| File name: | Asteroid raid bot.zip |
| Full analysis: | https://app.any.run/tasks/8d398490-6a2b-45e4-bc84-66d7f0aec2bf |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | March 22, 2019, 01:06:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
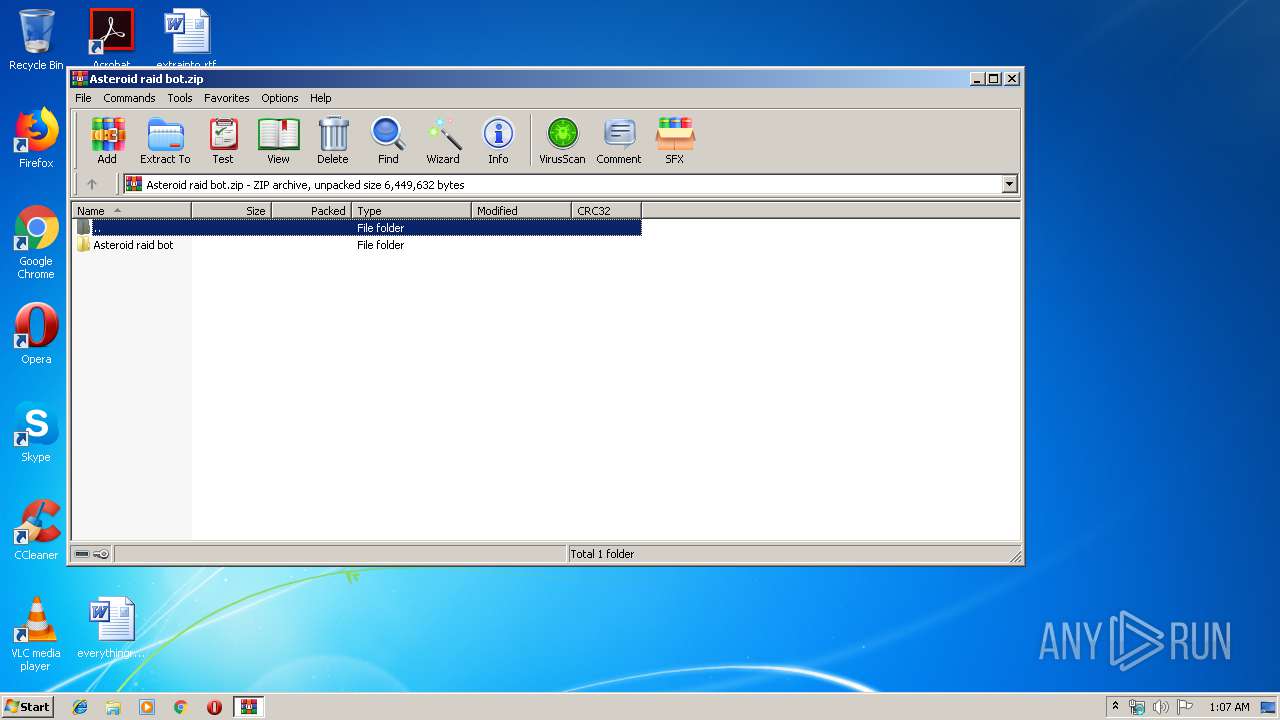
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | B8AD9B25E1B4BBDDC38061AE7A79983D |
| SHA1: | BF8CEE9AA93625B53A1D92FDAC28F6E9E7BE73D4 |
| SHA256: | AF1E049DC5B1138A746ABDBA412FC903CDB954C627A6C9372AD3A55FC21A1ED1 |
| SSDEEP: | 98304:uJt5PZXIHZAtHzrUxkasSxCIpEeGsZyu7SsDe+rt5xd2GTBxbRwo6SPd:i5tIHZApzrUxUSxC1N5+lDe+h5XT3F62 |
MALICIOUS
Actions looks like stealing of personal data
- Discord Raid Bot.exe (PID: 680)
Stealing of credential data
- Discord Raid Bot.exe (PID: 680)
Connects to CnC server
- Discord Raid Bot.exe (PID: 680)
QUASAR was detected
- Discord Raid Bot.exe (PID: 680)
SUSPICIOUS
Reads Environment values
- Discord Raid Bot.exe (PID: 680)
Reads the cookies of Google Chrome
- Discord Raid Bot.exe (PID: 680)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:11:22 12:13:03 |
| ZipCRC: | 0x0d25fbe6 |
| ZipCompressedSize: | 5222985 |
| ZipUncompressedSize: | 5343200 |
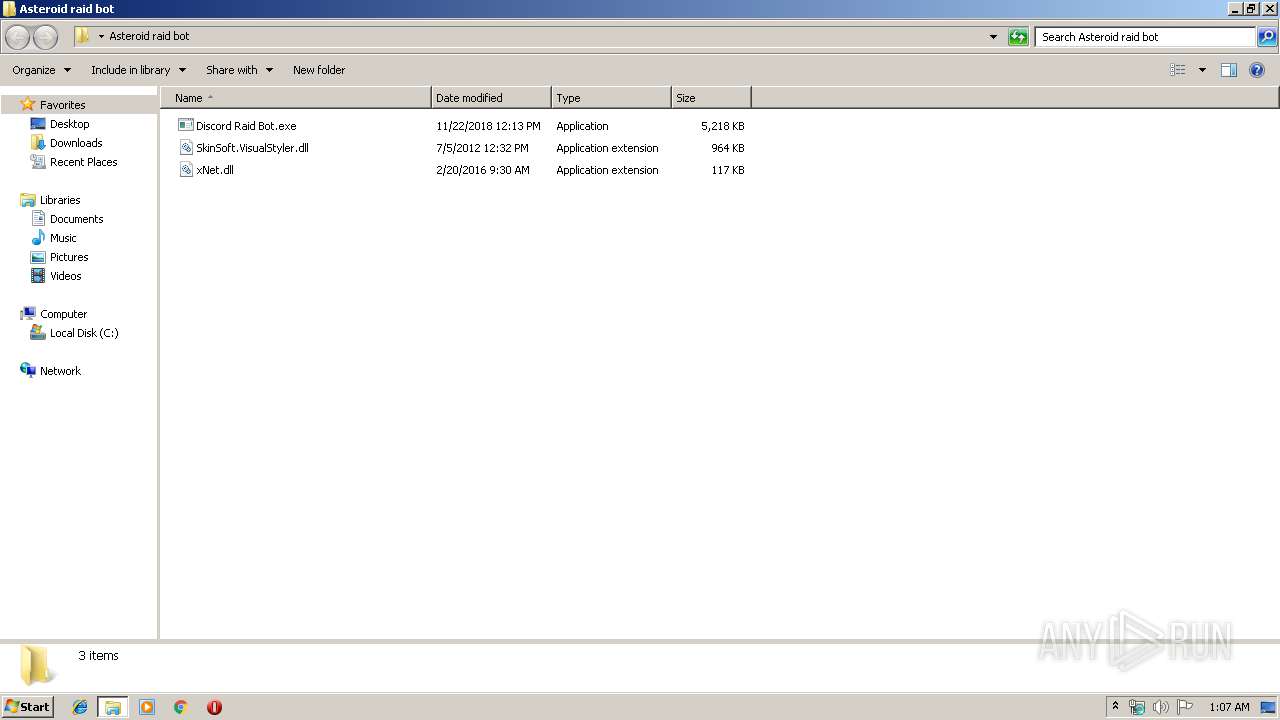
| ZipFileName: | Asteroid raid bot/Discord Raid Bot.exe |
Total processes
32
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 680 | "C:\Users\admin\Desktop\Asteroid raid bot\Discord Raid Bot.exe" | C:\Users\admin\Desktop\Asteroid raid bot\Discord Raid Bot.exe | explorer.exe | ||||||||||||
User: admin Company: xBYYN6oQut3hK Integrity Level: MEDIUM Description: zf8Xfu3Snv Exit code: 0 Version: 3.1.8.0 Modules
| |||||||||||||||
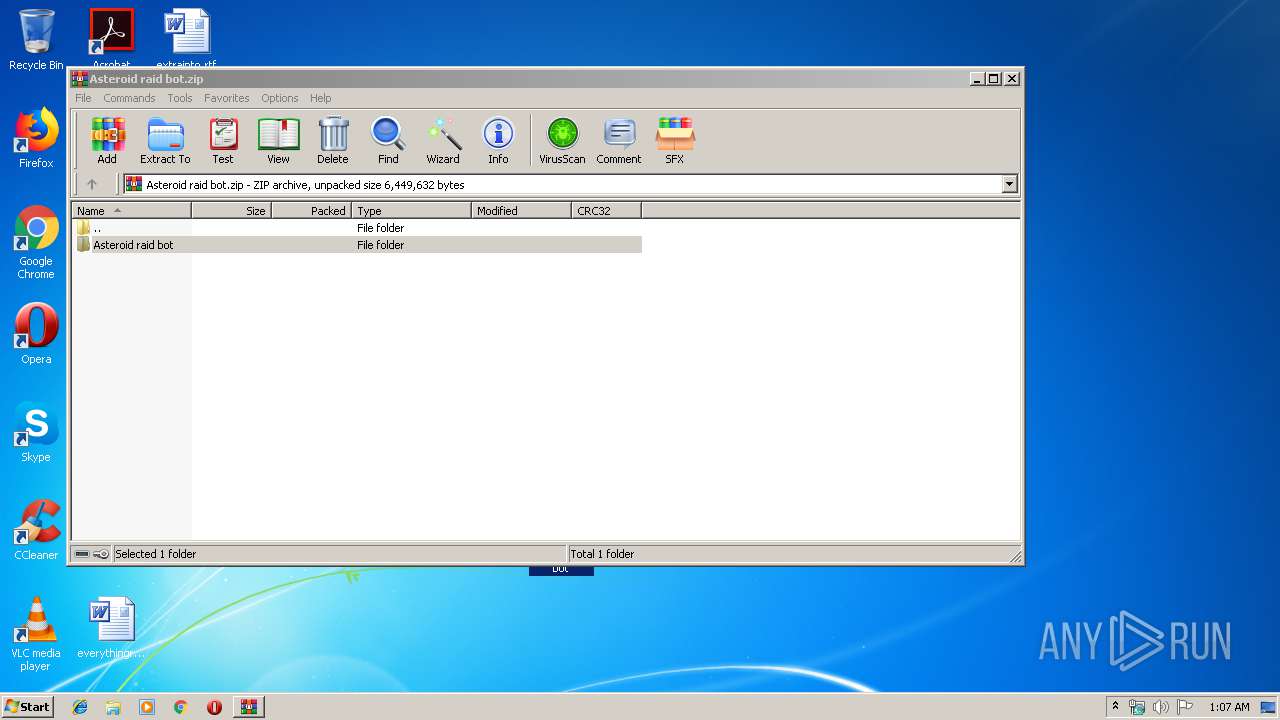
| 1308 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Asteroid raid bot.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
489
Read events
448
Write events
41
Delete events
0
Modification events
| (PID) Process: | (1308) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1308) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1308) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1308) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Asteroid raid bot.zip | |||
| (PID) Process: | (1308) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1308) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1308) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1308) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1308) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (1308) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1308 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1308.34064\Asteroid raid bot\Discord Raid Bot.exe | — | |
MD5:— | SHA256:— | |||
| 1308 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1308.34064\Asteroid raid bot\SkinSoft.VisualStyler.dll | — | |
MD5:— | SHA256:— | |||
| 1308 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1308.34064\Asteroid raid bot\xNet.dll | — | |
MD5:— | SHA256:— | |||
| 680 | Discord Raid Bot.exe | C:\Users\admin\AppData\Local\Temp\a222f117-e923-4ea5-909f-003d5dc76c3c_chrome.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
2
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
680 | Discord Raid Bot.exe | GET | 301 | 104.31.77.103:80 | http://browserloot.rokey.xyz/api/get-ip.php | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
680 | Discord Raid Bot.exe | 104.31.77.103:80 | browserloot.rokey.xyz | Cloudflare Inc | US | shared |
680 | Discord Raid Bot.exe | 104.31.77.103:443 | browserloot.rokey.xyz | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
browserloot.rokey.xyz |
| malicious |
rokey.xyz |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
680 | Discord Raid Bot.exe | A Network Trojan was detected | MALWARE [PTsecurity] BrowserLoot Stealer |
680 | Discord Raid Bot.exe | A Network Trojan was detected | MALWARE [PTsecurity] BrowserLoot Stealer Connection |
2 ETPRO signatures available at the full report