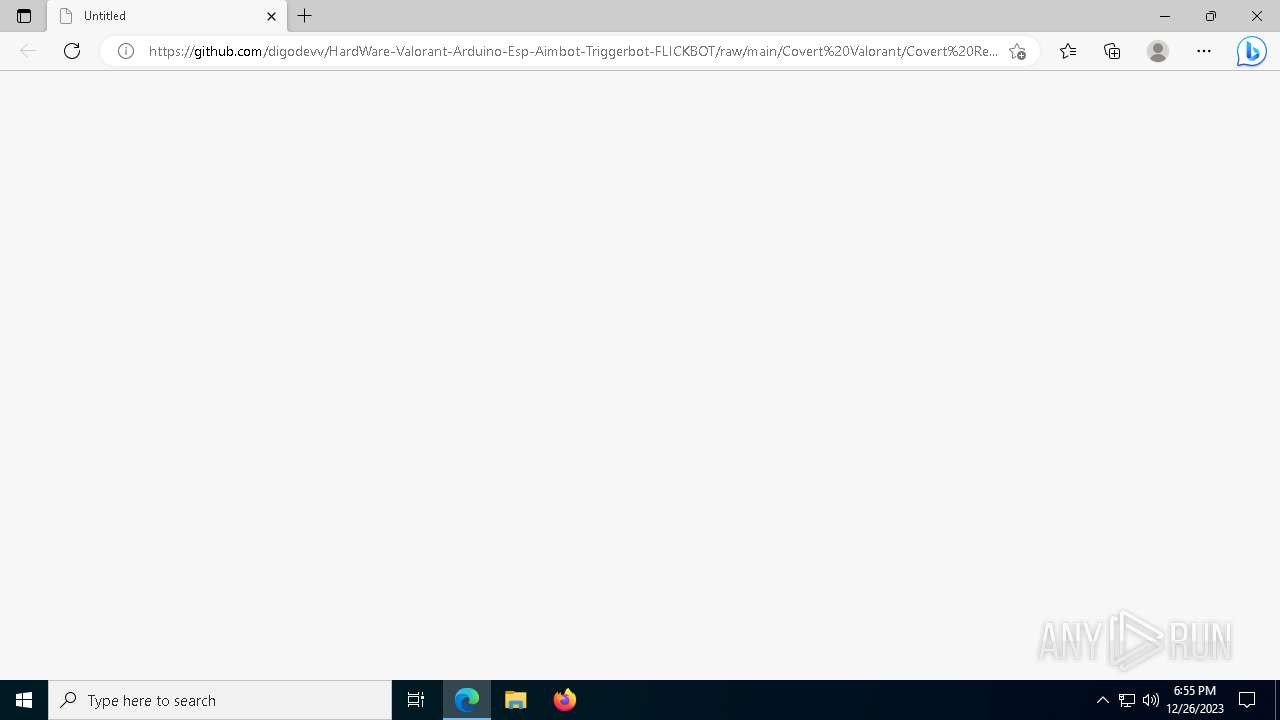
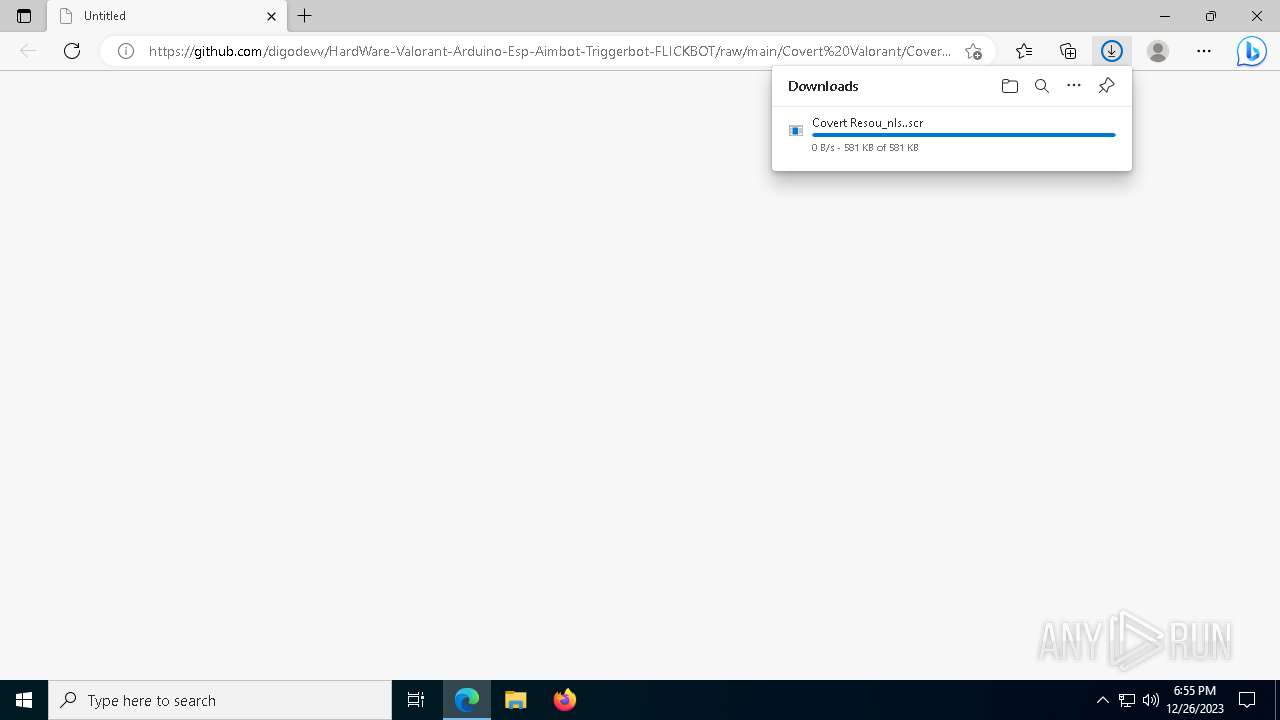
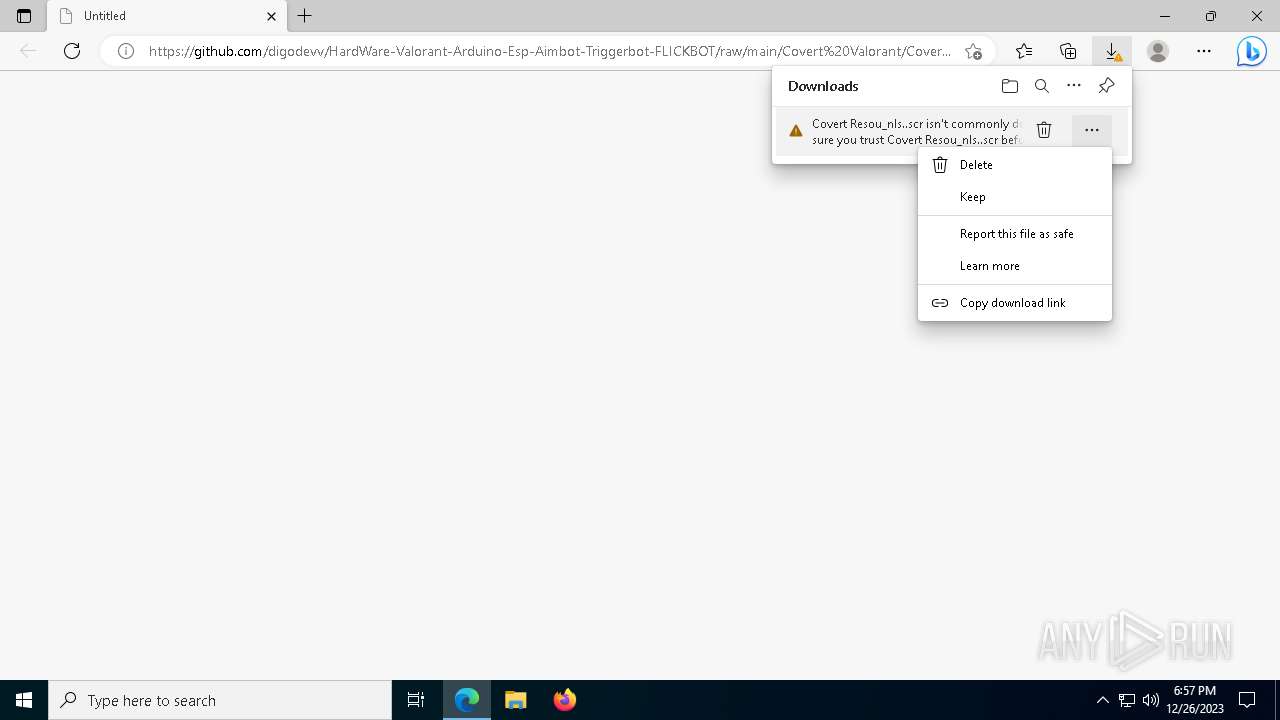
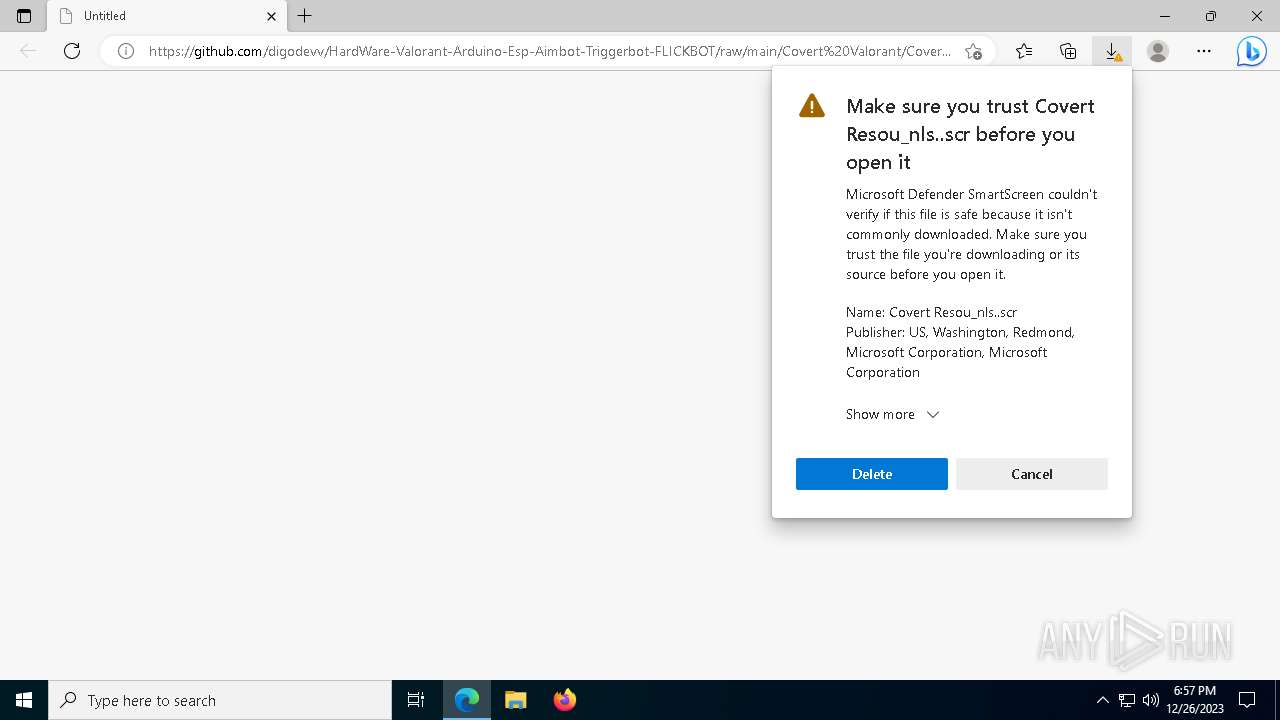
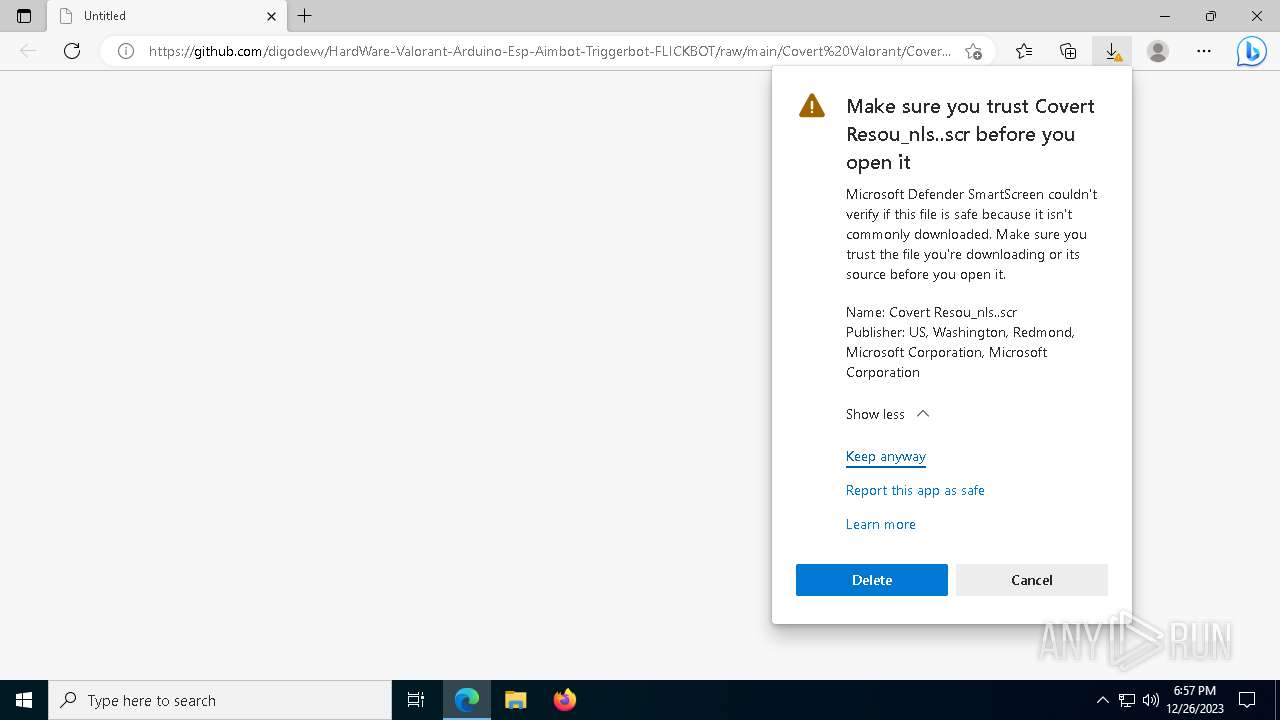
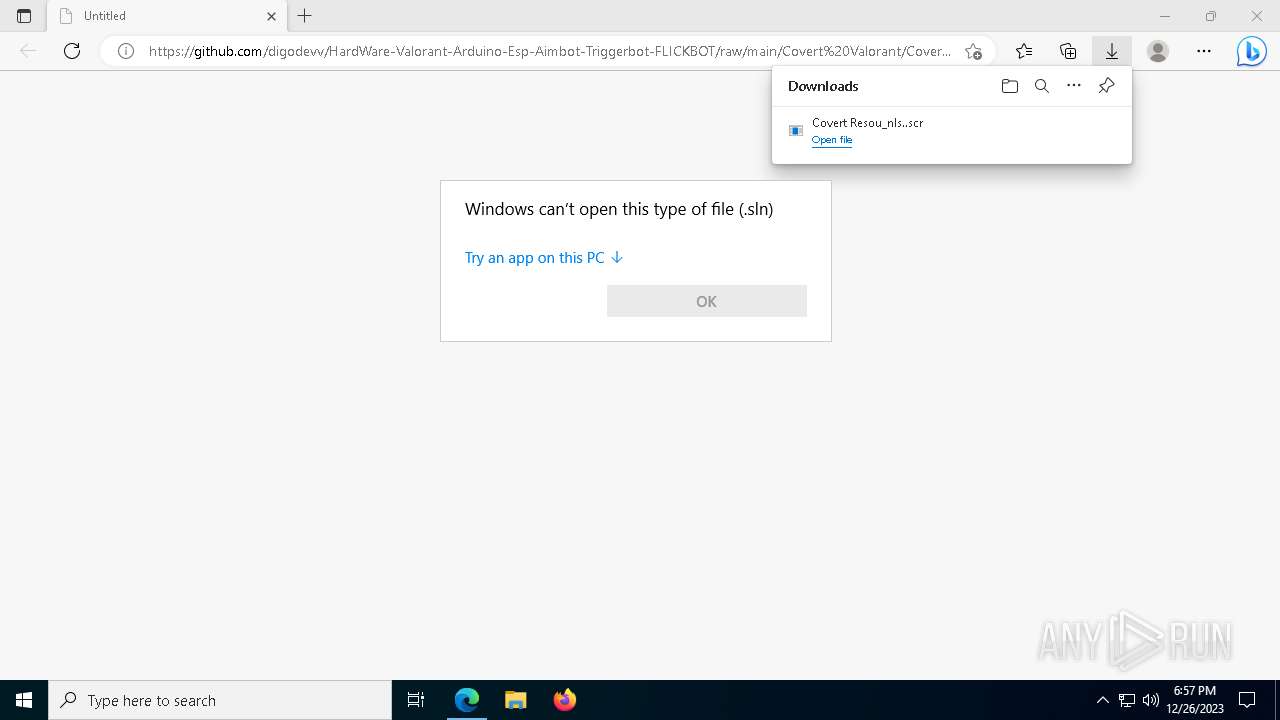
| URL: | https://github.com/digodevv/HardWare-Valorant-Arduino-Esp-Aimbot-Triggerbot-FLICKBOT/raw/main/Covert%20Valorant/Covert%20Resou%E2%80%AEnls..scr |
| Full analysis: | https://app.any.run/tasks/b3da1f7a-8f2e-4bfb-ad19-39d00a59a248 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | December 26, 2023, 18:55:25 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E0DF39C3DF2FA2C0246A0C68DDCBD087 |
| SHA1: | 2620819AF59572FA4D6C7BAF57EC3ECCC64AD2B1 |
| SHA256: | AEFFAB3640313FBF1C1433575BD4232C25C539DE0F4D8D8093FCC7A64220FC48 |
| SSDEEP: | 3:N8tEdxMCLitERyECpvlsIHTxXDmdn6ABNpoTABFW0zQkD:2uMLtNDlqsU6CNSWFW0zQa |
MALICIOUS
Uses Task Scheduler to run other applications
- cmd.exe (PID: 432)
- cmd.exe (PID: 6352)
- cmd.exe (PID: 7688)
Create files in the Startup directory
- ed3GJ2t86H.exe (PID: 6856)
ASYNCRAT has been detected (SURICATA)
- RegAsm.exe (PID: 7660)
- 3HBDD.exe (PID: 7192)
- RegAsm.exe (PID: 7564)
- 5HBDD.exe (PID: 7496)
KLIPPR has been detected (YARA)
- ed3GJ2t86H.exe (PID: 6856)
SUSPICIOUS
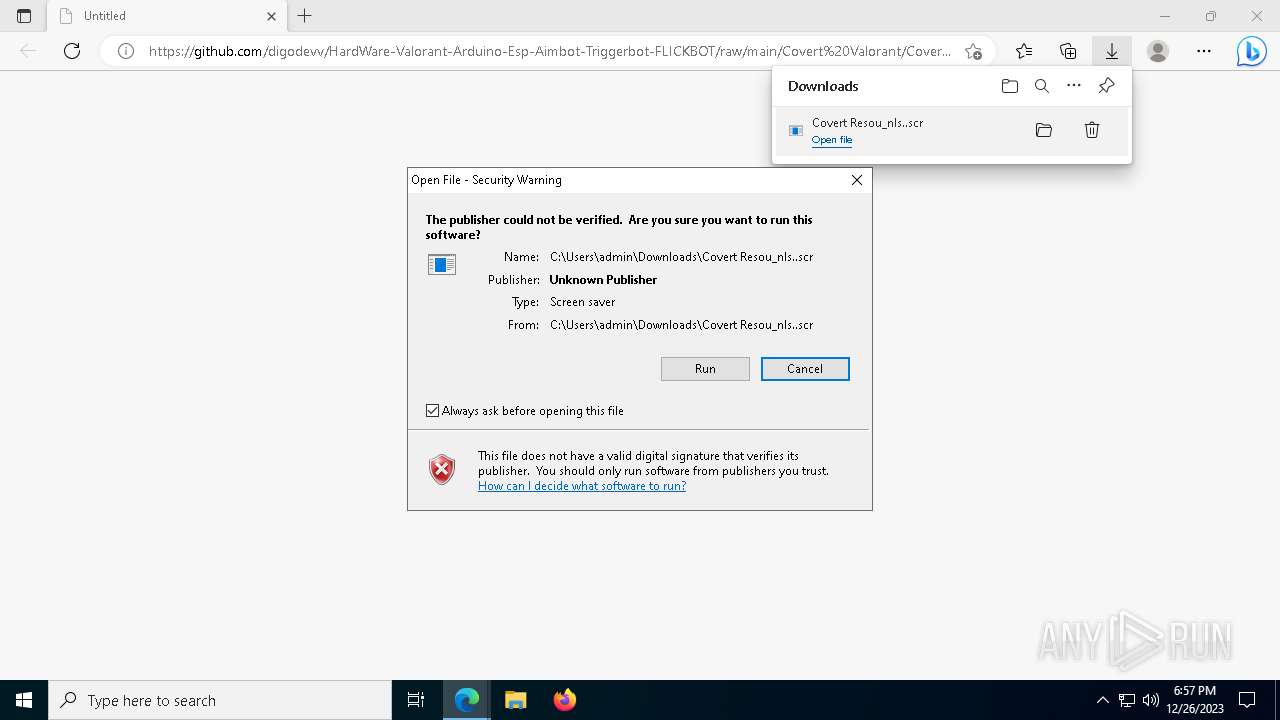
Starts application with an unusual extension
- msedge.exe (PID: 4796)
Starts CMD.EXE for commands execution
- Covert Resou_nls..scr (PID: 7320)
- ed3GJ2t86H.exe (PID: 7916)
- HBGE3.exe (PID: 7544)
- 4HBDD.exe (PID: 6136)
Base64-obfuscated command line is found
- M9OIUwWc5G.exe (PID: 7636)
- OYW9hw6UxW.exe (PID: 7656)
- JovcAT6O4h.exe (PID: 5964)
- 4XxUNlr0vD.exe (PID: 4052)
- VhP99aHpa2.exe (PID: 1248)
- hlFHm9sHhr.exe (PID: 7948)
Starts POWERSHELL.EXE for commands execution
- M9OIUwWc5G.exe (PID: 7636)
- OYW9hw6UxW.exe (PID: 7656)
- JovcAT6O4h.exe (PID: 5964)
- VhP99aHpa2.exe (PID: 1248)
- 4XxUNlr0vD.exe (PID: 4052)
- ed3GJ2t86H.exe (PID: 7916)
- hlFHm9sHhr.exe (PID: 7948)
- HBGE3.exe (PID: 7544)
- 4HBDD.exe (PID: 6136)
BASE64 encoded PowerShell command has been detected
- M9OIUwWc5G.exe (PID: 7636)
- OYW9hw6UxW.exe (PID: 7656)
- JovcAT6O4h.exe (PID: 5964)
- 4XxUNlr0vD.exe (PID: 4052)
- VhP99aHpa2.exe (PID: 1248)
- hlFHm9sHhr.exe (PID: 7948)
The process creates files with name similar to system file names
- powershell.exe (PID: 5164)
Unusual connection from system programs
- powershell.exe (PID: 6696)
- powershell.exe (PID: 6332)
- powershell.exe (PID: 4160)
- powershell.exe (PID: 6540)
- powershell.exe (PID: 8132)
The Powershell connects to the Internet
- powershell.exe (PID: 6696)
- powershell.exe (PID: 4160)
- powershell.exe (PID: 6332)
- powershell.exe (PID: 6540)
- powershell.exe (PID: 8132)
Connects to unusual port
- RegAsm.exe (PID: 7660)
- 3HBDD.exe (PID: 7192)
- RegAsm.exe (PID: 7564)
- 5HBDD.exe (PID: 7496)
INFO
Application launched itself
- msedge.exe (PID: 4796)
- ed3GJ2t86H.exe (PID: 7916)
- 3HBDD.exe (PID: 8092)
Reads the computer name
- identity_helper.exe (PID: 6788)
- Covert Resou_nls..scr (PID: 7320)
- M9OIUwWc5G.exe (PID: 7636)
- OYW9hw6UxW.exe (PID: 7656)
- JovcAT6O4h.exe (PID: 5964)
- 4XxUNlr0vD.exe (PID: 4052)
- VhP99aHpa2.exe (PID: 1248)
- ed3GJ2t86H.exe (PID: 7916)
- hlFHm9sHhr.exe (PID: 7948)
- ed3GJ2t86H.exe (PID: 6856)
- HBGE3.exe (PID: 7544)
- RegAsm.exe (PID: 7660)
- 2HBGE3.exe (PID: 6348)
- 3HBDD.exe (PID: 7192)
- 4HBDD.exe (PID: 6136)
- 3HBDD.exe (PID: 8092)
- RegAsm.exe (PID: 7564)
- 5HBDD.exe (PID: 7496)
- InstallUtil.exe (PID: 6452)
Checks supported languages
- identity_helper.exe (PID: 6788)
- Covert Resou_nls..scr (PID: 7320)
- M9OIUwWc5G.exe (PID: 7636)
- OYW9hw6UxW.exe (PID: 7656)
- JovcAT6O4h.exe (PID: 5964)
- VhP99aHpa2.exe (PID: 1248)
- 4XxUNlr0vD.exe (PID: 4052)
- ed3GJ2t86H.exe (PID: 7916)
- hlFHm9sHhr.exe (PID: 7948)
- ed3GJ2t86H.exe (PID: 6856)
- RegAsm.exe (PID: 7660)
- 3HBDD.exe (PID: 8092)
- 2HBGE3.exe (PID: 6348)
- 3HBDD.exe (PID: 7192)
- 4HBDD.exe (PID: 6136)
- RegAsm.exe (PID: 7564)
- 5HBDD.exe (PID: 7496)
- InstallUtil.exe (PID: 6452)
- HBGE3.exe (PID: 7544)
Reads the software policy settings
- slui.exe (PID: 7208)
- Covert Resou_nls..scr (PID: 7320)
- RegAsm.exe (PID: 7660)
- slui.exe (PID: 8080)
- 3HBDD.exe (PID: 7192)
- RegAsm.exe (PID: 7564)
- 5HBDD.exe (PID: 7496)
The process uses the downloaded file
- msedge.exe (PID: 6164)
- msedge.exe (PID: 4796)
Drops the executable file immediately after the start
- msedge.exe (PID: 1824)
- msedge.exe (PID: 4796)
- Covert Resou_nls..scr (PID: 7320)
- ed3GJ2t86H.exe (PID: 7916)
- powershell.exe (PID: 6696)
- ed3GJ2t86H.exe (PID: 6856)
- HBGE3.exe (PID: 7544)
- powershell.exe (PID: 6332)
- powershell.exe (PID: 4160)
- 3HBDD.exe (PID: 8092)
- powershell.exe (PID: 6540)
- powershell.exe (PID: 8132)
- 4HBDD.exe (PID: 6136)
- 5HBDD.exe (PID: 7496)
Checks proxy server information
- Covert Resou_nls..scr (PID: 7320)
- powershell.exe (PID: 6696)
- powershell.exe (PID: 6332)
- slui.exe (PID: 8080)
- powershell.exe (PID: 4160)
- powershell.exe (PID: 6540)
- powershell.exe (PID: 8132)
Create files in a temporary directory
- Covert Resou_nls..scr (PID: 7320)
The executable file from the user directory is run by the CMD process
- M9OIUwWc5G.exe (PID: 7636)
- OYW9hw6UxW.exe (PID: 7656)
- JovcAT6O4h.exe (PID: 5964)
- 4XxUNlr0vD.exe (PID: 4052)
- ed3GJ2t86H.exe (PID: 7916)
- hlFHm9sHhr.exe (PID: 7948)
- VhP99aHpa2.exe (PID: 1248)
Process checks computer location settings
- M9OIUwWc5G.exe (PID: 7636)
- OYW9hw6UxW.exe (PID: 7656)
- JovcAT6O4h.exe (PID: 5964)
- VhP99aHpa2.exe (PID: 1248)
- 4XxUNlr0vD.exe (PID: 4052)
- hlFHm9sHhr.exe (PID: 7948)
Creates files or folders in the user directory
- M9OIUwWc5G.exe (PID: 7636)
- OYW9hw6UxW.exe (PID: 7656)
- JovcAT6O4h.exe (PID: 5964)
- 4XxUNlr0vD.exe (PID: 4052)
- VhP99aHpa2.exe (PID: 1248)
- ed3GJ2t86H.exe (PID: 7916)
- hlFHm9sHhr.exe (PID: 7948)
- ed3GJ2t86H.exe (PID: 6856)
- HBGE3.exe (PID: 7544)
- 3HBDD.exe (PID: 8092)
- 4HBDD.exe (PID: 6136)
- 2HBGE3.exe (PID: 6348)
- 5HBDD.exe (PID: 7496)
- InstallUtil.exe (PID: 6452)
Reads the machine GUID from the registry
- ed3GJ2t86H.exe (PID: 7916)
- ed3GJ2t86H.exe (PID: 6856)
- HBGE3.exe (PID: 7544)
- RegAsm.exe (PID: 7660)
- 2HBGE3.exe (PID: 6348)
- 3HBDD.exe (PID: 7192)
- 3HBDD.exe (PID: 8092)
- 4HBDD.exe (PID: 6136)
- RegAsm.exe (PID: 7564)
- InstallUtil.exe (PID: 6452)
- 5HBDD.exe (PID: 7496)
The executable file from the user directory is run by the Powershell process
- HBGE3.exe (PID: 7544)
- 3HBDD.exe (PID: 8092)
- 2HBGE3.exe (PID: 6348)
- 4HBDD.exe (PID: 6136)
- 5HBDD.exe (PID: 7496)
Reads Environment values
- RegAsm.exe (PID: 7660)
- 3HBDD.exe (PID: 7192)
- RegAsm.exe (PID: 7564)
- 5HBDD.exe (PID: 7496)
Process drops legitimate windows executable
- powershell.exe (PID: 6332)
- powershell.exe (PID: 4160)
- 3HBDD.exe (PID: 8092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
220
Monitored processes
94
Malicious processes
18
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 432 | "cmd" /C schtasks /create /tn \WinrarServicer /tr "C:\Users\admin\AppData\Roaming\WinrarServicer\WinrarServicer.exe" /st 00:00 /du 9999:59 /sc once /ri 60 /f | C:\Windows\SysWOW64\cmd.exe | — | ed3GJ2t86H.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.746 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 784 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1100 | "cmd" /C C:\Users\admin\AppData\Local\Temp\PWhvMqtqqD.sln | C:\Windows\System32\cmd.exe | — | Covert Resou_nls..scr | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1248 | C:\Users\admin\AppData\Local\Temp\VhP99aHpa2.exe | C:\Users\admin\AppData\Local\Temp\VhP99aHpa2.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 1376 | "cmd" /C C:\Users\admin\AppData\Local\Temp\ed3GJ2t86H.exe | C:\Windows\System32\cmd.exe | — | Covert Resou_nls..scr | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1476 | "cmd" /C C:\Users\admin\AppData\Local\Temp\JovcAT6O4h.exe | C:\Windows\System32\cmd.exe | — | Covert Resou_nls..scr | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1824 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2124 --field-trial-handle=2096,i,12524251245572715495,8088127406683619176,131072 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 2104 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAABgAAAAAAAAAGAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1672 --field-trial-handle=2096,i,12524251245572715495,8088127406683619176,131072 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 111.0.1661.62 Modules
| |||||||||||||||
| 2544 | "powershell.exe" Remove -ItemProperty -Path 'HKCU:\SOFTWARE\Microsoft\Windows\CurrentVersion\Run' -Name 'Gbn1';New-ItemProperty -Path 'HKCU:\SOFTWARE\Microsoft\Windows\CurrentVersion\Run' -Name 'Gbn1' -Value '"C:\Users\admin\AppData\Roaming\Gbn1\Gbn1.exe"' -PropertyType 'String' | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | 4HBDD.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
71 178
Read events
71 007
Write events
170
Delete events
1
Modification events
| (PID) Process: | (4796) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4796) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4796) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (4796) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4796) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (4796) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4796) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (4796) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4796) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
| (PID) Process: | (4796) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 74A98451B7602F00 | |||
Executable files
29
Suspicious files
234
Text files
133
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4796 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFf3484.TMP | — | |
MD5:— | SHA256:— | |||
| 4796 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4796 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFf34c2.TMP | — | |
MD5:— | SHA256:— | |||
| 4796 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4796 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFf355f.TMP | — | |
MD5:— | SHA256:— | |||
| 4796 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4796 | msedge.exe | C:\USERS\ADMIN\APPDATA\LOCAL\MICROSOFT\EDGE\USER DATA\VARIATIONS | binary | |
MD5:6E1AF7D7074A6124EFDB62180565A385 | SHA256:70811DE44C337675FCFFDA381E8AB2FB66544B07FFCAE651804B75EF71C11748 | |||
| 4796 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\533548a5-2904-4809-bd98-3ccd39a1c88d.tmp | binary | |
MD5:566EA0168798C509B2915BC49B2E36CE | SHA256:65E1D2E8E33C99740E4159B24D4EDC8C8D882657EE1C584189CFC3404109C41E | |||
| 4796 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State | binary | |
MD5:566EA0168798C509B2915BC49B2E36CE | SHA256:65E1D2E8E33C99740E4159B24D4EDC8C8D882657EE1C584189CFC3404109C41E | |||
| 4796 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Last Version | text | |
MD5:D6DB6EA02FE506F2DA98F1C137243587 | SHA256:126173A7D7D0F54A9FCE5465180BC49DB023E723A41BB55A0F9497BE76FBAA28 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
50
TCP/UDP connections
98
DNS requests
65
Threats
28
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1092 | svchost.exe | POST | — | 138.91.171.81:80 | http://dmd.metaservices.microsoft.com/metadata.svc | unknown | — | — | unknown |
1092 | svchost.exe | POST | 302 | 2.18.97.227:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | unknown |
2908 | svchost.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
7816 | svchost.exe | GET | 206 | 2.21.20.151:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/26b10680-9c99-4cf8-93c0-fca56709a250?P1=1703837888&P2=404&P3=2&P4=DGVfFKfv05jpfUspkJJ8UIzyn6S3OmVCeXBt%2bmppluI5pysHMil1kSMcDSlQYmyH%2b7Nea%2fKOwbDwmBeznfMB%2bQ%3d%3d | unknown | binary | 1.09 Kb | unknown |
7816 | svchost.exe | HEAD | 200 | 2.21.20.151:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/26b10680-9c99-4cf8-93c0-fca56709a250?P1=1703837888&P2=404&P3=2&P4=DGVfFKfv05jpfUspkJJ8UIzyn6S3OmVCeXBt%2bmppluI5pysHMil1kSMcDSlQYmyH%2b7Nea%2fKOwbDwmBeznfMB%2bQ%3d%3d | unknown | — | — | unknown |
7816 | svchost.exe | GET | 206 | 2.21.20.151:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/26b10680-9c99-4cf8-93c0-fca56709a250?P1=1703837888&P2=404&P3=2&P4=DGVfFKfv05jpfUspkJJ8UIzyn6S3OmVCeXBt%2bmppluI5pysHMil1kSMcDSlQYmyH%2b7Nea%2fKOwbDwmBeznfMB%2bQ%3d%3d | unknown | binary | 29.1 Kb | unknown |
7816 | svchost.exe | GET | 206 | 2.21.20.151:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/26b10680-9c99-4cf8-93c0-fca56709a250?P1=1703837888&P2=404&P3=2&P4=DGVfFKfv05jpfUspkJJ8UIzyn6S3OmVCeXBt%2bmppluI5pysHMil1kSMcDSlQYmyH%2b7Nea%2fKOwbDwmBeznfMB%2bQ%3d%3d | unknown | binary | 2.23 Kb | unknown |
7816 | svchost.exe | HEAD | 200 | 2.21.20.151:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4643befd-79b8-4e0c-a2fb-c0e3ee78dcd5?P1=1703837889&P2=404&P3=2&P4=dBac8of%2fi4jxHxrTNJaWGoexMboYT9sc4aaUU4LADrdPXRWvxA10BTGyvtIPBSKxowtAVN5thjrENTecuzgH9A%3d%3d | unknown | binary | 403 b | unknown |
7816 | svchost.exe | GET | 206 | 2.21.20.151:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/26b10680-9c99-4cf8-93c0-fca56709a250?P1=1703837888&P2=404&P3=2&P4=DGVfFKfv05jpfUspkJJ8UIzyn6S3OmVCeXBt%2bmppluI5pysHMil1kSMcDSlQYmyH%2b7Nea%2fKOwbDwmBeznfMB%2bQ%3d%3d | unknown | binary | 9.03 Kb | unknown |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3720 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
1824 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | unknown |
— | — | 239.255.255.250:1900 | — | — | — | unknown |
1824 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | unknown |
— | — | 185.199.109.133:443 | raw.githubusercontent.com | FASTLY | US | unknown |
4180 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1824 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
1824 | msedge.exe | 13.107.213.45:443 | edgeassetservice.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| shared |
config.edge.skype.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
raw.githubusercontent.com |
| shared |
edge.microsoft.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
nav-edge.smartscreen.microsoft.com |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7320 | Covert Resou_nls..scr | Potentially Bad Traffic | ET INFO Pastebin-style Service (textbin .net in TLS SNI) |
2136 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
7320 | Covert Resou_nls..scr | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
2136 | svchost.exe | Misc activity | ET INFO Pastebin Service Domain in DNS Lookup (rentry .co) |
7320 | Covert Resou_nls..scr | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |
7320 | Covert Resou_nls..scr | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
7320 | Covert Resou_nls..scr | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
7320 | Covert Resou_nls..scr | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
7320 | Covert Resou_nls..scr | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
7320 | Covert Resou_nls..scr | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
4 ETPRO signatures available at the full report