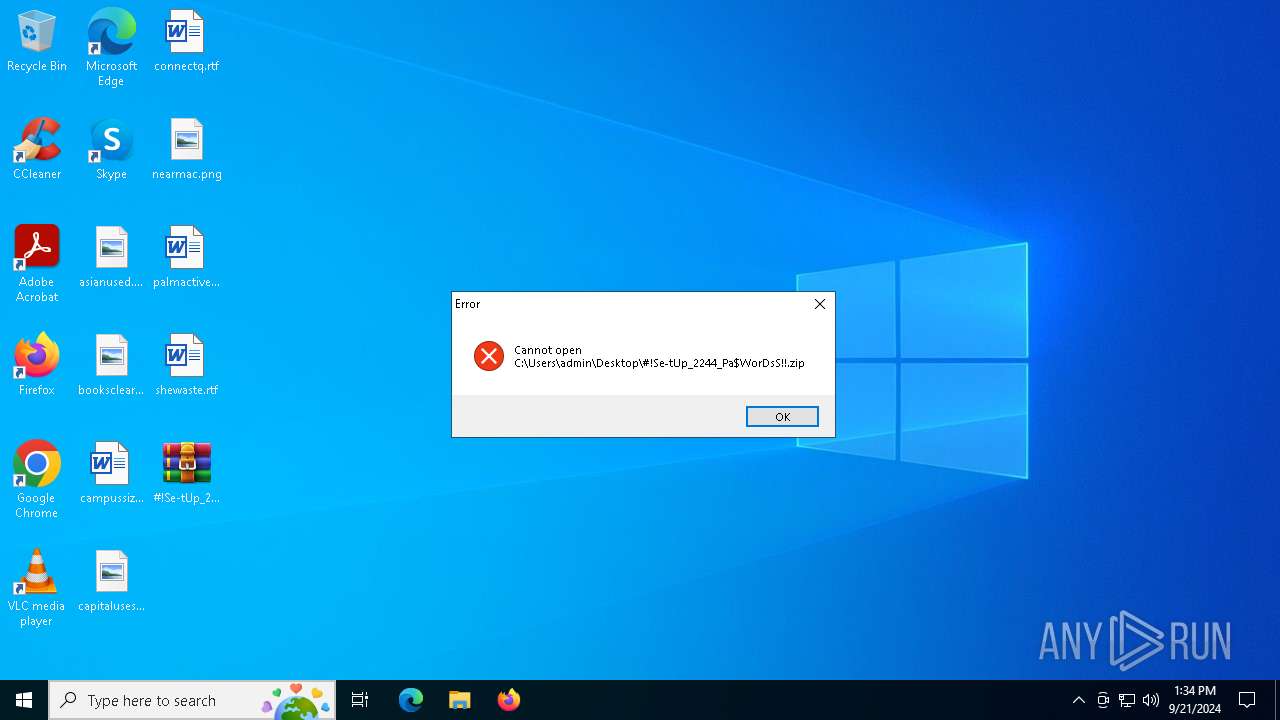
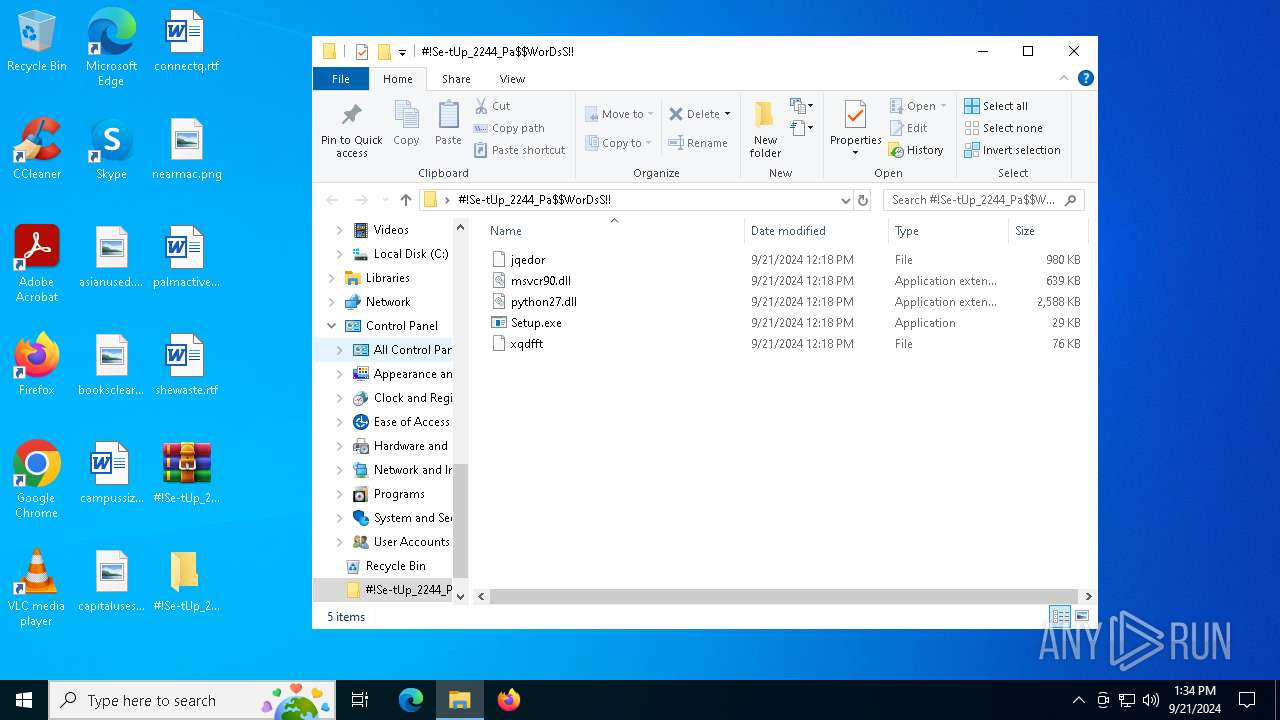
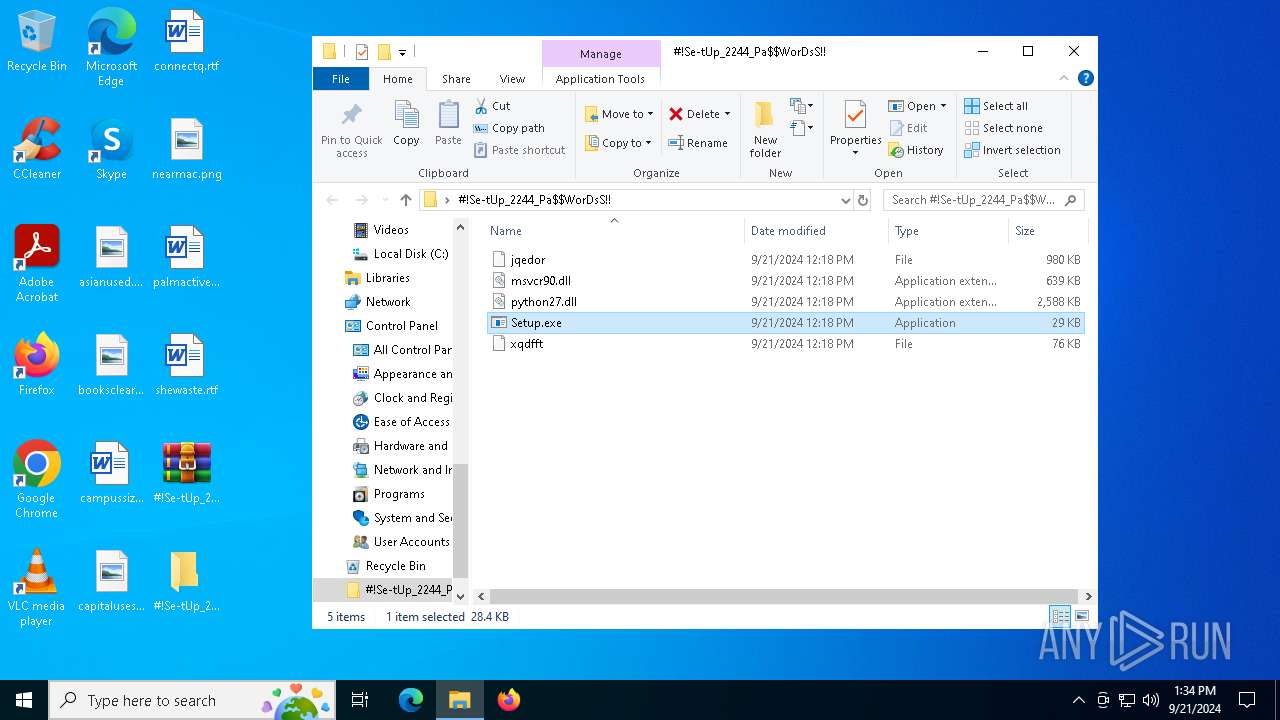
| File name: | #!Se-tUp_2244_Pa$WorDsS!!.zip |
| Full analysis: | https://app.any.run/tasks/26571777-48a2-4dda-b76c-bee1bf66f13a |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | September 21, 2024, 13:34:15 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | A1D18E8F012D3C577460DFC96D65B246 |
| SHA1: | 9DB802989A1A32C5553C0FAD2B51E92BDC2DCC65 |
| SHA256: | B028CB65C9EC369F9407D98257D536B416EAD2A609B90A9CEDB96A4814BBA7B8 |
| SSDEEP: | 98304:lhWoKFVrMUV4WKRpbZr56YH+otIdXKaou4y8Xqz/6ldvt7Zgp6gNmfY6w2GdOnJU:xktchM |
MALICIOUS
LUMMA has been detected (SURICATA)
- Nimble.pif (PID: 5400)
Stealers network behavior
- Nimble.pif (PID: 5400)
Bypass execution policy to execute commands
- powershell.exe (PID: 6320)
Changes powershell execution policy (Bypass)
- Nimble.pif (PID: 5400)
Actions looks like stealing of personal data
- Nimble.pif (PID: 5400)
Probably downloads file via BitsAdmin (POWERSHELL)
- powershell.exe (PID: 6320)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 6804)
SUSPICIOUS
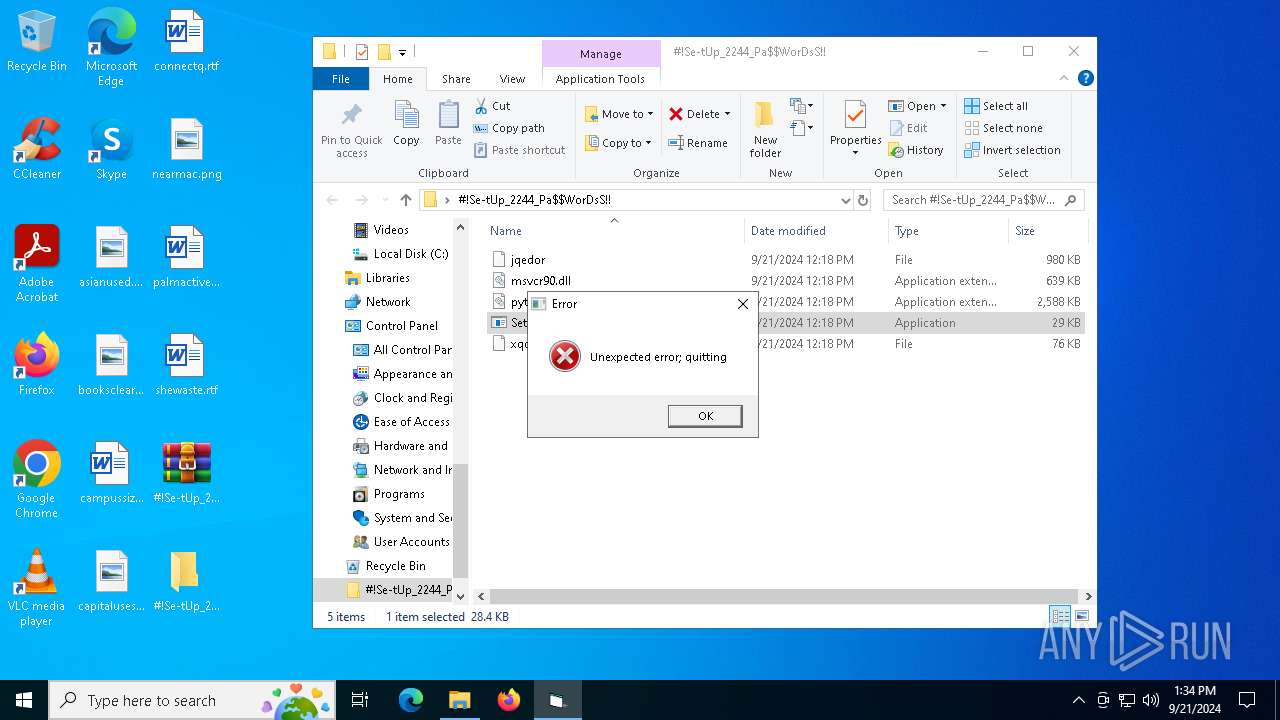
The process drops C-runtime libraries
- WinRAR.exe (PID: 6708)
- Setup.exe (PID: 2804)
Process drops legitimate windows executable
- WinRAR.exe (PID: 6976)
- WinRAR.exe (PID: 6708)
- Setup.exe (PID: 2804)
Loads Python modules
- Setup.exe (PID: 2804)
Executable content was dropped or overwritten
- Setup.exe (PID: 2804)
- more.com (PID: 4288)
- Nimble.pif (PID: 5400)
- NO1F12CQ9P2GBY42WWECW.exe (PID: 3768)
Starts application with an unusual extension
- Setup.exe (PID: 2804)
- more.com (PID: 4288)
Drops a file with a rarely used extension (PIF)
- more.com (PID: 4288)
Starts POWERSHELL.EXE for commands execution
- Nimble.pif (PID: 5400)
The process executes Powershell scripts
- Nimble.pif (PID: 5400)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 6320)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 6320)
There is functionality for communication over UDP network (YARA)
- NO1F12CQ9P2GBY42WWECW.exe (PID: 3768)
- CryptoHelper.exe (PID: 7044)
Starts CMD.EXE for commands execution
- NO1F12CQ9P2GBY42WWECW.exe (PID: 3768)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6800)
The process executes via Task Scheduler
- CryptoHelper.exe (PID: 7044)
INFO
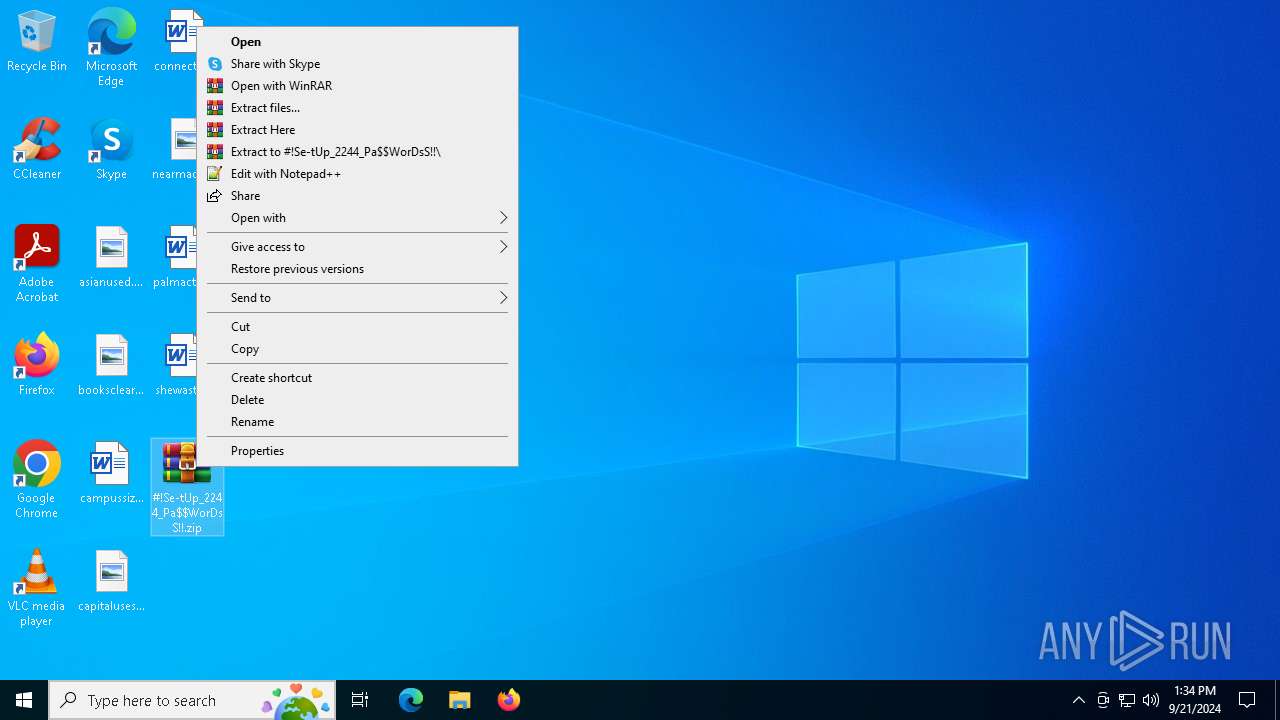
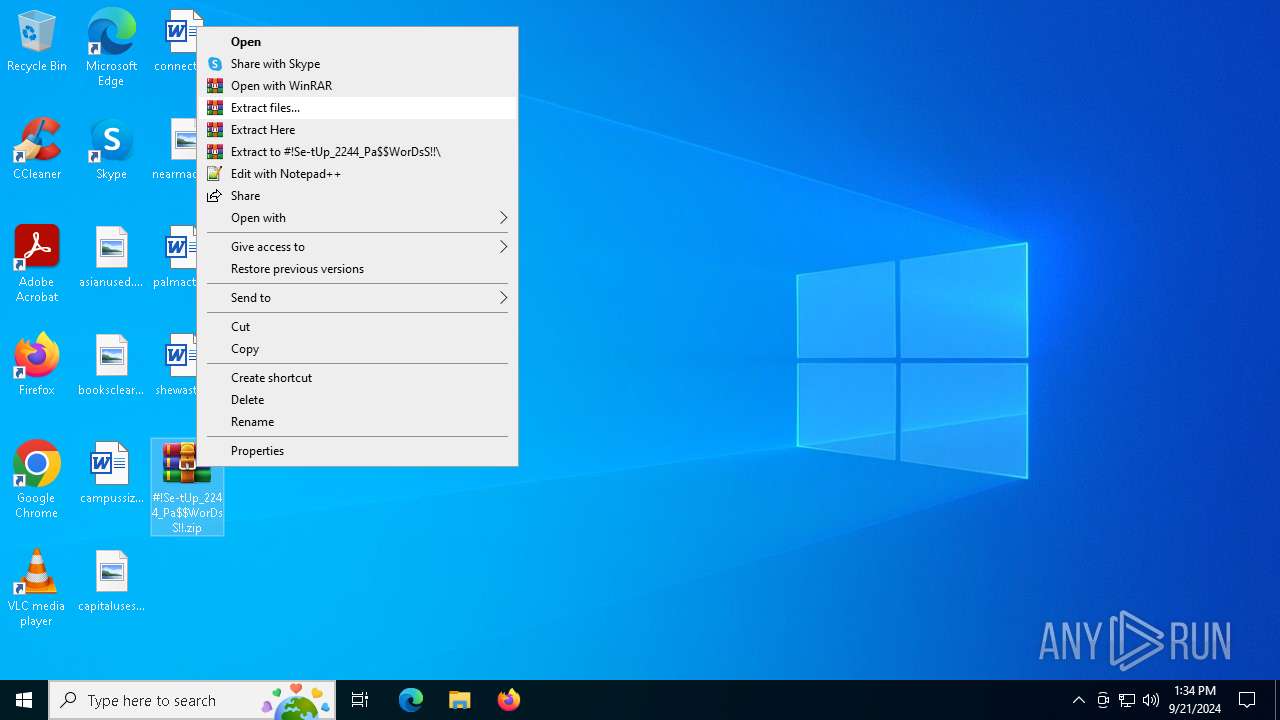
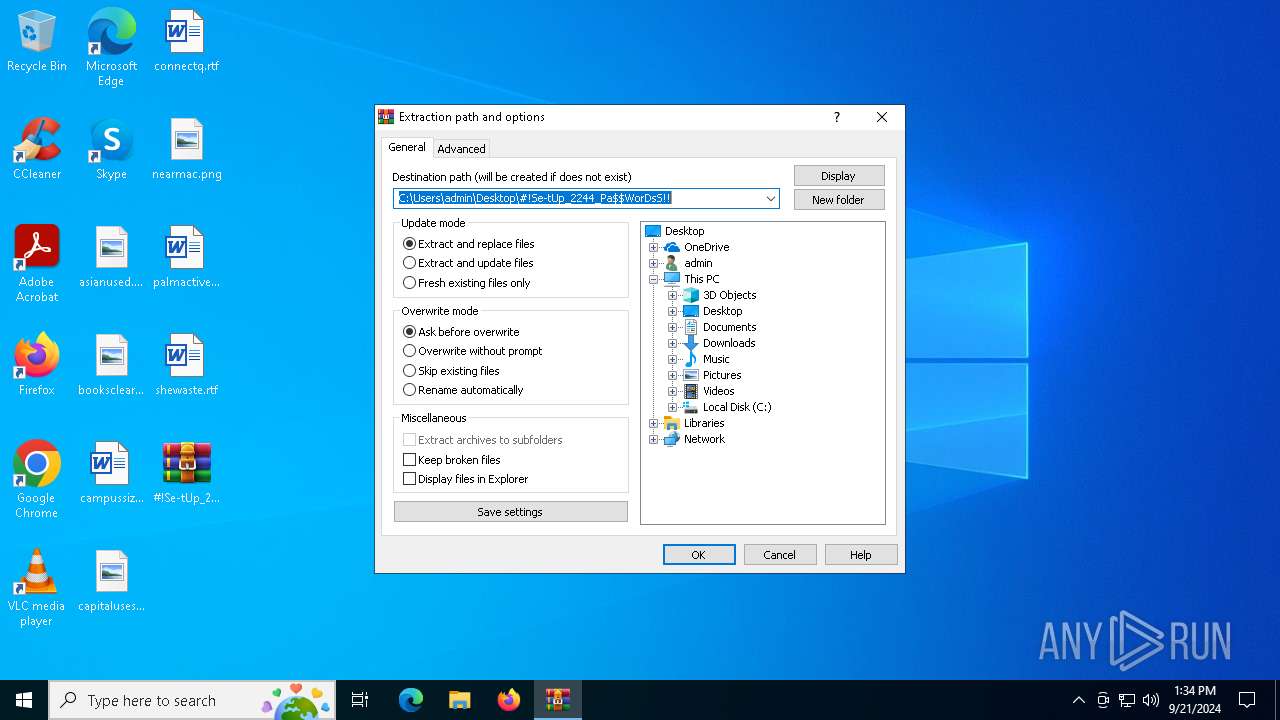
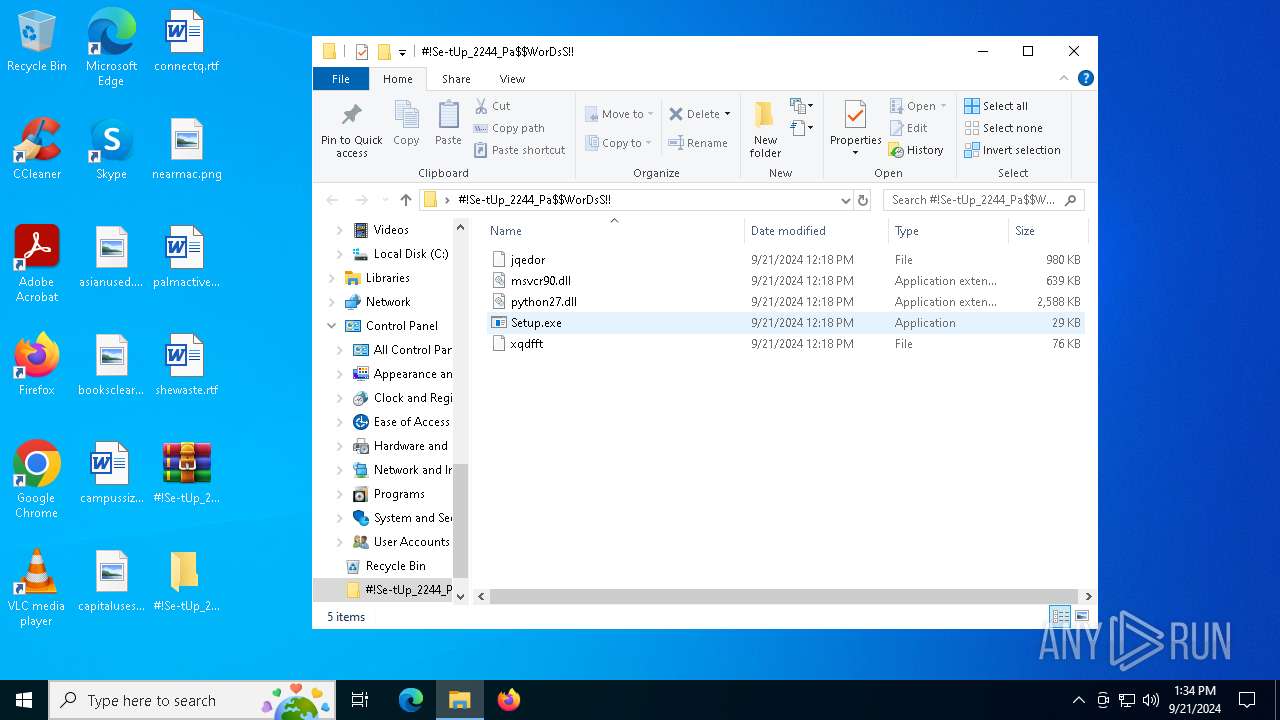
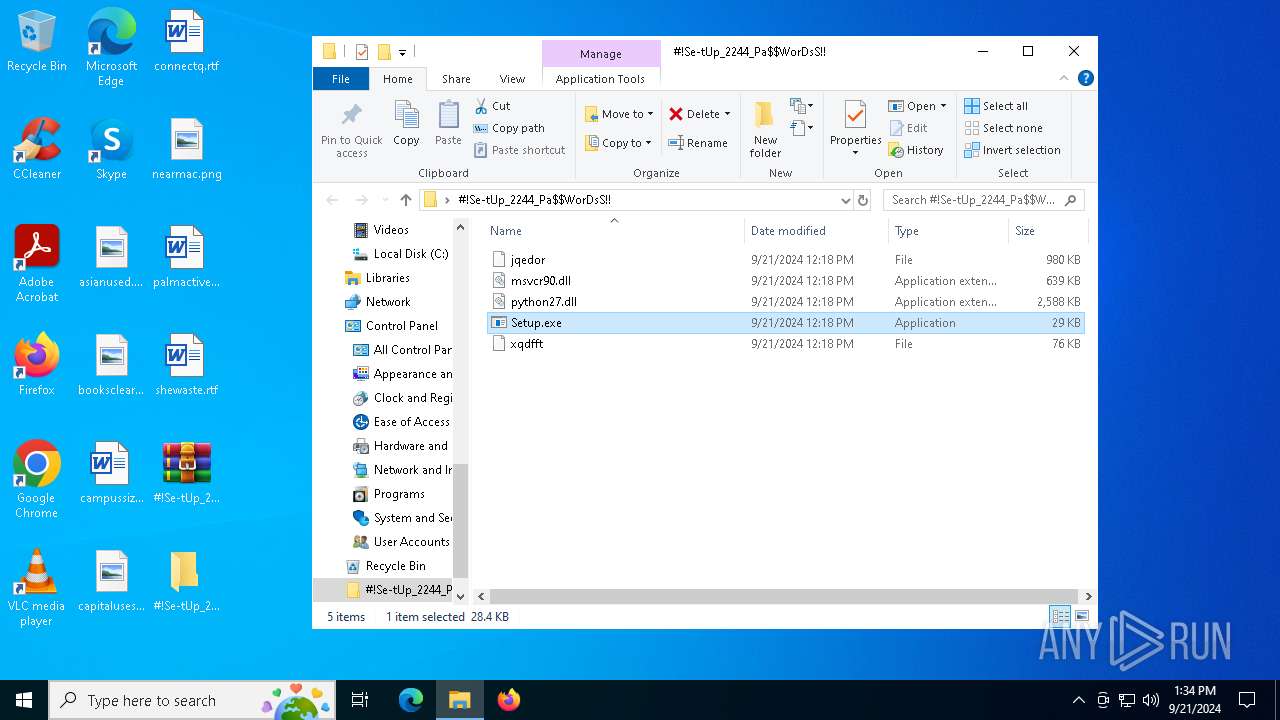
Manual execution by a user
- WinRAR.exe (PID: 6976)
- Setup.exe (PID: 2804)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6976)
The process uses the downloaded file
- WinRAR.exe (PID: 6976)
- powershell.exe (PID: 6320)
Checks supported languages
- Setup.exe (PID: 2804)
- StrCmp.exe (PID: 644)
- more.com (PID: 4288)
- Nimble.pif (PID: 5400)
- NO1F12CQ9P2GBY42WWECW.exe (PID: 3768)
Creates files or folders in the user directory
- Setup.exe (PID: 2804)
Reads the computer name
- Setup.exe (PID: 2804)
- StrCmp.exe (PID: 644)
- more.com (PID: 4288)
- Nimble.pif (PID: 5400)
Create files in a temporary directory
- Setup.exe (PID: 2804)
- more.com (PID: 4288)
- Nimble.pif (PID: 5400)
Reads the software policy settings
- Nimble.pif (PID: 5400)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6320)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6320)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:09:21 14:18:50 |
| ZipCRC: | 0x45adc72a |
| ZipCompressedSize: | 45184 |
| ZipUncompressedSize: | 77461 |
| ZipFileName: | xqdfft |
Total processes
143
Monitored processes
18
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | C:\Users\admin\AppData\Roaming\maf\KOXZKONOMQIFDAIMJQAGHVX\StrCmp.exe | C:\Users\admin\AppData\Roaming\maf\KOXZKONOMQIFDAIMJQAGHVX\StrCmp.exe | — | Setup.exe | |||||||||||
User: admin Company: aaa Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2272 | schtasks /create /f /sc MINUTE /mo 1 /tn CryptoHelper /tr C:\ProgramData\CryptoHelper.exe | C:\Windows\SysWOW64\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 2804 | "C:\Users\admin\Desktop\#!Se-tUp_2244_Pa$WorDsS!!\Setup.exe" | C:\Users\admin\Desktop\#!Se-tUp_2244_Pa$WorDsS!!\Setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 2944 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 3768 | "C:\Users\admin\AppData\Local\Temp\NO1F12CQ9P2GBY42WWECW.exe" | C:\Users\admin\AppData\Local\Temp\NO1F12CQ9P2GBY42WWECW.exe | Nimble.pif | ||||||||||||
User: admin Company: Marek Jasinski Integrity Level: MEDIUM Description: FreeCommander - freeware file manager for Windows Exit code: 0 Version: 2024.0.0.901 Modules
| |||||||||||||||
| 4288 | C:\WINDOWS\SysWOW64\more.com | C:\Windows\SysWOW64\more.com | Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5220 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 5364 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | more.com | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5400 | C:\Users\admin\AppData\Local\Temp\Nimble.pif | C:\Users\admin\AppData\Local\Temp\Nimble.pif | more.com | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
8 307
Read events
8 295
Write events
12
Delete events
0
Modification events
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_0 |
Value: 4C000000730100000402000000000000F0F0F000000000000000000000000000000000000000000058000B0000000000000000003B000000B402000000000000000000000000000001000000 | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_1 |
Value: 4C000000730100000500000000000000F0F0F0000000000000000000000000000000000000000000D80310000000000000000000180000002A00000000000000000000000000000002000000 | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_2 |
Value: 4C000000730100000400000000000000F0F0F00000000000000000000000000000000000000000009C0305000000000000000000180000006400000000000000000000000000000003000000 | |||
| (PID) Process: | (6976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\#!Se-tUp_2244_Pa$WorDsS!! | |||
| (PID) Process: | (6976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
9
Suspicious files
6
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4288 | more.com | C:\Users\admin\AppData\Local\Temp\tcvyglqdgdqe | — | |
MD5:— | SHA256:— | |||
| 6976 | WinRAR.exe | C:\Users\admin\Desktop\#!Se-tUp_2244_Pa$WorDsS!!\xqdfft | abr | |
MD5:0BA06A67683C5B51E3F2500867607410 | SHA256:B9C5F8910B193F96F29D66A5D654DB9113FF765634A5603203A6AB20C1ECCBE9 | |||
| 2804 | Setup.exe | C:\Users\admin\AppData\Roaming\maf\python27.dll | executable | |
MD5:7066D26251CD52653FE4C135DDCAC003 | SHA256:5DBAB5DEDB026DCAA2C4CA01D775A388AE0C8AC339BD15214BE6D65889190603 | |||
| 6976 | WinRAR.exe | C:\Users\admin\Desktop\#!Se-tUp_2244_Pa$WorDsS!!\Setup.exe | executable | |
MD5:B6F6C3C38568EE26F1AC70411A822405 | SHA256:A73454C7FAD23A80A3F6540AFDB64FC334980A11402569F1986AA39995AE496D | |||
| 5400 | Nimble.pif | C:\Users\admin\AppData\Local\Temp\NO1F12CQ9P2GBY42WWECW.exe | executable | |
MD5:4D05968F9891DA5D6550DF62F710AD31 | SHA256:BCBA61234968F946642ACA837984AD02BAEF7D1E455F928A86B32412B344EDC5 | |||
| 6320 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_20hoglrs.1d3.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2804 | Setup.exe | C:\Users\admin\AppData\Local\Temp\bd972ec2 | binary | |
MD5:51C19824292705E75F547981EAC4F690 | SHA256:5F811129589FC984E073F5D32F3FC8190D5253C928B7A00624190EC13B9DF868 | |||
| 4288 | more.com | C:\Users\admin\AppData\Local\Temp\Nimble.pif | executable | |
MD5:E2AD18DD86E1107005198C70276B66D8 | SHA256:940C2A648A7DC2999998BB720890FE794157F5FE22443B588126B14419046324 | |||
| 5400 | Nimble.pif | C:\Users\admin\AppData\Local\Temp\XE0N7G7CHBLOYNBO.ps1 | text | |
MD5:FD8EDC156E282155F7D2FBA4663530A3 | SHA256:F6D16DB3E818DC771911891F60A40C967676690F90F7EA03F7A2C6172966C881 | |||
| 6320 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_yjyitrwq.dtd.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
34
DNS requests
18
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3356 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7004 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7004 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6248 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2640 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3356 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3356 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6248 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
trolleyrreiwn.shop |
| unknown |
pang-scrooge-carnage.shop |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5400 | Nimble.pif | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |
2256 | svchost.exe | Misc activity | ET INFO Pastebin Service Domain in DNS Lookup (rentry .co) |
5400 | Nimble.pif | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |