| File name: | gen.exe |
| Full analysis: | https://app.any.run/tasks/352034dc-37c3-48b5-a729-b29848590059 |
| Verdict: | Malicious activity |
| Threats: | njRAT is a remote access trojan. It is one of the most widely accessible RATs on the market that features an abundance of educational information. Interested attackers can even find tutorials on YouTube. This allows it to become one of the most popular RATs in the world. |
| Analysis date: | November 07, 2023, 02:01:15 |
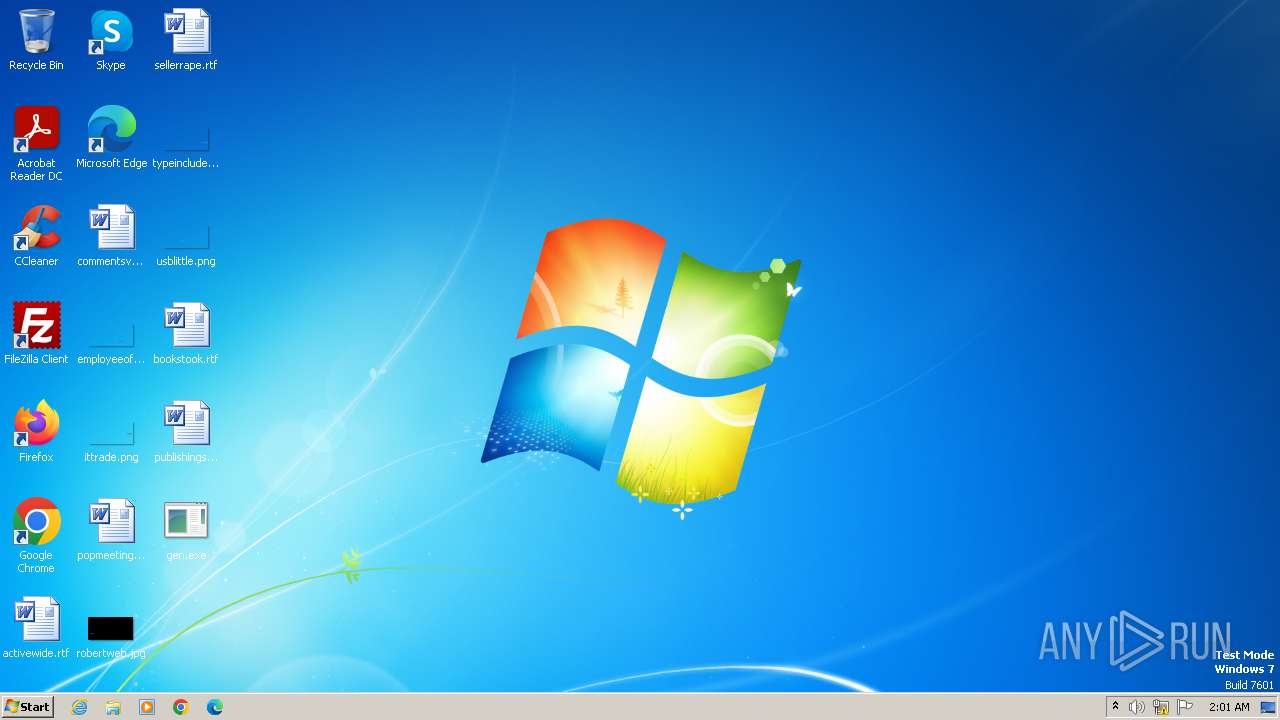
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 68ED0A1064123B9ABA449E8CF2DEBD86 |
| SHA1: | FDD292DF0F27C2D7F74F3A0C184E001AC9639FFB |
| SHA256: | AD04D48501EC9C2B5C9DF5BACAFA466A0BF1556FAD39BB472EB4CB6B83813532 |
| SSDEEP: | 768:oGqU0ObFtjXIf0NvcJqqiD8ZuSNuPkcI:A5O5dXG0dc8E3NQ |
MALICIOUS
NJRAT has been detected (YARA)
- gen.exe (PID: 3440)
Drops the executable file immediately after the start
- gen.exe (PID: 3440)
Create files in the Startup directory
- gen.exe (PID: 3440)
NjRAT is detected
- gen.exe (PID: 3440)
Changes the autorun value in the registry
- gen.exe (PID: 3440)
SUSPICIOUS
Uses NETSH.EXE to add a firewall rule or allowed programs
- gen.exe (PID: 3440)
INFO
Checks supported languages
- gen.exe (PID: 3440)
Reads the computer name
- gen.exe (PID: 3440)
Creates files or folders in the user directory
- gen.exe (PID: 3440)
Reads the machine GUID from the registry
- gen.exe (PID: 3440)
Reads Environment values
- gen.exe (PID: 3440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
NjRat
(PID) Process(3440) gen.exe
C2127.0.0.1
Ports27019
BotnetHacKed
Options
Auto-run registry keySoftware\Microsoft\Windows\CurrentVersion\Run\c0647cf3b0571461e91cc5a5a0a788fc
Splitter|'|'|
Versionim523
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:09:01 14:02:35+02:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 35840 |
| InitializedDataSize: | 1536 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xabae |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
38
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2904 | netsh firewall add allowedprogram "C:\Users\admin\Desktop\gen.exe" "gen.exe" ENABLE | C:\Windows\System32\netsh.exe | — | gen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3440 | "C:\Users\admin\Desktop\gen.exe" | C:\Users\admin\Desktop\gen.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
NjRat(PID) Process(3440) gen.exe C2127.0.0.1 Ports27019 BotnetHacKed Options Auto-run registry keySoftware\Microsoft\Windows\CurrentVersion\Run\c0647cf3b0571461e91cc5a5a0a788fc Splitter|'|'| Versionim523 | |||||||||||||||
Total events
862
Read events
793
Write events
69
Delete events
0
Modification events
| (PID) Process: | (2904) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3440) gen.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | c0647cf3b0571461e91cc5a5a0a788fc |
Value: "C:\Users\admin\Desktop\gen.exe" .. | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3440 | gen.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\c0647cf3b0571461e91cc5a5a0a788fc.exe | executable | |
MD5:68ED0A1064123B9ABA449E8CF2DEBD86 | SHA256:AD04D48501EC9C2B5C9DF5BACAFA466A0BF1556FAD39BB472EB4CB6B83813532 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |