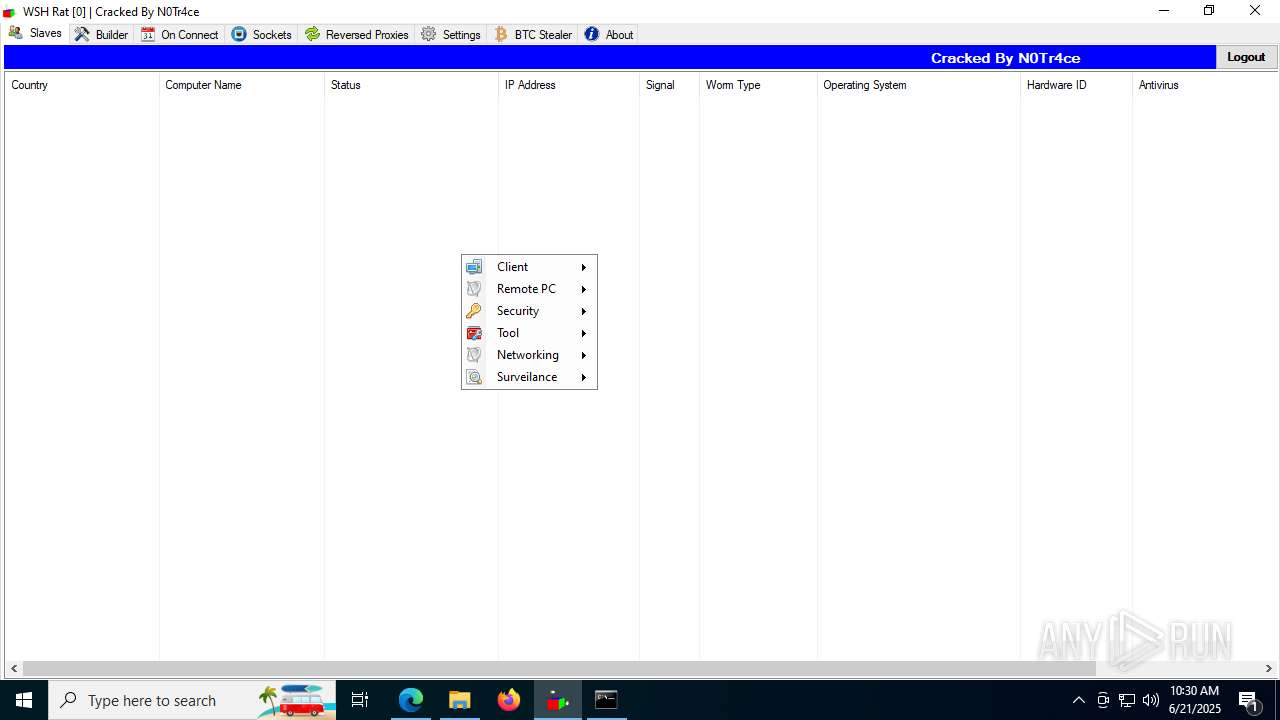
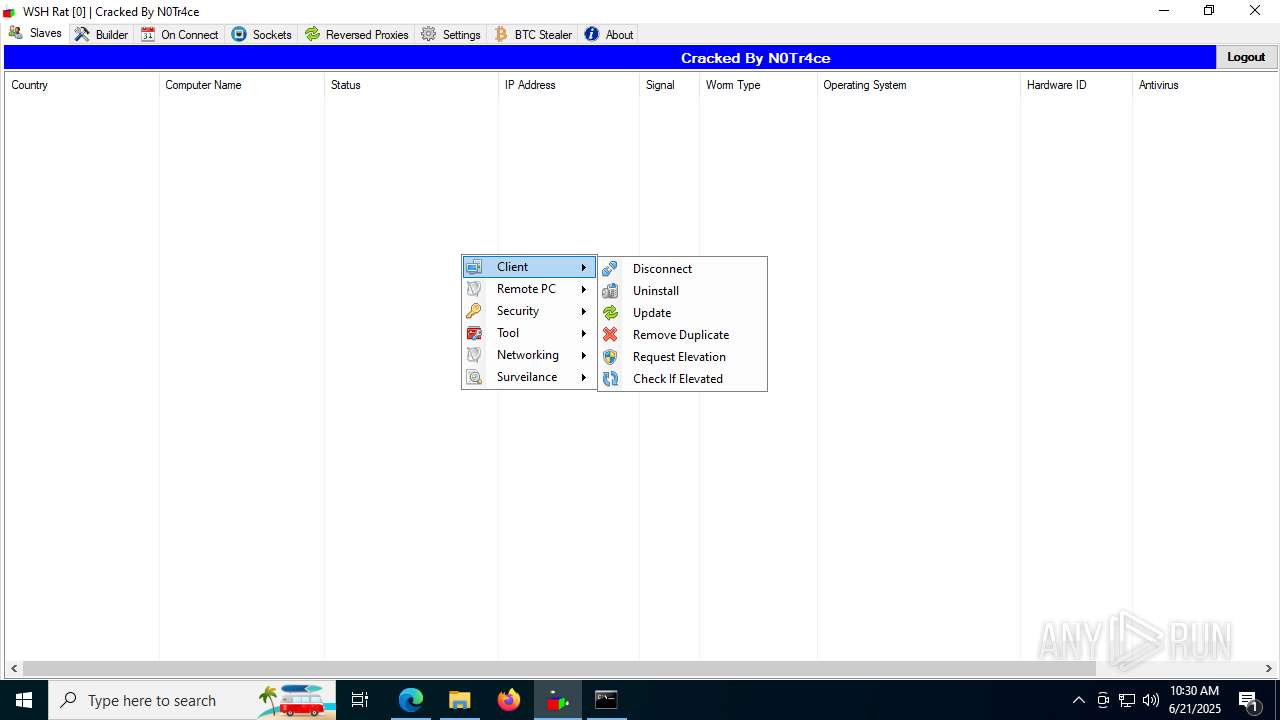
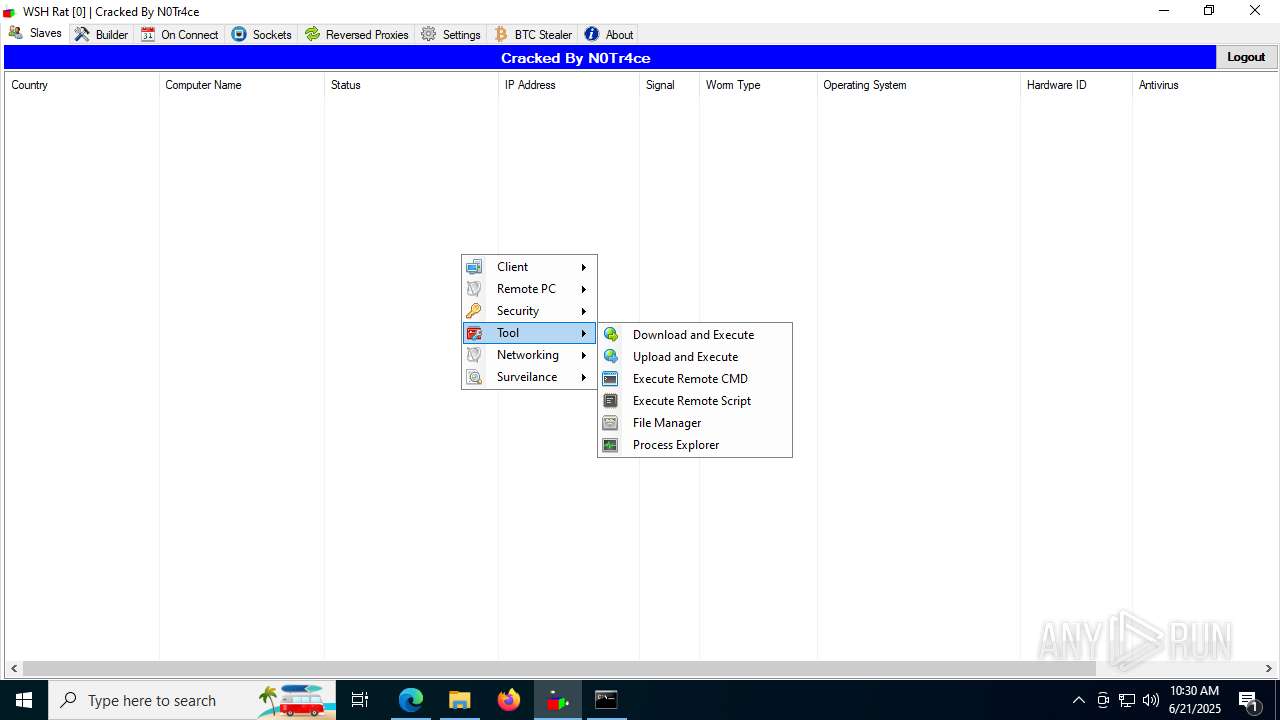
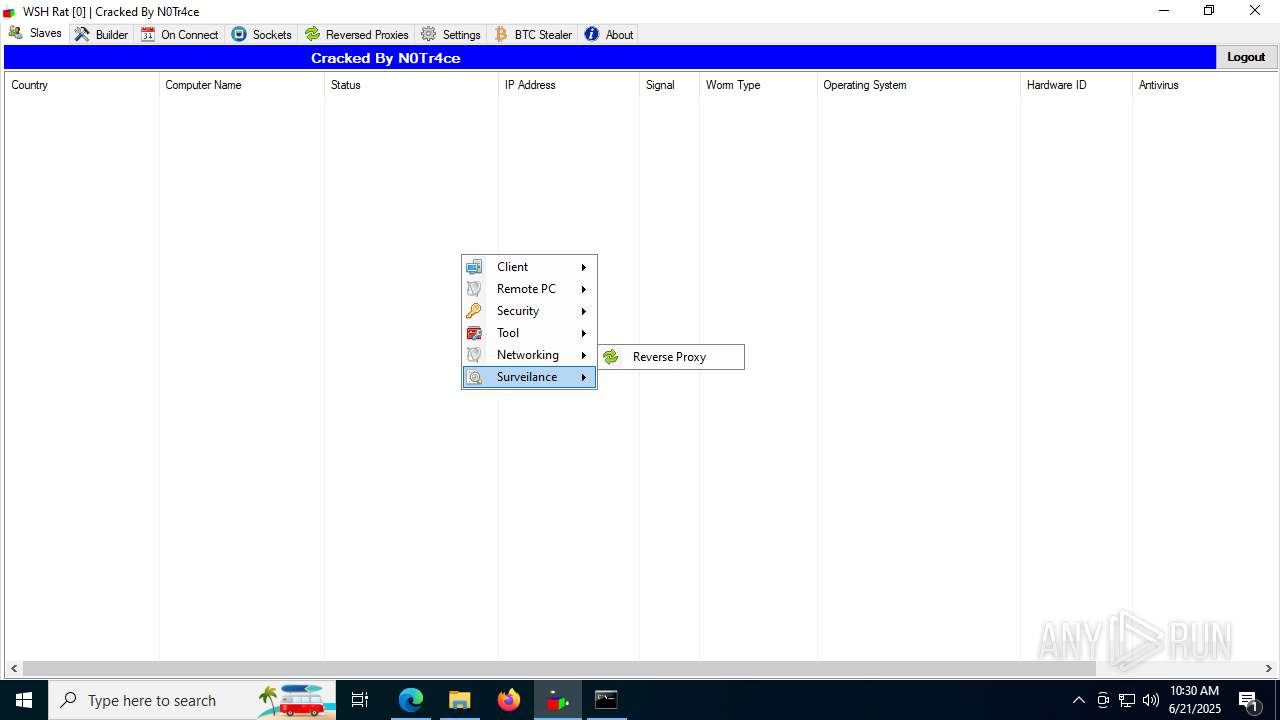
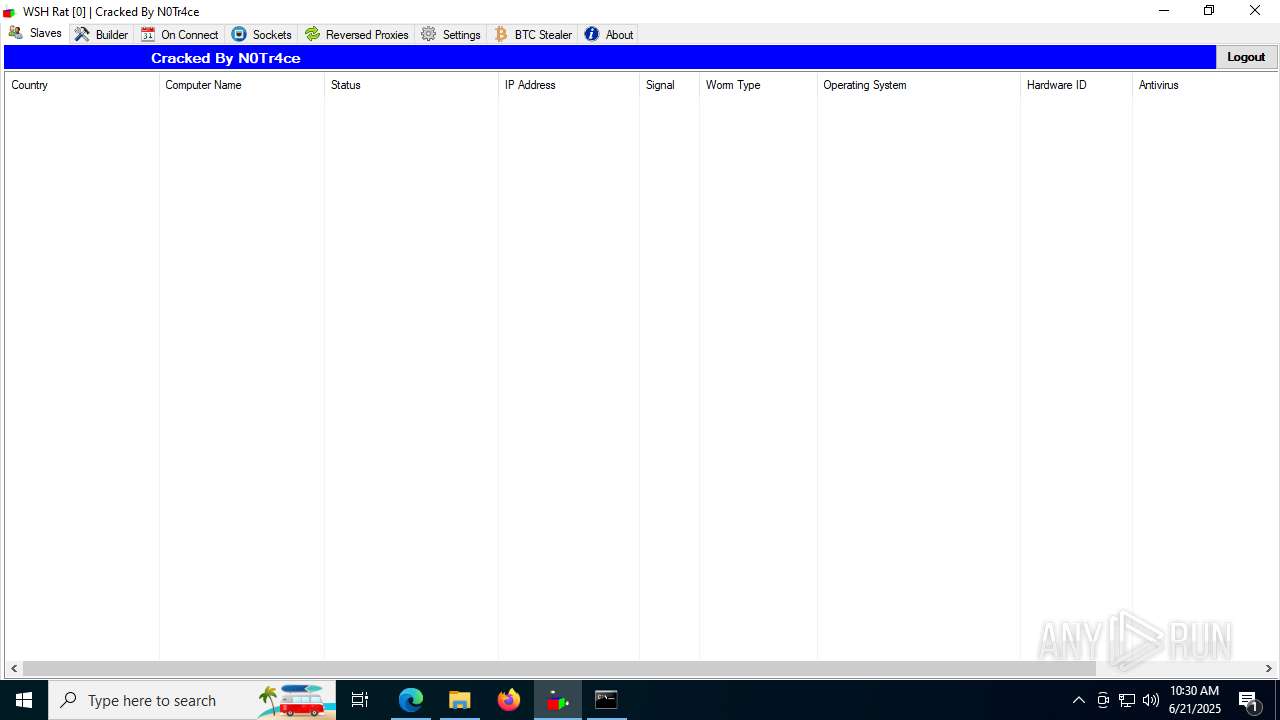
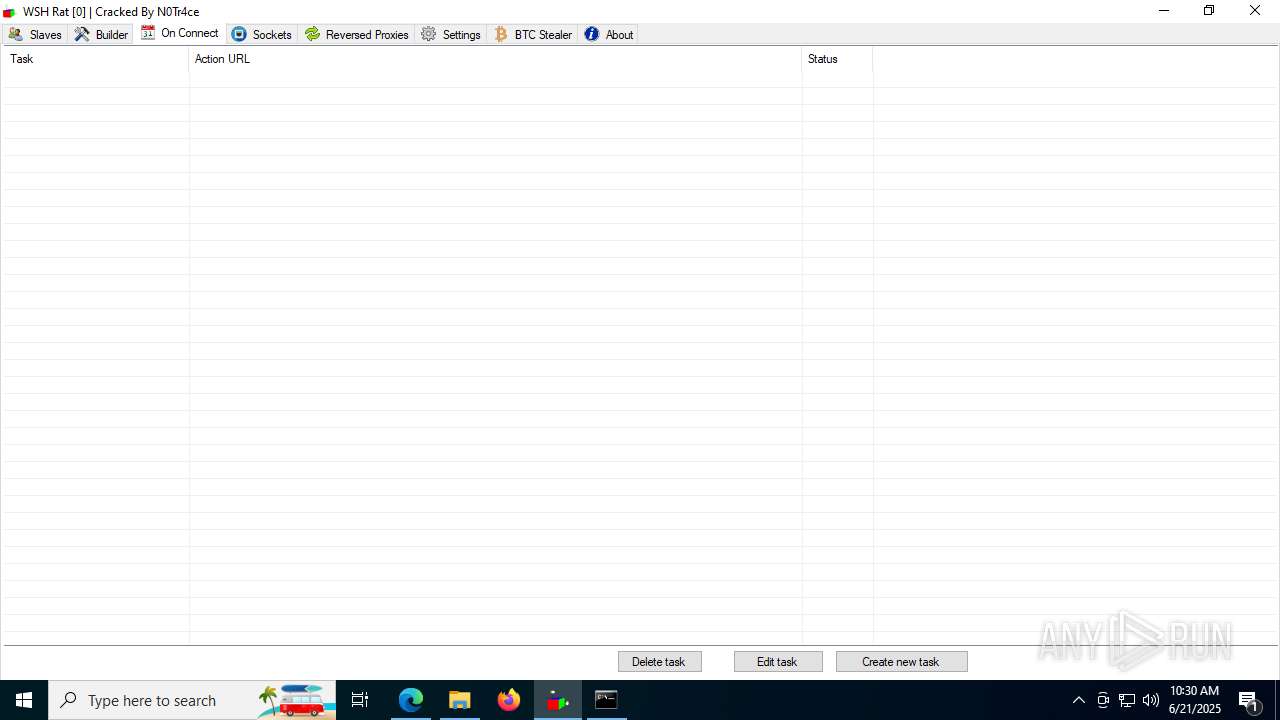
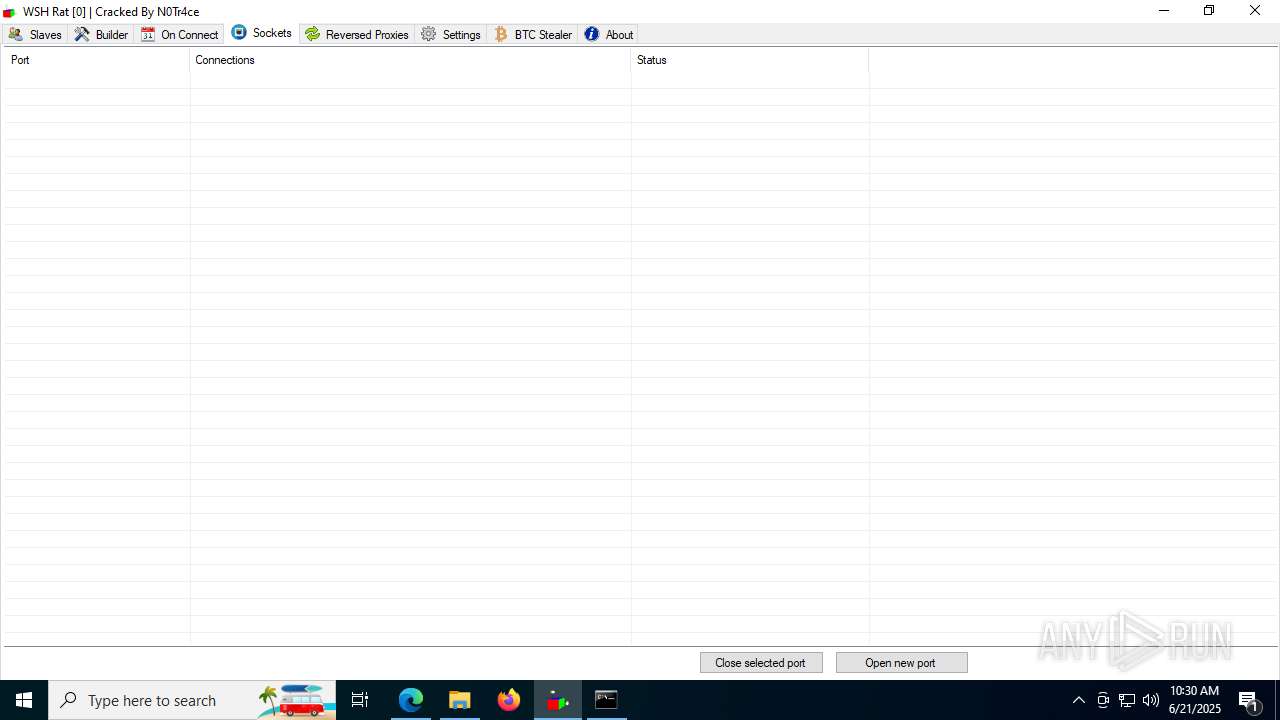
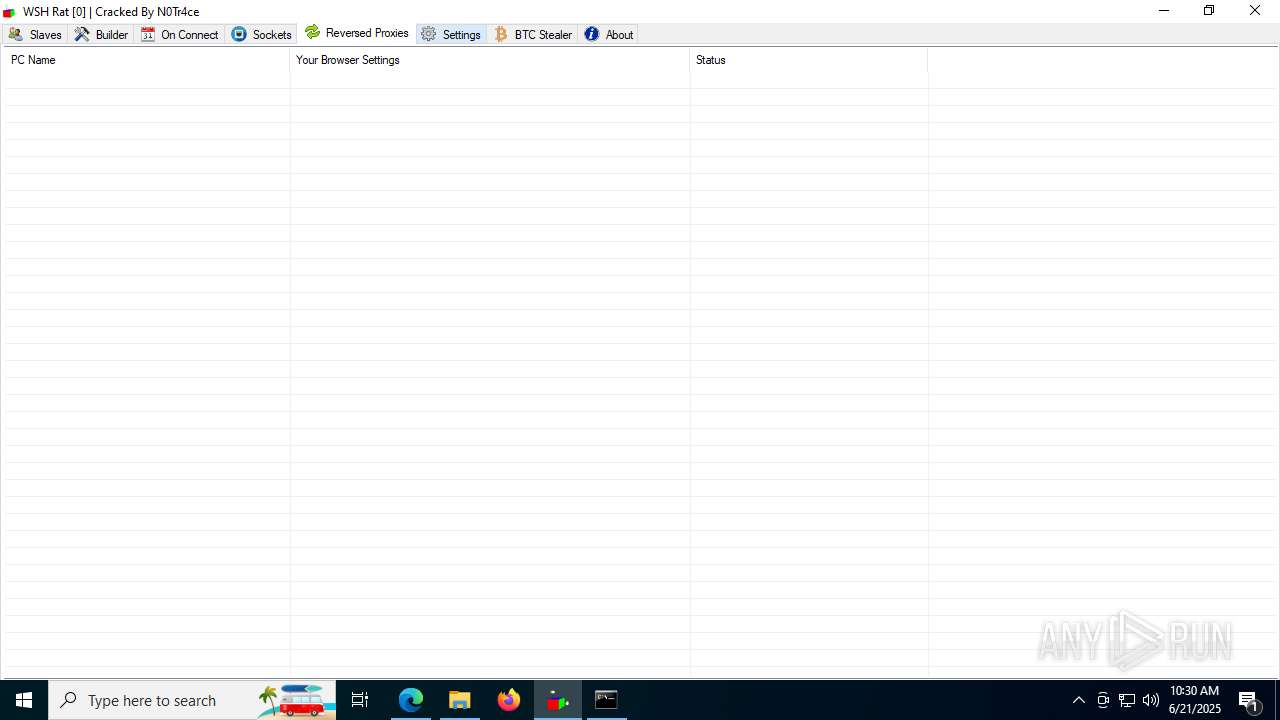
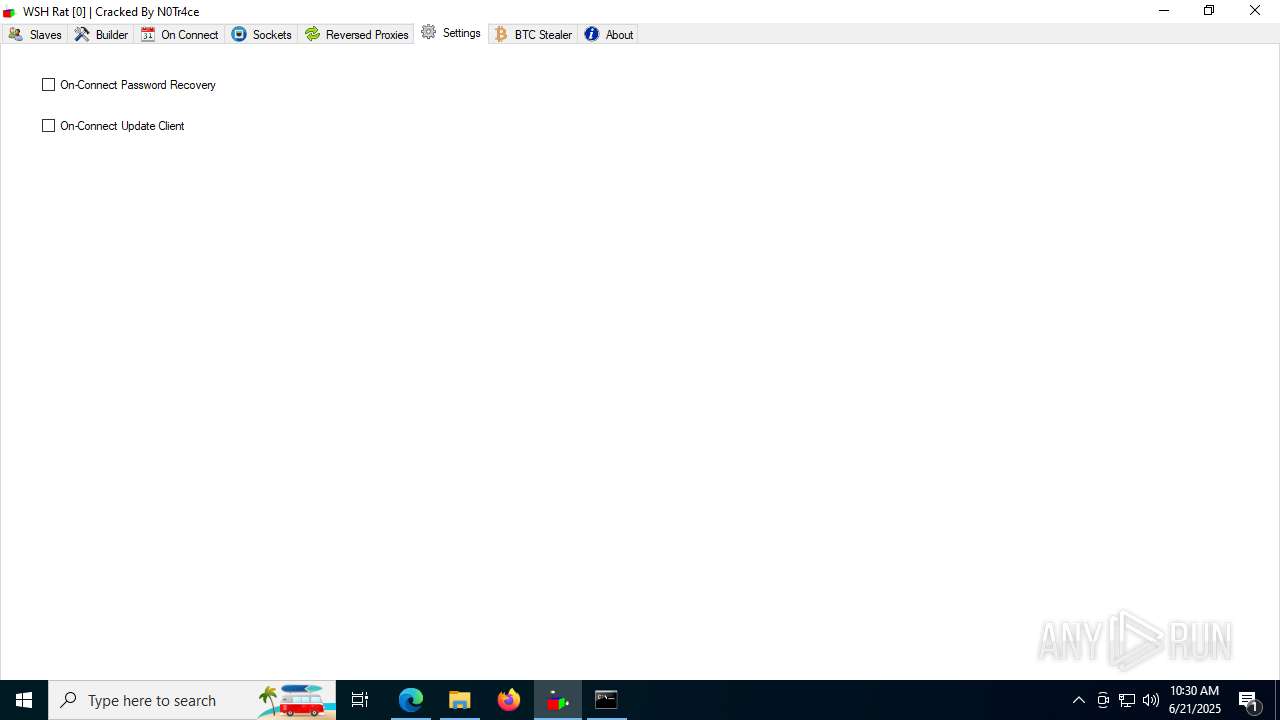
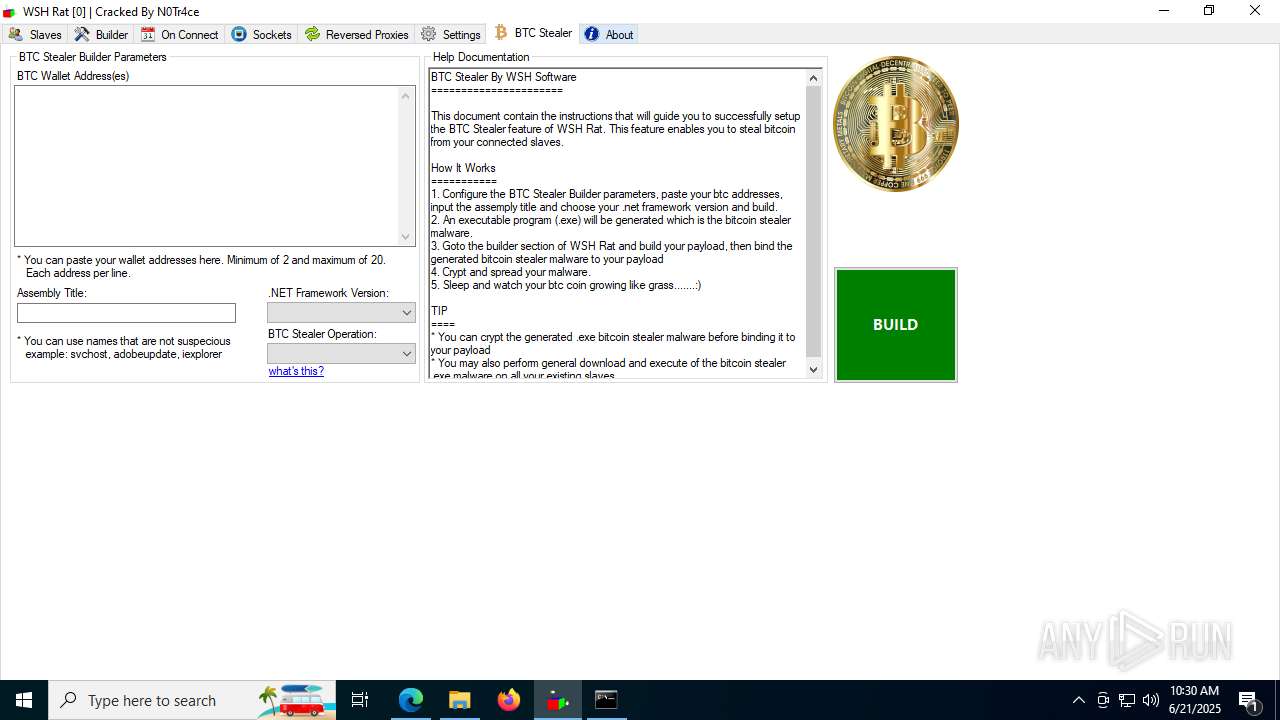
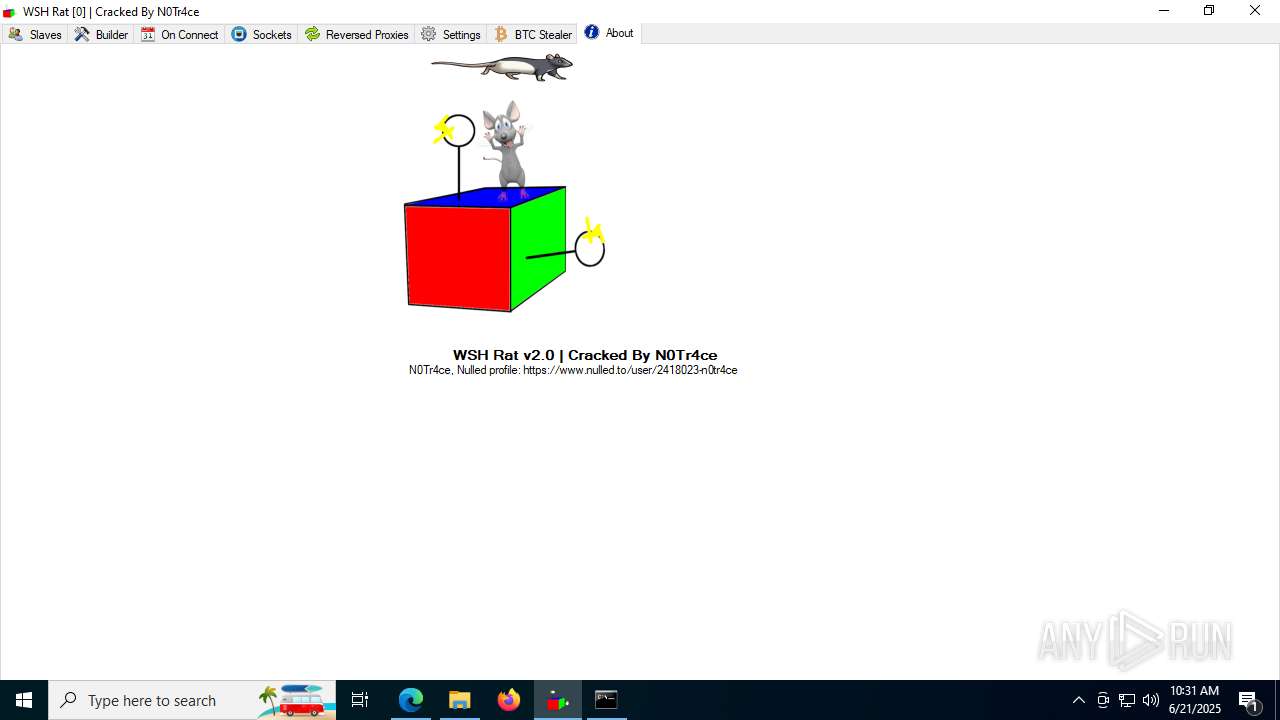
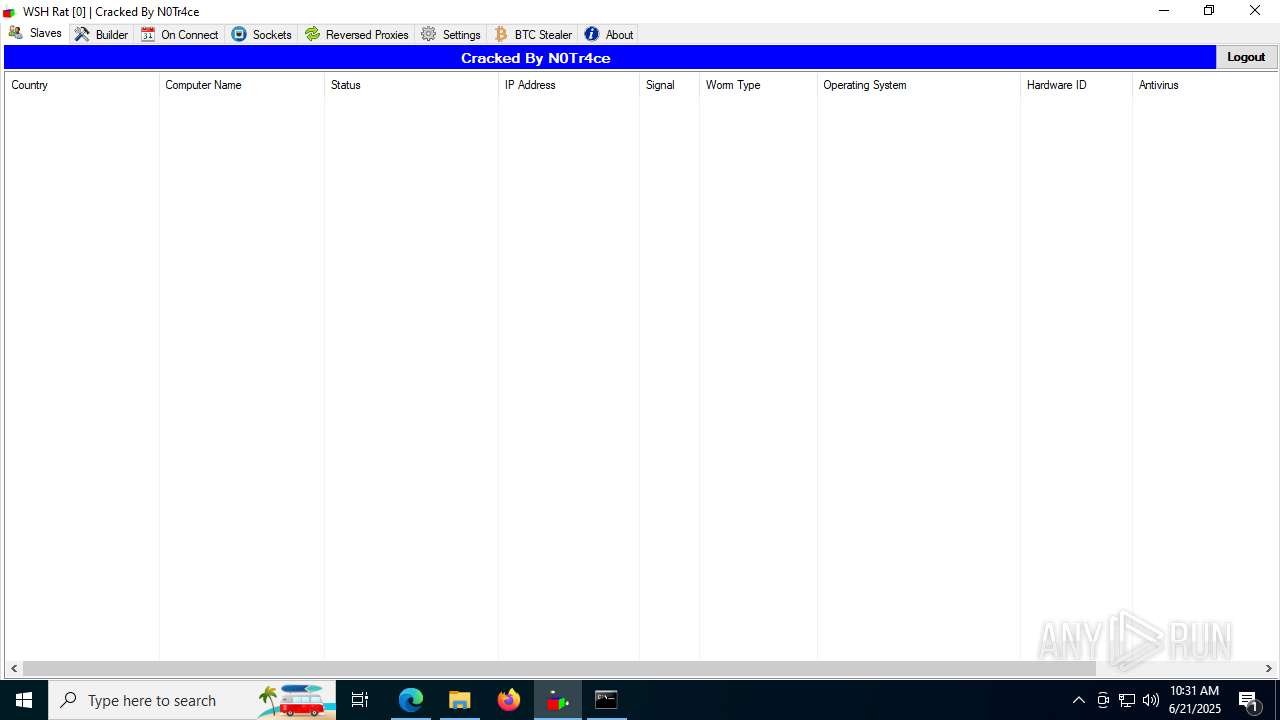
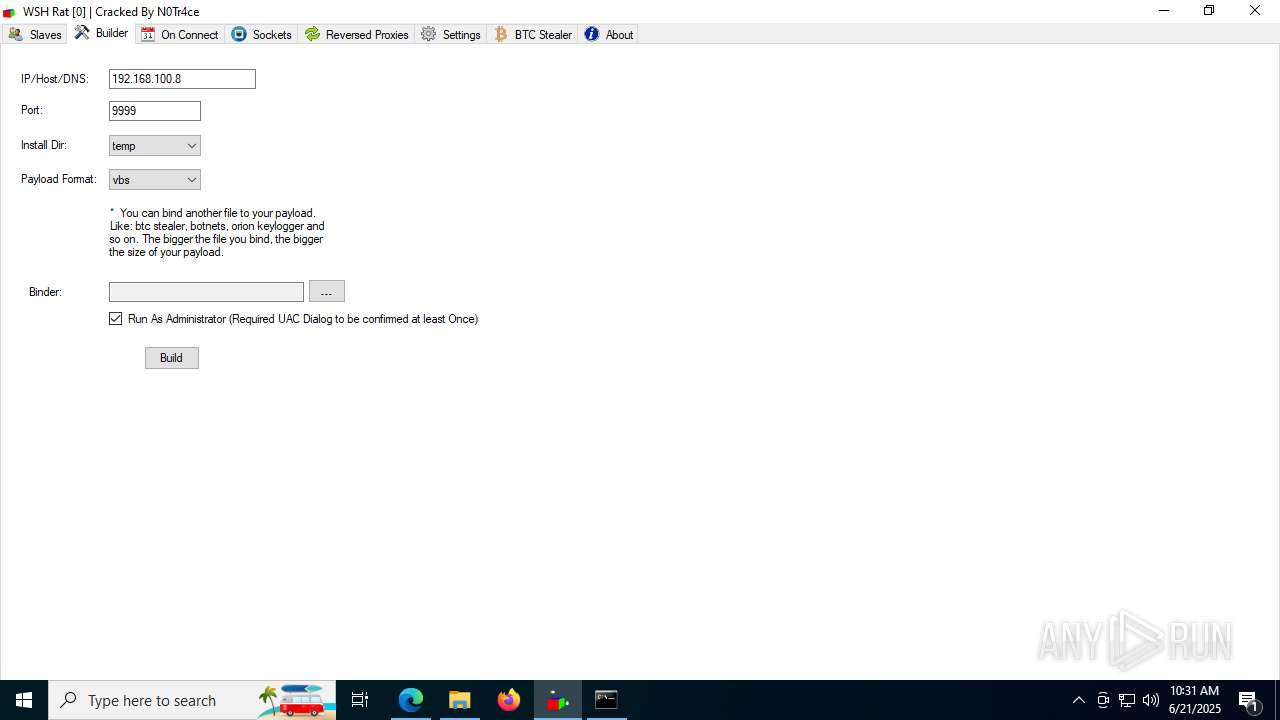
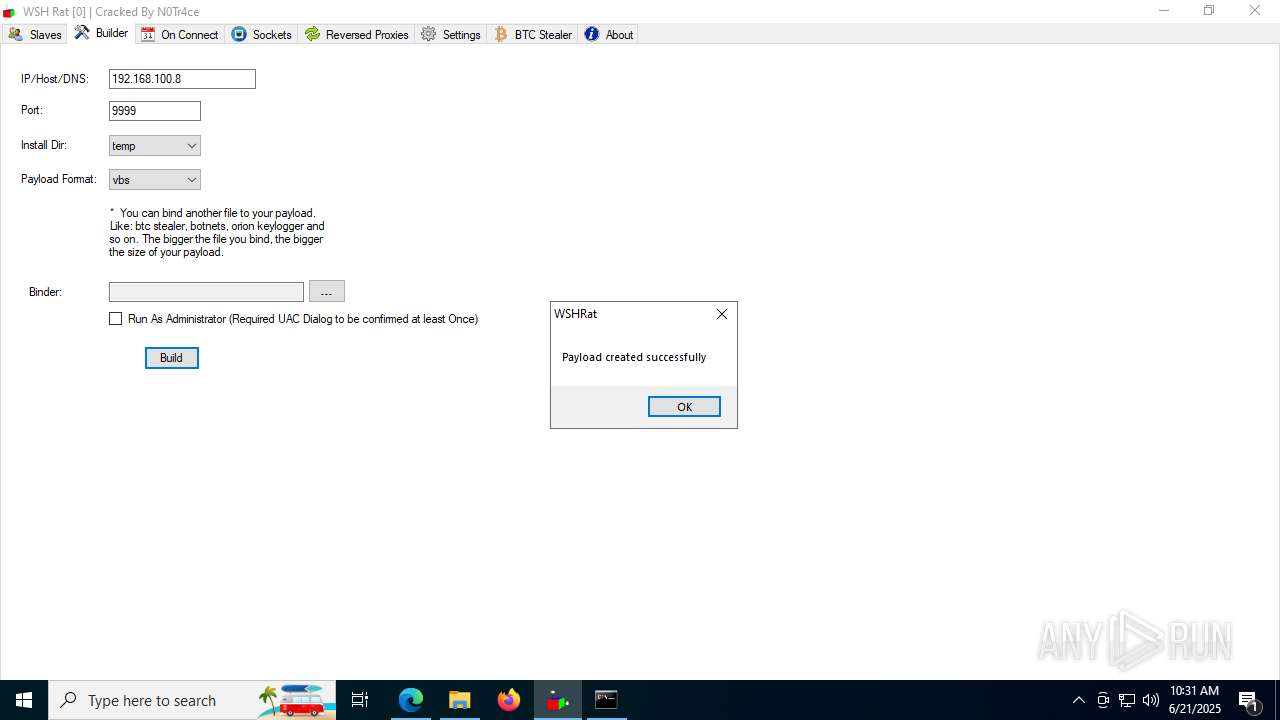
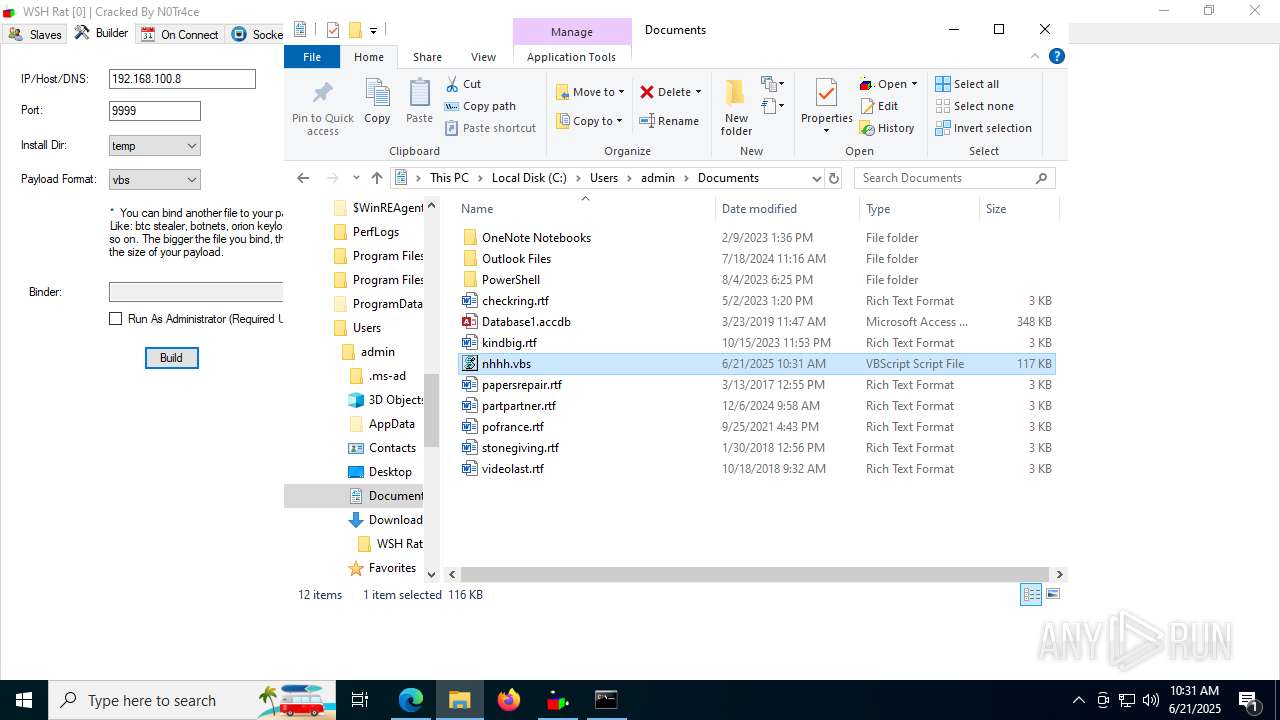
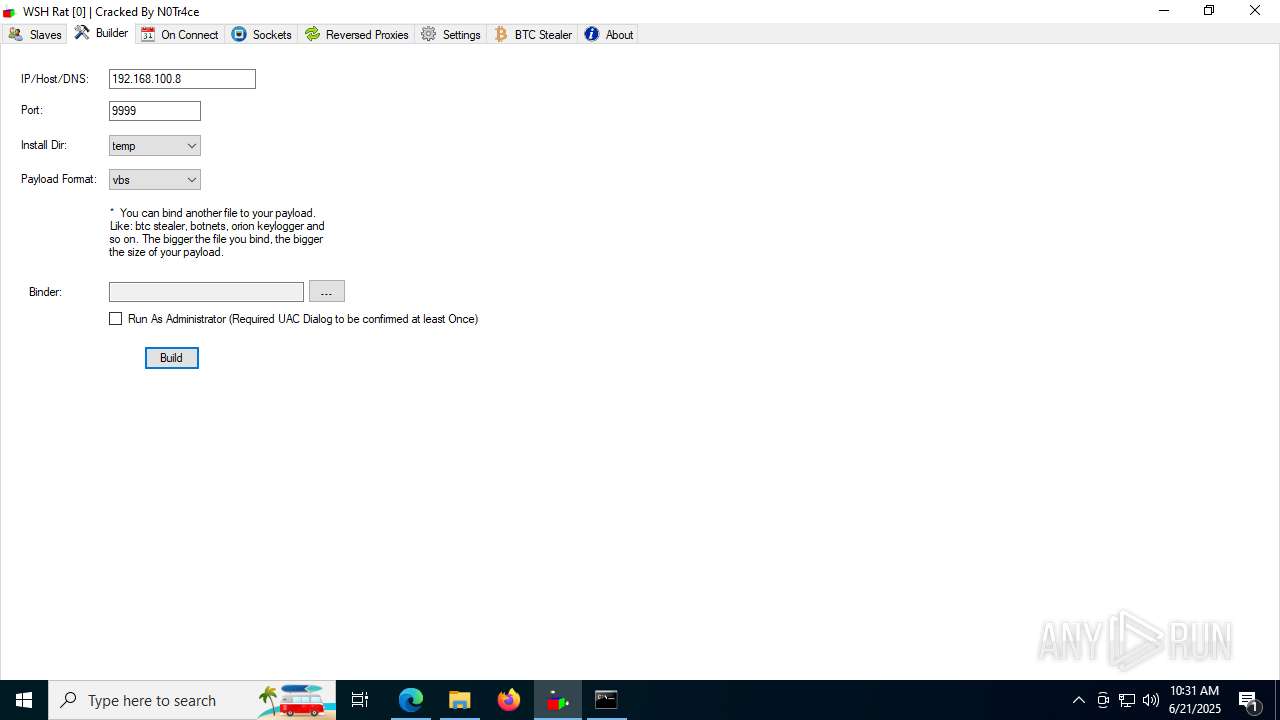
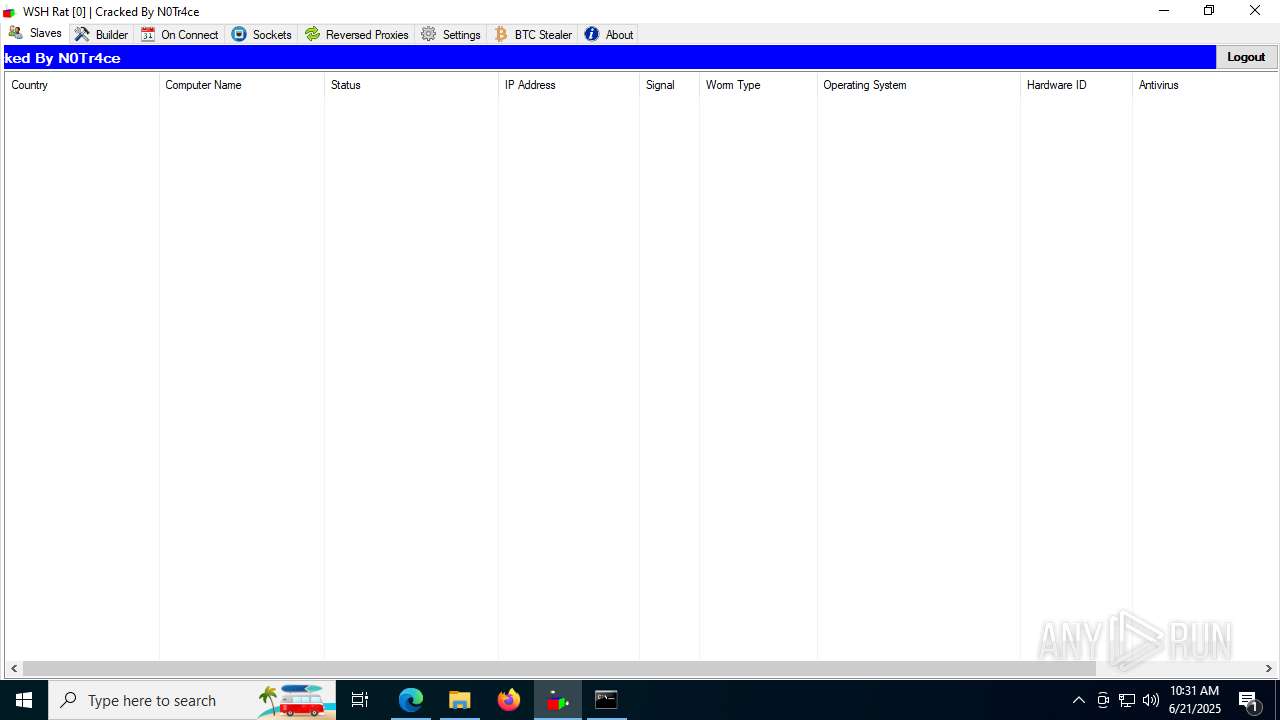
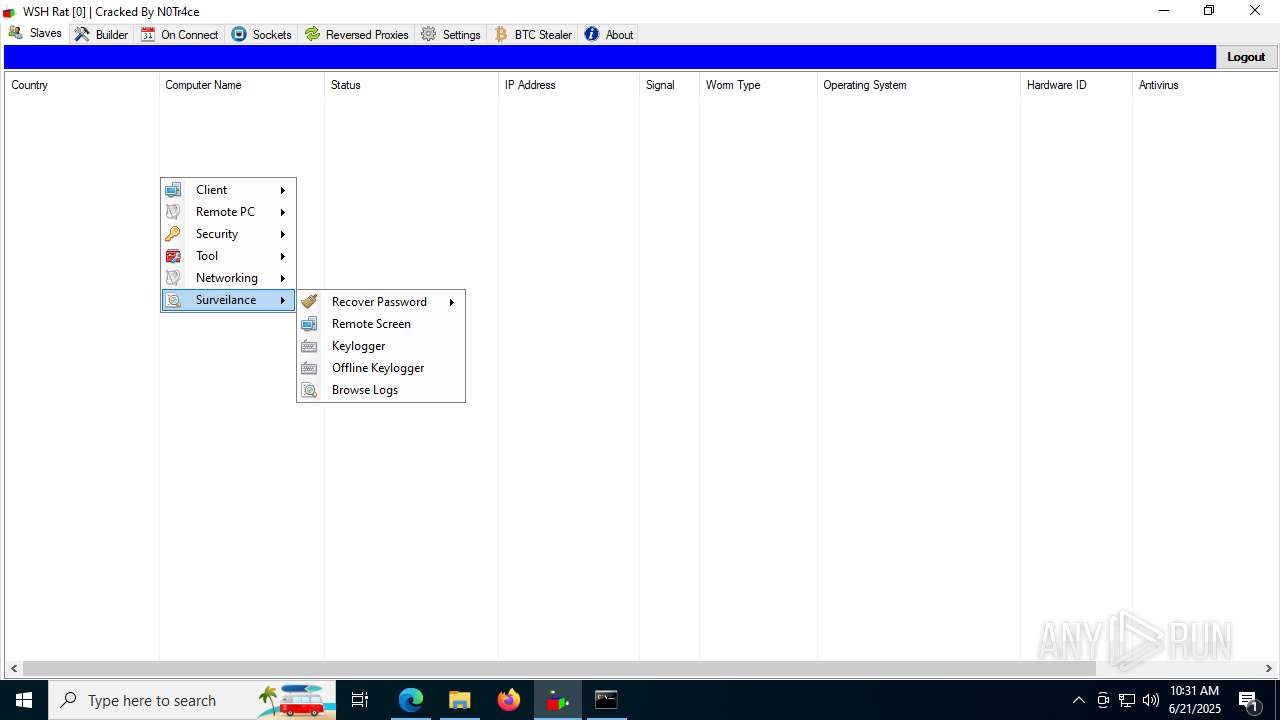
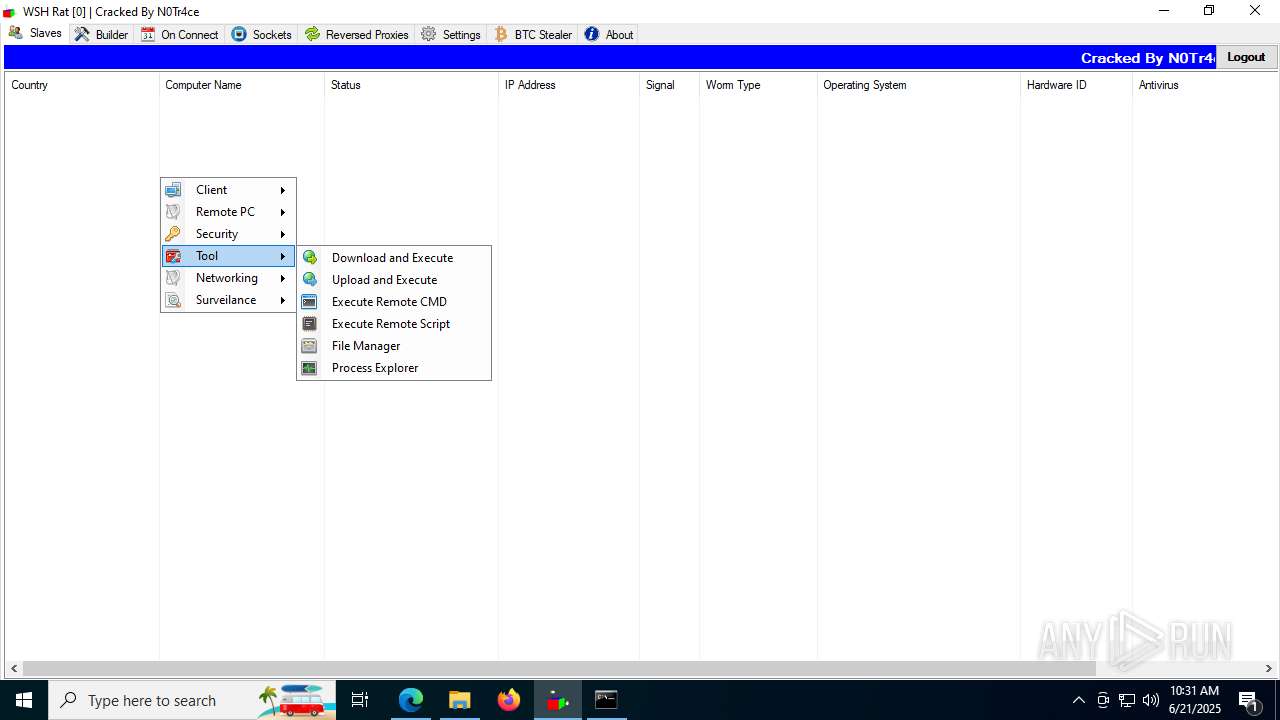
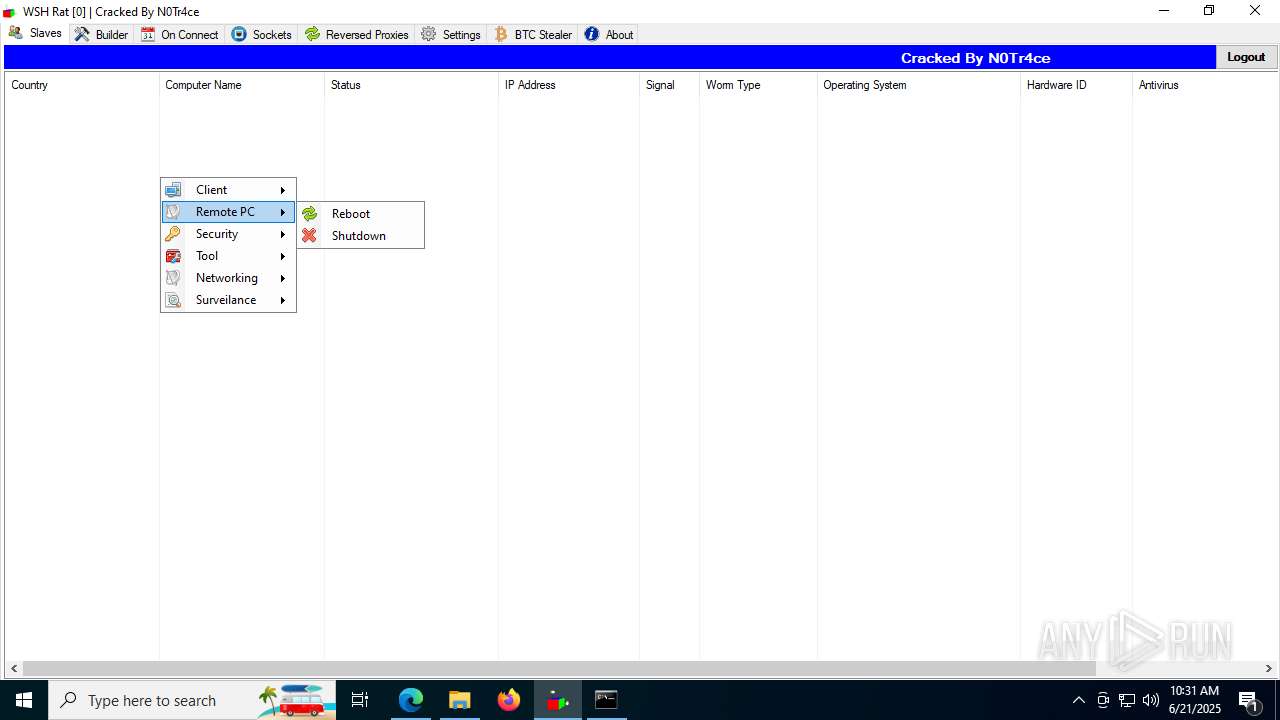
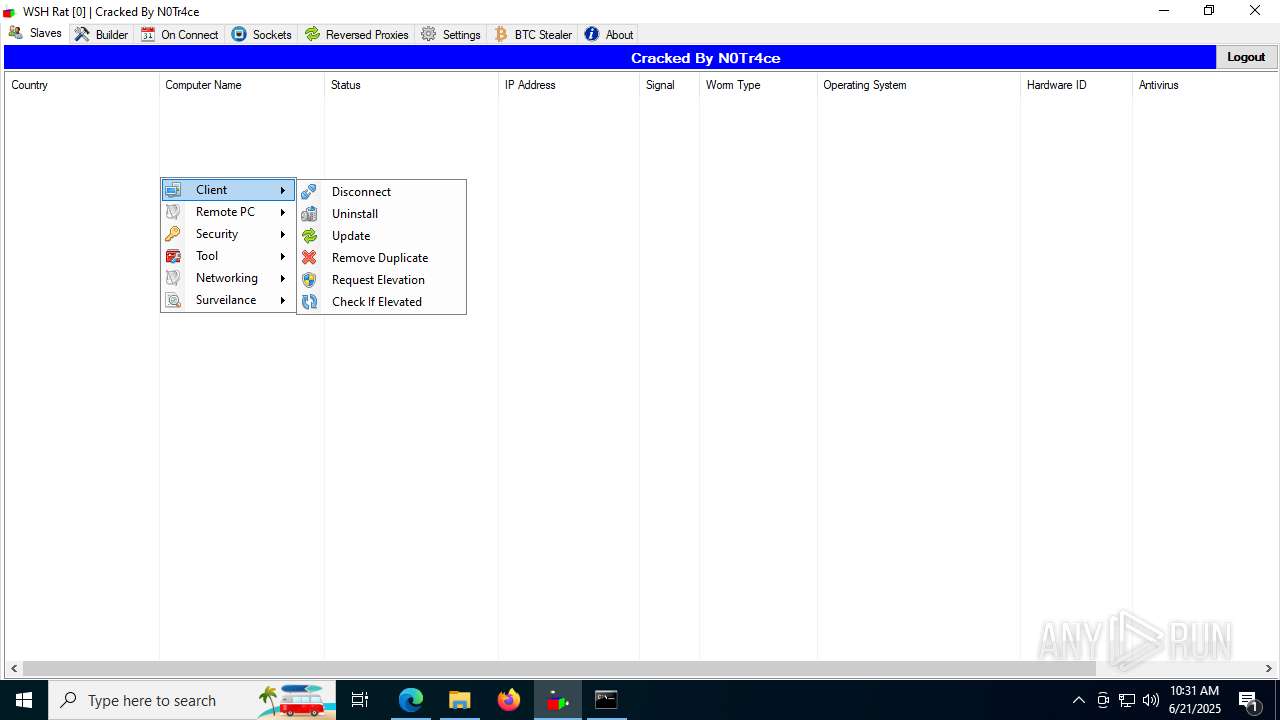
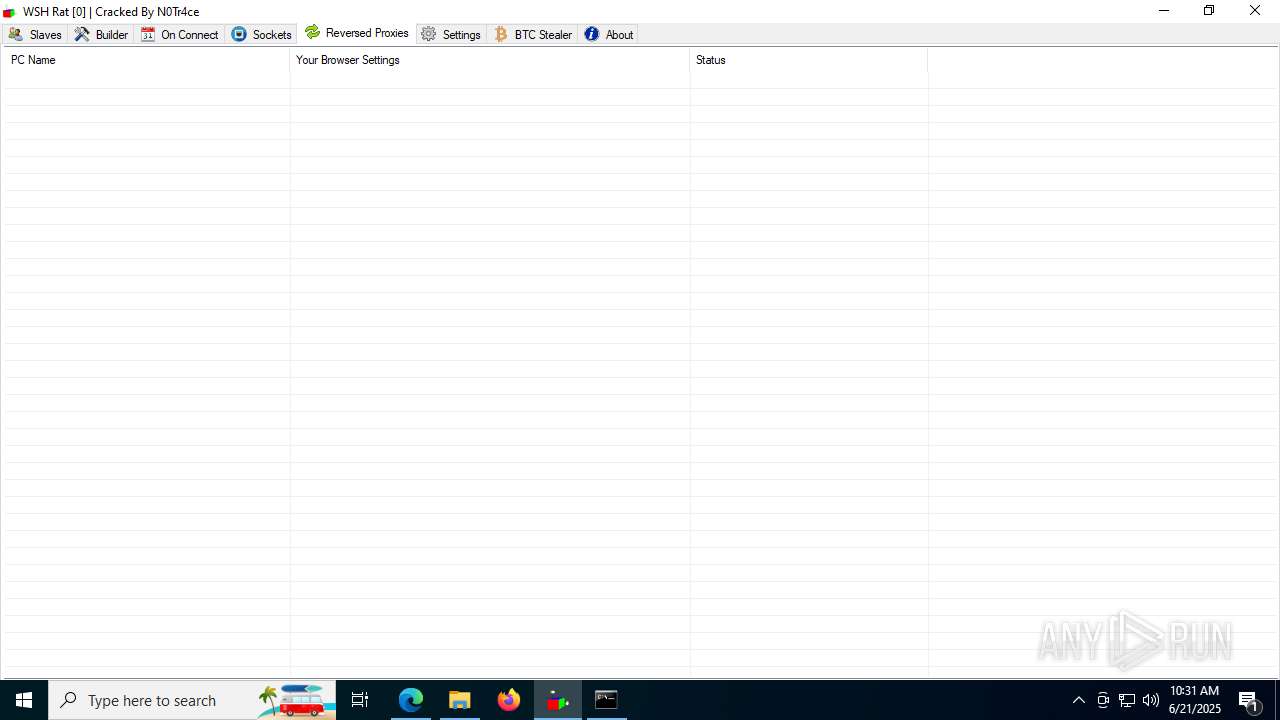
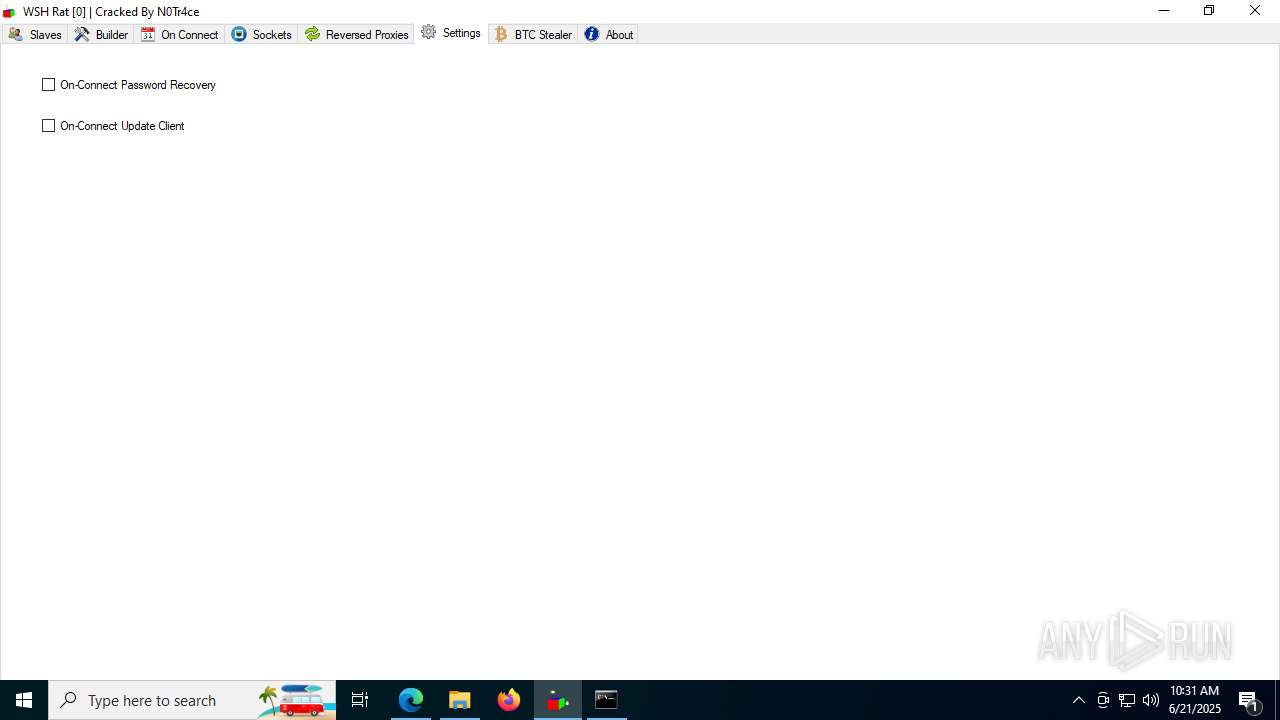
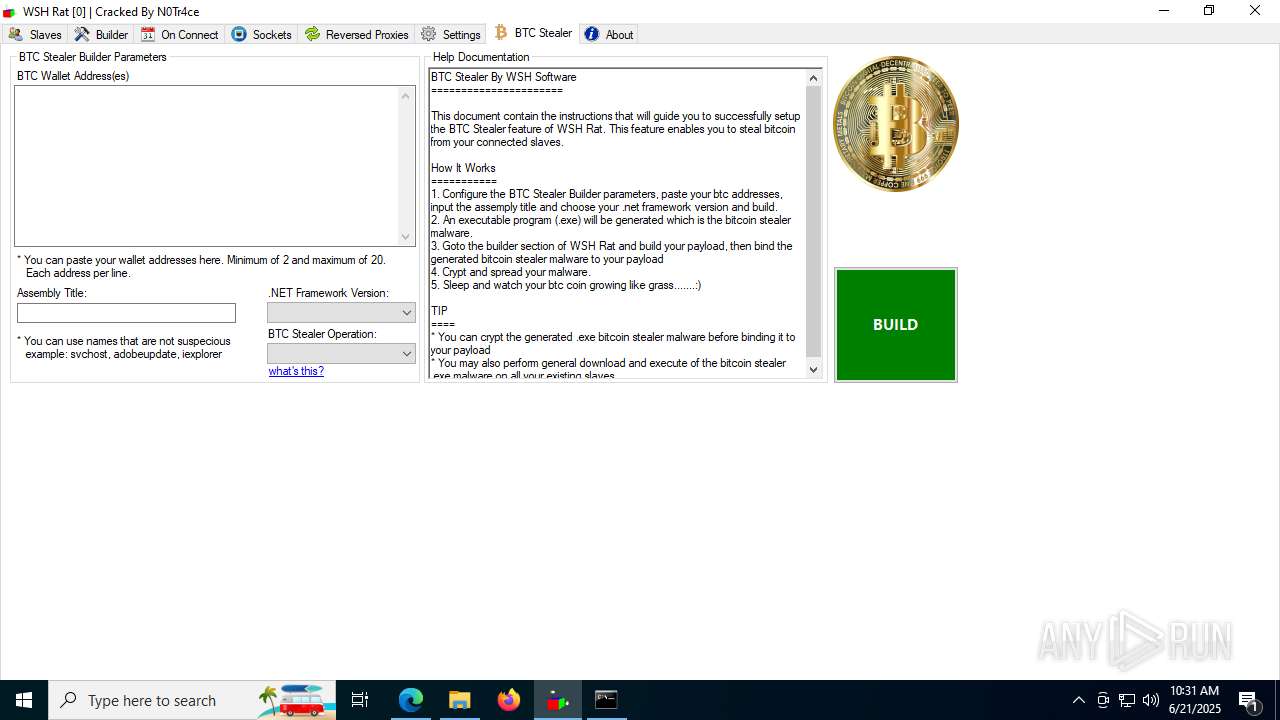
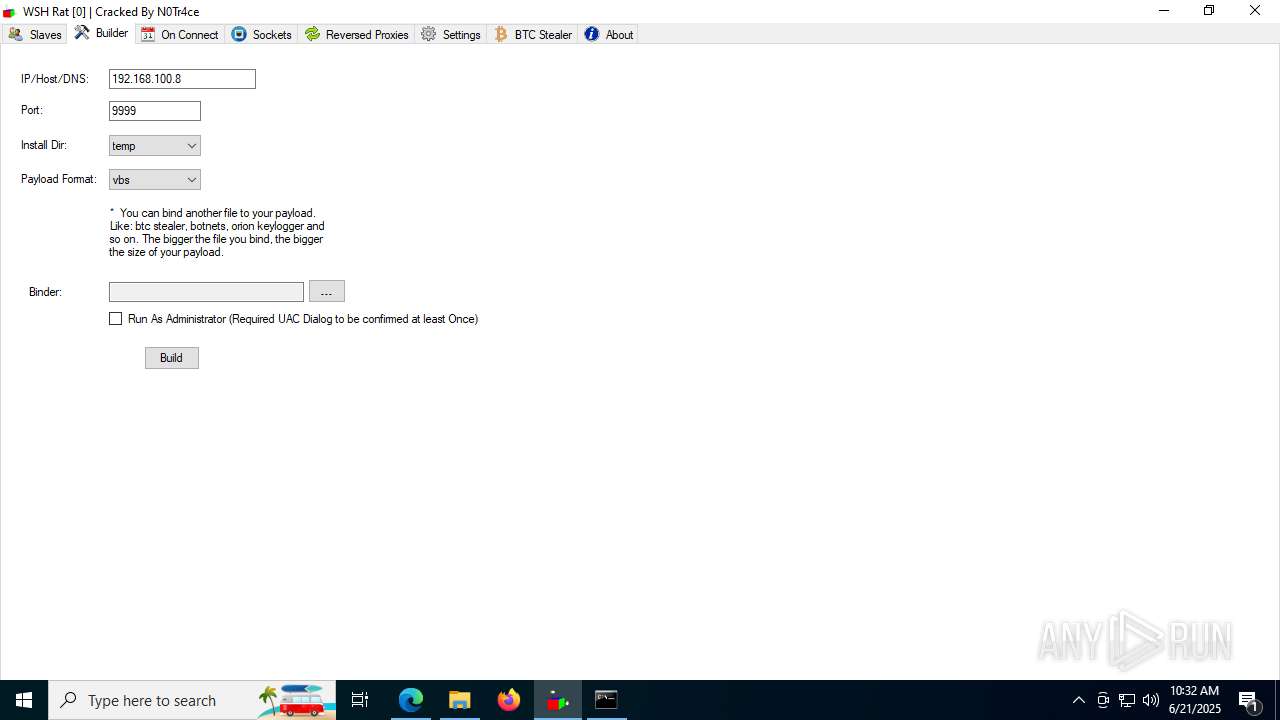
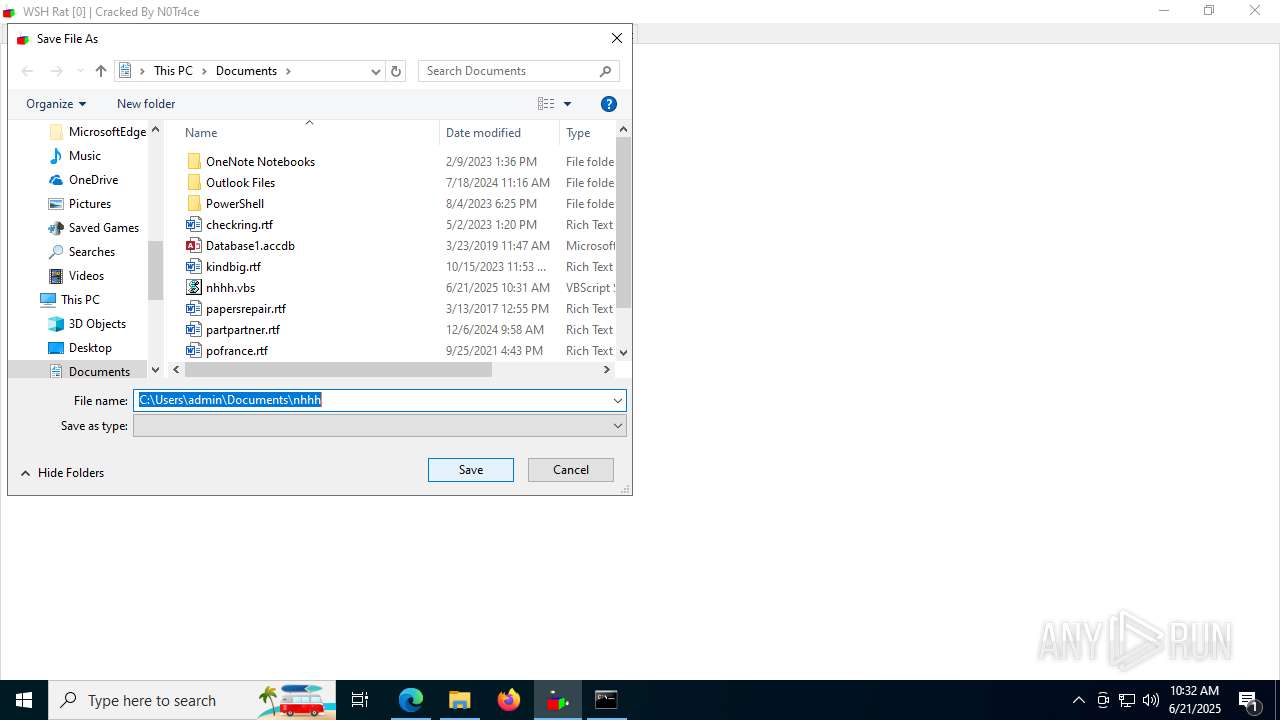
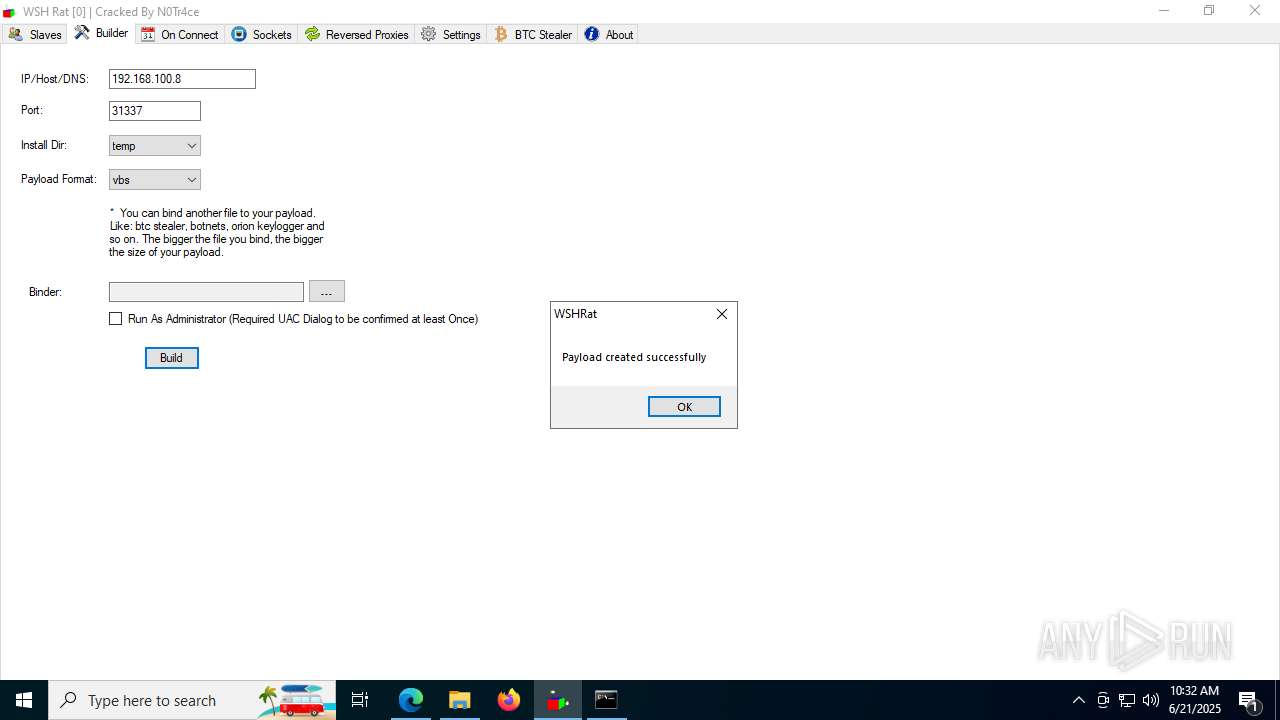
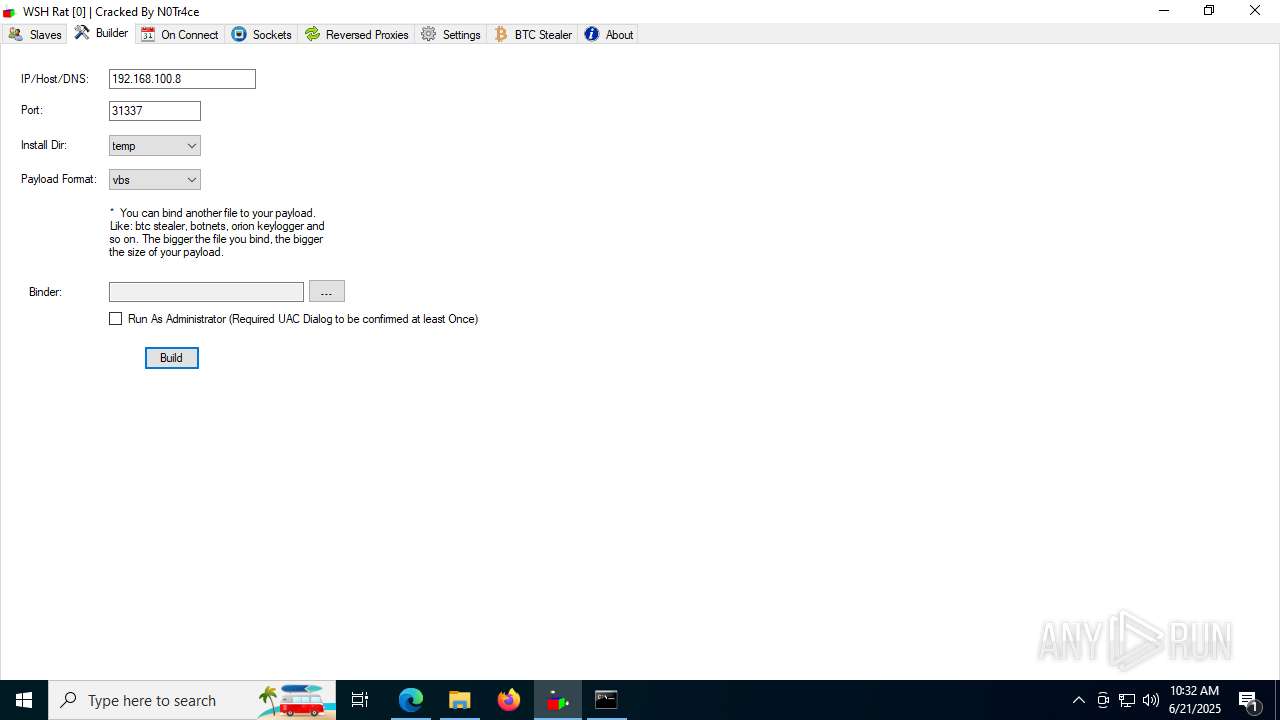
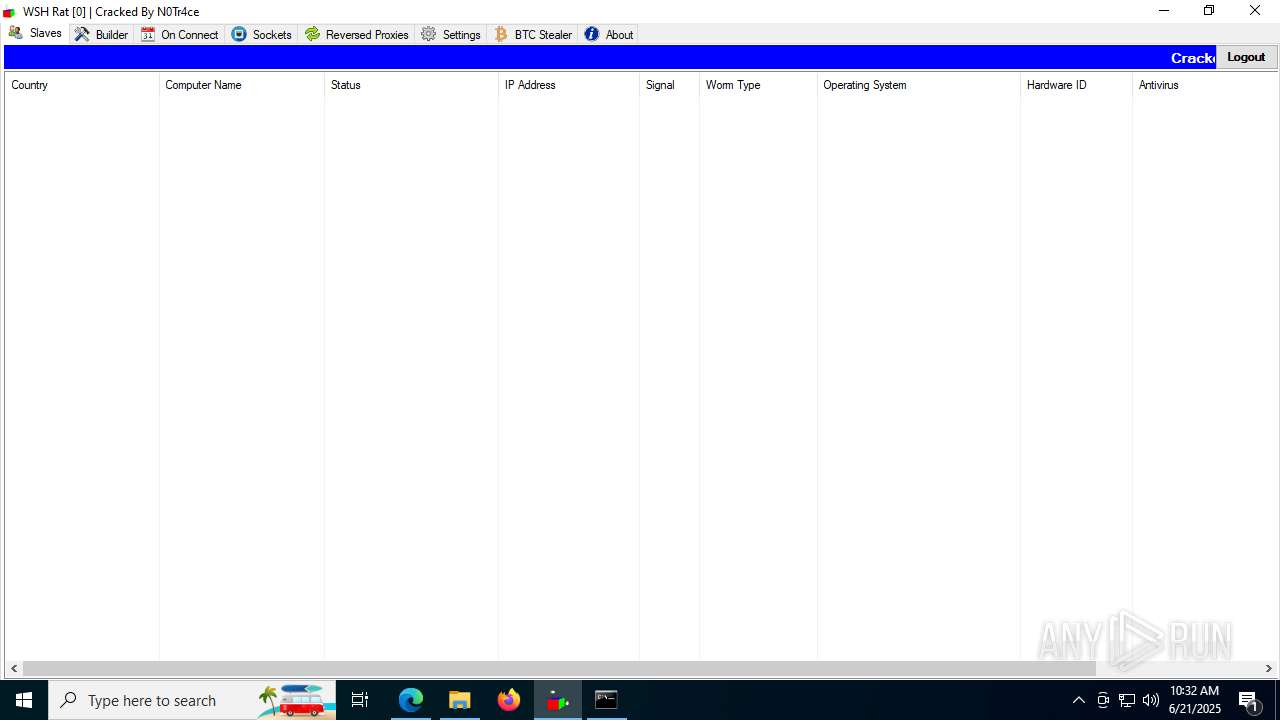
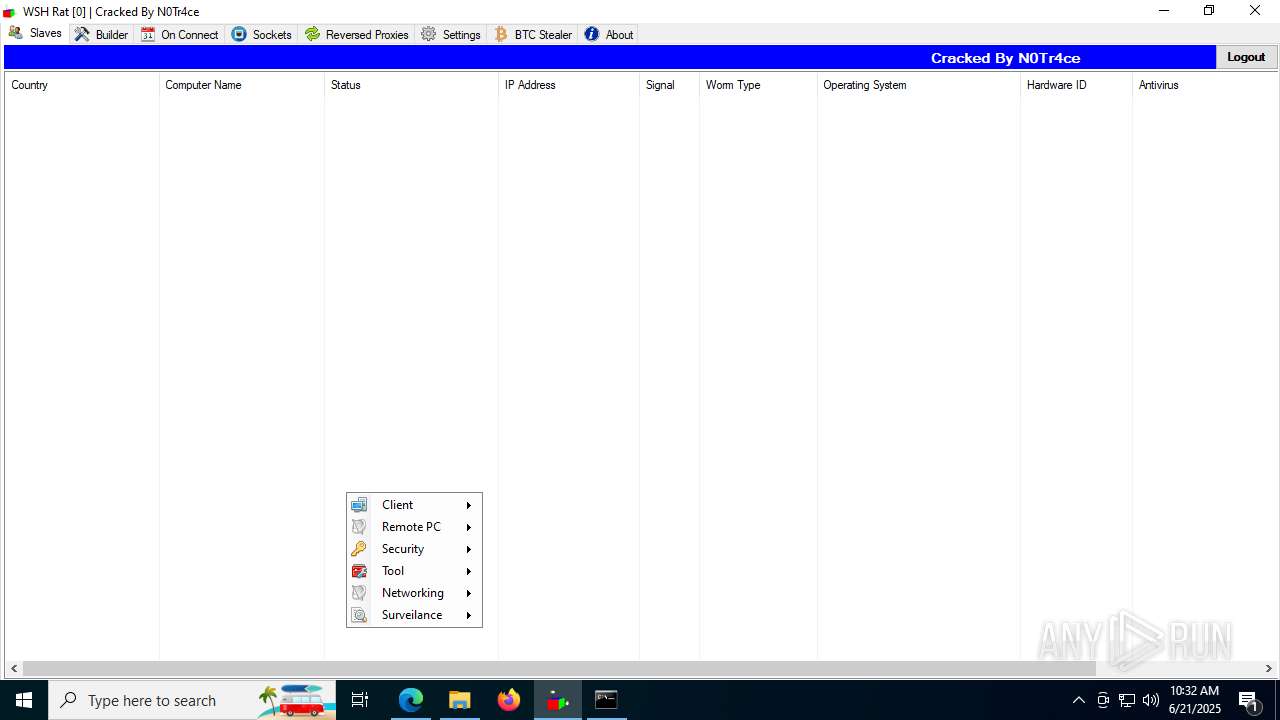
| Threats: | WSHRAT is a Remote Access Trojan — a malware that allows the attackers to take over the infected machines. The RAT has been in circulation since 2013 and it is arguably most notable for the numerous versions released into the wild. |
| Analysis date: | June 21, 2025, 10:27:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C8318759DB001C37A08667E2C26103D3 |
| SHA1: | 853CC76BC89972558EEFFCC8E3DDF7C37EBCDA10 |
| SHA256: | B09940FBE0132DBD11A3144B3327ACB73E6E4D9E53DD3FB76623E2FA6EE29393 |
| SSDEEP: | 3:N83mOCA:23mOD |
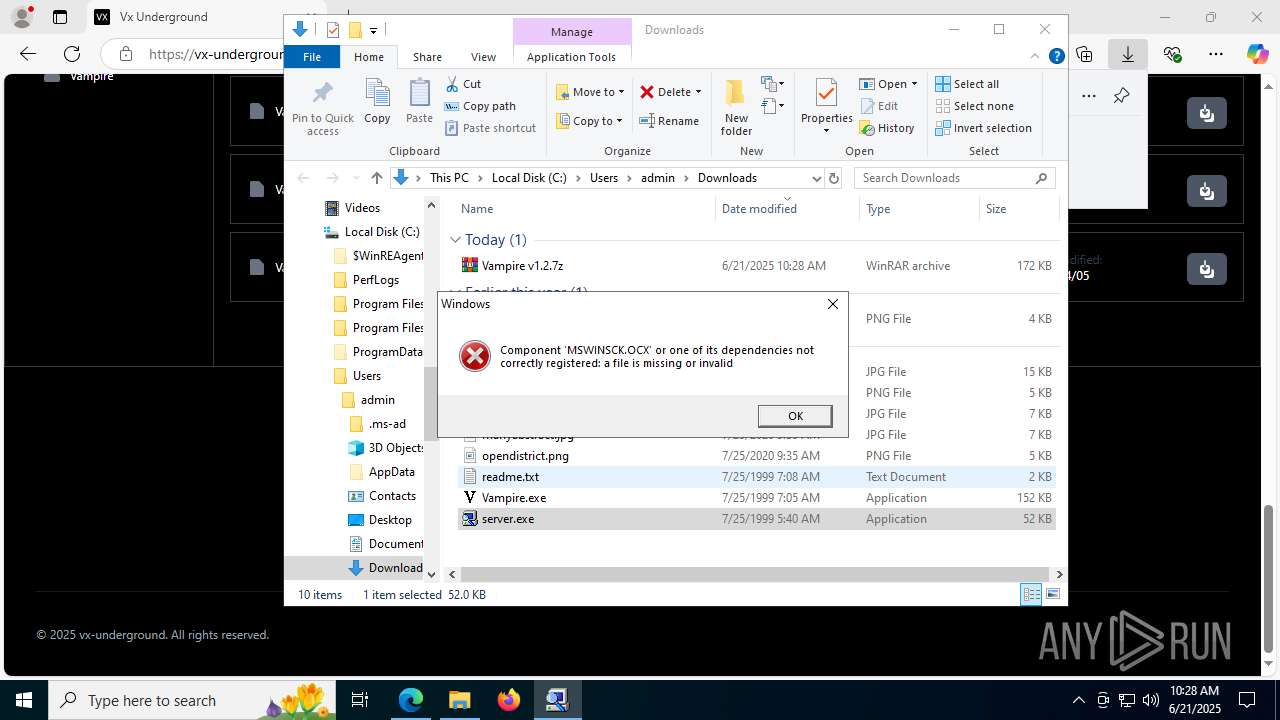
MALICIOUS
WSHRAT has been detected (YARA)
- WSH Rat.exe (PID: 5620)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 7596)
- wscript.exe (PID: 3624)
- wscript.exe (PID: 6140)
Gets path to any of the special folders (SCRIPT)
- wscript.exe (PID: 7596)
- wscript.exe (PID: 3624)
- wscript.exe (PID: 6140)
Gets startup folder path (SCRIPT)
- wscript.exe (PID: 7596)
- wscript.exe (PID: 3624)
- wscript.exe (PID: 6140)
Gets TEMP folder path (SCRIPT)
- wscript.exe (PID: 7596)
- wscript.exe (PID: 3624)
- wscript.exe (PID: 6140)
Checks whether a specified folder exists (SCRIPT)
- wscript.exe (PID: 7596)
- wscript.exe (PID: 3624)
- wscript.exe (PID: 6140)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 7596)
- wscript.exe (PID: 3624)
- wscript.exe (PID: 6140)
Reads the value of a key from the registry (SCRIPT)
- wscript.exe (PID: 7596)
- wscript.exe (PID: 3624)
- wscript.exe (PID: 6140)
Creates a new registry key or changes the value of an existing one (SCRIPT)
- wscript.exe (PID: 7596)
- wscript.exe (PID: 3624)
- wscript.exe (PID: 6140)
Gets a file object corresponding to the file in a specified path (SCRIPT)
- wscript.exe (PID: 7596)
- wscript.exe (PID: 3624)
- wscript.exe (PID: 6140)
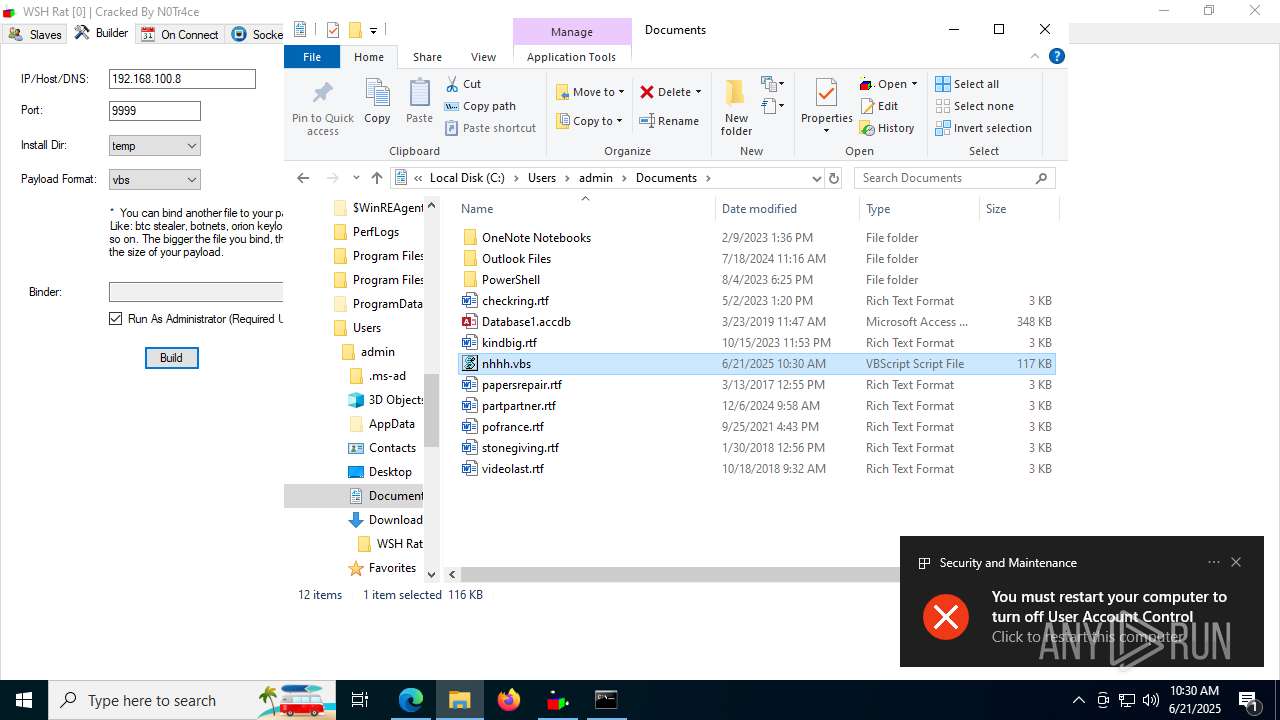
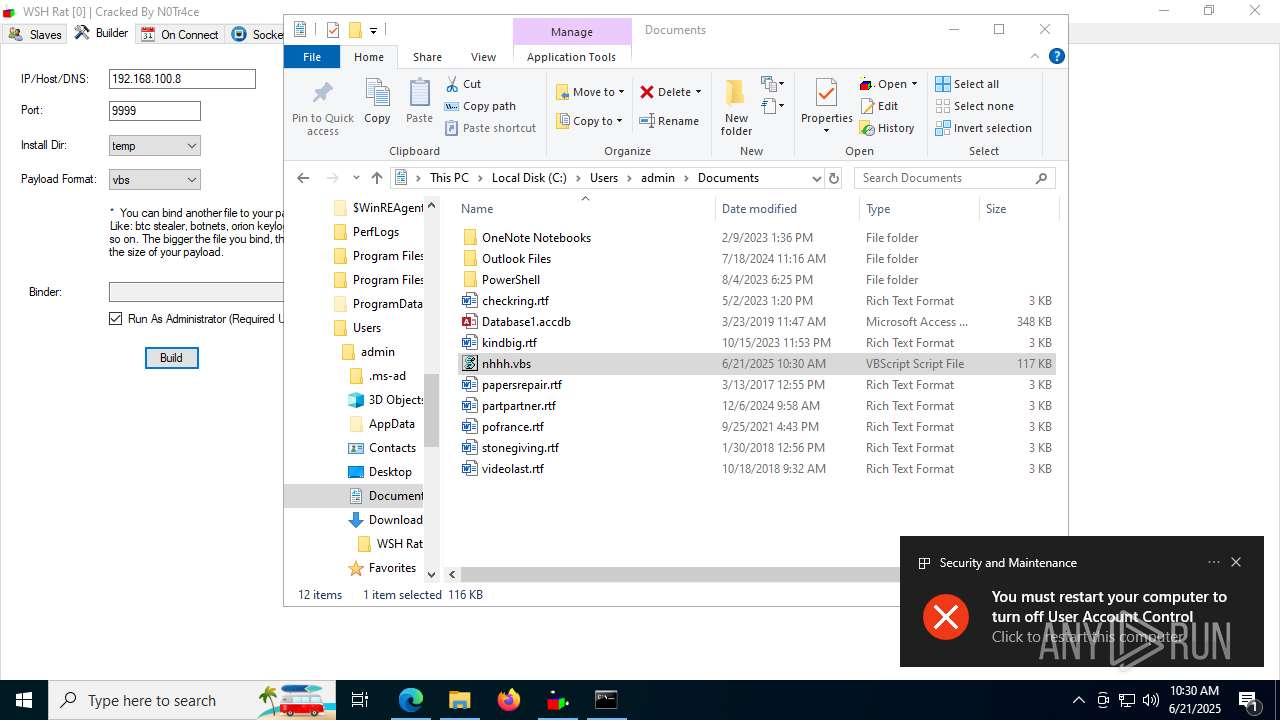
Modifies registry startup key (SCRIPT)
- wscript.exe (PID: 7596)
- wscript.exe (PID: 3624)
- wscript.exe (PID: 6140)
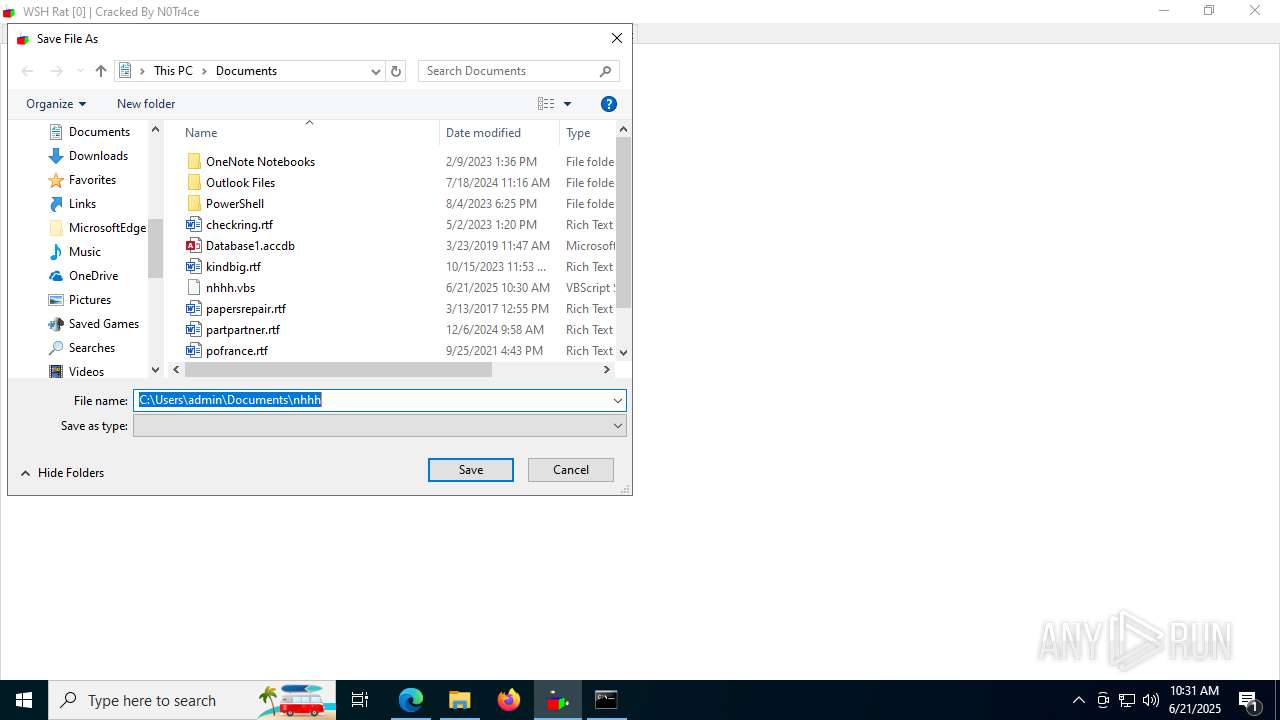
Copies file to a new location (SCRIPT)
- wscript.exe (PID: 7596)
- wscript.exe (PID: 3624)
- wscript.exe (PID: 6140)
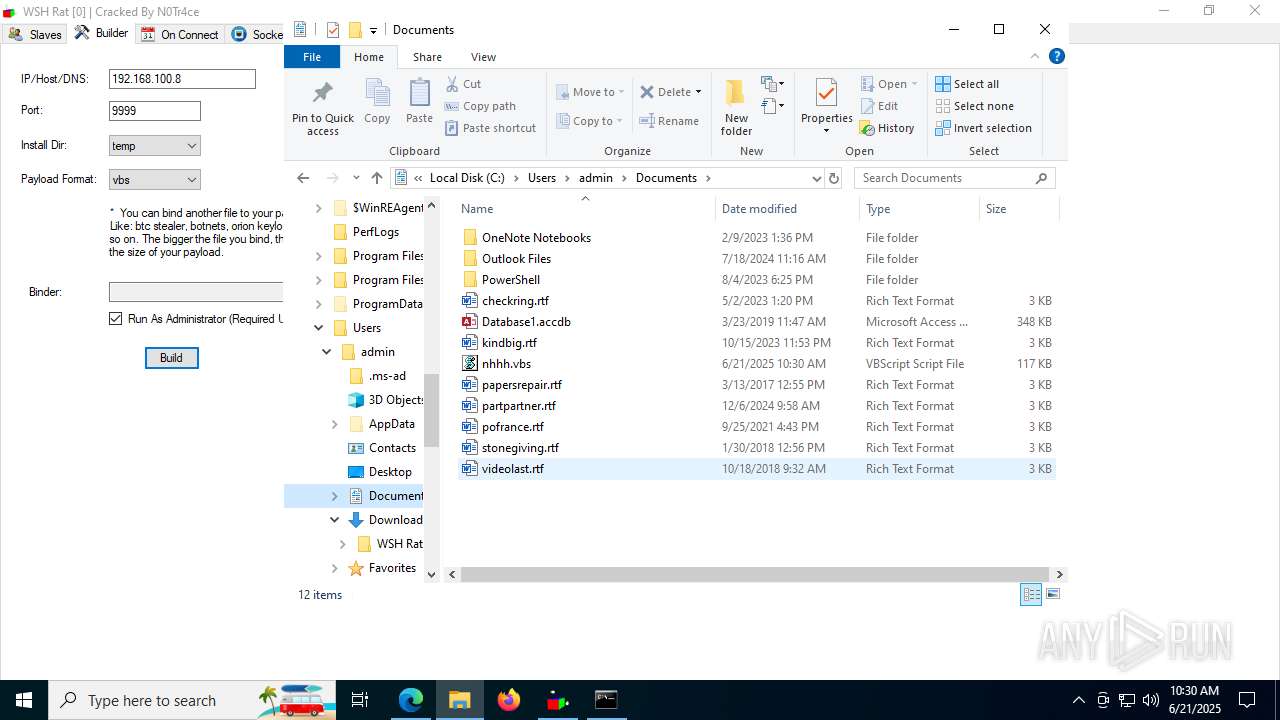
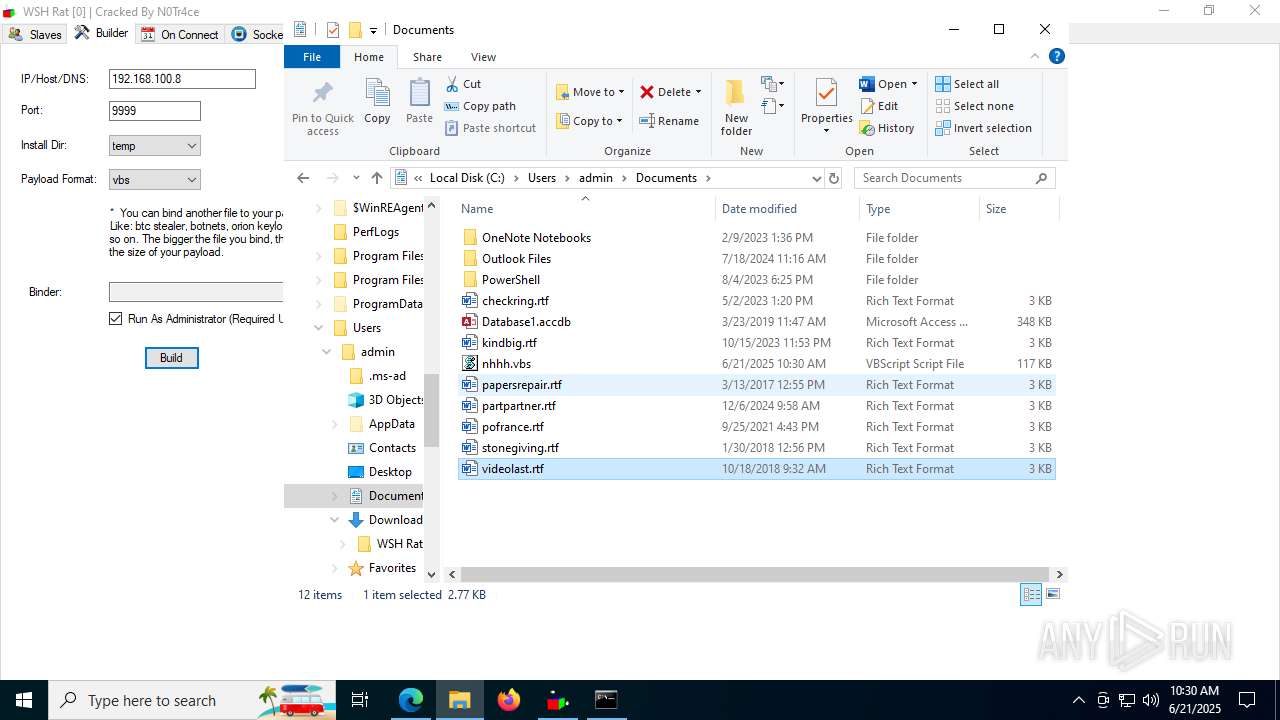
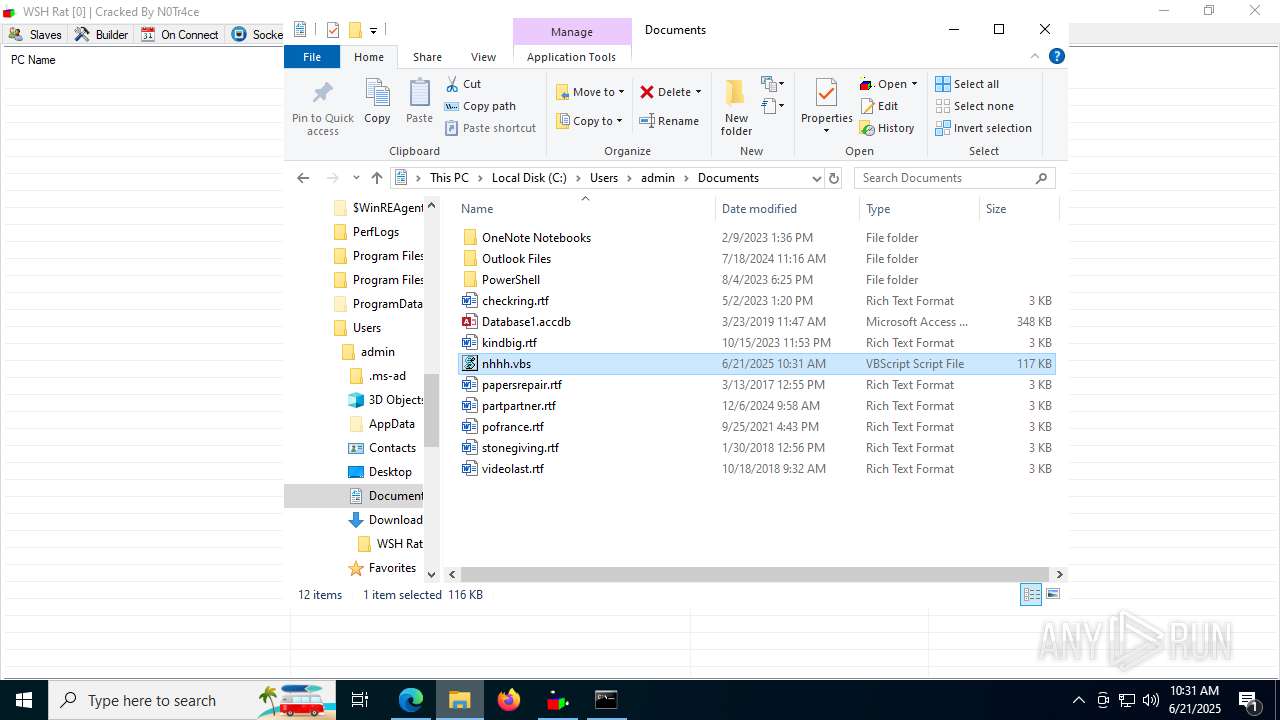
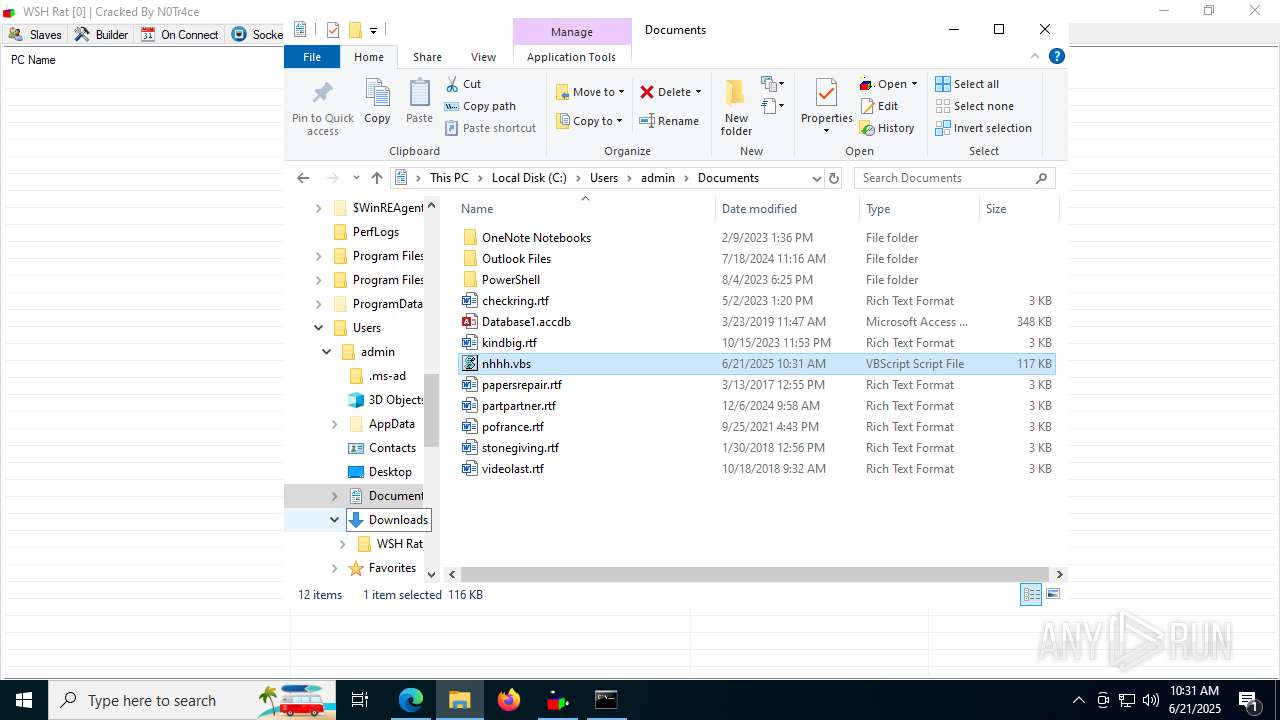
Create files in the Startup directory
- wscript.exe (PID: 7596)
- wscript.exe (PID: 3624)
Opens a text file (SCRIPT)
- wscript.exe (PID: 3624)
Gets username (SCRIPT)
- wscript.exe (PID: 3624)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 3624)
Accesses information about the status of the installed antivirus(Win32_AntivirusProduct) via WMI (SCRIPT)
- wscript.exe (PID: 3624)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 3624)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 3624)
SUSPICIOUS
Reads security settings of Internet Explorer
- GameBar.exe (PID: 5372)
- ShellExperienceHost.exe (PID: 7060)
- WSH Rat.exe (PID: 5620)
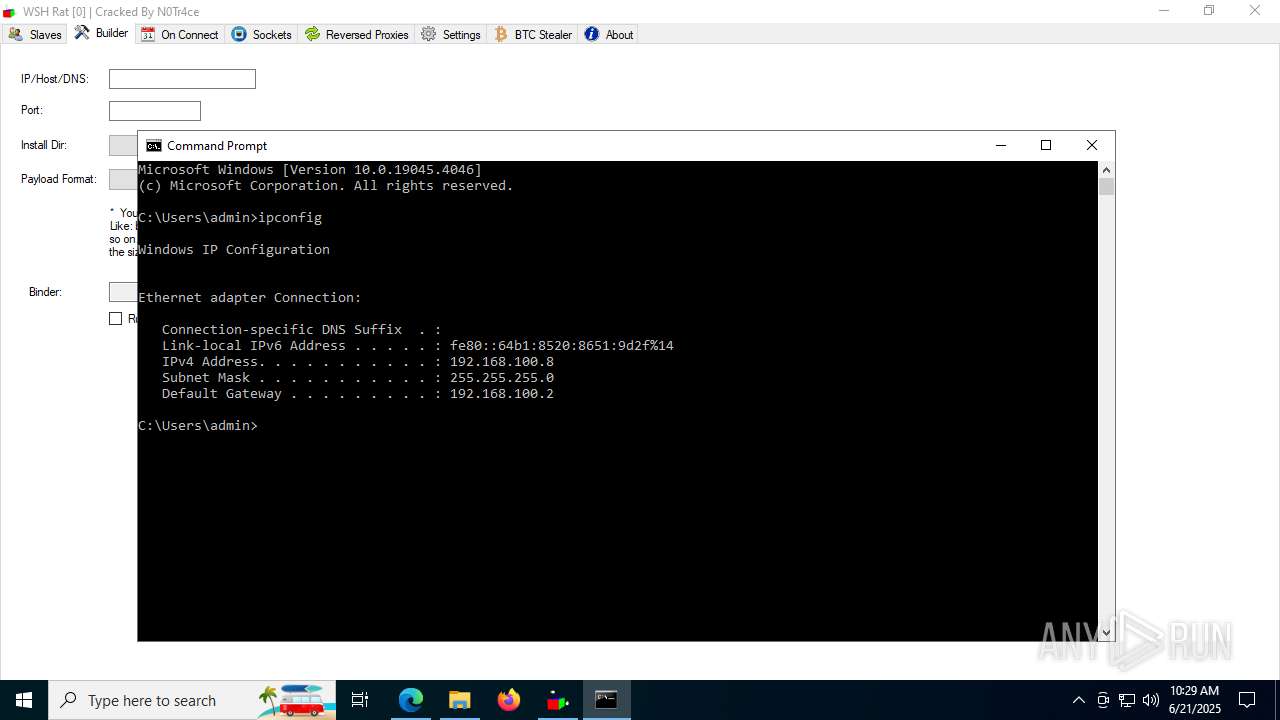
Process uses IPCONFIG to get network configuration information
- cmd.exe (PID: 5532)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 5352)
- wscript.exe (PID: 7596)
- wscript.exe (PID: 3624)
- wscript.exe (PID: 6140)
Runs shell command (SCRIPT)
- wscript.exe (PID: 5352)
- wscript.exe (PID: 7596)
- wscript.exe (PID: 6140)
Application launched itself
- wscript.exe (PID: 5352)
- wscript.exe (PID: 7596)
- wscript.exe (PID: 6140)
The process executes VB scripts
- wscript.exe (PID: 5352)
- wscript.exe (PID: 7596)
- wscript.exe (PID: 6140)
Reads Internet Explorer settings
- WSH Rat.exe (PID: 5620)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 7596)
- wscript.exe (PID: 3624)
- wscript.exe (PID: 6140)
Gets disk free space (SCRIPT)
- wscript.exe (PID: 3624)
Checks whether the drive is ready (SCRIPT)
- wscript.exe (PID: 3624)
Gets a collection of all available drive names (SCRIPT)
- wscript.exe (PID: 3624)
Gets computer name (SCRIPT)
- wscript.exe (PID: 3624)
Accesses current user name via WMI (SCRIPT)
- wscript.exe (PID: 3624)
Accesses local storage devices (Win32_LogicalDisk) via WMI (SCRIPT)
- wscript.exe (PID: 3624)
Accesses OperatingSystem(Win32_OperatingSystem) via WMI (SCRIPT)
- wscript.exe (PID: 3624)
Accesses computer name via WMI (SCRIPT)
- wscript.exe (PID: 3624)
Executes WMI query (SCRIPT)
- wscript.exe (PID: 3624)
Accesses WMI object, sets custom ImpersonationLevel (SCRIPT)
- wscript.exe (PID: 3624)
Accesses WMI object caption (SCRIPT)
- wscript.exe (PID: 3624)
Adds, changes, or deletes HTTP request header (SCRIPT)
- wscript.exe (PID: 3624)
Accesses operating system name via WMI (SCRIPT)
- wscript.exe (PID: 3624)
Gets the drive type (SCRIPT)
- wscript.exe (PID: 3624)
Accesses antivirus product name via WMI (SCRIPT)
- wscript.exe (PID: 3624)
Accesses WMI object display name (SCRIPT)
- wscript.exe (PID: 3624)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- wscript.exe (PID: 3624)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 3624)
Changes charset (SCRIPT)
- wscript.exe (PID: 3624)
Checks for external IP
- svchost.exe (PID: 2200)
- wscript.exe (PID: 3624)
INFO
Checks supported languages
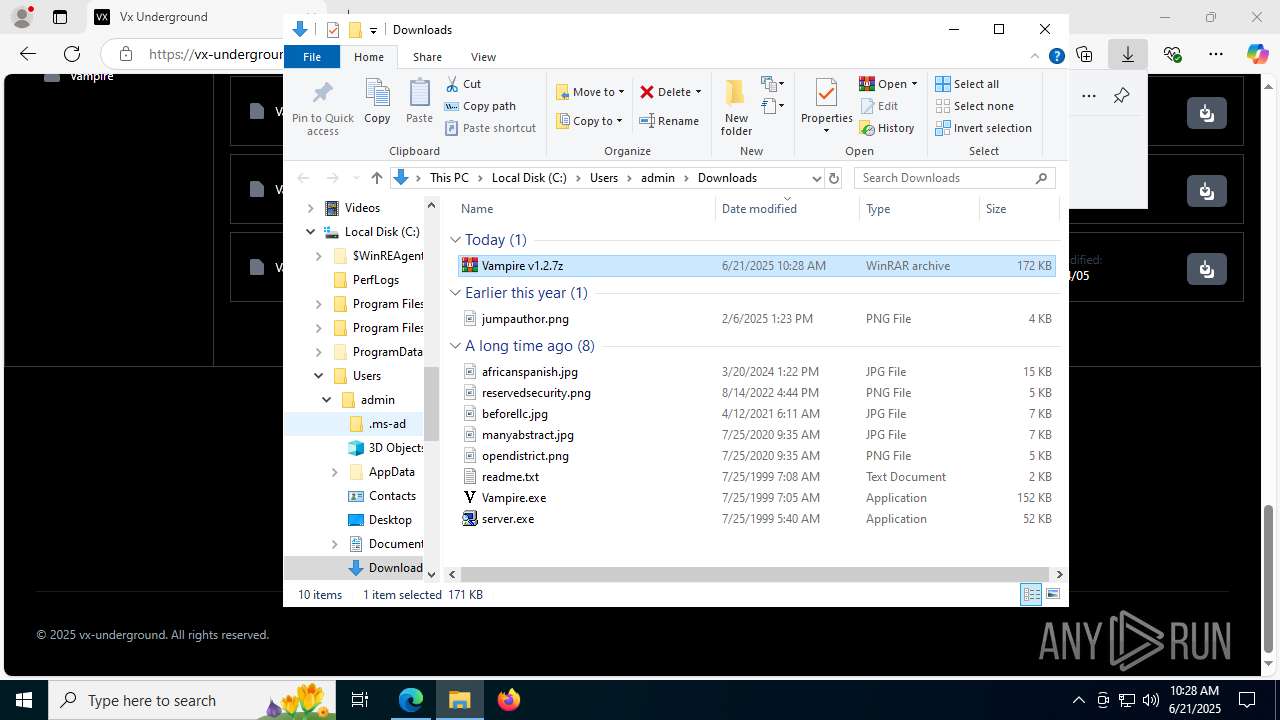
- identity_helper.exe (PID: 7724)
- server.exe (PID: 7252)
- Vampire.exe (PID: 7756)
- GameBar.exe (PID: 5372)
- ShellExperienceHost.exe (PID: 7060)
- server.exe (PID: 4828)
- server.exe (PID: 7604)
- WSH Rat.exe (PID: 5620)
Application launched itself
- msedge.exe (PID: 3092)
Reads Environment values
- identity_helper.exe (PID: 7724)
Reads the computer name
- identity_helper.exe (PID: 7724)
- server.exe (PID: 7252)
- Vampire.exe (PID: 7756)
- GameBar.exe (PID: 5372)
- ShellExperienceHost.exe (PID: 7060)
- server.exe (PID: 7604)
- server.exe (PID: 4828)
- WSH Rat.exe (PID: 5620)
The sample compiled with english language support
- msedge.exe (PID: 6532)
- msedge.exe (PID: 3092)
- WinRAR.exe (PID: 6936)
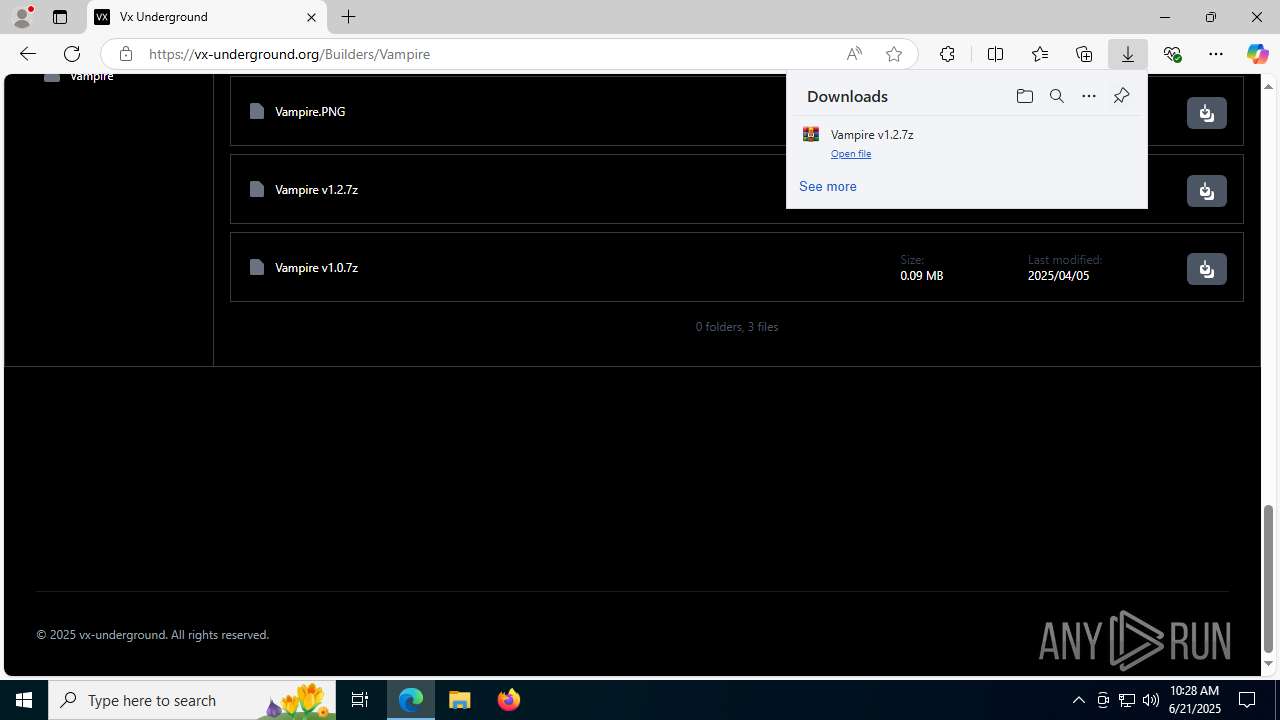
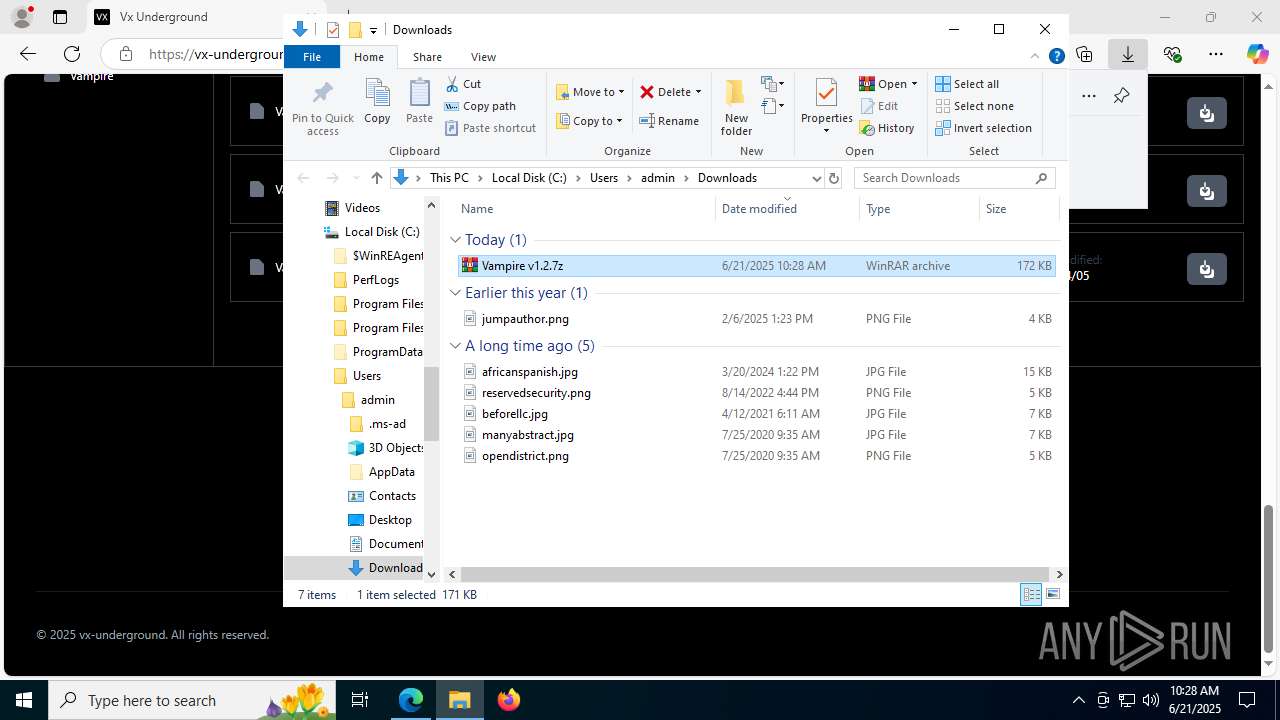
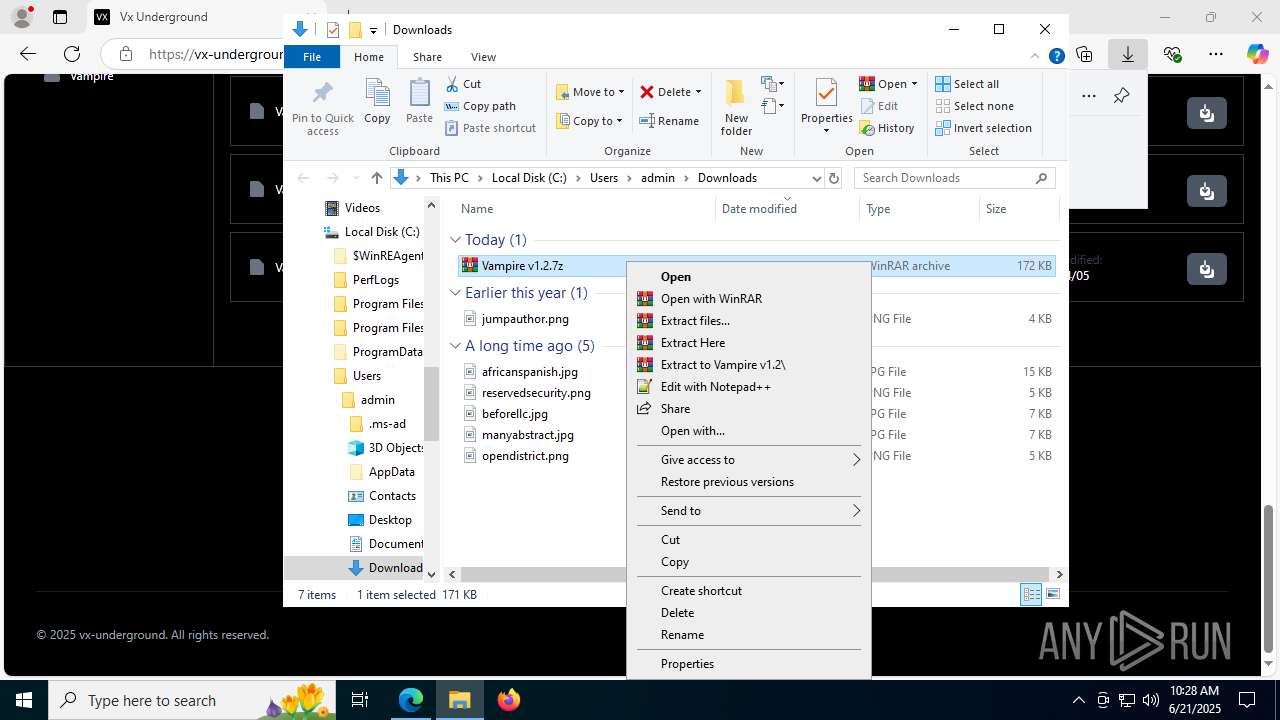
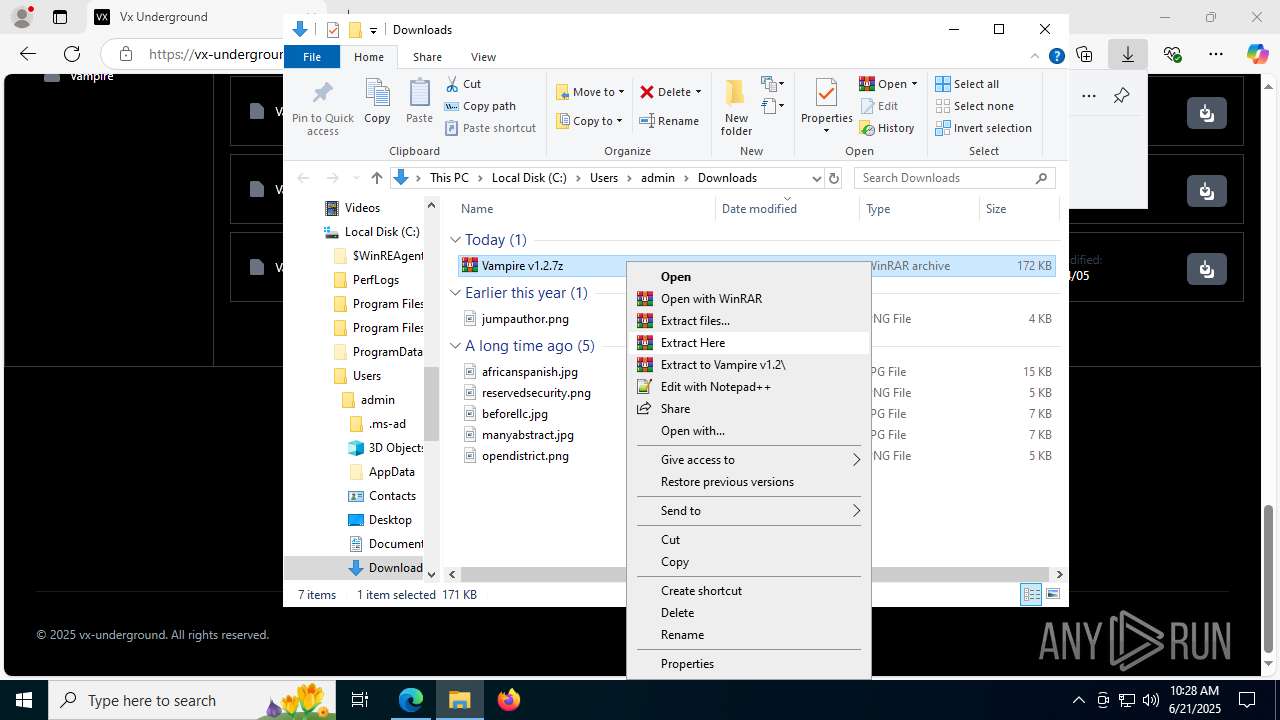
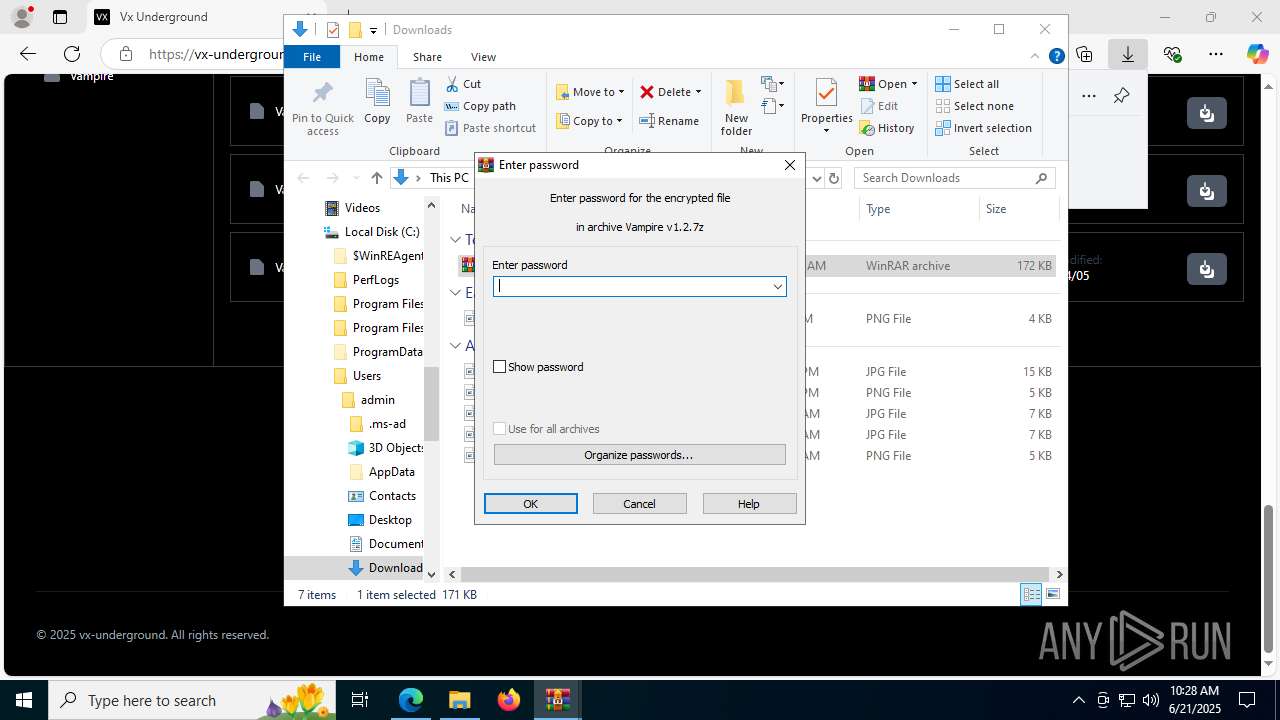
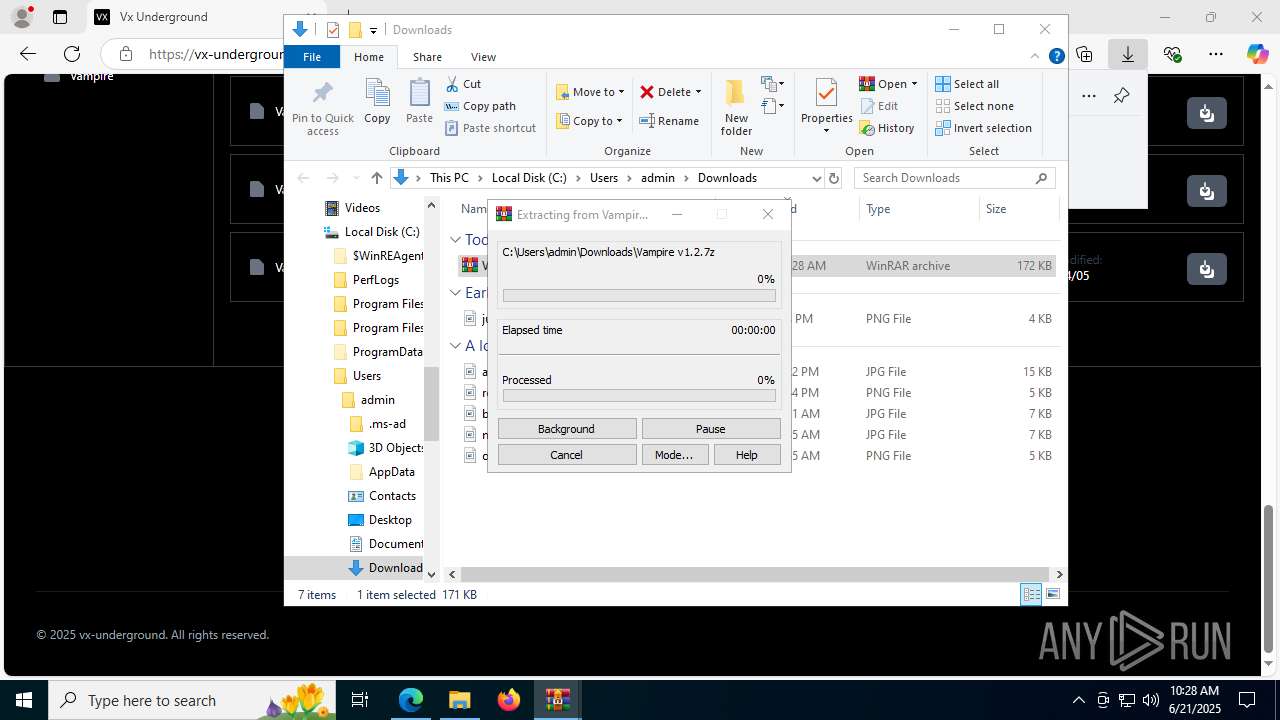
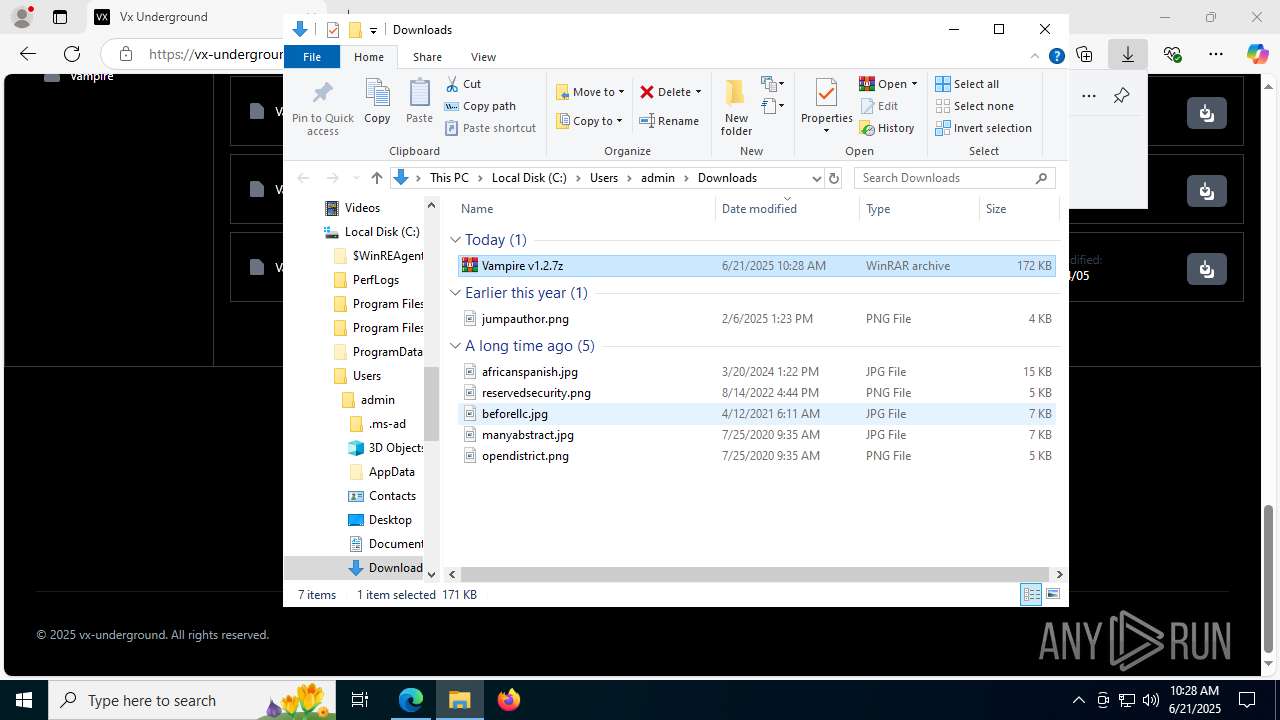
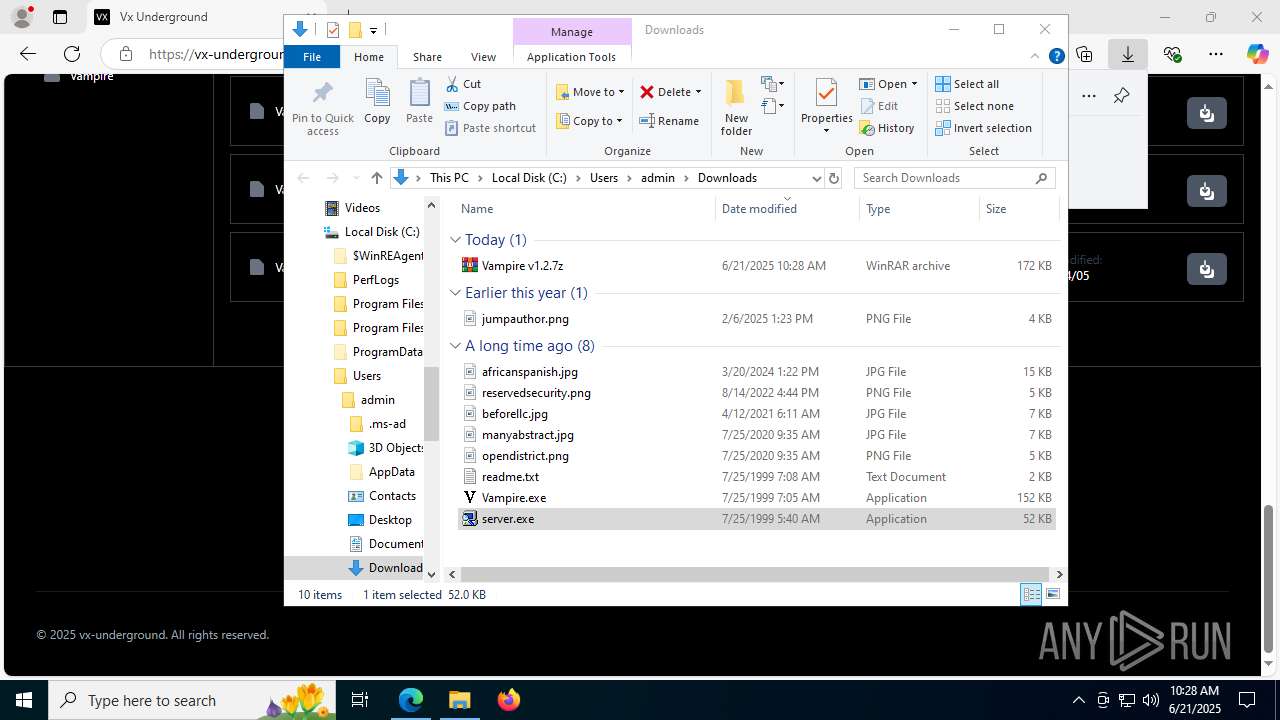
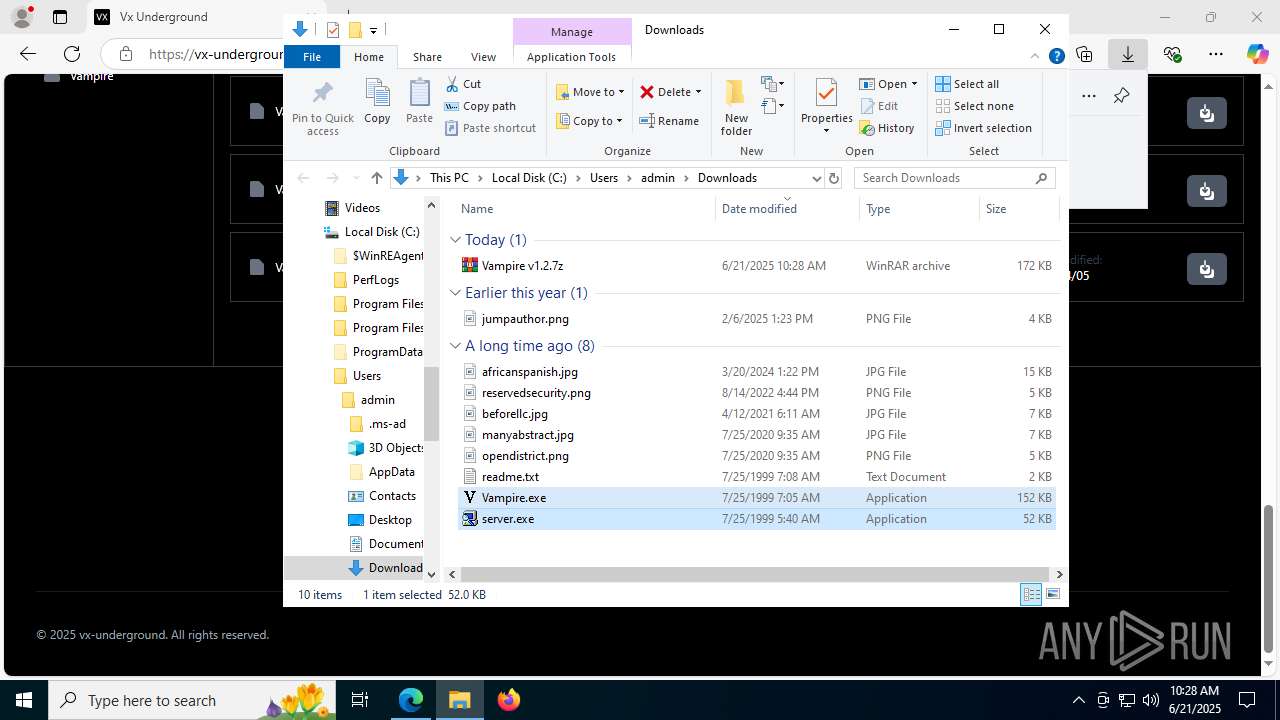
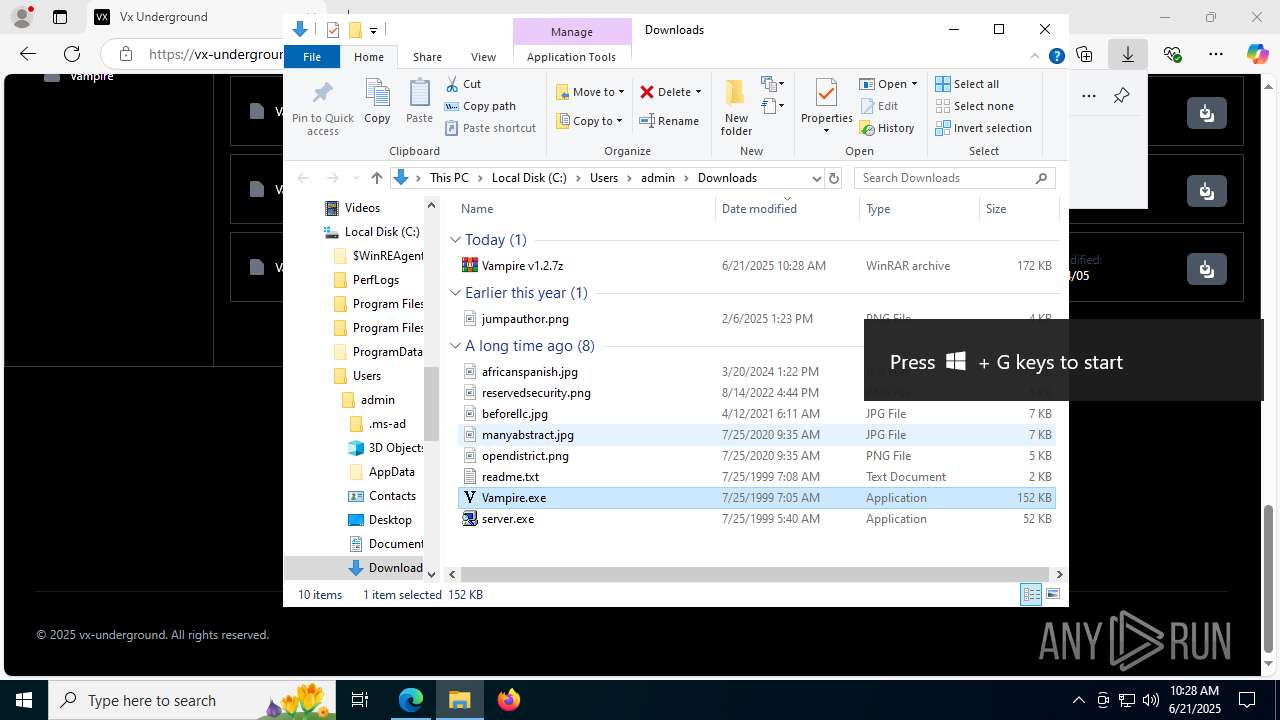
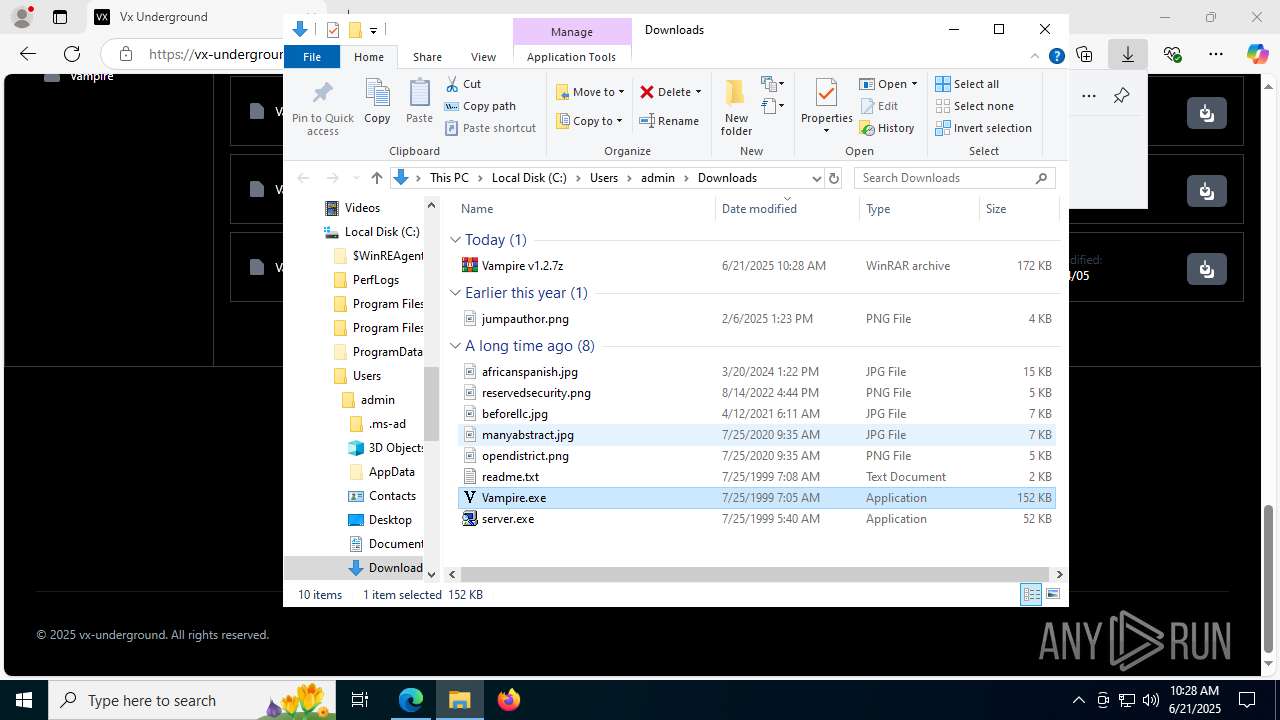
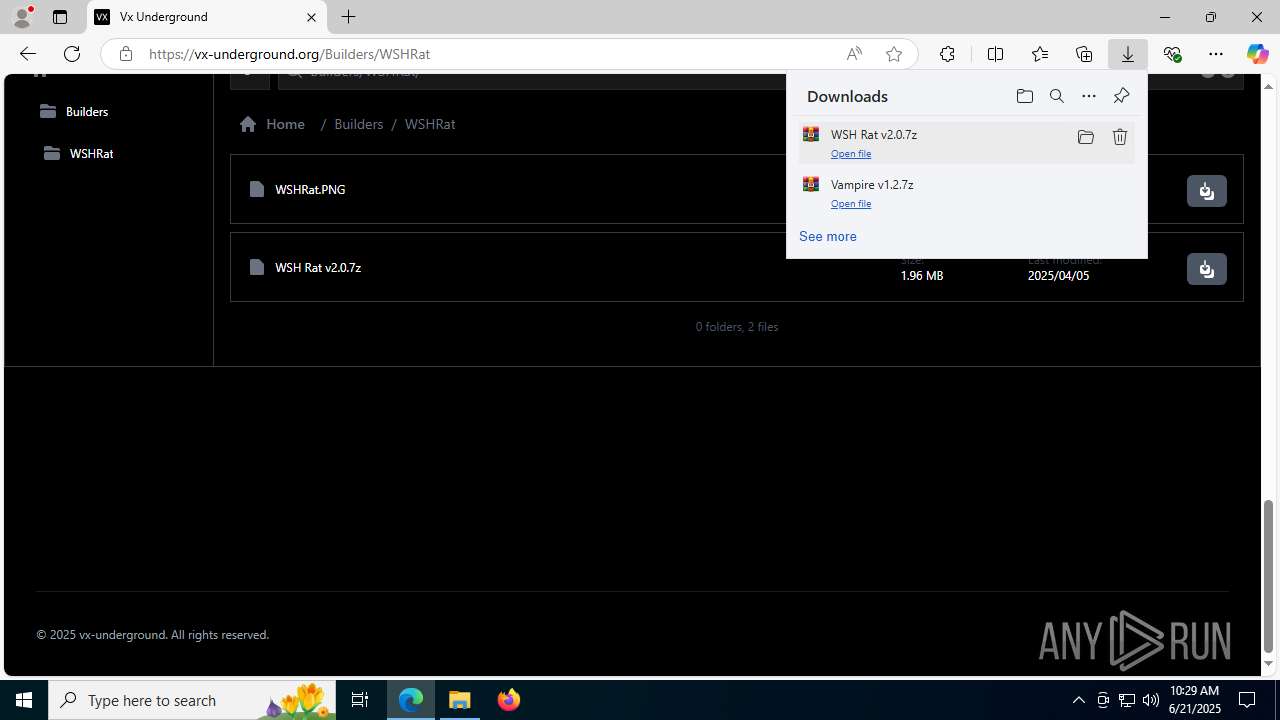
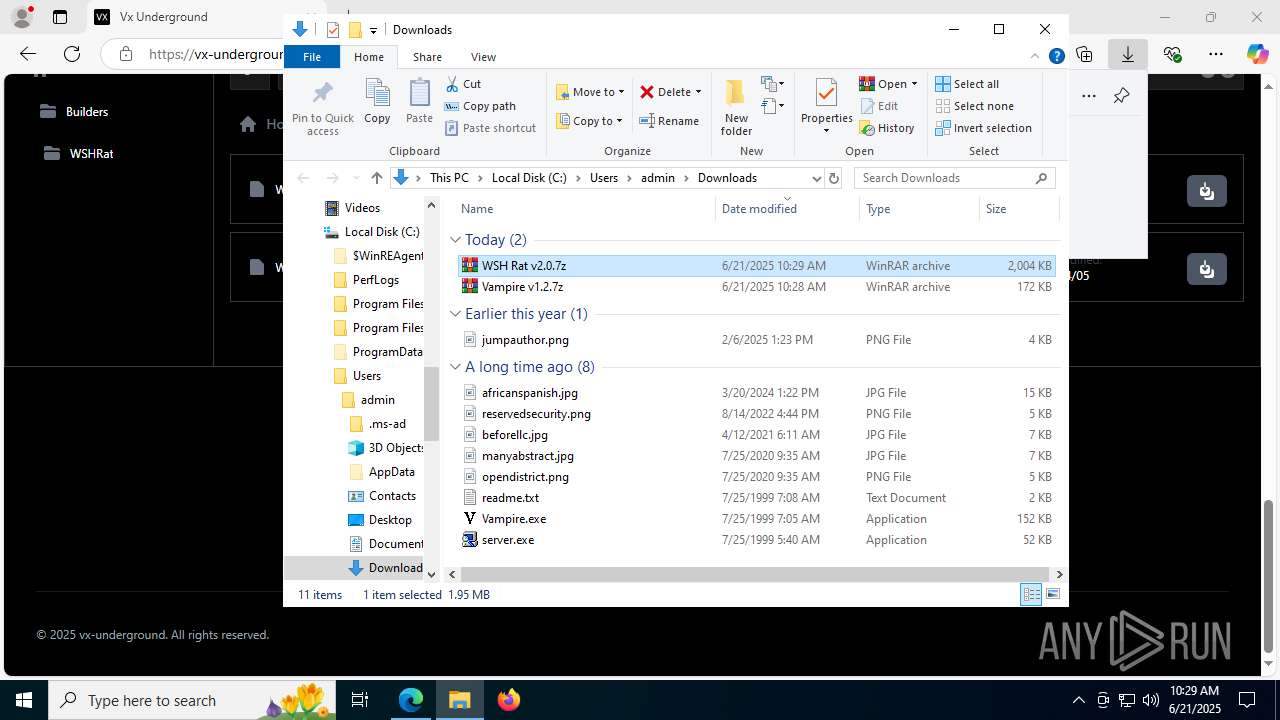
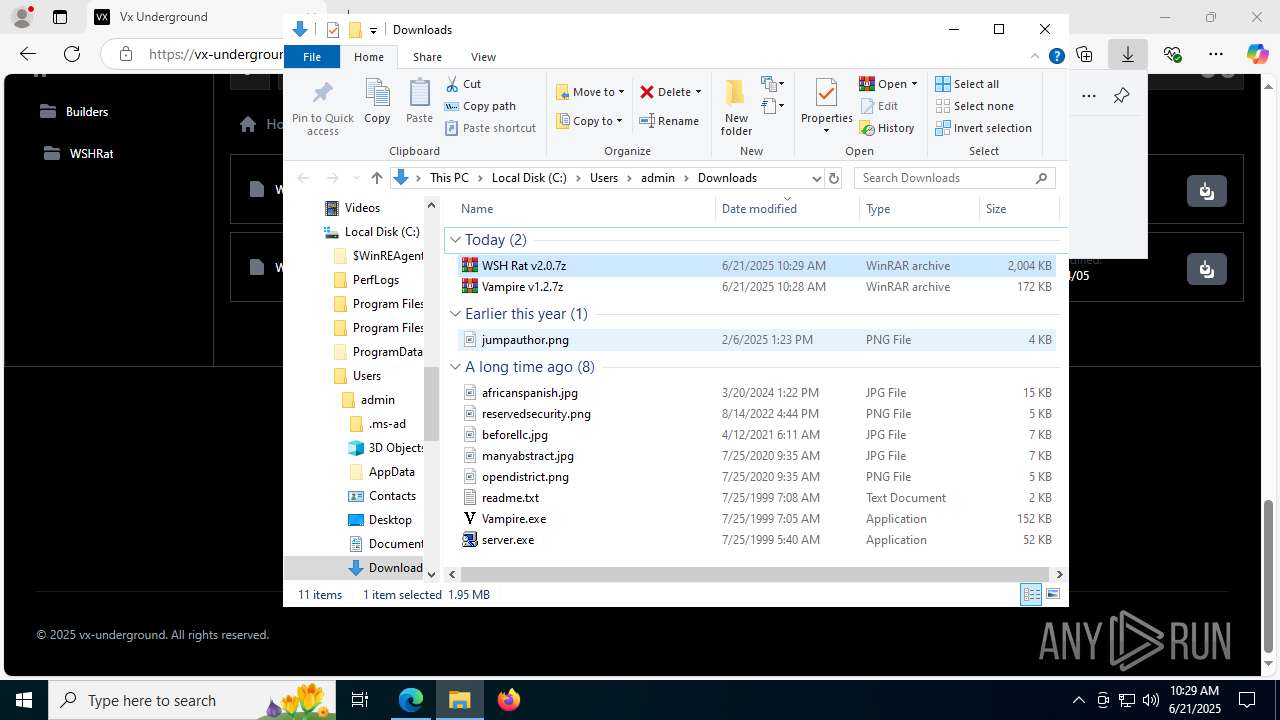
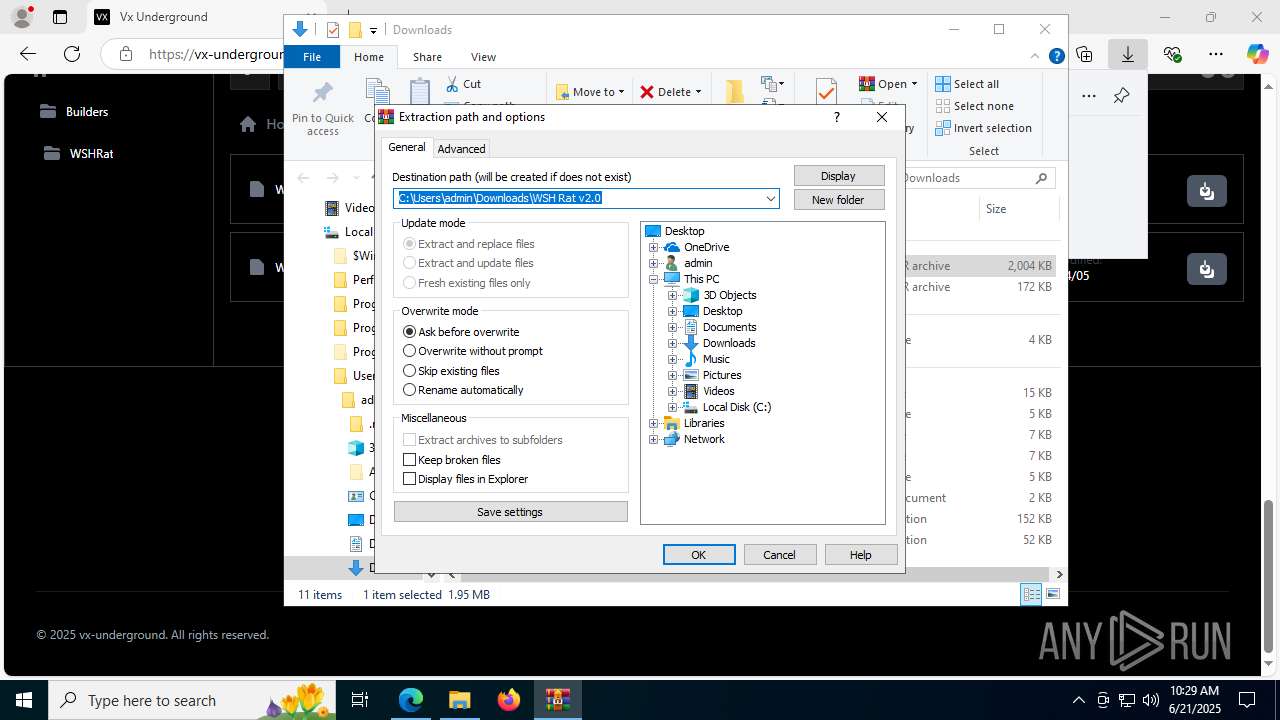
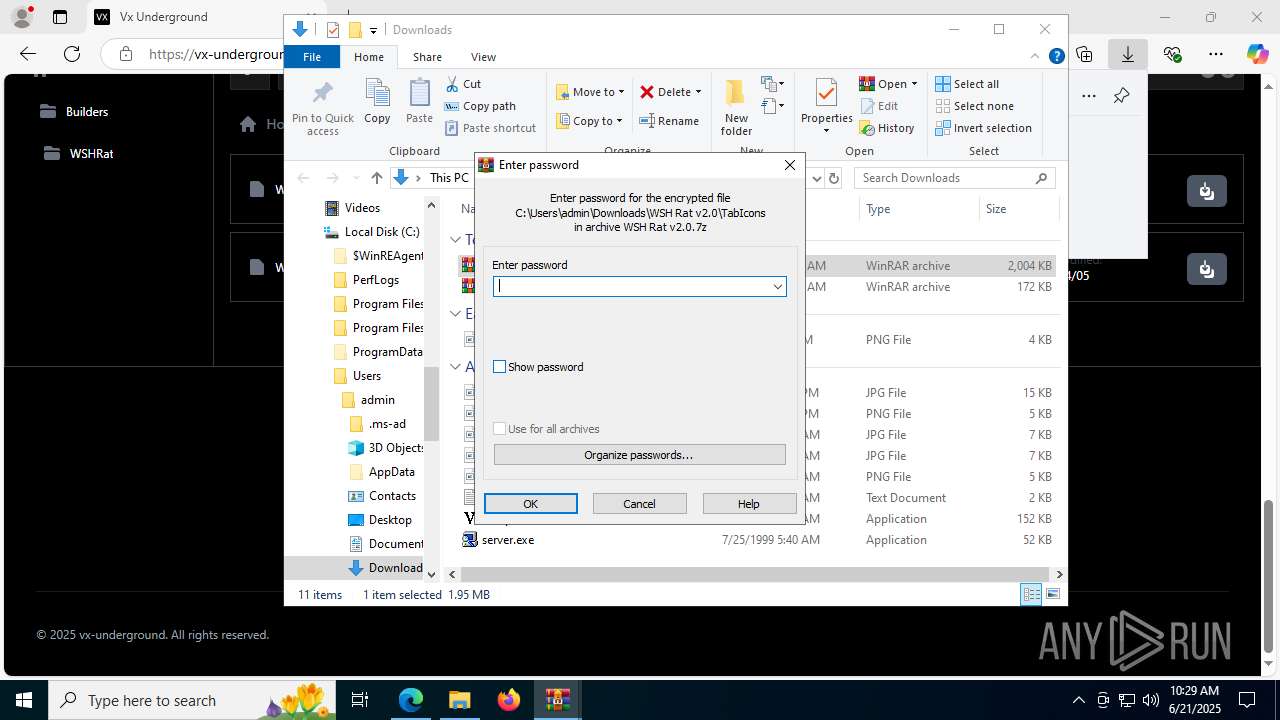
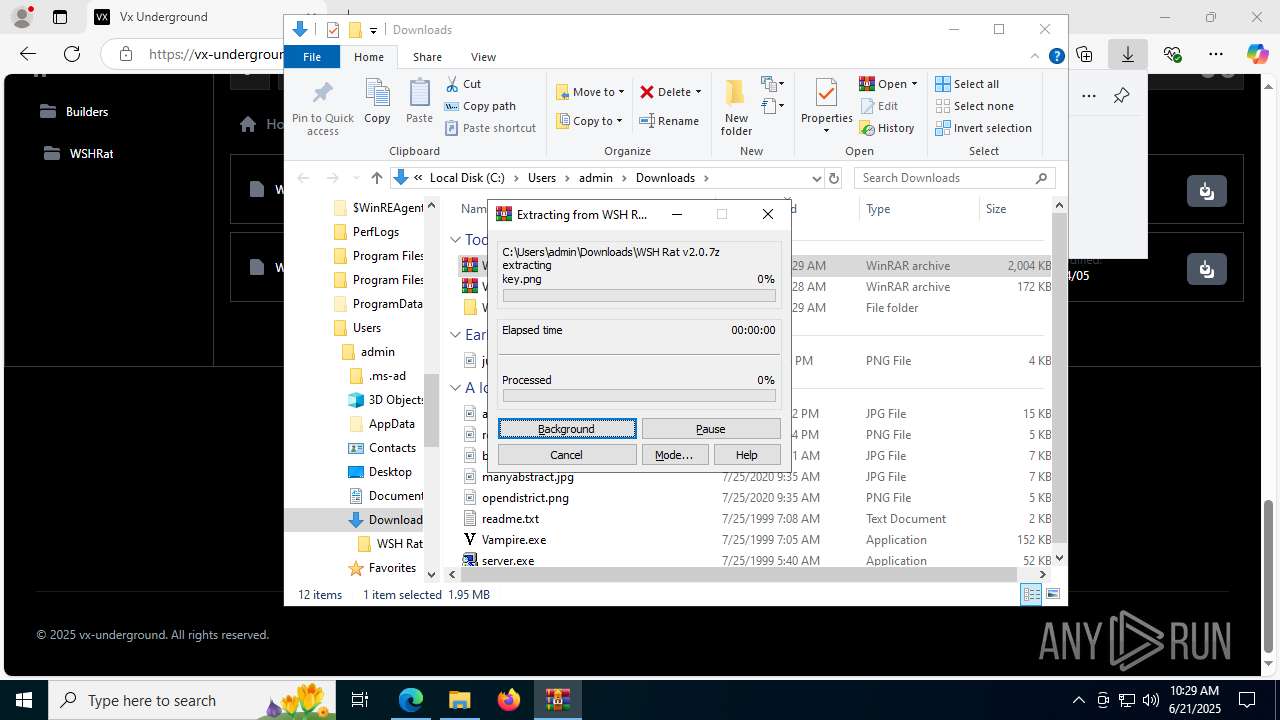
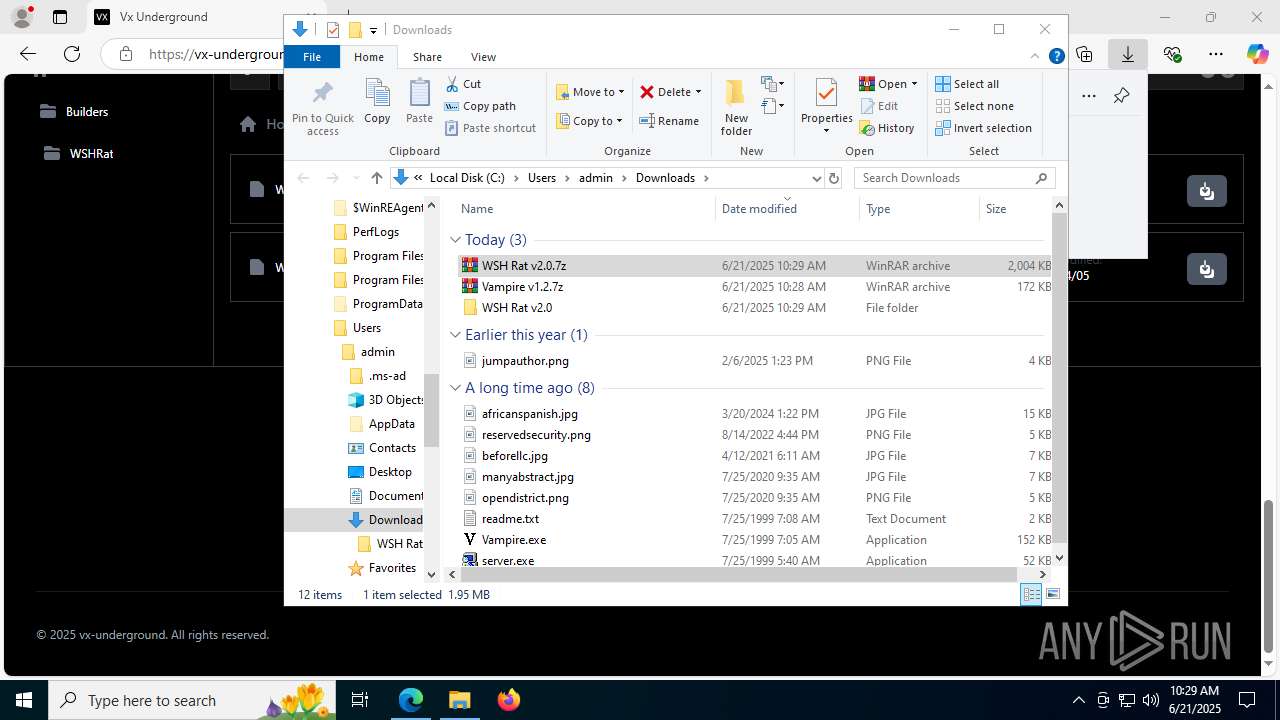
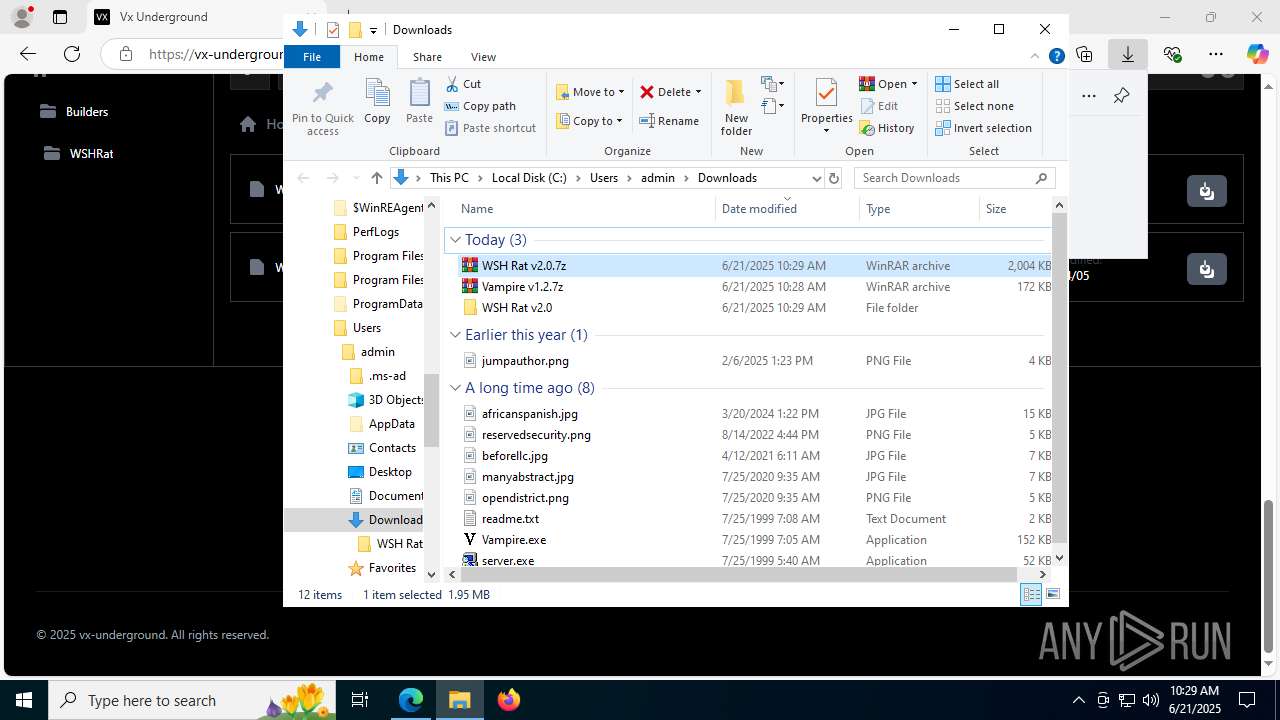
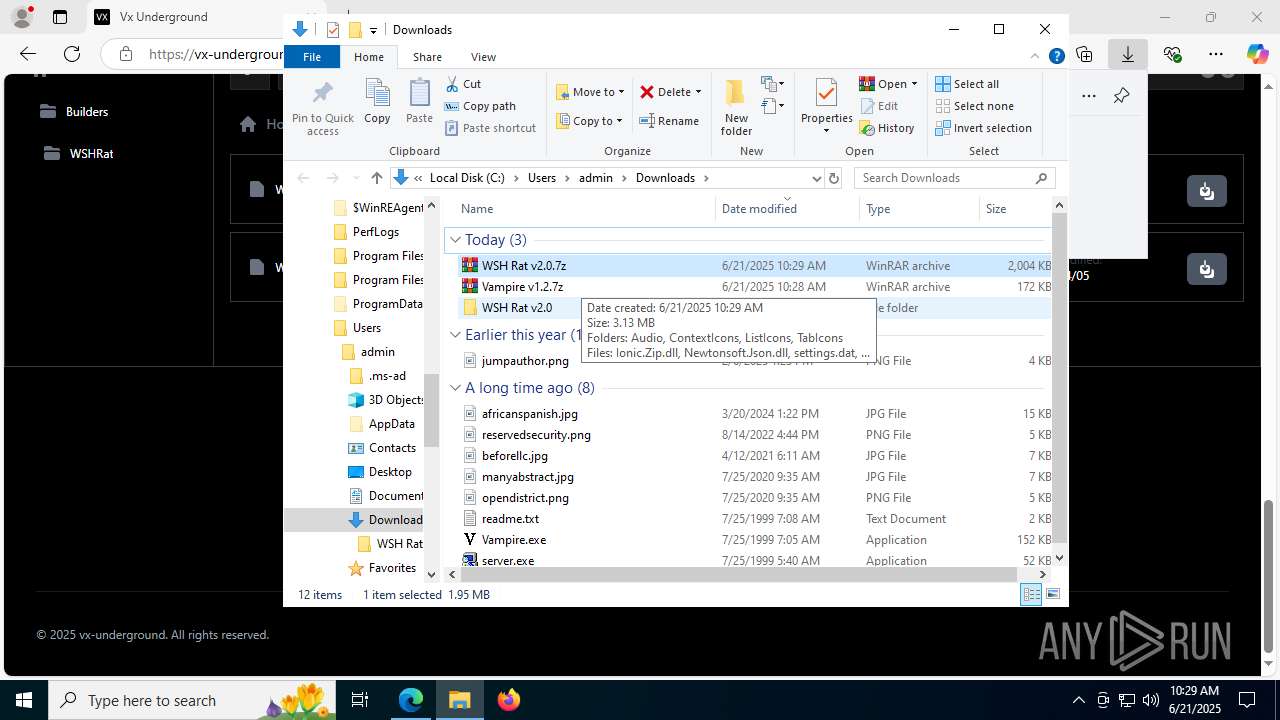
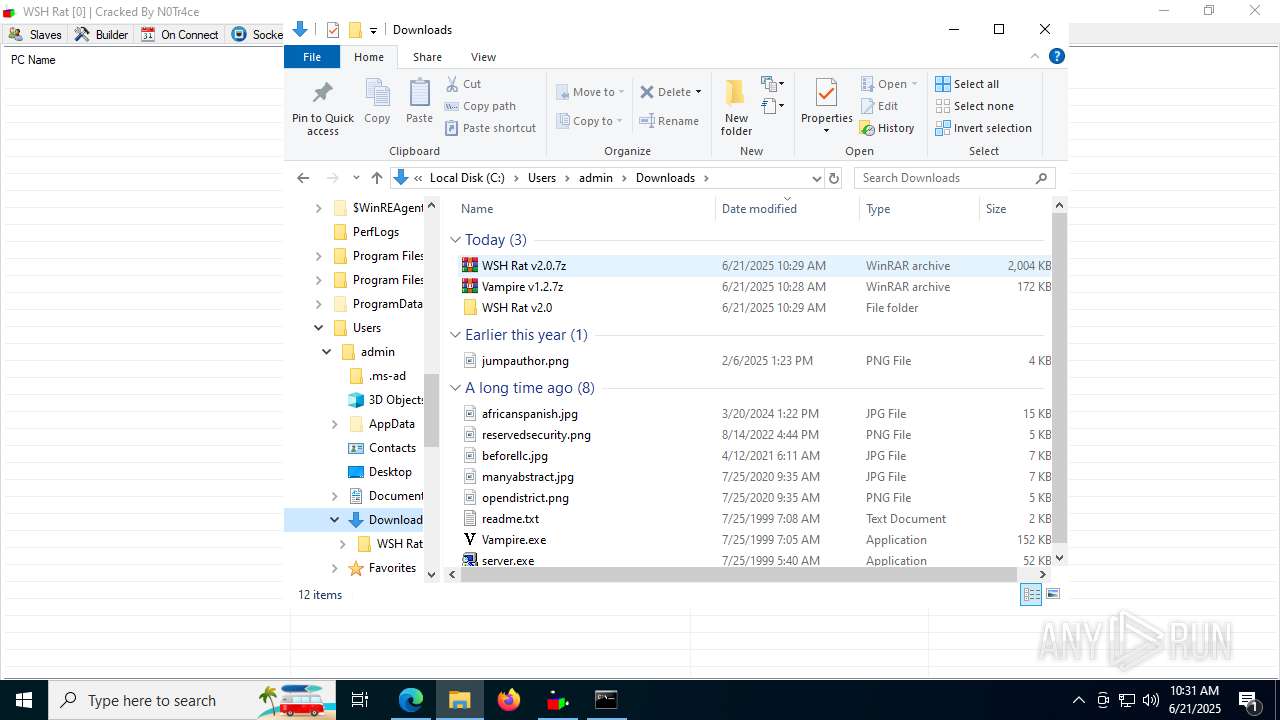
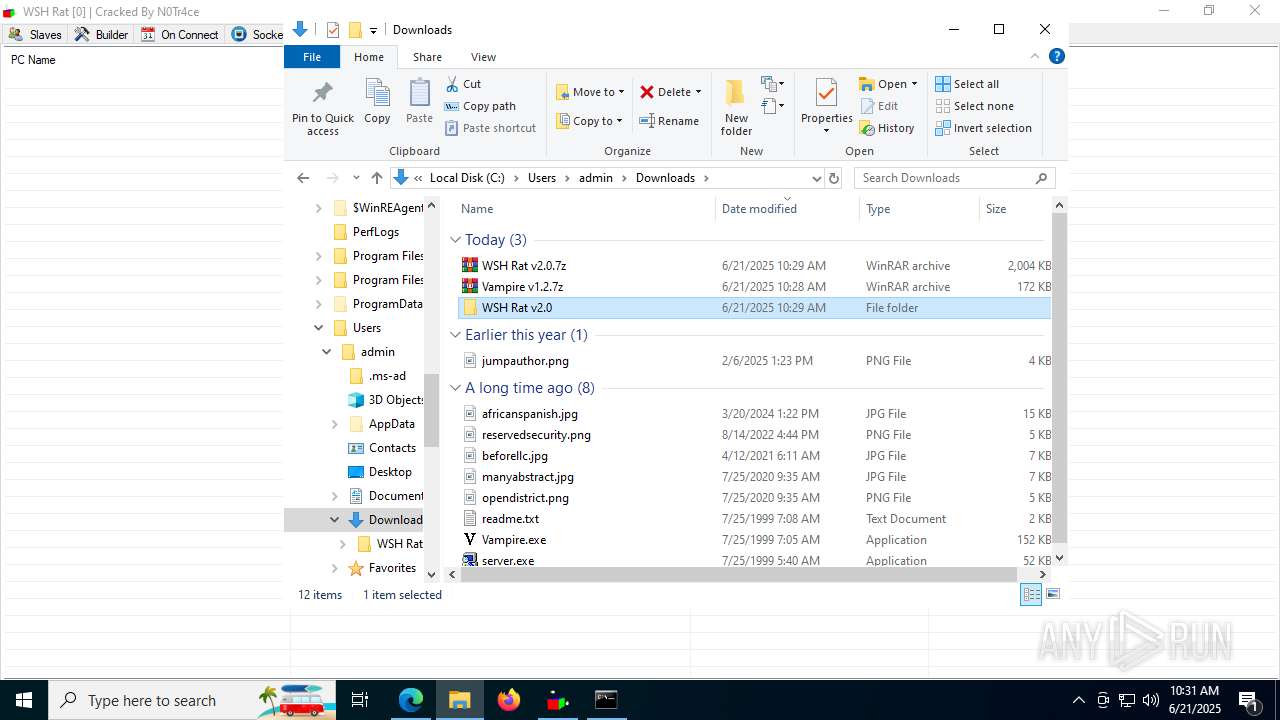
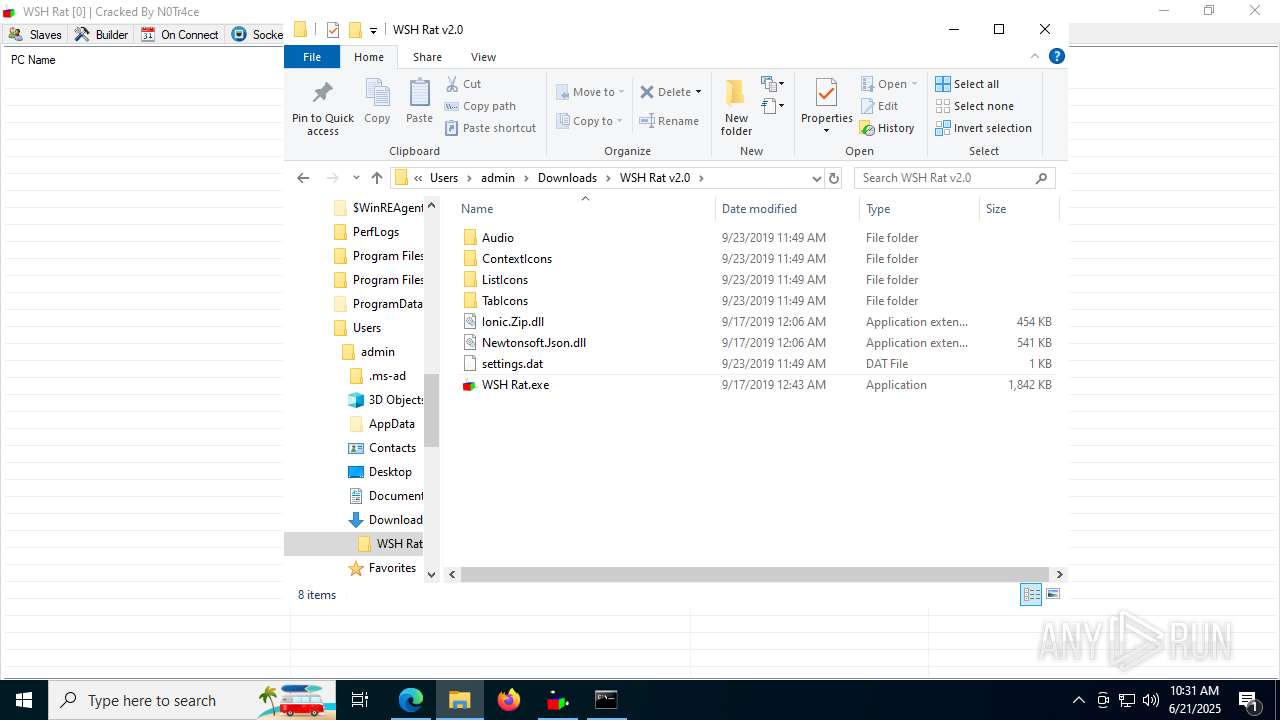
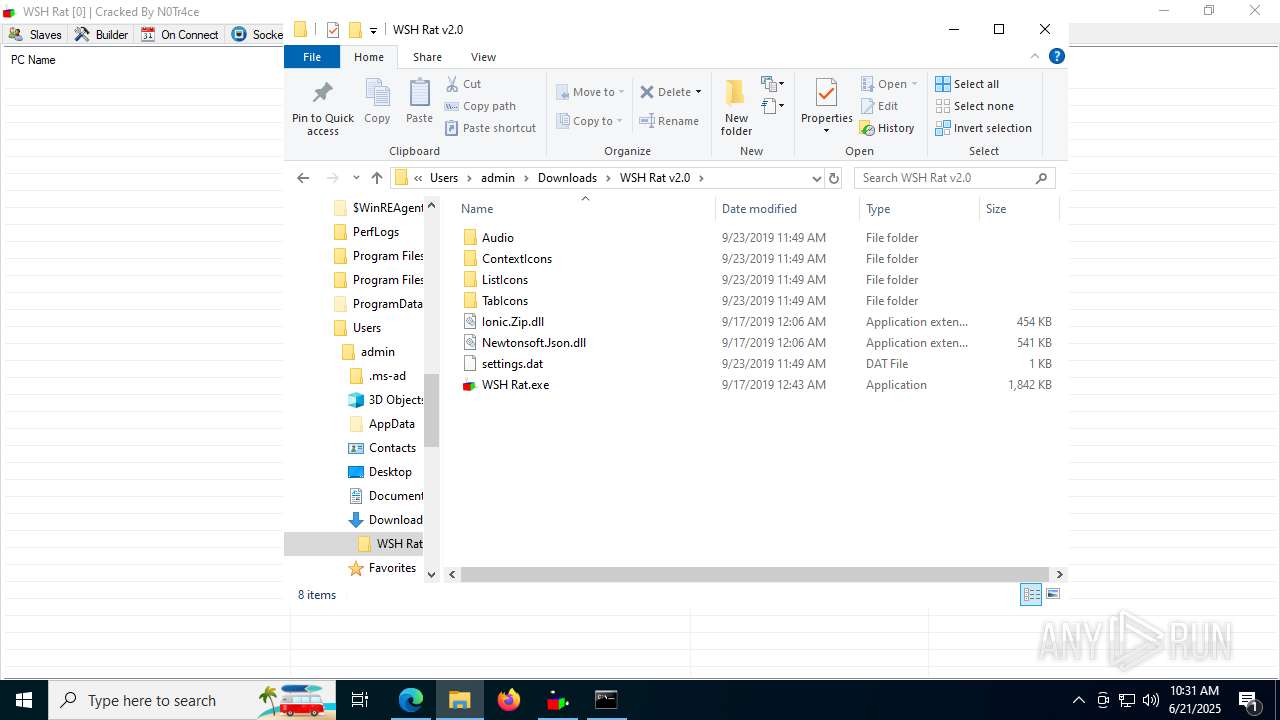
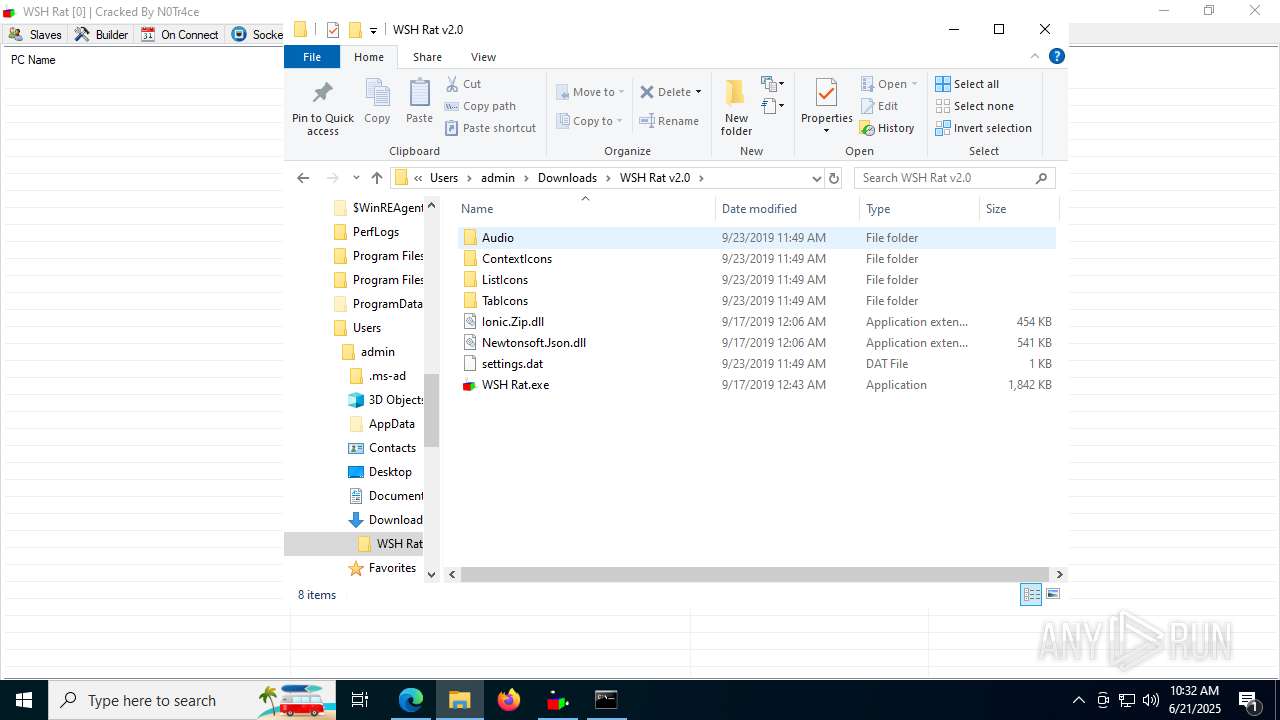
Launching a file from the Downloads directory
- msedge.exe (PID: 3092)
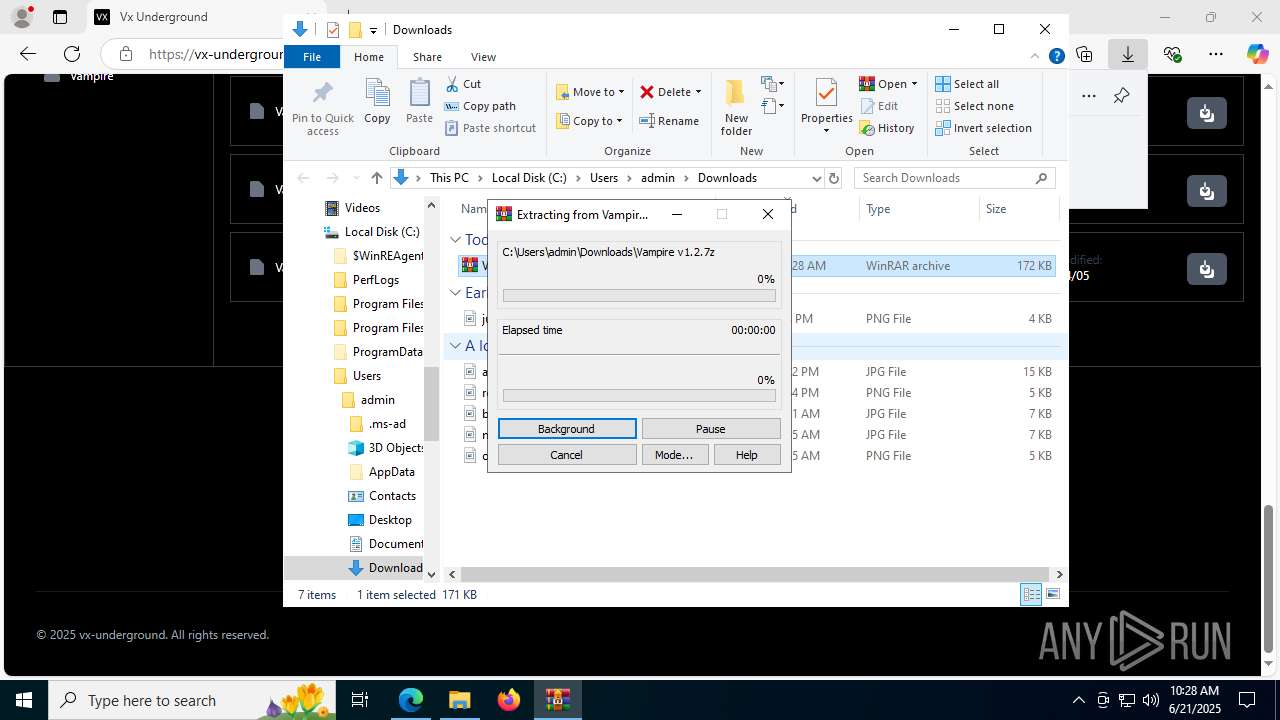
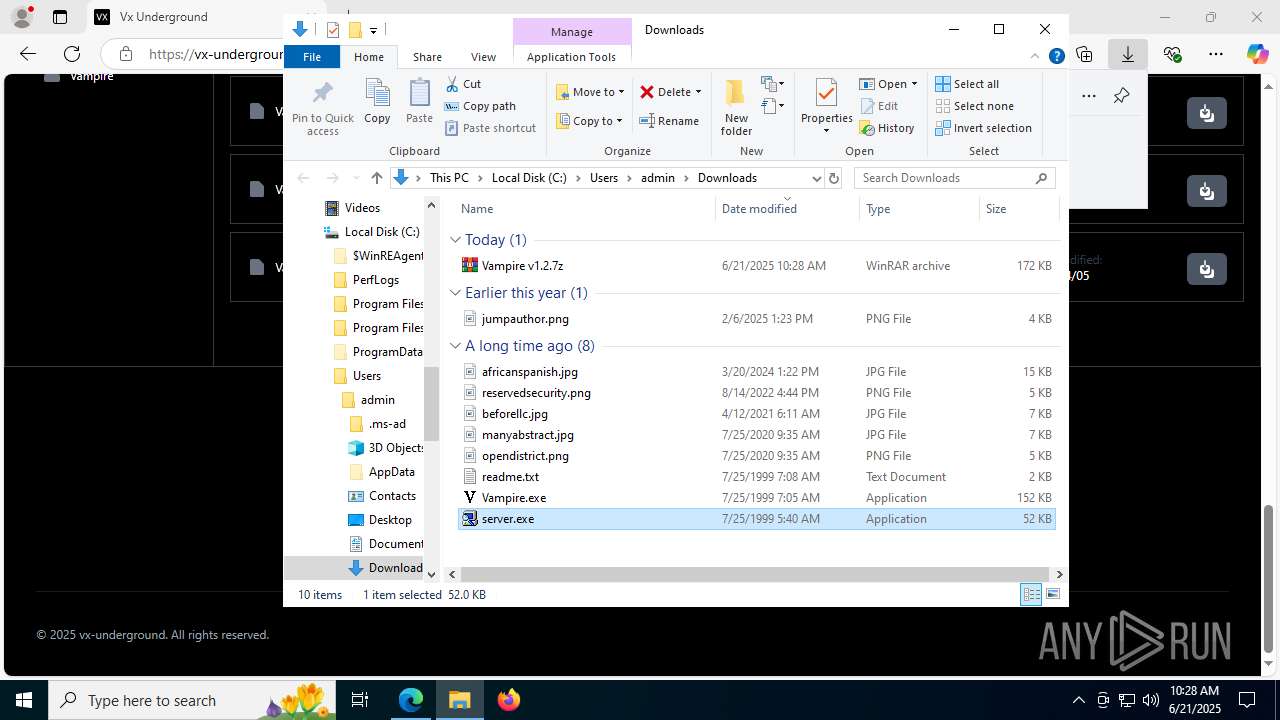
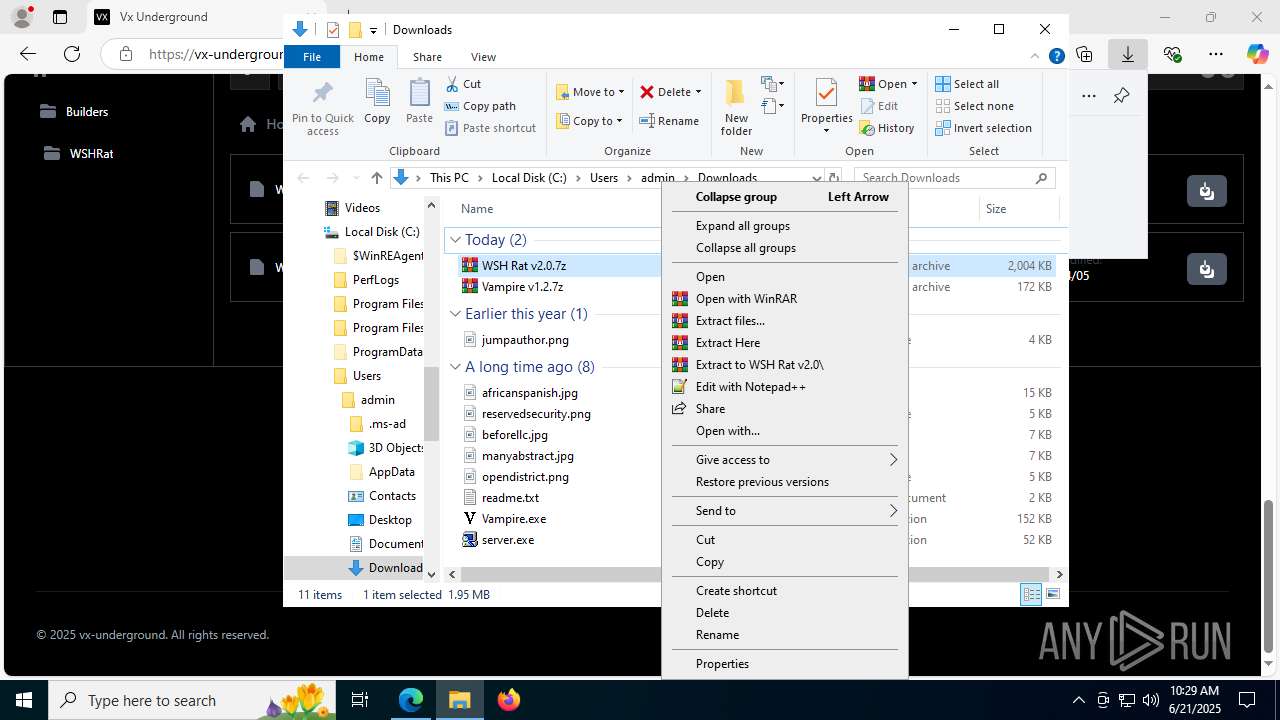
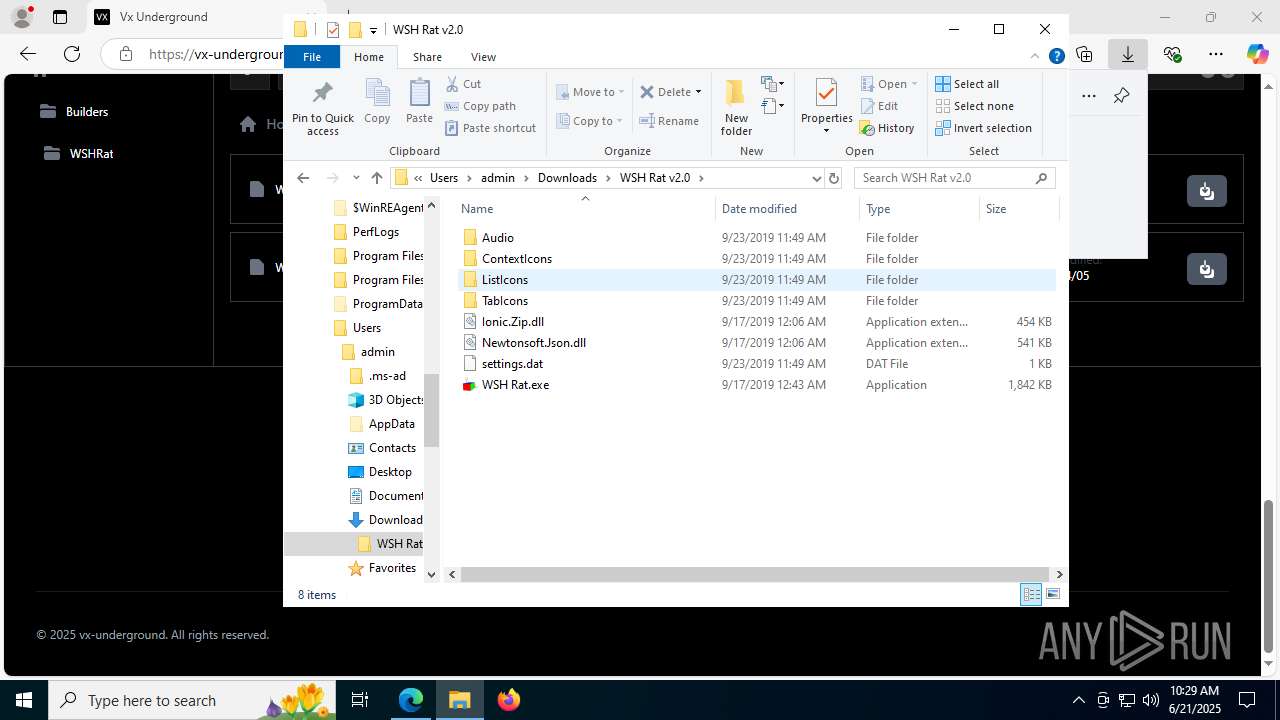
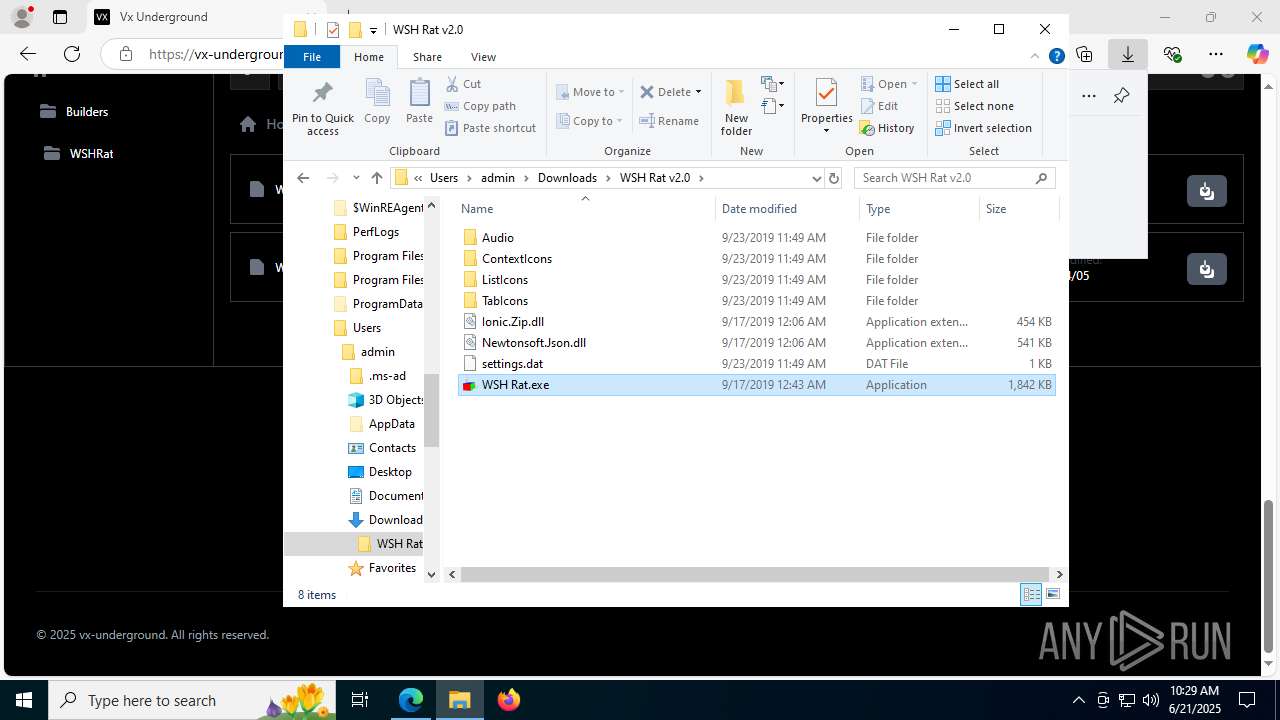
Manual execution by a user
- WinRAR.exe (PID: 6936)
- server.exe (PID: 7252)
- Vampire.exe (PID: 7756)
- server.exe (PID: 4828)
- server.exe (PID: 7604)
- WSH Rat.exe (PID: 5620)
- WinRAR.exe (PID: 5140)
- cmd.exe (PID: 5532)
- wscript.exe (PID: 5352)
- wscript.exe (PID: 7596)
- wscript.exe (PID: 6140)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6936)
- WinRAR.exe (PID: 5140)
Create files in a temporary directory
- server.exe (PID: 7252)
- Vampire.exe (PID: 7756)
- server.exe (PID: 4828)
- server.exe (PID: 7604)
Reads the machine GUID from the registry
- WSH Rat.exe (PID: 5620)
Checks proxy server information
- slui.exe (PID: 3576)
- wscript.exe (PID: 3624)
Reads the software policy settings
- slui.exe (PID: 3576)
Launching a file from the Startup directory
- wscript.exe (PID: 7596)
- wscript.exe (PID: 3624)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
212
Monitored processes
62
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 480 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4984,i,12889168259664332149,18109832344545684798,262144 --variations-seed-version --mojo-platform-channel-handle=4260 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1128 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7136,i,12889168259664332149,18109832344545684798,262144 --variations-seed-version --mojo-platform-channel-handle=5544 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1356 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3612,i,12889168259664332149,18109832344545684798,262144 --variations-seed-version --mojo-platform-channel-handle=3652 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1868 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4416,i,12889168259664332149,18109832344545684798,262144 --variations-seed-version --mojo-platform-channel-handle=6824 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2140 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2776,i,12889168259664332149,18109832344545684798,262144 --variations-seed-version --mojo-platform-channel-handle=2792 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2512 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffc4378f208,0x7ffc4378f214,0x7ffc4378f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2552 | "C:\Windows\System32\wscript.exe" //B "C:\Users\admin\AppData\Local\Temp\nhhh.vbs" | C:\Windows\System32\wscript.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 2980 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=1576,i,12889168259664332149,18109832344545684798,262144 --variations-seed-version --mojo-platform-channel-handle=5592 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3092 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://vx-underground.org/Builders/Vampire" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
23 227
Read events
23 009
Write events
200
Delete events
18
Modification events
| (PID) Process: | (3092) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3092) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3092) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3092) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3092) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3092) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 4070B8B6A8962F00 | |||
| (PID) Process: | (3092) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3092) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394070 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D332019A-2412-44D5-9C57-33CBA53F51A9} | |||
| (PID) Process: | (3092) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394070 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {EA15F4DD-E135-47A0-A782-DF71637F7A22} | |||
| (PID) Process: | (3092) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394070 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {560DC1B6-513F-4ACB-9435-8AC06B9FA39D} | |||
Executable files
15
Suspicious files
190
Text files
390
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3092 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF176457.TMP | — | |
MD5:— | SHA256:— | |||
| 3092 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF176457.TMP | — | |
MD5:— | SHA256:— | |||
| 3092 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3092 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3092 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF176476.TMP | — | |
MD5:— | SHA256:— | |||
| 3092 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3092 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF176486.TMP | — | |
MD5:— | SHA256:— | |||
| 3092 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3092 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF176486.TMP | — | |
MD5:— | SHA256:— | |||
| 3092 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
98
DNS requests
84
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.55.104.190:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6532 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:f6Qpp3whkHj6nWX-RyTnf0g3EjeKyoT4iufrJy2HfD0&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
5080 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7240 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3048 | svchost.exe | HEAD | 200 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751066851&P2=404&P3=2&P4=PsCzt%2breW7ZUxvz%2fOO2cjaay%2bb%2fM%2bOpQ%2b3RdGg465GyrdJVuPJ8lLs8dl5f6bSS%2f9p8IXFjTkm%2bdS5VdiCescQ%3d%3d | unknown | — | — | whitelisted |
7240 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3048 | svchost.exe | GET | 206 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751066851&P2=404&P3=2&P4=PsCzt%2breW7ZUxvz%2fOO2cjaay%2bb%2fM%2bOpQ%2b3RdGg465GyrdJVuPJ8lLs8dl5f6bSS%2f9p8IXFjTkm%2bdS5VdiCescQ%3d%3d | unknown | — | — | whitelisted |
3048 | svchost.exe | GET | 206 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751066851&P2=404&P3=2&P4=PsCzt%2breW7ZUxvz%2fOO2cjaay%2bb%2fM%2bOpQ%2b3RdGg465GyrdJVuPJ8lLs8dl5f6bSS%2f9p8IXFjTkm%2bdS5VdiCescQ%3d%3d | unknown | — | — | whitelisted |
3048 | svchost.exe | HEAD | 200 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1751066852&P2=404&P3=2&P4=Um44CYFLJfv5bl0jXgiddGi1%2b%2brRbCOSXE%2b4jbm743MFZ3e%2fBx2KtMakhi3FGQAi4jIlausF5M4wzvDIW45E5Q%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.55.104.190:80 | crl.microsoft.com | Akamai International B.V. | US | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6532 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6532 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6532 | msedge.exe | 104.18.95.41:443 | challenges.cloudflare.com | CLOUDFLARENET | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
vx-underground.org |
| malicious |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
challenges.cloudflare.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6532 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
6532 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
2200 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2200 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
3624 | wscript.exe | Misc activity | ET INFO Observed UA-CPU Header |
3624 | wscript.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |