| File name: | LummaC2.exe |
| Full analysis: | https://app.any.run/tasks/785eb0ea-185b-486a-8454-19e794d2d395 |
| Verdict: | Malicious activity |
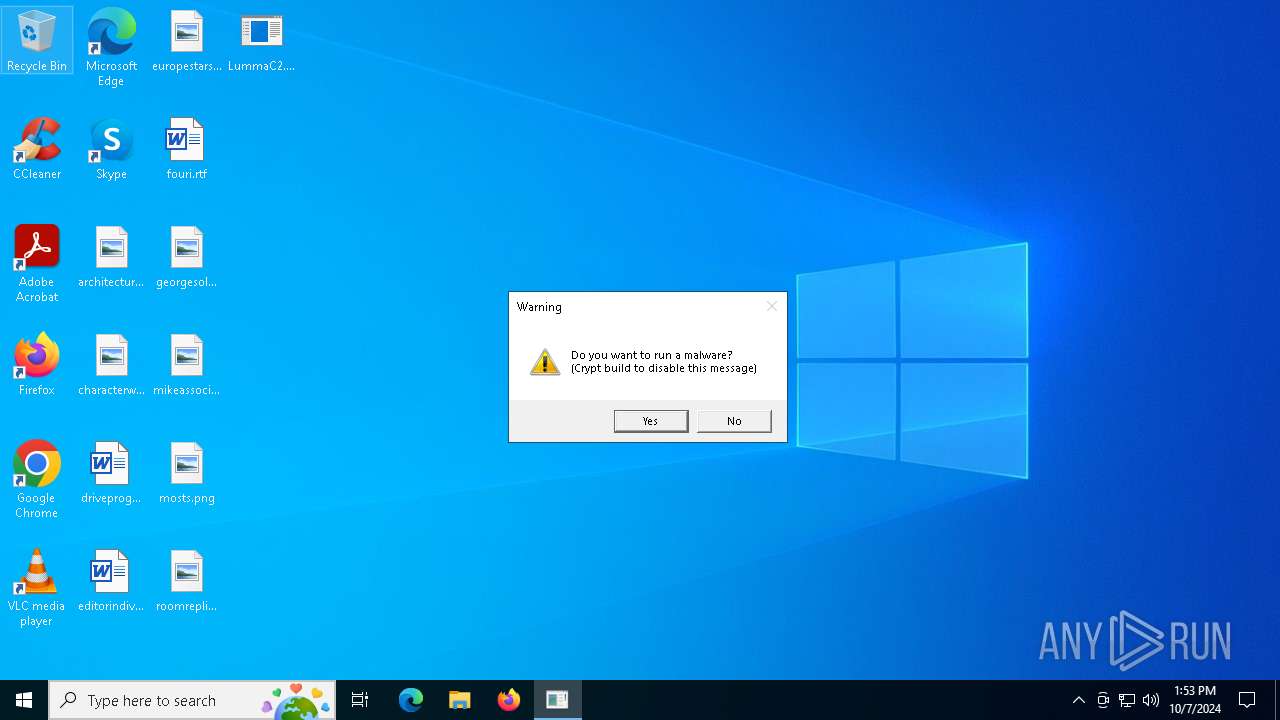
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | October 07, 2024, 13:53:15 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 21108F05D5813655E566CDD0AC4048E6 |
| SHA1: | 957C8436B406A476887D54439E57676DAA436194 |
| SHA256: | AF8AF32585C911CB7AF798349F50A31642344E4059DFECEE52384512EEF0A05D |
| SSDEEP: | 12288:3Nuvj0hk1RRtOgpLz4mfiH2EDlfBluufIe:3U3kKiWExfBluuge |
MALICIOUS
Actions looks like stealing of personal data
- LummaC2.exe (PID: 2868)
LUMMA has been detected (YARA)
- LummaC2.exe (PID: 2868)
SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- LummaC2.exe (PID: 2868)
Reads the computer name
- LummaC2.exe (PID: 2868)
Reads the machine GUID from the registry
- LummaC2.exe (PID: 2868)
Reads the software policy settings
- LummaC2.exe (PID: 2868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(2868) LummaC2.exe
C2 (9)exilepolsiy.sbs
bemuzzeki.sbs
invinjurhey.sbs
exemplarou.sbs
frizzettei.sbs
laddyirekyi.sbs
isoplethui.sbs
epiloggati.sbs
wickedneatr.sbs
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:10:04 13:44:42+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 303104 |
| InitializedDataSize: | 56320 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xd110 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
127
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2868 | "C:\Users\admin\Desktop\LummaC2.exe" | C:\Users\admin\Desktop\LummaC2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
Lumma(PID) Process(2868) LummaC2.exe C2 (9)exilepolsiy.sbs bemuzzeki.sbs invinjurhey.sbs exemplarou.sbs frizzettei.sbs laddyirekyi.sbs isoplethui.sbs epiloggati.sbs wickedneatr.sbs | |||||||||||||||
Total events
3 314
Read events
3 314
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
30
DNS requests
5
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1776 | RUXIMICS.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1776 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2868 | LummaC2.exe | 188.114.96.3:443 | epiloggati.sbs | CLOUDFLARENET | NL | malicious |
2280 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1776 | RUXIMICS.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2120 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4324 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
epiloggati.sbs |
| malicious |
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | A Network Trojan was detected | ET MALWARE Lumma Stealer Related Activity |
— | — | A Network Trojan was detected | ET MALWARE Lumma Stealer CnC Host Checkin |
— | — | A Network Trojan was detected | ET MALWARE Lumma Stealer Related Activity M2 |
— | — | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Win32/Lumma Stealer Check-In |
— | — | A Network Trojan was detected | ET MALWARE Lumma Stealer CnC Host Checkin |
— | — | Malware Command and Control Activity Detected | ET MALWARE [ANY.RUN] Win32/Lumma Stealer Exfiltration |
— | — | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Win32/Lumma Stealer Exfiltration |
— | — | A Network Trojan was detected | ET MALWARE Lumma Stealer CnC Host Checkin |
— | — | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Win32/Lumma Stealer Check-In |
1 ETPRO signatures available at the full report