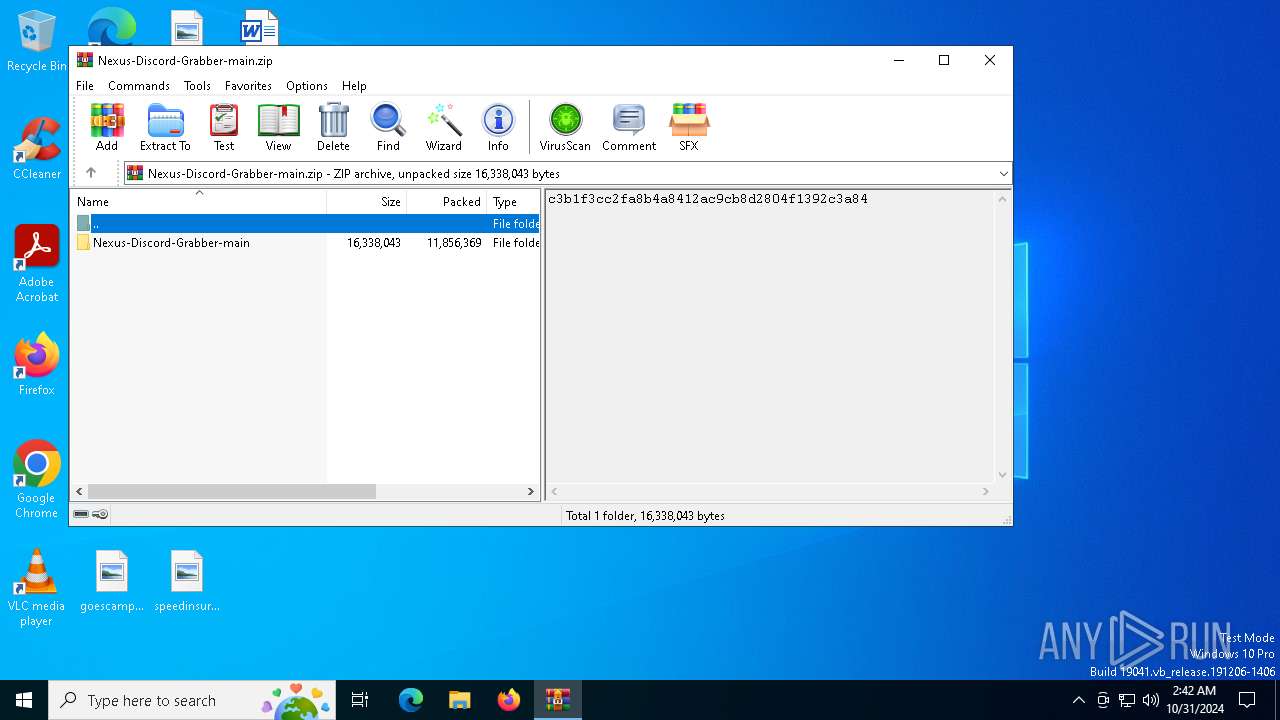
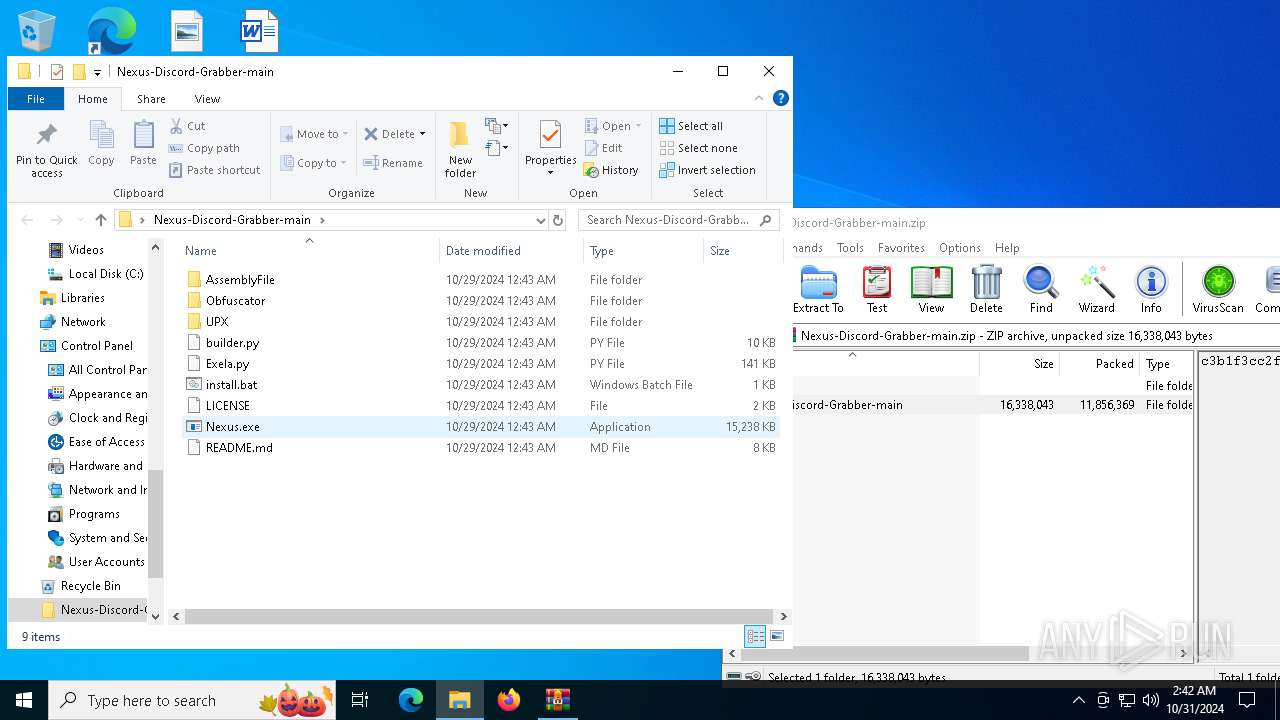
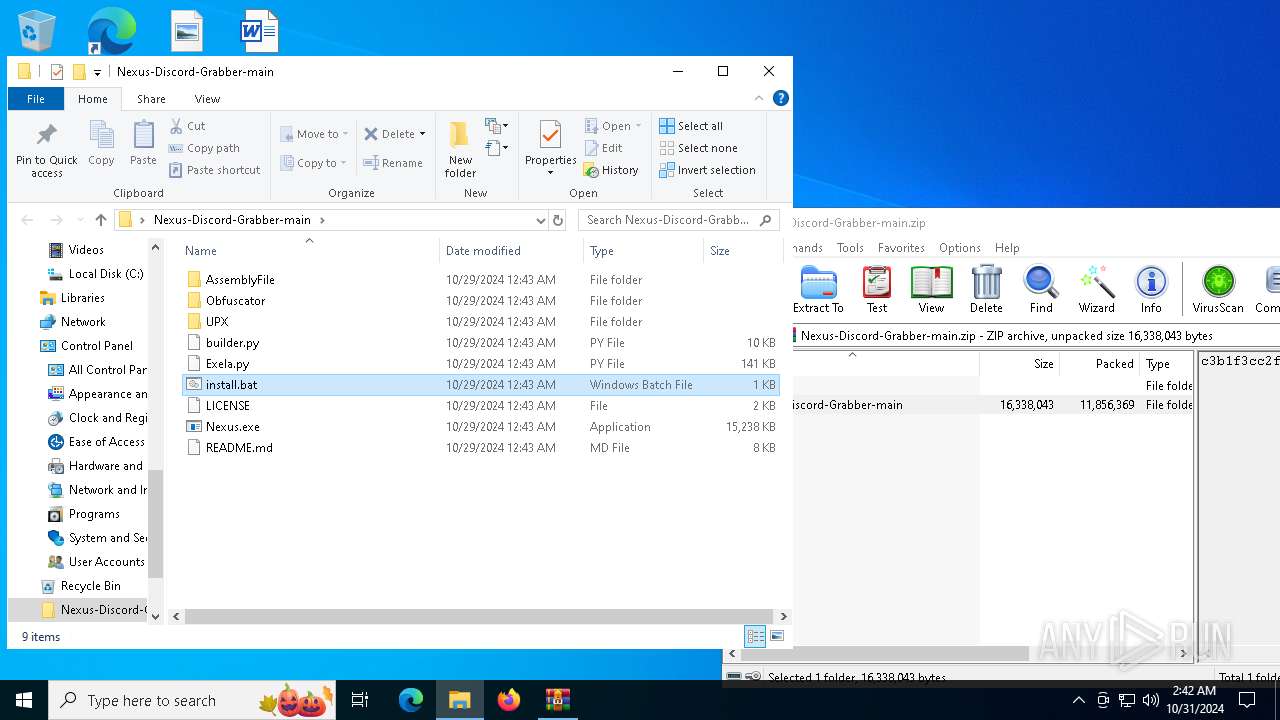
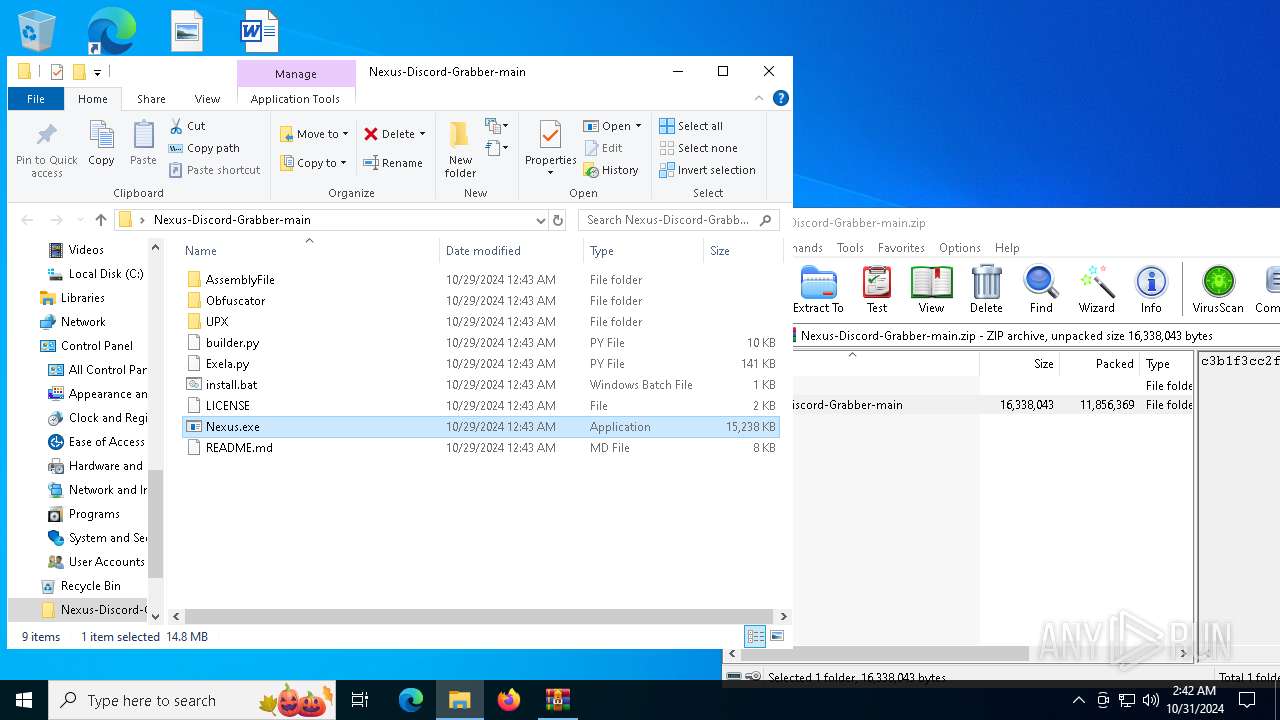
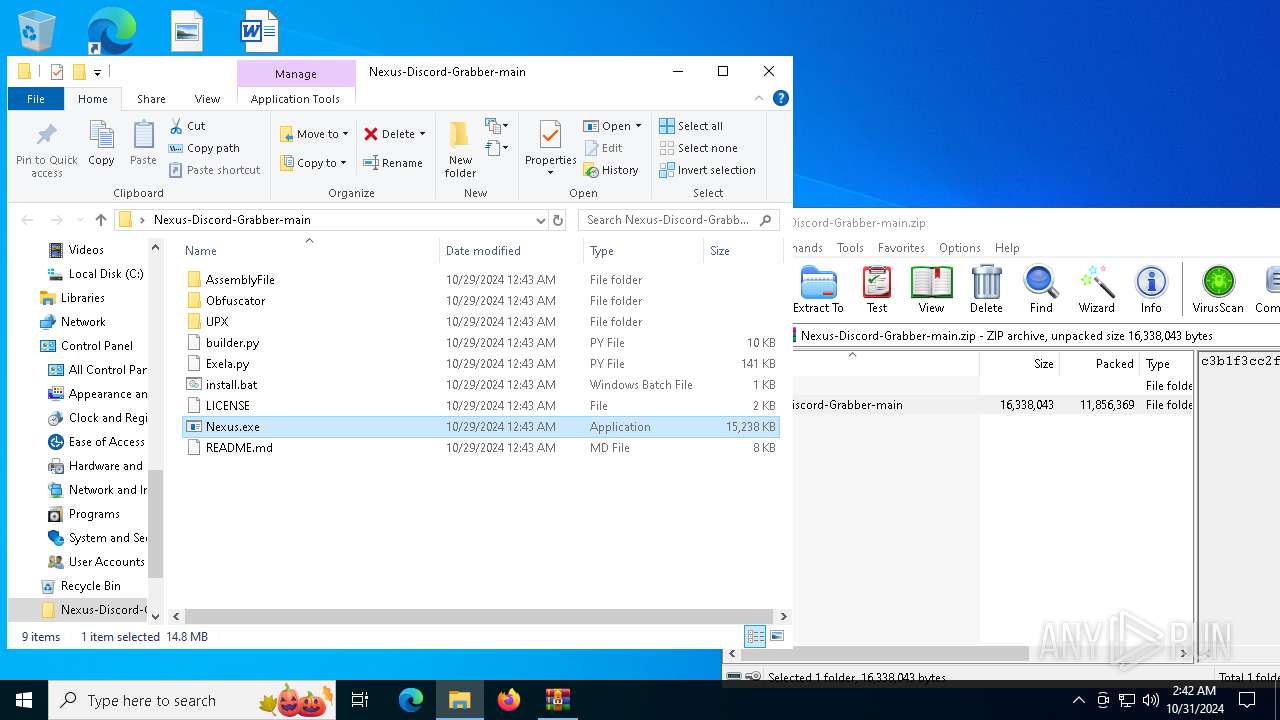
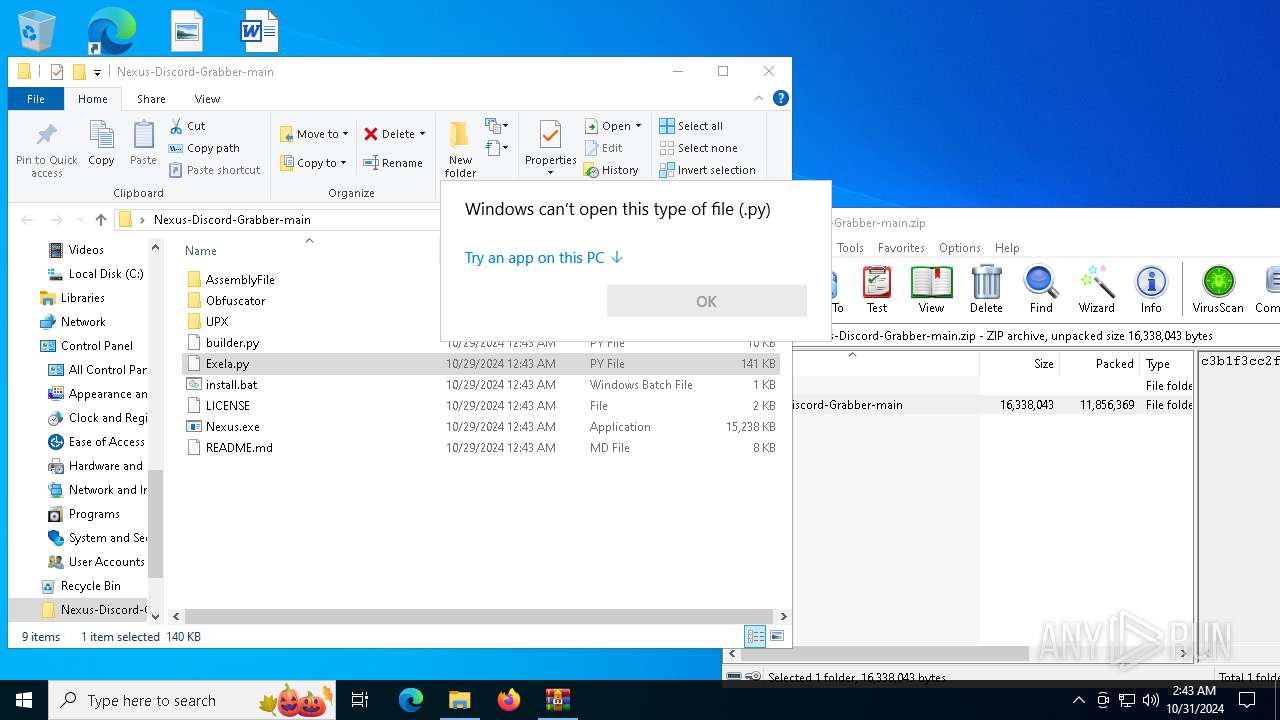
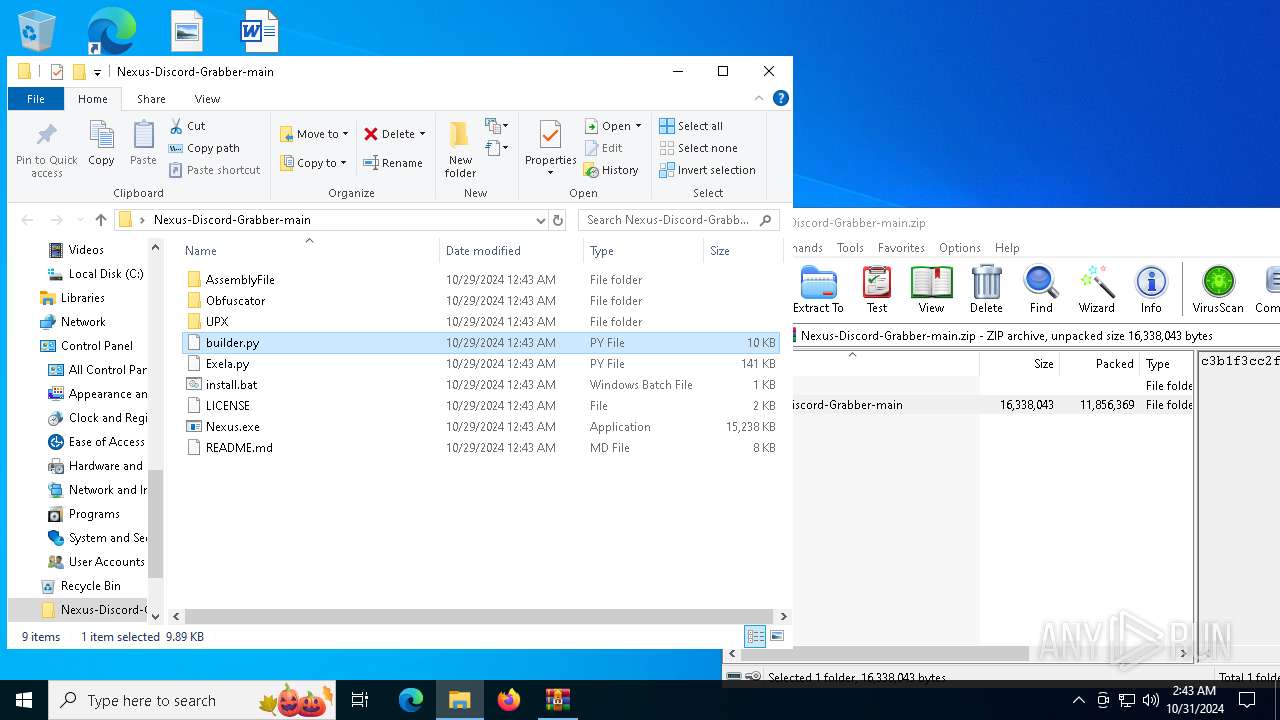
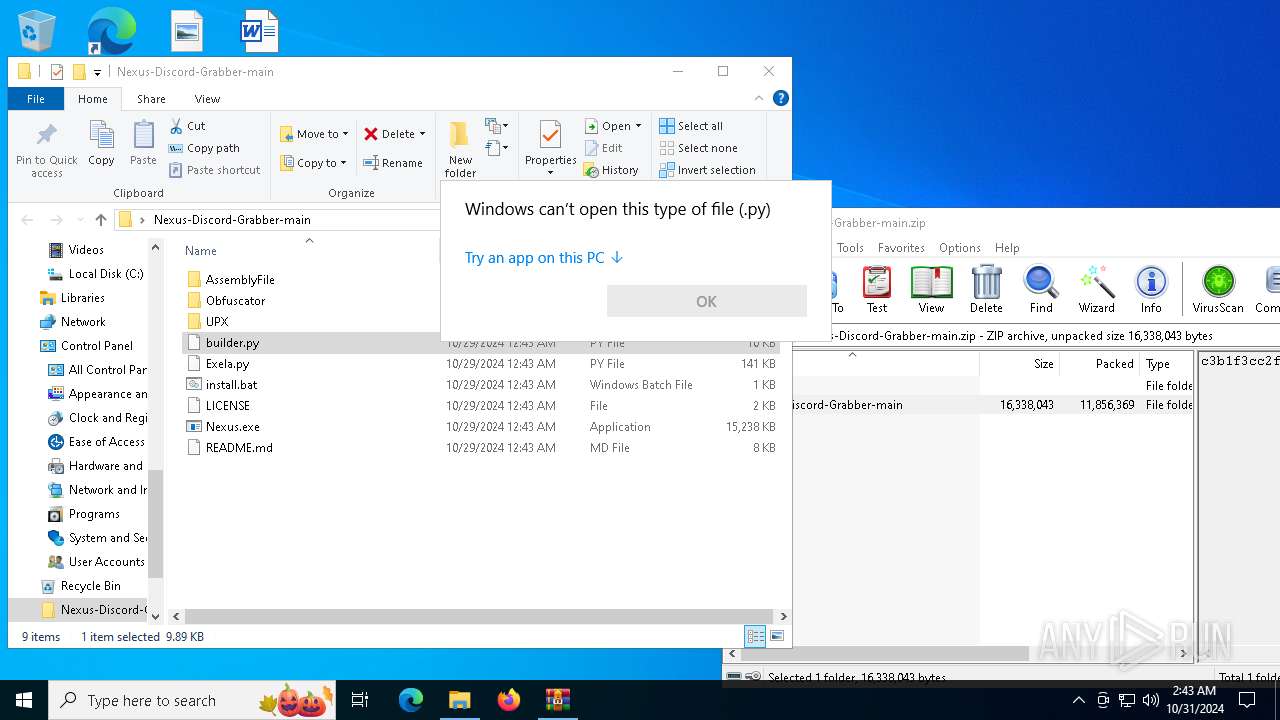
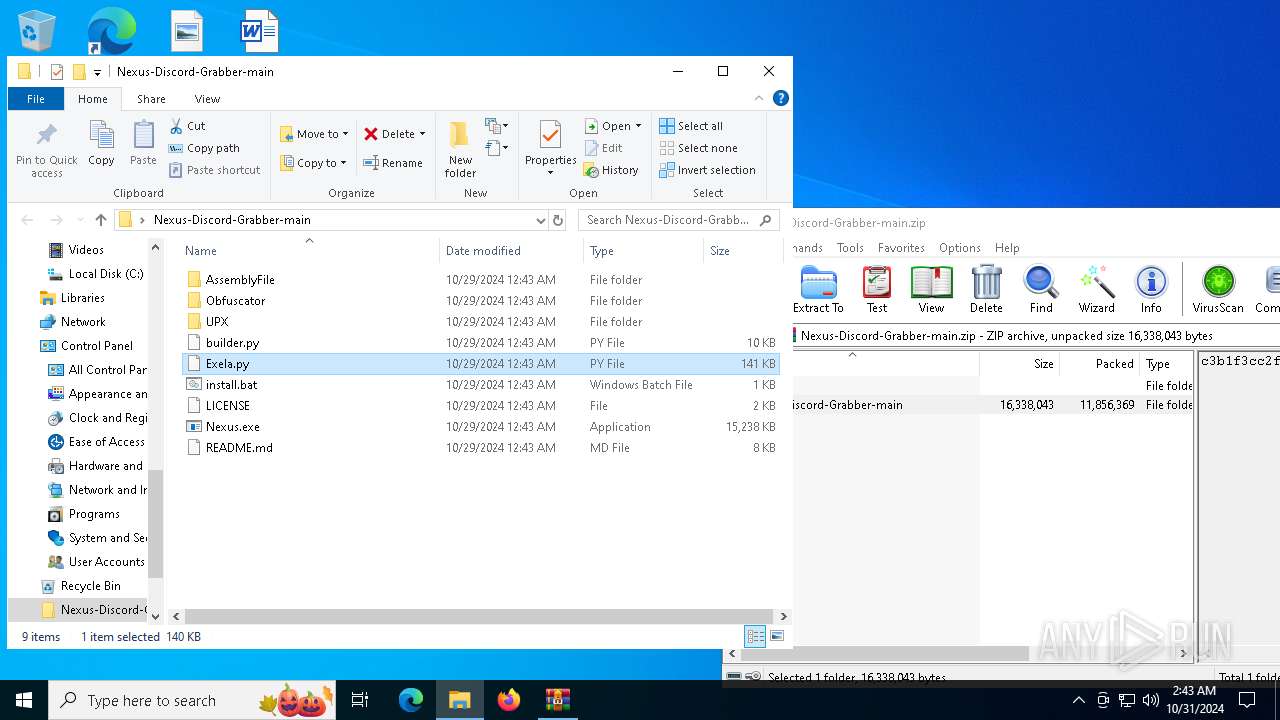
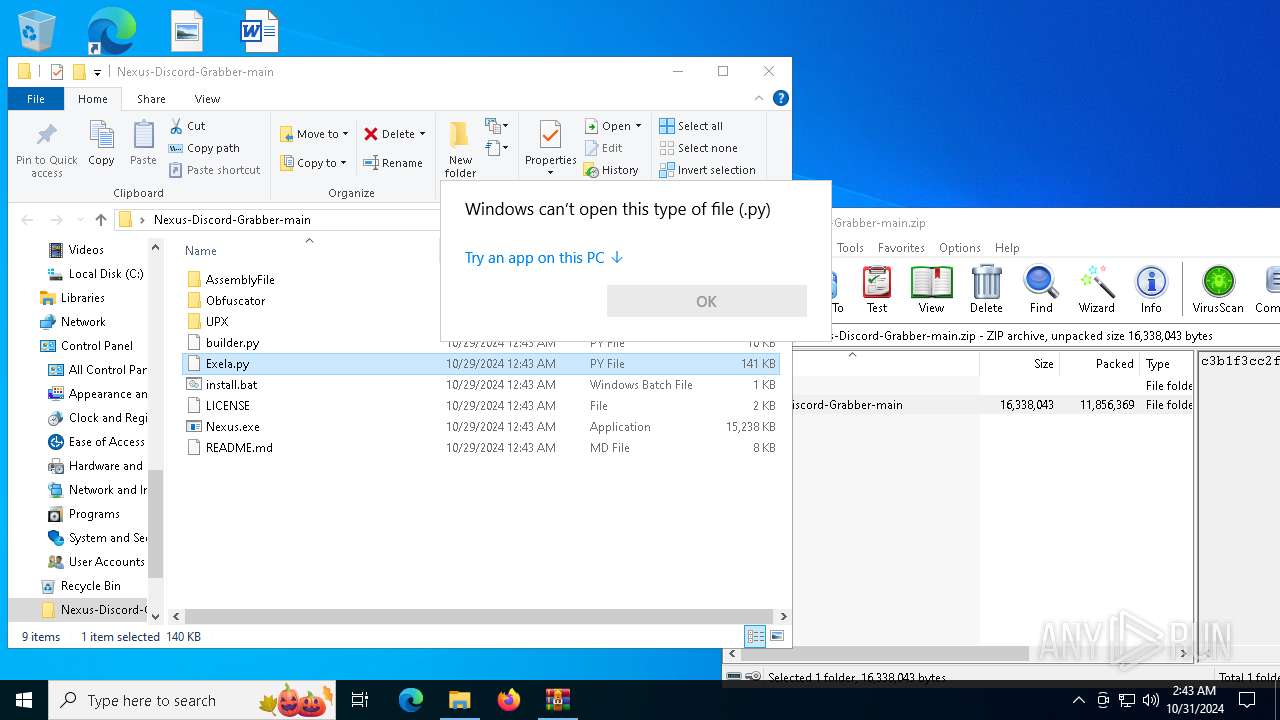
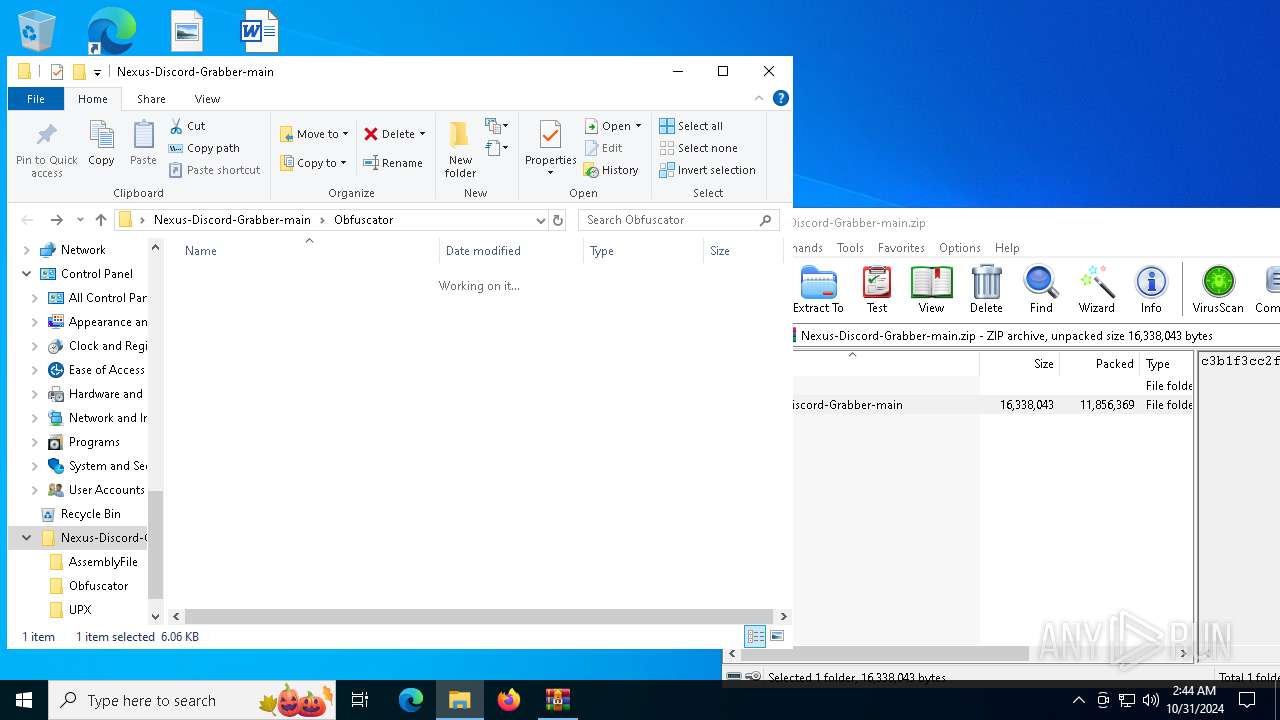
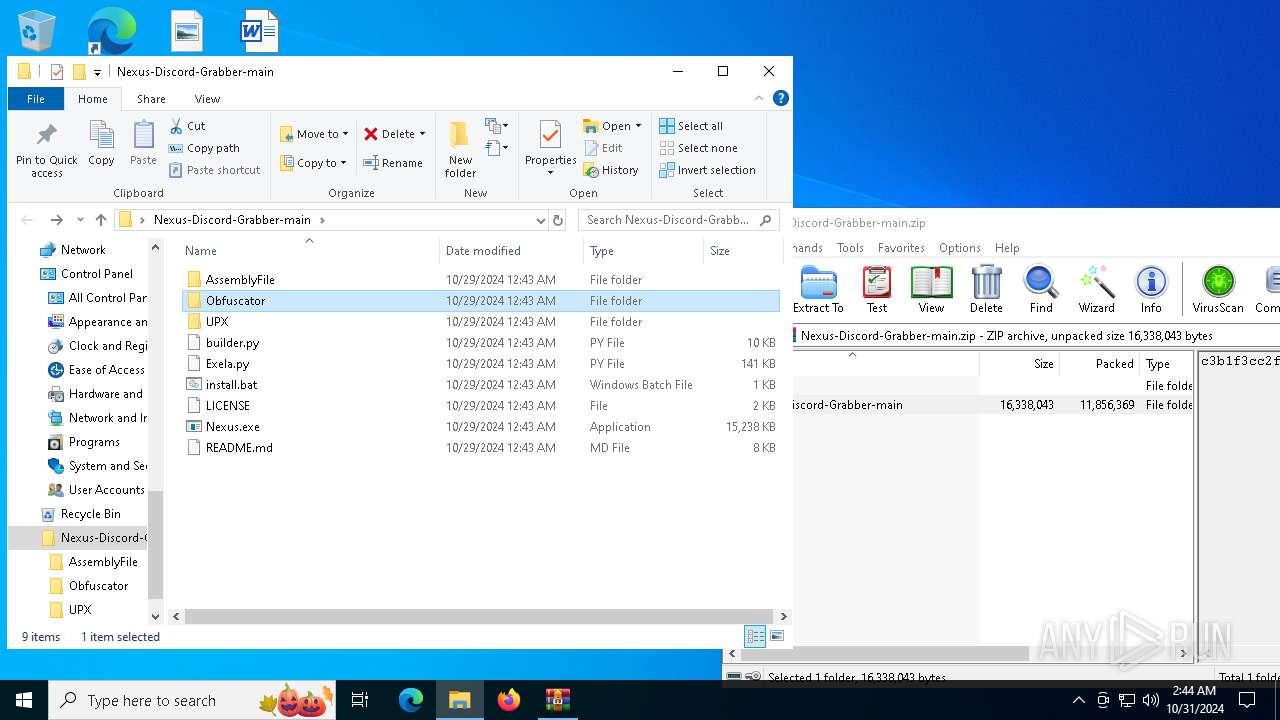
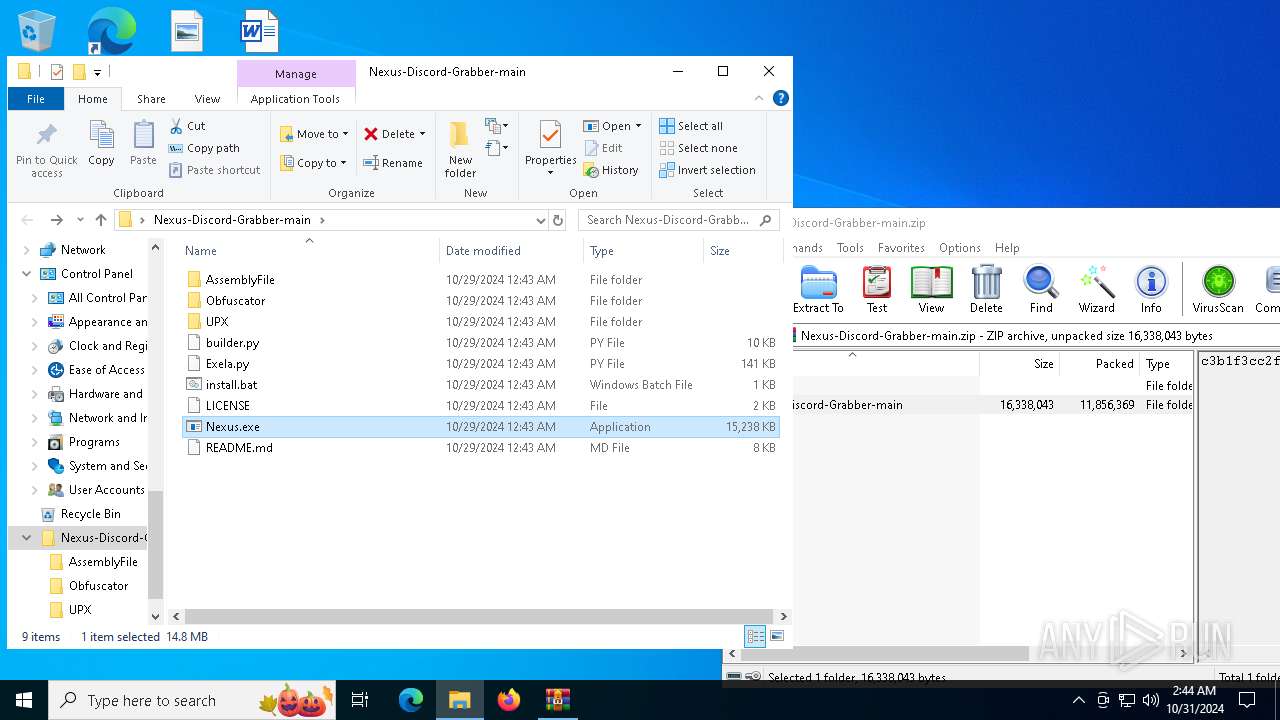
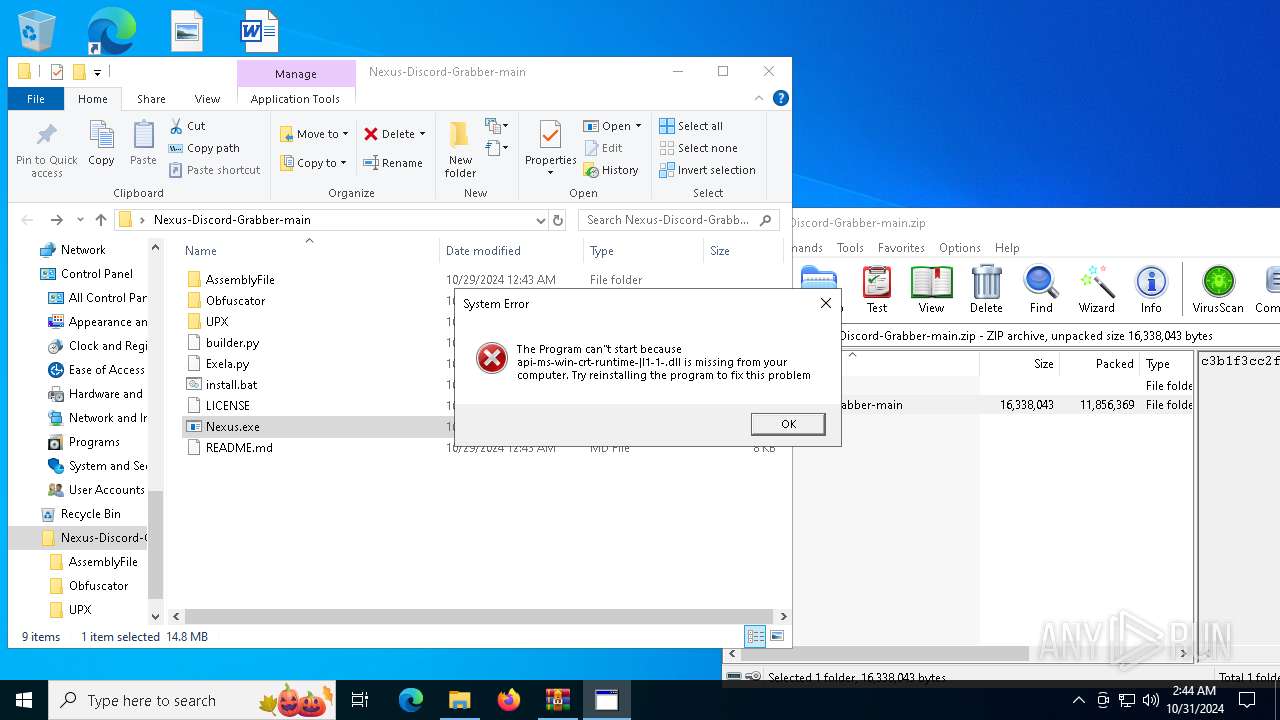
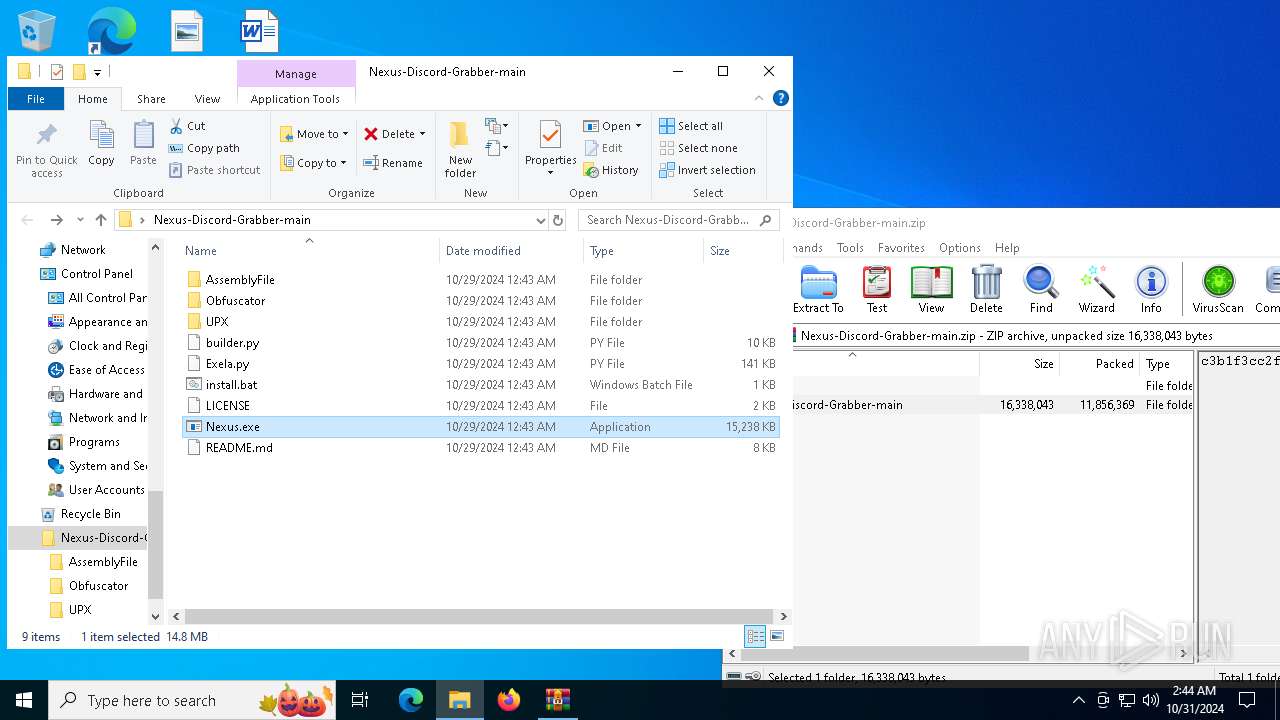
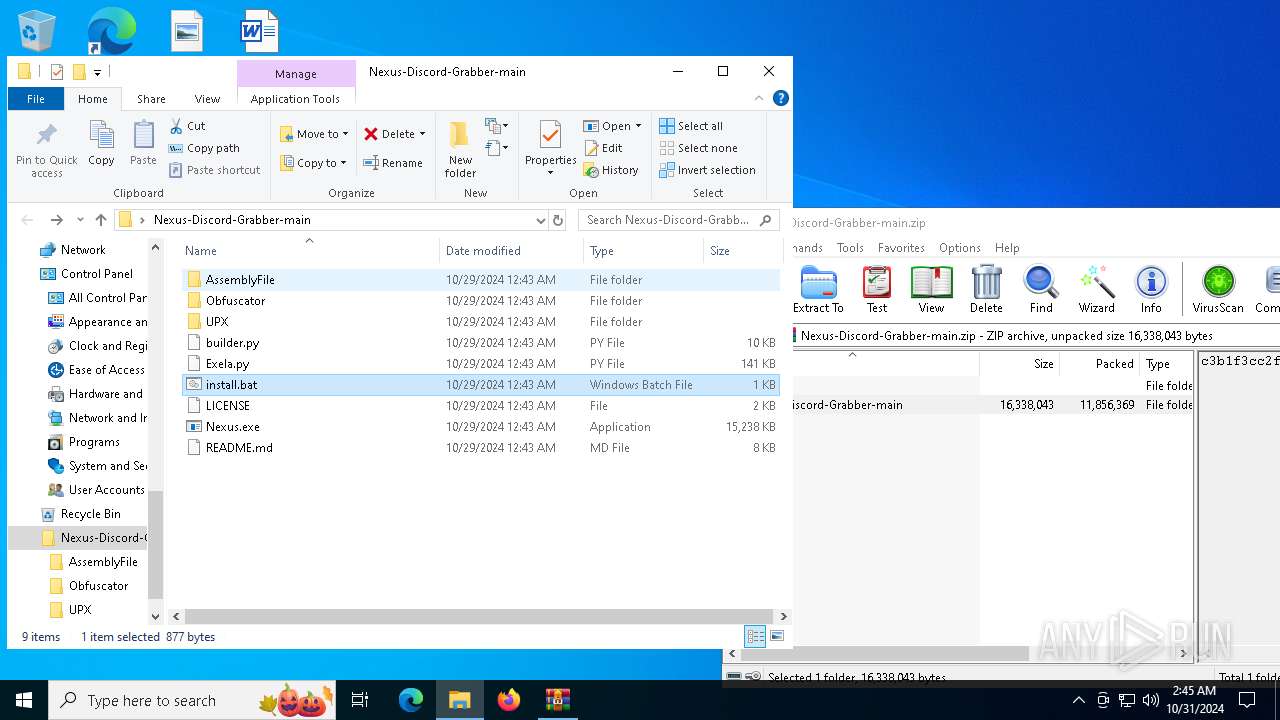
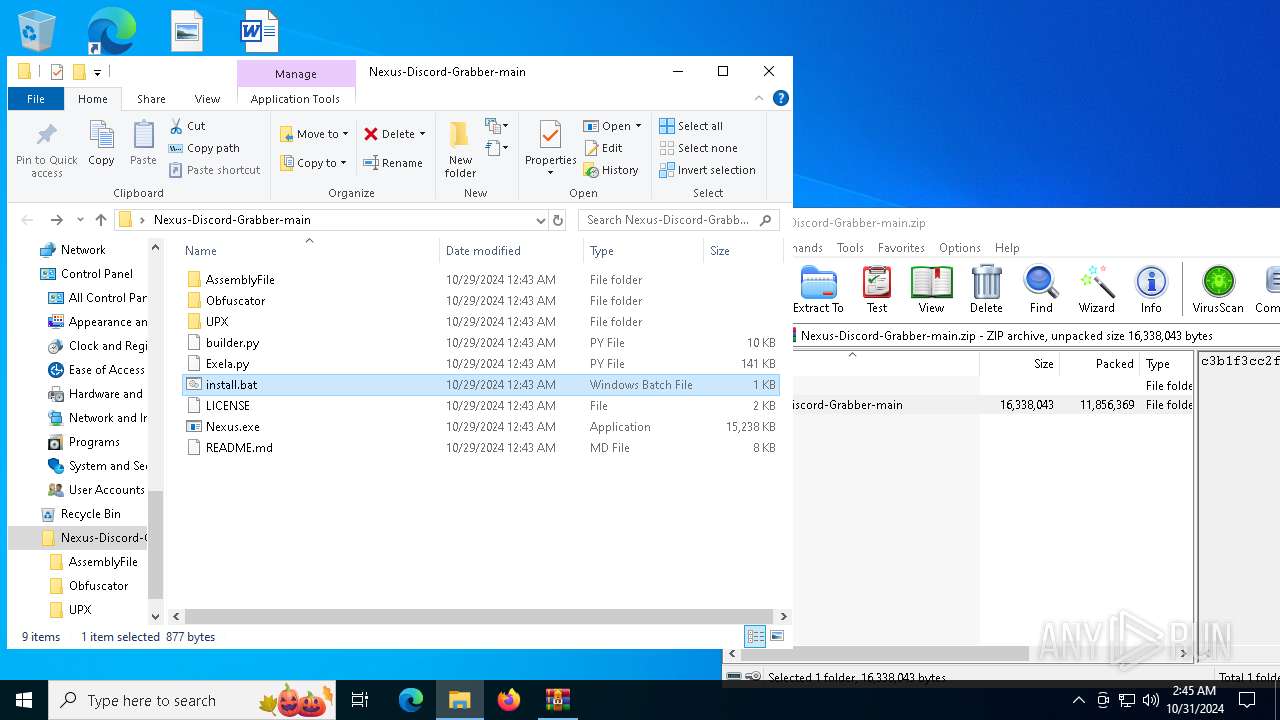
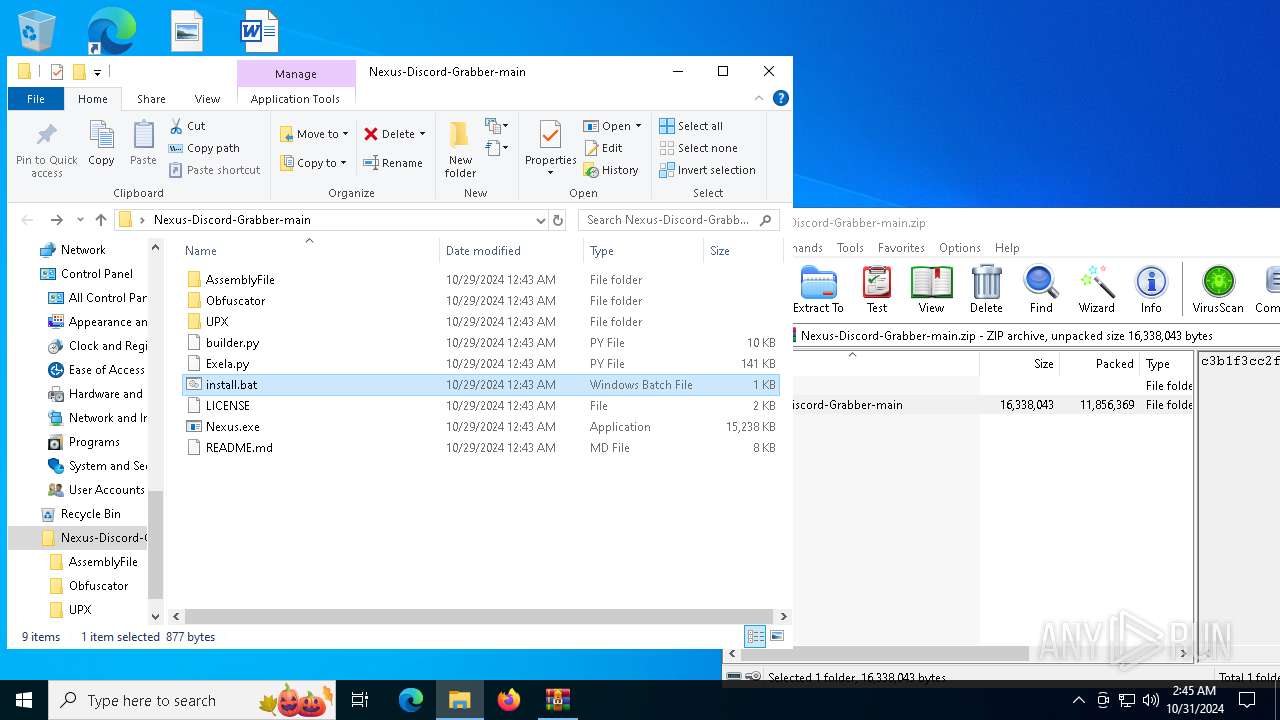
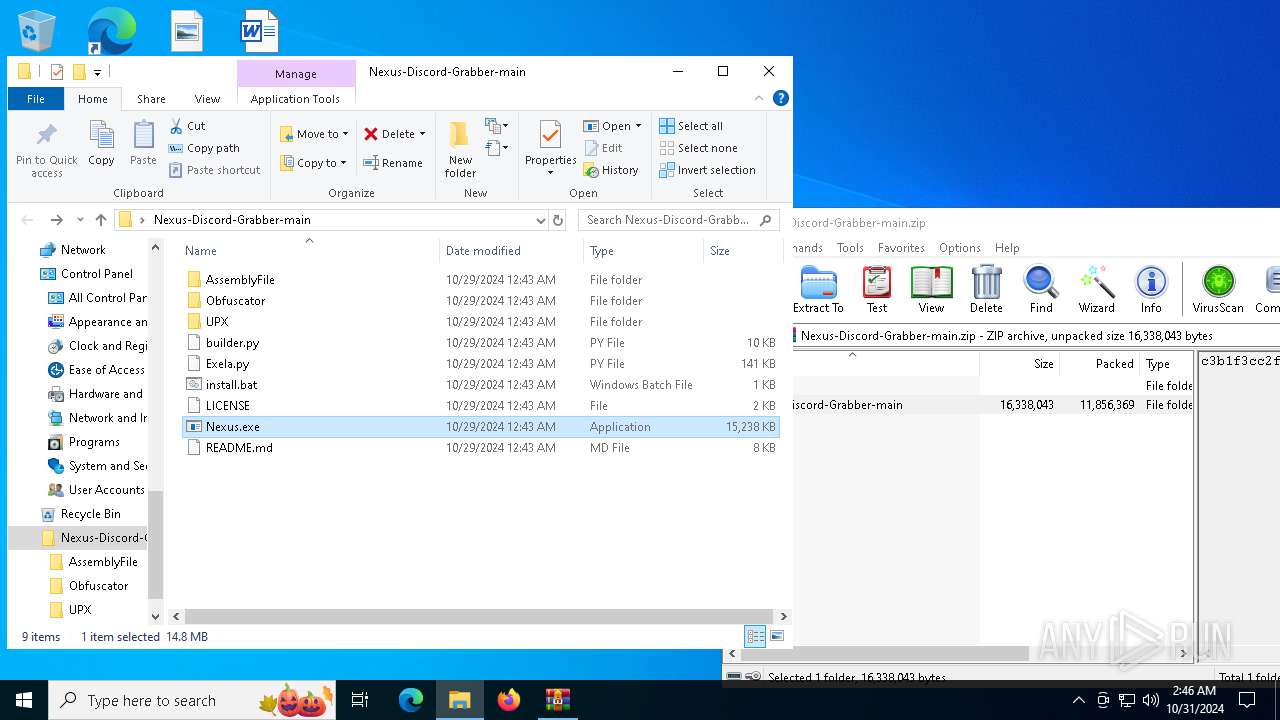
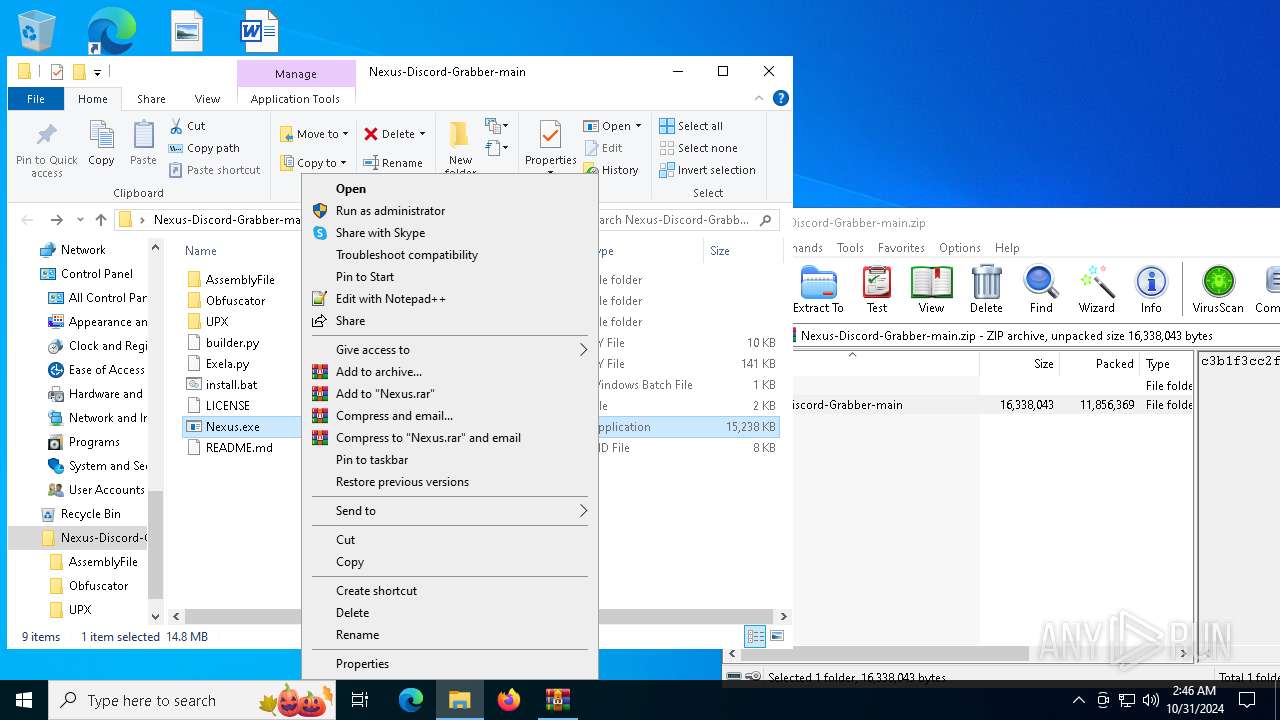
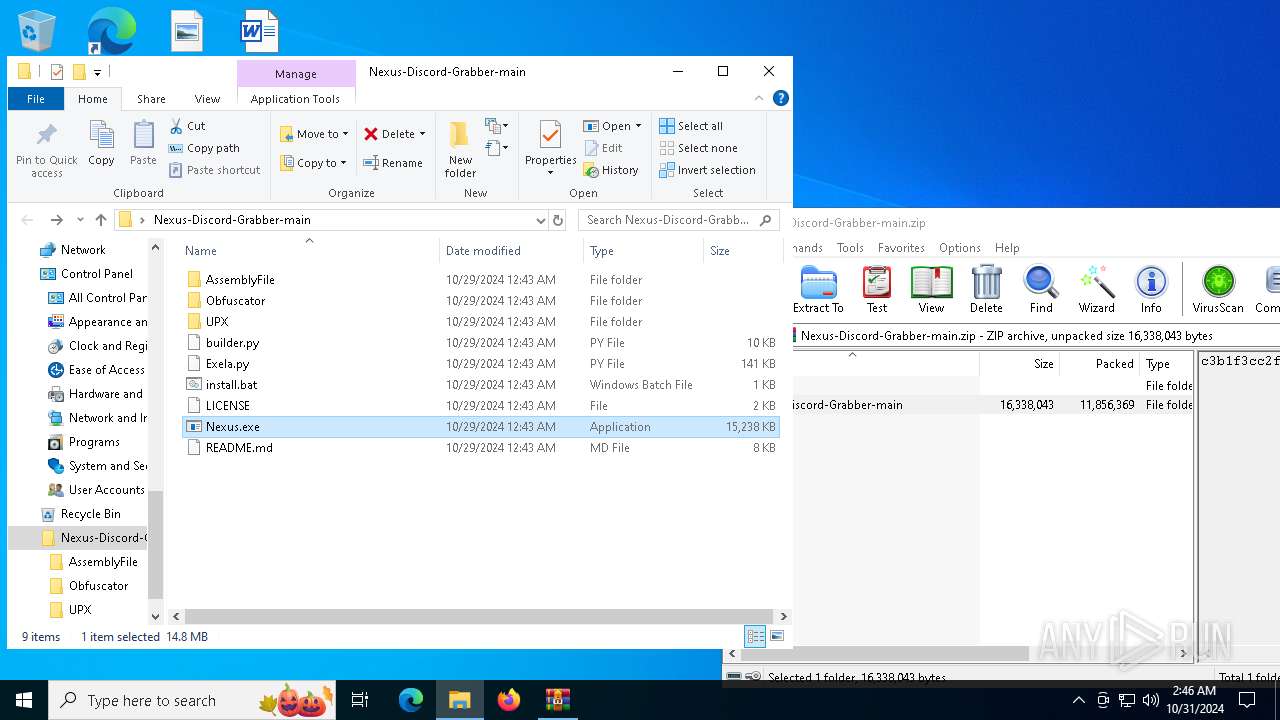
| File name: | Nexus-Discord-Grabber-main.zip |
| Full analysis: | https://app.any.run/tasks/6db80356-4c95-418b-a8e0-219a1ae56837 |
| Verdict: | Malicious activity |
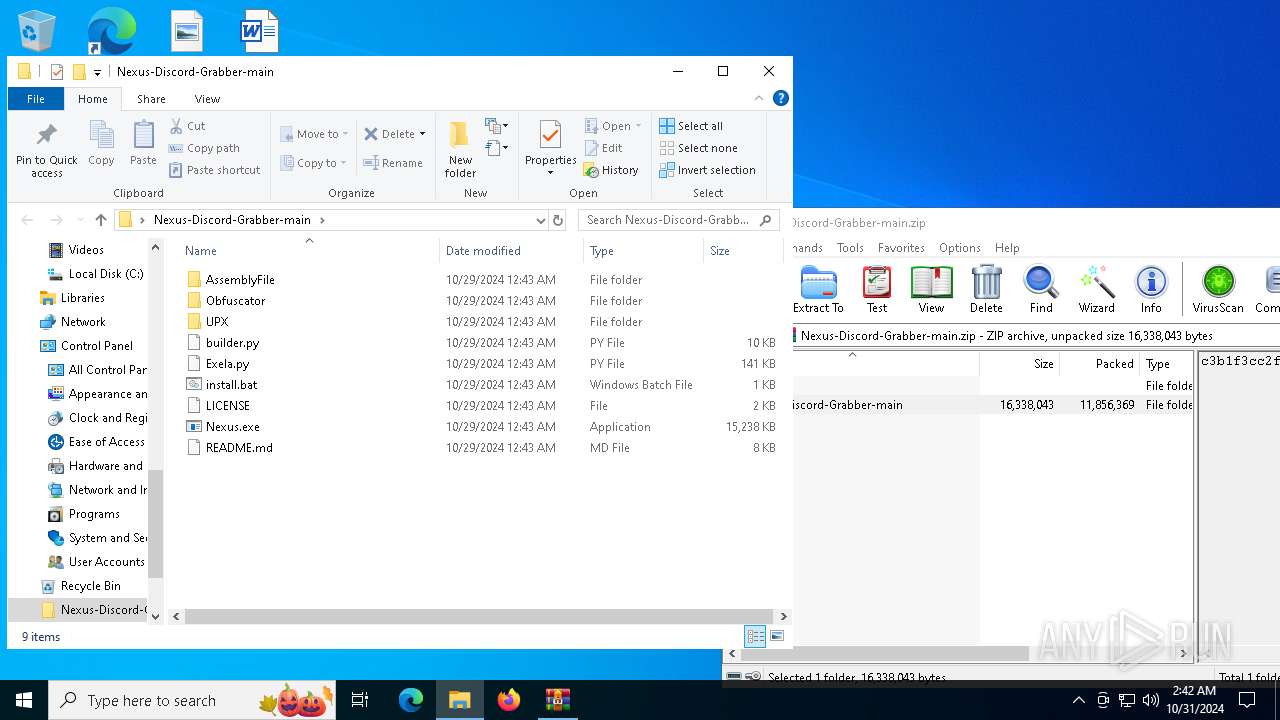
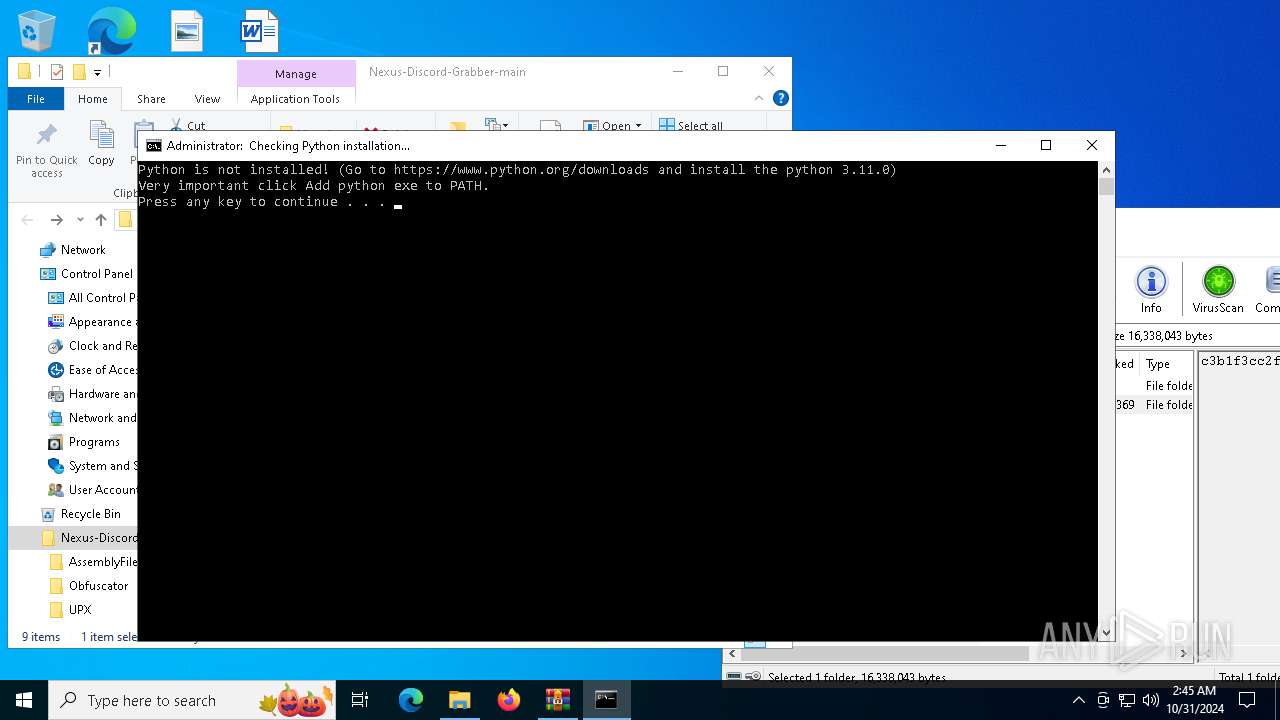
| Threats: | Exela Stealer is an infostealer malware written in Python. It is capable of collecting a wide range of sensitive information from compromised systems and exfiltrating it to attackers over Discord. It is frequently used to steal browser data, and obtain session files from various applications, including gaming platforms, social media platforms, and messaging apps. |
| Analysis date: | October 31, 2024, 02:42:01 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 4F4E5580D6776BAF372AB215B70F6461 |
| SHA1: | 0F5444DE4F3D1452CD03974DB2218F4961FC0A72 |
| SHA256: | AD06ECE5D6FC7FFE21DA143FC272ED2A172C0FEB68309E3055F9B3DCDEC2877D |
| SSDEEP: | 98304:+yKv8RZ/Z1wYkLbtlGwjvJ/wut9M1wCgmK5WlvKvJUQKTUQbOB6xJp2gSHaG87Mr:Y522iAIHq0zZXMQiv+/BRWhH |
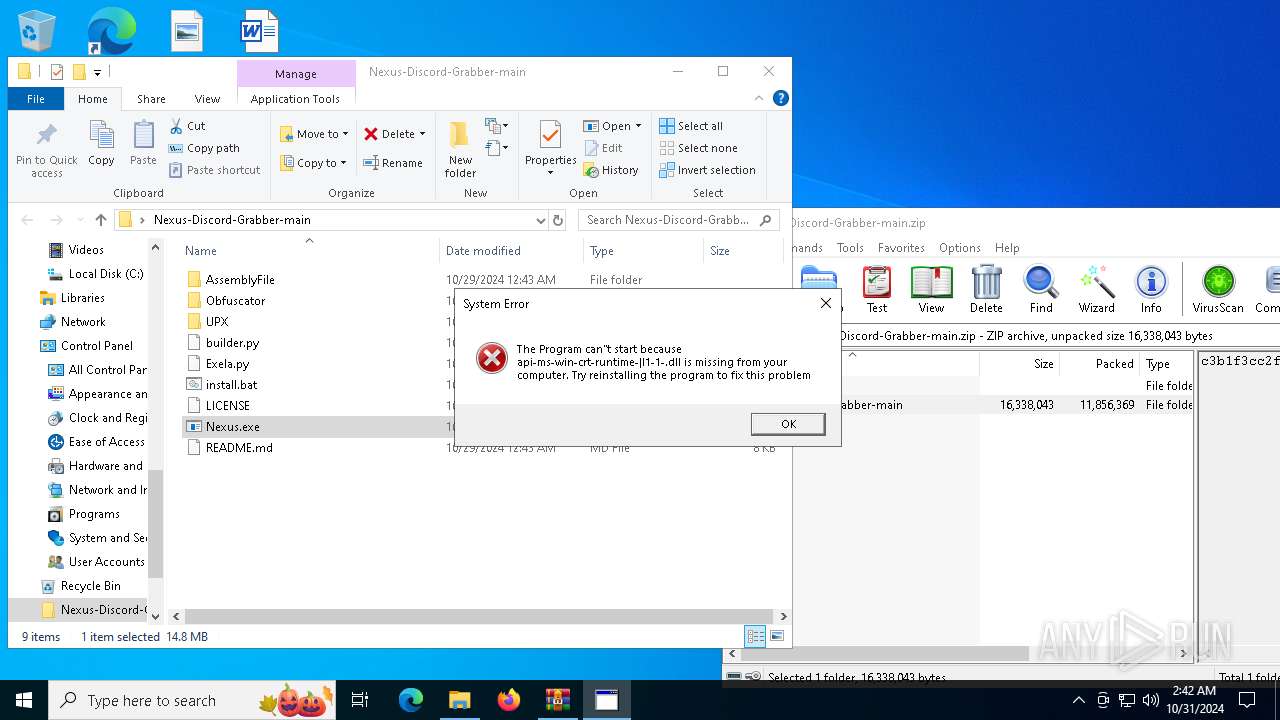
MALICIOUS
ExelaStealer has been detected
- Nexus.exe (PID: 7140)
- Nexus.exe (PID: 6176)
- Nexus.exe (PID: 6636)
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 6176)
- net.exe (PID: 1048)
- net.exe (PID: 944)
- net.exe (PID: 4808)
- net.exe (PID: 4340)
- net.exe (PID: 3732)
- cmd.exe (PID: 6248)
- net.exe (PID: 5284)
- net.exe (PID: 3108)
- net.exe (PID: 5932)
- net.exe (PID: 4996)
- cmd.exe (PID: 4260)
Starts NET.EXE to view/change users localgroup
- cmd.exe (PID: 6176)
- net.exe (PID: 4676)
- net.exe (PID: 2816)
- cmd.exe (PID: 6248)
- net.exe (PID: 3860)
- net.exe (PID: 5240)
- net.exe (PID: 7060)
- cmd.exe (PID: 4260)
- net.exe (PID: 6352)
Bypass execution policy to execute commands
- powershell.exe (PID: 7004)
- powershell.exe (PID: 5616)
- powershell.exe (PID: 5784)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 1428)
- cmd.exe (PID: 6308)
- cmd.exe (PID: 7136)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 6708)
- Nexus.exe (PID: 4548)
- Nexus.exe (PID: 7140)
- Nexus.exe (PID: 6324)
- Nexus.exe (PID: 1048)
Starts a Microsoft application from unusual location
- Nexus.exe (PID: 4548)
- Nexus.exe (PID: 7140)
- Nexus.exe (PID: 6324)
- Nexus.exe (PID: 6176)
- Nexus.exe (PID: 6636)
- Nexus.exe (PID: 1048)
The process drops C-runtime libraries
- Nexus.exe (PID: 4548)
- Nexus.exe (PID: 6324)
- Nexus.exe (PID: 1048)
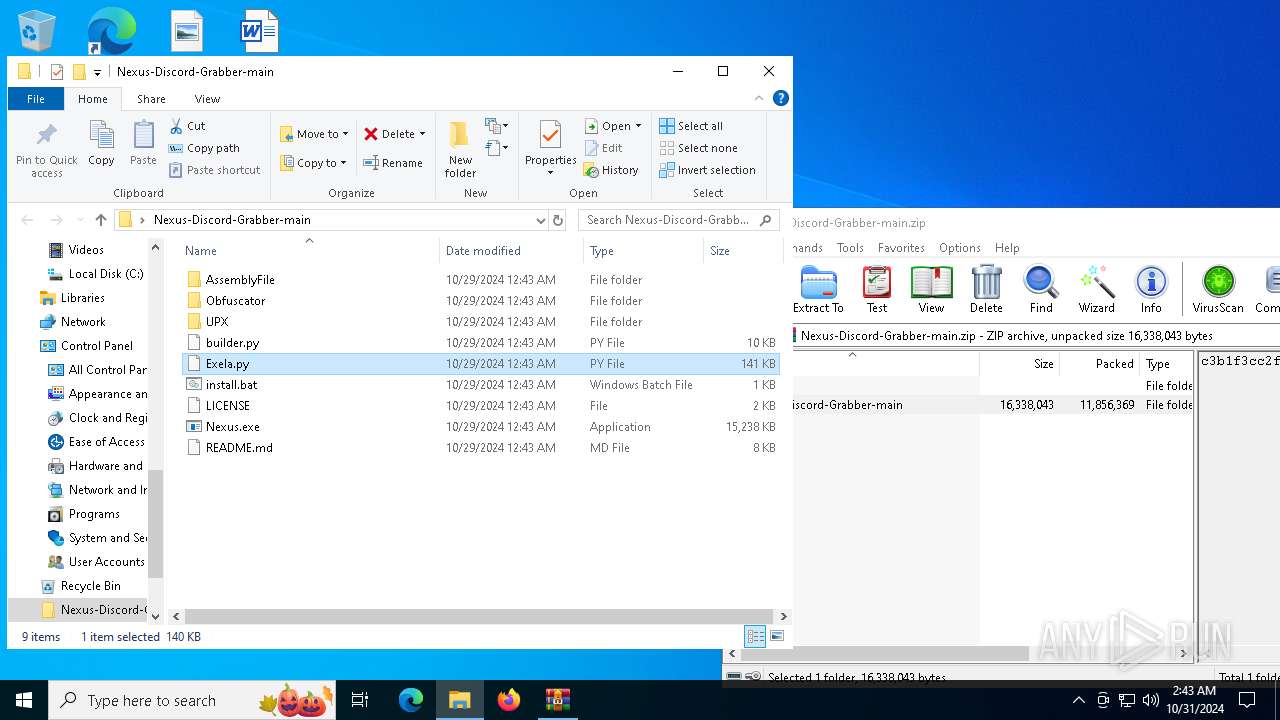
Process drops python dynamic module
- Nexus.exe (PID: 4548)
- Nexus.exe (PID: 6324)
- Nexus.exe (PID: 1048)
Executable content was dropped or overwritten
- Nexus.exe (PID: 4548)
- Nexus.exe (PID: 7140)
- csc.exe (PID: 3792)
- Nexus.exe (PID: 6324)
- Nexus.exe (PID: 1048)
- csc.exe (PID: 2588)
- csc.exe (PID: 4380)
Application launched itself
- Nexus.exe (PID: 4548)
- cmd.exe (PID: 5980)
- cmd.exe (PID: 4956)
- Nexus.exe (PID: 6324)
- cmd.exe (PID: 6276)
- cmd.exe (PID: 1440)
- Nexus.exe (PID: 1048)
- cmd.exe (PID: 4016)
- cmd.exe (PID: 2280)
Loads Python modules
- Nexus.exe (PID: 7140)
Starts CMD.EXE for commands execution
- Nexus.exe (PID: 7140)
- cmd.exe (PID: 4956)
- cmd.exe (PID: 5980)
- Nexus.exe (PID: 6176)
- cmd.exe (PID: 1440)
- cmd.exe (PID: 6276)
- Nexus.exe (PID: 6636)
- cmd.exe (PID: 2280)
- cmd.exe (PID: 4016)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 6296)
- cmd.exe (PID: 5976)
- cmd.exe (PID: 6424)
- cmd.exe (PID: 5596)
- cmd.exe (PID: 6908)
- cmd.exe (PID: 7060)
Get information on the list of running processes
- Nexus.exe (PID: 7140)
- cmd.exe (PID: 7144)
- cmd.exe (PID: 1332)
- cmd.exe (PID: 1880)
- cmd.exe (PID: 7060)
- cmd.exe (PID: 6176)
- Nexus.exe (PID: 6176)
- cmd.exe (PID: 1588)
- cmd.exe (PID: 4584)
- cmd.exe (PID: 2588)
- cmd.exe (PID: 2132)
- cmd.exe (PID: 6248)
- Nexus.exe (PID: 6636)
- cmd.exe (PID: 6304)
- cmd.exe (PID: 3700)
- cmd.exe (PID: 7032)
- cmd.exe (PID: 4076)
- cmd.exe (PID: 4260)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 4868)
- cmd.exe (PID: 4076)
- cmd.exe (PID: 7100)
Accesses video controller name via WMI (SCRIPT)
- WMIC.exe (PID: 3732)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 5824)
- cmd.exe (PID: 7060)
- cmd.exe (PID: 5196)
- cmd.exe (PID: 608)
- cmd.exe (PID: 6516)
- cmd.exe (PID: 7056)
- cmd.exe (PID: 6712)
- cmd.exe (PID: 3604)
- cmd.exe (PID: 3156)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2816)
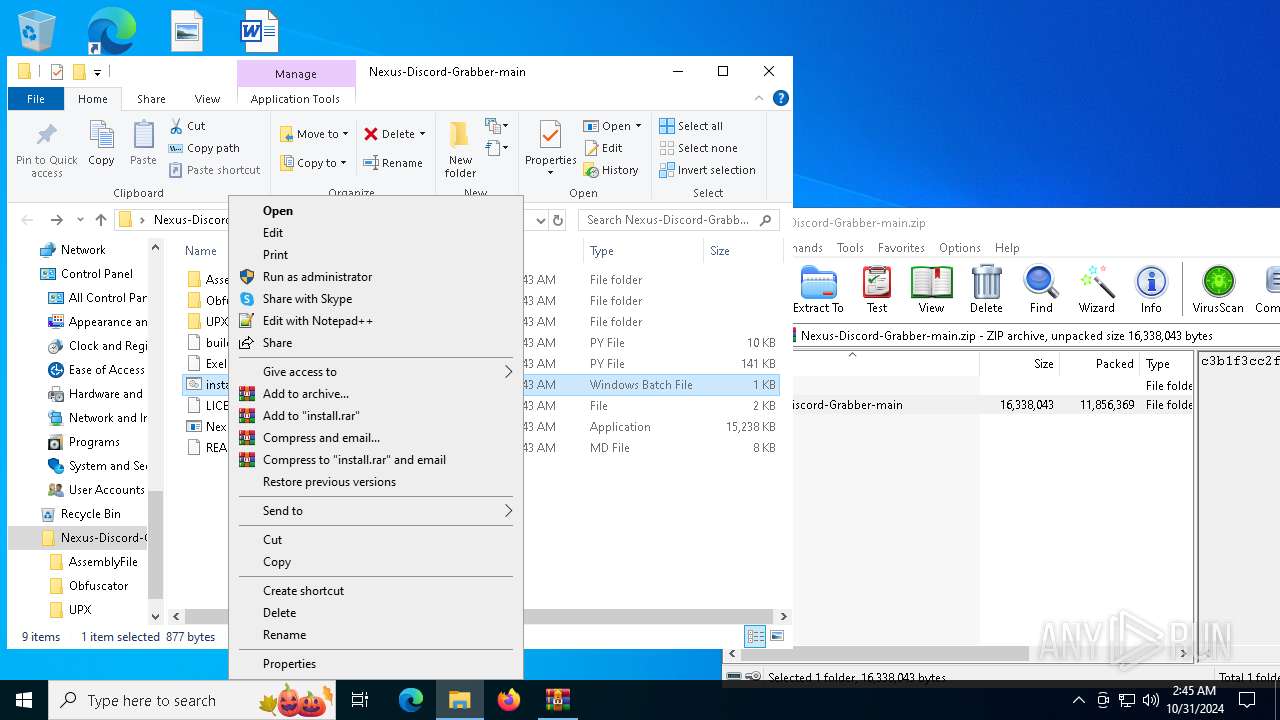
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6428)
- cmd.exe (PID: 944)
- cmd.exe (PID: 6540)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5372)
- cmd.exe (PID: 1428)
- cmd.exe (PID: 5920)
- cmd.exe (PID: 6308)
- cmd.exe (PID: 1160)
- cmd.exe (PID: 7136)
Starts application with an unusual extension
- cmd.exe (PID: 3728)
- cmd.exe (PID: 3792)
- cmd.exe (PID: 5220)
- cmd.exe (PID: 2576)
- cmd.exe (PID: 6320)
- cmd.exe (PID: 3828)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 6568)
- cmd.exe (PID: 4004)
- cmd.exe (PID: 3972)
Checks for external IP
- Nexus.exe (PID: 7140)
- svchost.exe (PID: 2172)
- Nexus.exe (PID: 6176)
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 6176)
- cmd.exe (PID: 6248)
- cmd.exe (PID: 4260)
Uses WMIC.EXE to obtain local storage devices information
- cmd.exe (PID: 6176)
- cmd.exe (PID: 6248)
- cmd.exe (PID: 4260)
Uses QUSER.EXE to read information about current user sessions
- query.exe (PID: 5700)
- query.exe (PID: 1112)
- query.exe (PID: 4032)
Uses WMIC.EXE to obtain commands that are run when users log in
- cmd.exe (PID: 6176)
- cmd.exe (PID: 6248)
- cmd.exe (PID: 4260)
Uses ROUTE.EXE to obtain the routing table information
- cmd.exe (PID: 6176)
- cmd.exe (PID: 6248)
- cmd.exe (PID: 4260)
Process uses IPCONFIG to discover network configuration
- cmd.exe (PID: 6176)
- cmd.exe (PID: 6248)
- cmd.exe (PID: 4260)
Starts SC.EXE for service management
- cmd.exe (PID: 6176)
- cmd.exe (PID: 6248)
- cmd.exe (PID: 4260)
Process uses ARP to discover network configuration
- cmd.exe (PID: 6176)
- cmd.exe (PID: 6248)
- cmd.exe (PID: 4260)
Suspicious use of NETSH.EXE
- cmd.exe (PID: 6176)
- cmd.exe (PID: 6248)
- cmd.exe (PID: 4260)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 1428)
- cmd.exe (PID: 6308)
- cmd.exe (PID: 7136)
Base64-obfuscated command line is found
- cmd.exe (PID: 1428)
- cmd.exe (PID: 6308)
- cmd.exe (PID: 7136)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 1428)
- cmd.exe (PID: 6308)
- cmd.exe (PID: 7136)
CSC.EXE is used to compile C# code
- csc.exe (PID: 3792)
- csc.exe (PID: 2588)
- csc.exe (PID: 4380)
INFO
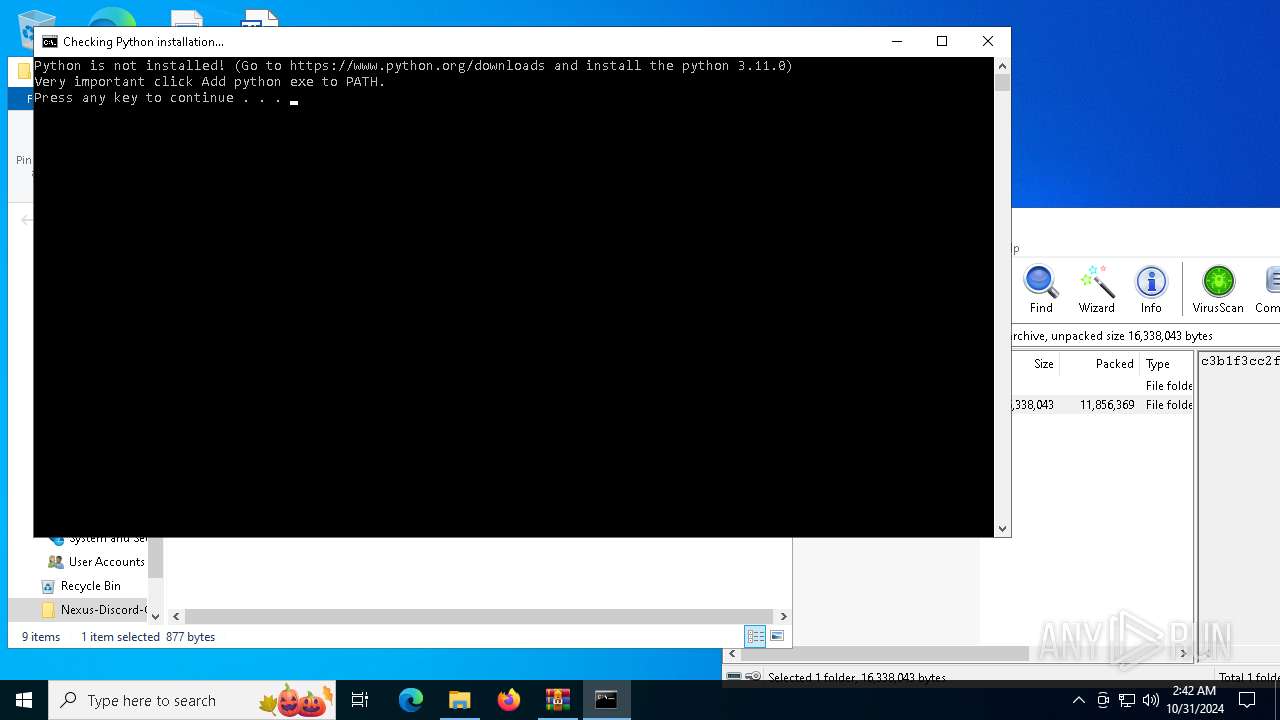
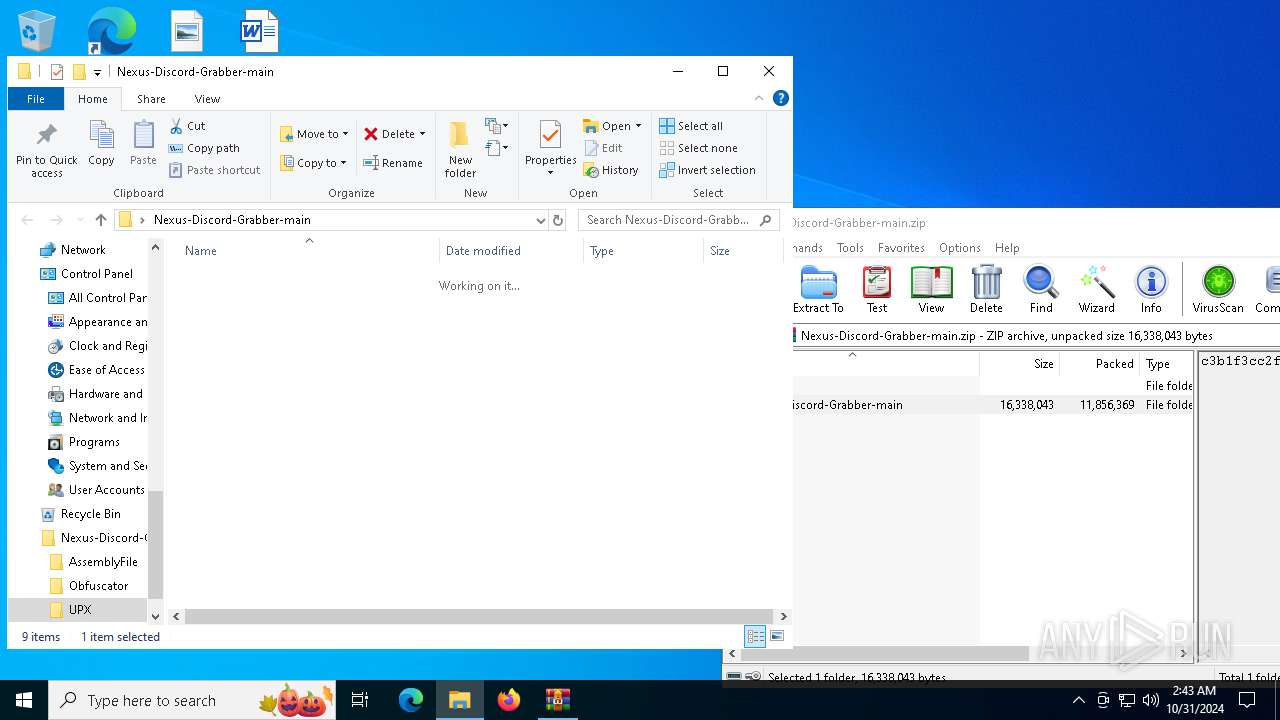
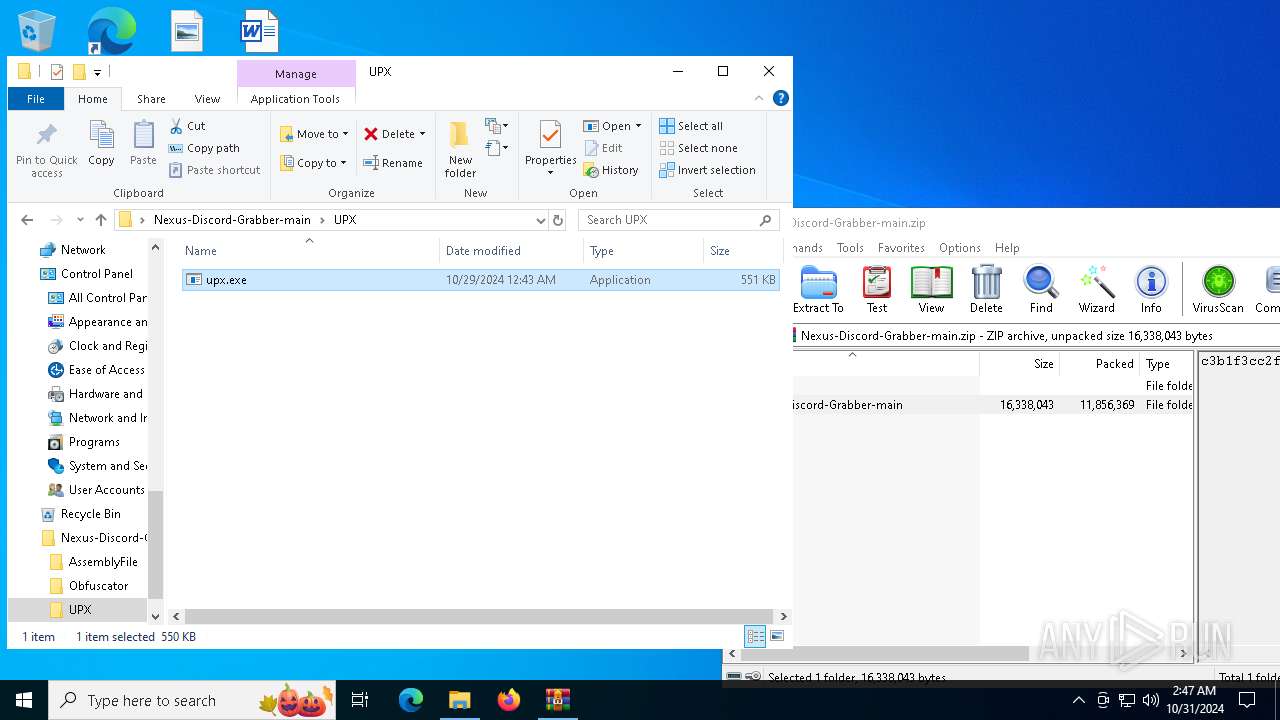
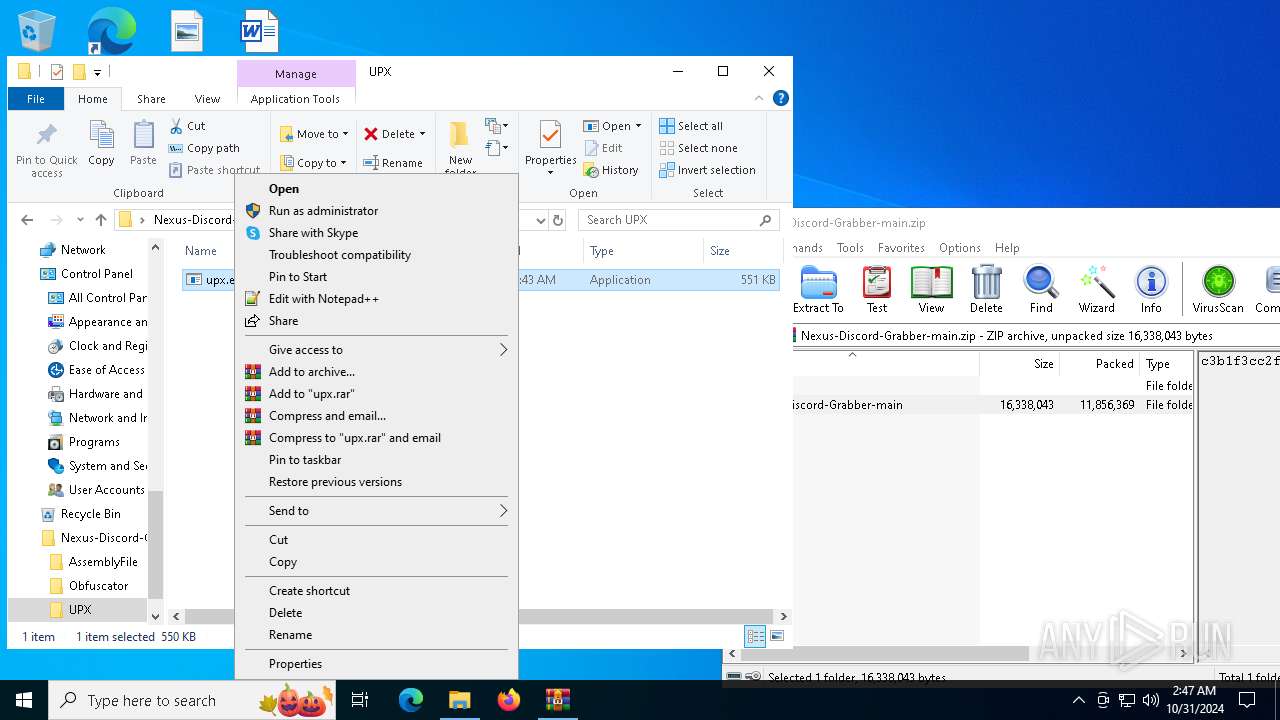
Manual execution by a user
- cmd.exe (PID: 2736)
- Nexus.exe (PID: 4548)
- Nexus.exe (PID: 6324)
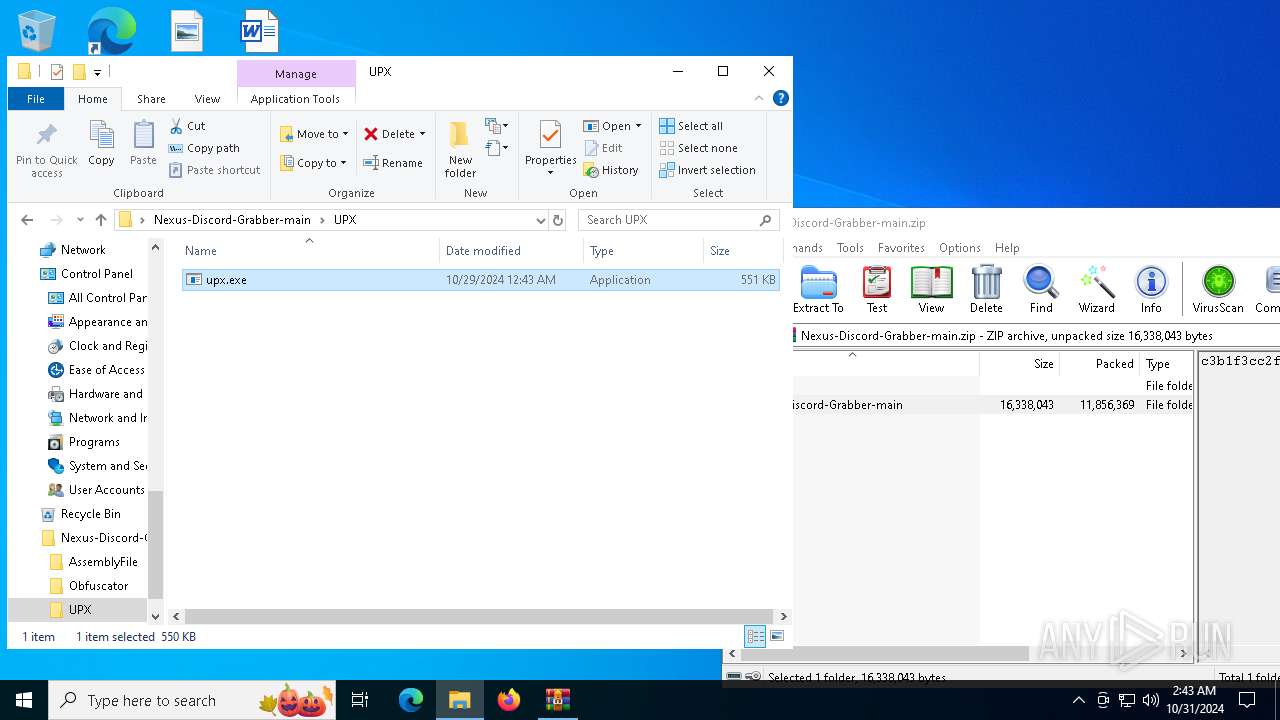
- upx.exe (PID: 6168)
- upx.exe (PID: 6964)
- Nexus.exe (PID: 1048)
- cmd.exe (PID: 3128)
- upx.exe (PID: 4568)
- upx.exe (PID: 3944)
- upx.exe (PID: 6772)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6708)
The process uses the downloaded file
- WinRAR.exe (PID: 6708)
Checks supported languages
- Nexus.exe (PID: 4548)
- Nexus.exe (PID: 7140)
Reads the computer name
- Nexus.exe (PID: 4548)
Create files in a temporary directory
- Nexus.exe (PID: 4548)
- Nexus.exe (PID: 7140)
Checks operating system version
- Nexus.exe (PID: 7140)
- Nexus.exe (PID: 6176)
- Nexus.exe (PID: 6636)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 5324)
- WMIC.exe (PID: 3732)
- WMIC.exe (PID: 4816)
The Powershell gets current clipboard
- powershell.exe (PID: 2140)
- powershell.exe (PID: 2724)
- powershell.exe (PID: 4208)
Changes the display of characters in the console
- cmd.exe (PID: 3792)
- cmd.exe (PID: 3728)
- cmd.exe (PID: 5220)
- cmd.exe (PID: 2576)
- cmd.exe (PID: 6320)
- cmd.exe (PID: 3828)
Prints a route via ROUTE.EXE
- ROUTE.EXE (PID: 5172)
- ROUTE.EXE (PID: 5612)
- ROUTE.EXE (PID: 6176)
Attempting to use instant messaging service
- Nexus.exe (PID: 7140)
- svchost.exe (PID: 2172)
- Nexus.exe (PID: 6176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xpi | | | Mozilla Firefox browser extension (66.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (33.3) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:10:28 17:43:56 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Nexus-Discord-Grabber-main/ |
Total processes
417
Monitored processes
287
Malicious processes
11
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 204 | C:\WINDOWS\system32\cmd.exe /c "gdb --version" | C:\Windows\System32\cmd.exe | — | Nexus.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 204 | wmic logicaldisk get caption,description,providername | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 608 | C:\WINDOWS\system32\cmd.exe /c "wmic csproduct get uuid" | C:\Windows\System32\cmd.exe | — | Nexus.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 692 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 764 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 944 | net user guest | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 944 | C:\WINDOWS\system32\cmd.exe /c "reg add HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run /v "Exela Update Service" /t REG_SZ /d "C:\Users\admin\AppData\Local\ExelaUpdateService\Exela.exe" /f" | C:\Windows\System32\cmd.exe | — | Nexus.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1048 | net user | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1048 | reg add HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run /v "Exela Update Service" /t REG_SZ /d "C:\Users\admin\AppData\Local\ExelaUpdateService\Exela.exe" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1048 | "C:\Users\admin\Desktop\Nexus-Discord-Grabber-main\Nexus.exe" | C:\Users\admin\Desktop\Nexus-Discord-Grabber-main\Nexus.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Exela Services Exit code: 0 Version: 10.0.19041.746 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
52 811
Read events
52 791
Write events
20
Delete events
0
Modification events
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Nexus-Discord-Grabber-main.zip | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6612) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Exela Update Service |
Value: C:\Users\admin\AppData\Local\ExelaUpdateService\Exela.exe | |||
| (PID) Process: | (6808) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdHigh |
Value: 31140670 | |||
| (PID) Process: | (6808) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdLow |
Value: | |||
| (PID) Process: | (4792) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
105
Suspicious files
58
Text files
146
Unknown types
0
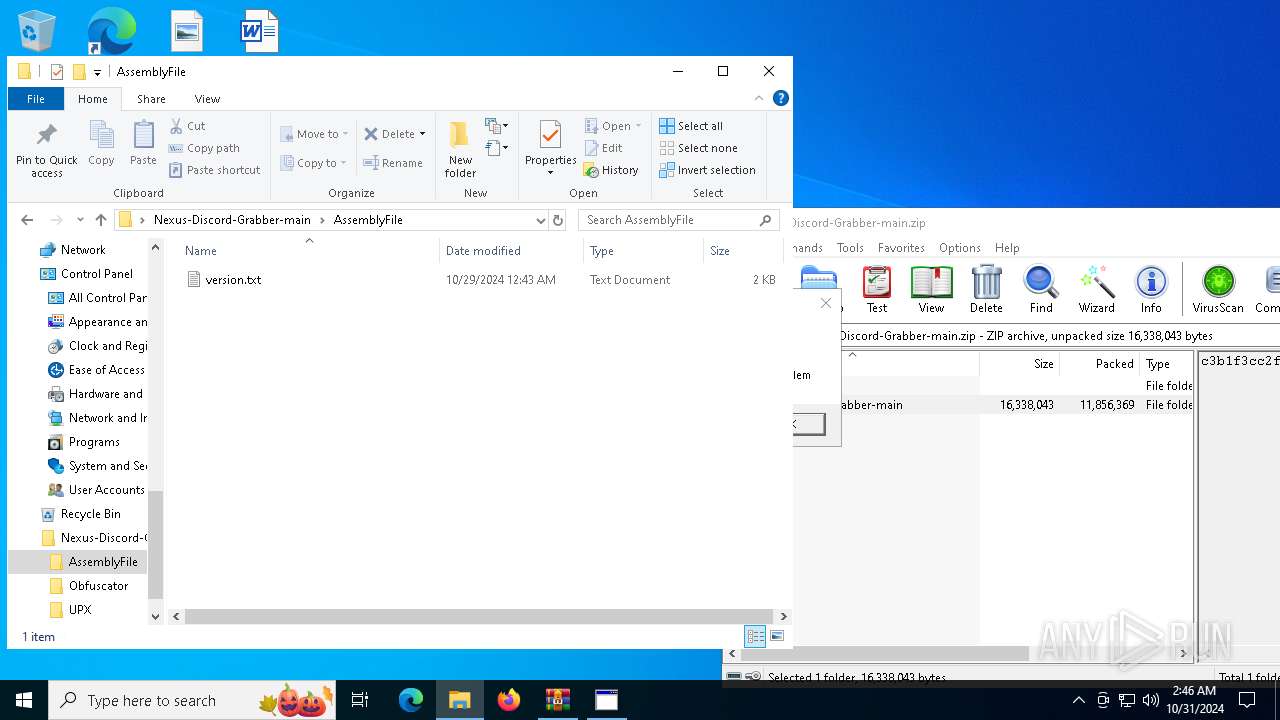
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
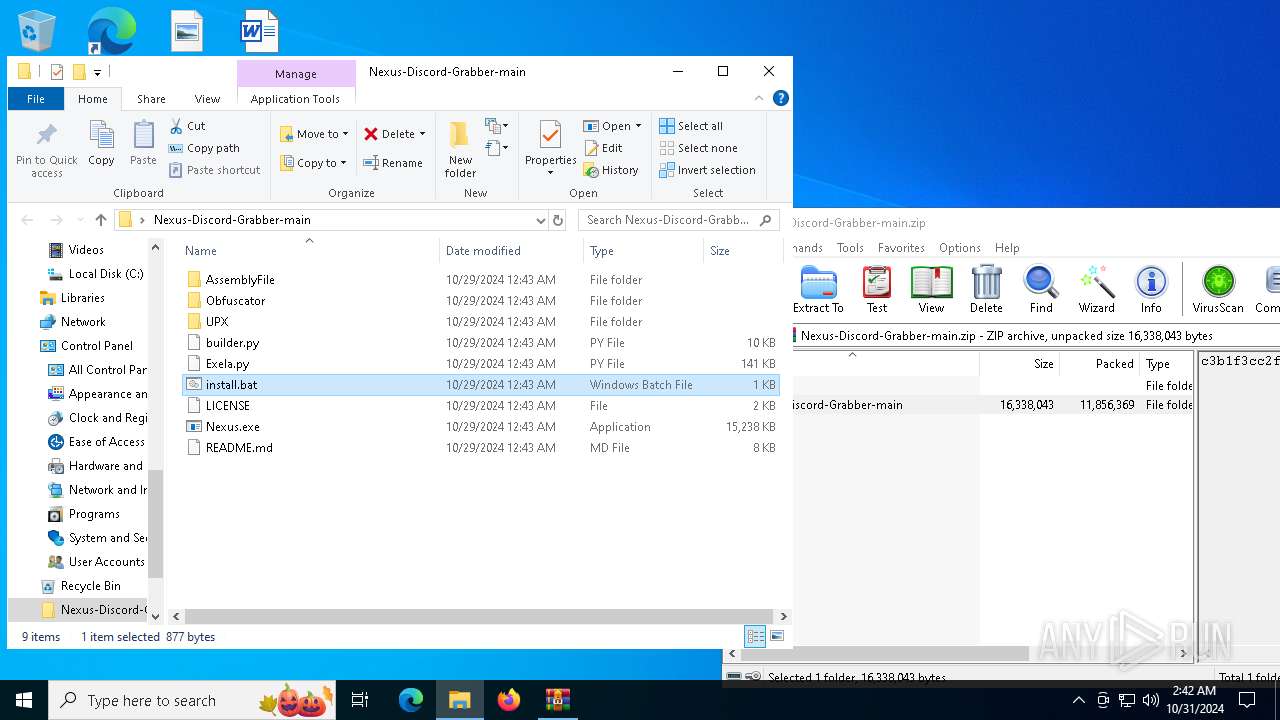
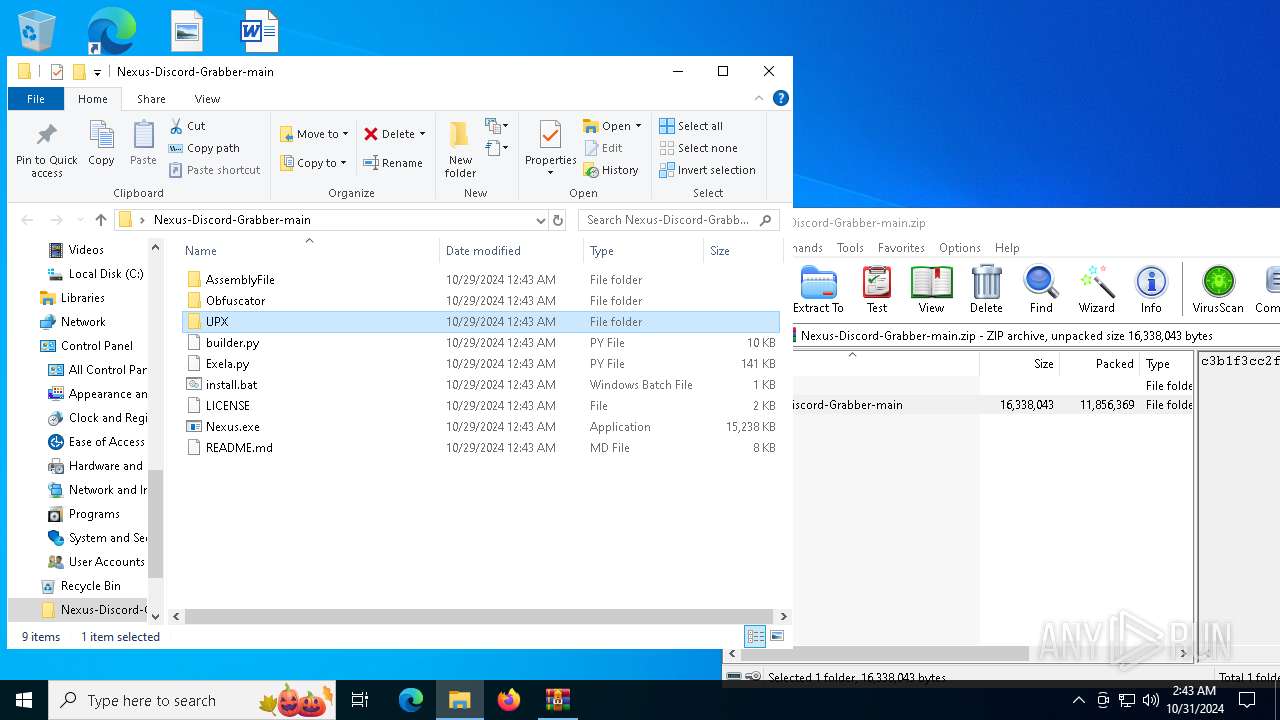
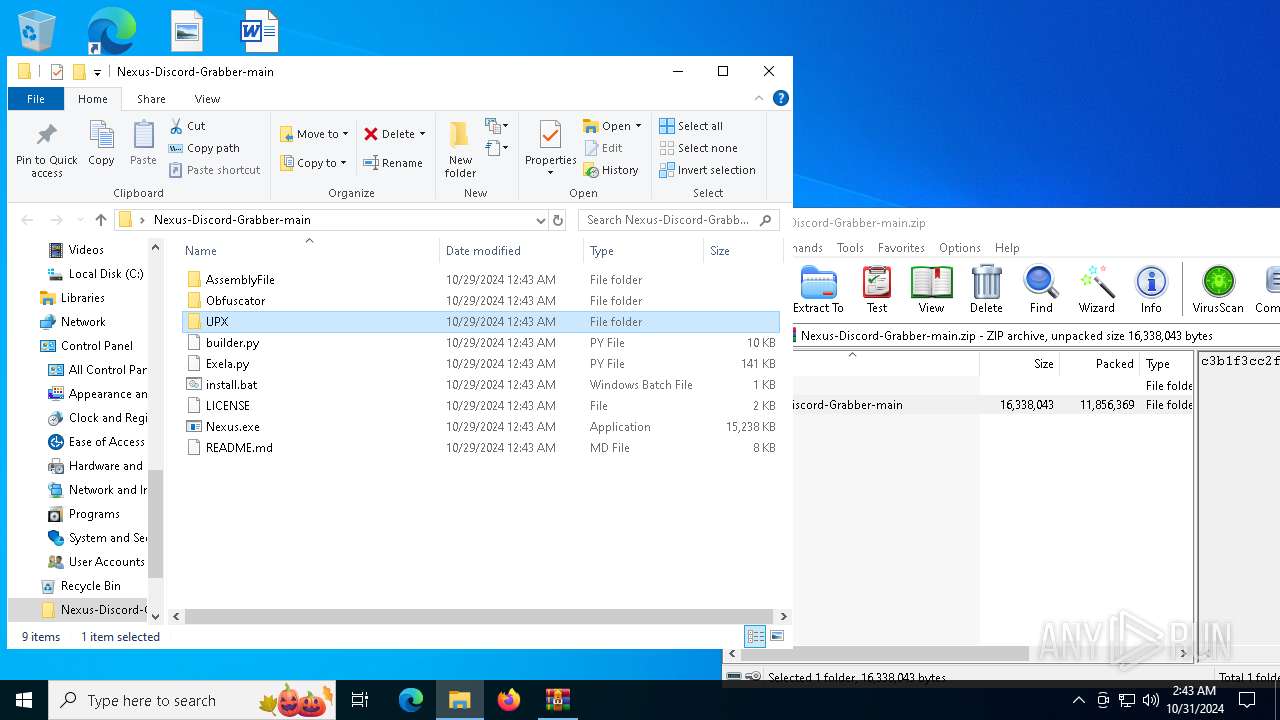
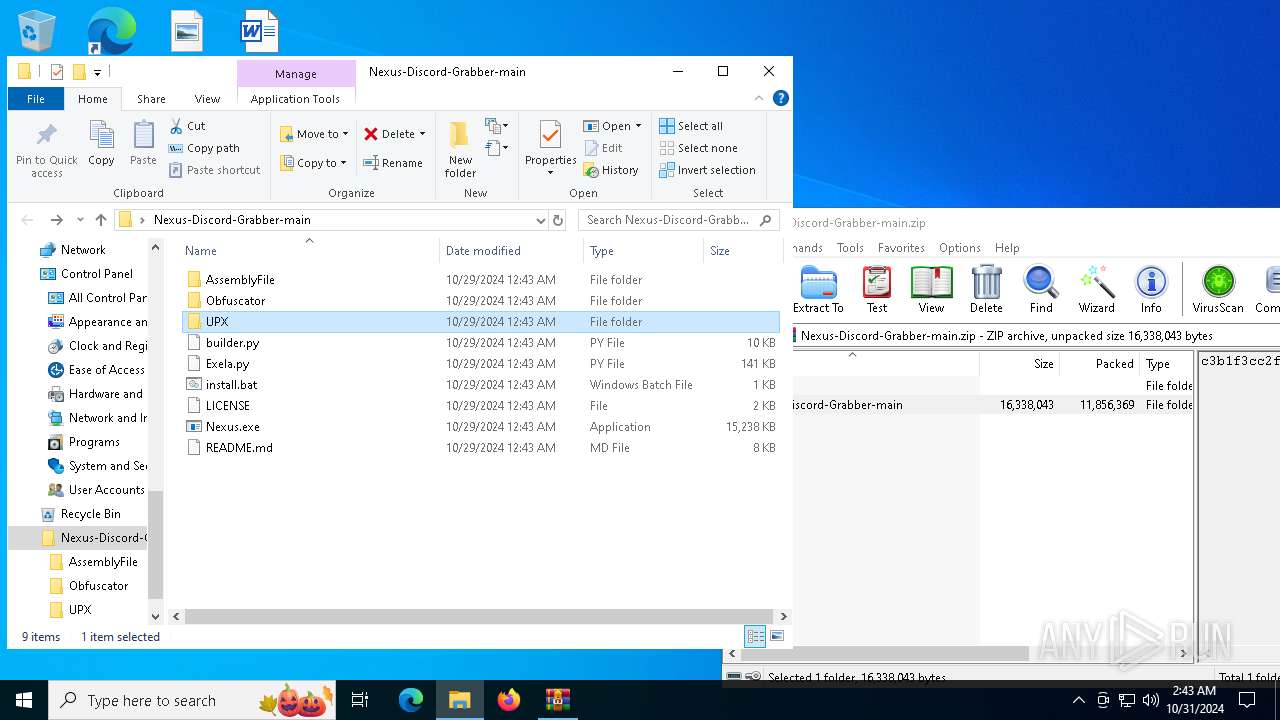
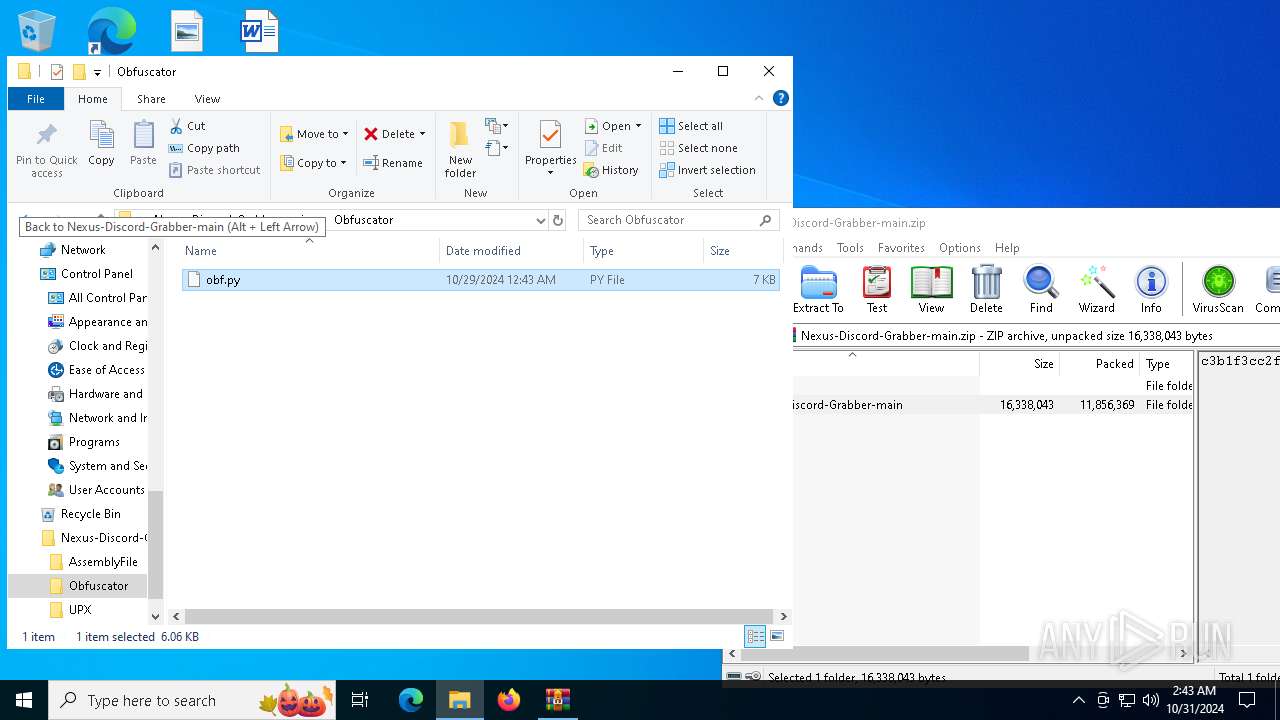
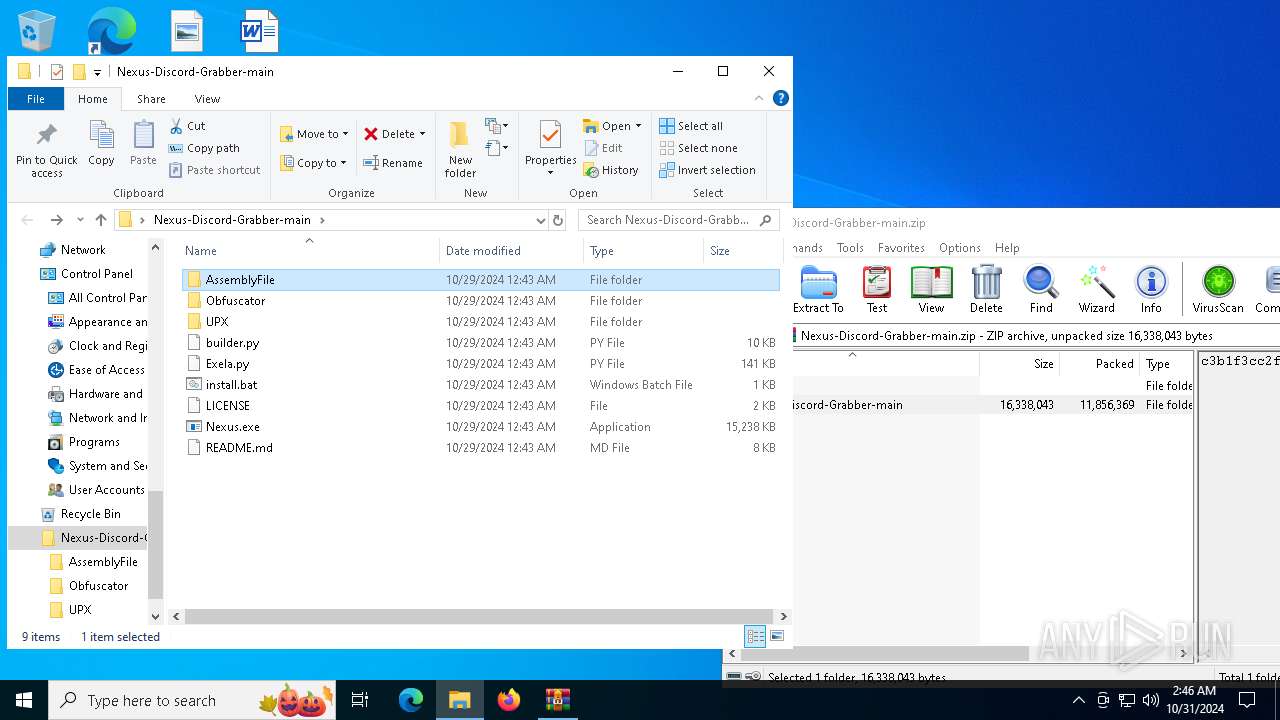
| 6708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6708.35838\Nexus-Discord-Grabber-main\Obfuscator\obf.py | text | |
MD5:BFBF108641C41832AC8584A6B85960CC | SHA256:2BA721B0F3311123399CFA098502AD53CFA4E8E0FE6CE0DE65ED2C84EA1C1101 | |||
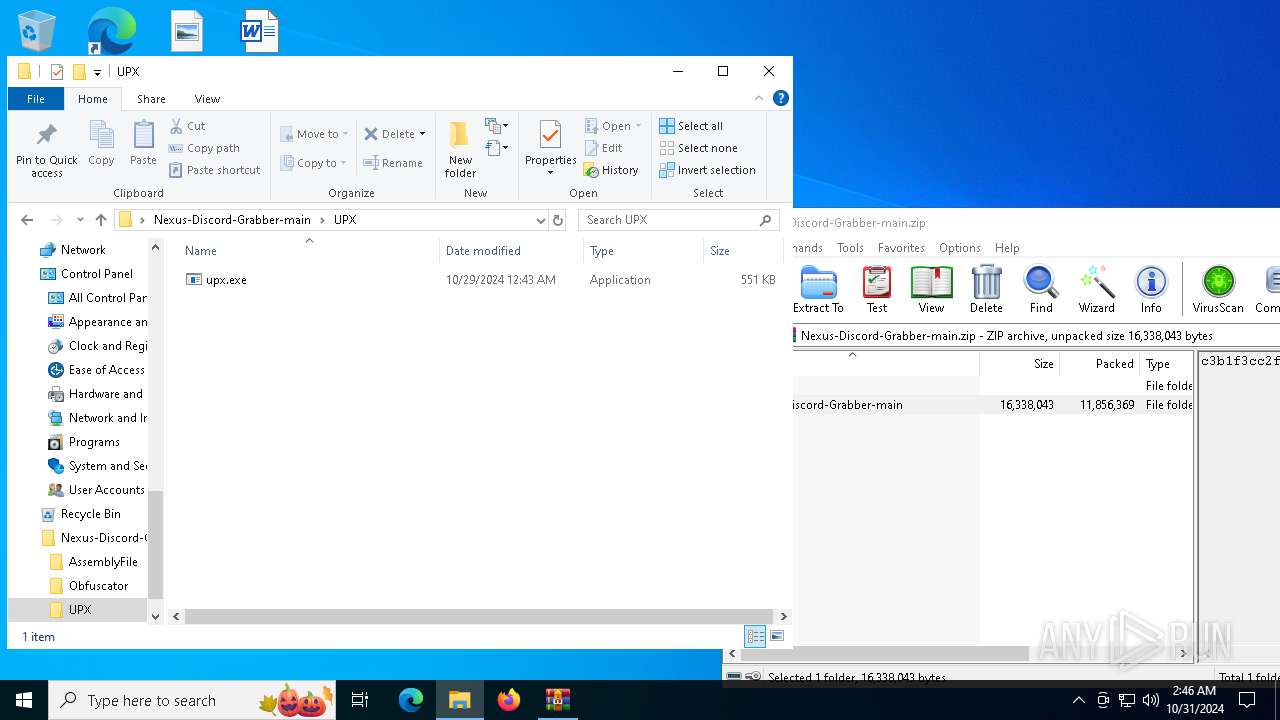
| 6708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6708.35838\Nexus-Discord-Grabber-main\UPX\upx.exe | executable | |
MD5:39ECDF78CB357513D1FD565C5E9EDBDD | SHA256:1EA92DA93EEAF4D456114B847B9BDDFB47EF854E7C24143F290D5E3F44973E91 | |||
| 6708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6708.35838\Nexus-Discord-Grabber-main\install.bat | text | |
MD5:CD480B40656A01015F5C7E16832D3384 | SHA256:C2863C67203376C14E8F2C64E16F65185D2F1272C75FE9D6B43F301AD1181D64 | |||
| 6708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6708.35838\Nexus-Discord-Grabber-main\builder.py | text | |
MD5:C334E5C6DBDC27F8E8B48D1DAC286F23 | SHA256:27EBC271F47BD76B63B5F3AA36B7F0587F3BD543C9CA5E0E89719DF54EF82F73 | |||
| 4548 | Nexus.exe | C:\Users\admin\AppData\Local\Temp\_MEI45482\_decimal.pyd | executable | |
MD5:E9501519A447B13DCCA19E09140C9E84 | SHA256:6B5FE2DEA13B84E40B0278D1702AA29E9E2091F9DC09B64BBFF5FD419A604C3C | |||
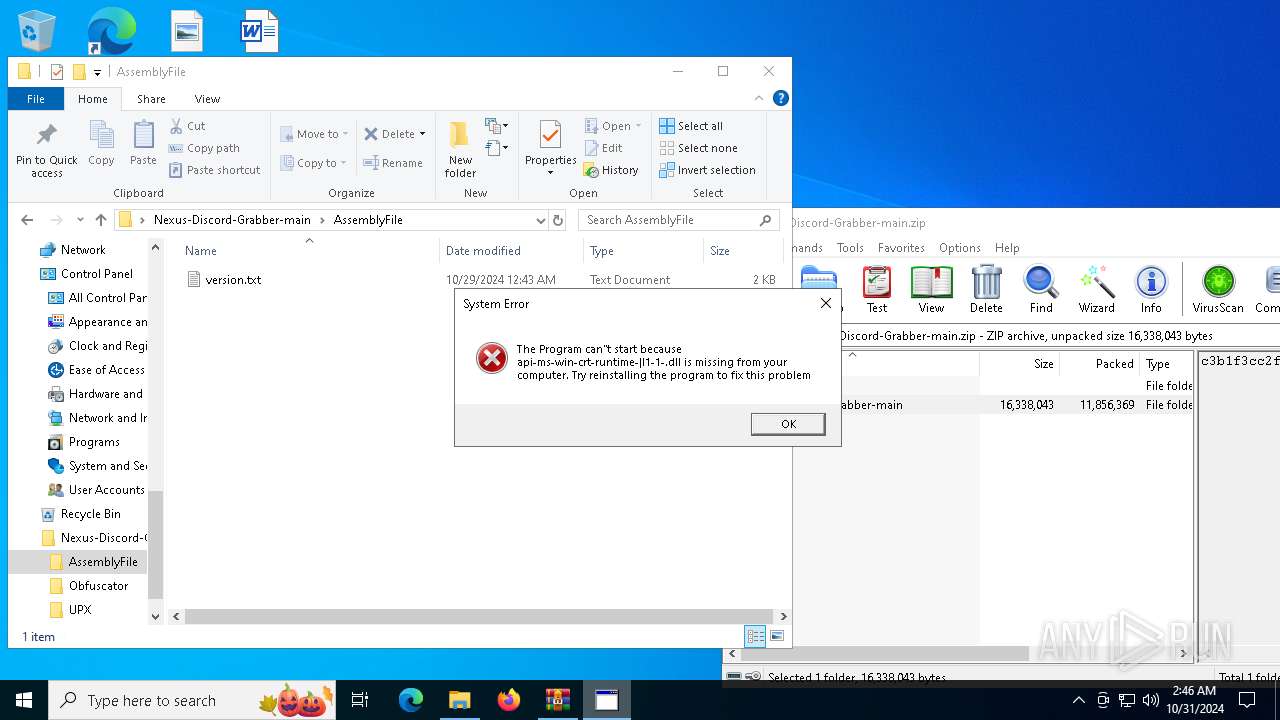
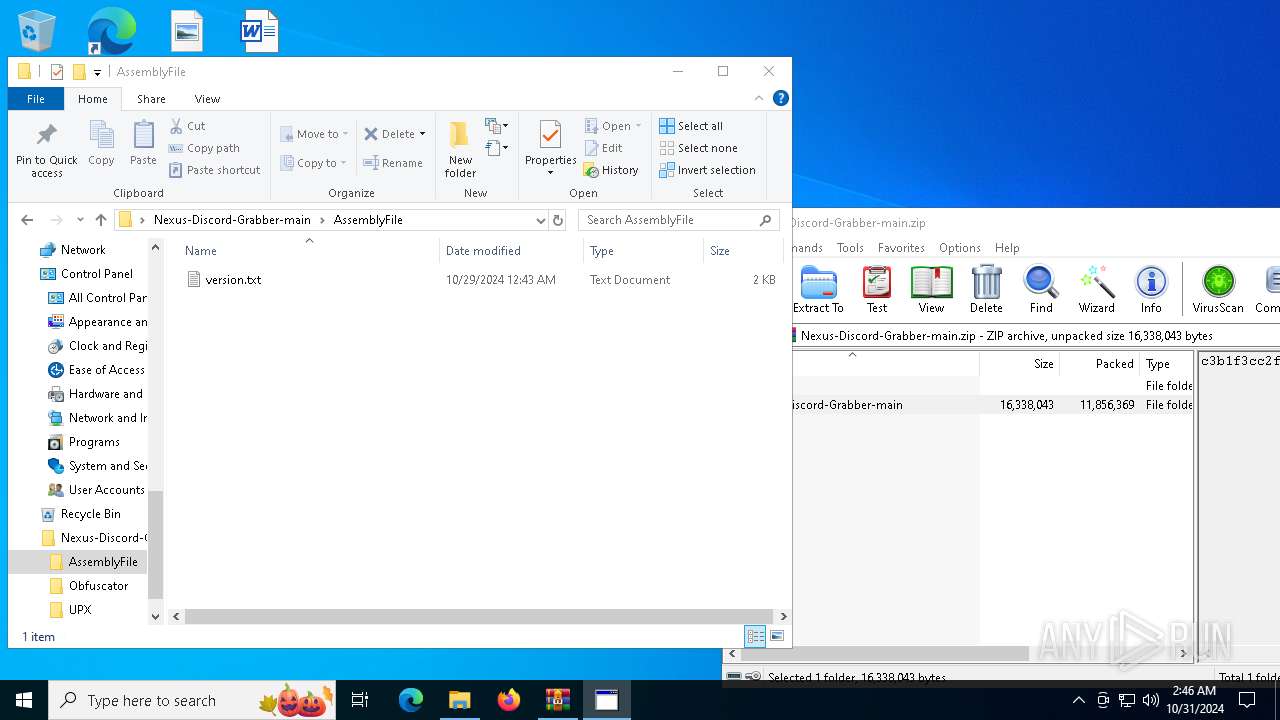
| 6708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6708.35838\Nexus-Discord-Grabber-main\AssemblyFile\version.txt | text | |
MD5:B13F73267D6A3E865A941BF7BB817D19 | SHA256:5C7DA4BF53B1EBDA26683C75E5C03D1D062683D4F1AF10DB939BA334787136CF | |||
| 4548 | Nexus.exe | C:\Users\admin\AppData\Local\Temp\_MEI45482\_asyncio.pyd | executable | |
MD5:1B8CE772A230A5DA8CBDCCD8914080A5 | SHA256:FA5A1E7031DE5849AB2AB5A177E366B41E1DF6BBD90C8D2418033A01C740771F | |||
| 6708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6708.35838\Nexus-Discord-Grabber-main\README.md | html | |
MD5:92F35B73494F790F3CFCC626EDC85A89 | SHA256:D3A83FE61CF00C21CB49480037AA455D169A0018858200089B5CA6D2E8D1D095 | |||
| 6708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6708.35838\Nexus-Discord-Grabber-main\Exela.py | text | |
MD5:53D0F2EDF910D03BF6A5B2A2806ADF02 | SHA256:FF0B26B330F3BDDC1A9EBA6DAE2BC4F8609FC85592F8F3C6344F2907A7A57CF9 | |||
| 4548 | Nexus.exe | C:\Users\admin\AppData\Local\Temp\_MEI45482\_ctypes.pyd | executable | |
MD5:B4C41A4A46E1D08206C109CE547480C7 | SHA256:9925AB71A4D74CE0CCC036034D422782395DD496472BD2D7B6D617F4D6DDC1F9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
64
DNS requests
26
Threats
28
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.20.245.138:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.20.245.138:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2776 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6676 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
3728 | SIHClient.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3728 | SIHClient.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 2.23.209.130:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.20.245.138:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
5488 | MoUsoCoreWorker.exe | 2.20.245.138:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
— | — | 23.32.185.131:80 | www.microsoft.com | AKAMAI-AS | BR | whitelisted |
6944 | svchost.exe | 23.32.185.131:80 | www.microsoft.com | AKAMAI-AS | BR | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.32.185.131:80 | www.microsoft.com | AKAMAI-AS | BR | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
7140 | Nexus.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
2172 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
2172 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
7140 | Nexus.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
7140 | Nexus.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
2172 | svchost.exe | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
2172 | svchost.exe | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
7140 | Nexus.exe | Misc activity | ET INFO File Sharing Related Domain in TLS SNI (gofile .io) |
7140 | Nexus.exe | Misc activity | ET INFO File Sharing Related Domain in TLS SNI (gofile .io) |