| File name: | Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.7z |
| Full analysis: | https://app.any.run/tasks/e5bf7954-af46-4271-8946-866e2fac855e |
| Verdict: | Malicious activity |
| Threats: | Dharma is advanced ransomware that has been observed in the wild since 2016. It is considered to be the second most profitable RaaS operation by the FBI. The malware targets hospitals and state organizations, encrypts files, and demands a payment to restore access to lost information. |
| Analysis date: | May 09, 2025, 17:42:34 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
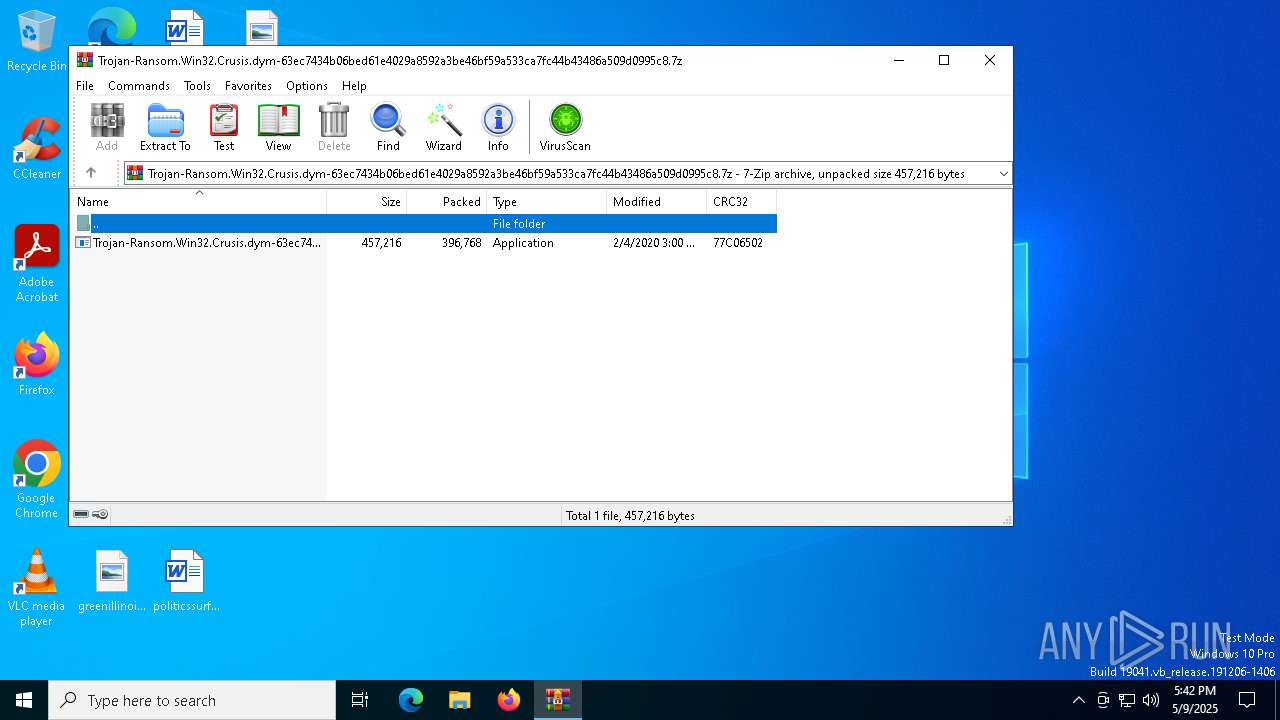
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | BD203F3AA6917DAB5561A5AAE94C49C1 |
| SHA1: | 3F2BCB793493B4A13FEF6EFD67D50FFE8F4062B3 |
| SHA256: | AF3B5E9CAC5AA06A934159868C22A4FF871EE6D4DD7604F6881B2D1D2E62984C |
| SSDEEP: | 12288:1/hL6ovfUAxSVYPU/42wgS6N29j4NmD68bOH0:1/hL6oHUAxSVYPU436N2mmD6UOH0 |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 5972)
DHARMA mutex has been found
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 5956)
RANSOMWARE has been detected
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 5956)
Deletes shadow copies
- cmd.exe (PID: 6800)
Changes the autorun value in the registry
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 5956)
Create files in the Startup directory
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 5956)
Renames files like ransomware
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 5956)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 7924)
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 5956)
Application launched itself
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 7924)
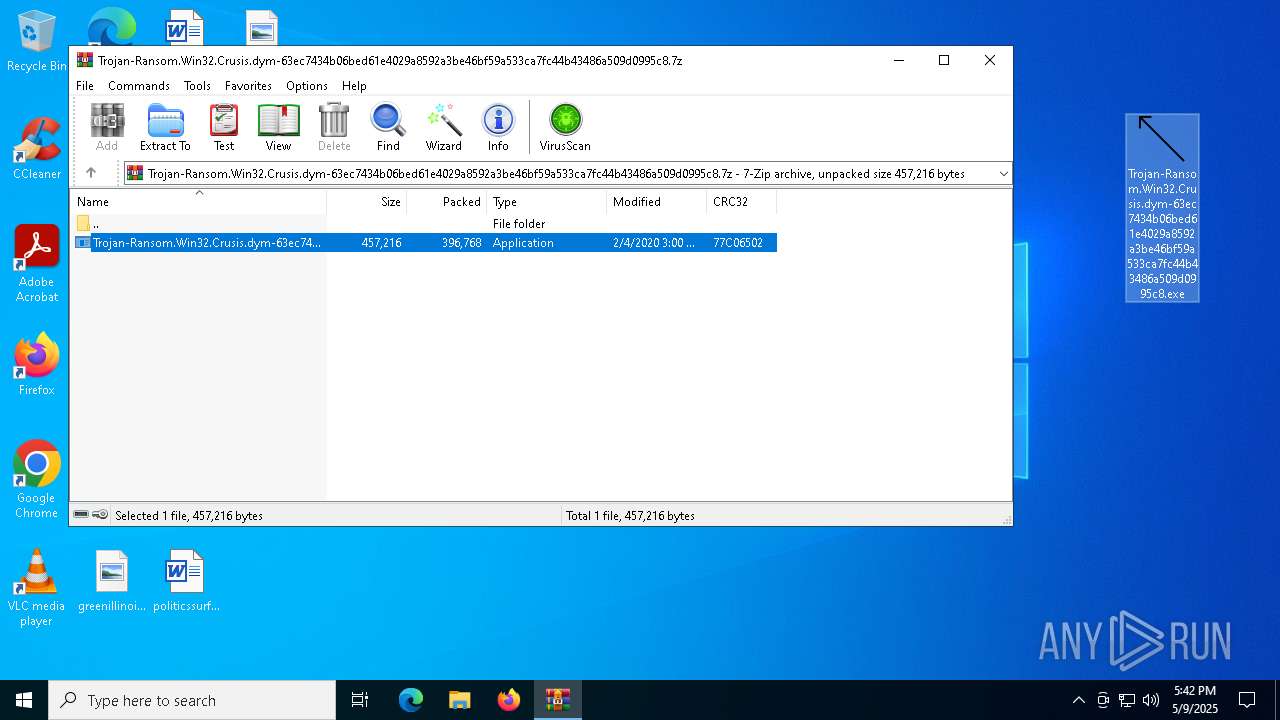
Executable content was dropped or overwritten
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 5956)
Starts CMD.EXE for commands execution
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 5956)
Creates file in the systems drive root
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 5956)
Executes as Windows Service
- VSSVC.exe (PID: 3240)
The process creates files with name similar to system file names
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 5956)
Process drops legitimate windows executable
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 5956)
INFO
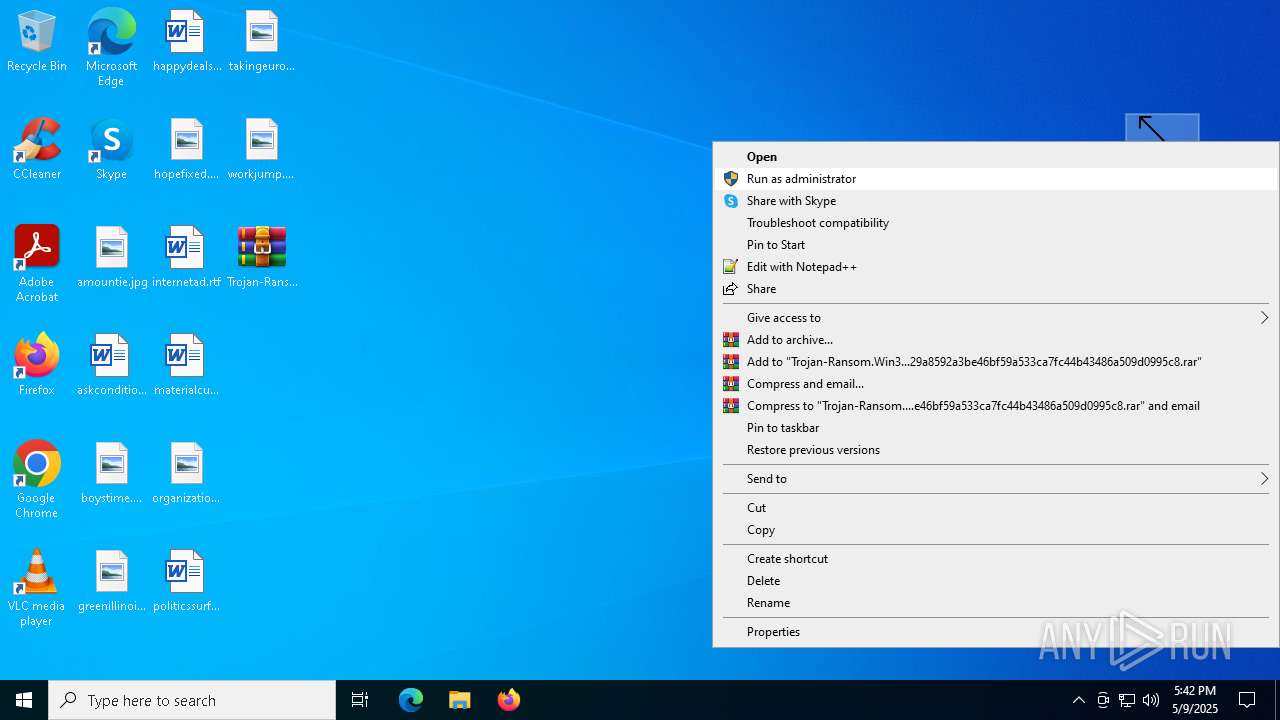
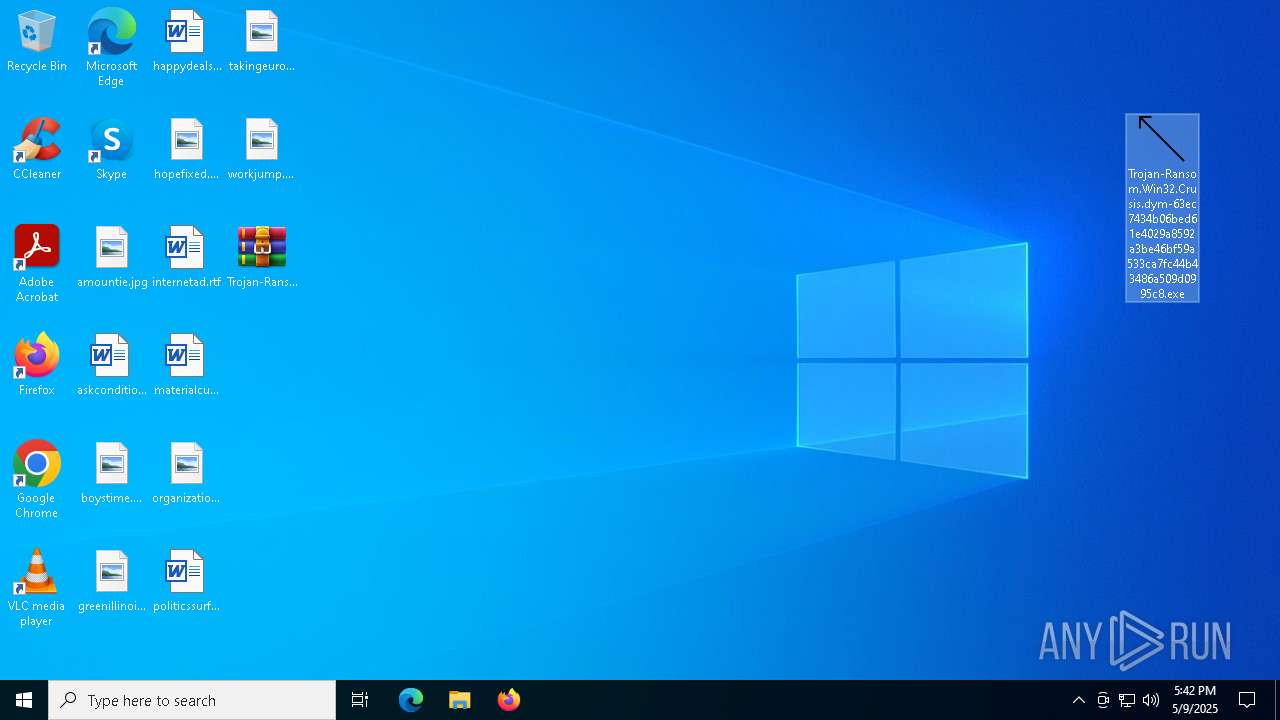
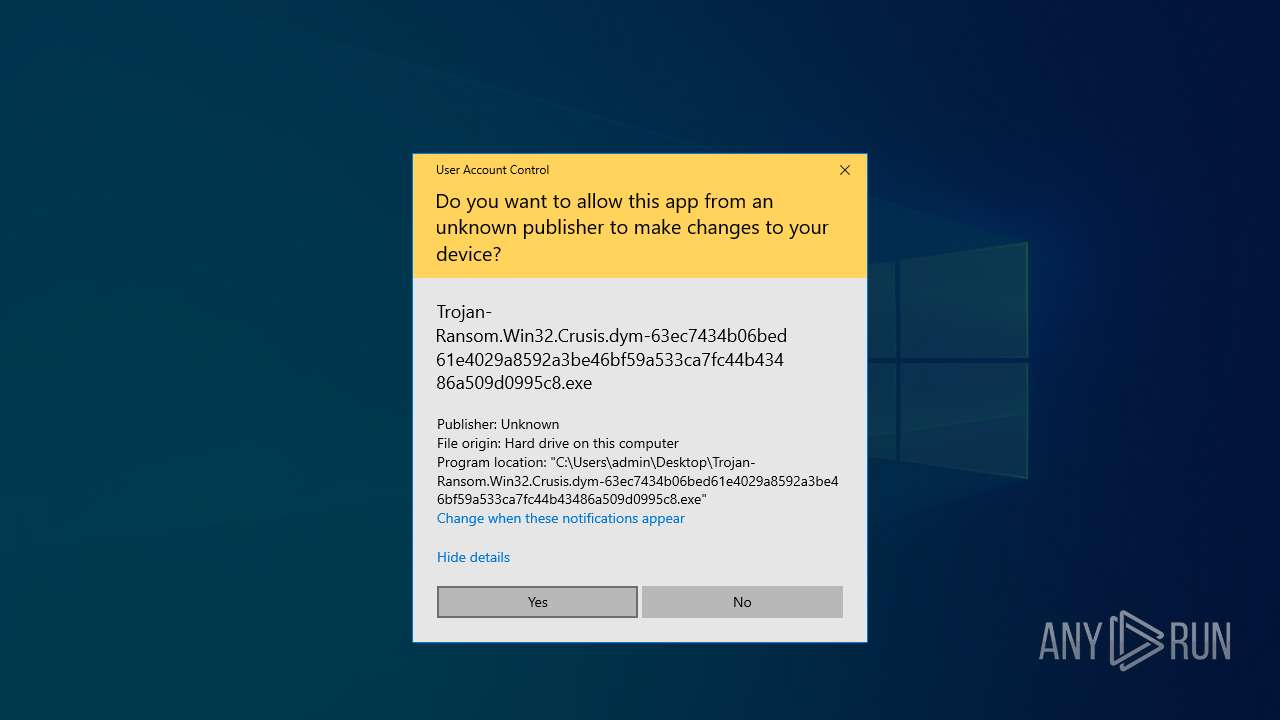
Manual execution by a user
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 7924)
The sample compiled with english language support
- WinRAR.exe (PID: 5972)
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 5956)
Checks supported languages
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 7924)
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 5956)
- mode.com (PID: 2692)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5972)
Reads the computer name
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 7924)
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 5956)
Create files in a temporary directory
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 7924)
UPX packer has been detected
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 7924)
Disables trace logs
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 7924)
Starts MODE.COM to configure console settings
- mode.com (PID: 2692)
Creates files or folders in the user directory
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 5956)
Creates files in the program directory
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 5956)
The sample compiled with korean language support
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 5956)
The sample compiled with portuguese language support
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 5956)
Reads the software policy settings
- slui.exe (PID: 7268)
The sample compiled with german language support
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 5956)
The sample compiled with french language support
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 5956)
The sample compiled with Italian language support
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 5956)
The sample compiled with japanese language support
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 5956)
The sample compiled with russian language support
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 5956)
The sample compiled with spanish language support
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 5956)
The sample compiled with turkish language support
- Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe (PID: 5956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2020:02:04 15:00:04+00:00 |
| ArchivedFileName: | Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe |
Total processes
146
Monitored processes
11
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1020 | vssadmin delete shadows /all /quiet | C:\Windows\System32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1812 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2096 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2692 | mode con cp select=1251 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3240 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5956 | C:\Users\admin\Desktop\Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe | C:\Users\admin\Desktop\Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe | Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe | ||||||||||||
User: admin Company: ThunderSoft Integrity Level: HIGH Description: Nasas Flatten Ceatec 2319 Modules
| |||||||||||||||
| 5972 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.7z | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6800 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7232 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) | |||||||||||||||
| 7268 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 425
Read events
1 406
Write events
19
Delete events
0
Modification events
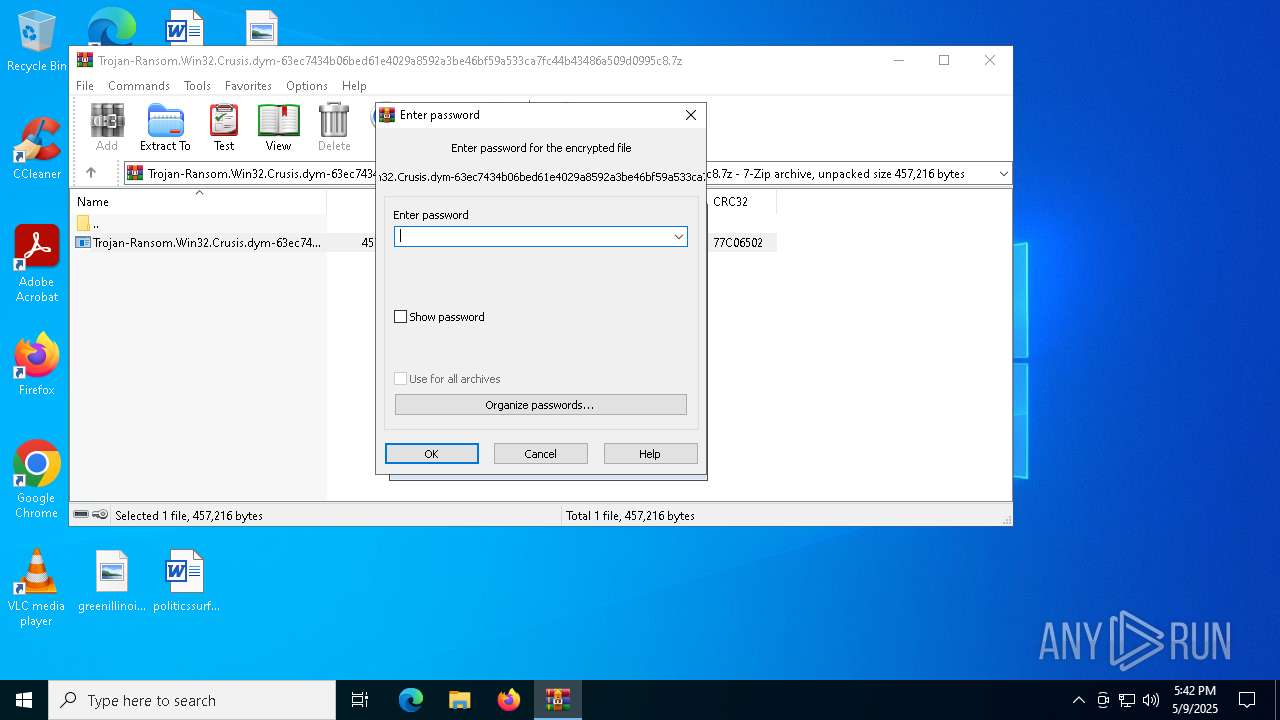
| (PID) Process: | (5972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (5972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (5972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (5972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | psize |
Value: 80 | |||
| (PID) Process: | (5972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | crc |
Value: 70 | |||
| (PID) Process: | (5972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_0 |
Value: 4C000000730100000402000000000000F0F0F00000000000000000000000000000000000000000000803040000000000000000003B000000B402000000000000000000000000000001000000 | |||
| (PID) Process: | (5972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_1 |
Value: 4C000000730100000500000000000000F0F0F0000000000000000000000000000000000000000000E20204000000000000000000180000002A00000000000000000000000000000002000000 | |||
Executable files
437
Suspicious files
17 732
Text files
11
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7924 | Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe | C:\Users\admin\AppData\Local\Temp\62821472 | — | |
MD5:— | SHA256:— | |||
| 5956 | Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe | C:\$Recycle.Bin\S-1-5-21-1693682860-607145093-2874071422-1001\desktop.ini | — | |
MD5:— | SHA256:— | |||
| 5956 | Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe | C:\$Recycle.Bin\S-1-5-21-1693682860-607145093-2874071422-500\desktop.ini | — | |
MD5:— | SHA256:— | |||
| 5956 | Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe | C:\$Recycle.Bin\S-1-5-21-1693682860-607145093-2874071422-1000\desktop.ini | — | |
MD5:— | SHA256:— | |||
| 5956 | Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe | C:\BOOTNXT | — | |
MD5:— | SHA256:— | |||
| 5956 | Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe | C:\found.000\dir0000.chk\UpdateSessionOrchestration.016.etl | — | |
MD5:— | SHA256:— | |||
| 5956 | Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe | C:\$WinREAgent\Backup\location.txt | — | |
MD5:— | SHA256:— | |||
| 5956 | Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe | C:\$Recycle.Bin\S-1-5-18\desktop.ini | — | |
MD5:— | SHA256:— | |||
| 5956 | Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe | C:\$WinREAgent\Backup\Winre.wim.id-26B799FA.[admin@datastex.club].ROGER | — | |
MD5:— | SHA256:— | |||
| 5956 | Trojan-Ransom.Win32.Crusis.dym-63ec7434b06bed61e4029a8592a3be46bf59a533ca7fc44b43486a509d0995c8.exe | C:\found.000\dir0000.chk\UpdateSessionOrchestration.037.etl | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
25
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8072 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8072 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |