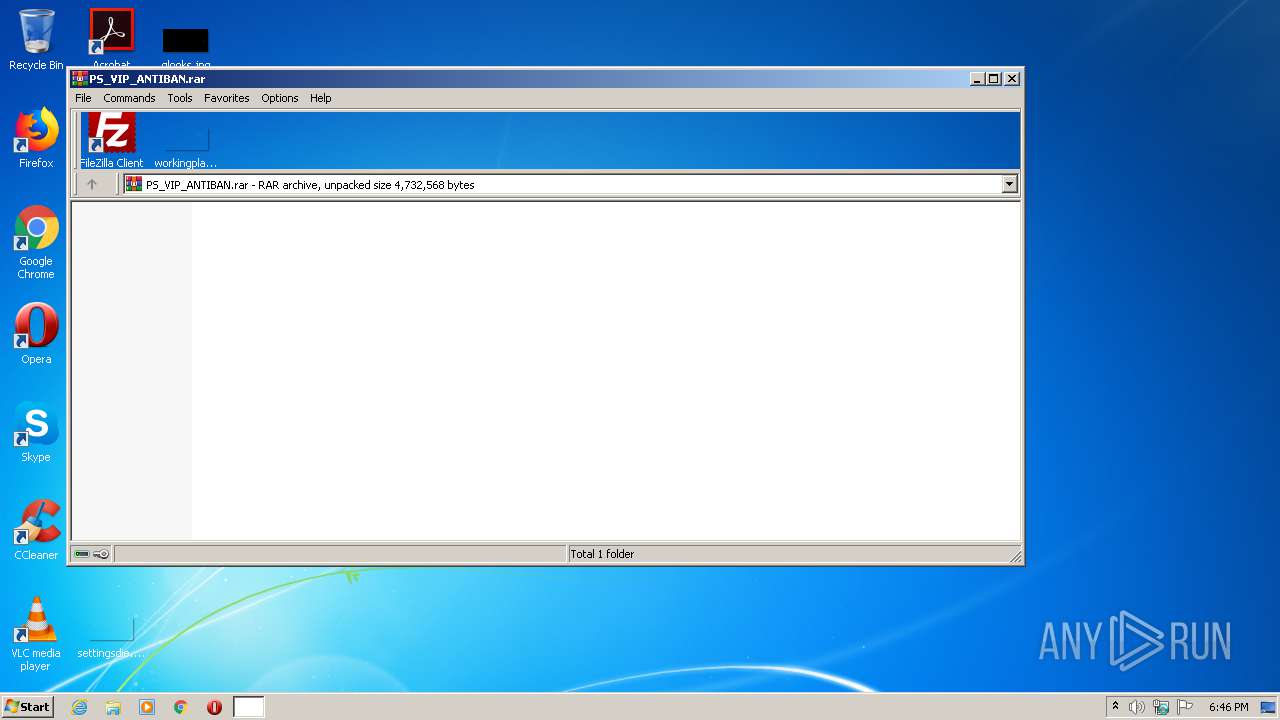
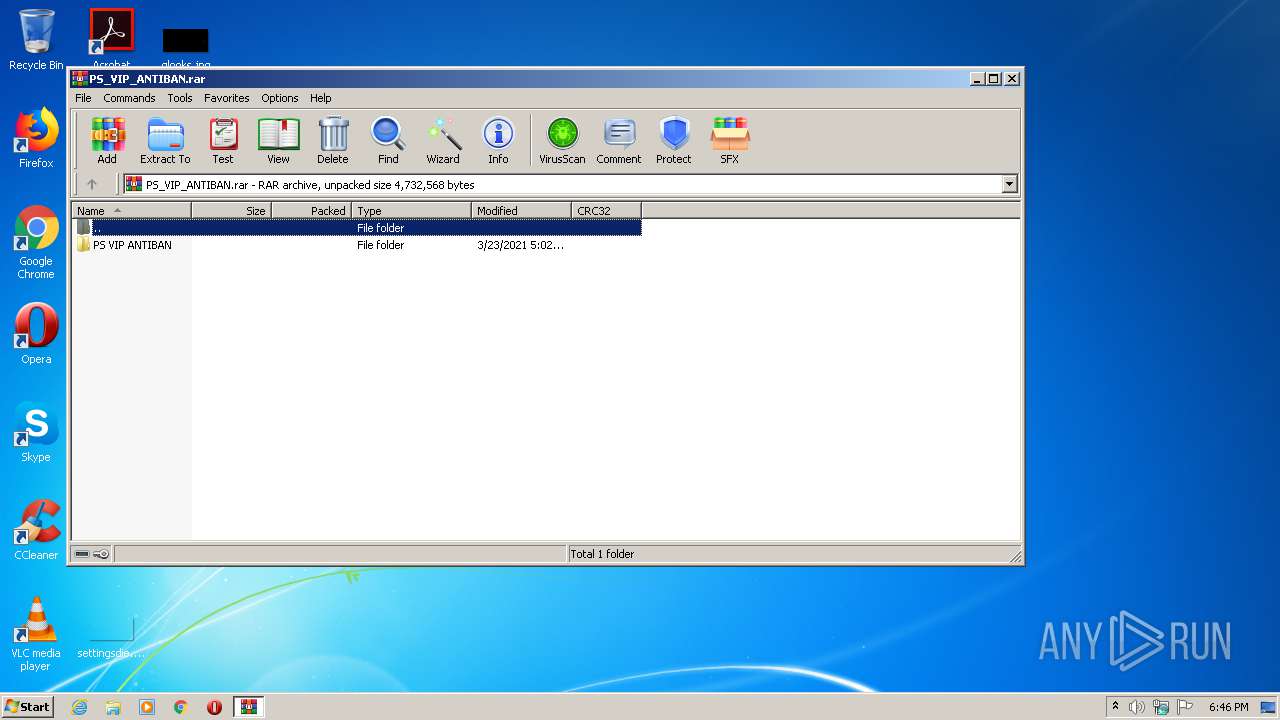
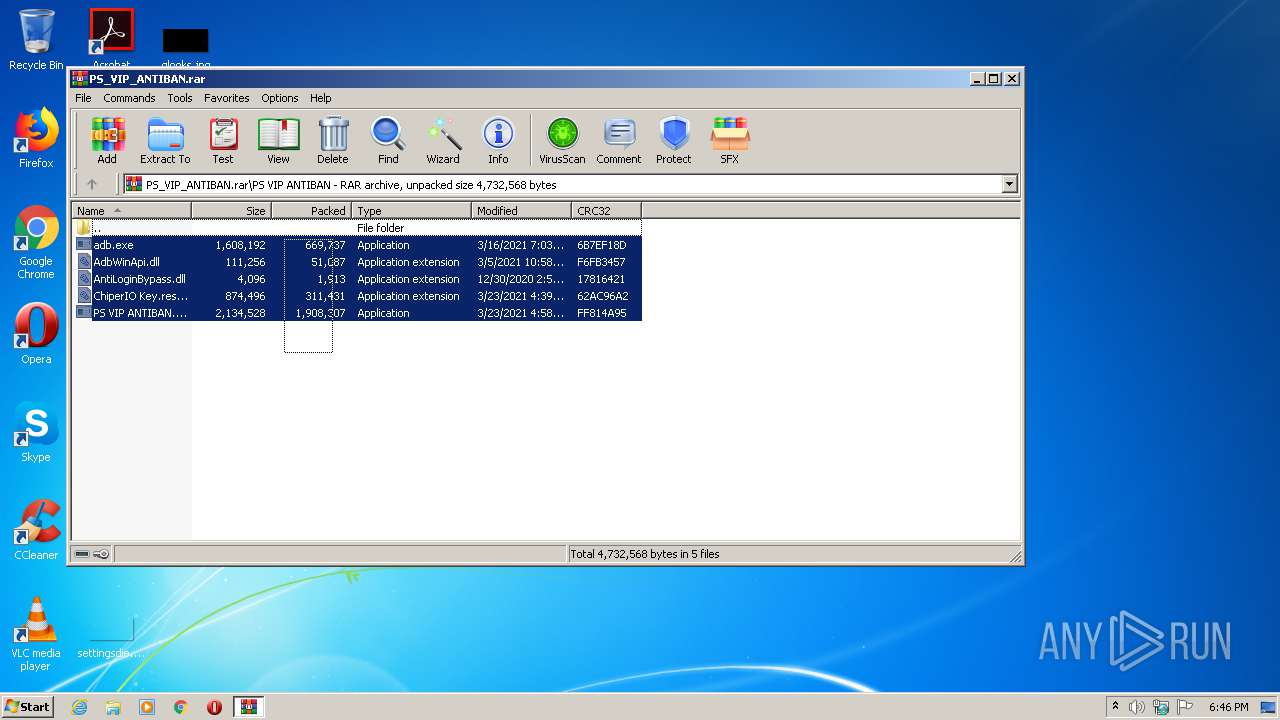
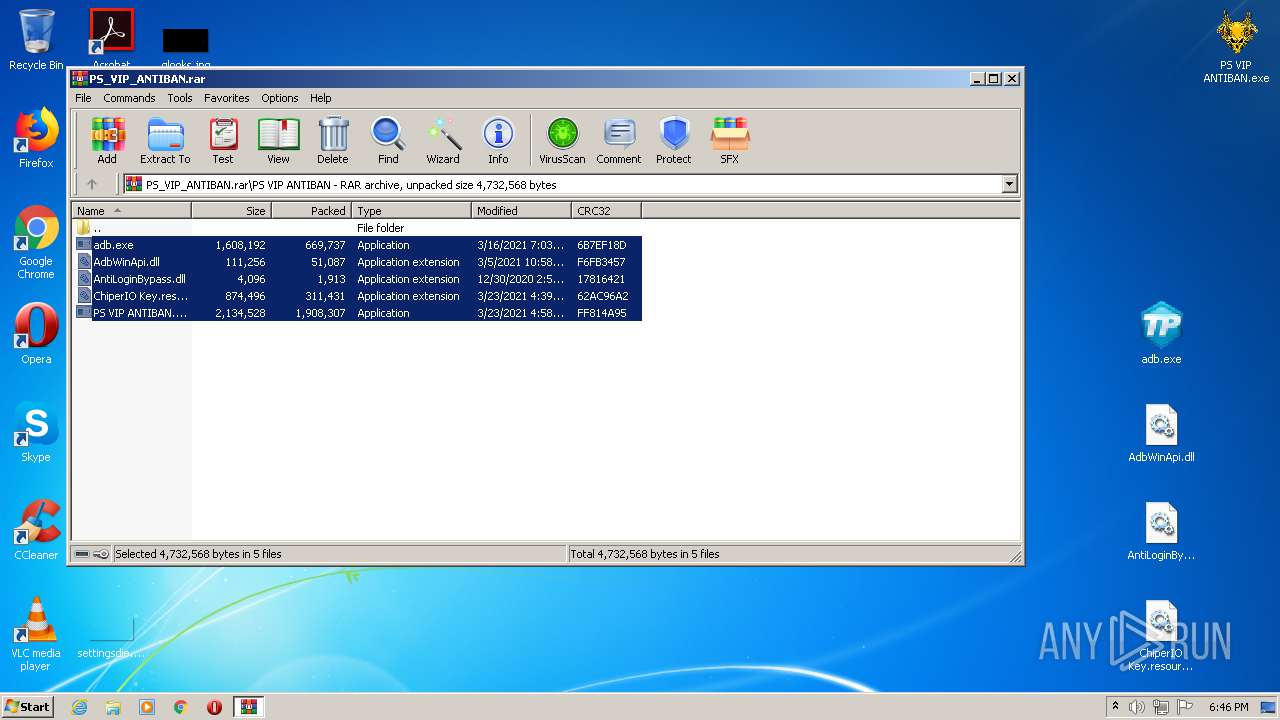
| File name: | PS_VIP_ANTIBAN.rar |
| Full analysis: | https://app.any.run/tasks/4fd08441-eb0e-4158-a260-467a707f6405 |
| Verdict: | Malicious activity |
| Threats: | njRAT is a remote access trojan. It is one of the most widely accessible RATs on the market that features an abundance of educational information. Interested attackers can even find tutorials on YouTube. This allows it to become one of the most popular RATs in the world. |
| Analysis date: | March 25, 2021, 18:45:33 |
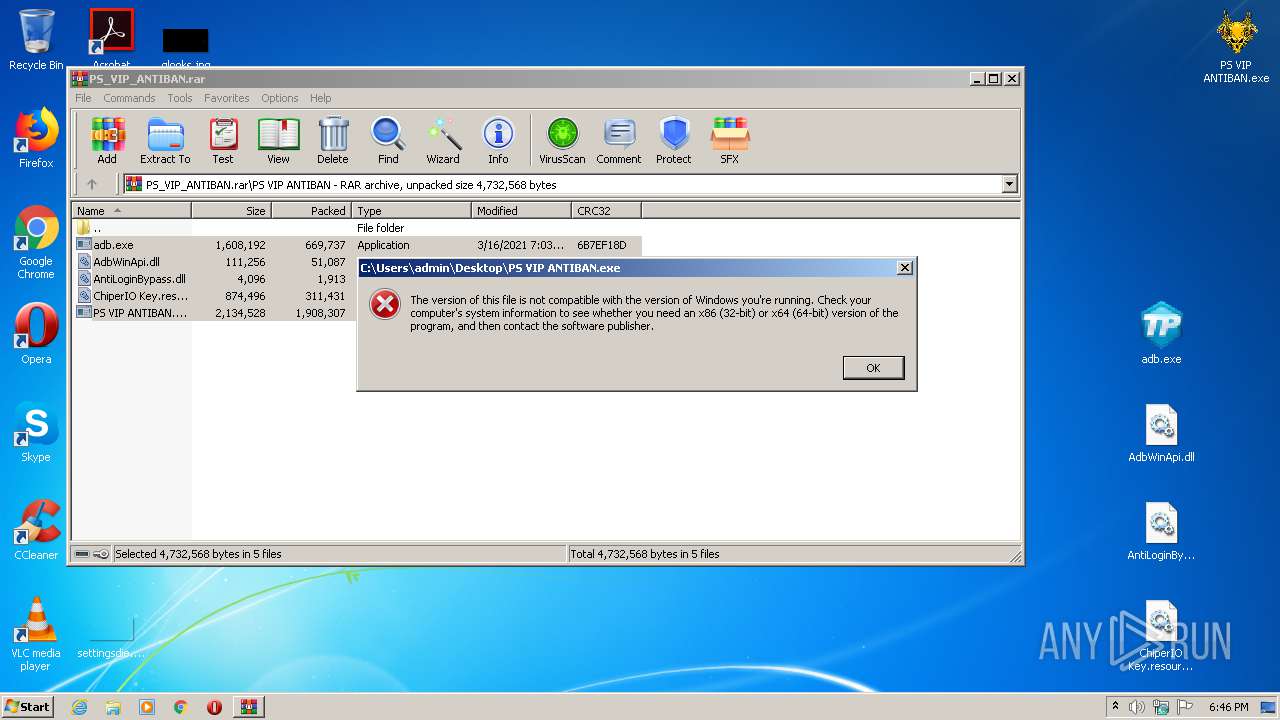
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 6EEF8334AF4EEC7312D4183F0AA05EF0 |
| SHA1: | F21D62AEBB7C5A7CA7173604F6D442E3C1F29C8A |
| SHA256: | B029A83D9D0F9E4D553B775FCDB7C78C07FC89F23CE4F1D88D2E792FBC303FD6 |
| SSDEEP: | 49152:qsW1sp7gF3+P7Sk6yojWqE2xnqGkpfEbikndcdZPCocxgNhS9wISvS9VtPnwFhVi:qs6spa3+b6Ch2xnnk9A7CRcShSV9VBw4 |
MALICIOUS
Drops executable file immediately after starts
- adb.exe (PID: 3508)
- ._cache_adb.exe (PID: 2532)
Loads dropped or rewritten executable
- ._cache_adb.exe (PID: 2532)
- SearchProtocolHost.exe (PID: 2948)
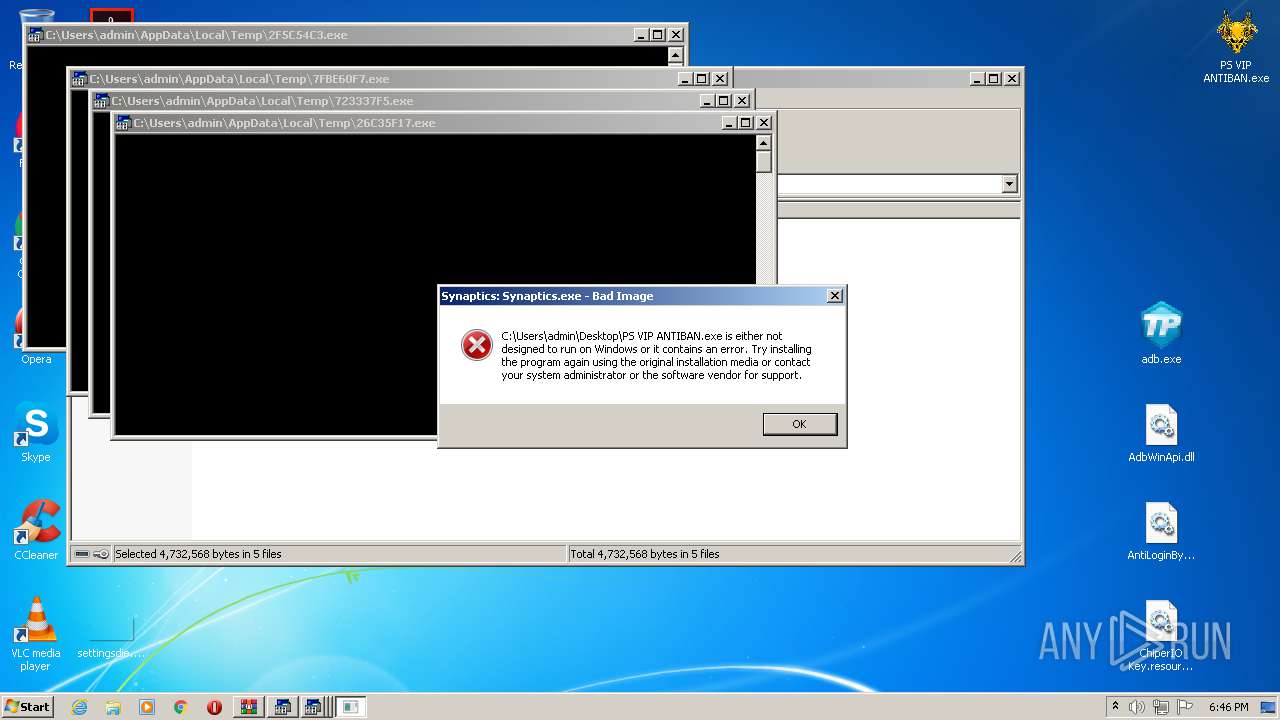
Application was dropped or rewritten from another process
- LXGmYx.exe (PID: 1576)
- adb.exe (PID: 3508)
- Synaptics.exe (PID: 1076)
- ._cache_adb.exe (PID: 2532)
Changes the autorun value in the registry
- adb.exe (PID: 3508)
Connects to CnC server
- LXGmYx.exe (PID: 1576)
- Synaptics.exe (PID: 1076)
NJRAT was detected
- Synaptics.exe (PID: 1076)
Changes settings of System certificates
- Synaptics.exe (PID: 1076)
SUSPICIOUS
Creates files in the program directory
- adb.exe (PID: 3508)
Executable content was dropped or overwritten
- adb.exe (PID: 3508)
- ._cache_adb.exe (PID: 2532)
Drops a file with too old compile date
- adb.exe (PID: 3508)
Starts CMD.EXE for commands execution
- LXGmYx.exe (PID: 1576)
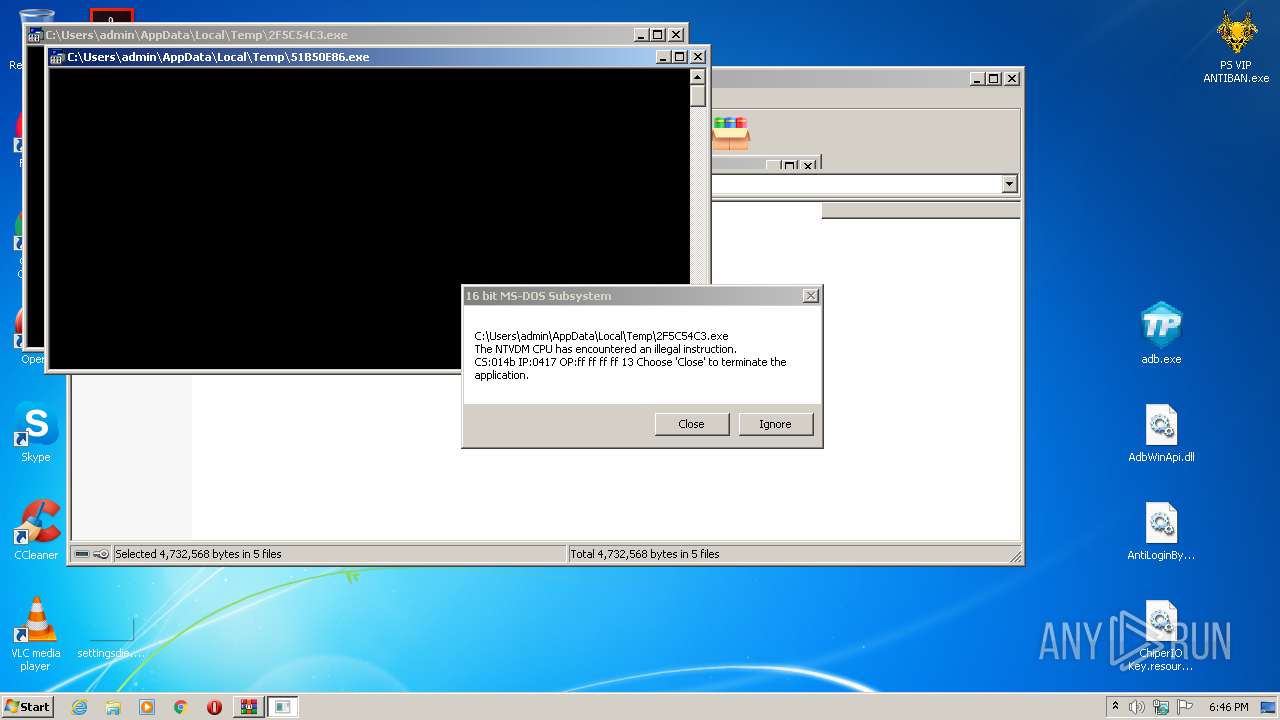
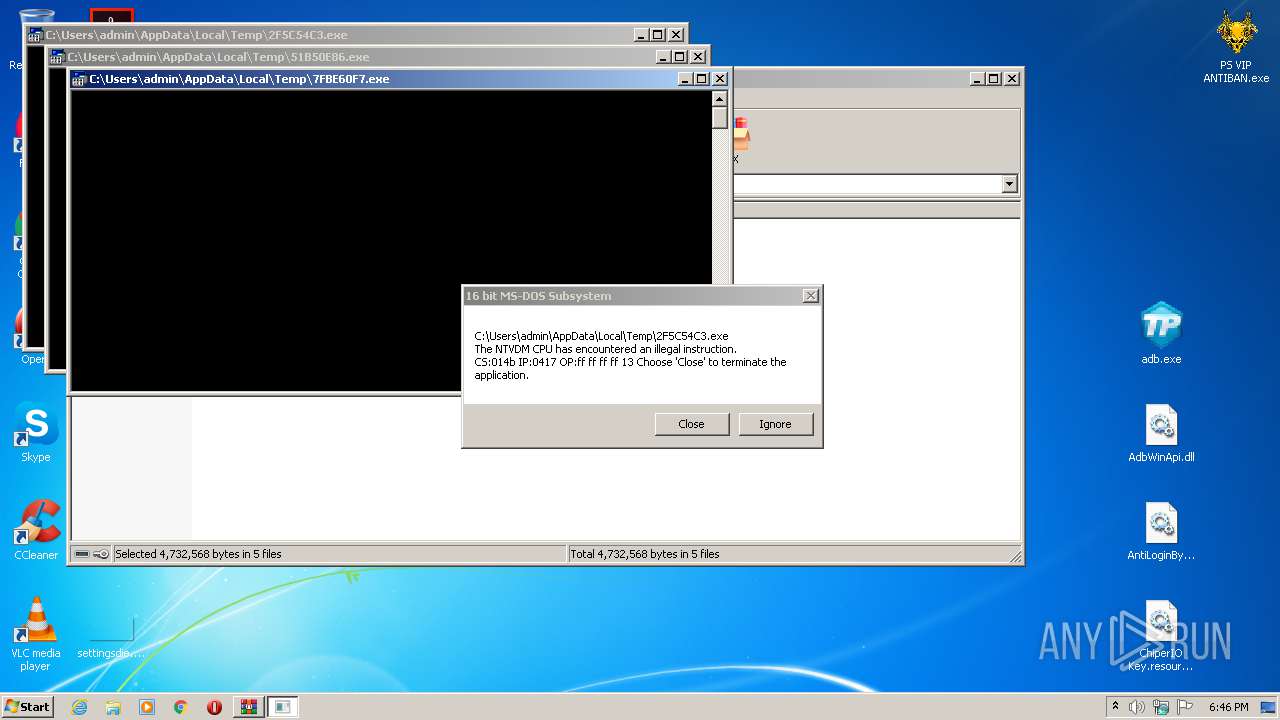
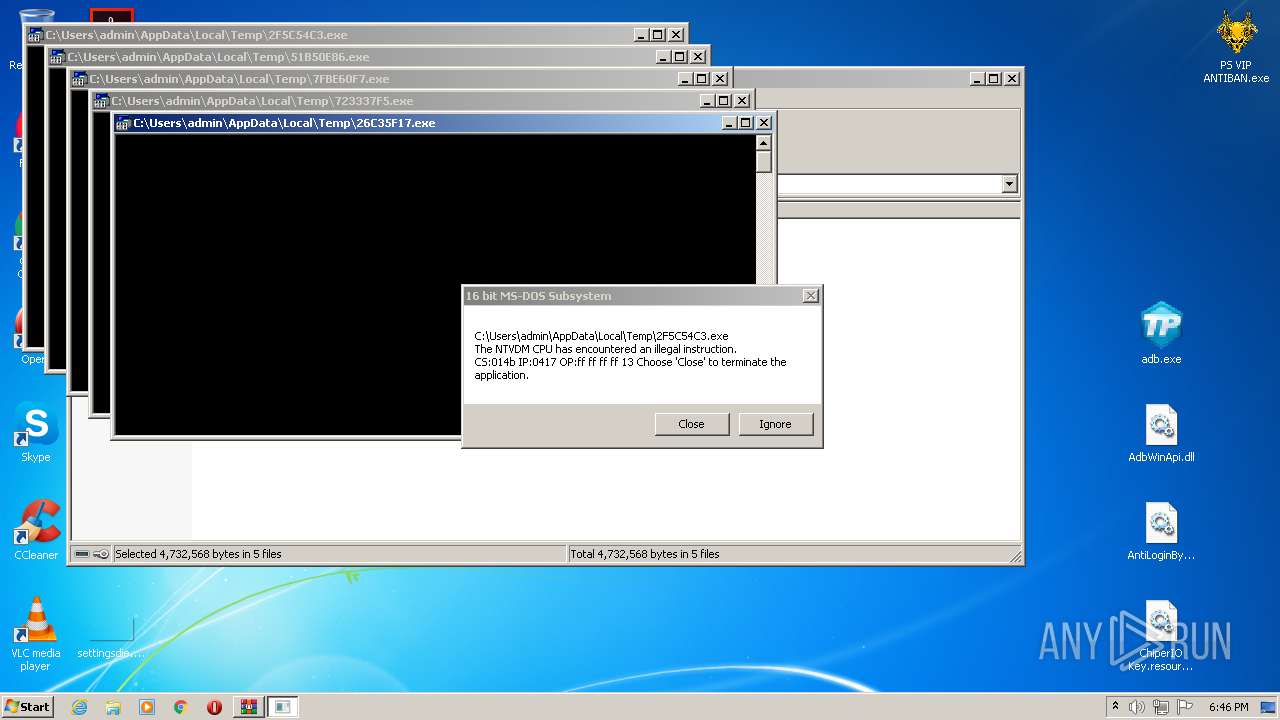
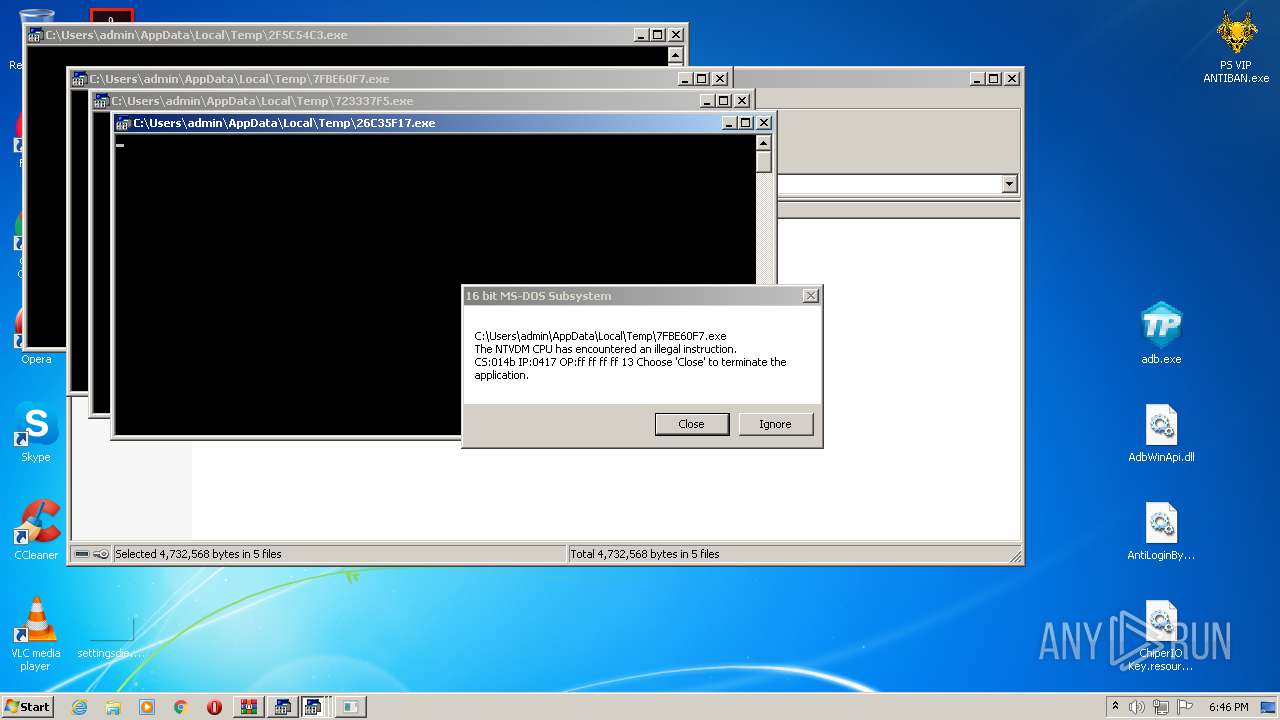
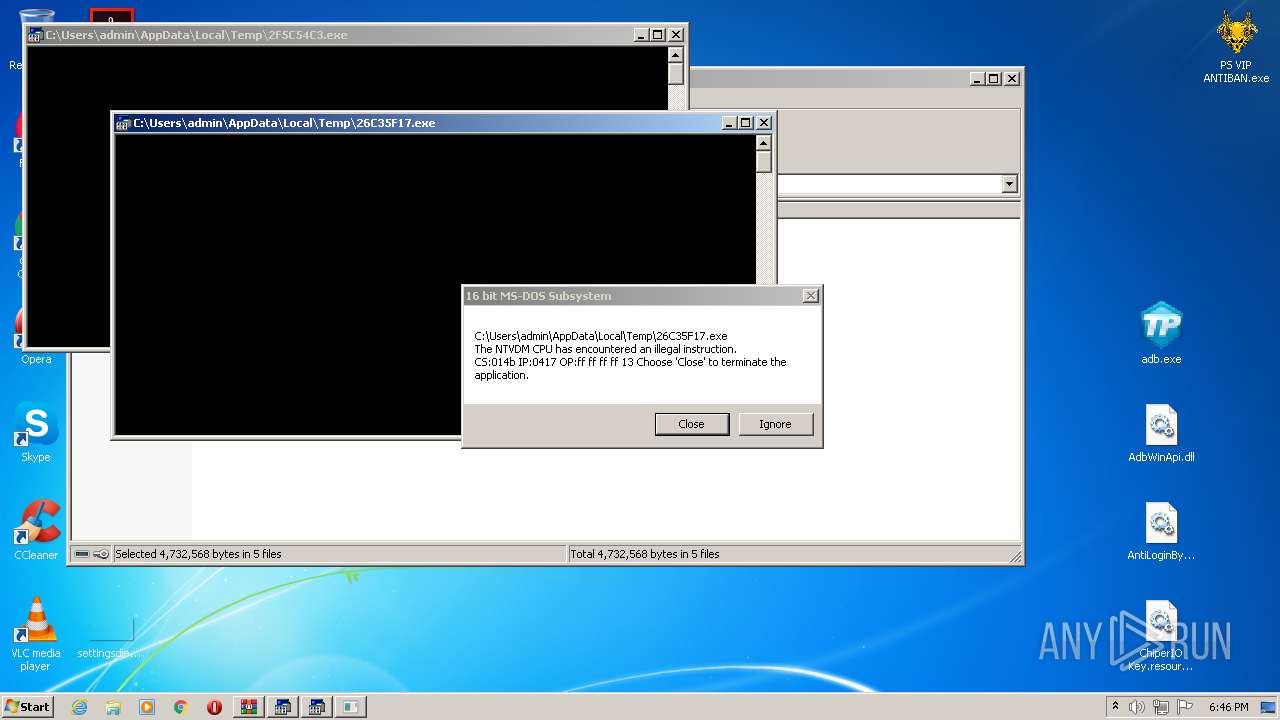
Executes application which crashes
- LXGmYx.exe (PID: 1576)
Adds / modifies Windows certificates
- Synaptics.exe (PID: 1076)
Creates files in the user directory
- Synaptics.exe (PID: 1076)
INFO
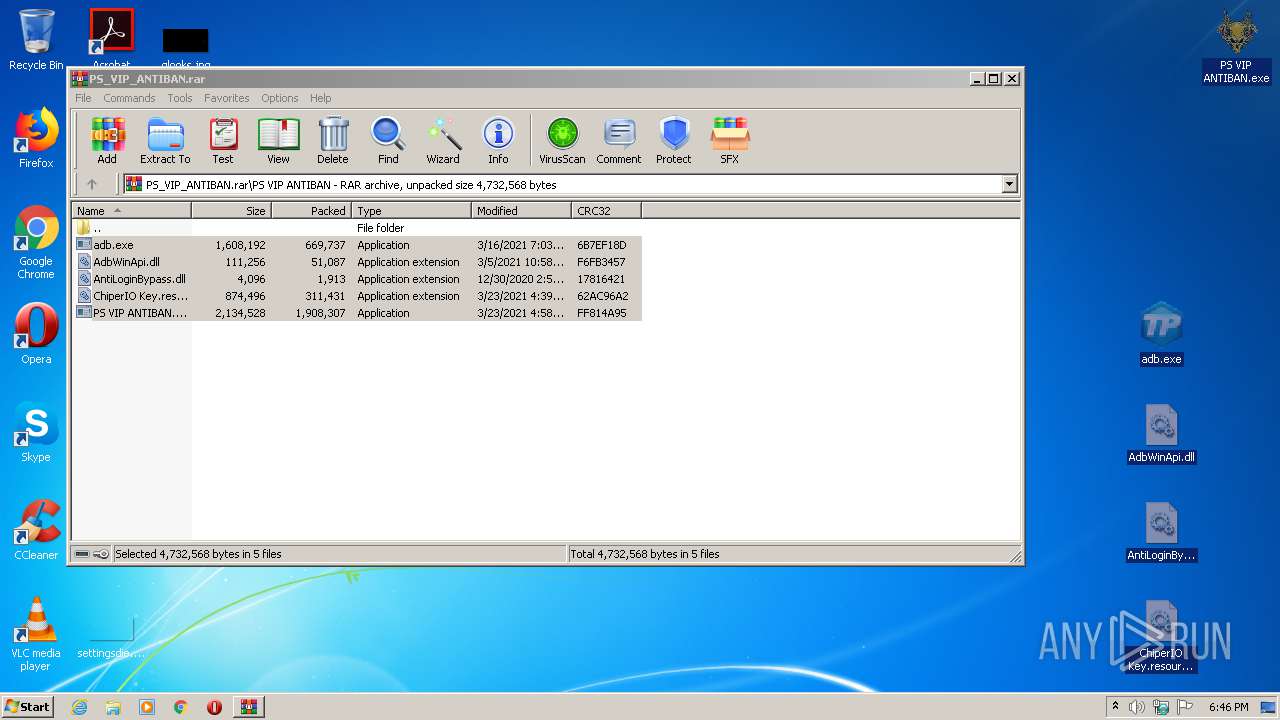
Manual execution by user
- adb.exe (PID: 3508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
57
Monitored processes
12
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1032 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\PS_VIP_ANTIBAN.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1076 | "C:\ProgramData\Synaptics\Synaptics.exe" InjUpdate | C:\ProgramData\Synaptics\Synaptics.exe | adb.exe | ||||||||||||
User: admin Company: Synaptics Integrity Level: HIGH Description: Synaptics Pointing Device Driver Exit code: 0 Version: 1.0.0.4 Modules
| |||||||||||||||
| 1576 | C:\Users\admin\AppData\Local\Temp\LXGmYx.exe | C:\Users\admin\AppData\Local\Temp\LXGmYx.exe | ._cache_adb.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2164 | "C:\Windows\system32\ntvdm.exe" -i2 | C:\Windows\system32\ntvdm.exe | — | LXGmYx.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 255 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
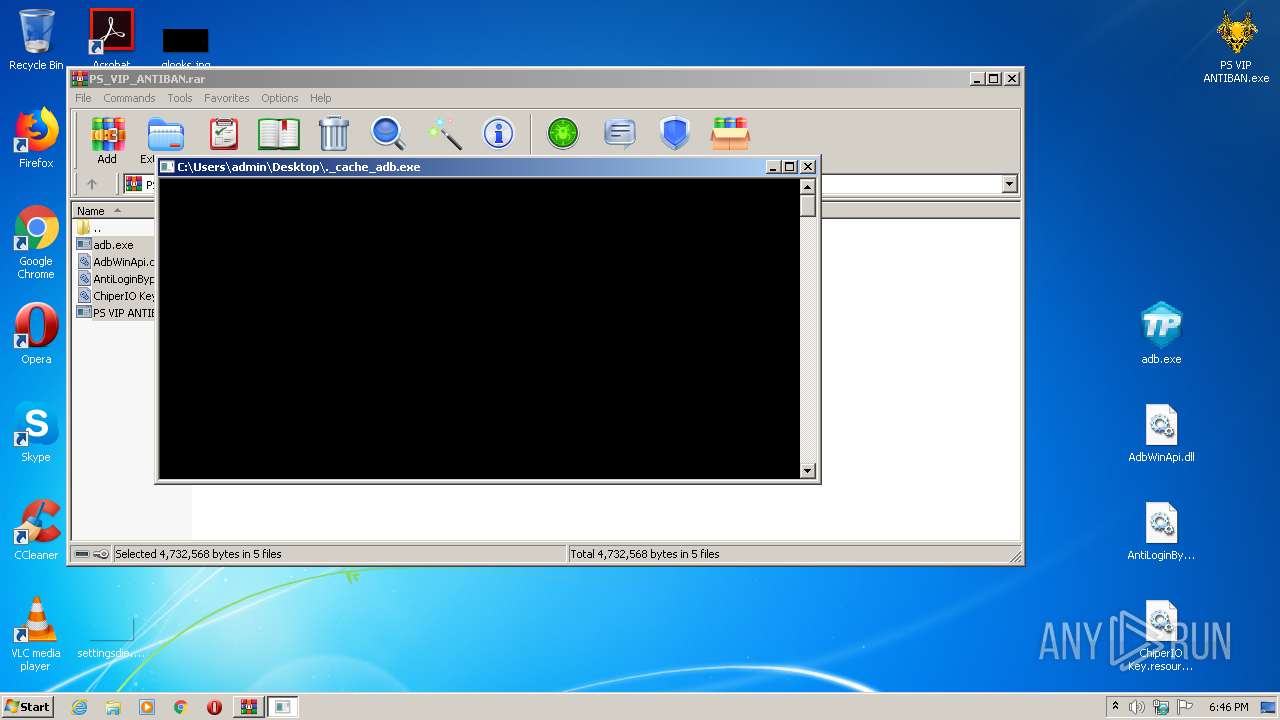
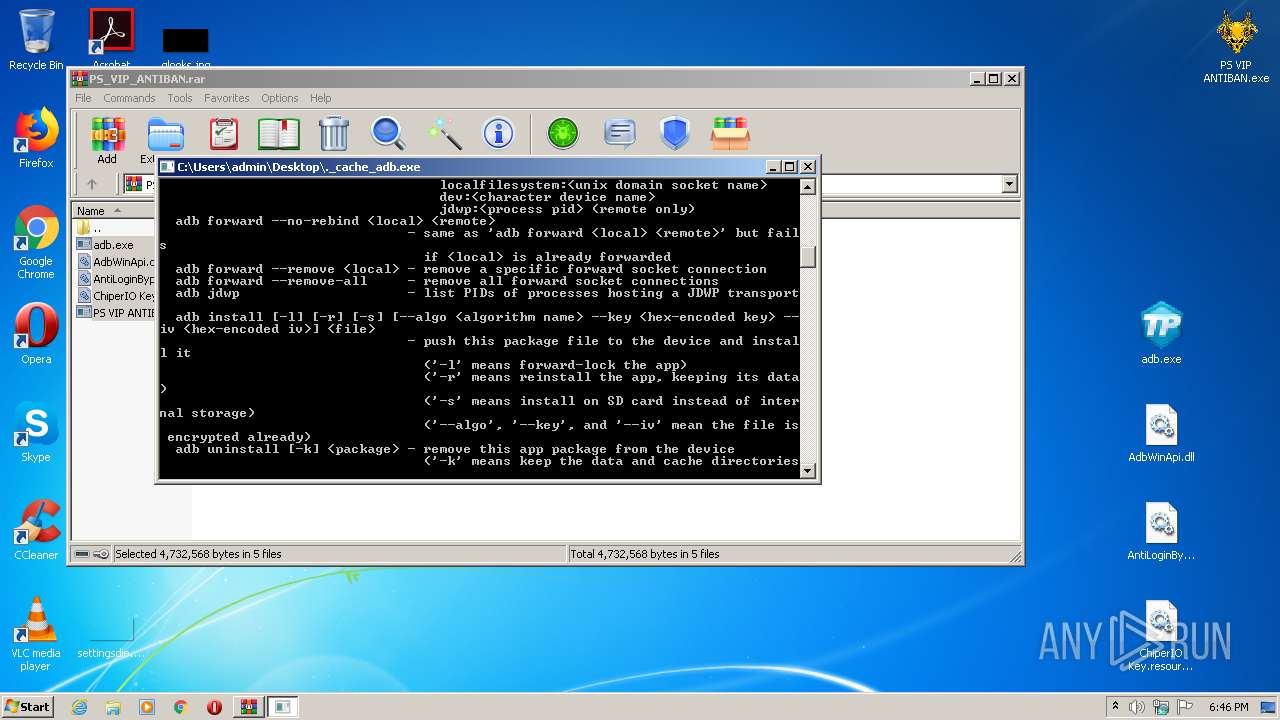
| 2532 | "C:\Users\admin\Desktop\._cache_adb.exe" | C:\Users\admin\Desktop\._cache_adb.exe | adb.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 2648 | "C:\Windows\system32\ntvdm.exe" -i4 | C:\Windows\system32\ntvdm.exe | — | LXGmYx.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 255 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2664 | "C:\Windows\system32\ntvdm.exe" -i3 | C:\Windows\system32\ntvdm.exe | — | LXGmYx.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 255 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2716 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | LXGmYx.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 255 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2948 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3508 | "C:\Users\admin\Desktop\adb.exe" | C:\Users\admin\Desktop\adb.exe | explorer.exe | ||||||||||||
User: admin Company: Synaptics Integrity Level: MEDIUM Description: Synaptics Pointing Device Driver Exit code: 0 Version: 1.0.0.4 Modules
| |||||||||||||||
Total events
1 152
Read events
1 050
Write events
102
Delete events
0
Modification events
| (PID) Process: | (1032) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1032) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1032) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1032) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (1032) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\PS_VIP_ANTIBAN.rar | |||
| (PID) Process: | (1032) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1032) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1032) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1032) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1576) LXGmYx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
4
Suspicious files
14
Text files
17
Unknown types
7
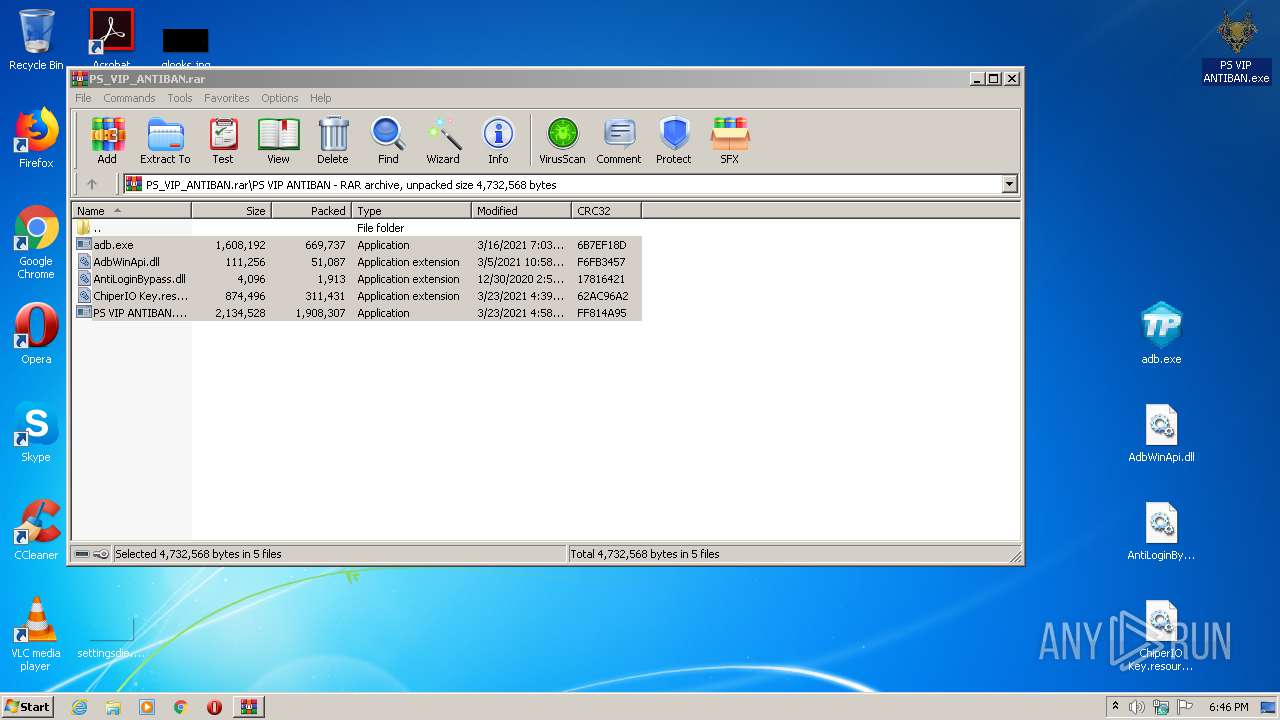
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
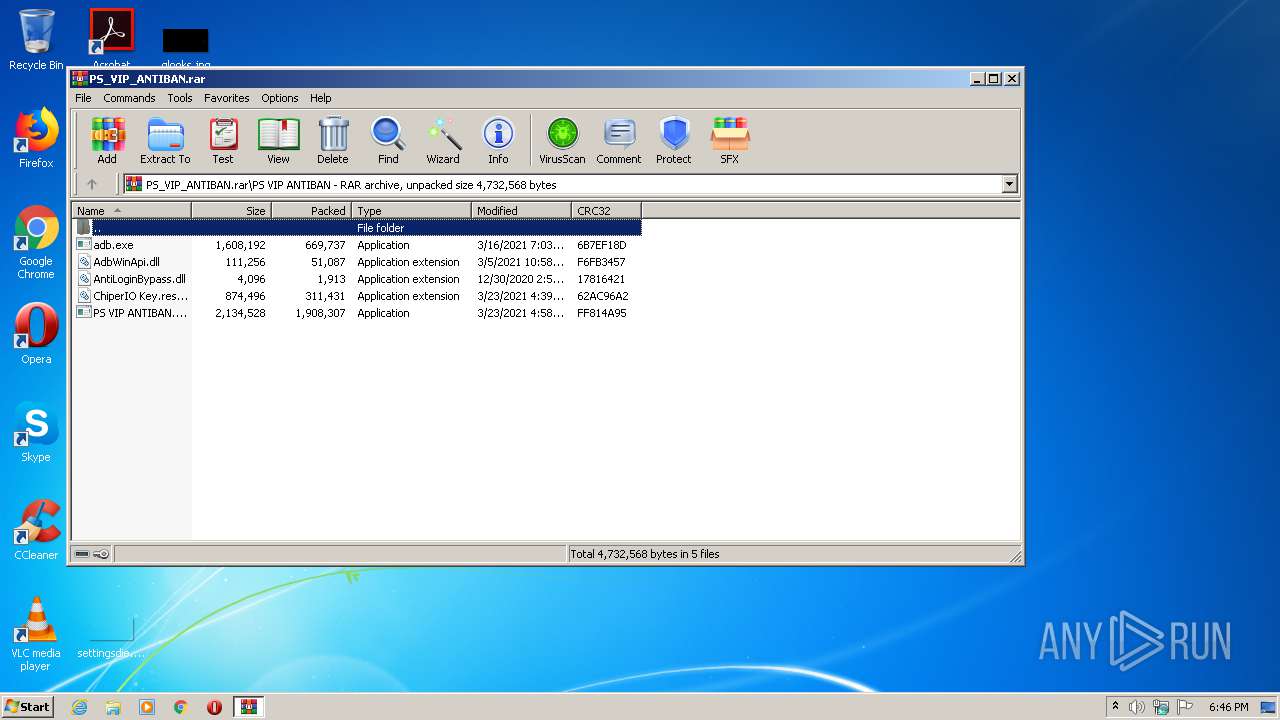
| 1032 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1032.29640\PS VIP ANTIBAN\adb.exe | — | |
MD5:— | SHA256:— | |||
| 1032 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1032.29640\PS VIP ANTIBAN\AdbWinApi.dll | — | |
MD5:— | SHA256:— | |||
| 1032 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1032.29640\PS VIP ANTIBAN\AntiLoginBypass.dll | — | |
MD5:— | SHA256:— | |||
| 1032 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1032.29640\PS VIP ANTIBAN\ChiperIO Key.resources.dll | — | |
MD5:— | SHA256:— | |||
| 1032 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1032.29640\PS VIP ANTIBAN\PS VIP ANTIBAN.exe | — | |
MD5:— | SHA256:— | |||
| 3508 | adb.exe | C:\ProgramData\Synaptics\RCXDA1F.tmp | — | |
MD5:— | SHA256:— | |||
| 2716 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsE01B.tmp | — | |
MD5:— | SHA256:— | |||
| 2716 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsE02B.tmp | — | |
MD5:— | SHA256:— | |||
| 2164 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsE318.tmp | — | |
MD5:— | SHA256:— | |||
| 2164 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsE348.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
18
DNS requests
12
Threats
25
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1576 | LXGmYx.exe | GET | — | 63.251.106.25:799 | http://ddos.dnsnb8.net:799/cj//k1.rar | US | — | — | malicious |
1576 | LXGmYx.exe | GET | — | 63.251.106.25:799 | http://ddos.dnsnb8.net:799/cj//k3.rar | US | — | — | malicious |
1576 | LXGmYx.exe | GET | — | 63.251.106.25:799 | http://ddos.dnsnb8.net:799/cj//k2.rar | US | — | — | malicious |
1576 | LXGmYx.exe | GET | — | 63.251.106.25:799 | http://ddos.dnsnb8.net:799/cj//k2.rar | US | — | — | malicious |
1576 | LXGmYx.exe | GET | — | 63.251.106.25:799 | http://ddos.dnsnb8.net:799/cj//k3.rar | US | — | — | malicious |
1576 | LXGmYx.exe | GET | — | 63.251.106.25:799 | http://ddos.dnsnb8.net:799/cj//k4.rar | US | — | — | malicious |
1576 | LXGmYx.exe | GET | — | 63.251.106.25:799 | http://ddos.dnsnb8.net:799/cj//k5.rar | US | — | — | malicious |
1076 | Synaptics.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
1076 | Synaptics.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
1076 | Synaptics.exe | GET | 200 | 69.42.215.252:80 | http://freedns.afraid.org/api/?action=getdyndns&sha=a30fa98efc092684e8d1c5cff797bcc613562978 | US | text | 31 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1576 | LXGmYx.exe | 63.251.106.25:799 | ddos.dnsnb8.net | Voxel Dot Net, Inc. | US | malicious |
1076 | Synaptics.exe | 69.42.215.252:80 | freedns.afraid.org | Awknet Communications, LLC | US | malicious |
1076 | Synaptics.exe | 142.250.186.97:443 | doc-14-14-docs.googleusercontent.com | Google Inc. | US | whitelisted |
1076 | Synaptics.exe | 172.217.16.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
1076 | Synaptics.exe | 140.82.59.108:80 | — | — | US | suspicious |
1076 | Synaptics.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1076 | Synaptics.exe | 153.92.0.100:80 | xred.site50.net | Hostinger International Limited | US | shared |
1076 | Synaptics.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
1076 | Synaptics.exe | 172.217.16.142:443 | docs.google.com | Google Inc. | US | whitelisted |
1076 | Synaptics.exe | 162.125.66.18:443 | www.dropbox.com | Dropbox, Inc. | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ddos.dnsnb8.net |
| malicious |
xred.mooo.com |
| suspicious |
freedns.afraid.org |
| malicious |
docs.google.com |
| shared |
ocsp.pki.goog |
| whitelisted |
doc-14-14-docs.googleusercontent.com |
| shared |
www.dropbox.com |
| shared |
ocsp.digicert.com |
| whitelisted |
xred.site50.net |
| shared |
www.000webhost.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1040 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to Abused Domain *.mooo.com |
1076 | Synaptics.exe | A Network Trojan was detected | SPYWARE [PTsecurity] njRat style IP-Check |
1576 | LXGmYx.exe | A Network Trojan was detected | BACKDOOR [PTsecurity] Bdaejec.A |
1576 | LXGmYx.exe | A Network Trojan was detected | BACKDOOR [PTsecurity] Bdaejec.A |
1576 | LXGmYx.exe | A Network Trojan was detected | BACKDOOR [PTsecurity] Bdaejec.A |
1576 | LXGmYx.exe | A Network Trojan was detected | BACKDOOR [PTsecurity] Bdaejec.A |
1576 | LXGmYx.exe | A Network Trojan was detected | BACKDOOR [PTsecurity] Bdaejec.A |
1576 | LXGmYx.exe | A Network Trojan was detected | BACKDOOR [PTsecurity] Bdaejec.A |
1576 | LXGmYx.exe | A Network Trojan was detected | BACKDOOR [PTsecurity] Bdaejec.A |
1076 | Synaptics.exe | A Network Trojan was detected | ET POLICY Suspicious User-Agent Containing .exe |
11 ETPRO signatures available at the full report