| URL: | https://dnp.motorhinoafrica.com/b#bnBkL3VvYndiQWhvanVvdnBkZGIwenNFNXpZMkoxW1Bybkt4WDM2VU5lU0ZJNjZRVkh6Y21jb2RbaTl1Sm1xOG17NlV5W3N1T29GczN3MzJlVmg5Z3JPcjFWa3dnSTl5bHcxSlh0Q01oN0NPd3ZbRnZqU2xUSk53UGpmZmVwakdudm0zT01DbXdXZHZVcWRraEdxUGtxcFgxdlA4WkxpWllEa3lSVUhLWllaUmRLUUVnSmR7OlBEVURmcW9ieUhlb0dZbTN2anlwRW9EajdkMWxjUk83aExlS21TbnZtTEhRZFdCZDZoajFVN1BwZGR7UzVHOTZOTW9RQzF1UFZmUkJQazNMRWhjc1I4U3ZKSGVNTER5enBndDhiZllGUmgzTEl1dUlbbzpTTzdDYmpKd09TOXZvcWhQZHRtd3Z0aGVKWzZSOEZ2WGJmMjhUZlJJRFc1NGpzY2N2cFdpRkQxWURYWU41WlY2Rk50Q2JMZWVORUJLeXZSW3ZGT21XRjhLbUI5TUZyRWlXY1RZaEh6d1dbMnNaRGRaVmpGSmxMNXpmMUNTTW9KMVdCVVpTRXFZZklSdGYzWERTRFZ3V0dwVmlYRlhFSnBXMVdqczpsW0Y6U3hZVll6Znd5NVZkc1Y3S1djSTVLanRkaDU2ZUNEOnplVTNQekxOWnlHaGM2T21EbVZqW2NsTU80aThGZms0allMQnpZOU5VRVB5W3hsVDJKWnprd1JXNVsyc2ZpVnc3SmZjR0k4VzJwMmNNa2htUXlrVVhjdVU5d2JiS3JoV09NW1R2ajlndXhWRkRjNFBHMTo0YjJQSmlGeEl1ZGhOOFNbZHdSY21KTnpzcVRMT2h6NjJ0b3J7SHVZaEdXdnZwYjM3NVZNaFRxU2QyODpqMnRUWU1IZnFCUVRudTo4UWlLblV6UnNSYnNtSUJQZGtTW0N5eUk0MUxEUGh4enZNdHpFcVR2blh6WmgyV1U5R3pHRnVlU0JXYkJXbm9veElKW3VWODk5NVJXZGNiNVt2d3lqY1pJeGx3WndENnA0V2p6WURyREdXajFtUFplT0trb2xnRTdCSk51R2xSdDVZVU9mbERzRjNQM2N3Nm5nbkdxVHt3cGc2NXBIdlBXdDF7ZXpzdng4Om9adGtpWVJ6ZGMyMmc5dzF0Y0VaVWVTa3RtS056cXJPZmJxbXBJWmhzOENiWHk3Tmhza1hVRXFJM1o2RGJWTHFyeVJRNmhCY2ZWZUdTWGdvUlFzVjpobmNmM0REN3Q3Z21FVmhLSGRaR0tnNkhZbGtTMkNkYkQ5cnBnWWZISEtxSUg3WElvY00zbHdZOW9LdE5qdW1GWEw5ZEp2SjVvQmJWbDlEOjBxanB3MGZlL3dvanlmbWJpcWZkMDA7dHF1dWk= |
| Full analysis: | https://app.any.run/tasks/a555cbb4-5a0a-4459-8a70-f978bde36233 |
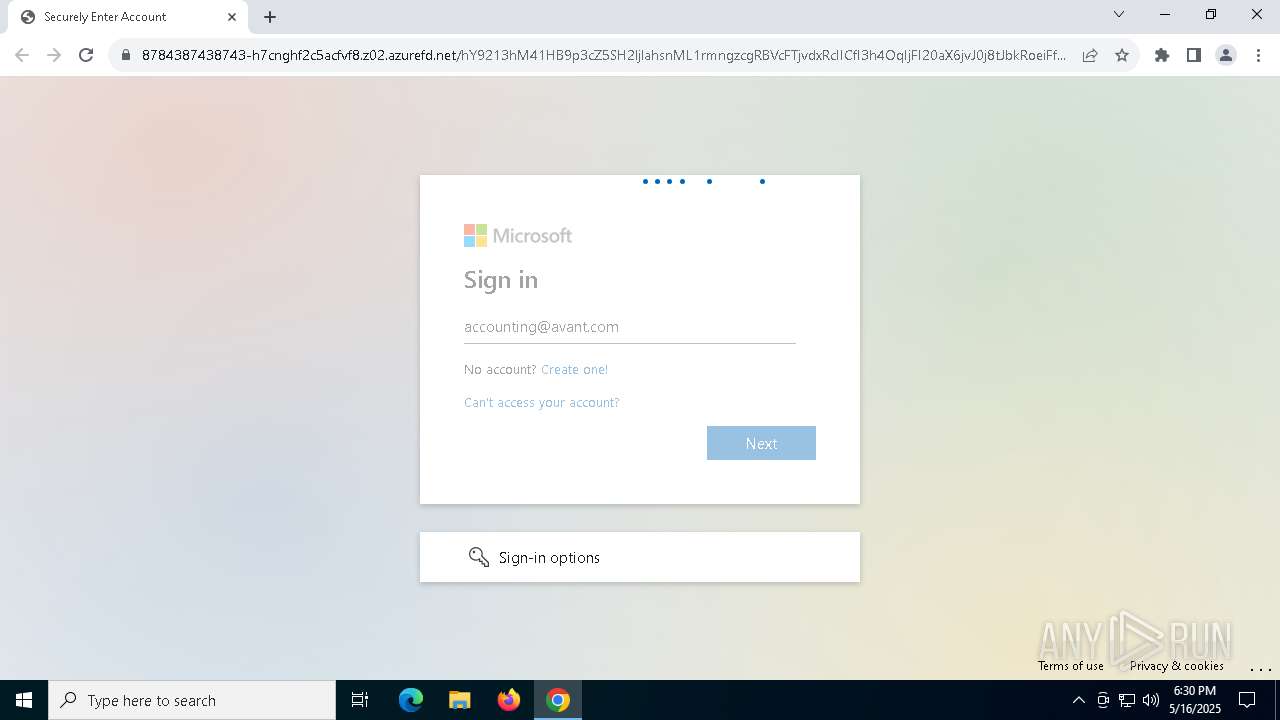
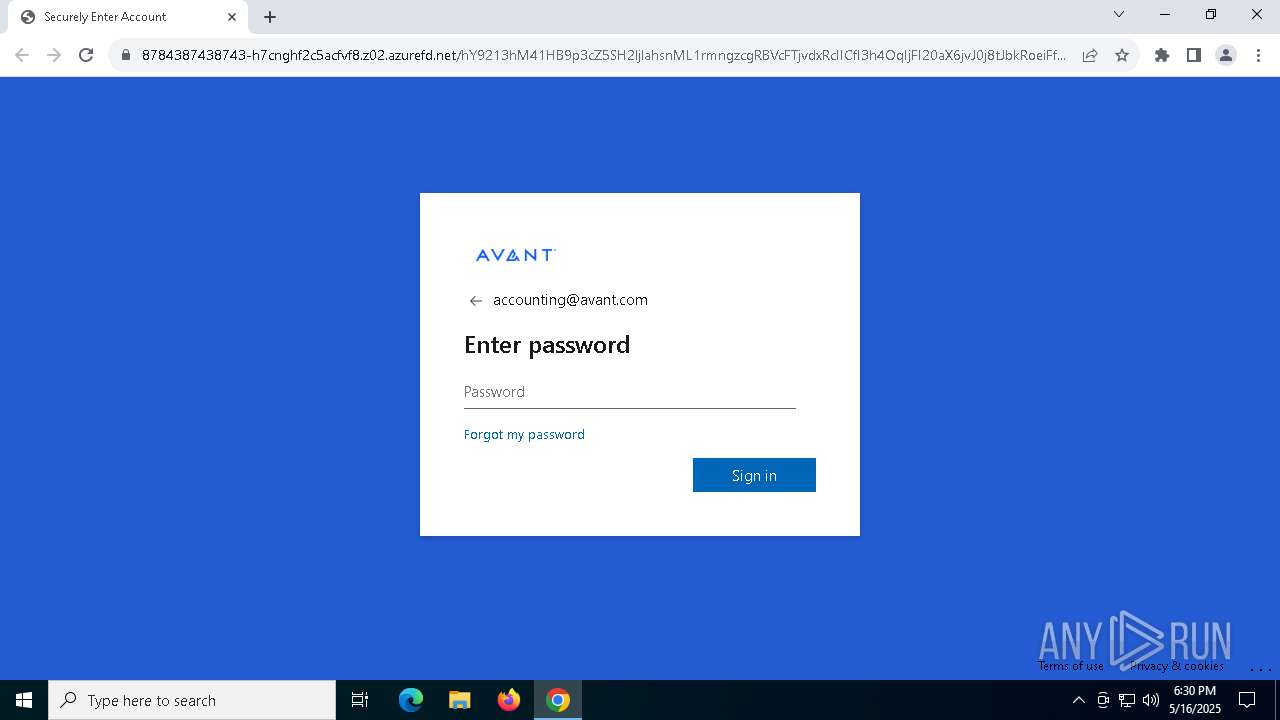
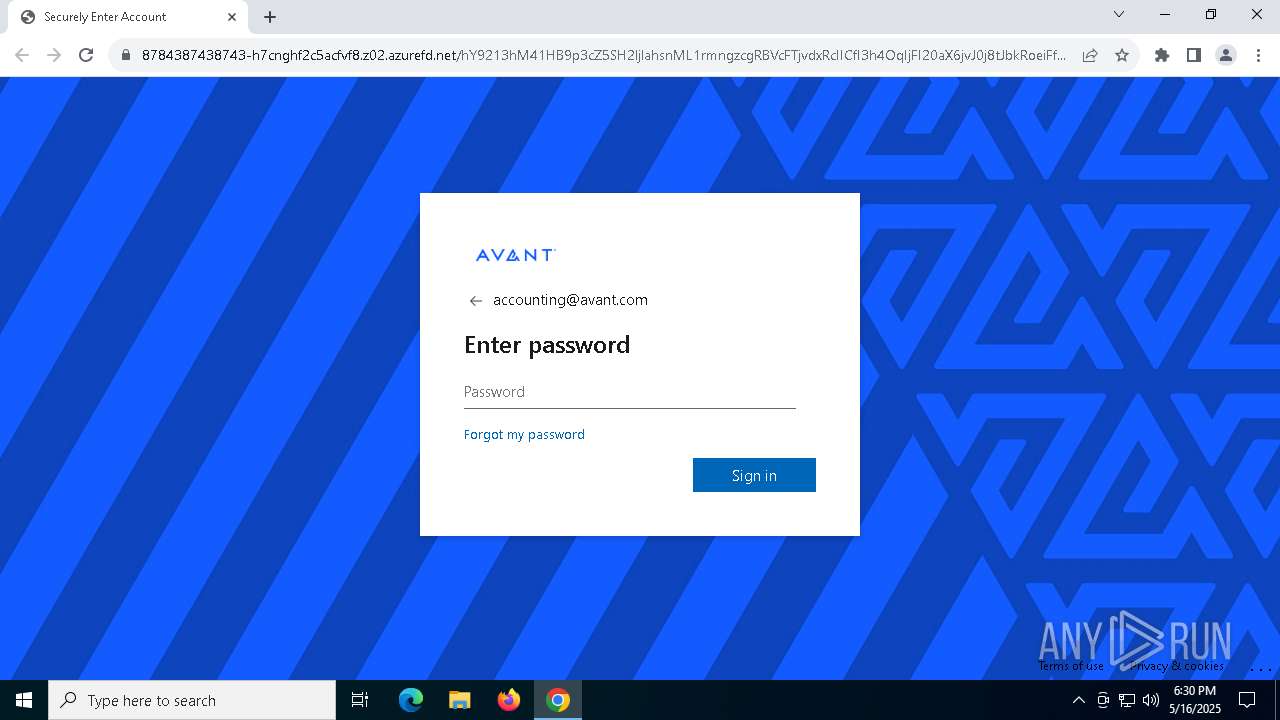
| Verdict: | Malicious activity |
| Threats: | Tycoon 2FA is a phishing-as-a-service (PhaaS) platform designed to bypass multi-factor authentication (MFA) protections, particularly targeting Microsoft 365 and Gmail accounts. Its advanced evasion techniques and modular architecture make it a significant threat to organizations relying on MFA for security. |
| Analysis date: | May 16, 2025, 18:30:13 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2A2254F7490BABABE9C60935E1DA5094 |
| SHA1: | 4C3DC40BE2C56B7A5561C417840CFADDF467F22B |
| SHA256: | AD9D2F709B87C85C9AEBAB650999059CD9C3D71B6A23DD2C4FE3C141992680CC |
| SSDEEP: | 24:2VwJ4/XcCTkvxmDzcYP5qz4d4K+OLVgVqeTWRhD4NVyLTpC3GneF7OOJaOAXXNY:x4/3TMKP5qfmJqqe6RhUN4TpCbFLAXS |
MALICIOUS
PHISHING has been detected (SURICATA)
- chrome.exe (PID: 7368)
SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 6800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
149
Monitored processes
14
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5204 --field-trial-handle=1884,i,8157225805340482109,2487532893548057341,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 6800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://dnp.motorhinoafrica.com/b#bnBkL3VvYndiQWhvanVvdnBkZGIwenNFNXpZMkoxW1Bybkt4WDM2VU5lU0ZJNjZRVkh6Y21jb2RbaTl1Sm1xOG17NlV5W3N1T29GczN3MzJlVmg5Z3JPcjFWa3dnSTl5bHcxSlh0Q01oN0NPd3ZbRnZqU2xUSk53UGpmZmVwakdudm0zT01DbXdXZHZVcWRraEdxUGtxcFgxdlA4WkxpWllEa3lSVUhLWllaUmRLUUVnSmR7OlBEVURmcW9ieUhlb0dZbTN2anlwRW9EajdkMWxjUk83aExlS21TbnZtTEhRZFdCZDZoajFVN1BwZGR7UzVHOTZOTW9RQzF1UFZmUkJQazNMRWhjc1I4U3ZKSGVNTER5enBndDhiZllGUmgzTEl1dUlbbzpTTzdDYmpKd09TOXZvcWhQZHRtd3Z0aGVKWzZSOEZ2WGJmMjhUZlJJRFc1NGpzY2N2cFdpRkQxWURYWU41WlY2Rk50Q2JMZWVORUJLeXZSW3ZGT21XRjhLbUI5TUZyRWlXY1RZaEh6d1dbMnNaRGRaVmpGSmxMNXpmMUNTTW9KMVdCVVpTRXFZZklSdGYzWERTRFZ3V0dwVmlYRlhFSnBXMVdqczpsW0Y6U3hZVll6Znd5NVZkc1Y3S1djSTVLanRkaDU2ZUNEOnplVTNQekxOWnlHaGM2T21EbVZqW2NsTU80aThGZms0allMQnpZOU5VRVB5W3hsVDJKWnprd1JXNVsyc2ZpVnc3SmZjR0k4VzJwMmNNa2htUXlrVVhjdVU5d2JiS3JoV09NW1R2ajlndXhWRkRjNFBHMTo0YjJQSmlGeEl1ZGhOOFNbZHdSY21KTnpzcVRMT2h6NjJ0b3J7SHVZaEdXdnZwYjM3NVZNaFRxU2QyODpqMnRUWU1IZnFCUVRudTo4UWlLblV6UnNSYnNtSUJQZGtTW0N5eUk0MUxEUGh4enZNdHpFcVR2blh6WmgyV1U5R3pHRnVlU0JXYkJXbm9veElKW3VWODk5NVJXZGNiNVt2d3lqY1pJeGx3WndENnA0V2p6WURyREdXajFtUFplT0trb2xnRTdCSk51R2xSdDVZVU9mbERzRjNQM2N3Nm5nbkdxVHt3cGc2NXBIdlBXdDF7ZXpzdng4Om9adGtpWVJ6ZGMyMmc5dzF0Y0VaVWVTa3RtS056cXJPZmJxbXBJWmhzOENiWHk3Tmhza1hVRXFJM1o2RGJWTHFyeVJRNmhCY2ZWZUdTWGdvUlFzVjpobmNmM0REN3Q3Z21FVmhLSGRaR0tnNkhZbGtTMkNkYkQ5cnBnWWZISEtxSUg3WElvY00zbHdZOW9LdE5qdW1GWEw5ZEp2SjVvQmJWbDlEOjBxanB3MGZlL3dvanlmbWJpcWZkMDA7dHF1dWk=" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 7220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x220,0x224,0x228,0x1fc,0x22c,0x7ffc88eedc40,0x7ffc88eedc4c,0x7ffc88eedc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 7356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1804 --field-trial-handle=1884,i,8157225805340482109,2487532893548057341,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 7368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2128 --field-trial-handle=1884,i,8157225805340482109,2487532893548057341,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 7380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2240 --field-trial-handle=1884,i,8157225805340482109,2487532893548057341,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 7568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2988 --field-trial-handle=1884,i,8157225805340482109,2487532893548057341,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 7576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3104 --field-trial-handle=1884,i,8157225805340482109,2487532893548057341,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 7600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3476 --field-trial-handle=1884,i,8157225805340482109,2487532893548057341,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 7840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=3924 --field-trial-handle=1884,i,8157225805340482109,2487532893548057341,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
2 904
Read events
2 899
Write events
5
Delete events
0
Modification events
| (PID) Process: | (6800) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6800) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6800) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6800) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6800) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
31
Text files
18
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10c0e1.TMP | — | |
MD5:— | SHA256:— | |||
| 6800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10c0e1.TMP | — | |
MD5:— | SHA256:— | |||
| 6800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10c0e1.TMP | — | |
MD5:— | SHA256:— | |||
| 6800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10c0e1.TMP | — | |
MD5:— | SHA256:— | |||
| 6800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10c0f0.TMP | — | |
MD5:— | SHA256:— | |||
| 6800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
54
DNS requests
77
Threats
30
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.0.162.201:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6700 | SIHClient.exe | GET | 200 | 23.53.245.217:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.53.245.217:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.53.245.217:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.0.162.201:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6700 | SIHClient.exe | GET | 200 | 23.53.245.217:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.22.98.7:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4208 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.0.162.201:80 | crl.microsoft.com | Akamai International B.V. | ID | whitelisted |
2104 | svchost.exe | 23.0.162.201:80 | crl.microsoft.com | Akamai International B.V. | ID | whitelisted |
2104 | svchost.exe | 23.53.245.217:80 | www.microsoft.com | Akamai International B.V. | US | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.53.245.217:80 | www.microsoft.com | Akamai International B.V. | US | whitelisted |
6800 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
dnp.motorhinoafrica.com |
| unknown |
accounts.google.com |
| whitelisted |
4839794398349343-g4eydqdkguhcdvgs.z02.azurefd.net |
| malicious |
client.wns.windows.com |
| whitelisted |
cephalexinv.de |
| unknown |
8784387438743-h7cnghf2c5acfvf8.z02.azurefd.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7368 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain (g4eydqdkguhcdvgs .z02 .azurefd .net) |
7368 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain (g4eydqdkguhcdvgs .z02 .azurefd .net) |
7368 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain (g4eydqdkguhcdvgs .z02 .azurefd .net) |
7368 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
7368 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
7368 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
7368 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7368 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7368 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7368 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |