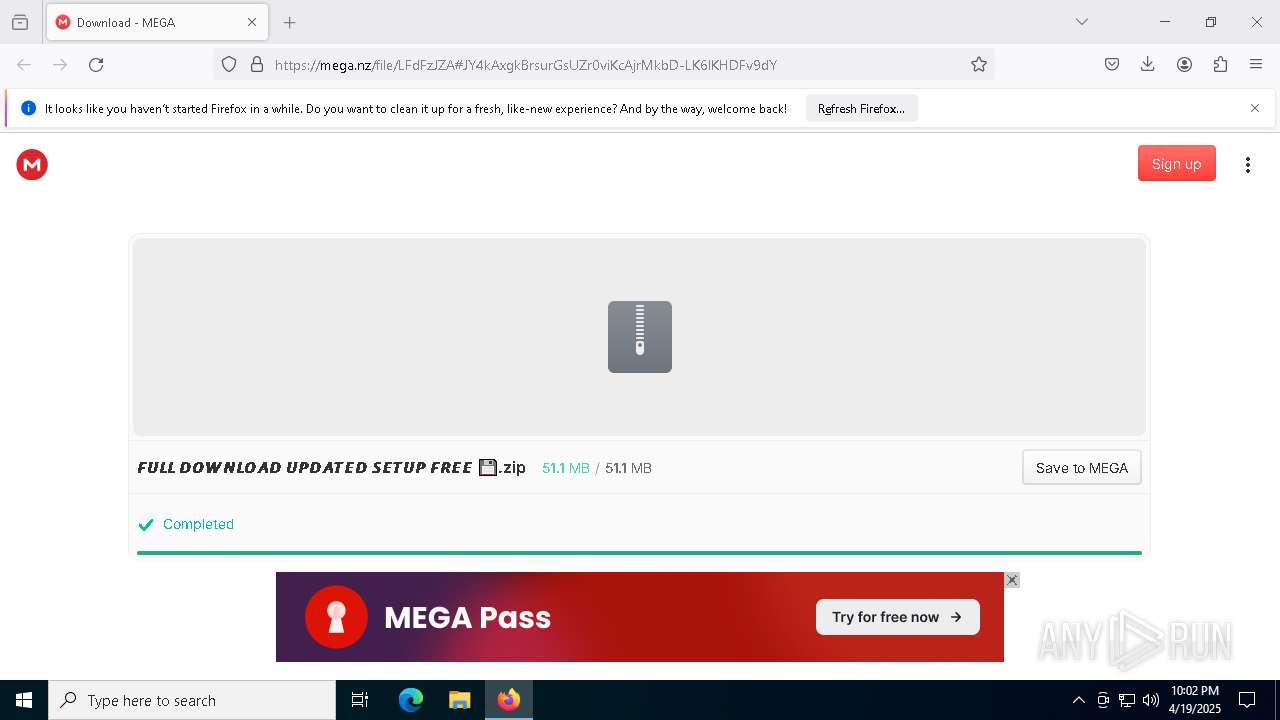
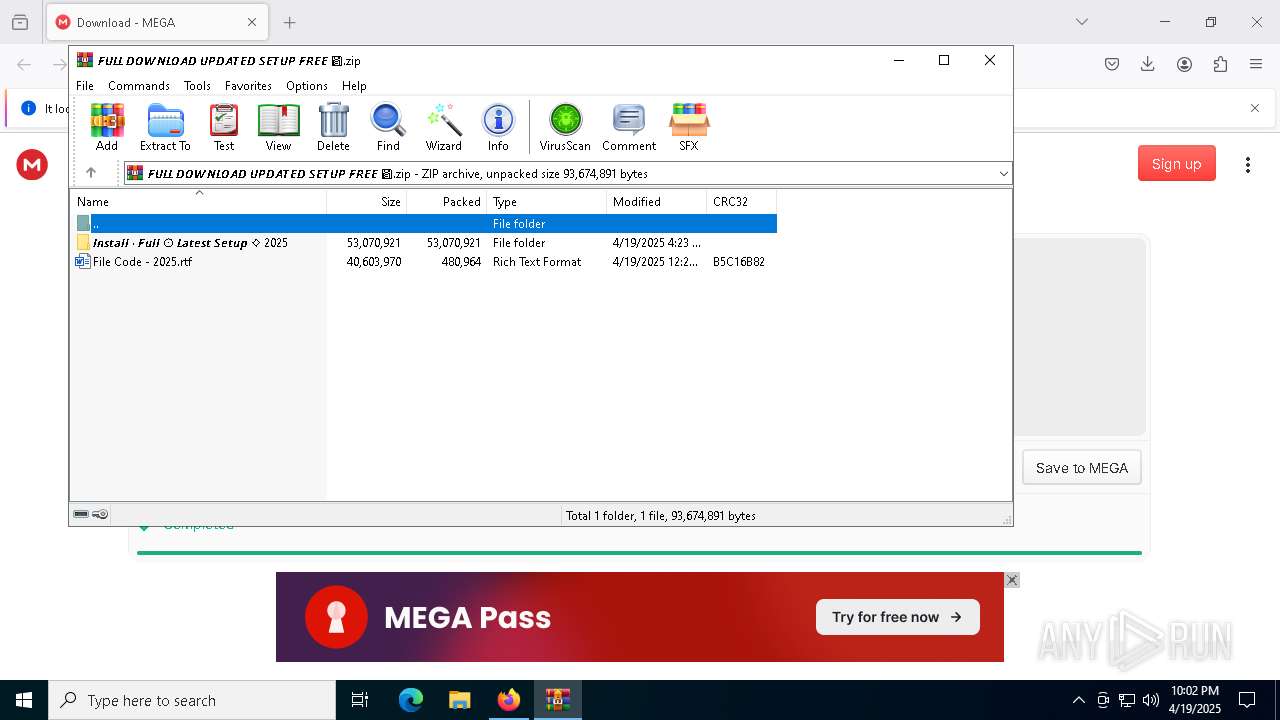
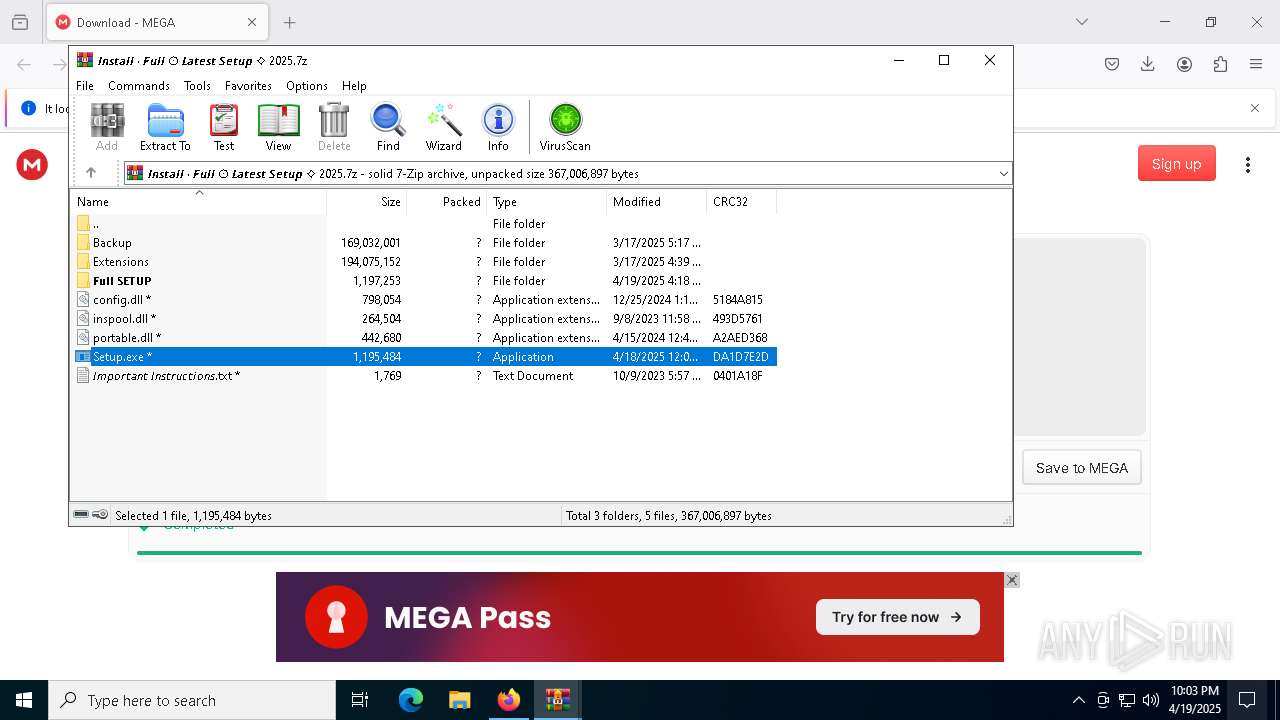
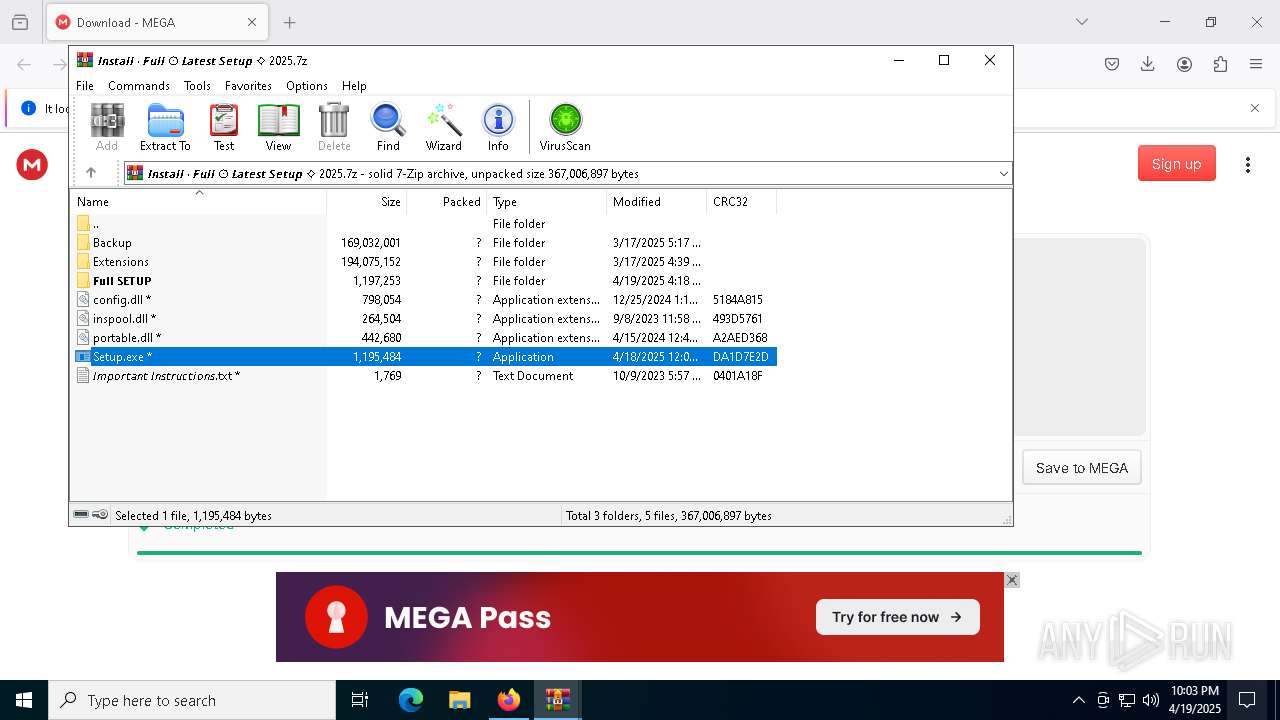
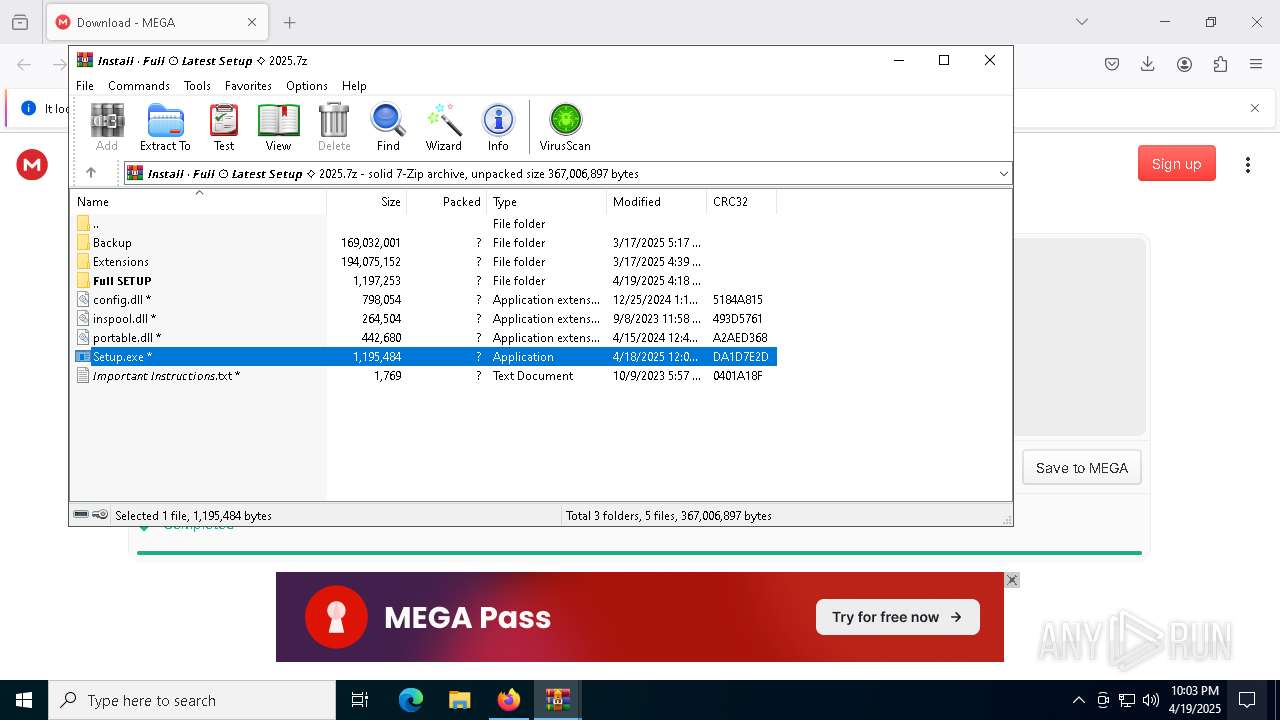
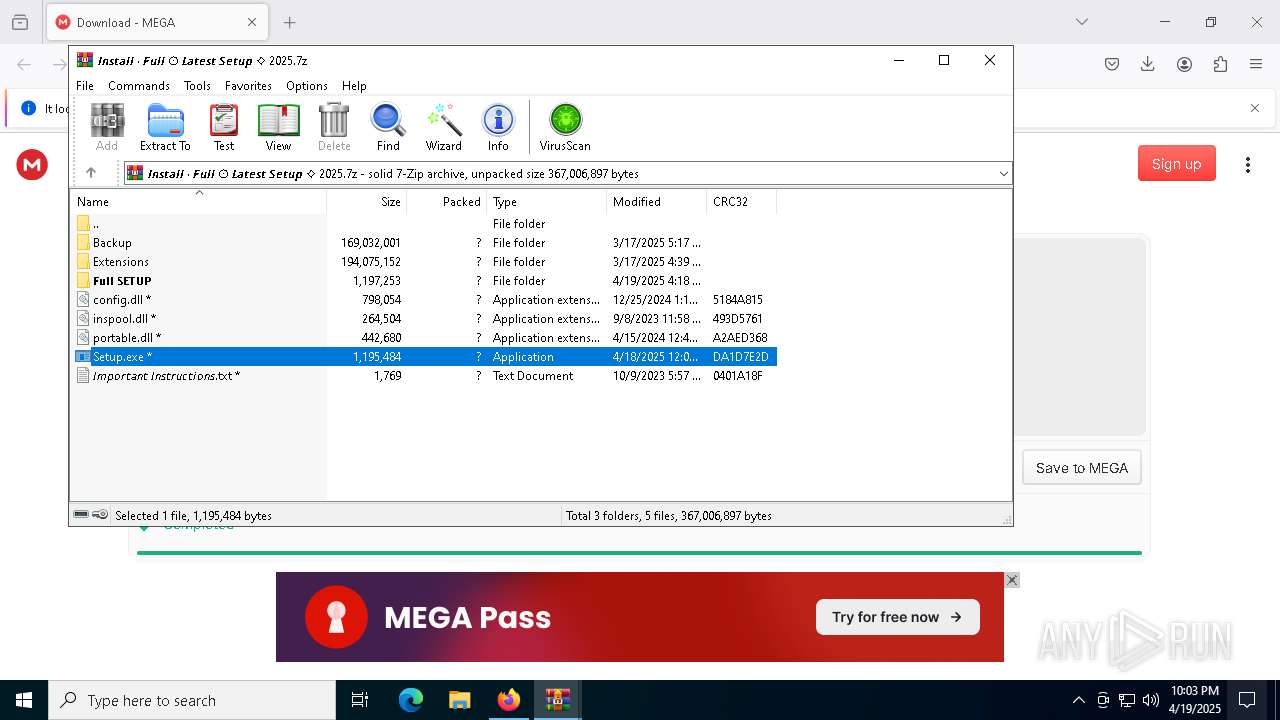
| URL: | https://mega.nz/file/LFdFzJZA#JY4kAxgkBrsurGsUZr0viKcAjrMkbD-LK6lKHDFv9dY |
| Full analysis: | https://app.any.run/tasks/735e1f9a-8caa-433a-a47f-46f827926757 |
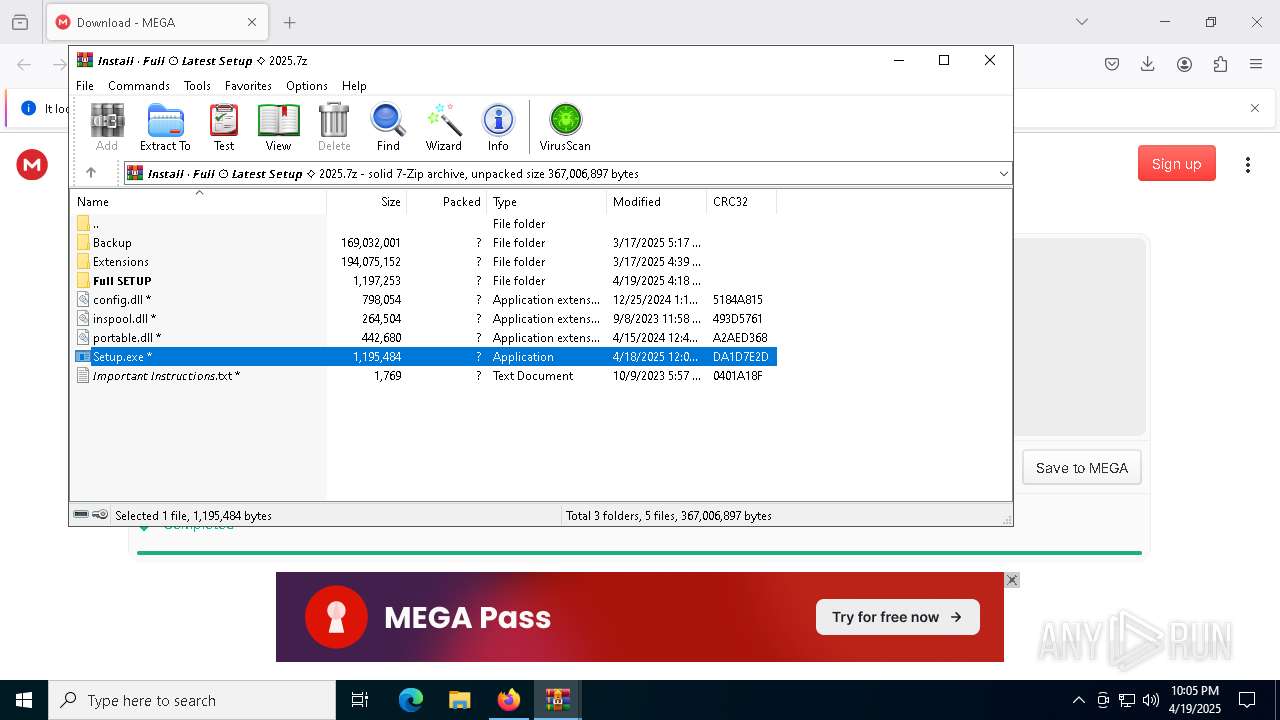
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | April 19, 2025, 22:01:19 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1CE73D2FBBC4794A7B8F97E856A77D1B |
| SHA1: | 0C35B5380065AD7C2BE70B297FA7CB752D2843AB |
| SHA256: | B07E50BEC7F44451FEF7BA2AD629B86F41019CC8719B1668B6F778383A244E30 |
| SSDEEP: | 3:N8X/i+1v/kXLd1GQFw/XVoXo8:2XkZJFw/XCXo8 |
MALICIOUS
Executing a file with an untrusted certificate
- Setup.exe (PID: 7252)
- OE9OXDN1NNDY5GYVW.exe (PID: 6132)
Steals credentials from Web Browsers
- Levitra.com (PID: 2568)
LUMMA has been detected (SURICATA)
- Levitra.com (PID: 2568)
- svchost.exe (PID: 2196)
LUMMA mutex has been found
- Levitra.com (PID: 2568)
Actions looks like stealing of personal data
- Levitra.com (PID: 2568)
Changes the autorun value in the registry
- OE9OXDN1NNDY5GYVW.exe (PID: 6132)
AutoIt loader has been detected (YARA)
- Levitra.com (PID: 2568)
Connects to the CnC server
- svchost.exe (PID: 2196)
SUSPICIOUS
Application launched itself
- WinRAR.exe (PID: 6940)
- cmd.exe (PID: 7200)
Process drops legitimate windows executable
- WinRAR.exe (PID: 5112)
The process creates files with name similar to system file names
- WinRAR.exe (PID: 5112)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5112)
- Setup.exe (PID: 7252)
- WinRAR.exe (PID: 6940)
- OE9OXDN1NNDY5GYVW.exe (PID: 6132)
Starts CMD.EXE for commands execution
- Setup.exe (PID: 7252)
- cmd.exe (PID: 7200)
Executing commands from a ".bat" file
- Setup.exe (PID: 7252)
Get information on the list of running processes
- cmd.exe (PID: 7200)
Starts application with an unusual extension
- cmd.exe (PID: 7200)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7200)
Starts the AutoIt3 executable file
- cmd.exe (PID: 7200)
The executable file from the user directory is run by the CMD process
- Levitra.com (PID: 2568)
There is functionality for taking screenshot (YARA)
- Setup.exe (PID: 7252)
- Levitra.com (PID: 2568)
- OE9OXDN1NNDY5GYVW.exe (PID: 6132)
Contacting a server suspected of hosting an CnC
- Levitra.com (PID: 2568)
- svchost.exe (PID: 2196)
Searches for installed software
- Levitra.com (PID: 2568)
Executable content was dropped or overwritten
- Levitra.com (PID: 2568)
- OE9OXDN1NNDY5GYVW.exe (PID: 6132)
Found regular expressions for crypto-addresses (YARA)
- OE9OXDN1NNDY5GYVW.exe (PID: 6132)
Connects to unusual port
- OE9OXDN1NNDY5GYVW.exe (PID: 6132)
INFO
Application launched itself
- firefox.exe (PID: 7388)
- firefox.exe (PID: 7356)
The sample compiled with chinese language support
- WinRAR.exe (PID: 5112)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5112)
Checks supported languages
- Setup.exe (PID: 7252)
- extrac32.exe (PID: 6240)
- Levitra.com (PID: 2568)
- OE9OXDN1NNDY5GYVW.exe (PID: 6132)
Create files in a temporary directory
- Setup.exe (PID: 7252)
- extrac32.exe (PID: 6240)
- Levitra.com (PID: 2568)
Process checks computer location settings
- Setup.exe (PID: 7252)
Manual execution by a user
- WinRAR.exe (PID: 6940)
Reads the software policy settings
- slui.exe (PID: 4212)
- slui.exe (PID: 6468)
- Levitra.com (PID: 2568)
- OE9OXDN1NNDY5GYVW.exe (PID: 6132)
The sample compiled with english language support
- WinRAR.exe (PID: 5112)
Reads the computer name
- Setup.exe (PID: 7252)
- extrac32.exe (PID: 6240)
- Levitra.com (PID: 2568)
- OE9OXDN1NNDY5GYVW.exe (PID: 6132)
Creates a new folder
- cmd.exe (PID: 6512)
Reads mouse settings
- Levitra.com (PID: 2568)
Checks proxy server information
- slui.exe (PID: 6468)
- OE9OXDN1NNDY5GYVW.exe (PID: 6132)
The sample compiled with japanese language support
- Levitra.com (PID: 2568)
- OE9OXDN1NNDY5GYVW.exe (PID: 6132)
Creates files in the program directory
- OE9OXDN1NNDY5GYVW.exe (PID: 6132)
Reads the machine GUID from the registry
- OE9OXDN1NNDY5GYVW.exe (PID: 6132)
Creates files or folders in the user directory
- OE9OXDN1NNDY5GYVW.exe (PID: 6132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
163
Monitored processes
34
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6028 -childID 8 -isForBrowser -prefsHandle 5964 -prefMapHandle 5972 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1400 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {4786a266-20fd-4fad-970d-81c626ed8254} 7388 "\\.\pipe\gecko-crash-server-pipe.7388" 2344b06f690 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2288 | findstr /I "opssvc wrsa" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2416 | findstr "SophosHealth bdservicehost AvastUI AVGUI nsWscSvc ekrn" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2568 | Levitra.com i | C:\Users\admin\AppData\Local\Temp\450545\Levitra.com | cmd.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Exit code: 0 Version: 3, 3, 15, 5 Modules
| |||||||||||||||
| 3396 | cmd /c copy /b 450545\Levitra.com + Made + Hose + Four + Gay + Beautifully + Cooked + Fla + Screenshot + Tomorrow 450545\Levitra.com | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3968 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4212 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
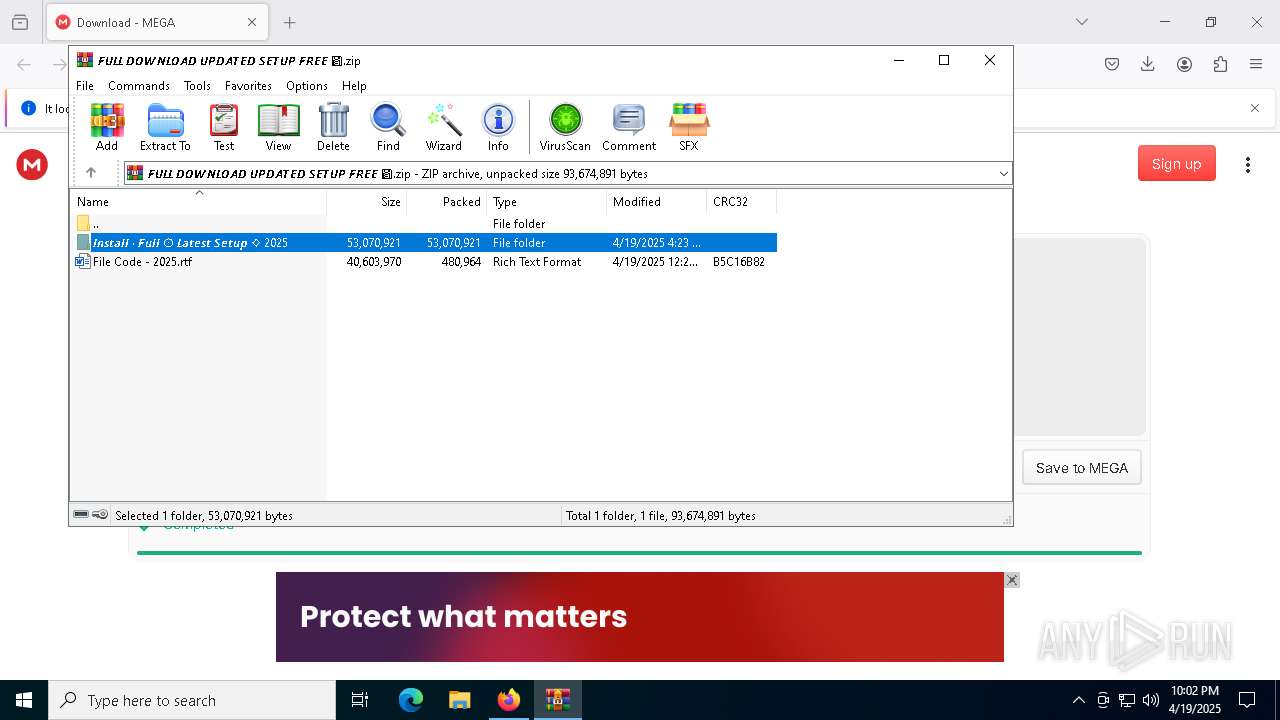
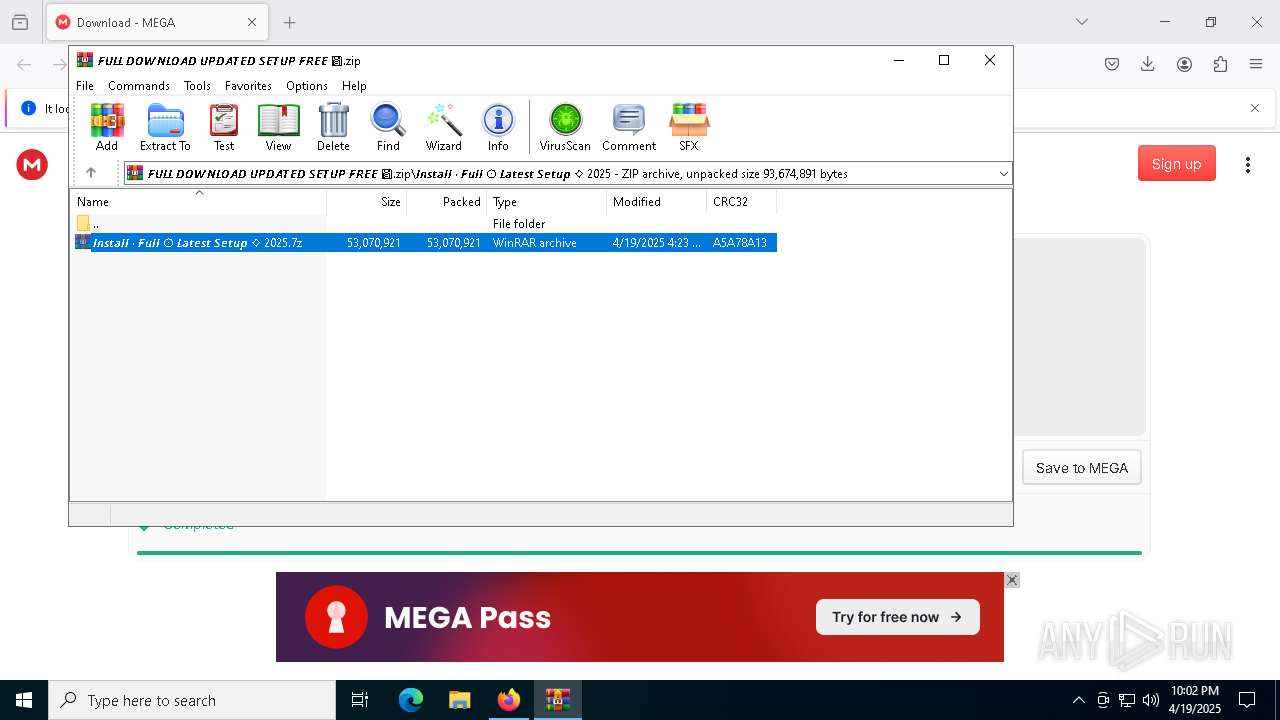
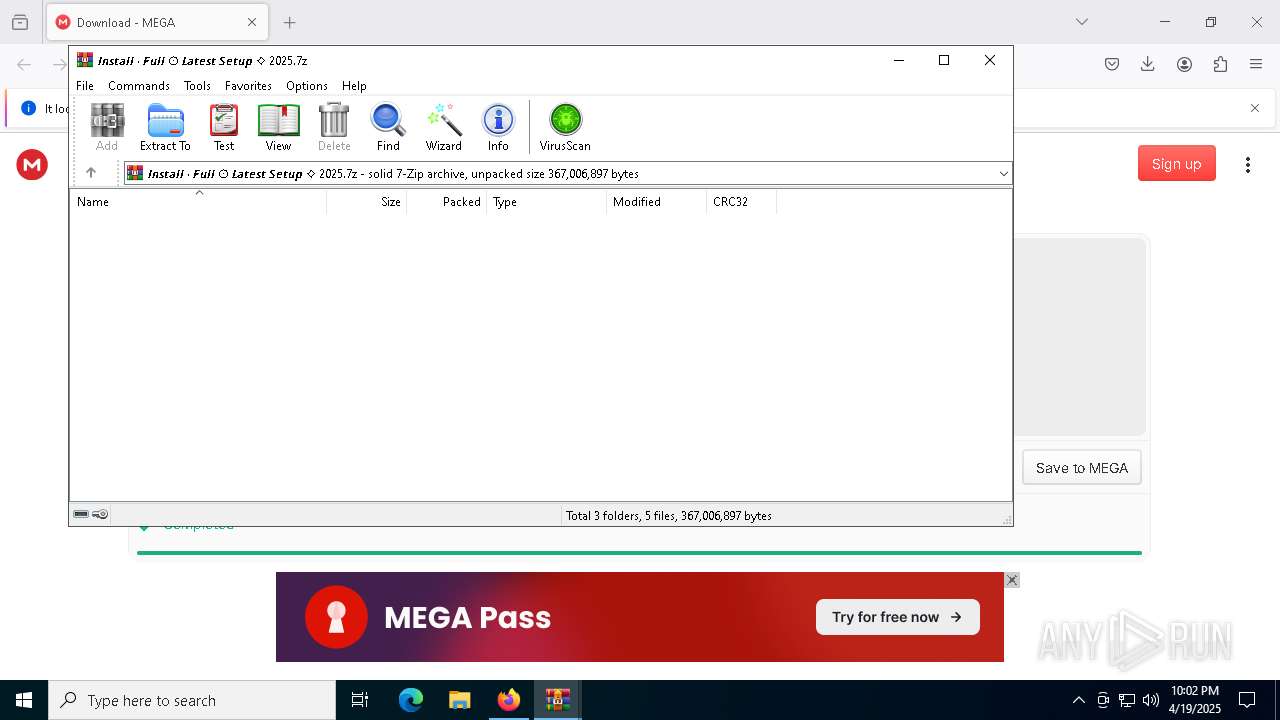
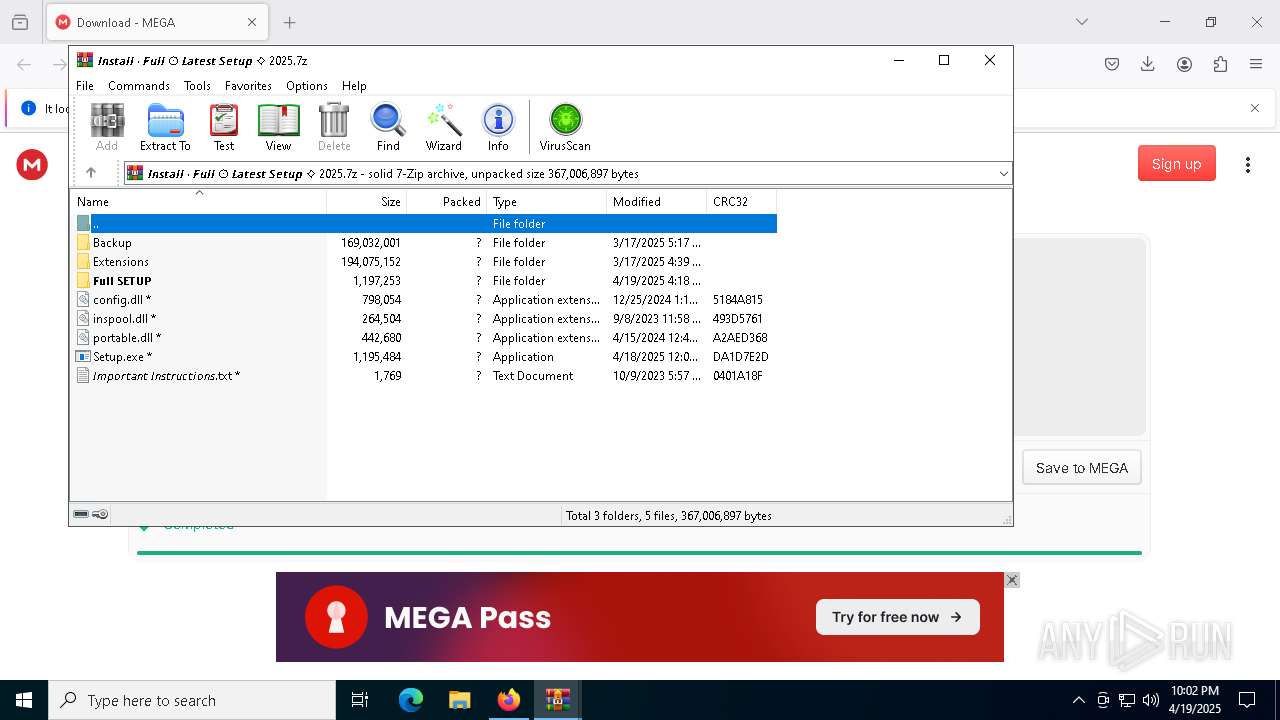
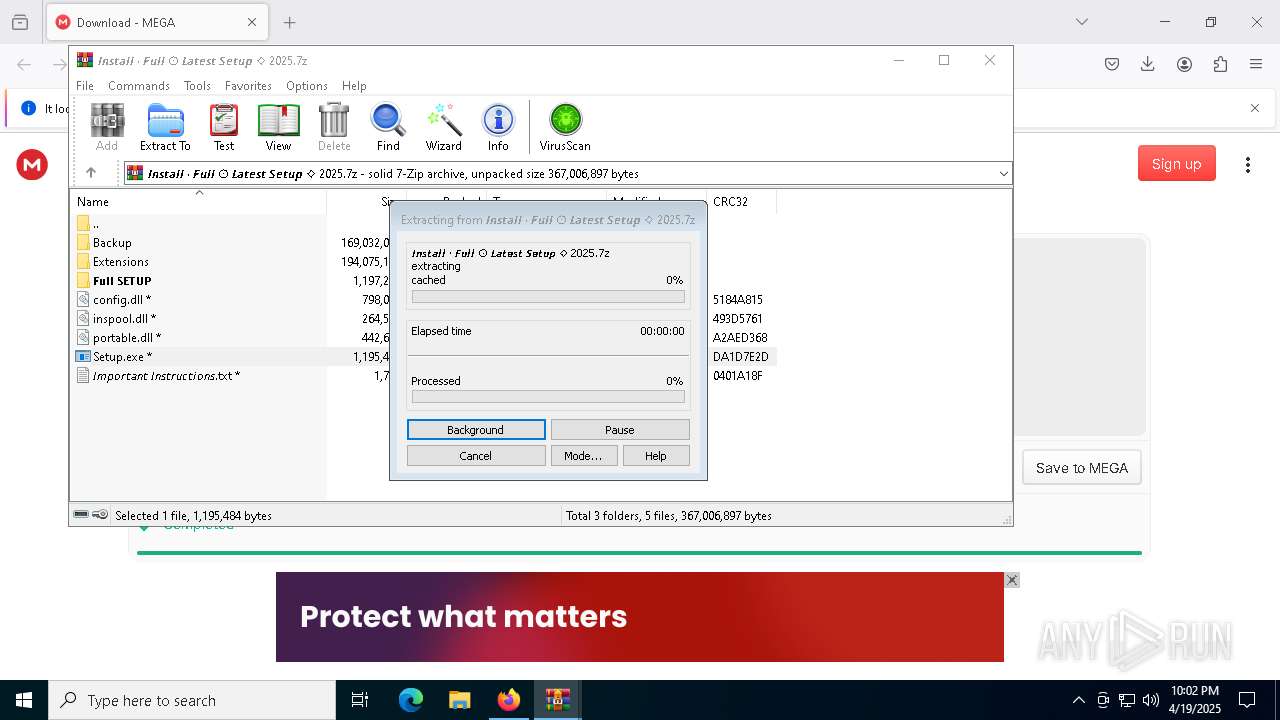
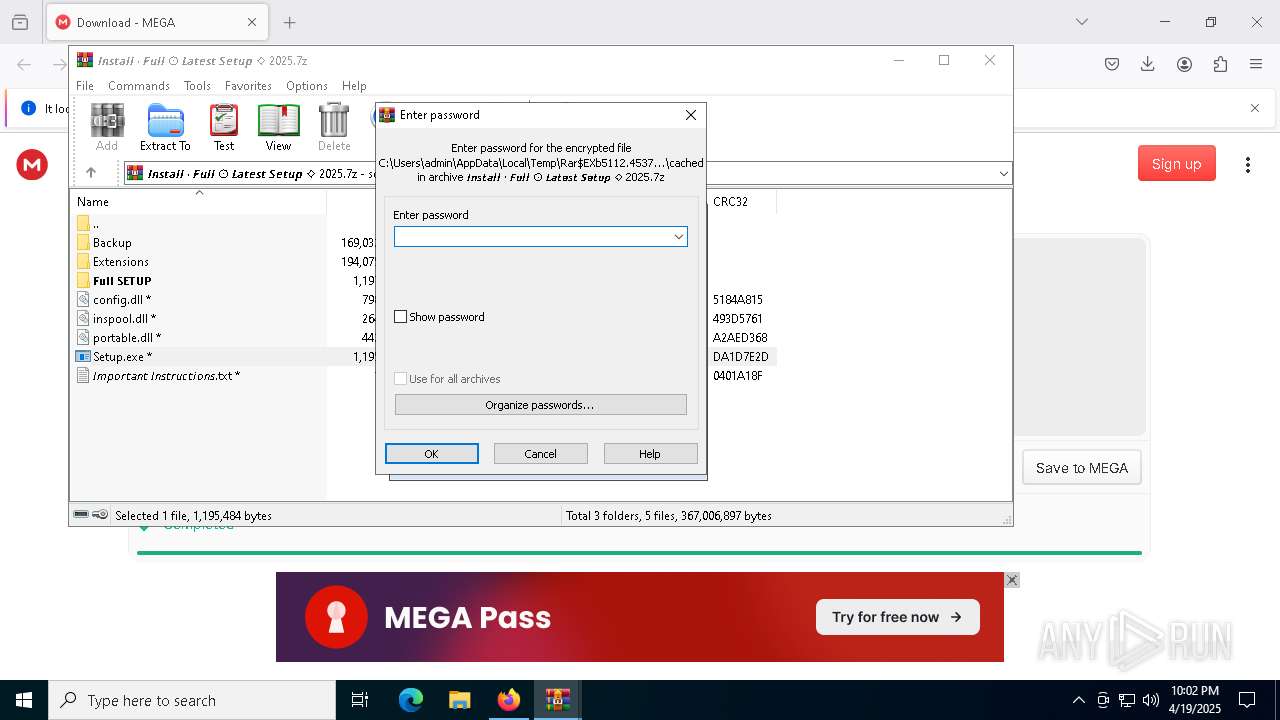
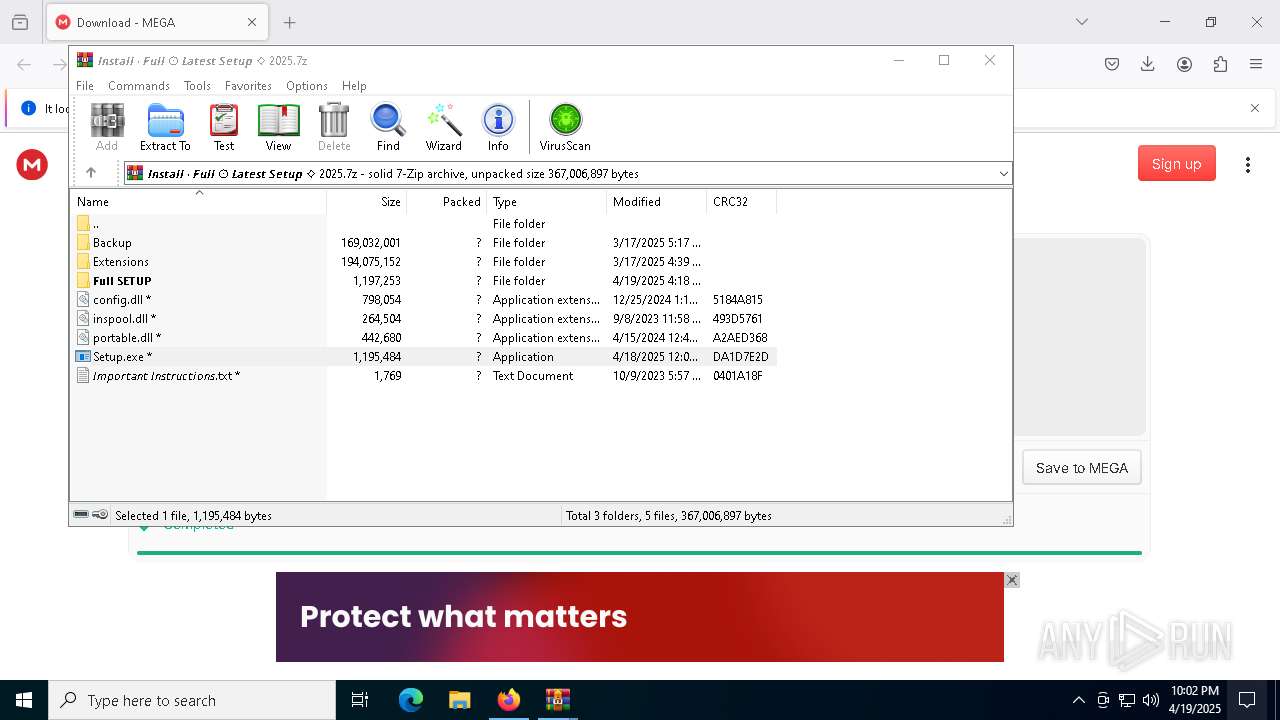
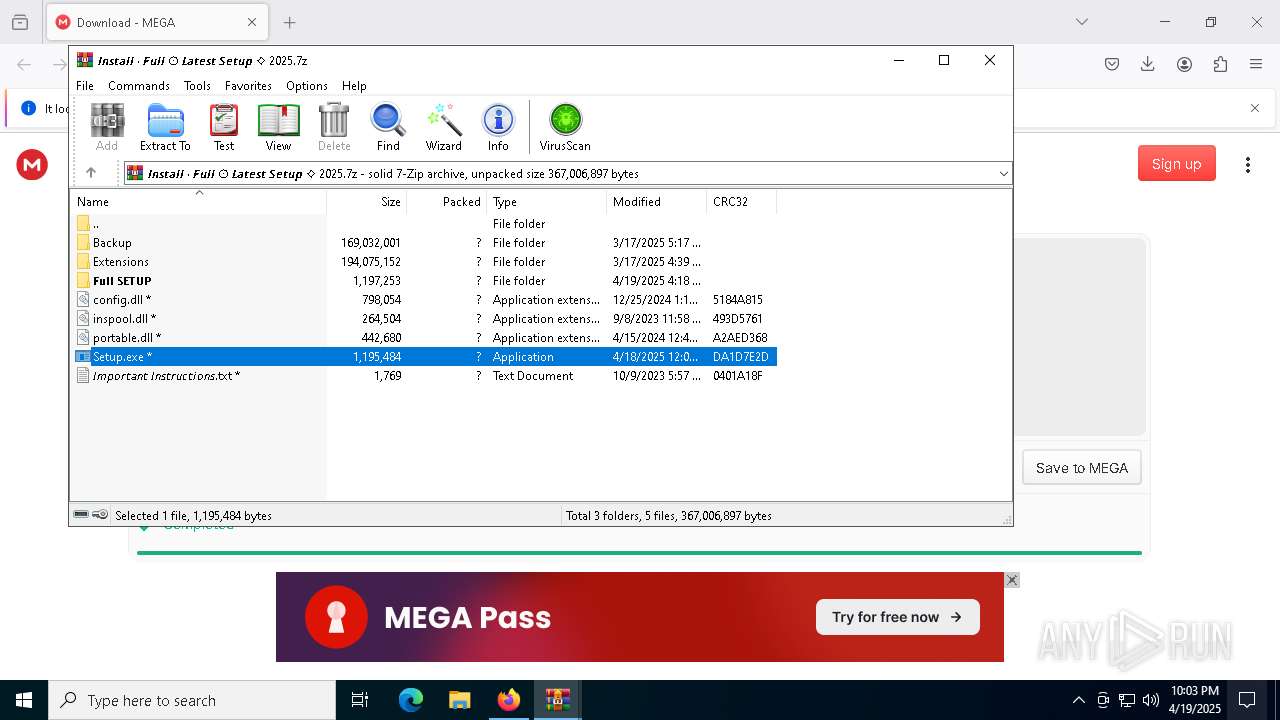
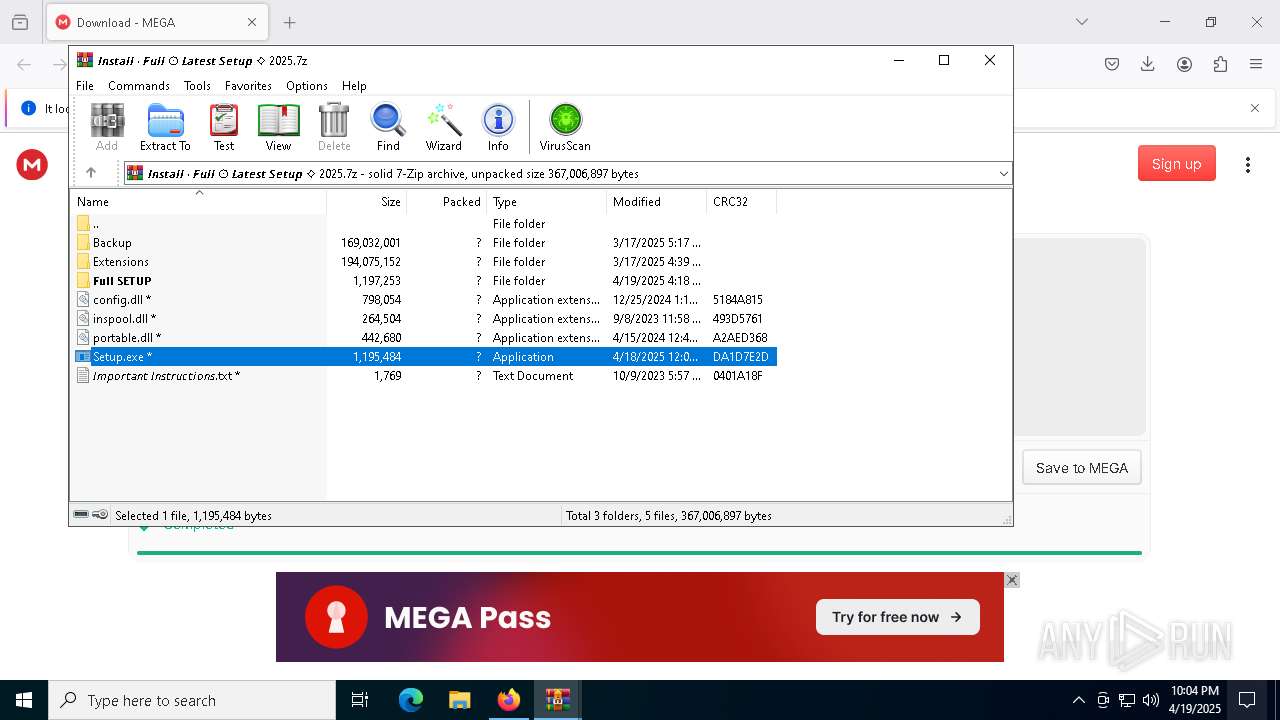
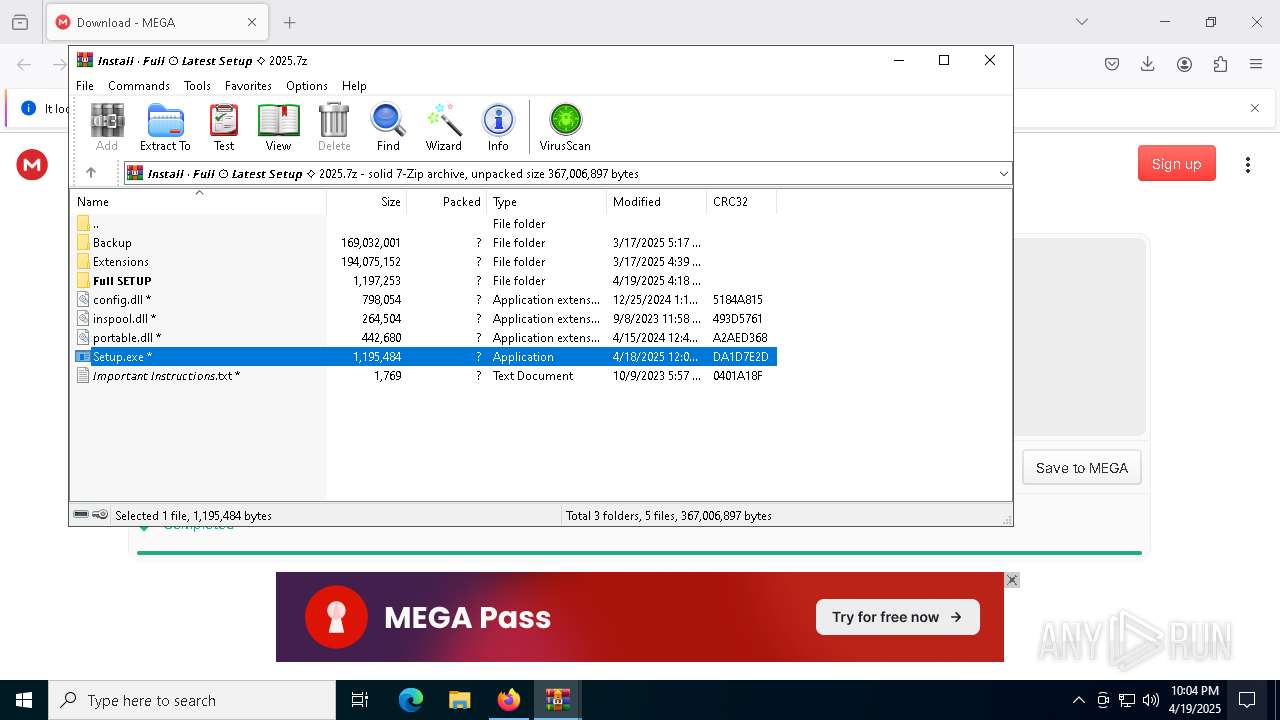
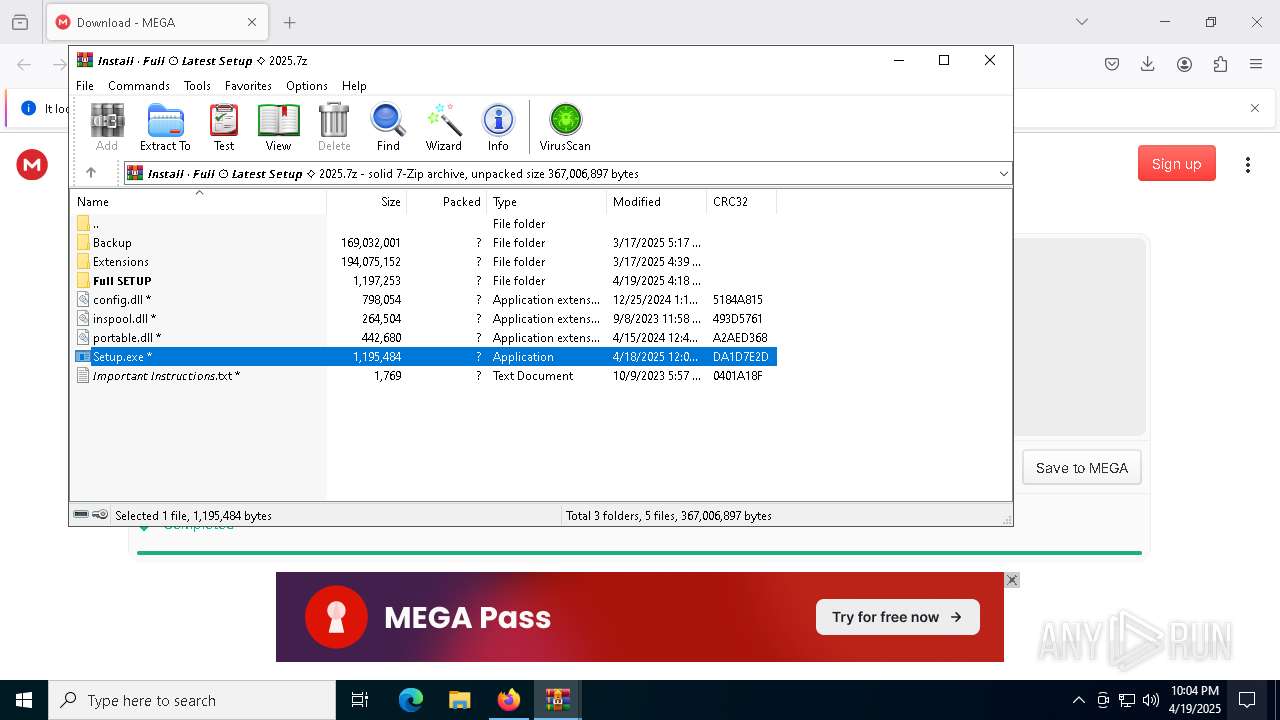
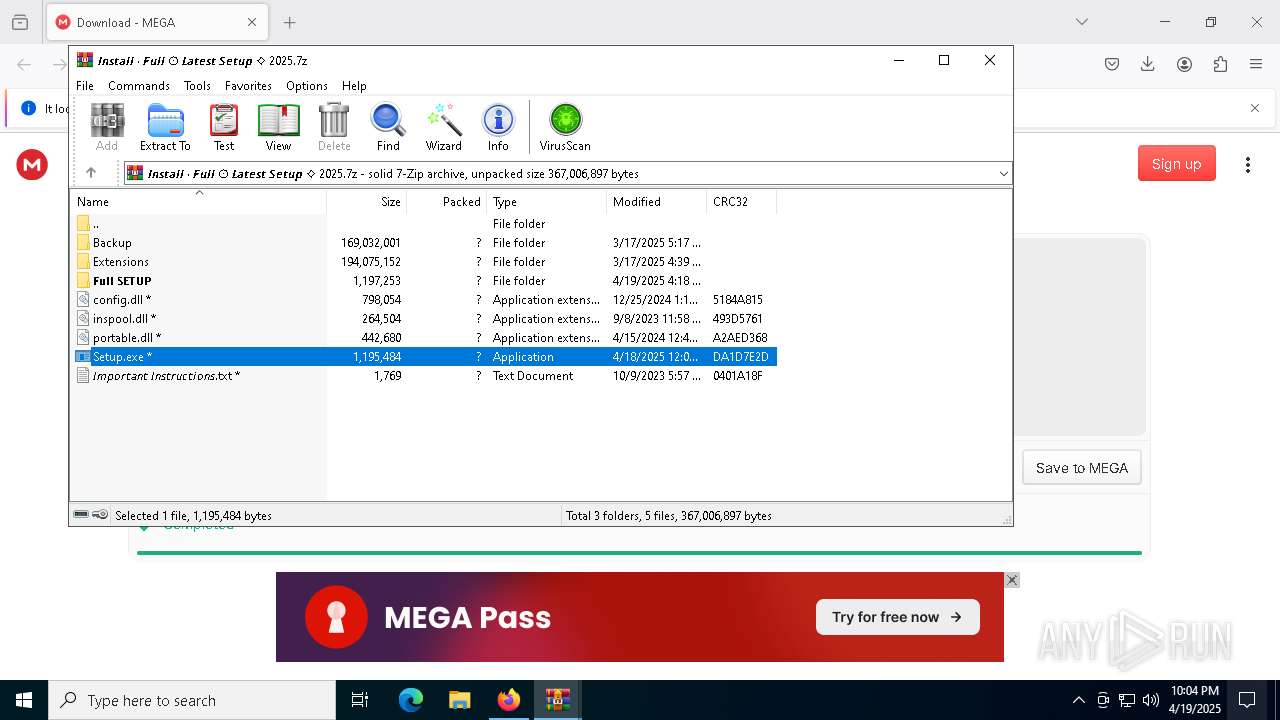
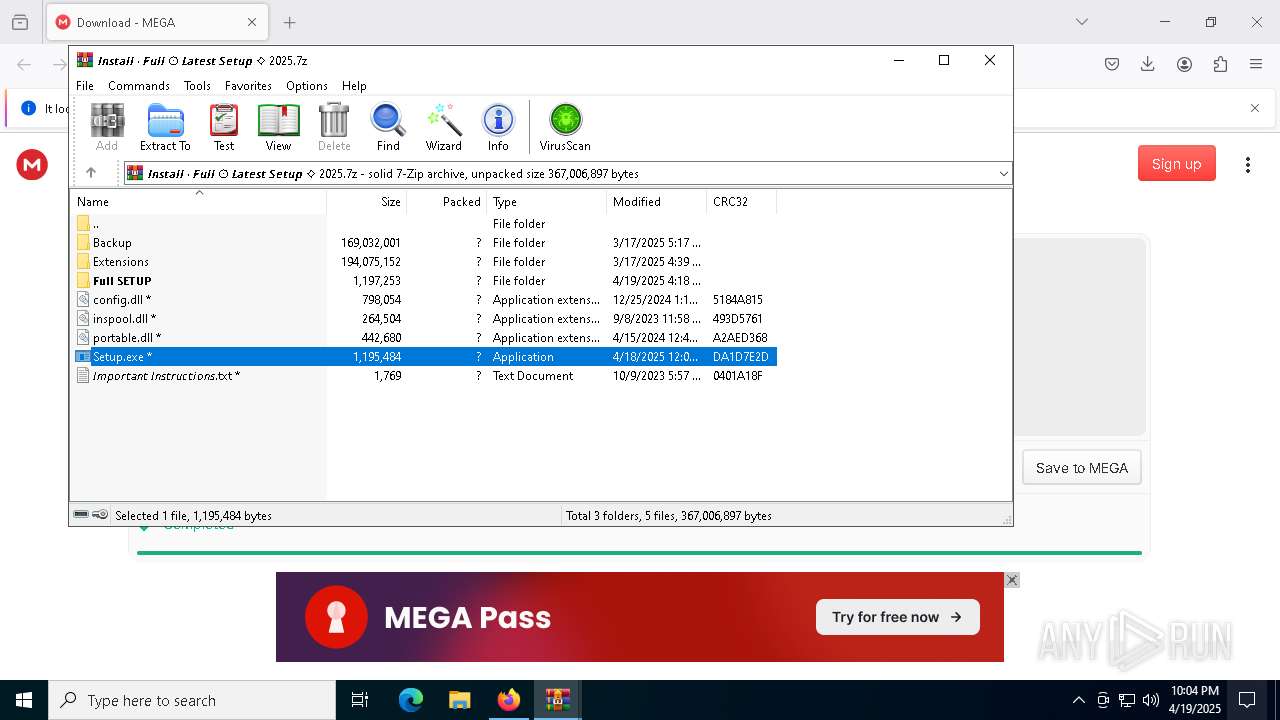
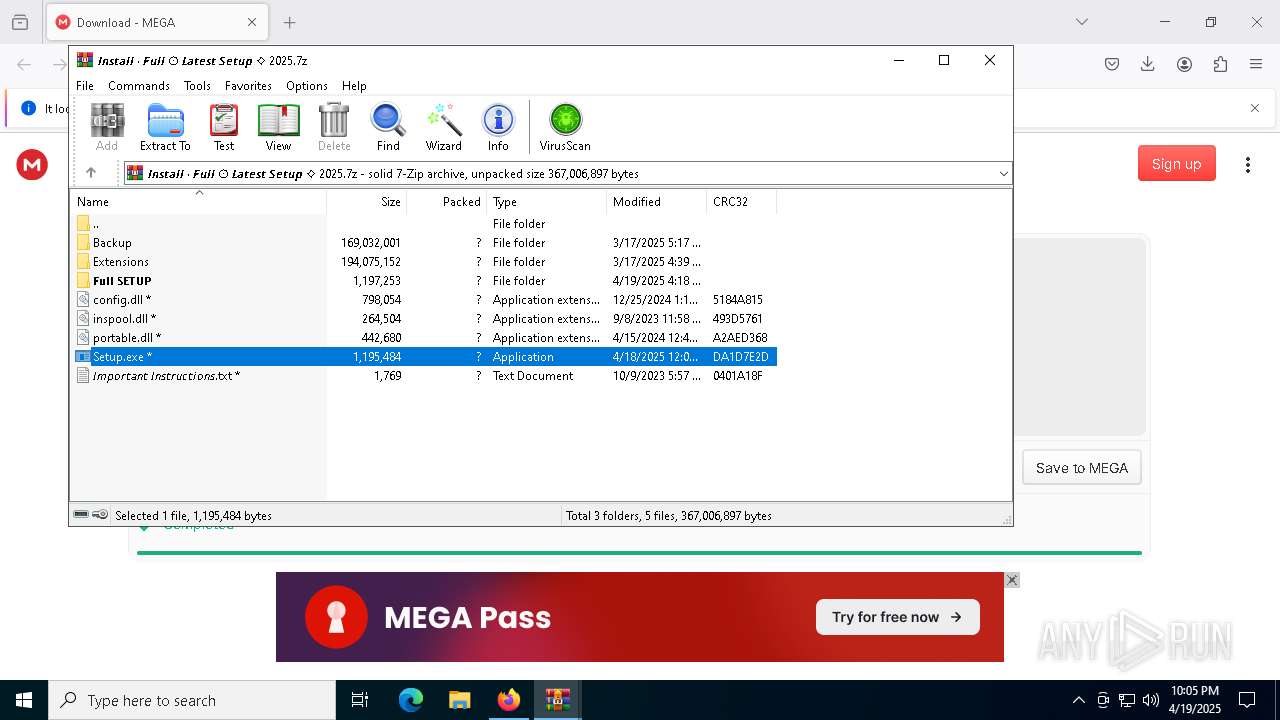
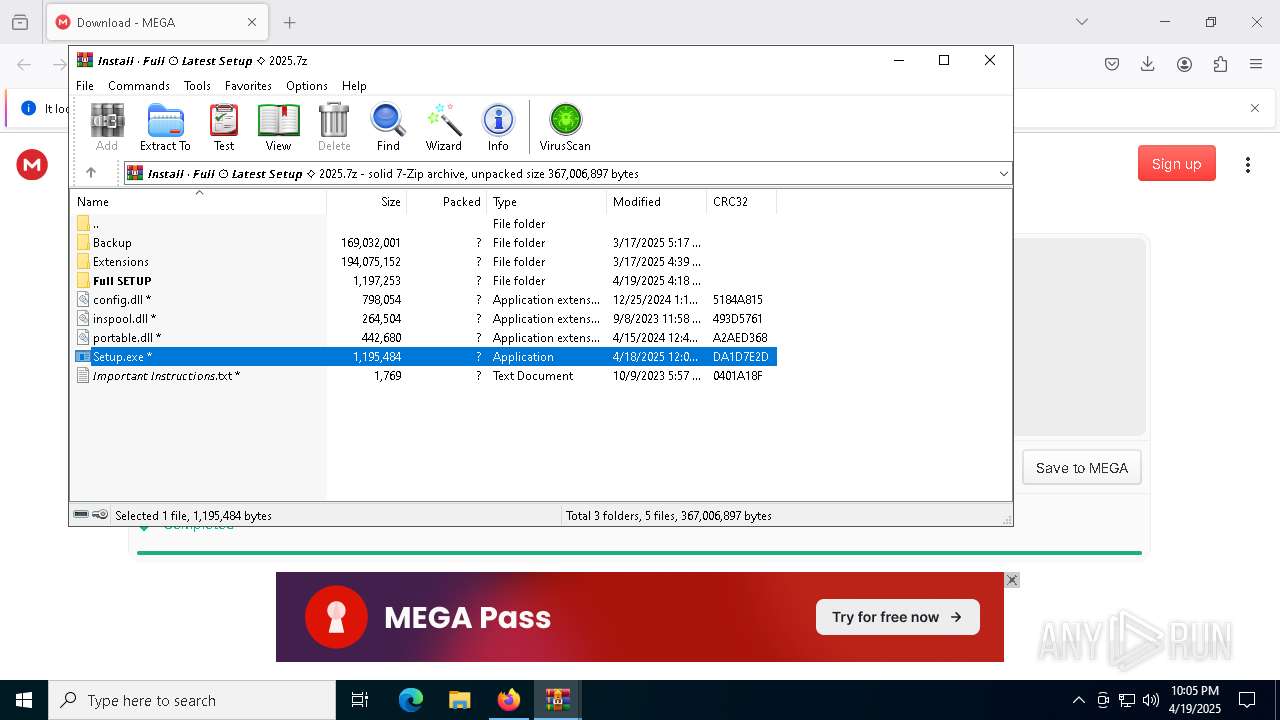
| 5112 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa6940.44898\𝙄𝙣𝙨𝙩𝙖𝙡𝙡 ∙ 𝙁𝙪𝙡𝙡 ⨀ 𝙇𝙖𝙩𝙚𝙨𝙩 𝙎𝙚𝙩𝙪𝙥 ⟡ 2025.7z" | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 5972 | cmd /c copy /b ..\Ryan.xla + ..\Naturally.xla + ..\Lotus.xla + ..\Calvin.xla + ..\Unknown.xla + ..\Navy.xla + ..\Replacing.xla + ..\Enb.xla i | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 283
Read events
21 261
Write events
22
Delete events
0
Modification events
| (PID) Process: | (7388) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (6940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\𝙁𝙐𝙇𝙇 𝘿𝙊𝙒𝙉𝙇𝙊𝘼𝘿 𝙐𝙋𝘿𝘼𝙏𝙀𝘿 𝙎𝙀𝙏𝙐𝙋 𝙁𝙍𝙀𝙀 💾.zip | |||
| (PID) Process: | (6940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5112) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
Executable files
121
Suspicious files
250
Text files
212
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7388 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7388 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7388 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 7388 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7388 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7388 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7388 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 7388 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db | binary | |
MD5:04EACDDC1BF7FC5C9628CDDB5761F21E | SHA256:431AA67539F837E7EF437E06337D654C8EE1B4DF3F44E130D30CEA3C7FEAF6AC | |||
| 7388 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:3462294949FCE0DDBDC5EB19DD2B3B55 | SHA256:AA07E227121171B851F7202696A0C00ACB3390A7B8FC222EC81D44FAAD5B9F2C | |||
| 7388 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\protections.sqlite-journal | binary | |
MD5:A4140550C16D7B532E75F44AFC8F8834 | SHA256:E568FDAA38764DD1D6091E58668074119B31787CFACB5BB37EB0E00211EE77EC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
114
DNS requests
135
Threats
28
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7388 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
7388 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
7388 | firefox.exe | POST | 200 | 2.23.82.57:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
7388 | firefox.exe | POST | 200 | 216.58.212.163:80 | http://o.pki.goog/s/wr3/cgo | unknown | — | — | whitelisted |
7388 | firefox.exe | POST | 200 | 2.23.82.57:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7388 | firefox.exe | POST | 200 | 2.23.82.57:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7388 | firefox.exe | POST | 200 | 216.58.212.163:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7388 | firefox.exe | POST | 200 | 2.23.82.57:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7388 | firefox.exe | 31.216.145.5:443 | mega.nz | Datacenter Luxembourg S.A. | LU | whitelisted |
7388 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
7388 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | — | — | whitelisted |
7388 | firefox.exe | 216.58.212.170:443 | safebrowsing.googleapis.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
mega.nz |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7388 | firefox.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
2196 | svchost.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7388 | firefox.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
2196 | svchost.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7388 | firefox.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
2196 | svchost.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
2196 | svchost.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
2196 | svchost.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
2196 | svchost.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |