| URL: | https://go.keepo.bio/redirect?event_type=open_link&continue=eyJsaW5rIjoiaHR0cHM6XC9cL2J1aWxkZXIuY2hlbGVwaS5jb250cmFjdG9yc1wvcjVZVWlka0ghNHVTUG10bU5WRndrTXRcLyIsInRpdGxlIjoiVGFrZSIsImlkIjoiNjMwNDk3YjktODEwNC00ZWU1LTg2NDQtNjNjNjQ2YTQxYzk1Iiwic2l0ZUlkIjoiYzc0MzE0MWYtMzg3ZS00NjE2LWExMzgtZGY1MWRhOWJkODc1IiwidXNlcklkIjoiOWJhNjRlMzAtM2Y1MC00Nzc5LWI4MTItN2ExM2VmNTc0YjkyIiwidXJsIjoiaHR0cHM6XC9cL3Rha2Vvbi5rZWVwby5iaW8iLCJzZWN0aW9uSWQiOiJmZmJmMWJmYS0yNGJlLTQ5YjItOWIwOS0zOTVkNzczYjM1ODEiLCJzZWN0aW9uVHlwZSI6ImxpbmtzIn0%3D |
| Full analysis: | https://app.any.run/tasks/036cd184-b795-4cae-bc79-7b475e90d665 |
| Verdict: | Malicious activity |
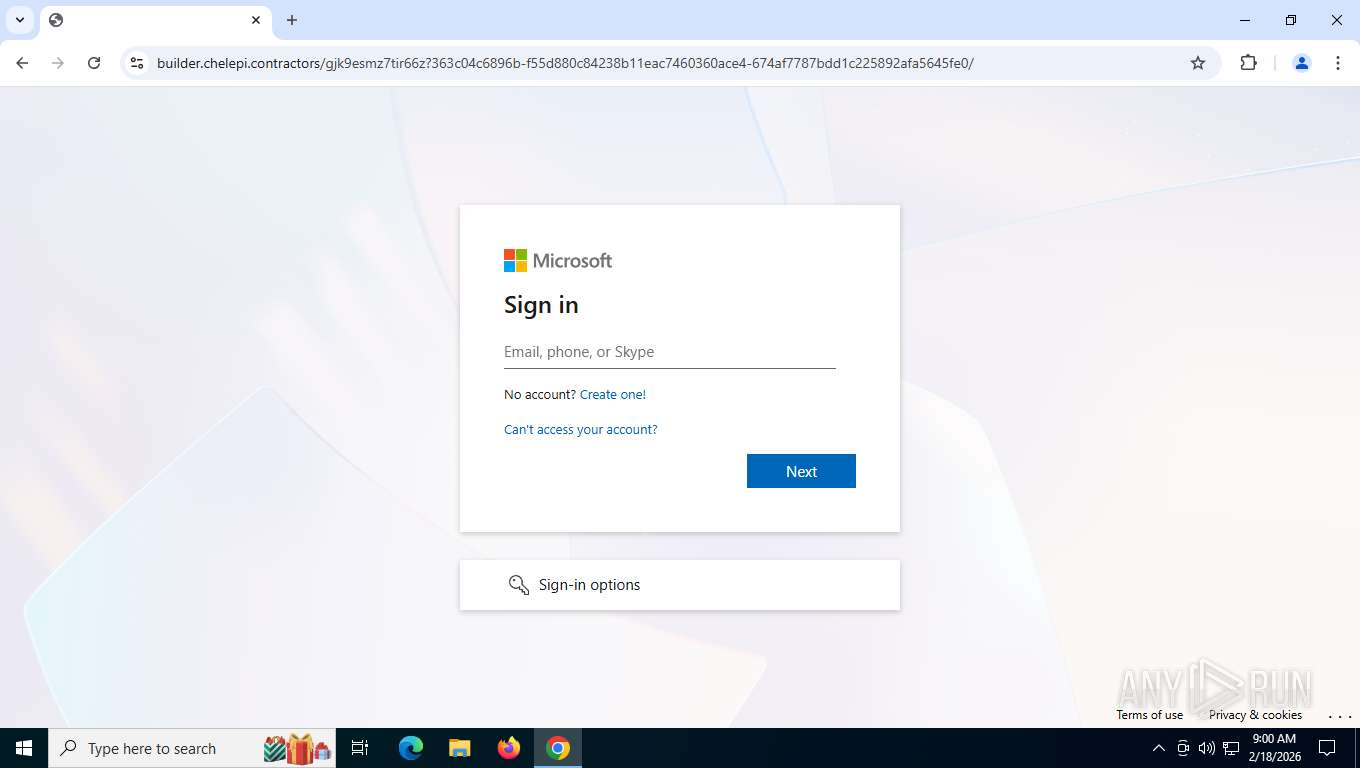
| Threats: | Tycoon 2FA is a phishing-as-a-service (PhaaS) platform designed to bypass multi-factor authentication (MFA) protections, particularly targeting Microsoft 365 and Gmail accounts. Its advanced evasion techniques and modular architecture make it a significant threat to organizations relying on MFA for security. |
| Analysis date: | February 18, 2026, 14:00:16 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FE5AF48028214D9CE8AAD947B5699961 |
| SHA1: | 556D47FBC84A6F1077375B94A12CFB52EA91A72B |
| SHA256: | AF2BF32C978FD467BF62FF1B4D9D515DBC54E7E84845041418A78F8F4BB07E4A |
| SSDEEP: | 12:2m36YwCdWw8n8dz2+3XzQutQ1TOPjFYxSIgQqz:2m3sCEw733XzQuUToG72 |
MALICIOUS
PHISHING has been detected (ML)
- chrome.exe (PID: 8396)
Tycoon 2FA phishing kit has been detected
- chrome.exe (PID: 8396)
PHISHING has been detected (SURICATA)
- chrome.exe (PID: 7088)
Fake Microsoft Authentication Page has been detected
- chrome.exe (PID: 8396)
SUSPICIOUS
Page with zero-length space title
- chrome.exe (PID: 8396)
INFO
Drops script file
- chrome.exe (PID: 8396)
Application launched itself
- chrome.exe (PID: 8396)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
176
Monitored processes
29
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=8 --field-trial-handle=3392,i,7922114716386139292,11586480391462462404,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=3316 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=1984,i,7922114716386139292,11586480391462462404,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=1980 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1036 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --field-trial-handle=3248,i,7922114716386139292,11586480391462462404,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=3452 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=6 --field-trial-handle=3236,i,7922114716386139292,11586480391462462404,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=3328 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=3536,i,7922114716386139292,11586480391462462404,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=4900 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5908,i,7922114716386139292,11586480391462462404,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5480 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5476,i,7922114716386139292,11586480391462462404,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5904 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5688,i,7922114716386139292,11586480391462462404,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5648 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=6068,i,7922114716386139292,11586480391462462404,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=6080 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
223
Read events
223
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
18
Text files
11
Unknown types
101
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8396 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF1e53da.TMP | — | |
MD5:— | SHA256:— | |||
| 8396 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8396 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1e53ea.TMP | — | |
MD5:— | SHA256:— | |||
| 8396 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF1e53ea.TMP | — | |
MD5:— | SHA256:— | |||
| 8396 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8396 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8396 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF1e53fa.TMP | — | |
MD5:— | SHA256:— | |||
| 8396 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8396 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF1e53ea.TMP | — | |
MD5:— | SHA256:— | |||
| 8396 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
81
TCP/UDP connections
44
DNS requests
48
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7088 | chrome.exe | GET | 302 | 104.21.9.14:443 | https://go.keepo.bio/redirect?event_type=open_link&continue=eyJsaW5rIjoiaHR0cHM6XC9cL2J1aWxkZXIuY2hlbGVwaS5jb250cmFjdG9yc1wvcjVZVWlka0ghNHVTUG10bU5WRndrTXRcLyIsInRpdGxlIjoiVGFrZSIsImlkIjoiNjMwNDk3YjktODEwNC00ZWU1LTg2NDQtNjNjNjQ2YTQxYzk1Iiwic2l0ZUlkIjoiYzc0MzE0MWYtMzg3ZS00NjE2LWExMzgtZGY1MWRhOWJkODc1IiwidXNlcklkIjoiOWJhNjRlMzAtM2Y1MC00Nzc5LWI4MTItN2ExM2VmNTc0YjkyIiwidXJsIjoiaHR0cHM6XC9cL3Rha2Vvbi5rZWVwby5iaW8iLCJzZWN0aW9uSWQiOiJmZmJmMWJmYS0yNGJlLTQ5YjItOWIwOS0zOTVkNzczYjM1ODEiLCJzZWN0aW9uVHlwZSI6ImxpbmtzIn0%3D | US | — | — | unknown |
7088 | chrome.exe | GET | 200 | 142.250.201.174:80 | http://clients2.google.com/time/1/current?cup2key=8:GisK1C3hqPs-yLN-2Fz_bxyOBMMzmREF0TZk7BPvkM8&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | binary | 105 b | whitelisted |
7088 | chrome.exe | GET | 200 | 142.251.140.170:443 | https://safebrowsingohttpgateway.googleapis.com/v1/ohttp/hpkekeyconfig?key=AIzaSyA2KlwBX3mkFo30om9LUFYQhpqLoa_BNhE | US | — | 41 b | whitelisted |
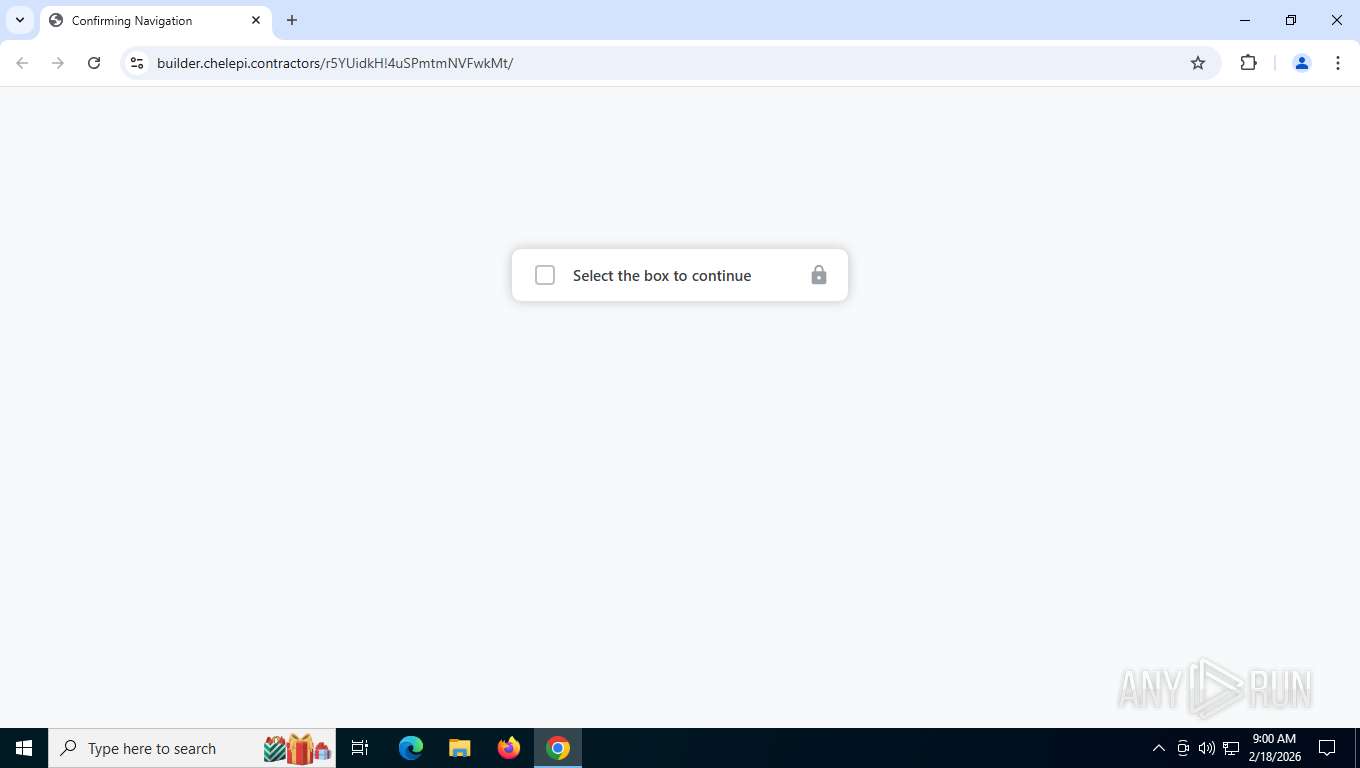
7088 | chrome.exe | GET | 200 | 172.67.153.185:443 | https://builder.chelepi.contractors/r5YUidkH!4uSPmtmNVFwkMt/ | US | — | 3.25 Kb | unknown |
7088 | chrome.exe | POST | 200 | 142.251.127.84:443 | https://accounts.google.com/ListAccounts?gpsia=1&source=ChromiumBrowser&json=standard | US | text | 17 b | whitelisted |
7088 | chrome.exe | GET | 200 | 142.251.208.163:443 | https://clientservices.googleapis.com/chrome-variations/seed?osname=win&channel=stable&milestone=133 | US | binary | 86.7 Kb | whitelisted |
7088 | chrome.exe | GET | 200 | 172.67.153.185:443 | https://builder.chelepi.contractors/favicon.ico | US | binary | 38.5 Kb | unknown |
7088 | chrome.exe | POST | 200 | 142.251.30.94:443 | https://update.googleapis.com/service/update2/json?cup2key=14:gElliPNcblH-xOVxOjZc1Tphqh24OQBYg-D--Xd9v3U&cup2hreq=dd384b28440085cb05f94f4ccee93213303752d6e67042953d06a28e45c24cdd | US | binary | 289 b | whitelisted |
7088 | chrome.exe | POST | 200 | 172.67.153.185:443 | https://builder.chelepi.contractors/r5YUidkH!4uSPmtmNVFwkMt/ | US | binary | 90 b | unknown |
7088 | chrome.exe | GET | 200 | 172.67.153.185:443 | https://builder.chelepi.contractors/r5YUidkH!4uSPmtmNVFwkMt/ | US | binary | 6.03 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
8068 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
2976 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7088 | chrome.exe | 142.250.201.174:80 | clients2.google.com | GOOGLE | US | whitelisted |
7088 | chrome.exe | 142.251.140.170:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
7088 | chrome.exe | 104.21.9.14:443 | go.keepo.bio | CLOUDFLARENET | US | whitelisted |
7088 | chrome.exe | 142.251.208.163:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
go.keepo.bio |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
builder.chelepi.contractors |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7088 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Tycoon2FA related URL pattern observed 2026-02-02 |
7088 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7088 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7088 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Tycoon related URL chain observed |
7088 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7088 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7088 | chrome.exe | Misc activity | INFO [ANY.RUN] External IP Lookup Service DNS query (ipbase .com) |
7088 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7088 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6768 | MoUsoCoreWorker.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |