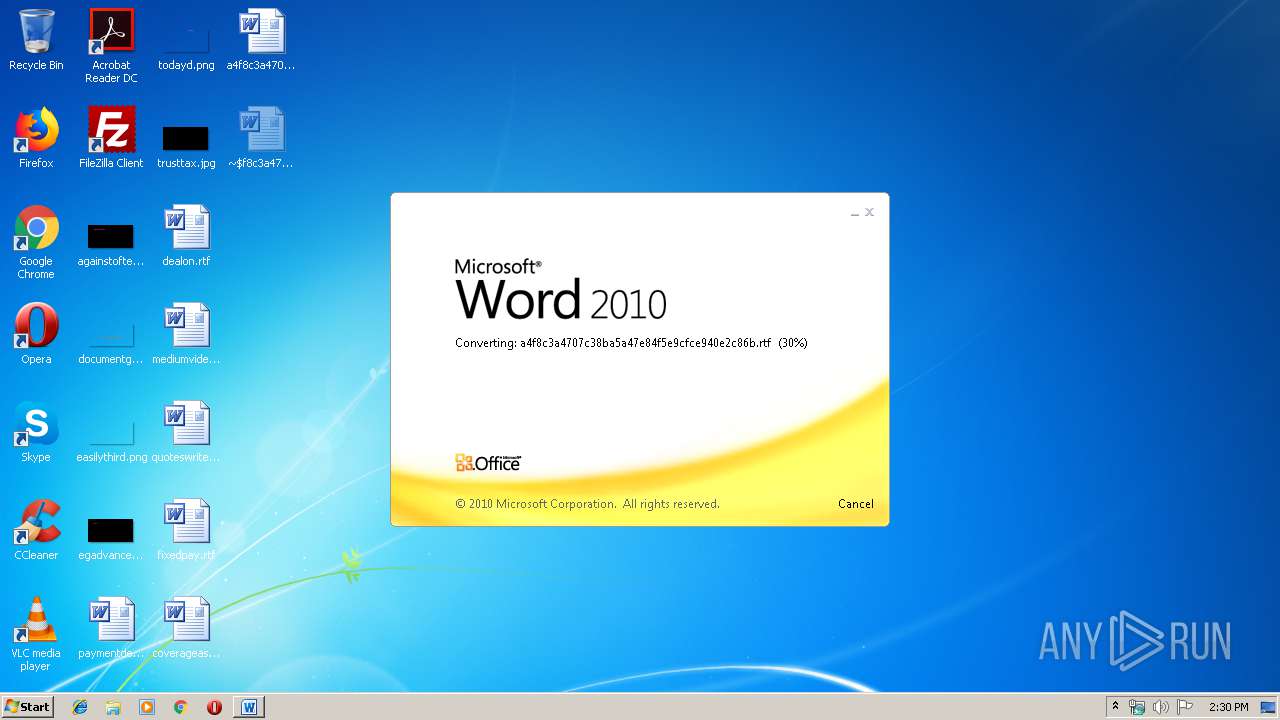
| File name: | a4f8c3a4707c38ba5a47e84f5e9cfce940e2c86b |
| Full analysis: | https://app.any.run/tasks/7159b1a7-c582-409c-bf3c-b28013e08ce5 |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | October 09, 2019, 13:30:24 |
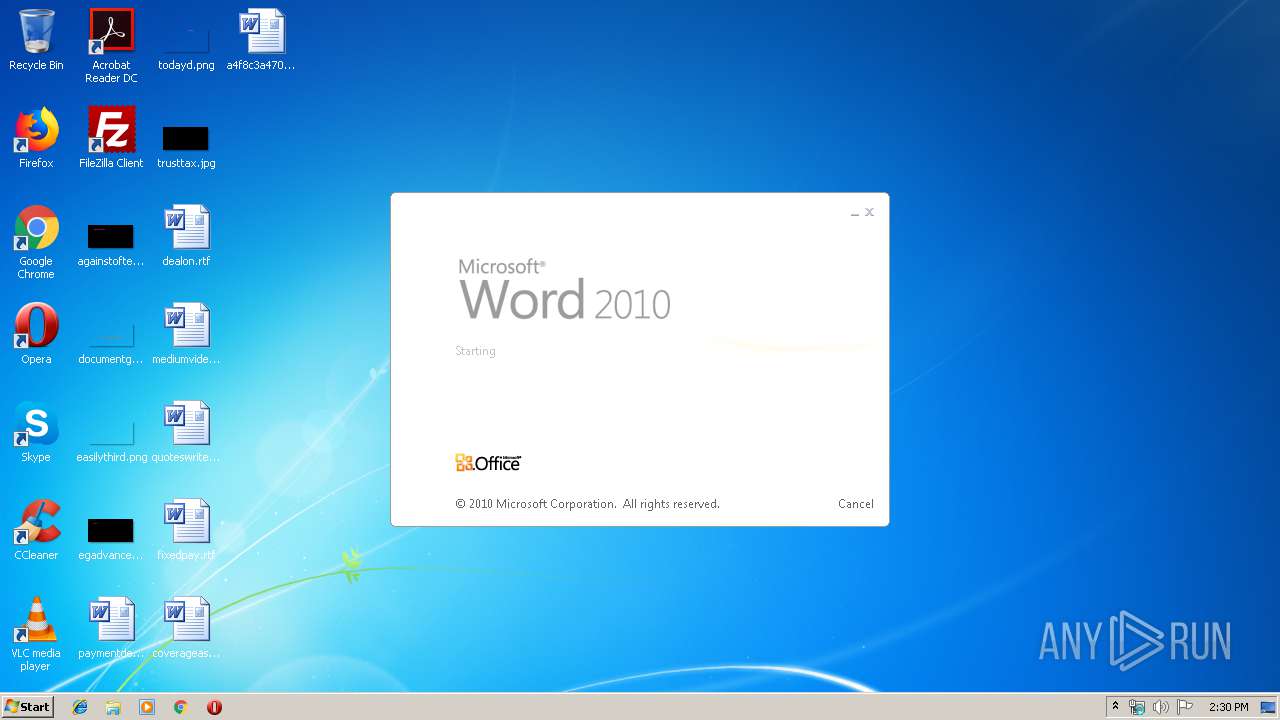
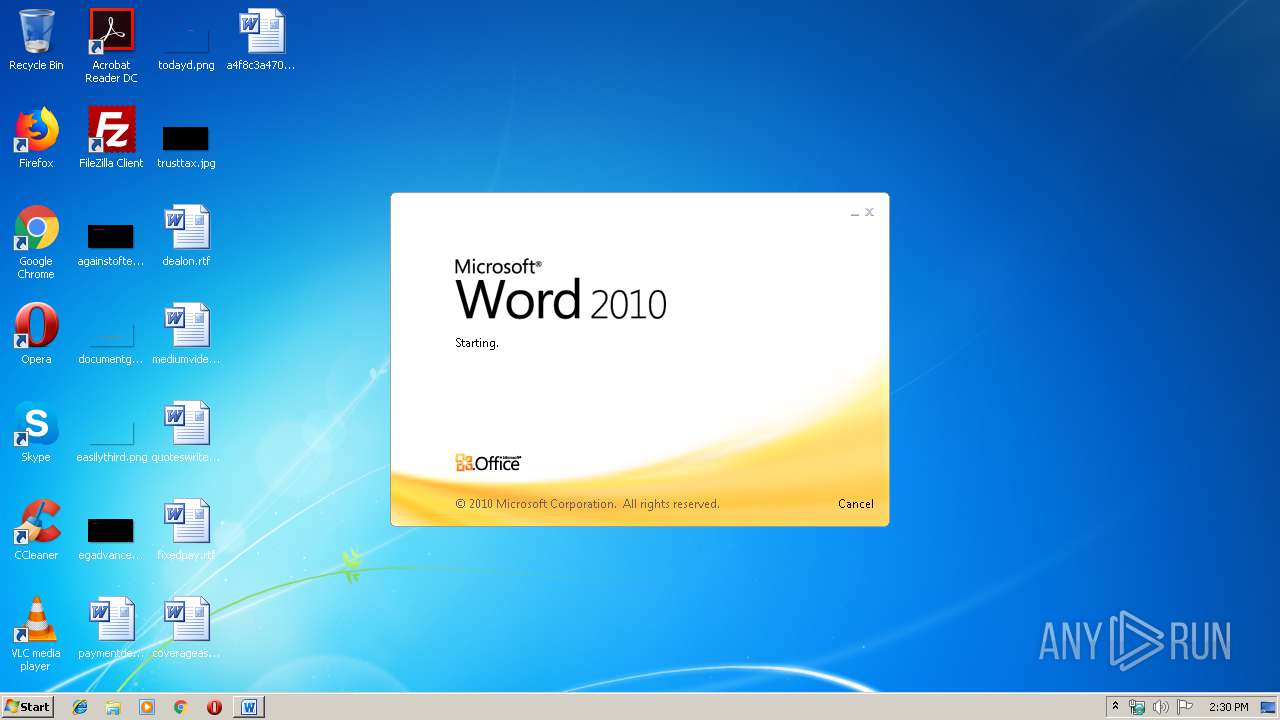
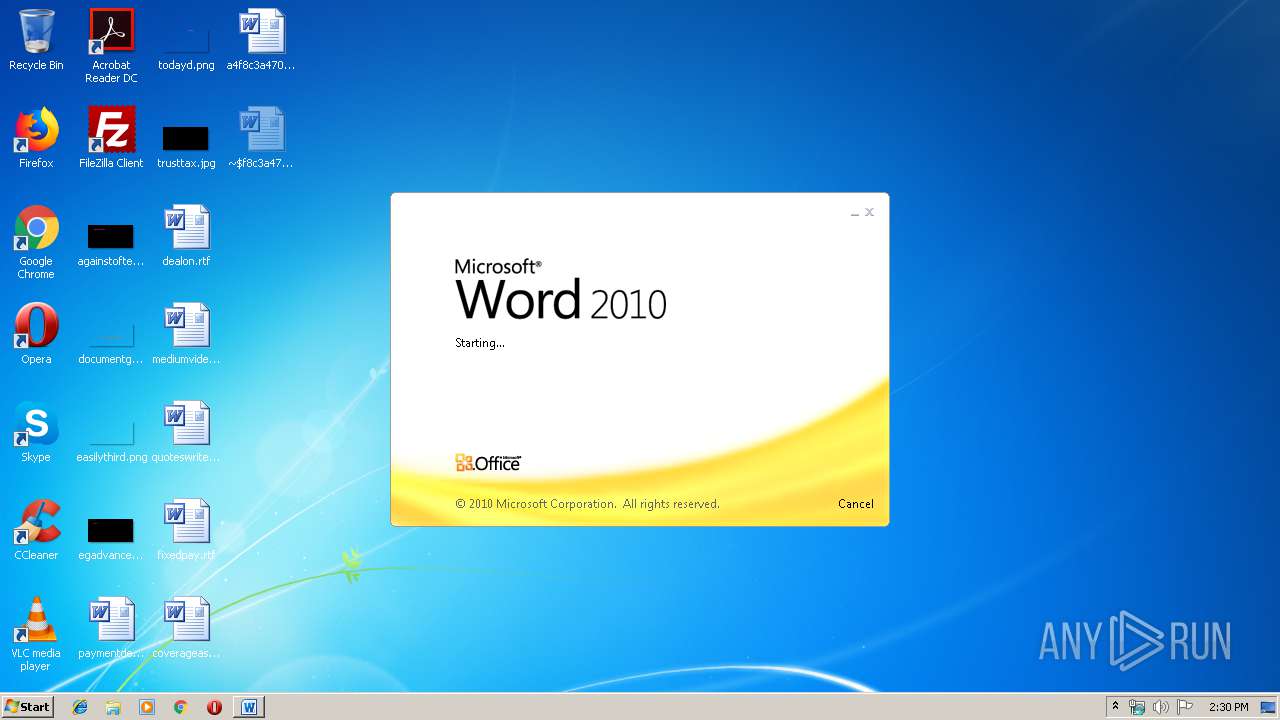
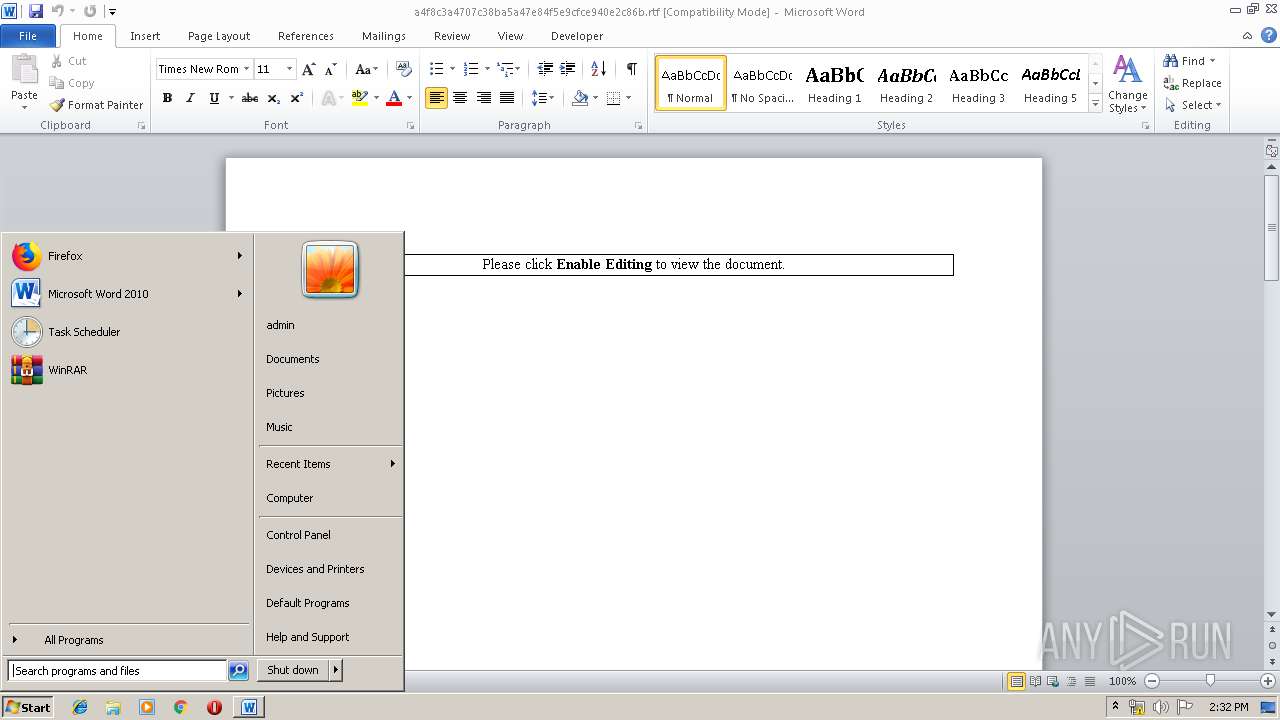
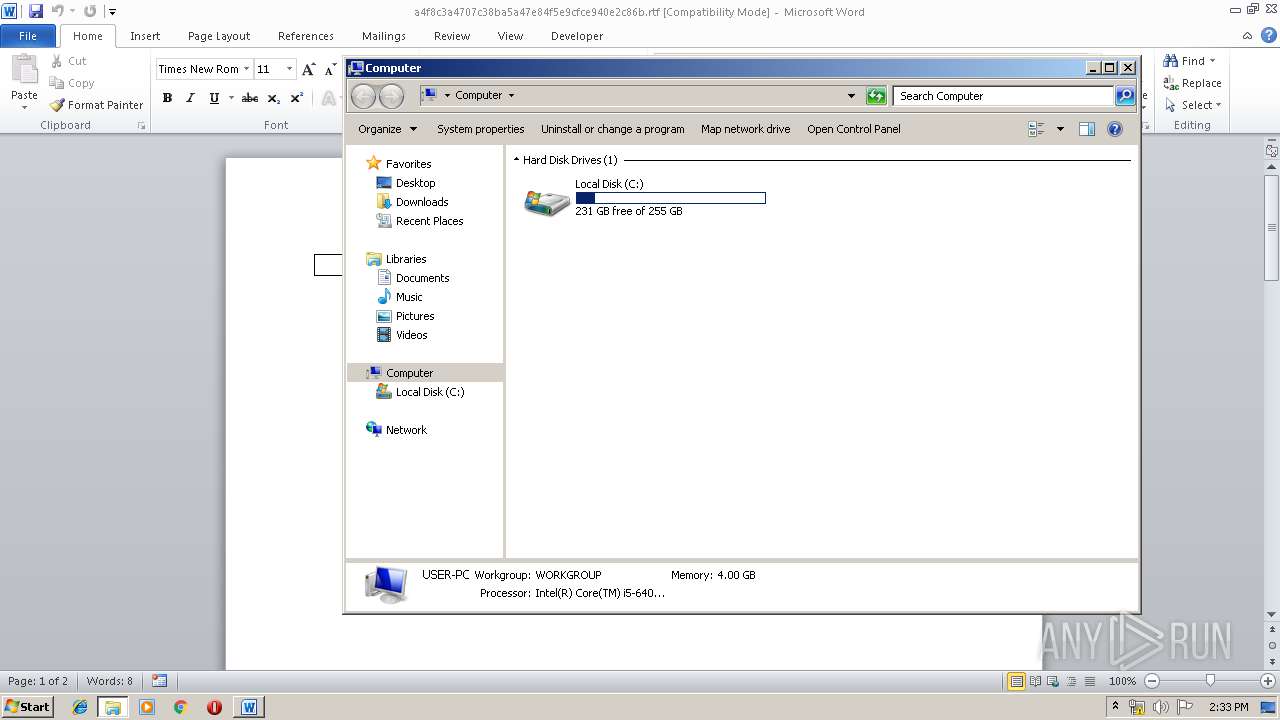
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, unknown character set |
| MD5: | 711B32636EB827B182D493E5E22BFA1C |
| SHA1: | A4F8C3A4707C38BA5A47E84F5E9CFCE940E2C86B |
| SHA256: | B032CA95B91C371C729714DABD9180DF49A449AF8EF0D3F198DCC80C5C53F4BC |
| SSDEEP: | 1536:mIQwSTn1jtHv9YNpZB7ie1ehegeefDcf/PeqC3gMSYkR08GeL+Z7FRIxPILSQWn7:mIQebP8mxgLSQWn7 |
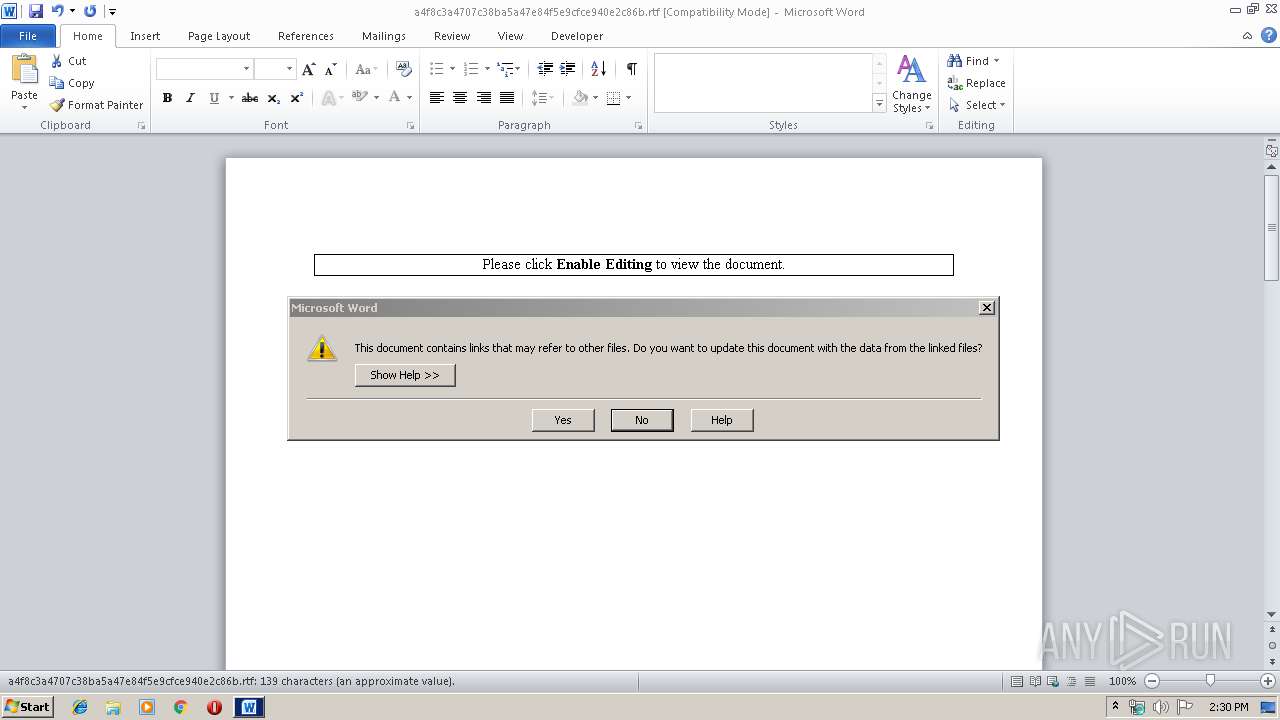
MALICIOUS
Requests a remote executable file from MS Office
- WINWORD.EXE (PID: 2892)
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 2892)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2892)
Application was dropped or rewritten from another process
- anichima.exe (PID: 2064)
- anichima.exe (PID: 2328)
Changes the login/logoff helper path in the registry
- anichima.exe (PID: 2064)
Downloads executable files from IP
- WINWORD.EXE (PID: 2892)
Detected Hawkeye Keylogger
- anichima.exe (PID: 2328)
Uses NirSoft utilities to collect credentials
- vbc.exe (PID: 2864)
- vbc.exe (PID: 3292)
Actions looks like stealing of personal data
- vbc.exe (PID: 3292)
- vbc.exe (PID: 2864)
Stealing of credential data
- vbc.exe (PID: 3292)
- vbc.exe (PID: 2864)
SUSPICIOUS
Unusual connect from Microsoft Office
- WINWORD.EXE (PID: 2892)
Creates files in the user directory
- anichima.exe (PID: 2064)
Executable content was dropped or overwritten
- anichima.exe (PID: 2064)
Application launched itself
- anichima.exe (PID: 2064)
Executes scripts
- anichima.exe (PID: 2328)
Loads DLL from Mozilla Firefox
- vbc.exe (PID: 3292)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2892)
Creates files in the user directory
- WINWORD.EXE (PID: 2892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
Total processes
41
Monitored processes
5
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
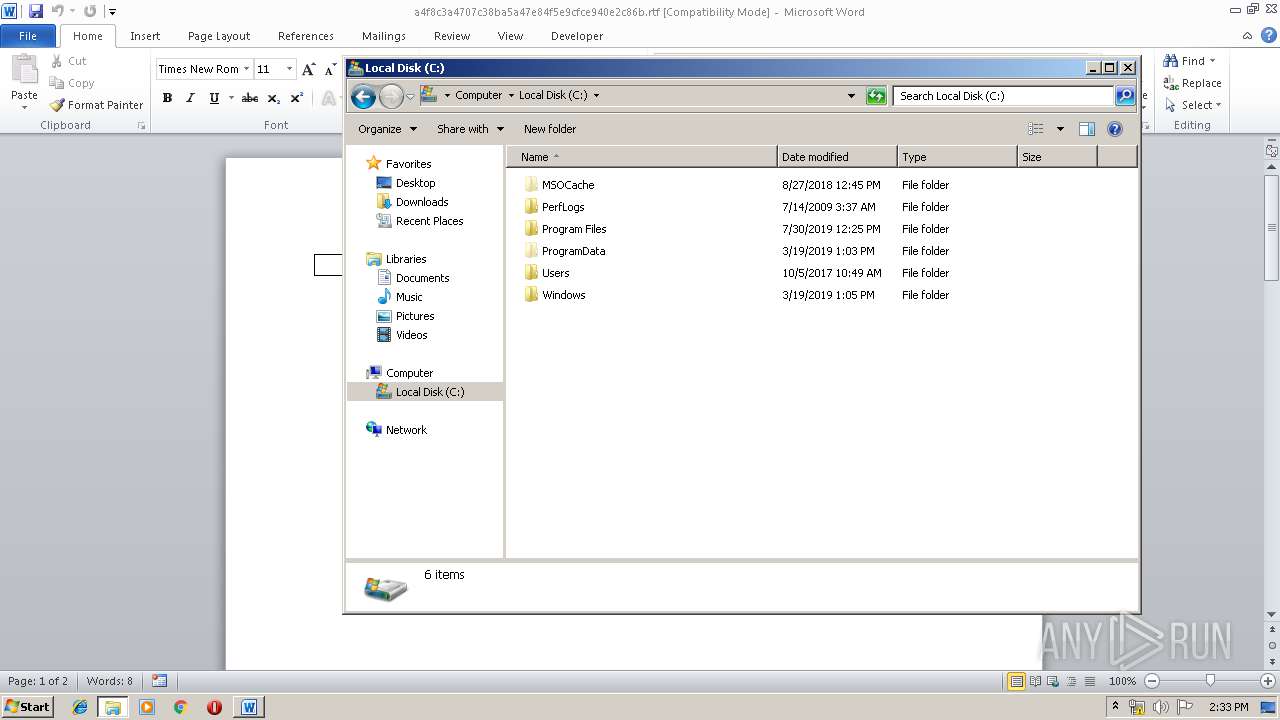
| 2064 | "C:\Users\admin\AppData\Roaming\anichima.exe" | C:\Users\admin\AppData\Roaming\anichima.exe | WINWORD.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Description: XZ2Studio Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2328 | "C:\Users\admin\AppData\Roaming\anichima.exe" | C:\Users\admin\AppData\Roaming\anichima.exe | anichima.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: XZ2Studio Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2864 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmp86CB.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | anichima.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 2892 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\a4f8c3a4707c38ba5a47e84f5e9cfce940e2c86b.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3292 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmp5A2D.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | anichima.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
Total events
1 292
Read events
890
Write events
371
Delete events
31
Modification events
| (PID) Process: | (2892) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 4u: |
Value: 34753A004C0B0000010000000000000000000000 | |||
| (PID) Process: | (2892) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2892) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2892) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1330184243 | |||
| (PID) Process: | (2892) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1330184359 | |||
| (PID) Process: | (2892) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1330184360 | |||
| (PID) Process: | (2892) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 4C0B000068881DBFA57ED50100000000 | |||
| (PID) Process: | (2892) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 8z: |
Value: 387A3A004C0B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2892) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 8z: |
Value: 387A3A004C0B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2892) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
3
Suspicious files
0
Text files
5
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2892 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR594.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2892 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\3AA2C5C6.png | — | |
MD5:— | SHA256:— | |||
| 2892 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Abctfhghghghghg.sct | html | |
MD5:— | SHA256:— | |||
| 2892 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\crypted[1].exe | executable | |
MD5:— | SHA256:— | |||
| 2892 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\anichima.exe | executable | |
MD5:— | SHA256:— | |||
| 2892 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2064 | anichima.exe | C:\Users\admin\AppData\Roaming\0z5c3hv348Ql5s2p\NBL66GTIirP4.exe | executable | |
MD5:— | SHA256:— | |||
| 2328 | anichima.exe | C:\Users\admin\AppData\Local\Temp\25291068-43af-3e16-50f6-5889d9ce7904 | text | |
MD5:— | SHA256:— | |||
| 2892 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2892 | WINWORD.EXE | C:\Users\admin\Desktop\~$f8c3a4707c38ba5a47e84f5e9cfce940e2c86b.rtf | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
7
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2892 | WINWORD.EXE | GET | 200 | 185.234.218.36:80 | http://185.234.218.36/crypted.exe | unknown | executable | 477 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2892 | WINWORD.EXE | 185.234.218.36:80 | — | — | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bot.whatismyipaddress.com |
| shared |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2892 | WINWORD.EXE | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
2892 | WINWORD.EXE | A Network Trojan was detected | ET TROJAN Download Request Containing Suspicious Filename - Crypted |
2892 | WINWORD.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from dotted Quad by MSXMLHTTP M1 |
2892 | WINWORD.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2892 | WINWORD.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from dotted Quad by MSXMLHTTP M2 |
2892 | WINWORD.EXE | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |