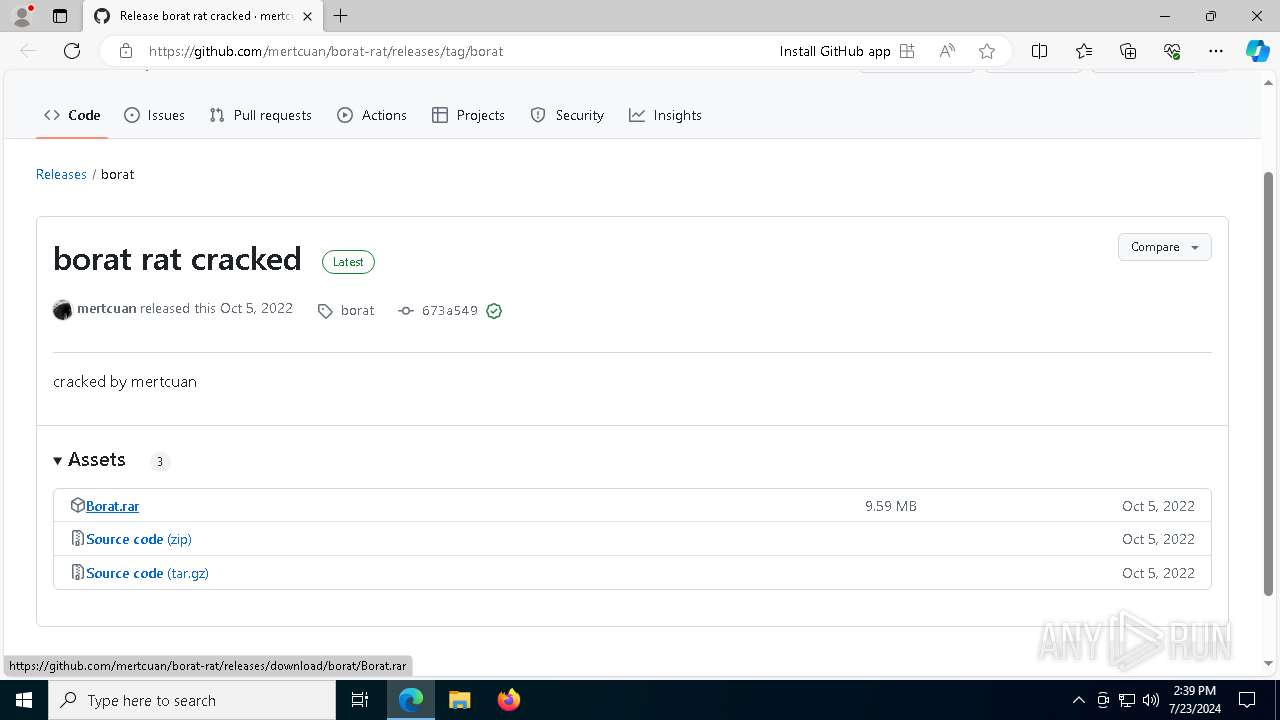
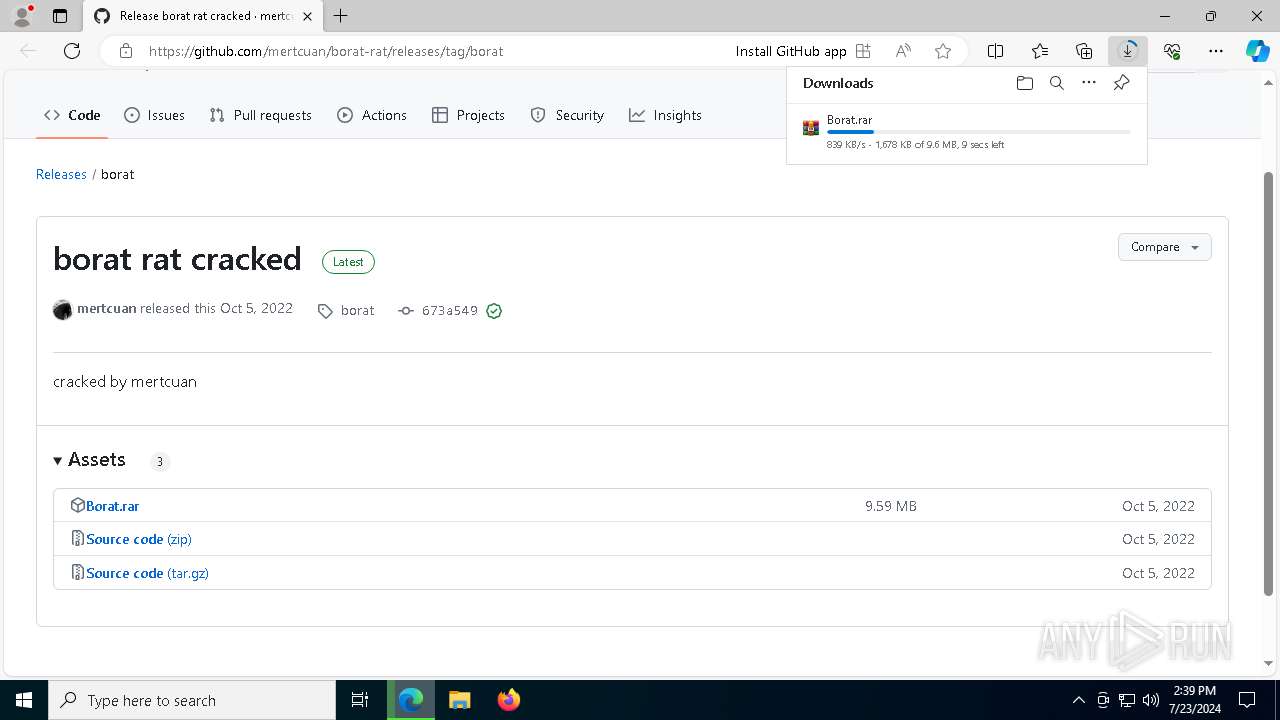
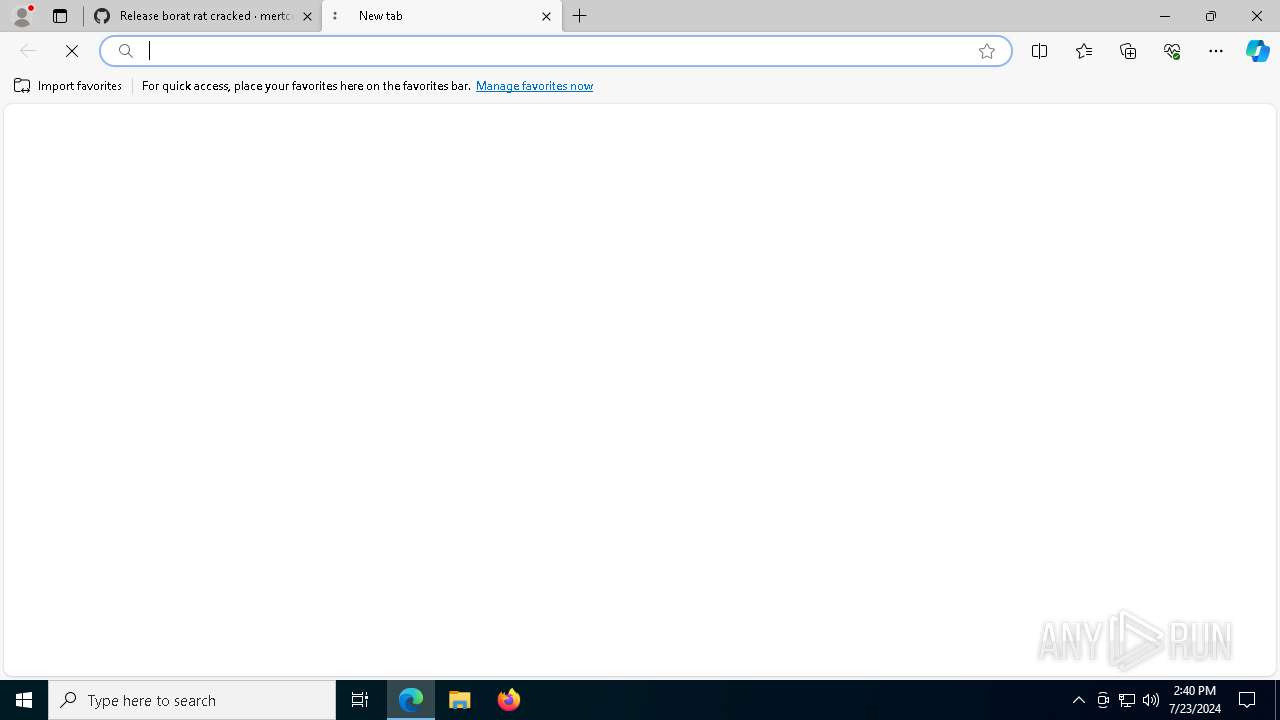
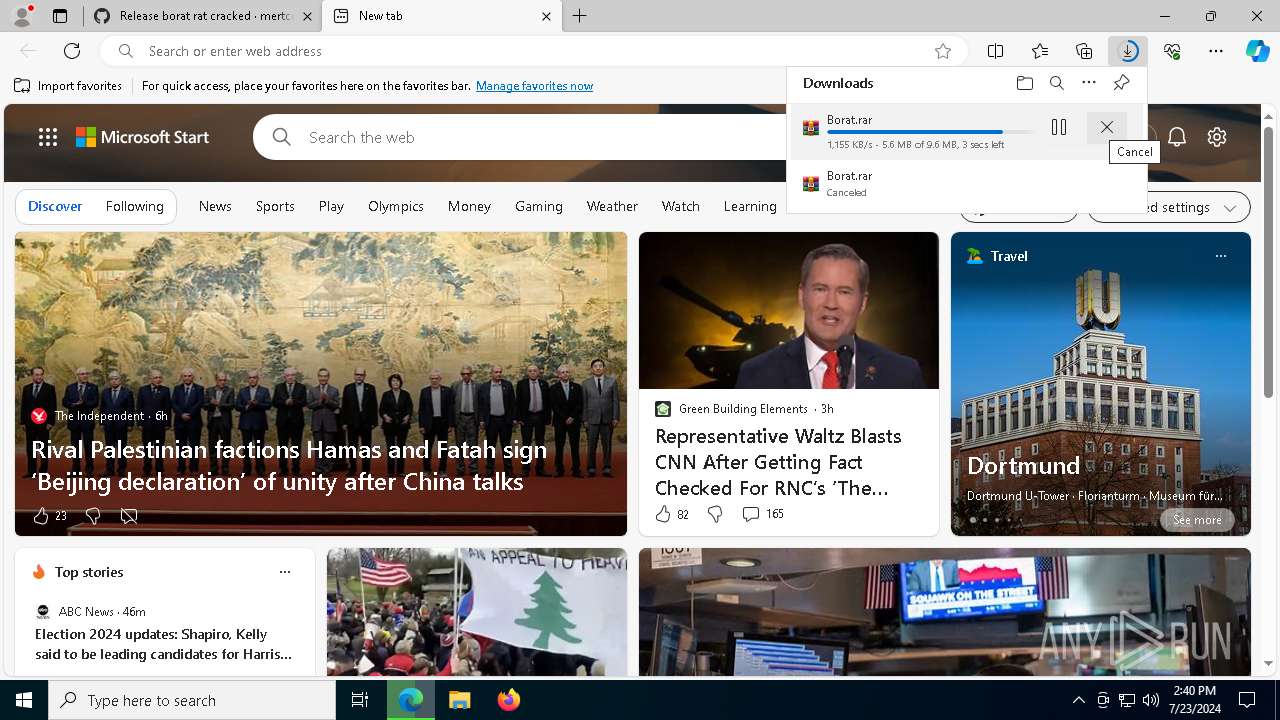
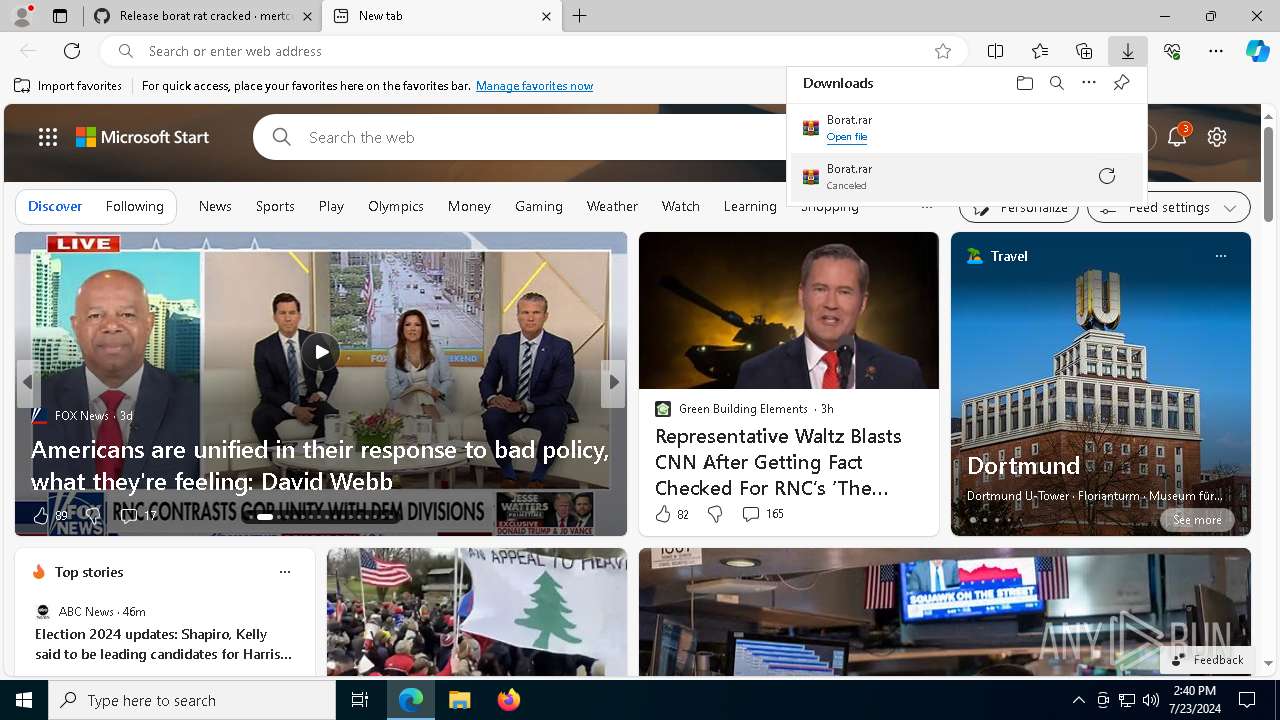
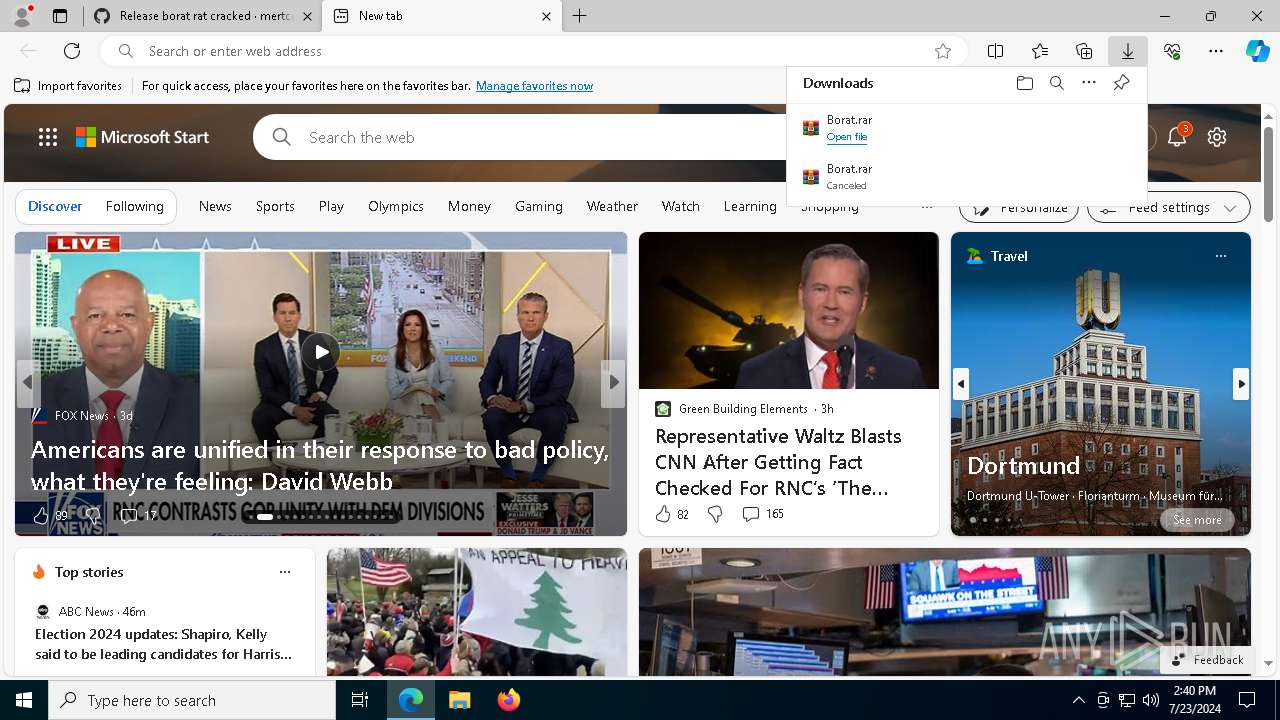
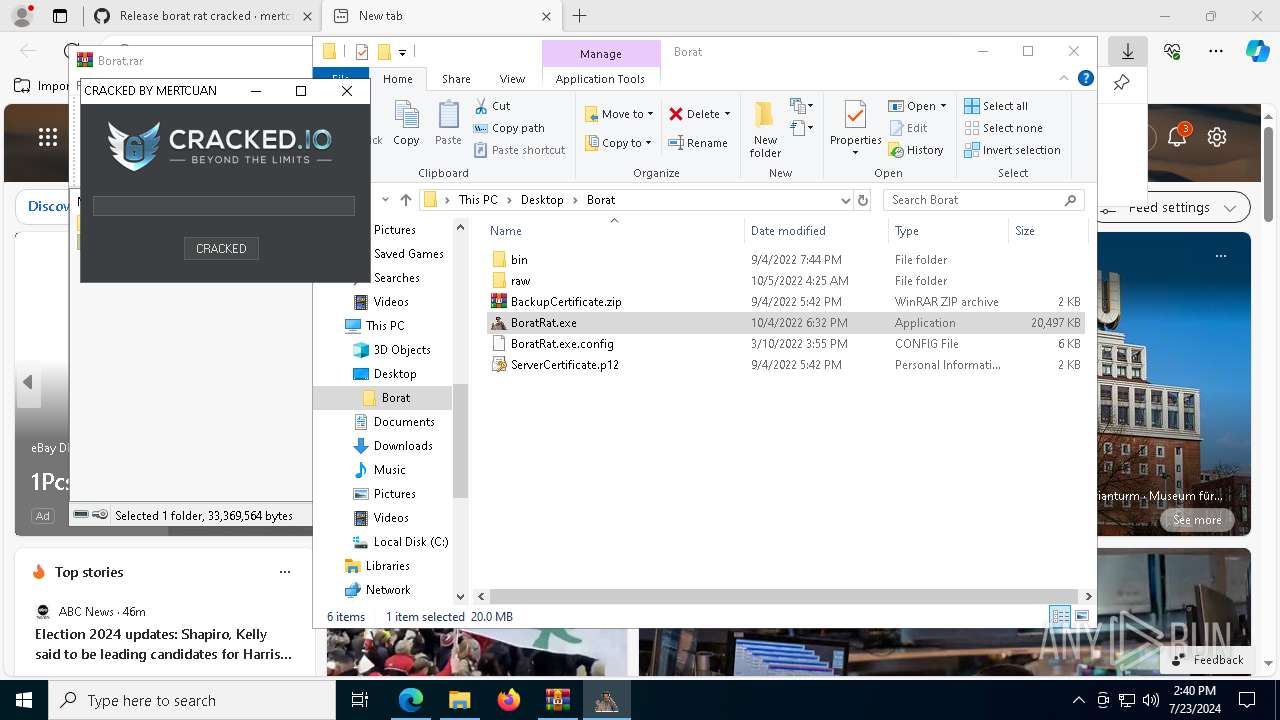
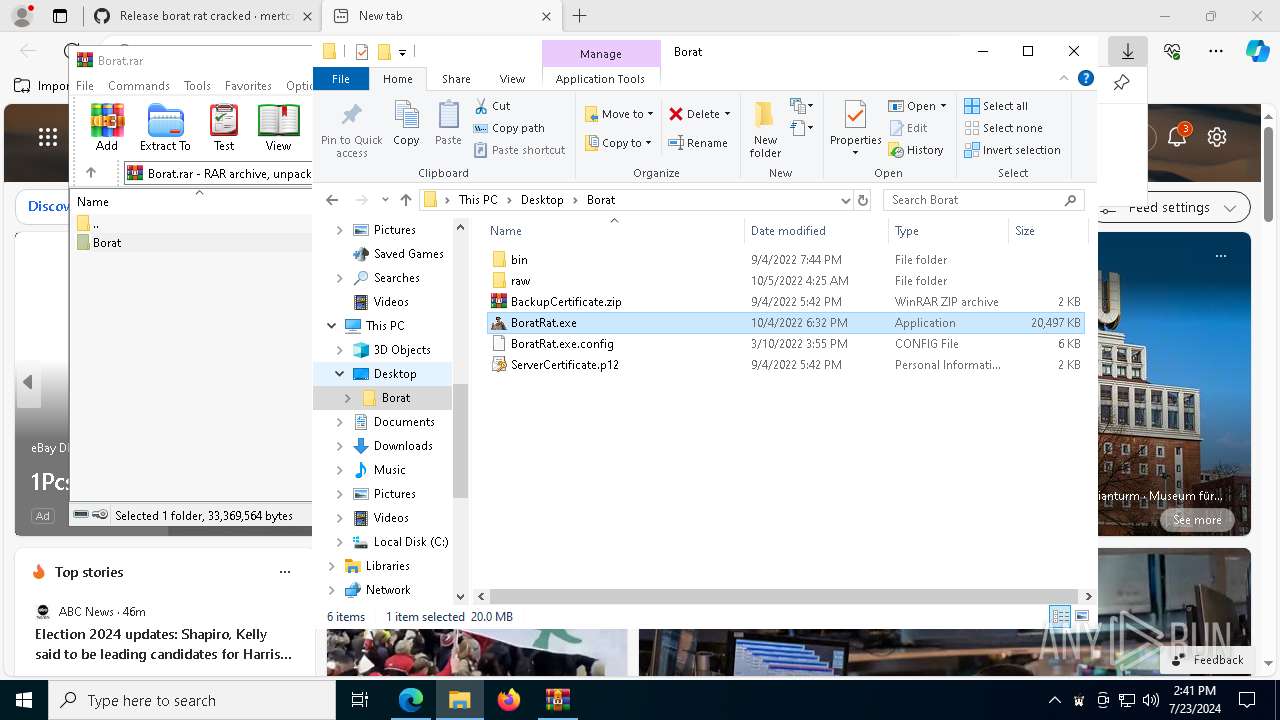
| URL: | https://github.com/mertcuan/borat-rat/releases/tag/borat |
| Full analysis: | https://app.any.run/tasks/037ab8ad-8987-47f9-84b0-137ec91b1cf3 |
| Verdict: | Malicious activity |
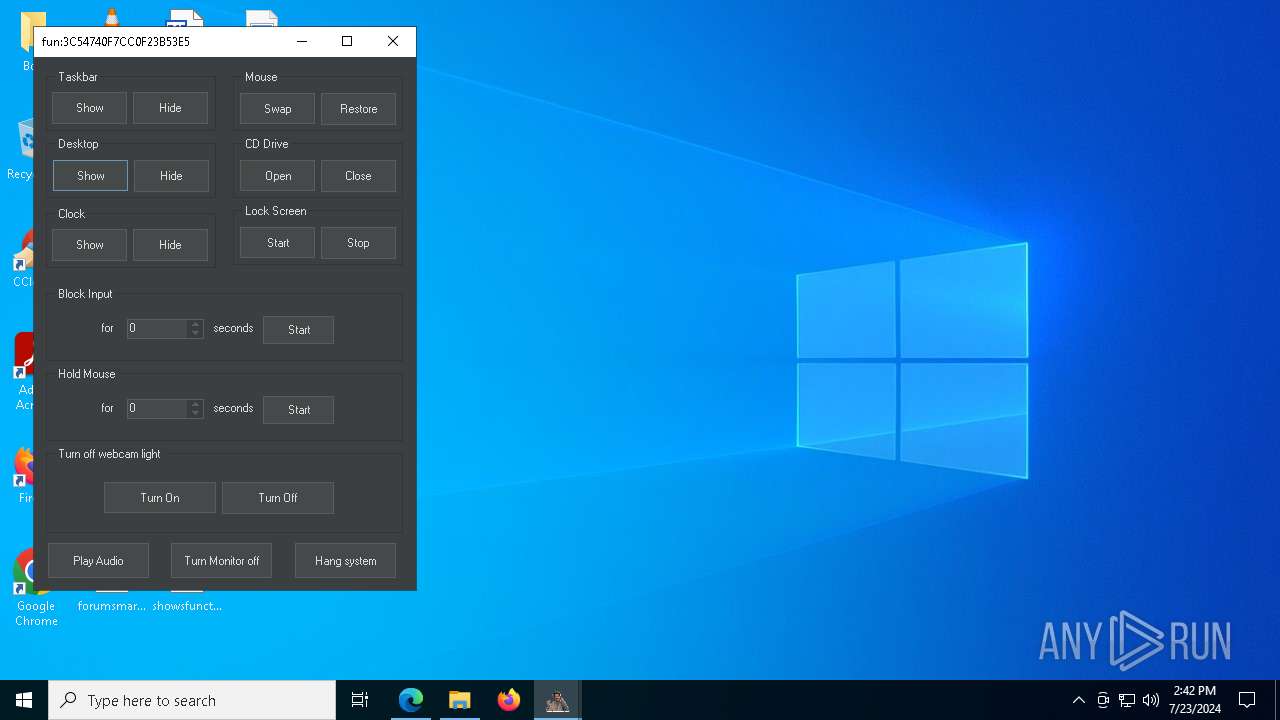
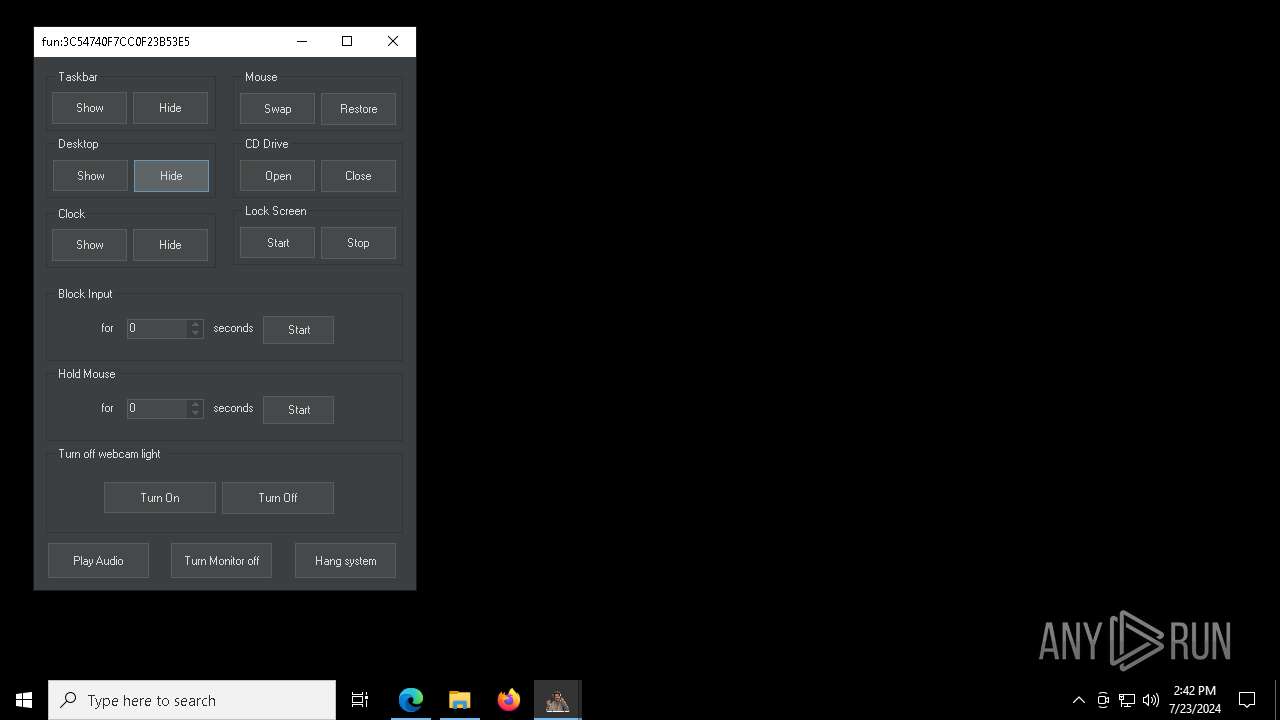
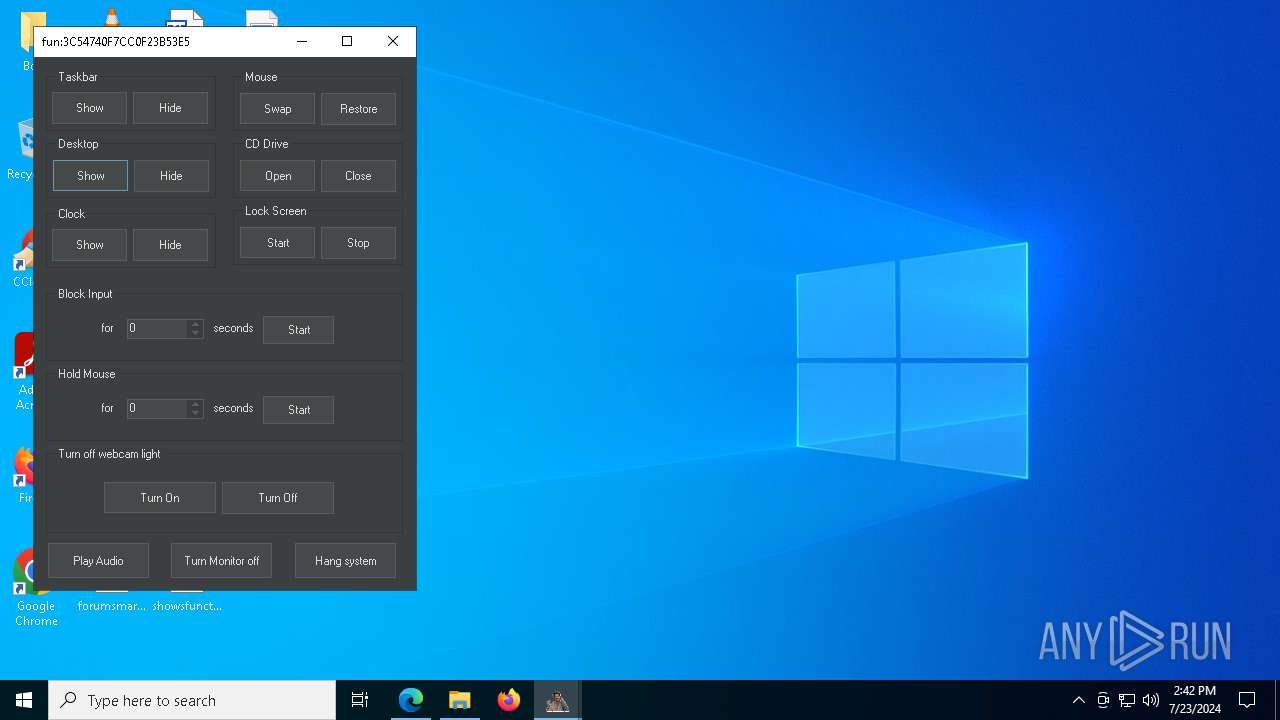
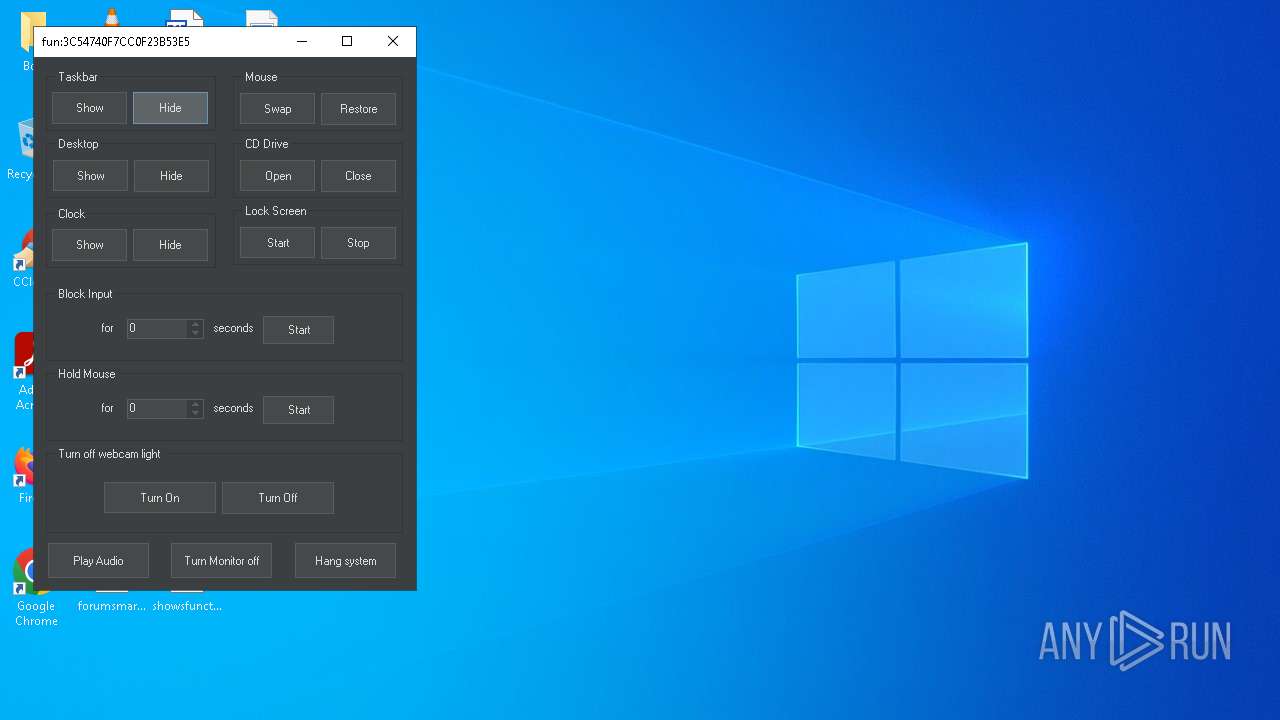
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | July 23, 2024, 14:39:45 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E889AA7FB4D8EBD10568A737AF148FD7 |
| SHA1: | 087DEFD5A07D456CB86DE1A675CE7F27FB833038 |
| SHA256: | AE1274A4FDCB853444A1086615318F6CEA6A8603E8E042C536469FB16D5E6FFF |
| SSDEEP: | 3:N8tEd4FtsqEnKqKqX4n:2uuFSqEnKxs4n |
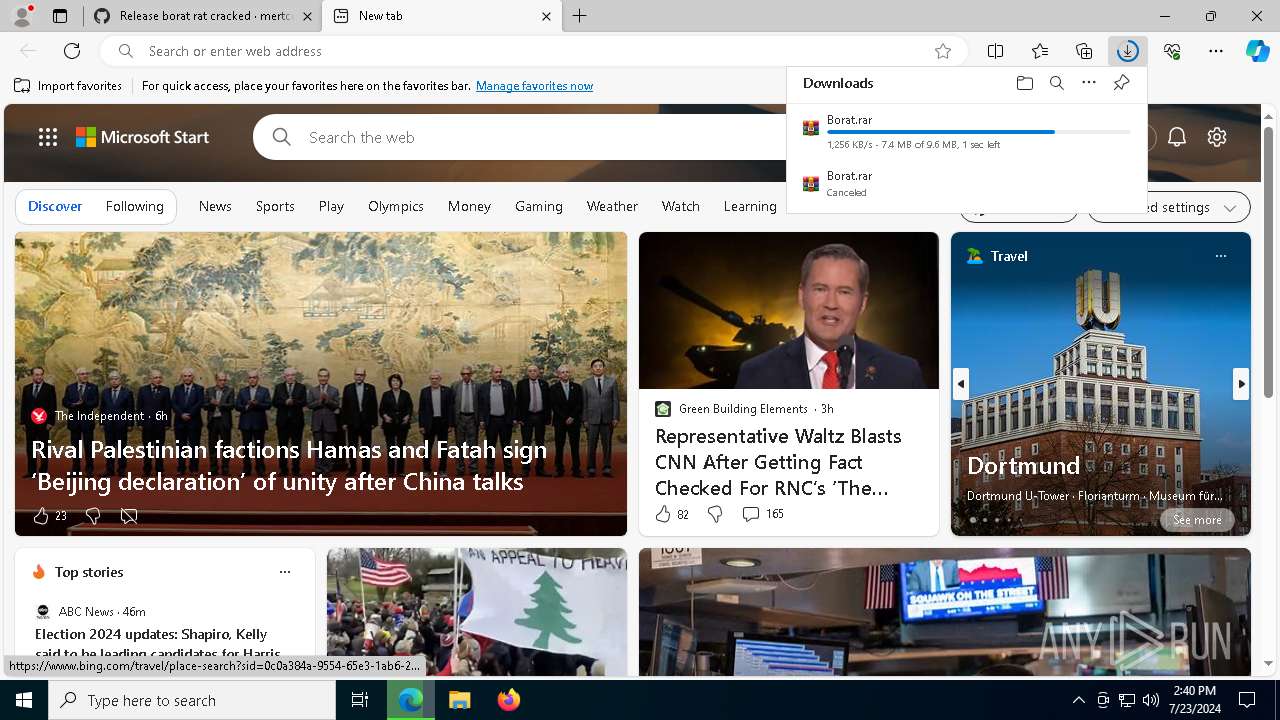
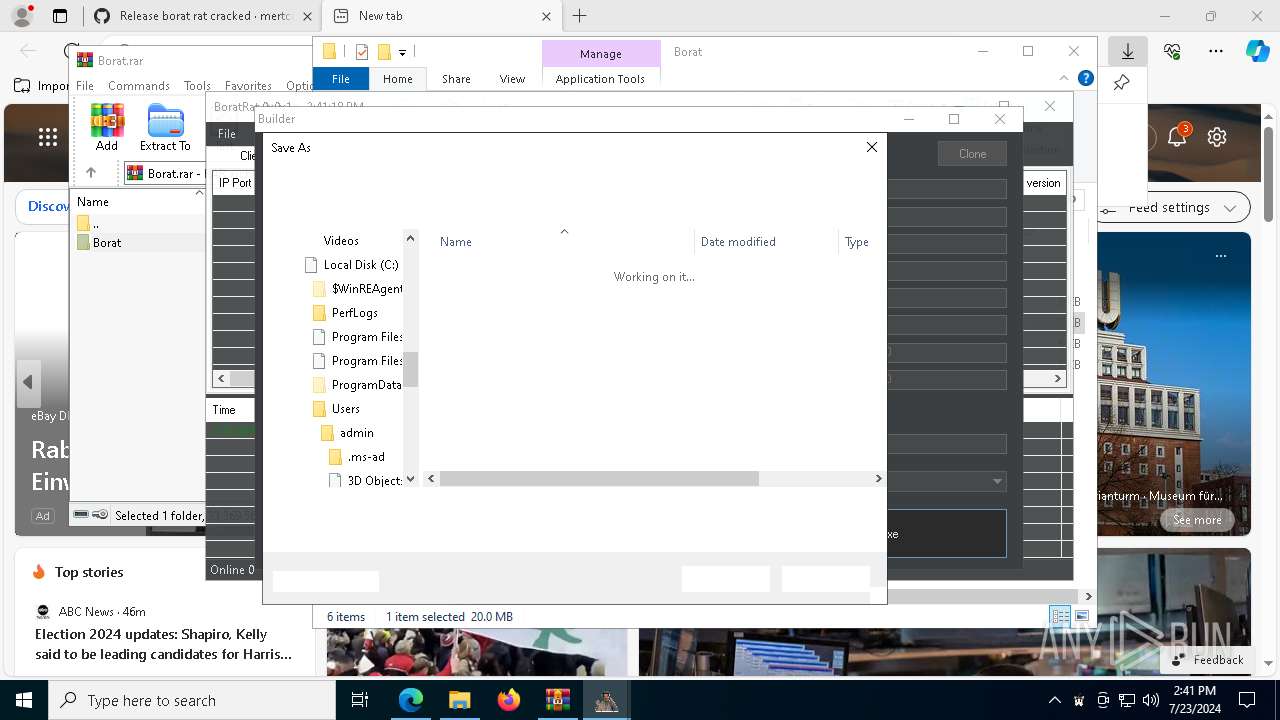
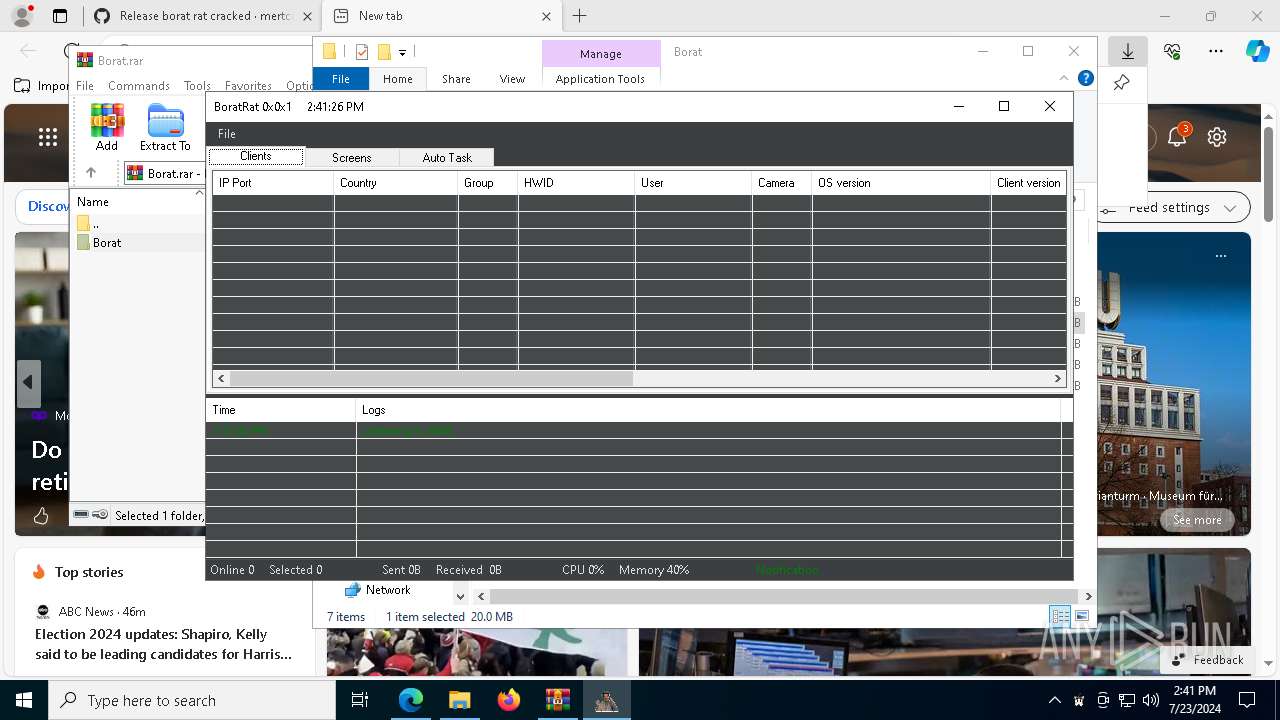
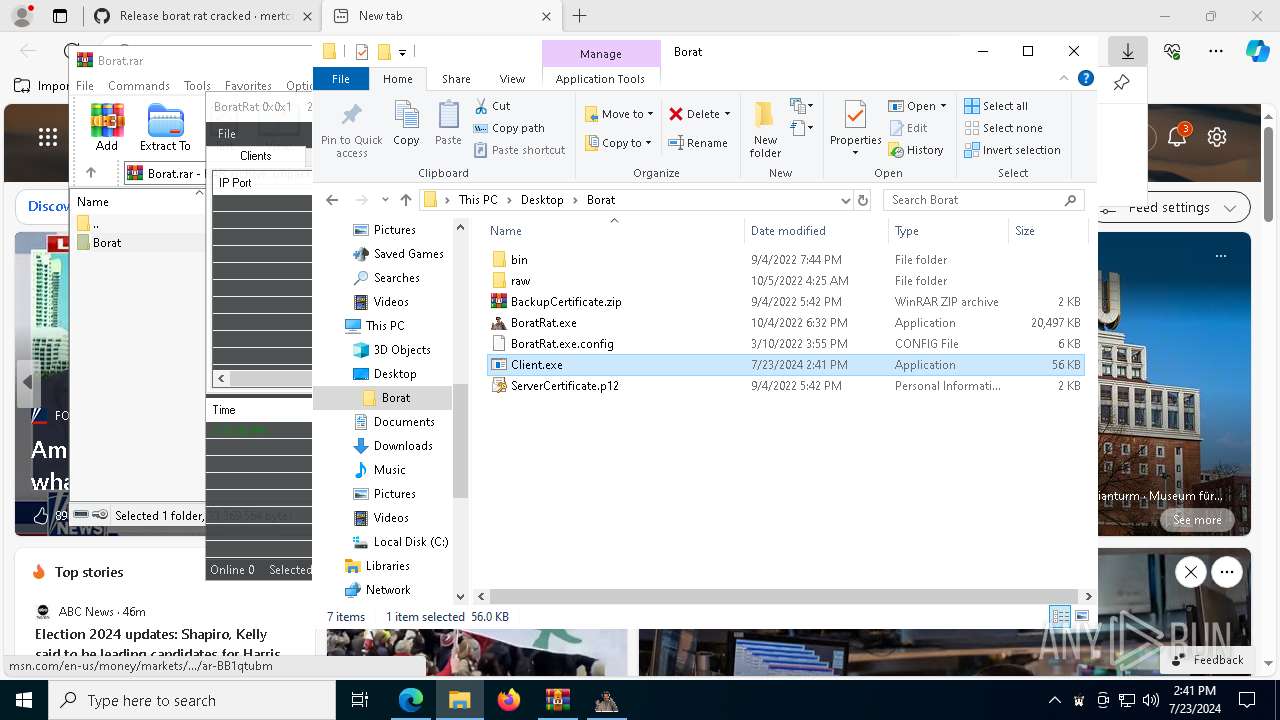
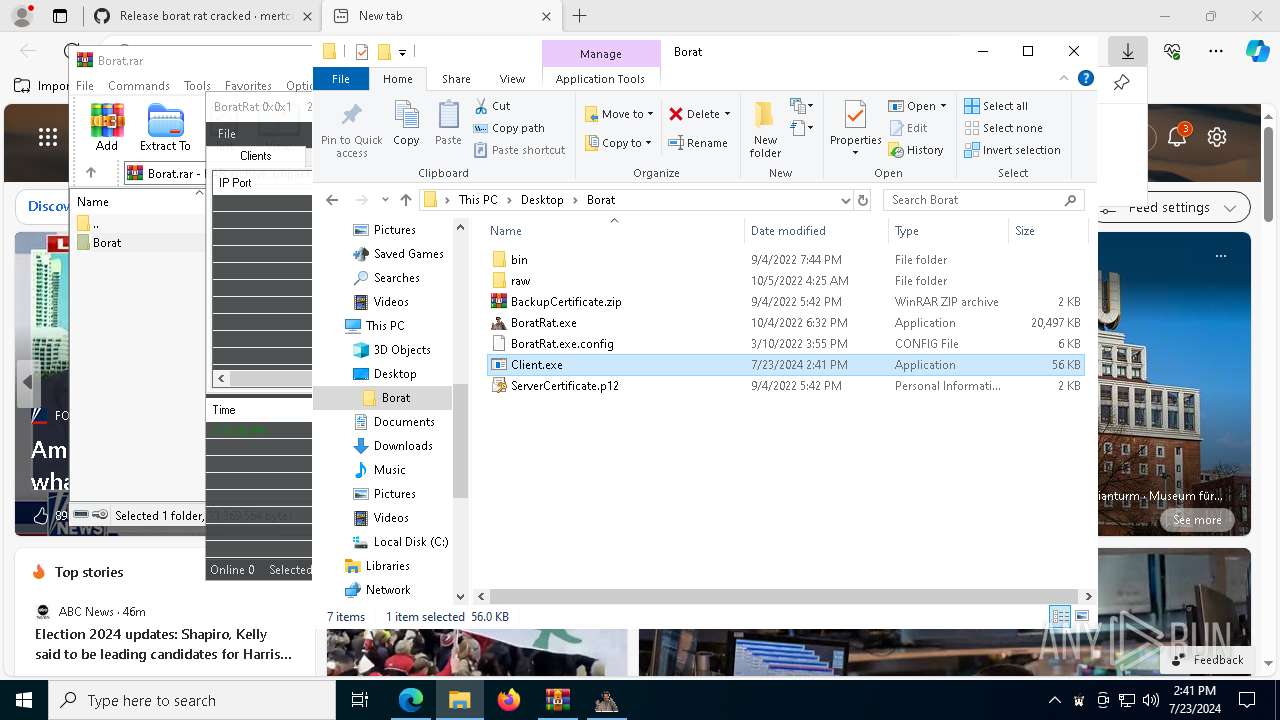
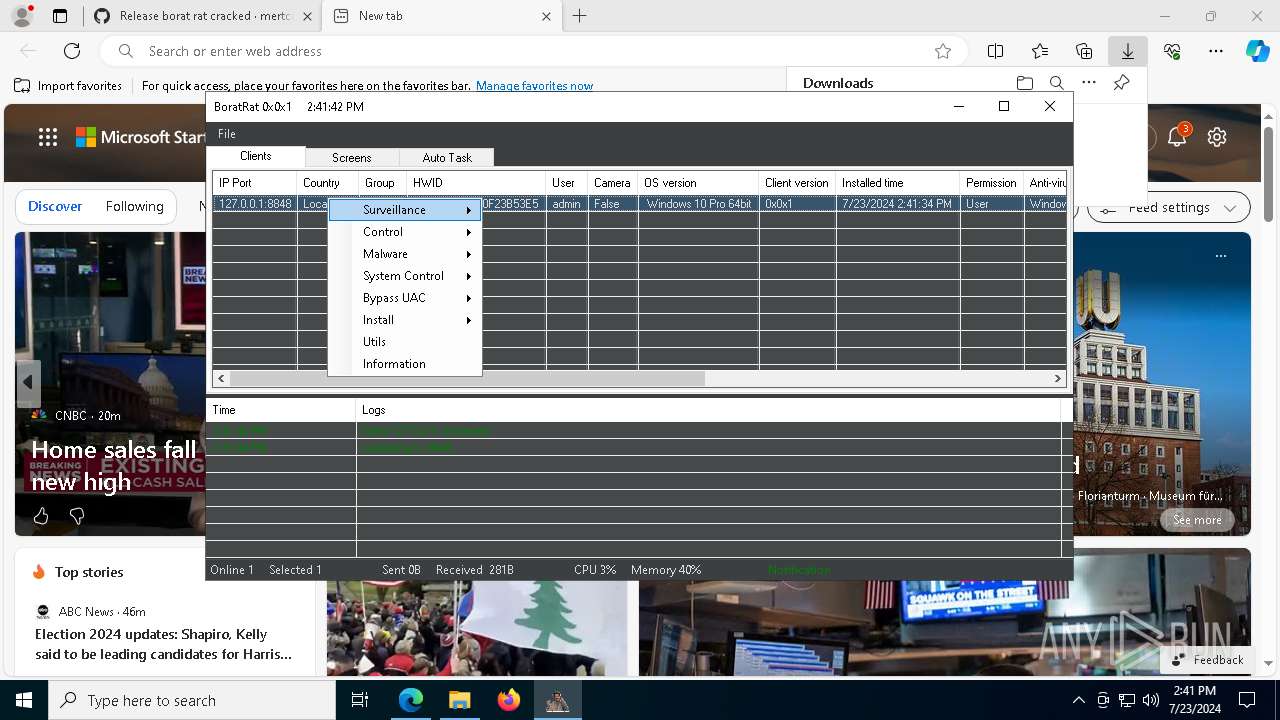
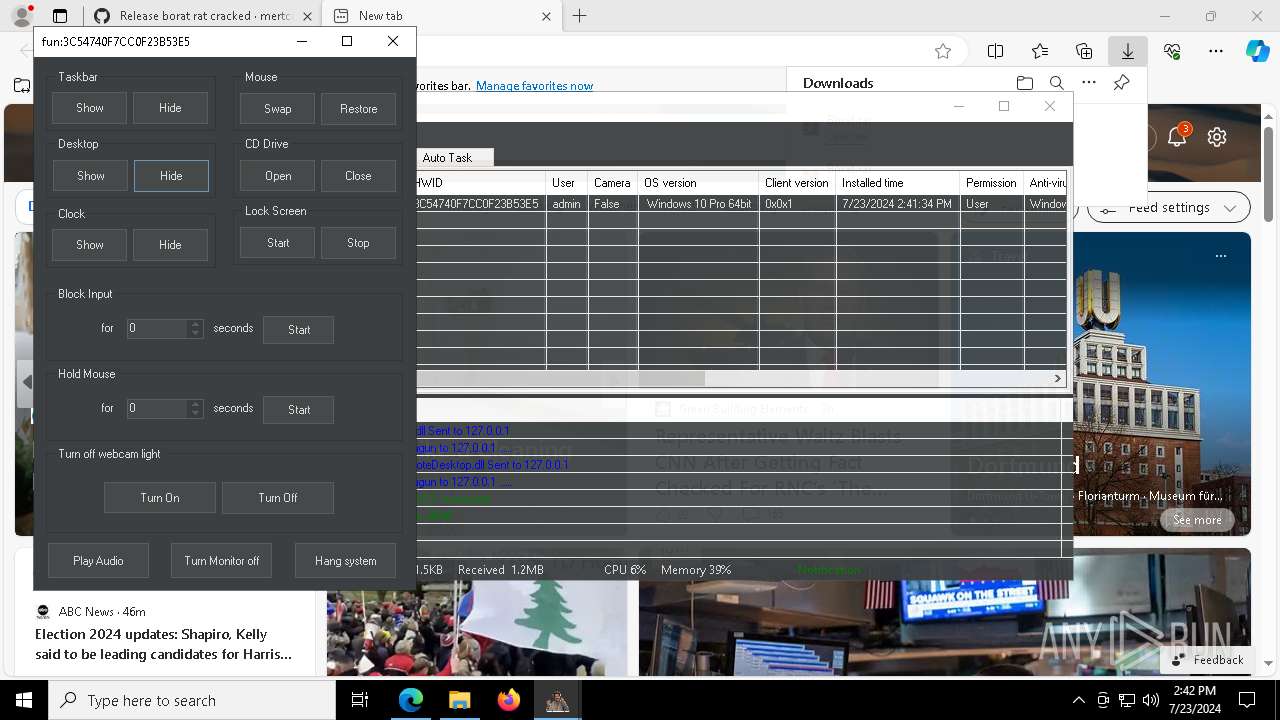
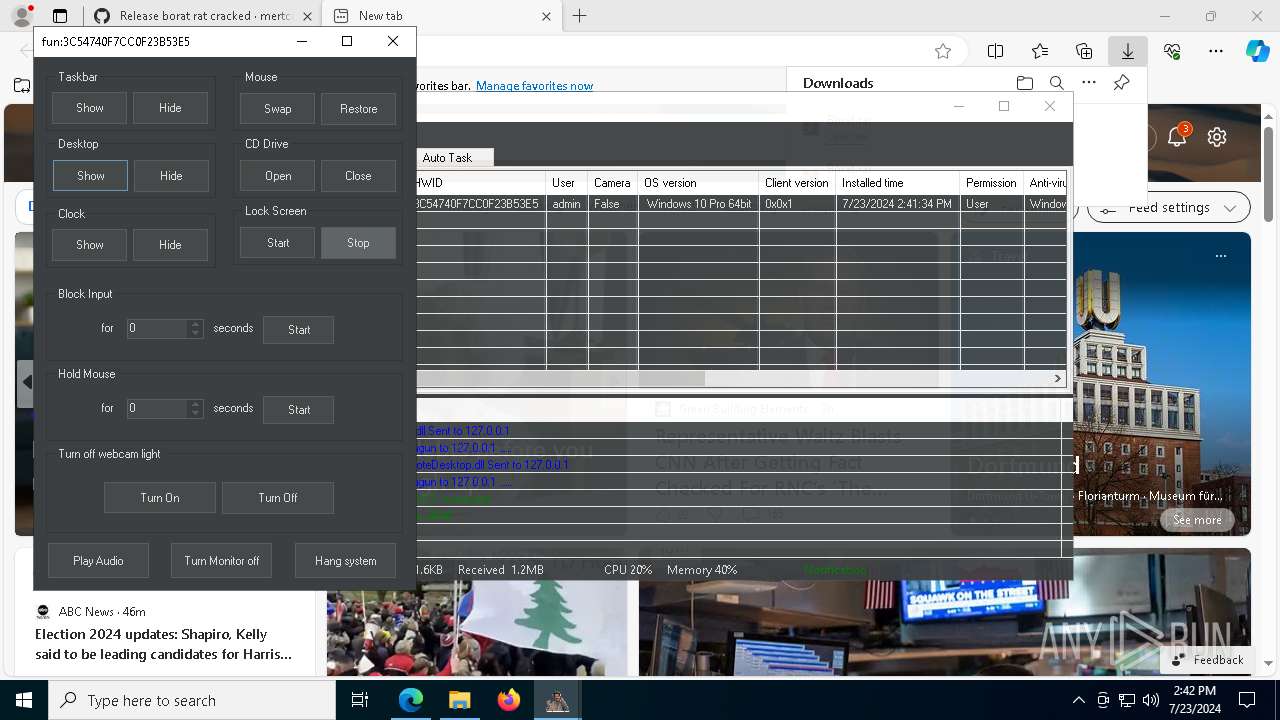
MALICIOUS
Actions looks like stealing of personal data
- WinRAR.exe (PID: 4116)
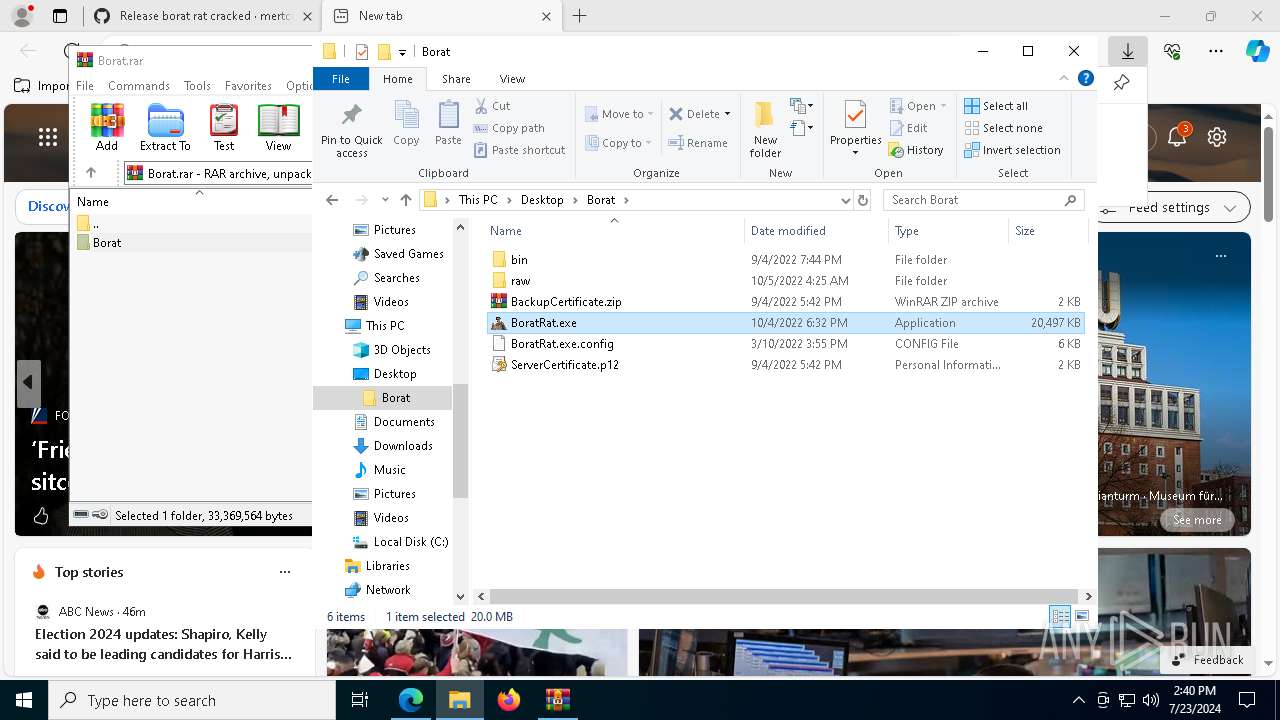
- BoratRat.exe (PID: 7928)
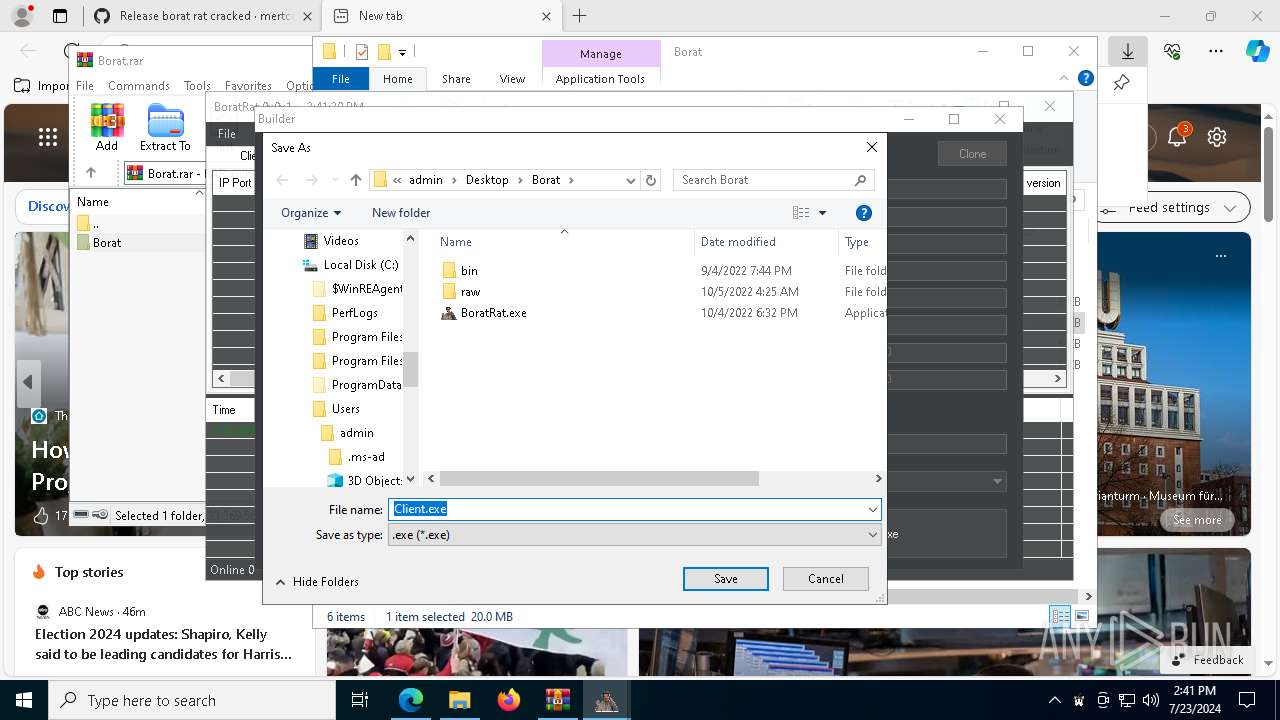
BORAT mutex has been found
- Client.exe (PID: 7648)
- test.exe (PID: 7408)
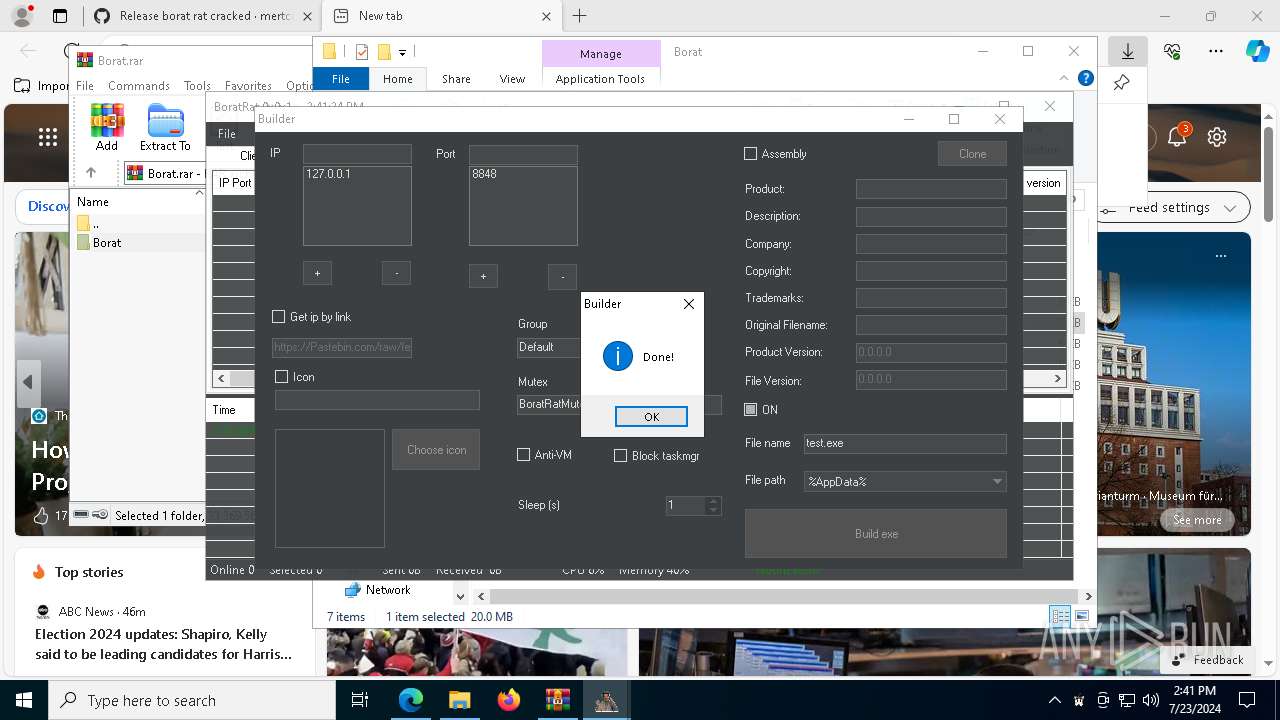
ASYNCRAT has been detected (YARA)
- BoratRat.exe (PID: 7928)
- test.exe (PID: 7408)
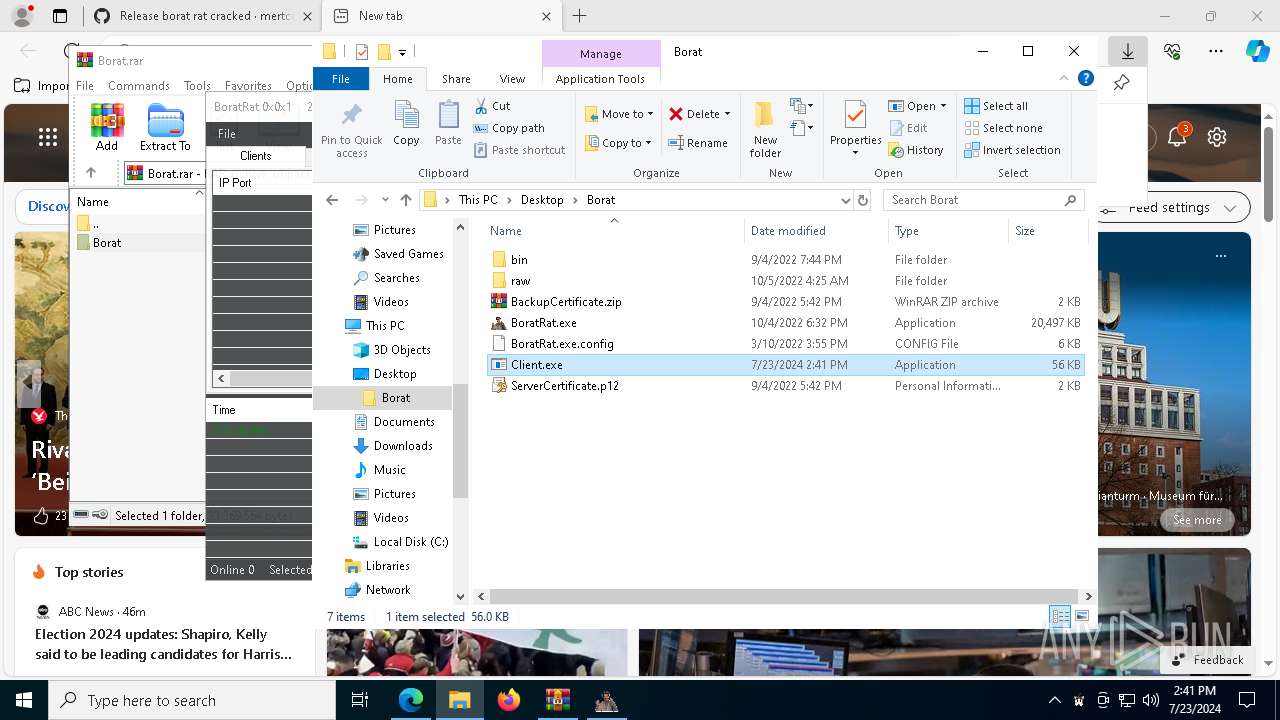
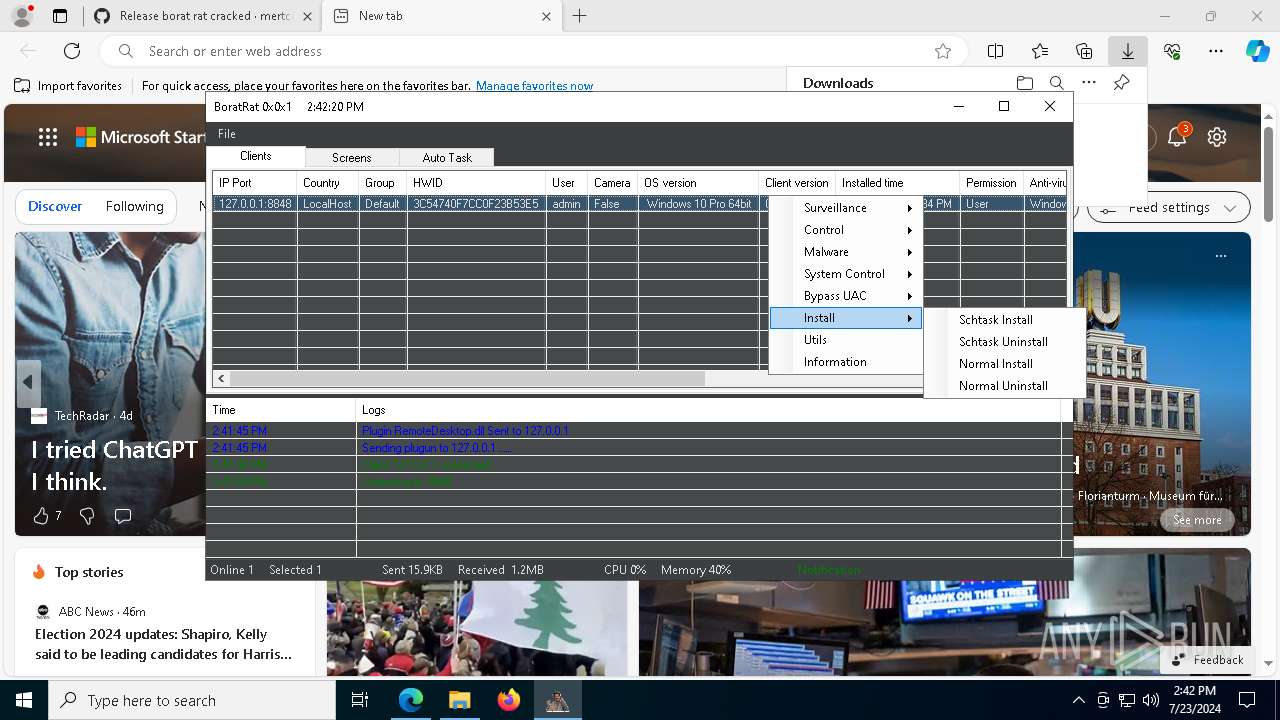
Changes the autorun value in the registry
- Client.exe (PID: 7648)
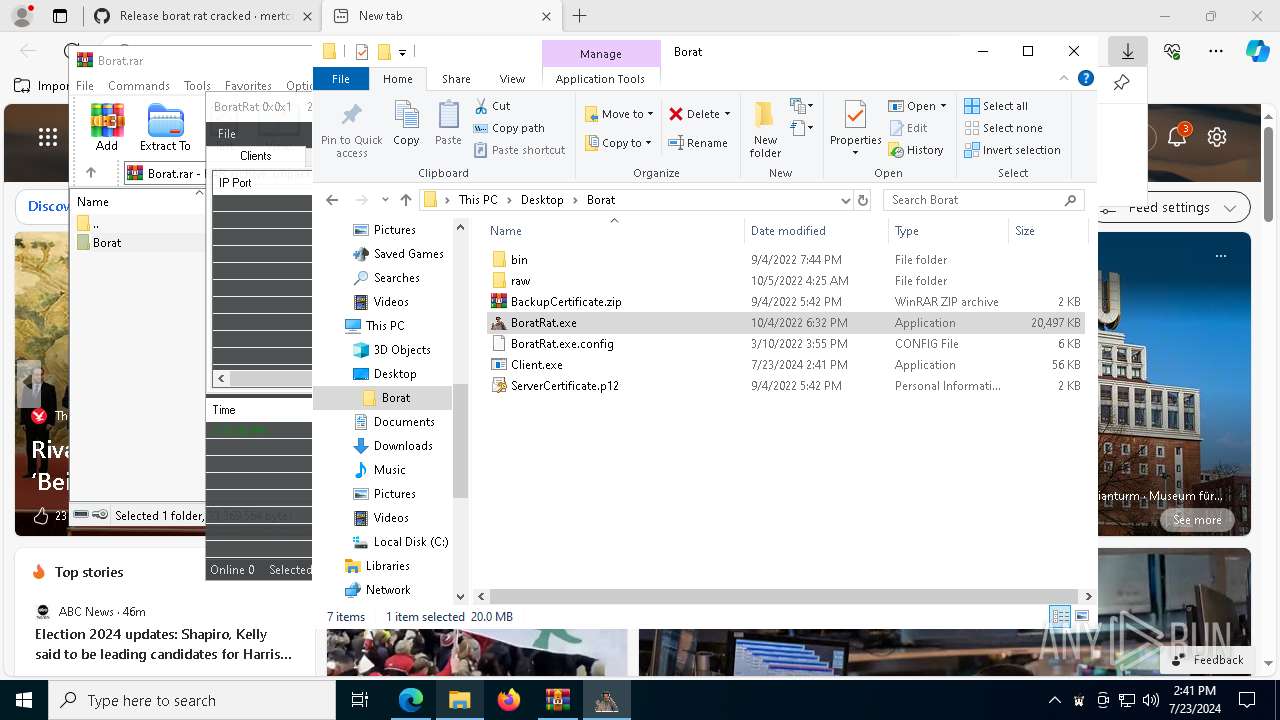
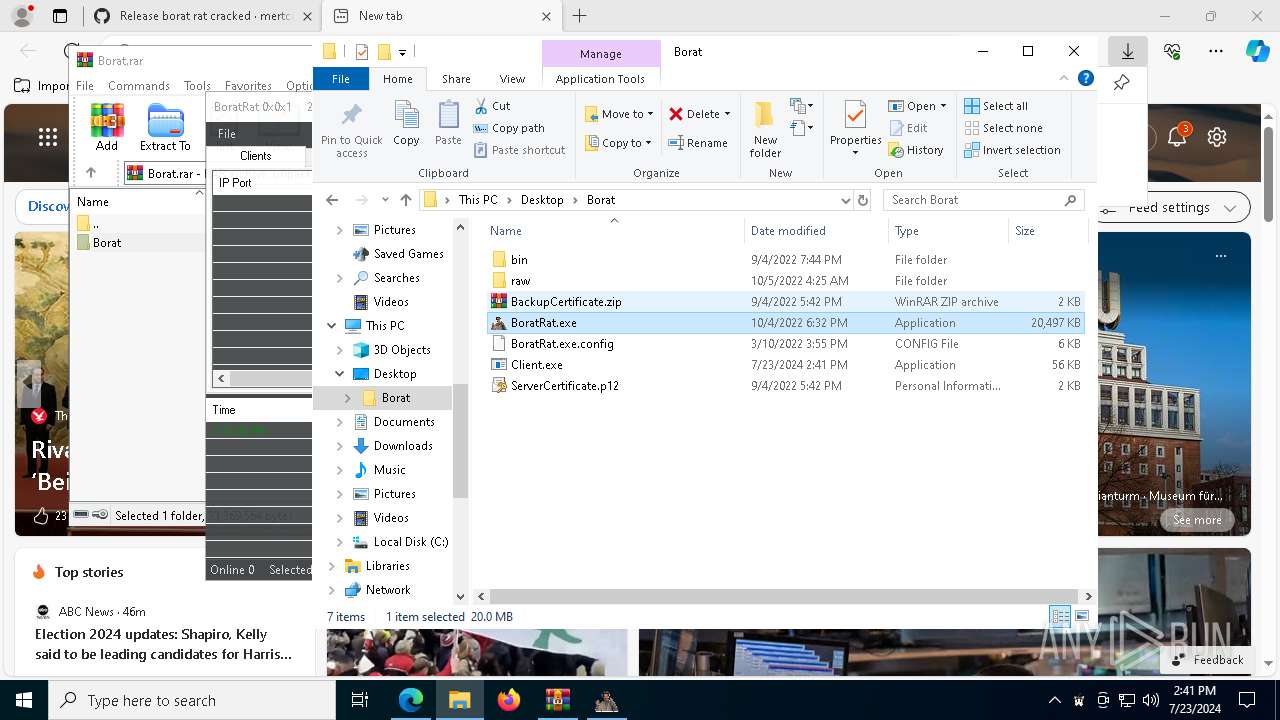
Drops the executable file immediately after the start
- Client.exe (PID: 7648)
SUSPICIOUS
Reads security settings of Internet Explorer
- BoratRat.exe (PID: 7928)
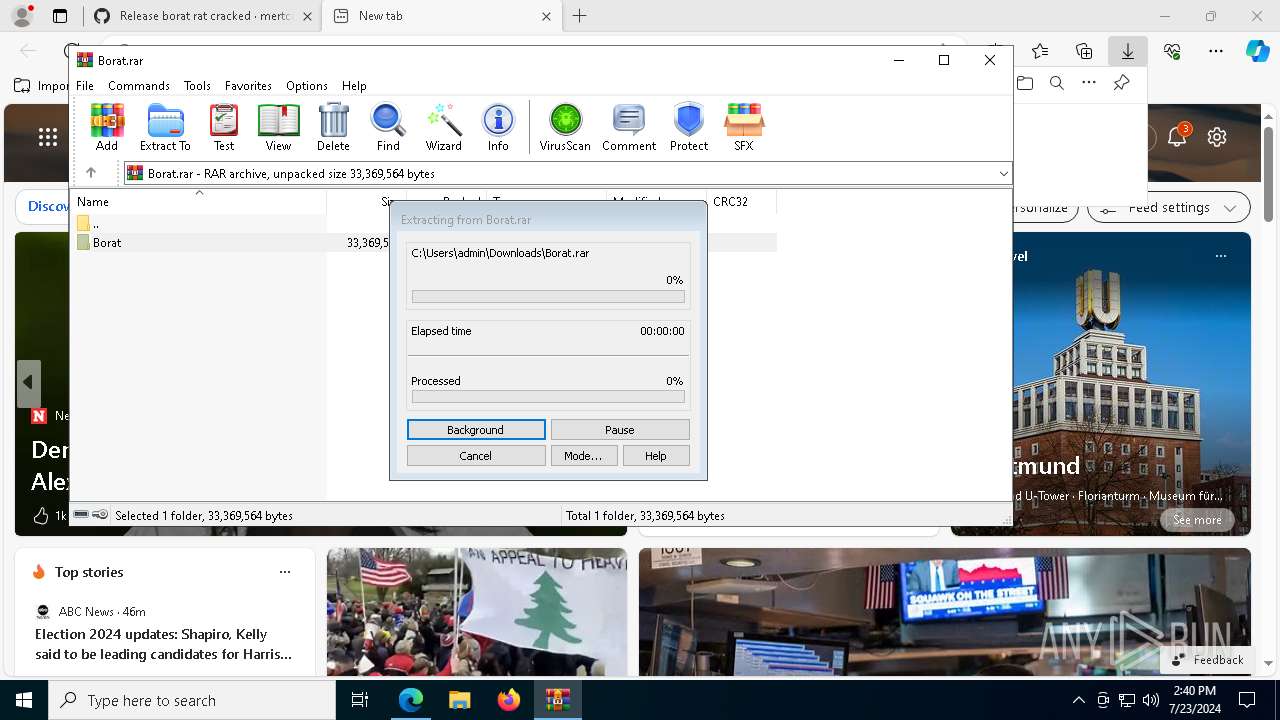
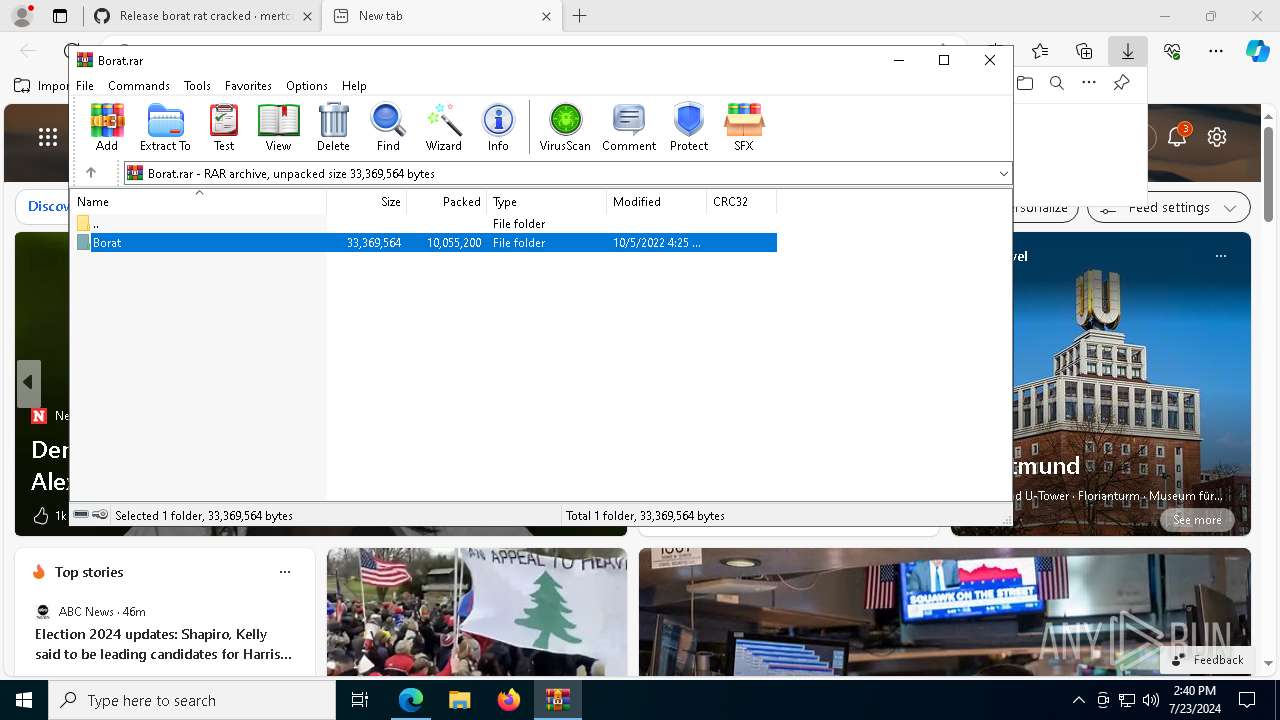
The process creates files with name similar to system file names
- WinRAR.exe (PID: 4116)
The process checks if it is being run in the virtual environment
- BoratRat.exe (PID: 7928)
- Client.exe (PID: 7648)
Creates file in the systems drive root
- BoratRat.exe (PID: 7928)
Executable content was dropped or overwritten
- Client.exe (PID: 7648)
Executing commands from a ".bat" file
- Client.exe (PID: 7648)
Starts CMD.EXE for commands execution
- Client.exe (PID: 7648)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2096)
The executable file from the user directory is run by the CMD process
- test.exe (PID: 7408)
INFO
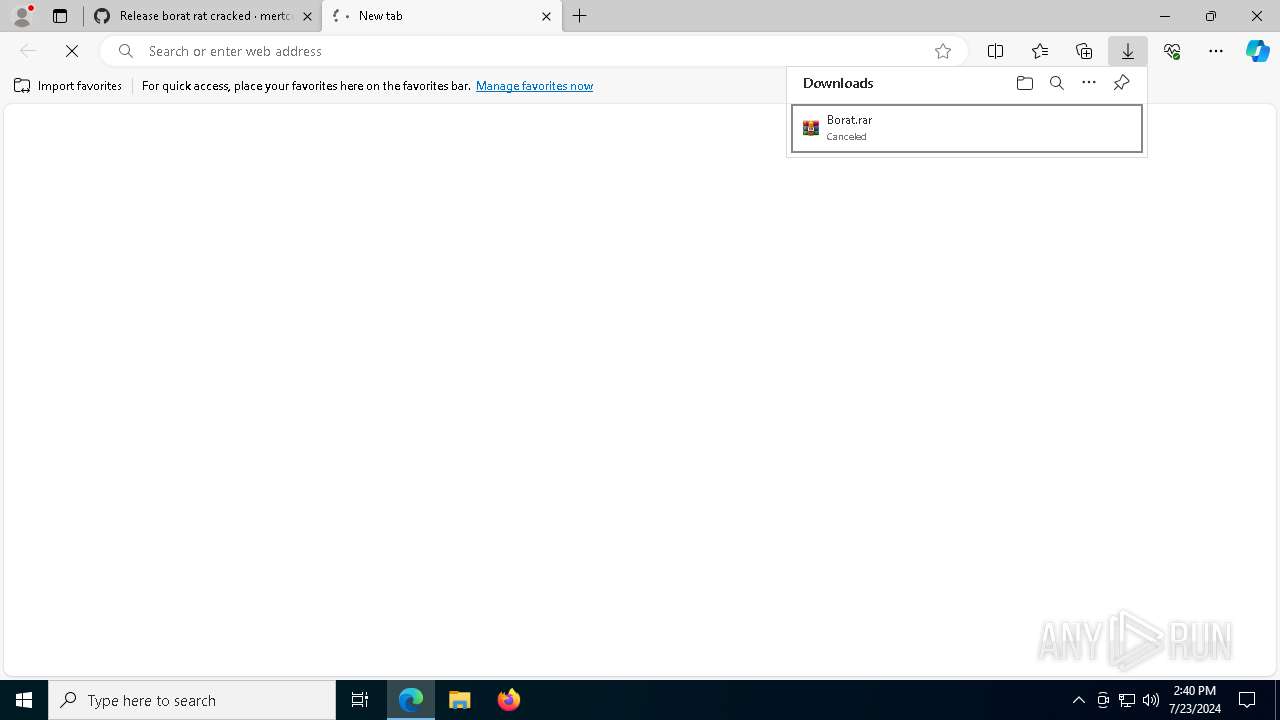
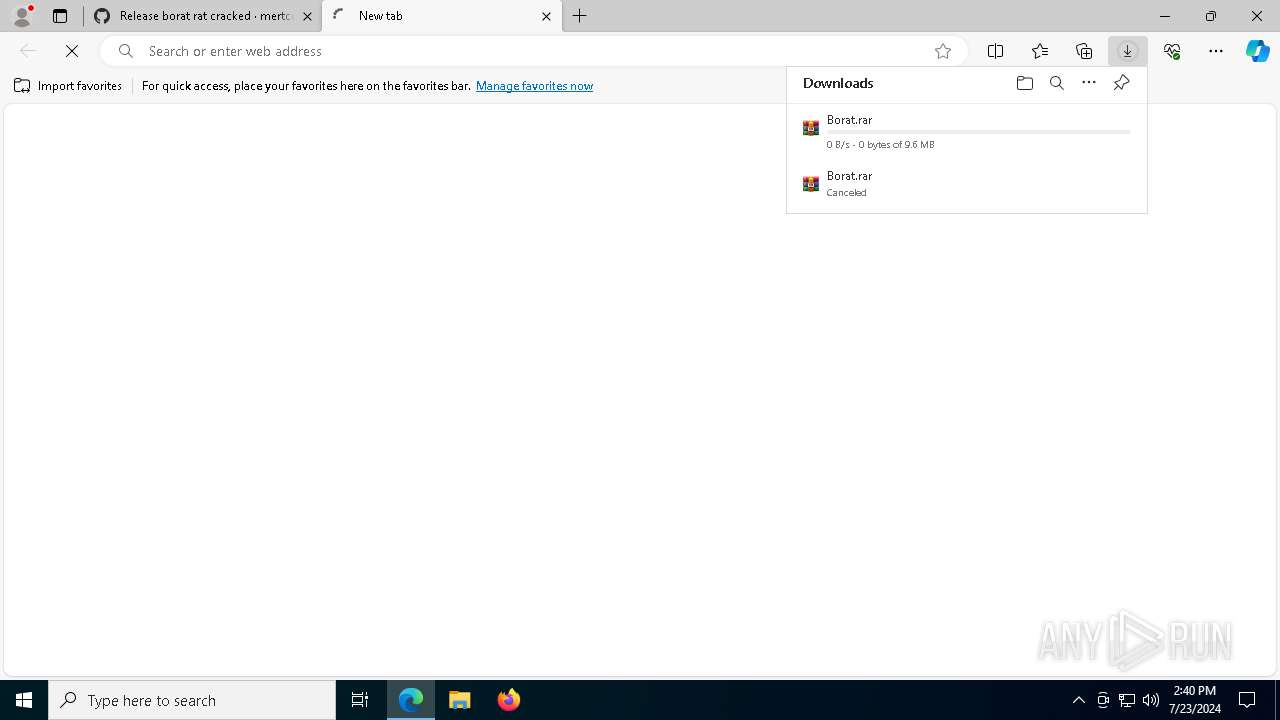
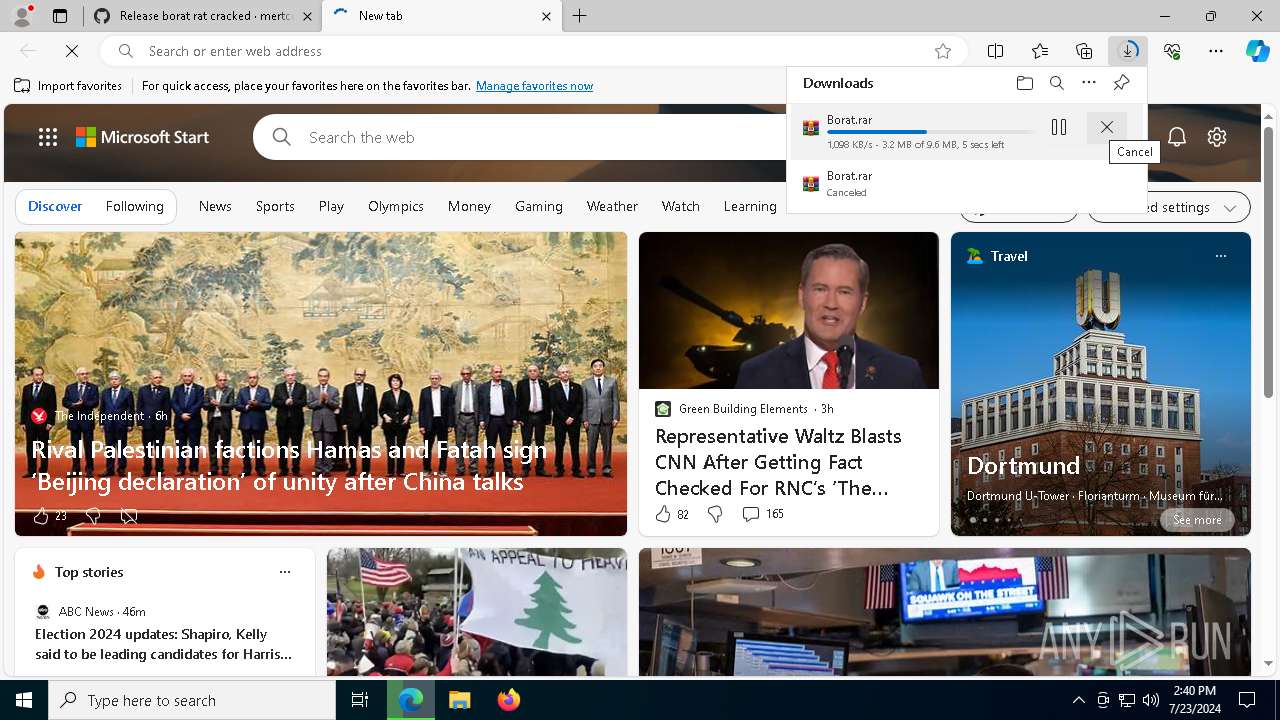
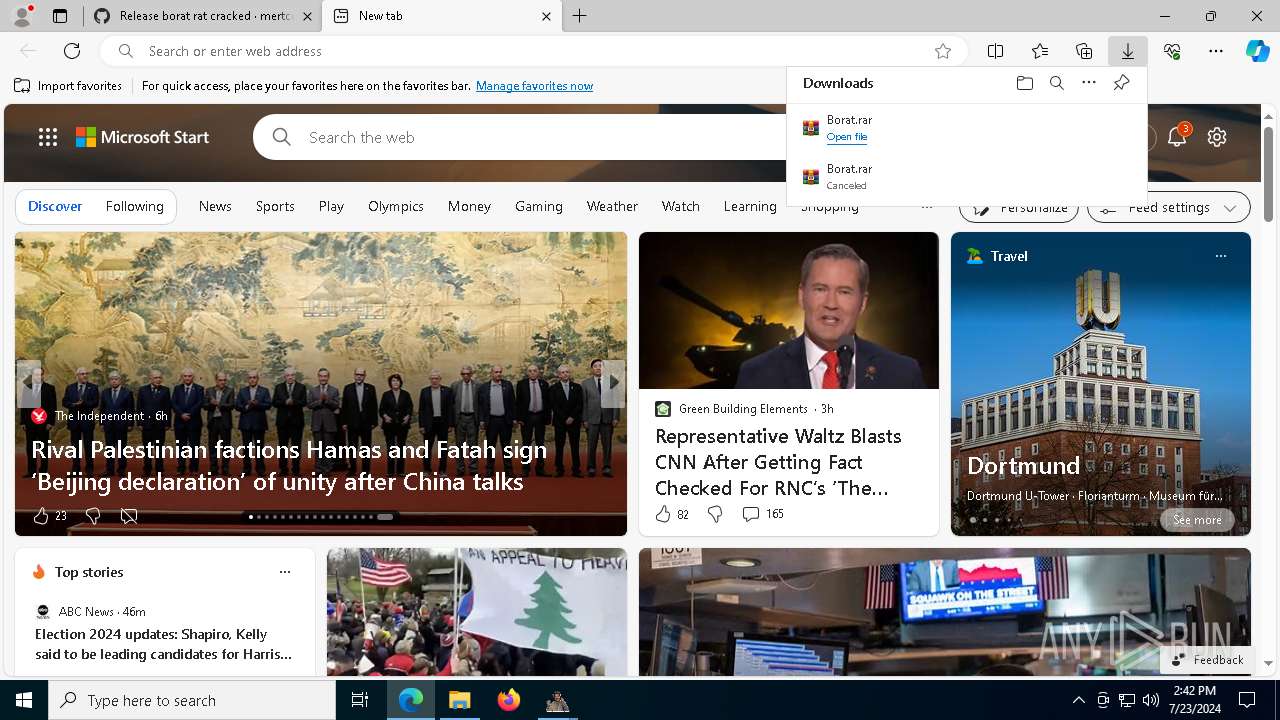
Drops the executable file immediately after the start
- msedge.exe (PID: 3140)
- msedge.exe (PID: 6916)
- WinRAR.exe (PID: 4116)
Reads Microsoft Office registry keys
- msedge.exe (PID: 3140)
The process uses the downloaded file
- WinRAR.exe (PID: 4116)
- msedge.exe (PID: 6328)
- msedge.exe (PID: 3140)
Reads Environment values
- identity_helper.exe (PID: 7776)
- BoratRat.exe (PID: 7928)
- test.exe (PID: 7408)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4116)
Checks supported languages
- identity_helper.exe (PID: 7776)
- BoratRat.exe (PID: 7928)
- Client.exe (PID: 7648)
- TextInputHost.exe (PID: 7256)
- test.exe (PID: 7408)
Reads the computer name
- identity_helper.exe (PID: 7776)
- BoratRat.exe (PID: 7928)
- Client.exe (PID: 7648)
- test.exe (PID: 7408)
- TextInputHost.exe (PID: 7256)
Reads the machine GUID from the registry
- BoratRat.exe (PID: 7928)
- Client.exe (PID: 7648)
- test.exe (PID: 7408)
Manual execution by a user
- BoratRat.exe (PID: 7928)
- Client.exe (PID: 7648)
Application launched itself
- msedge.exe (PID: 3140)
Creates files or folders in the user directory
- BoratRat.exe (PID: 7928)
- Client.exe (PID: 7648)
Potential access to remote process (Base64 Encoded 'OpenProcess')
- BoratRat.exe (PID: 7928)
Create files in a temporary directory
- Client.exe (PID: 7648)
Checks proxy server information
- slui.exe (PID: 7252)
Reads the software policy settings
- test.exe (PID: 7408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
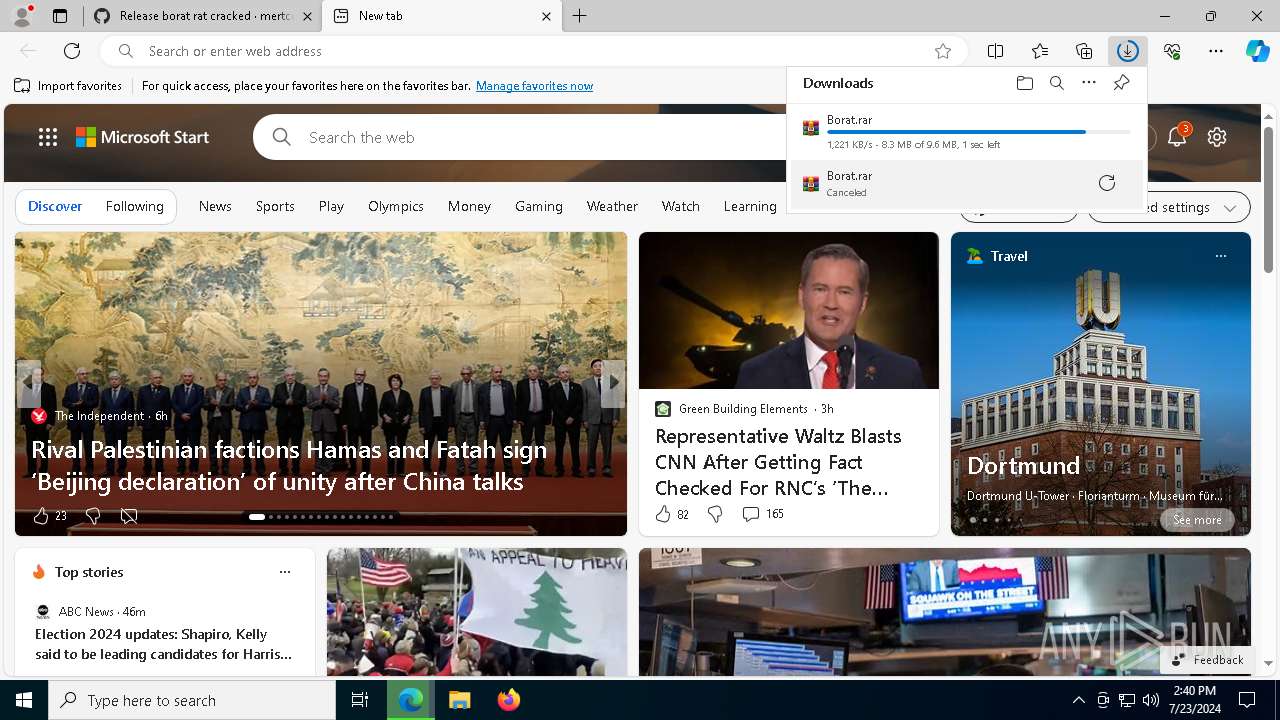
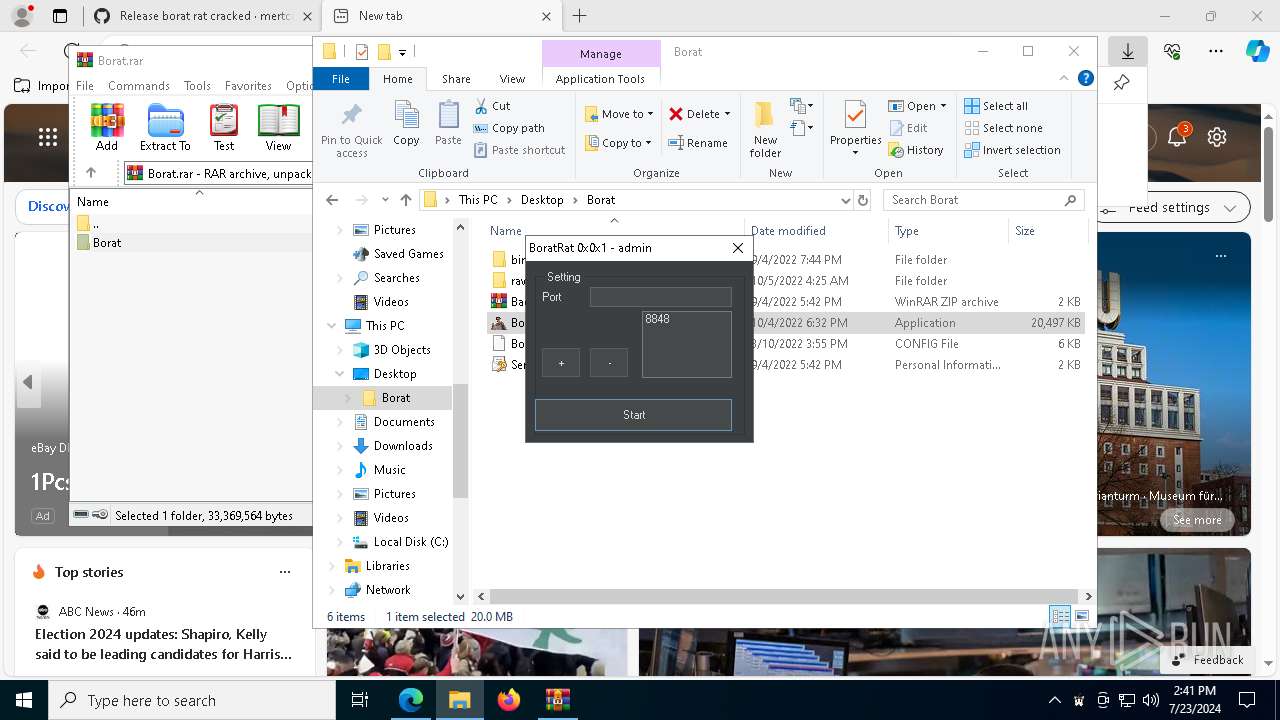
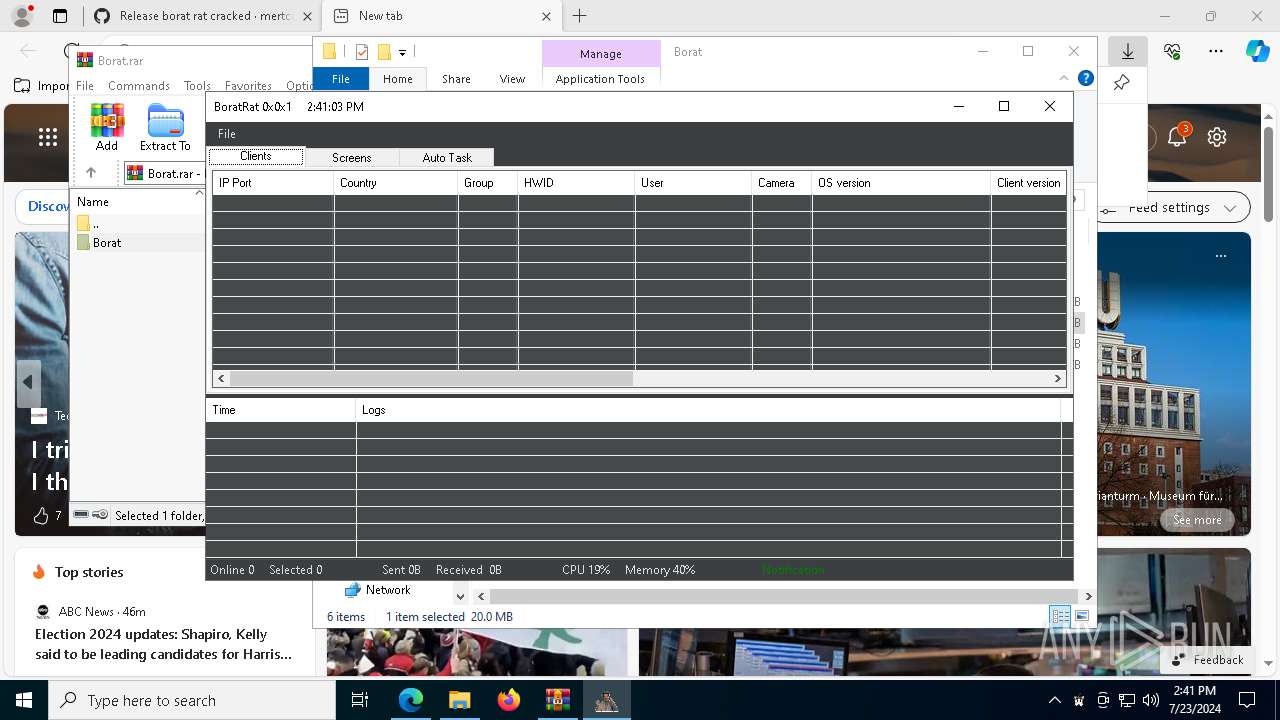
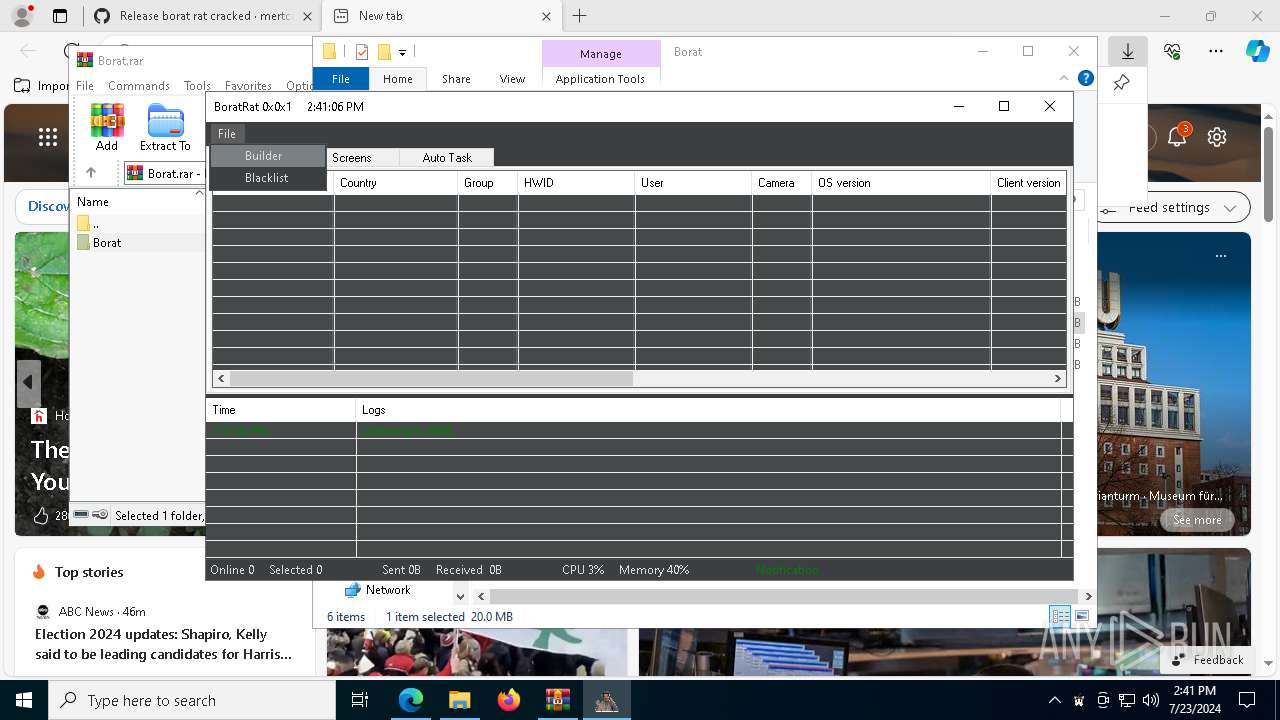
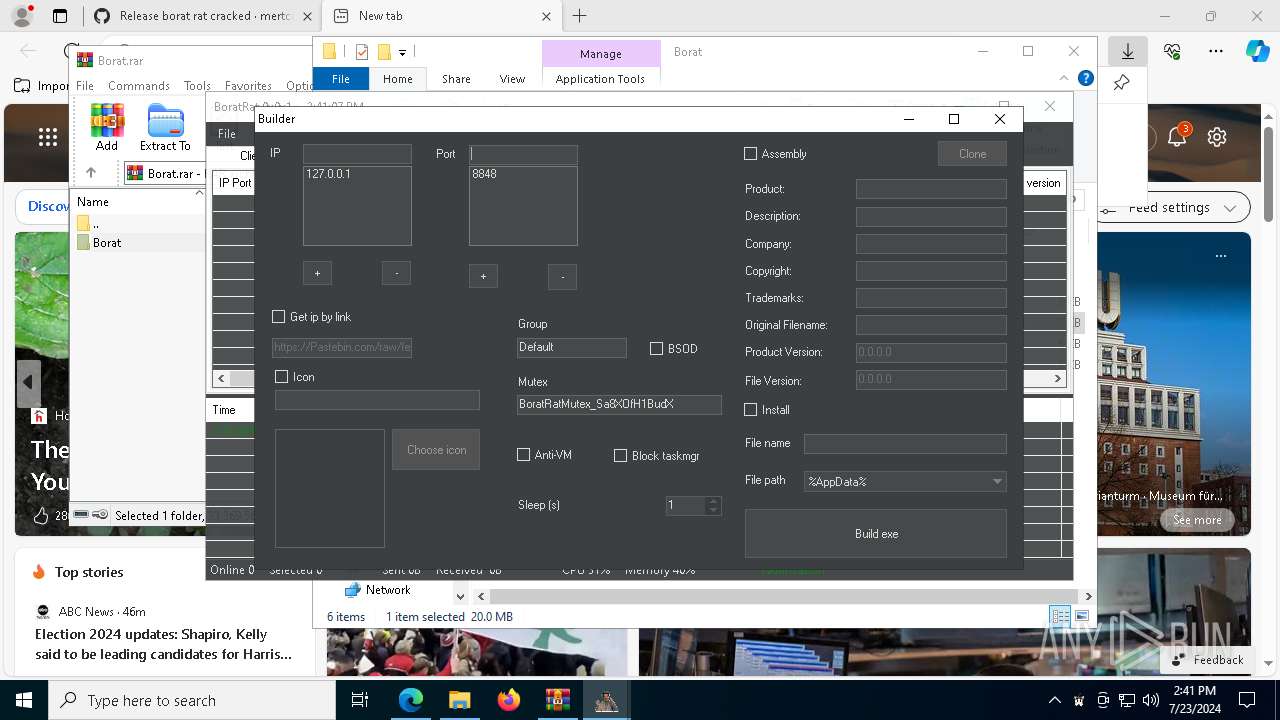
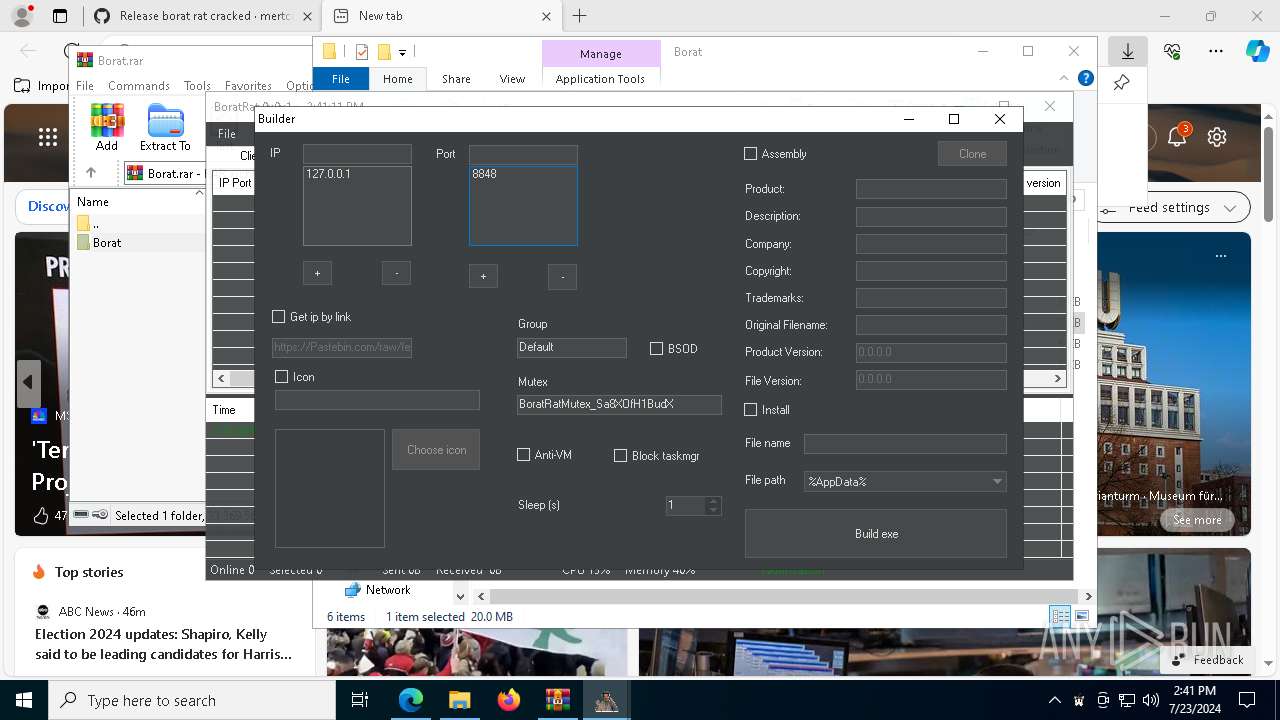
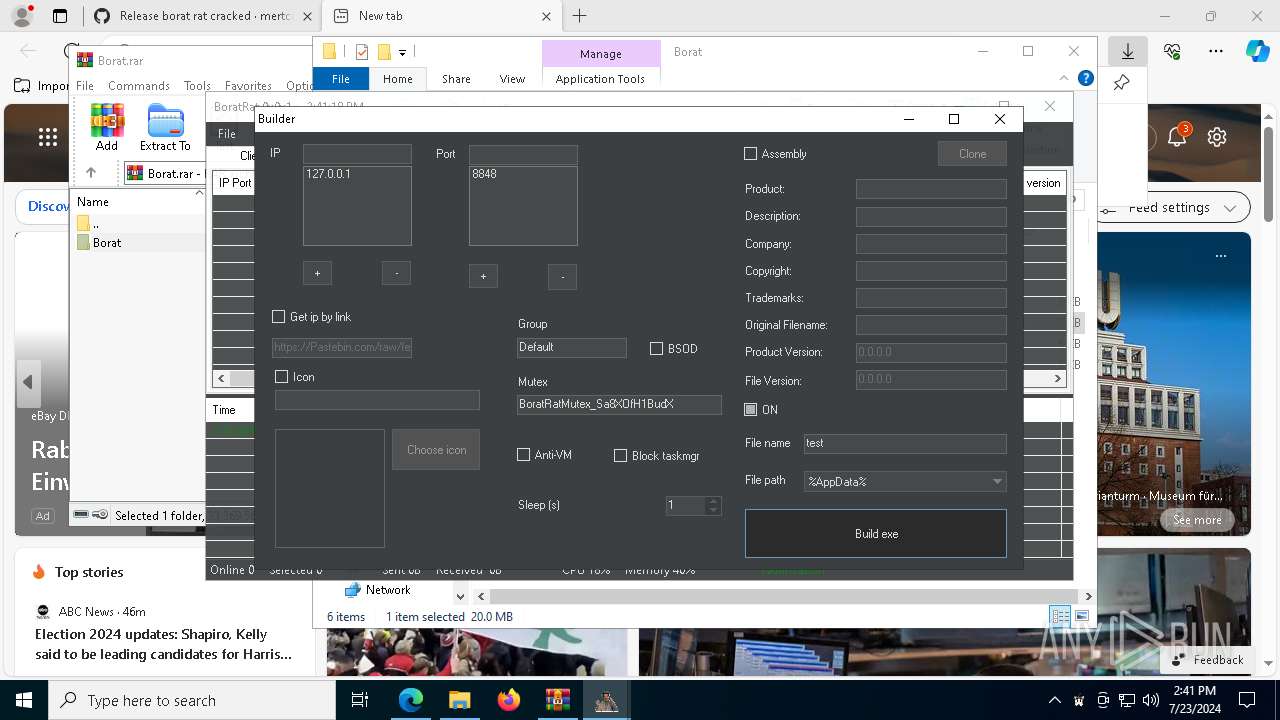
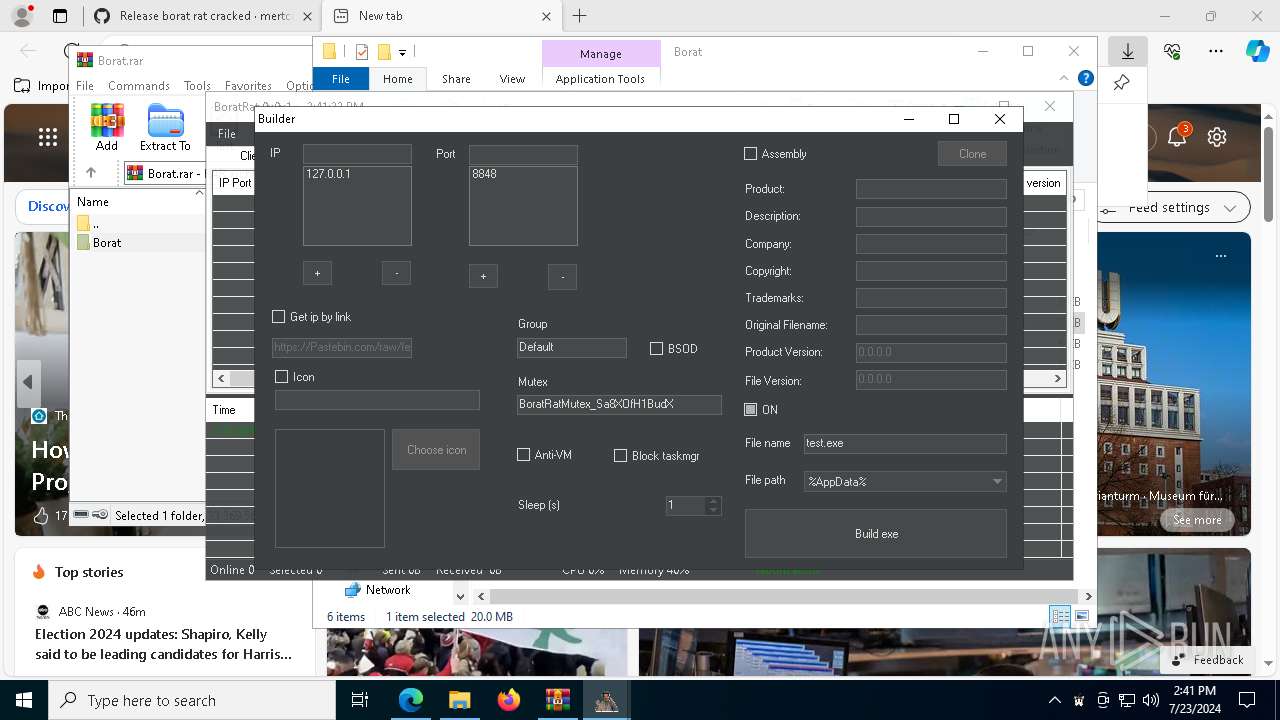
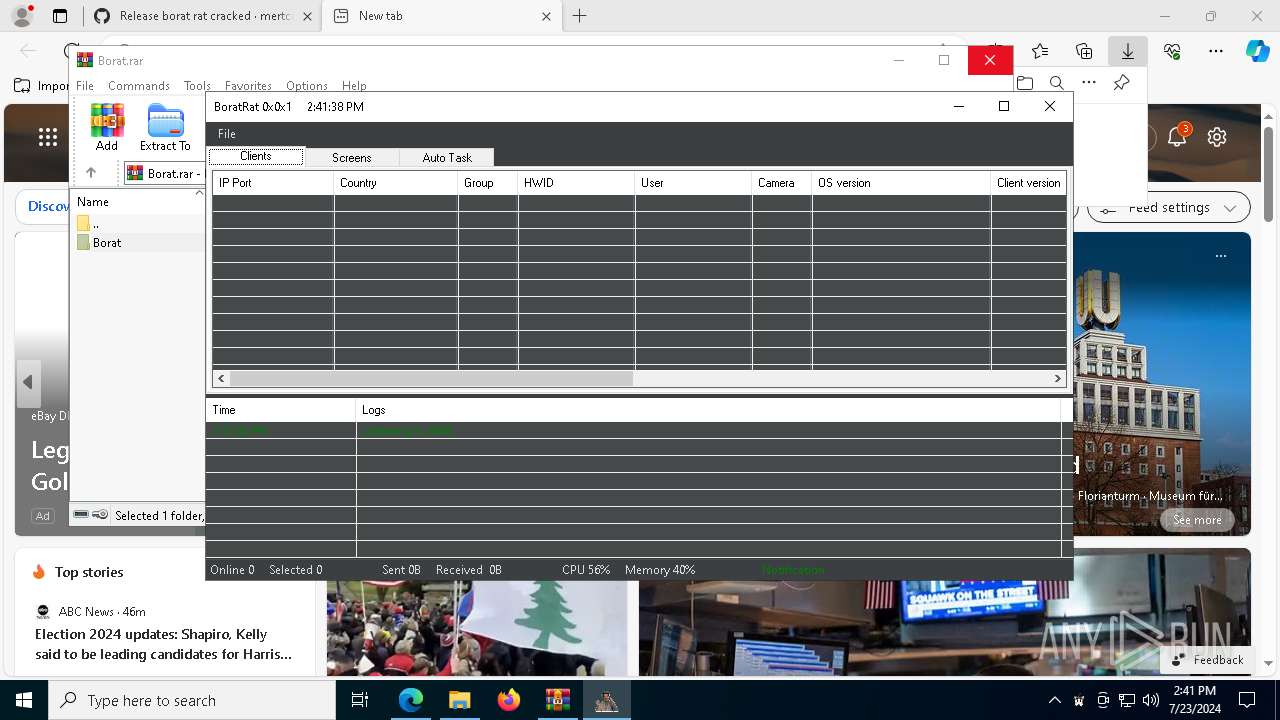
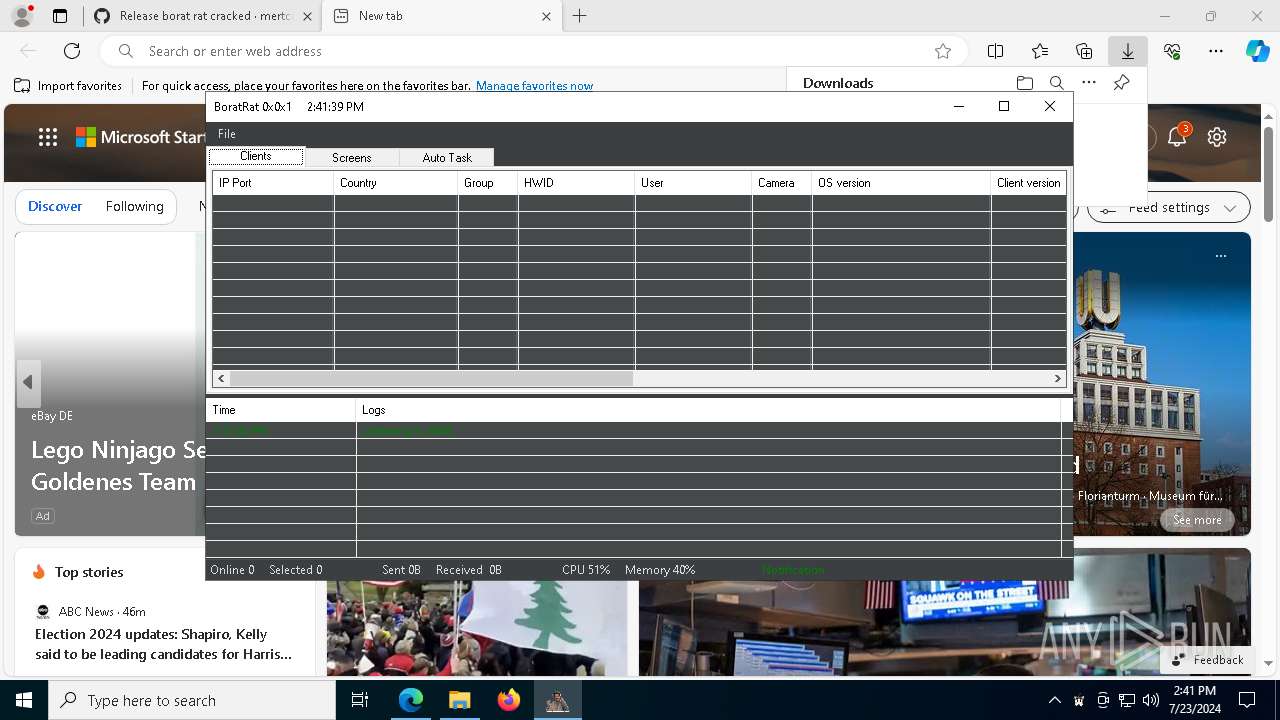
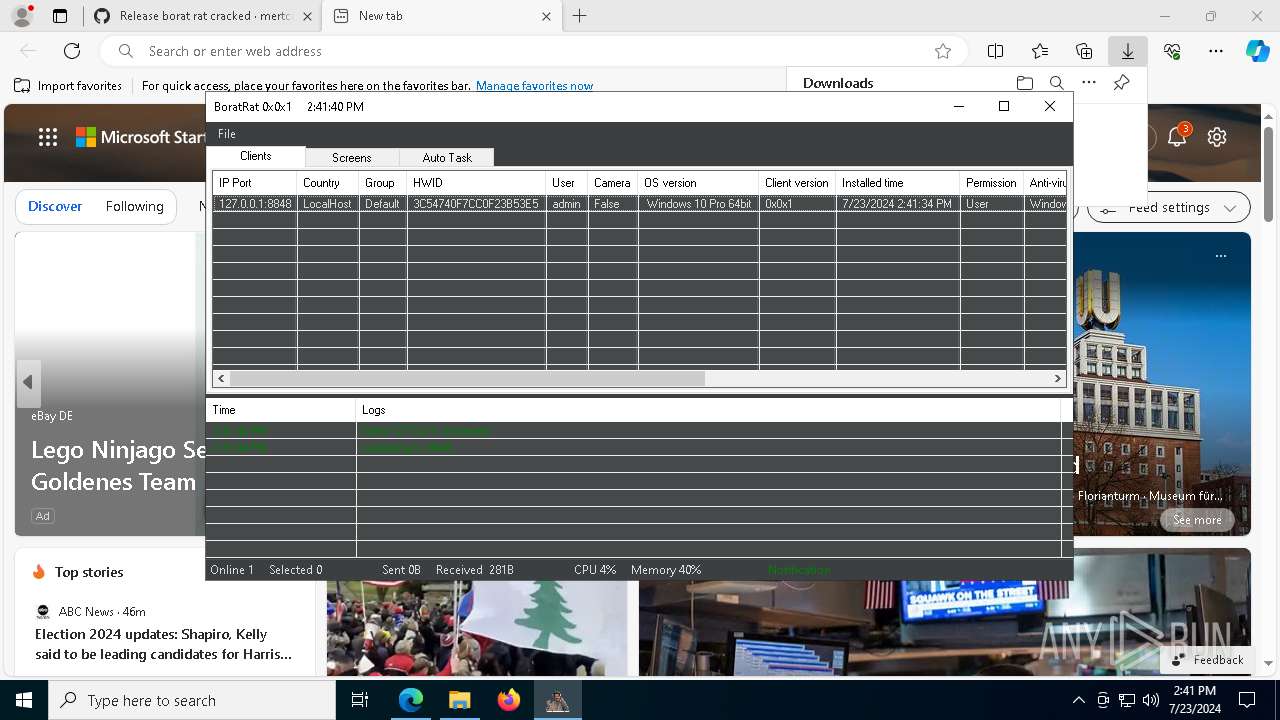
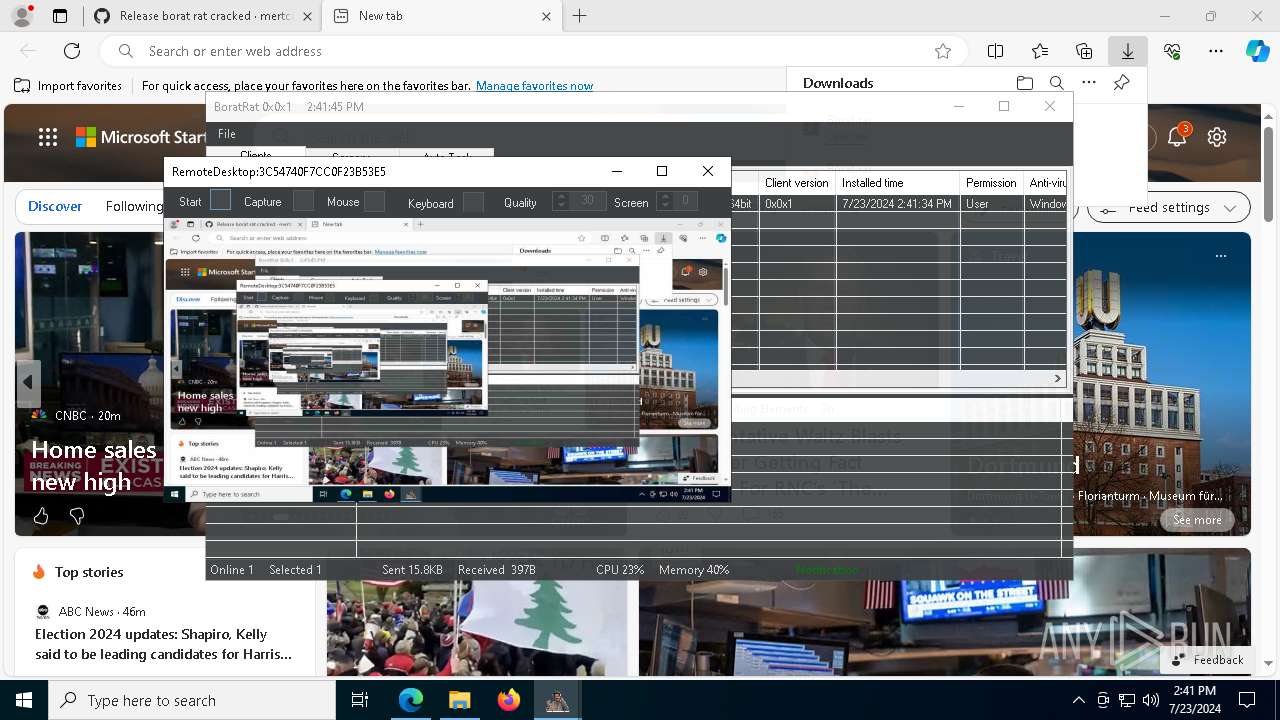
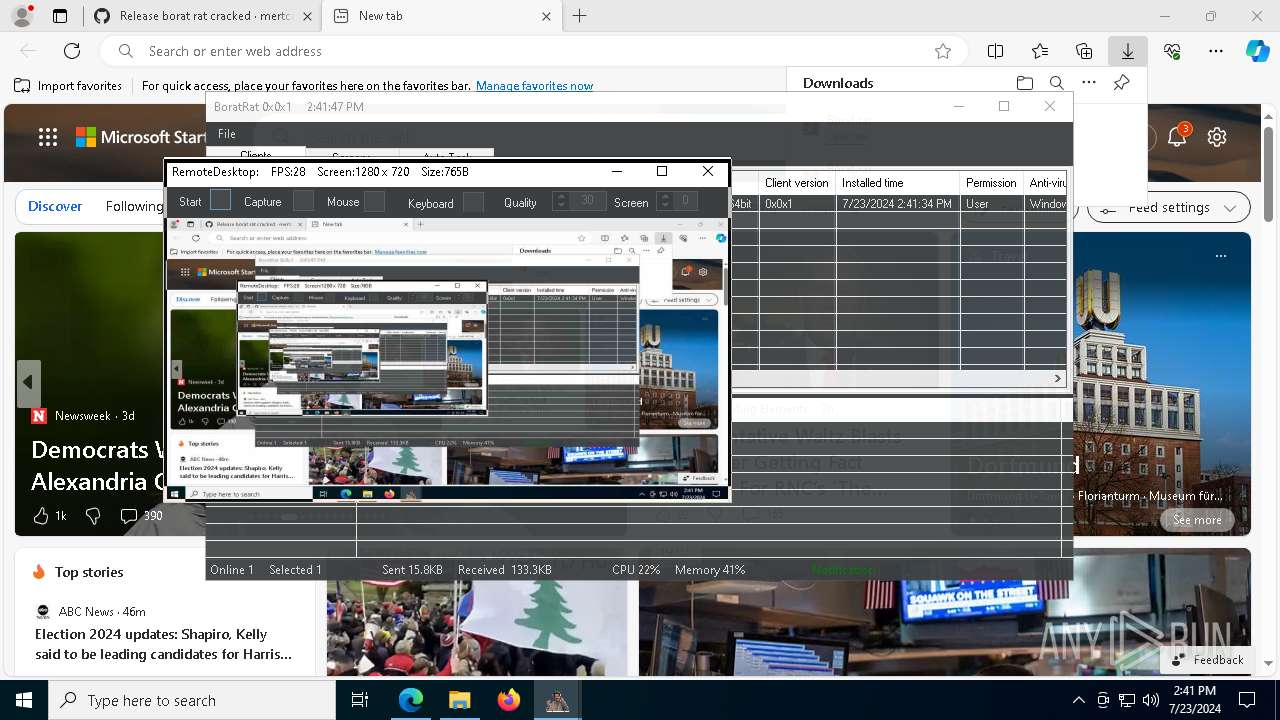
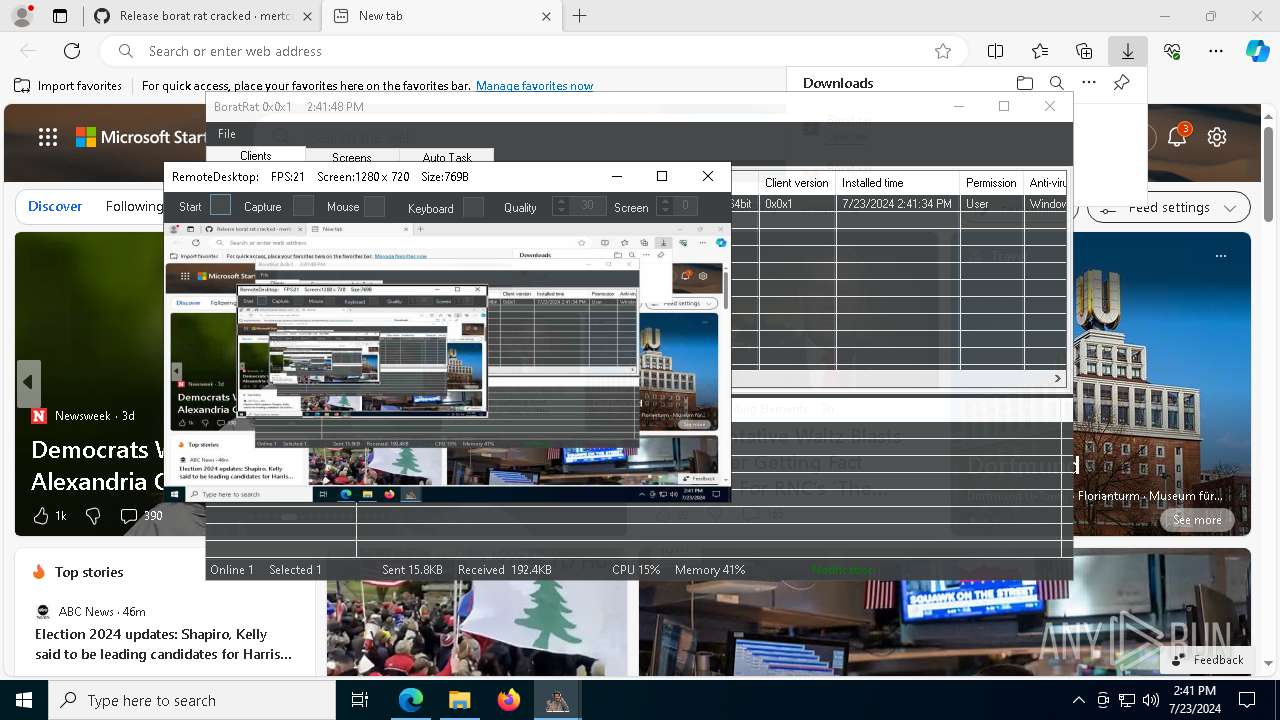
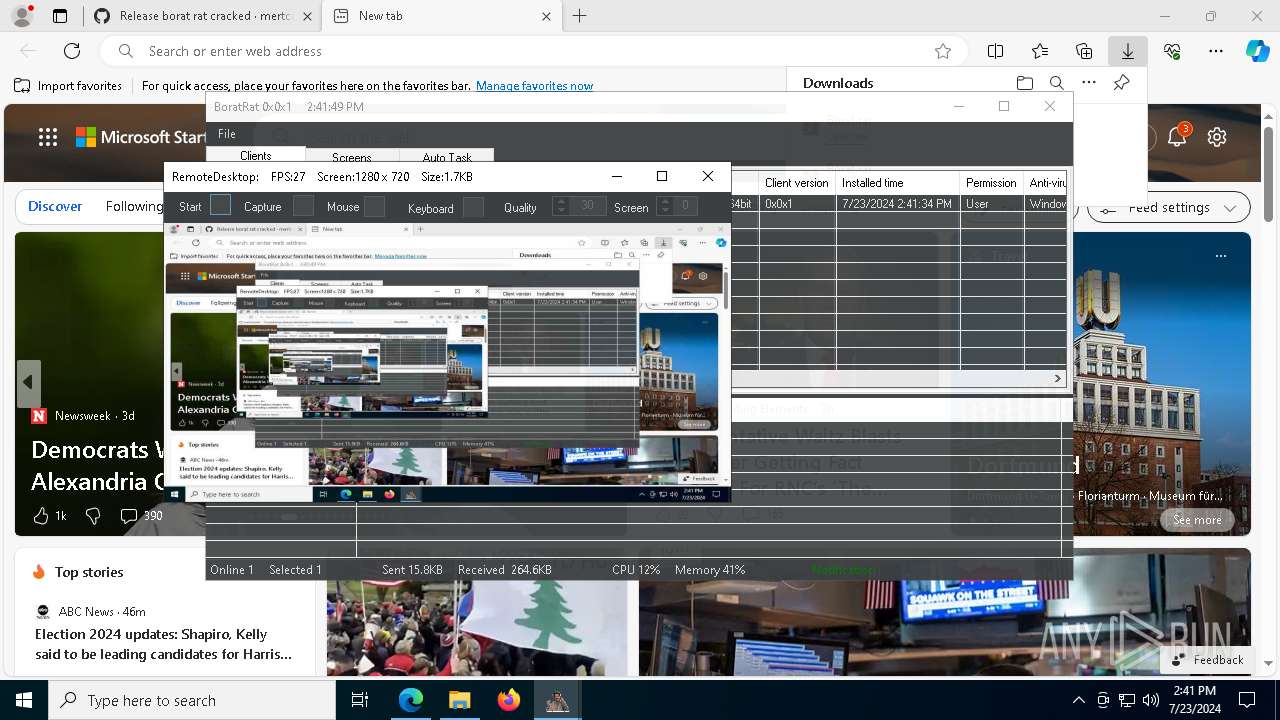
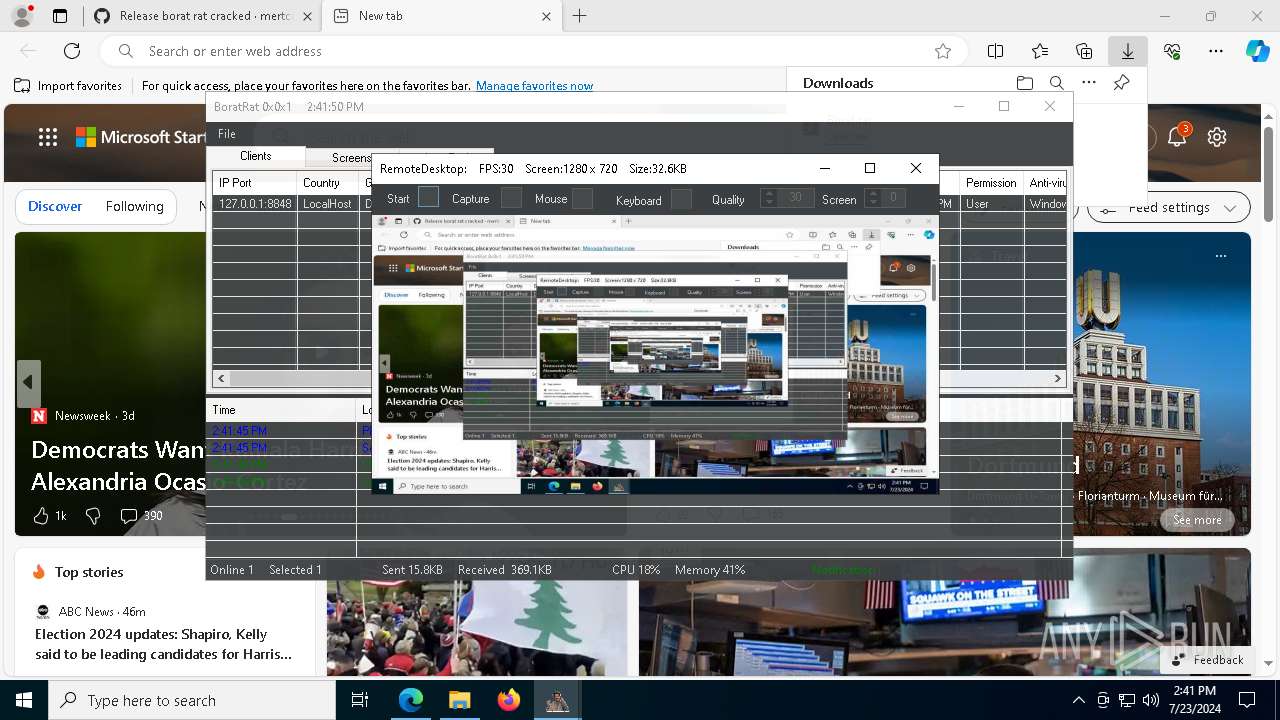
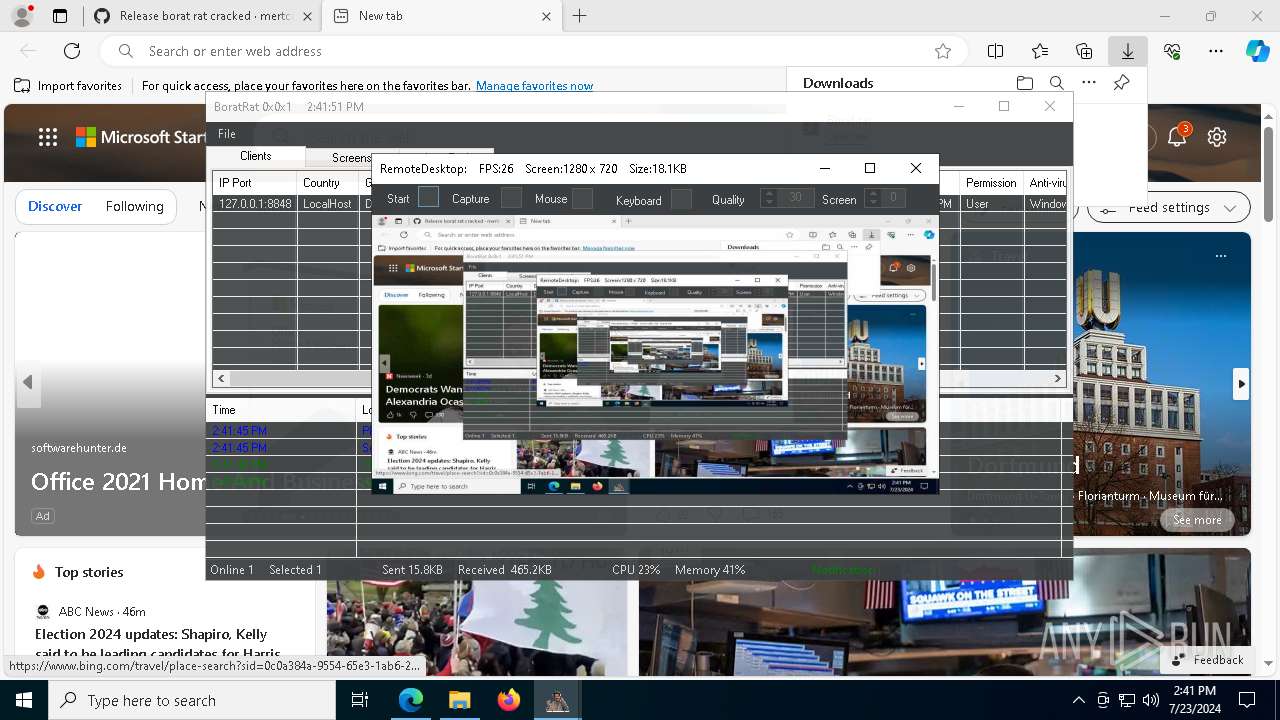
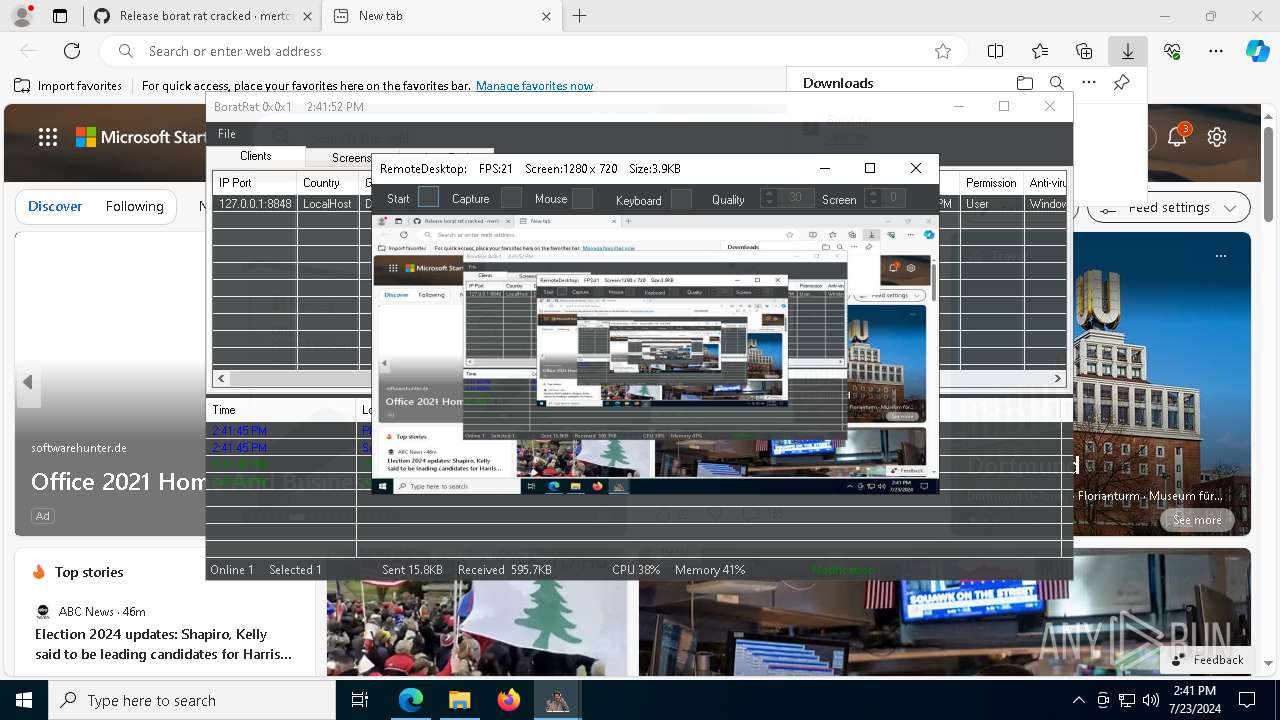
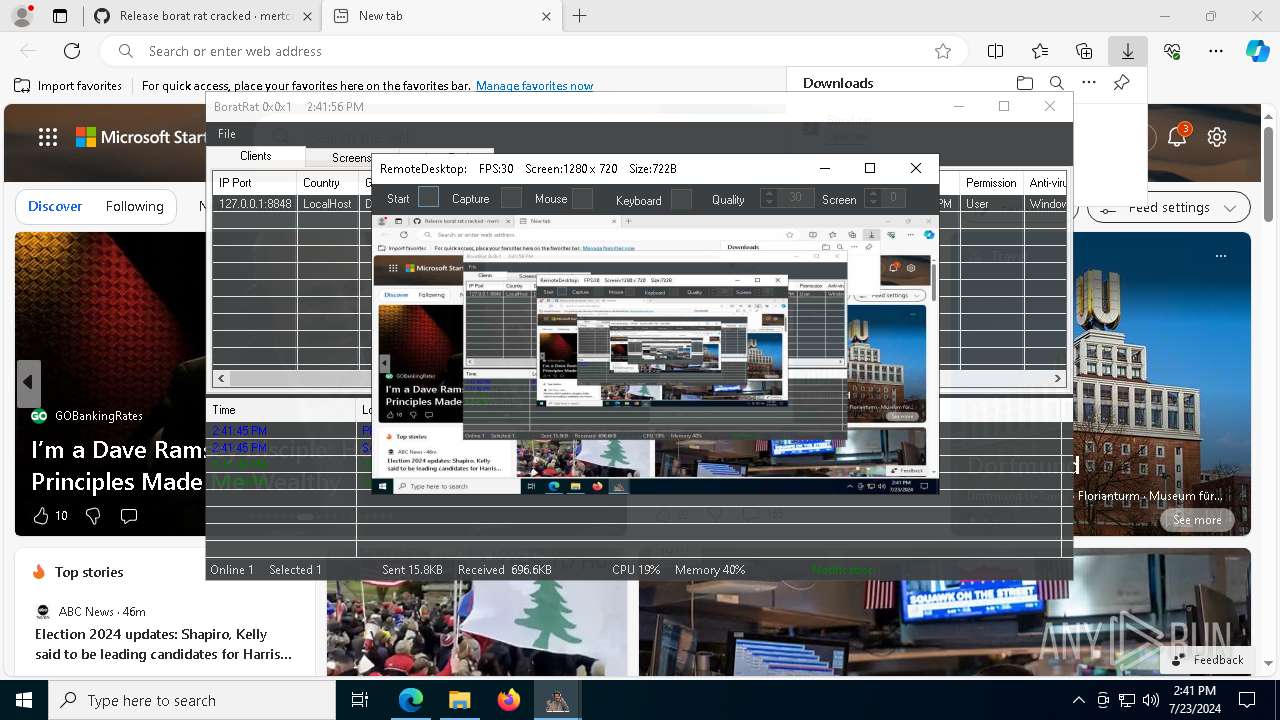
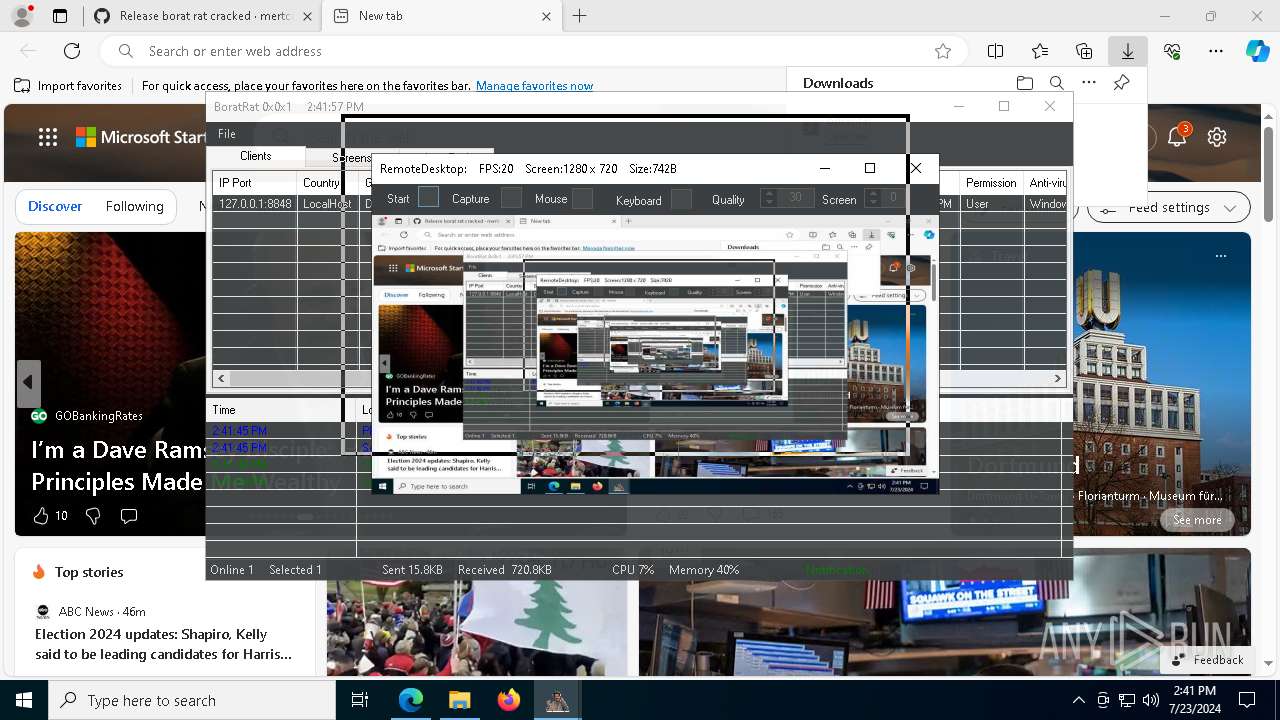
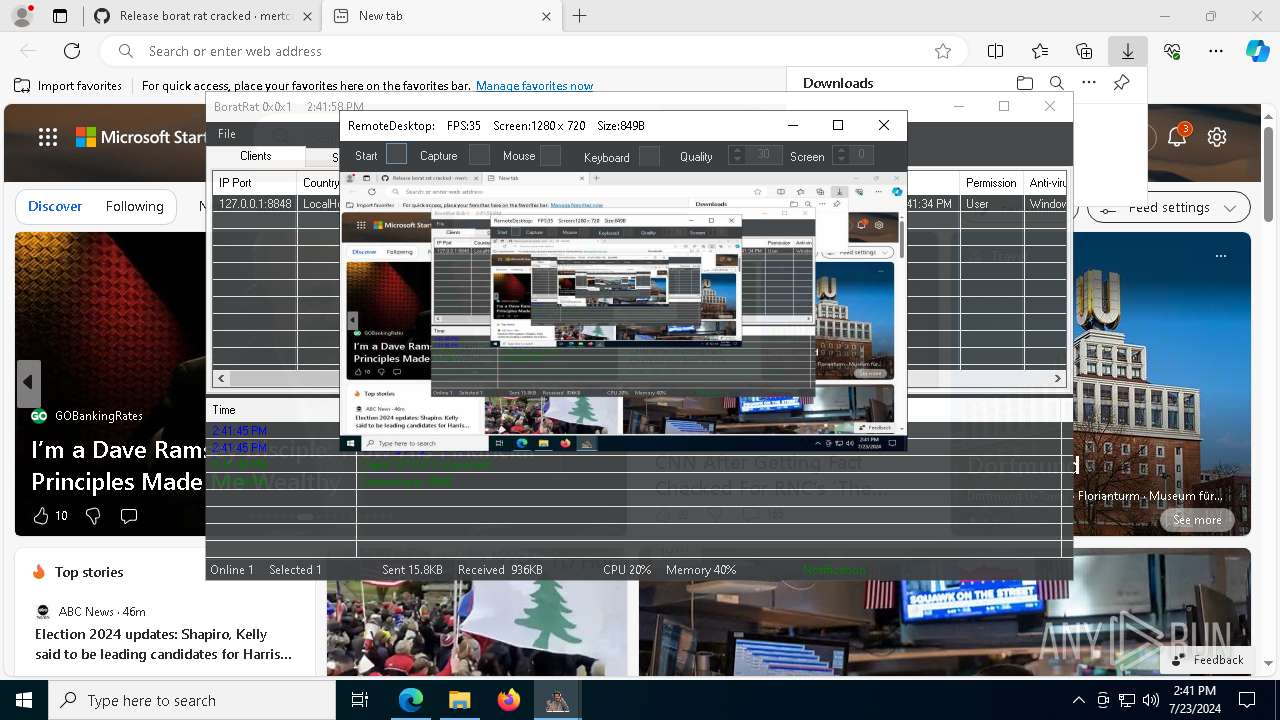
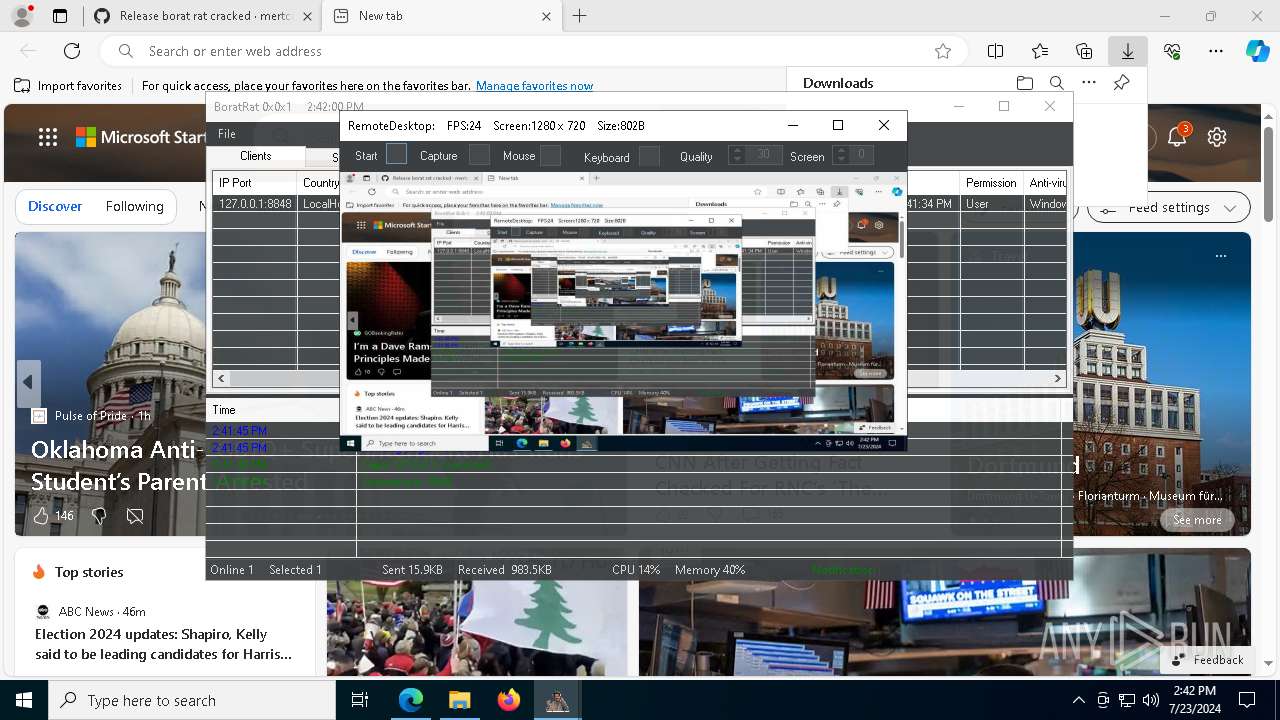
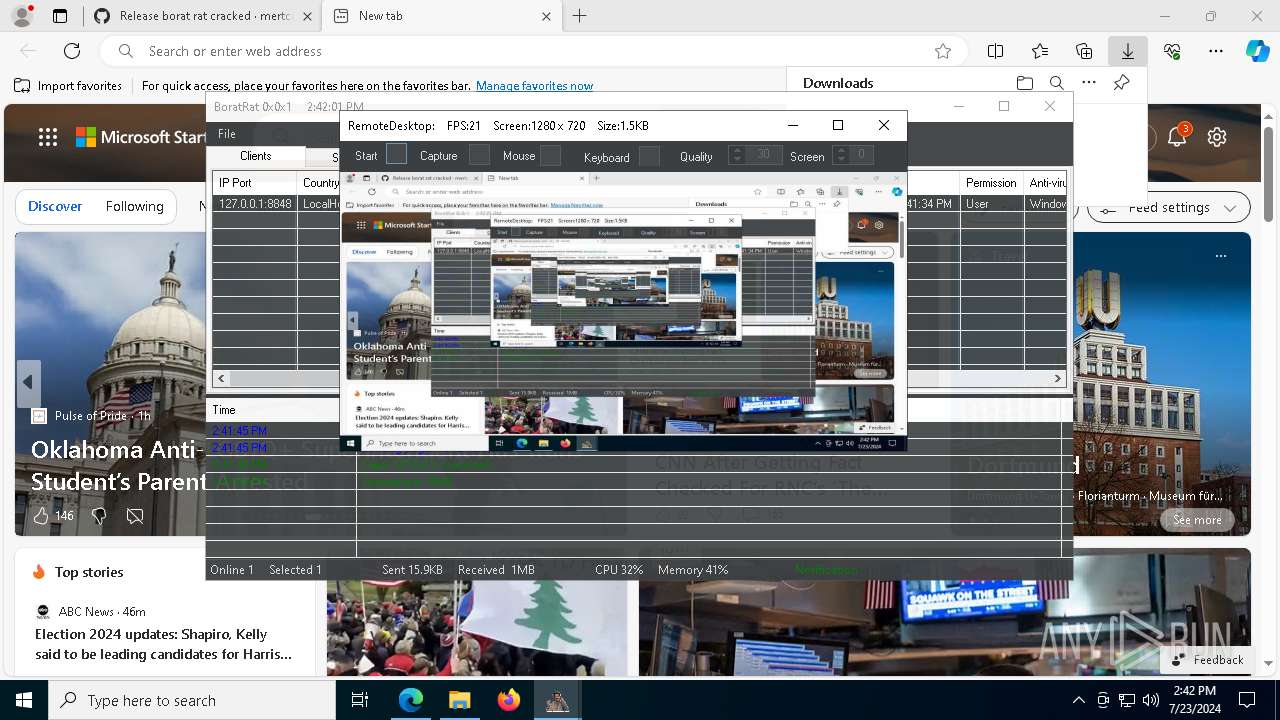
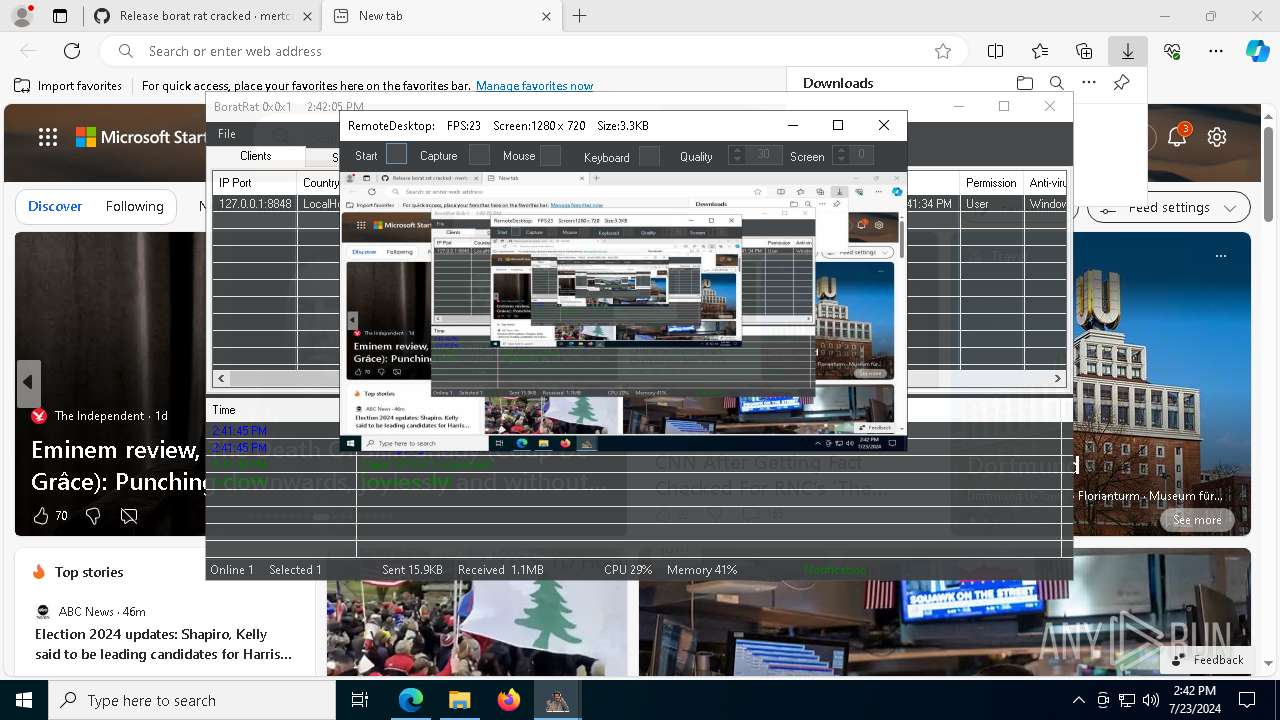
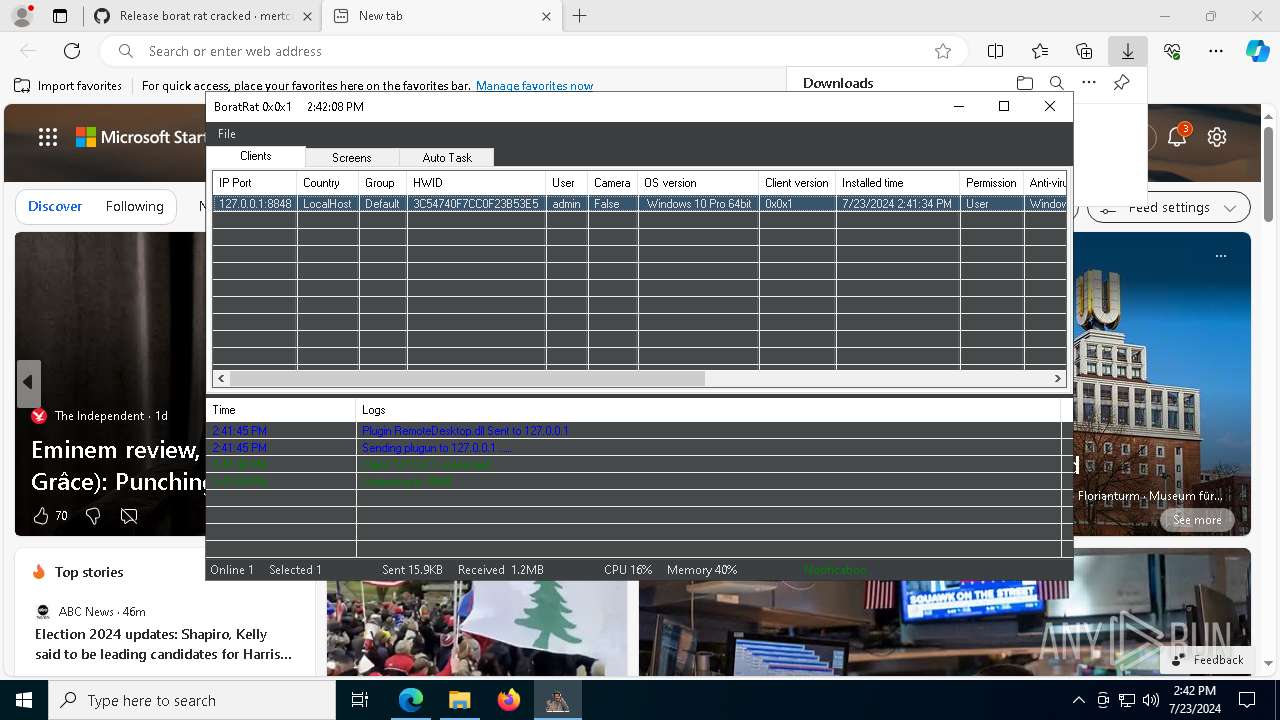
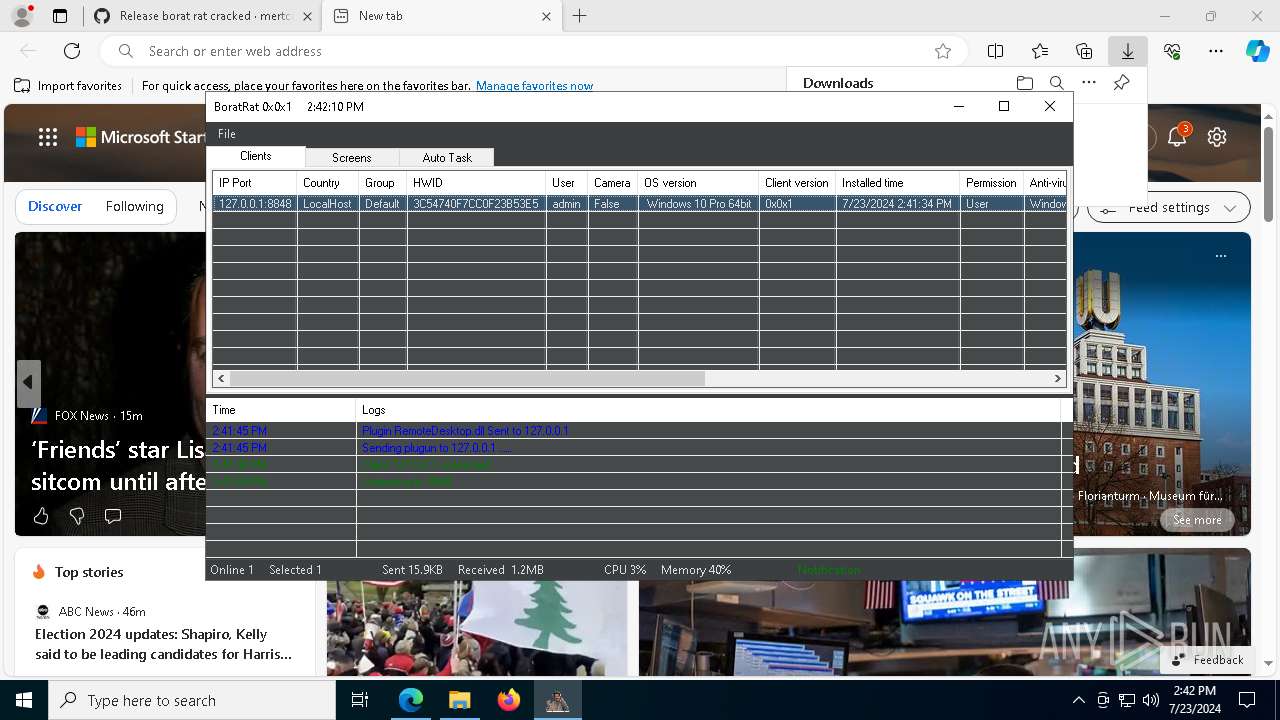
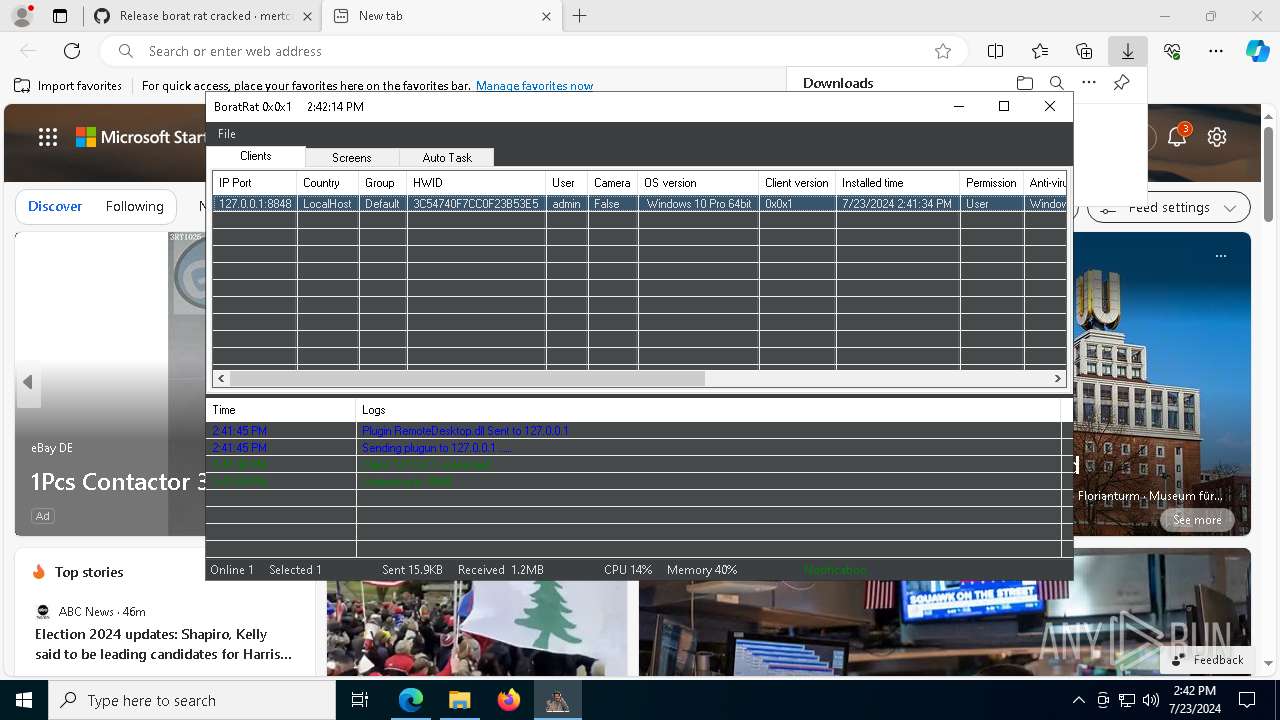
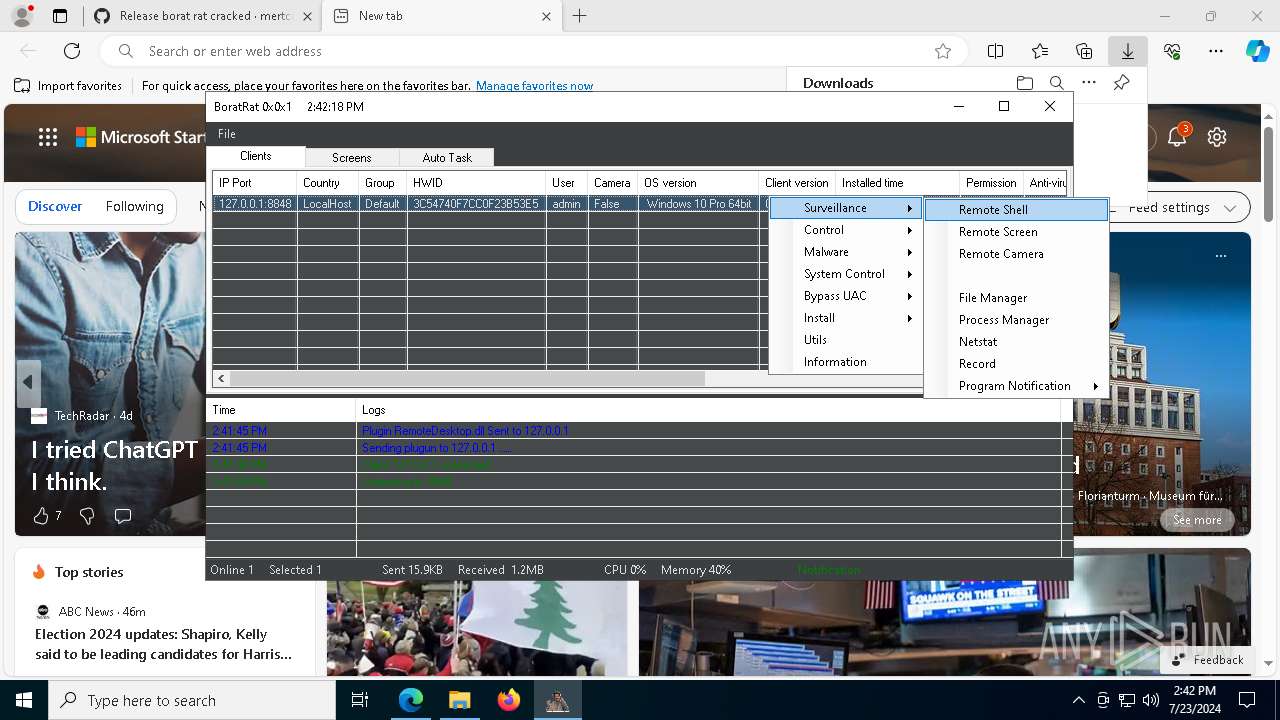
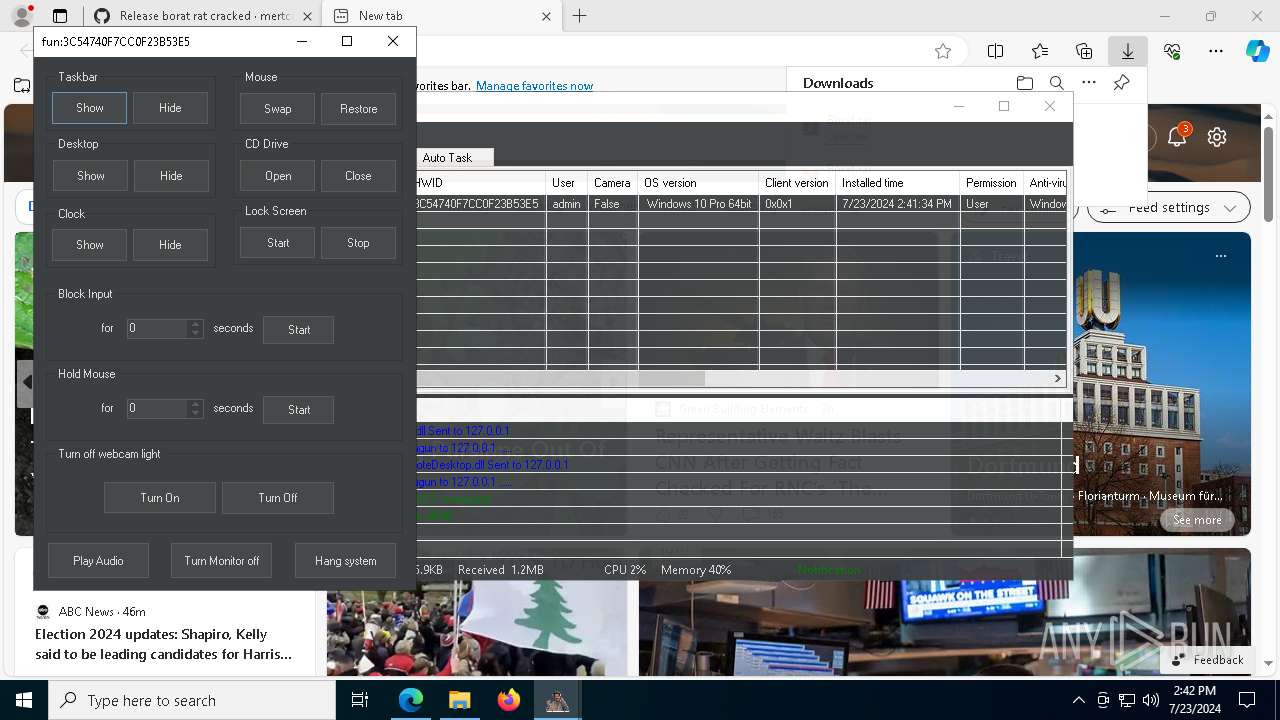
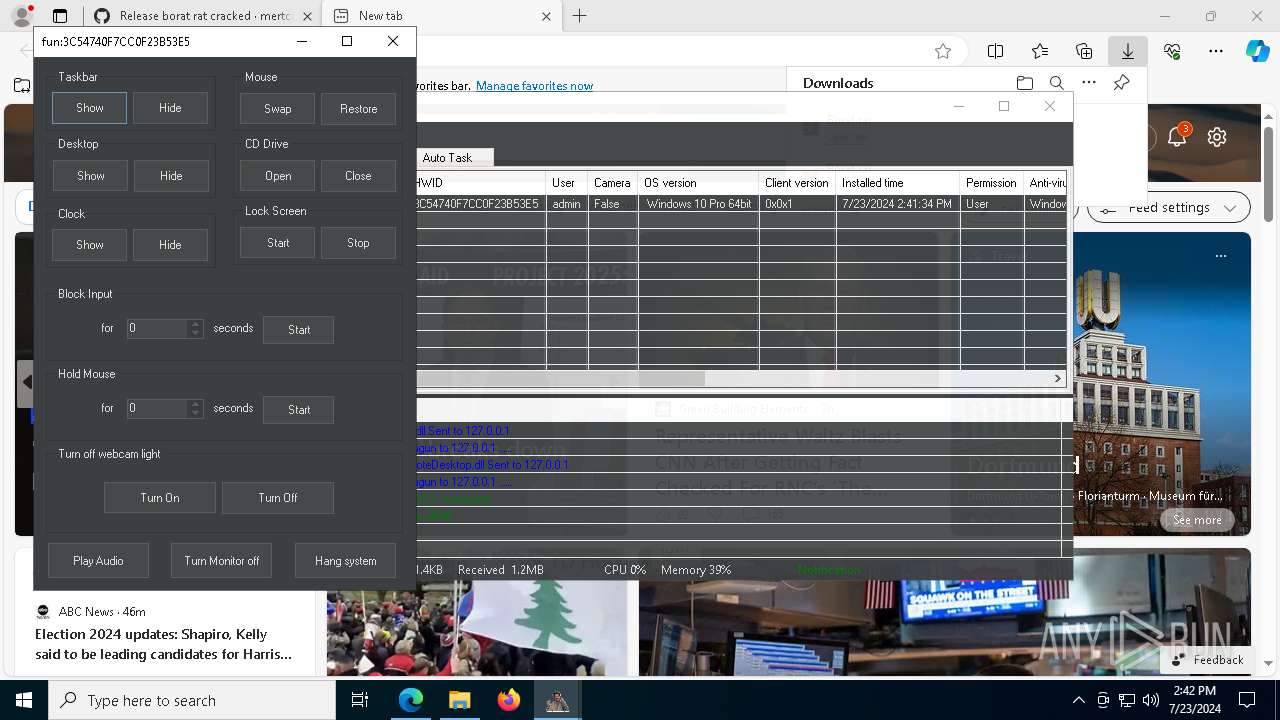
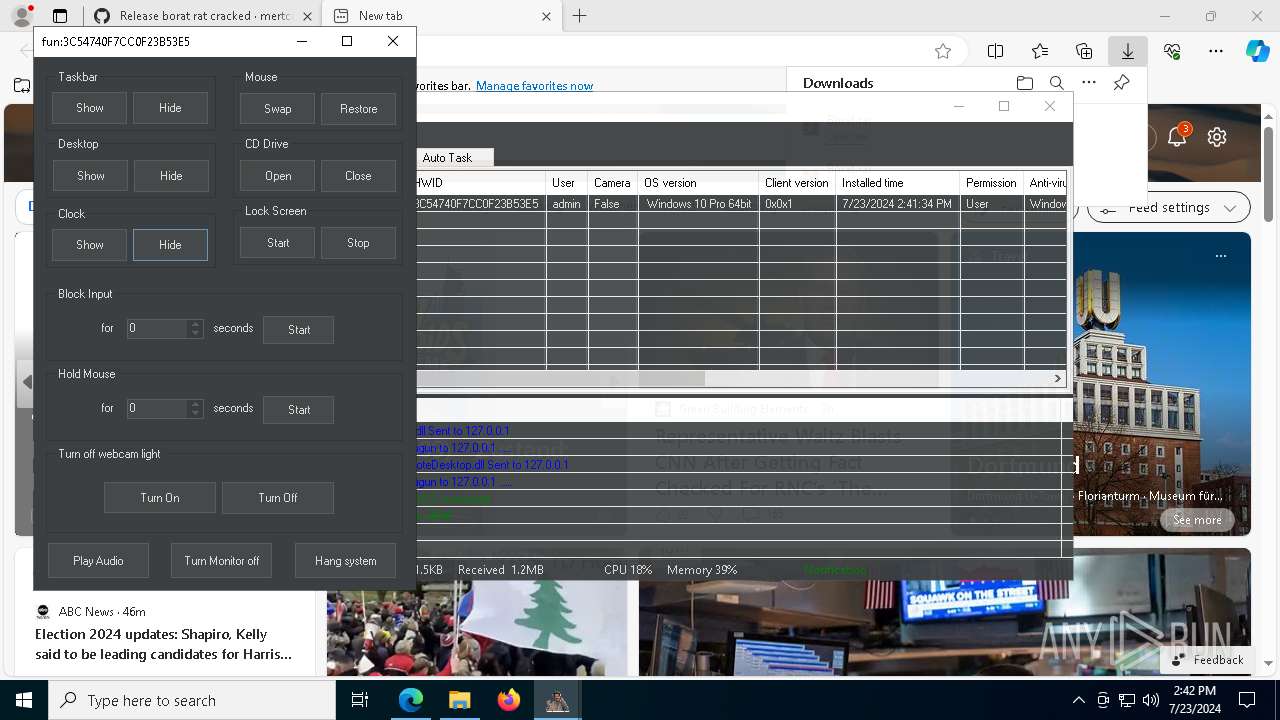
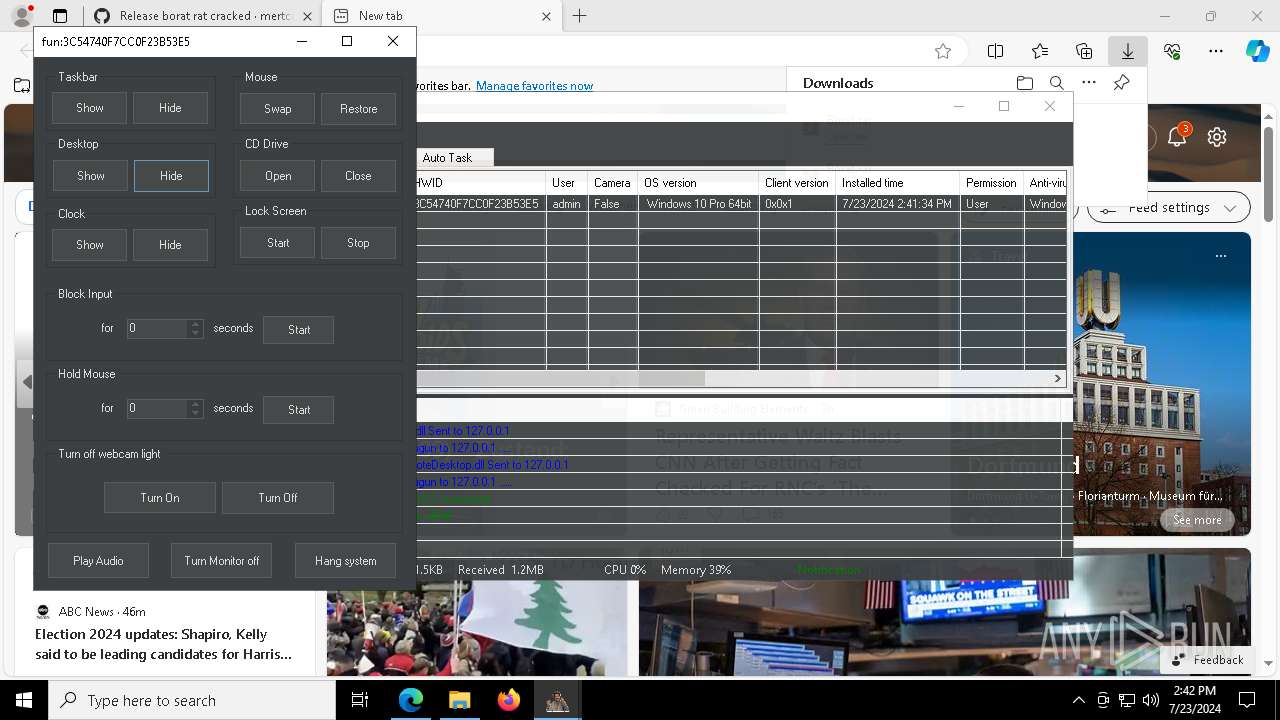
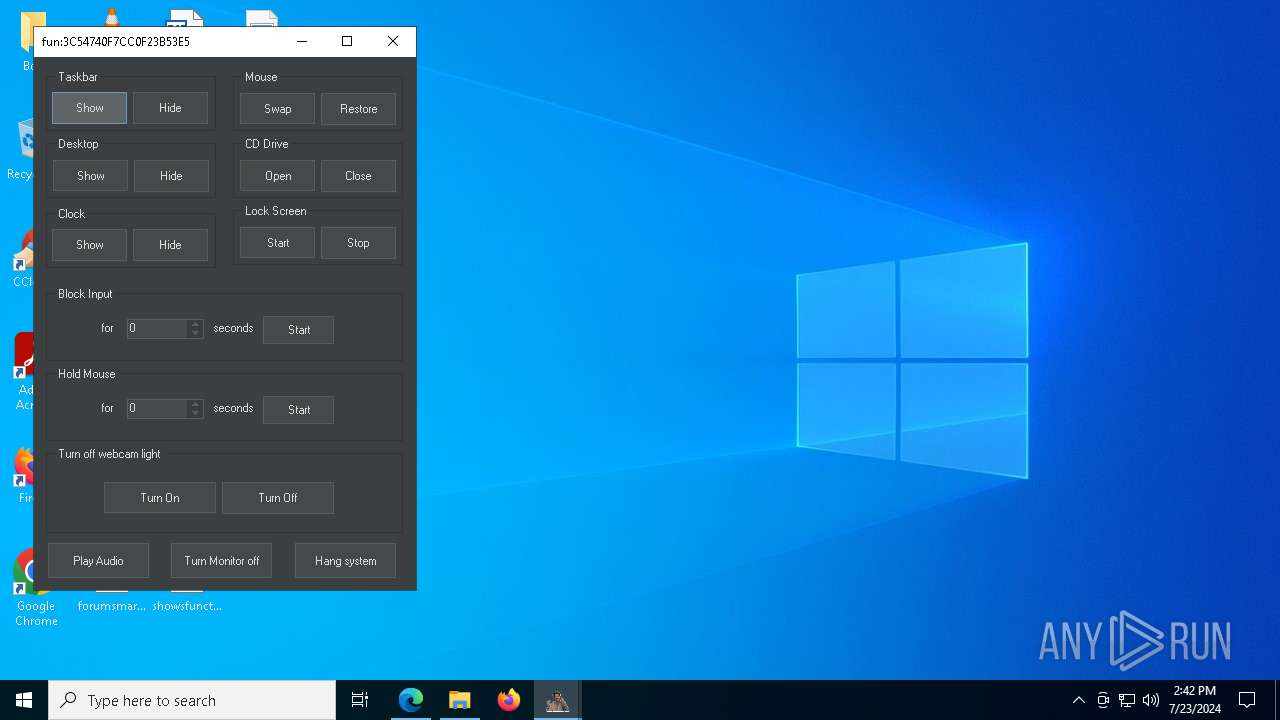
AsyncRat
(PID) Process(7408) test.exe
C2 (1)127.0.0.1
Ports (1)8848
Version0x0x1
Options
AutoRuntrue
MutexBoratRatMutex_Sa8XOfH1BudX
InstallFolder%AppData%
Certificates
Cert1MIICPTCCAaagAwIBAgIVAOBn4LGl7BufH3AY6NsdG2+okhltMA0GCSqGSIb3DQEBDQUAMG4xGDAWBgNVBAMMD0JvcmF0UmF0IFNlcnZlcjEVMBMGA1UECwwMU2E4WE9mSDFCdWRYMSEwHwYDVQQKDBhCb3JhdFJhdCBCeSBTYThYT2ZIMUJ1ZFgxCzAJBgNVBAcMAlNIMQswCQYDVQQGEwJDTjAeFw0yMTExMjMxNzQyNTFaFw0zMjA5MDExNzQyNTFaMBMxETAPBgNVBAMMCEJvcmF0UmF0MIGfMA0GCSqG...
Server_SignatureZglttBxpXgPTGs4IU05Qf8CLGpYls9nxXKoXE4TasRc3A6qOnd9XyYKi5xZYWe2OY4FBVa308Vl1v8Itaqo4Hyj8xNe6Xn3nHkXj/Ktxij3xTNedS3TjzdqZXMi+inqmIrRB2w6IKUshvP4xhVDkRHGZq4Eleec5nkauywvGtf0=
Keys
AESbf6f7ae5e824186106dfc97078b38a8ba6b52ddca5a86f765a9efd0d42d732eb
SaltBor@tRAT584
Total processes
187
Monitored processes
48
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 364 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x300,0x304,0x308,0x2f8,0x310,0x7ffeffd55fd8,0x7ffeffd55fe4,0x7ffeffd55ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 396 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1048 | timeout 3 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1956 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5684 --field-trial-handle=2368,i,4617898906037392129,6504853660643658942,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2096 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\tmpAA8F.tmp.bat"" | C:\Windows\System32\cmd.exe | — | Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3068 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=4132 --field-trial-handle=2368,i,4617898906037392129,6504853660643658942,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3112 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3140 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://github.com/mertcuan/borat-rat/releases/tag/borat" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3204 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7372 --field-trial-handle=2368,i,4617898906037392129,6504853660643658942,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
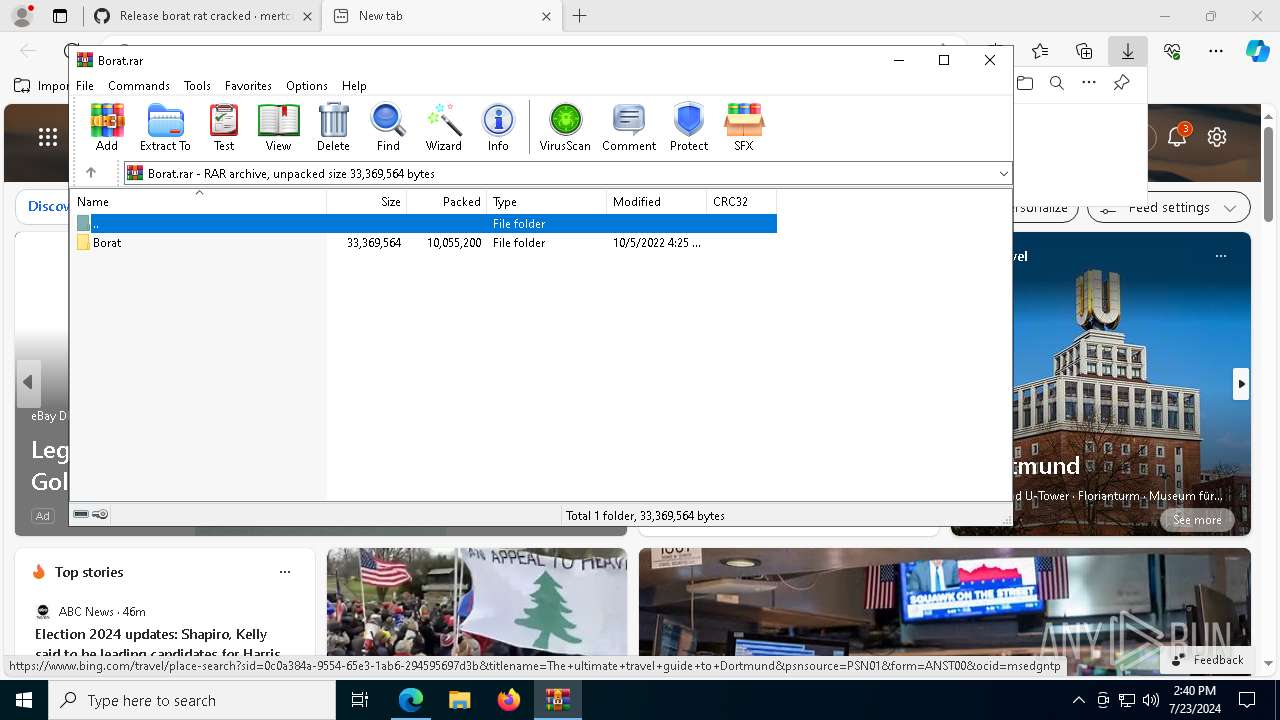
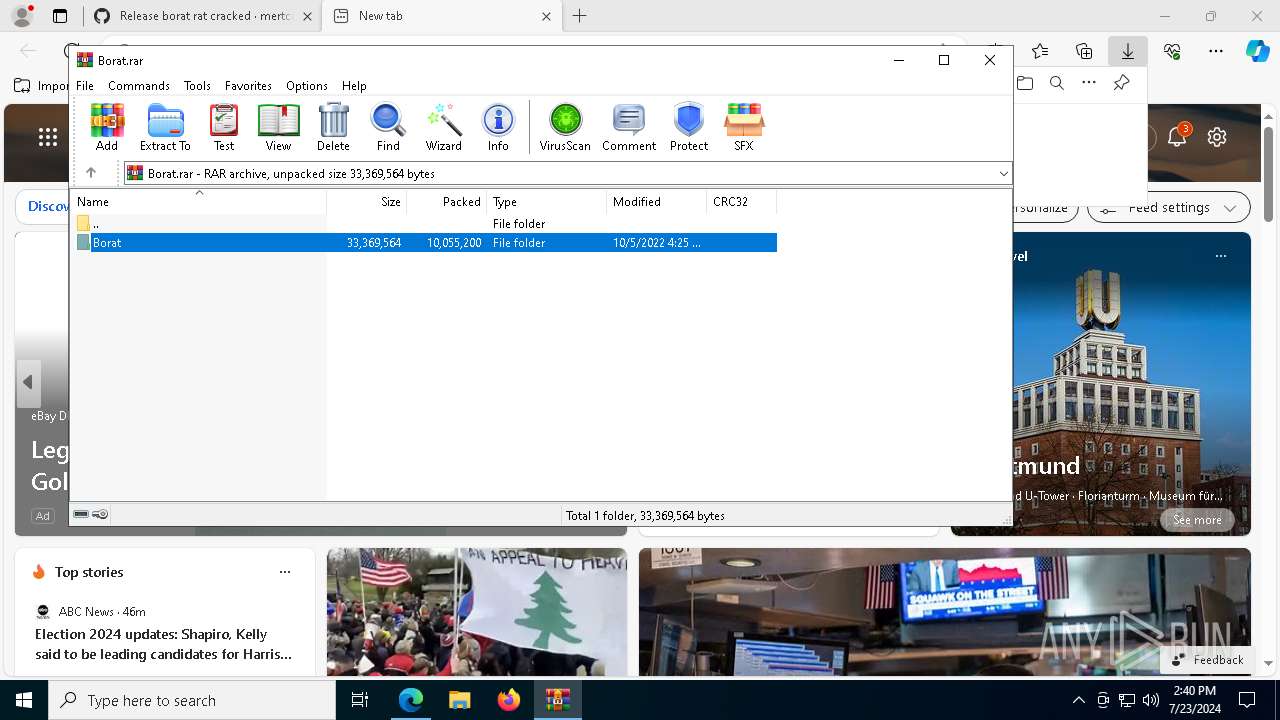
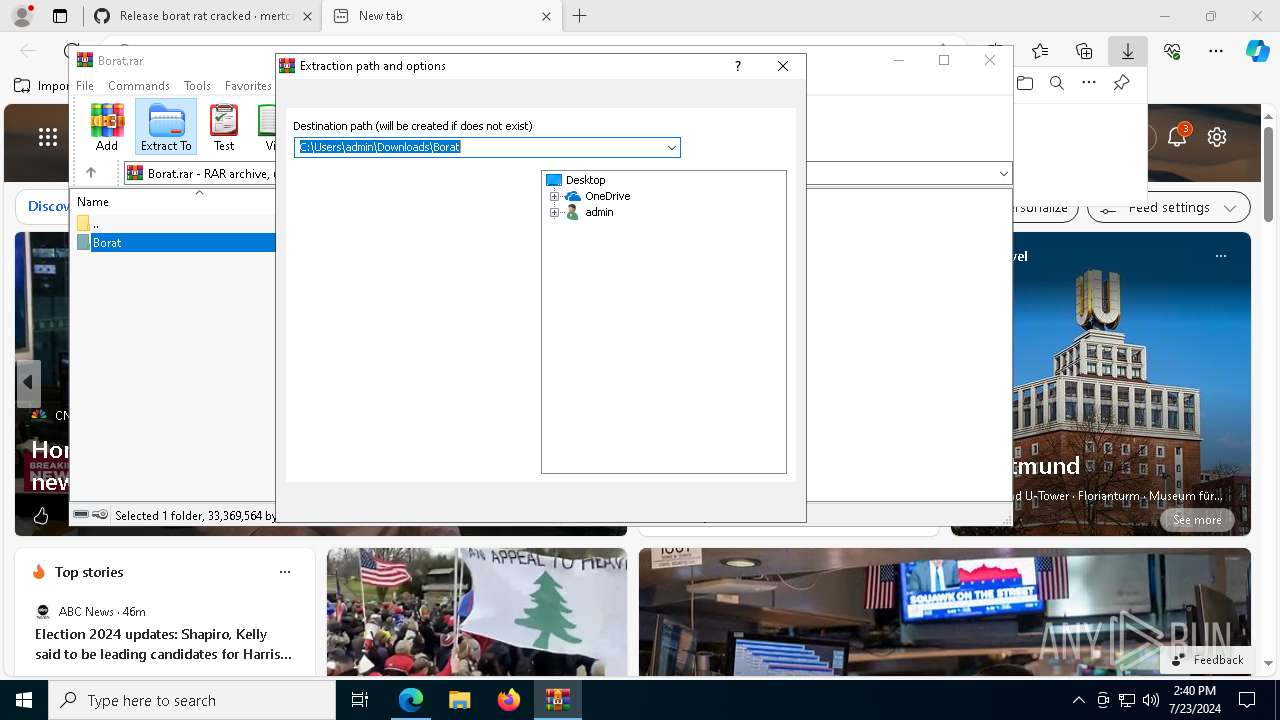
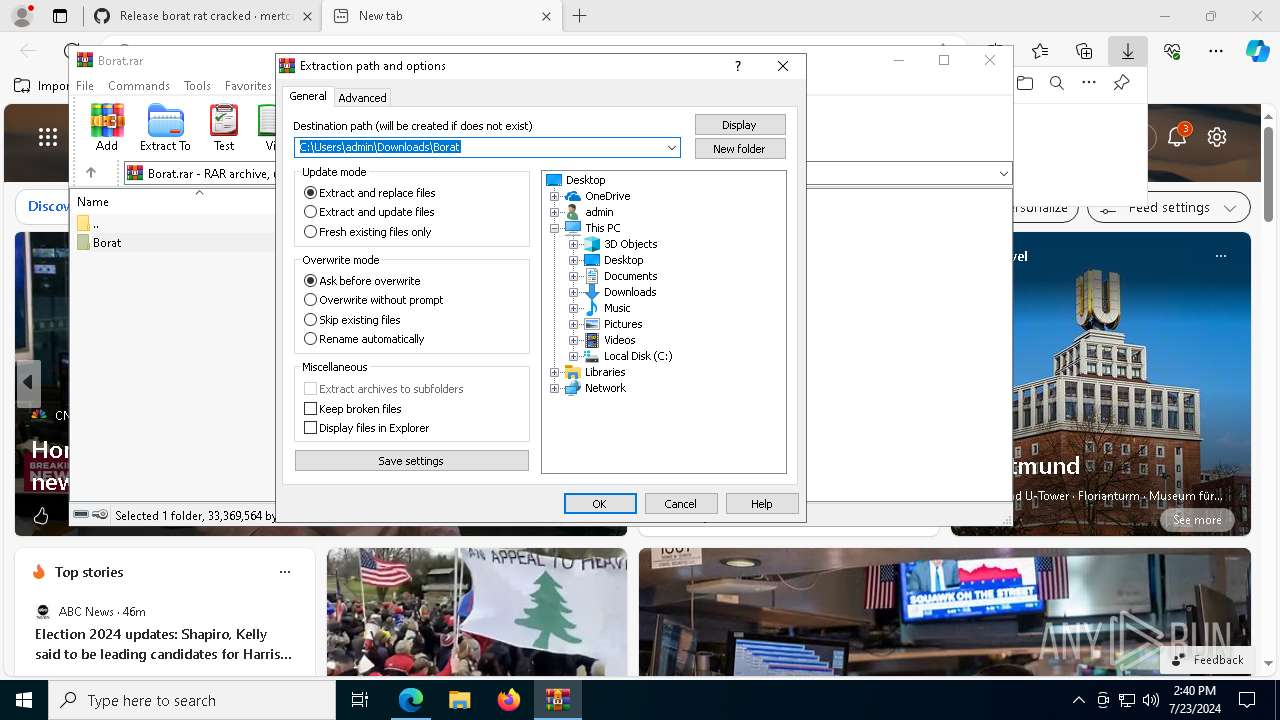
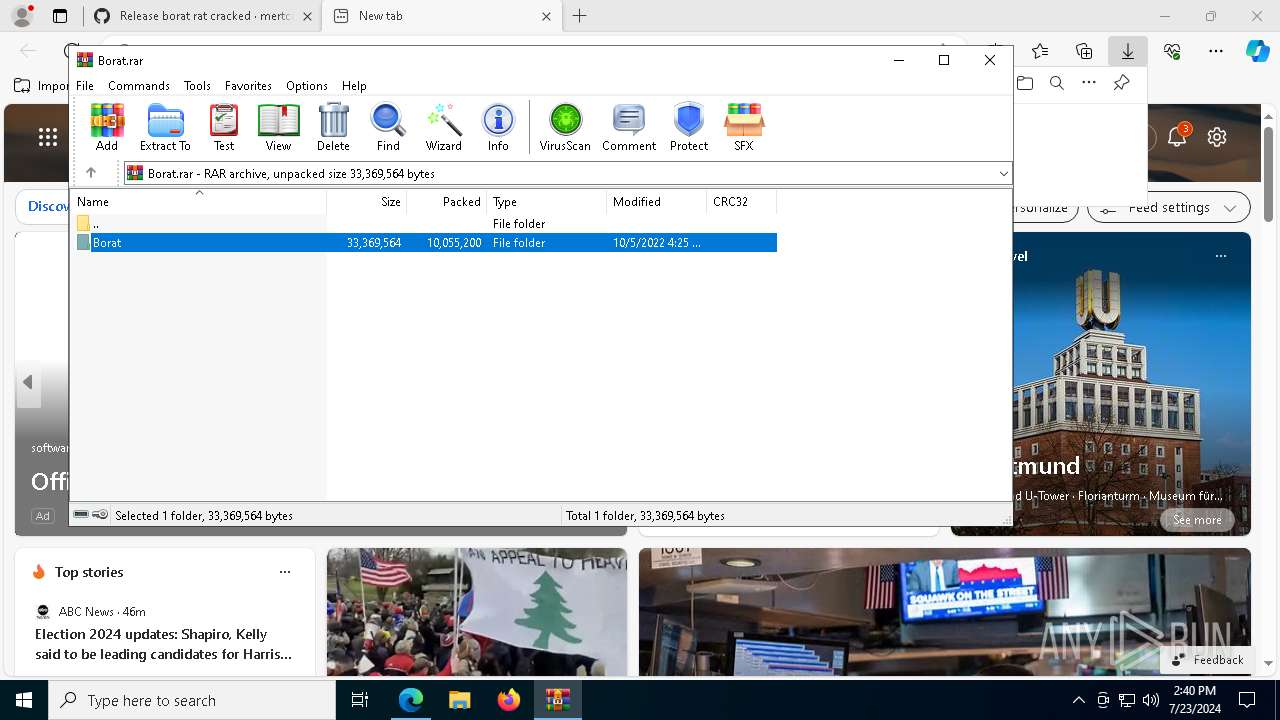
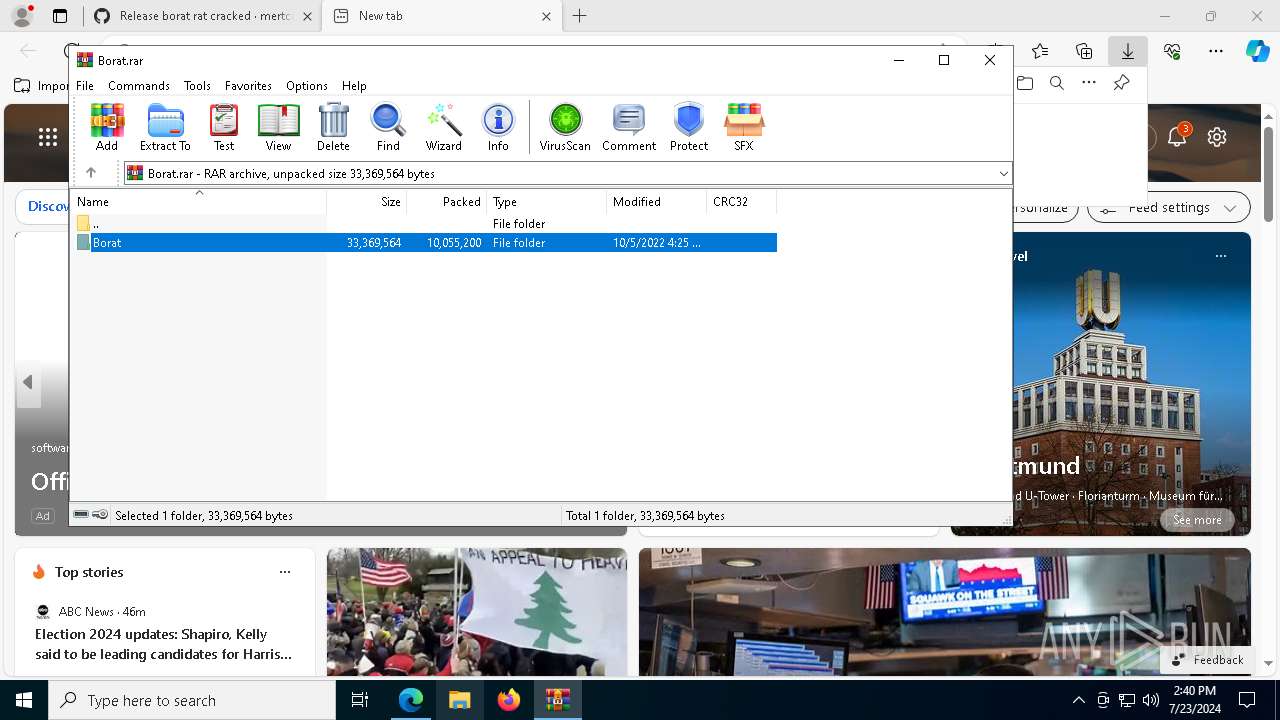
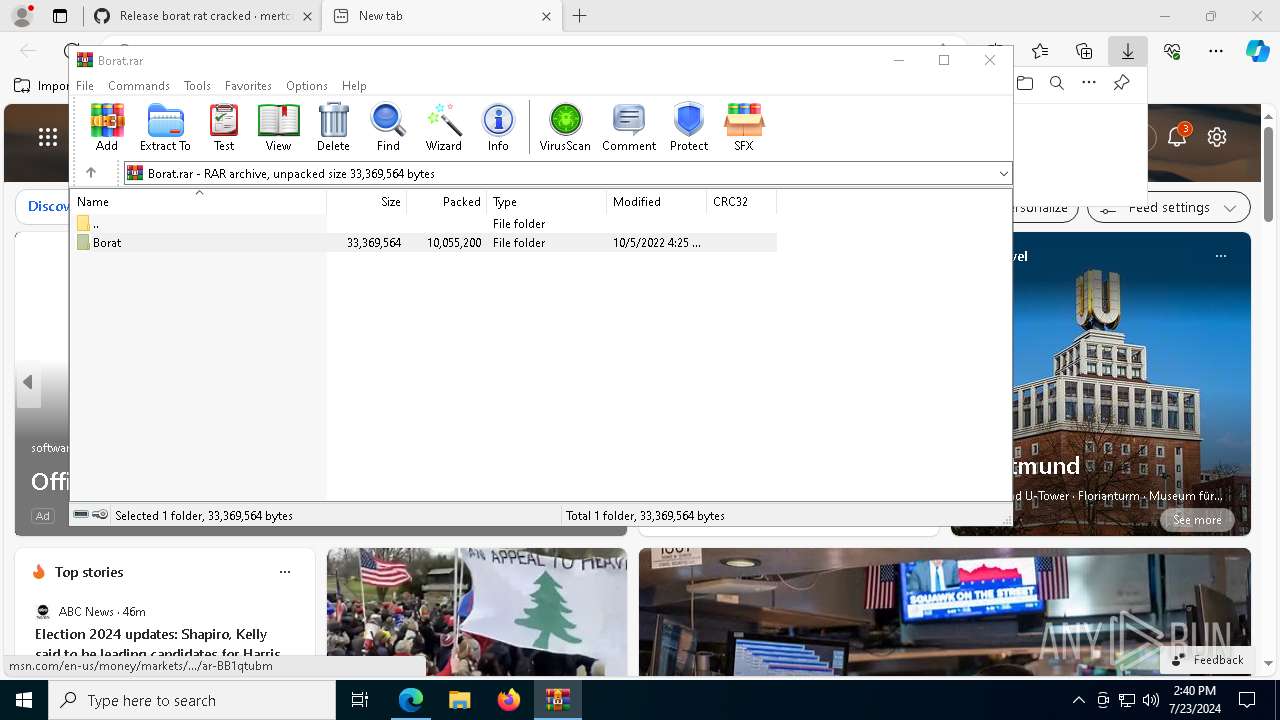
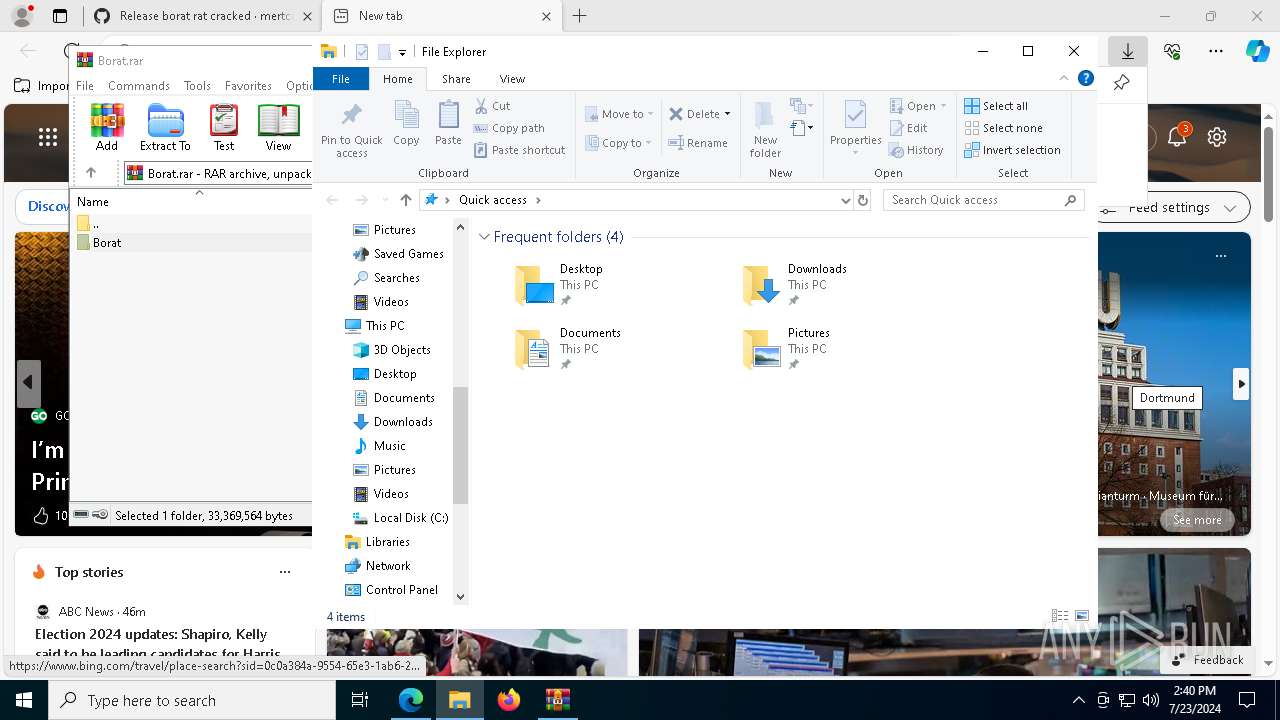
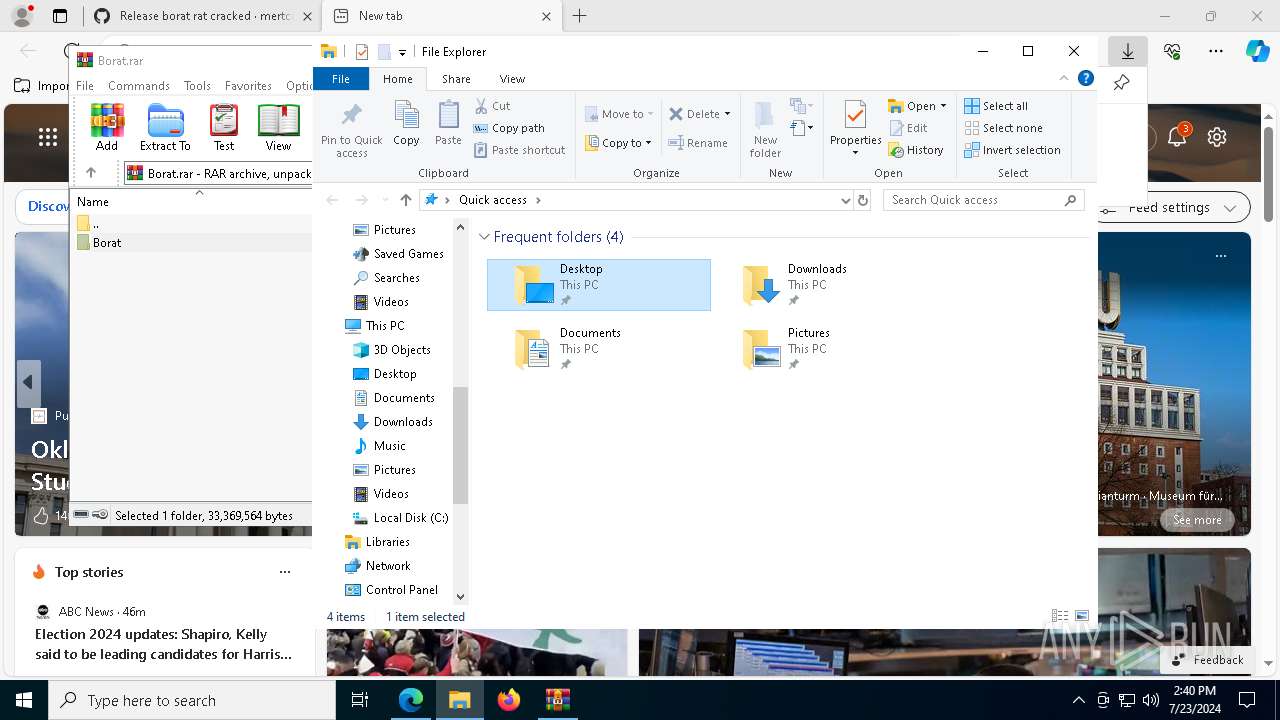
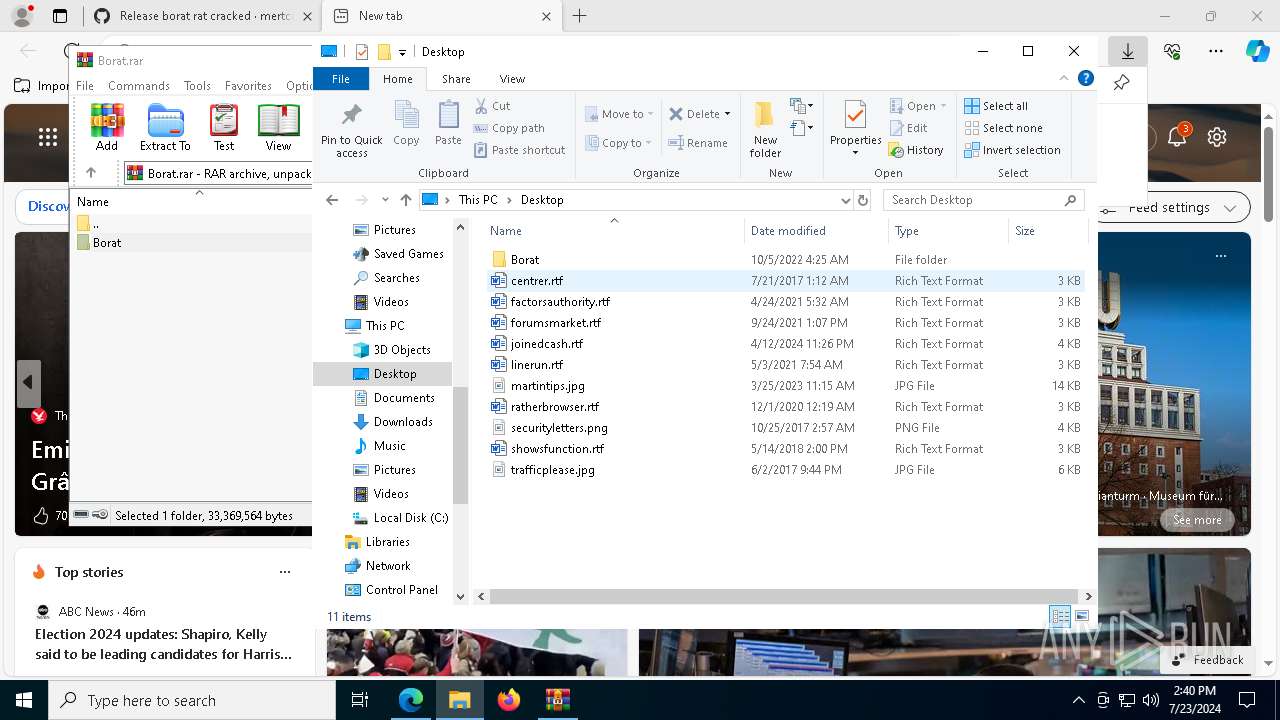
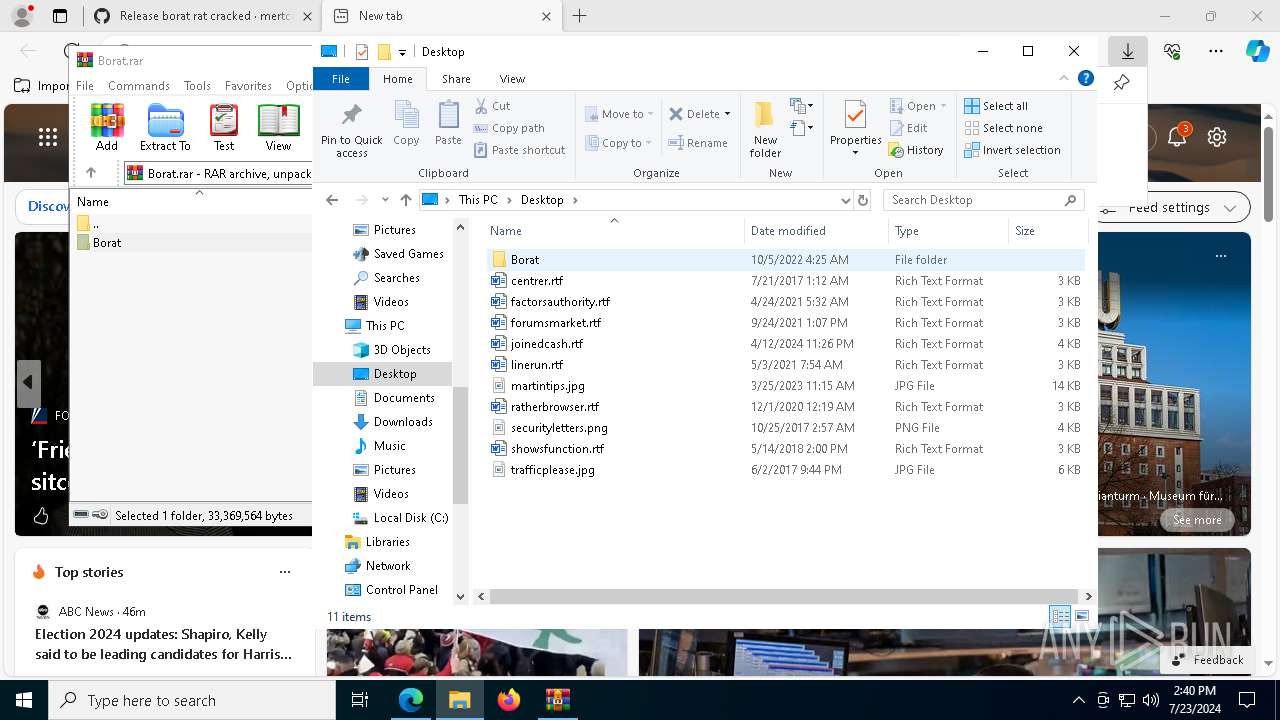
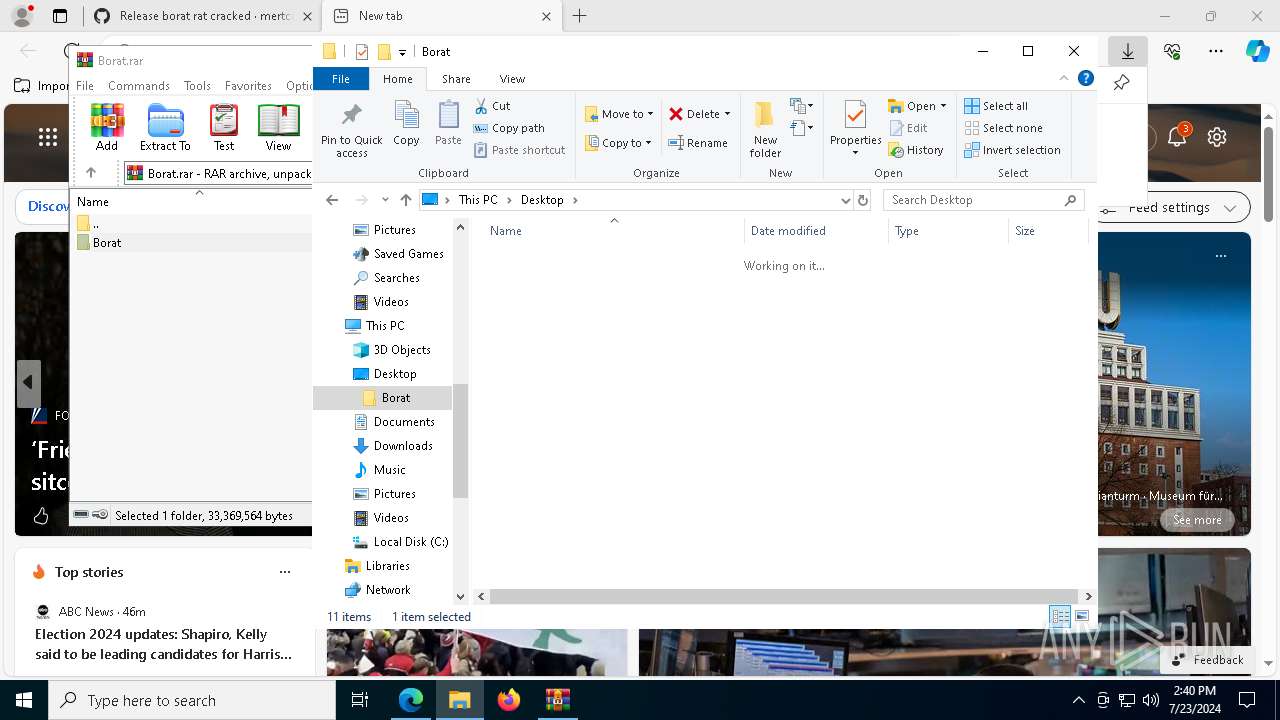
| 4116 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Borat.rar" | C:\Program Files\WinRAR\WinRAR.exe | msedge.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
31 974
Read events
31 823
Write events
144
Delete events
7
Modification events
| (PID) Process: | (3140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (3140) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3140) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
25
Suspicious files
371
Text files
126
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe1180.TMP | — | |
MD5:— | SHA256:— | |||
| 3140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFe1190.TMP | — | |
MD5:— | SHA256:— | |||
| 3140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFe1190.TMP | — | |
MD5:— | SHA256:— | |||
| 3140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFe11ed.TMP | — | |
MD5:— | SHA256:— | |||
| 3140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFe11ed.TMP | — | |
MD5:— | SHA256:— | |||
| 3140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
140
DNS requests
145
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6916 | msedge.exe | GET | 304 | 184.24.77.47:80 | http://apps.identrust.com/roots/dstrootcax3.p7c | unknown | — | — | whitelisted |
6916 | msedge.exe | GET | 304 | 69.192.161.44:80 | http://r3.i.lencr.org/ | unknown | — | — | whitelisted |
6916 | msedge.exe | GET | 304 | 69.192.161.44:80 | http://x1.i.lencr.org/ | unknown | — | — | whitelisted |
944 | svchost.exe | GET | — | 23.48.23.54:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/07b2b28d-48a0-4636-b791-6e6129c8a3da?P1=1722296909&P2=404&P3=2&P4=HeZnwbU4F%2b9xdHQXY%2bqivw9f2%2fp%2fJ165RvzDIgv6TY4vgeUwK%2fa6JbFbSVuyffzmWSKousmuQ7iL4xcFc%2bhR9g%3d%3d | unknown | — | — | whitelisted |
944 | svchost.exe | HEAD | 200 | 23.48.23.54:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/07b2b28d-48a0-4636-b791-6e6129c8a3da?P1=1722296909&P2=404&P3=2&P4=HeZnwbU4F%2b9xdHQXY%2bqivw9f2%2fp%2fJ165RvzDIgv6TY4vgeUwK%2fa6JbFbSVuyffzmWSKousmuQ7iL4xcFc%2bhR9g%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6012 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4516 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3380 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 184.86.251.10:443 | — | Akamai International B.V. | DE | unknown |
4204 | svchost.exe | 4.209.33.156:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
3140 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6916 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6916 | msedge.exe | 140.82.121.3:443 | github.com | GITHUB | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| shared |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6916 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
6916 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |