| File name: | SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003 |
| Full analysis: | https://app.any.run/tasks/aacb4a7d-e18e-4cc6-b330-bccc6ecad7fa |
| Verdict: | Malicious activity |
| Threats: | RedLine Stealer is a malicious program that collects users’ confidential data from browsers, systems, and installed software. It also infects operating systems with other malware. |
| Analysis date: | December 02, 2023, 12:34:51 |
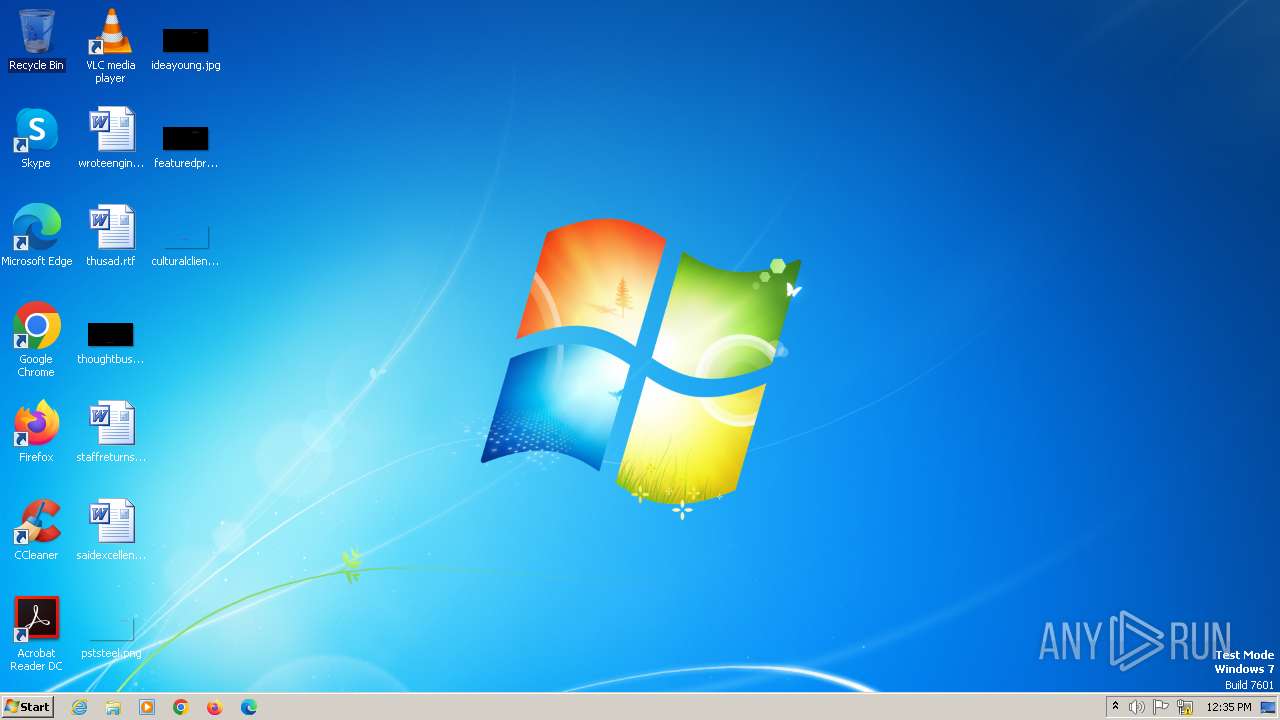
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A3DEA4C1F895C2729505CB4712AD469D |
| SHA1: | FDFEEBAB437BF7F97FB848CD67ABEC9409ADB3B2 |
| SHA256: | ACFA700A776EF8622839FD22F3BCCA3E7183E3EE2E21473CA0D9CCDC895C4AFD |
| SSDEEP: | 98304:wc838d8UFdeT3b5rT1fSEtD+ZEoY6c0BLW17vbgYpWCSYNGeAvOcGxYdT7UIxu76:fCzBMN |
MALICIOUS
REDLINE has been detected (YARA)
- SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe (PID: 1092)
Steals credentials from Web Browsers
- SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe (PID: 1092)
REDLINE has been detected (SURICATA)
- SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe (PID: 1092)
Connects to the CnC server
- SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe (PID: 1092)
Actions looks like stealing of personal data
- SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe (PID: 1092)
SUSPICIOUS
Reads the BIOS version
- SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe (PID: 1092)
Searches for installed software
- SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe (PID: 1092)
Connects to unusual port
- SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe (PID: 1092)
Reads browser cookies
- SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe (PID: 1092)
INFO
Reads the computer name
- SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe (PID: 1092)
Checks supported languages
- SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe (PID: 1092)
Reads Environment values
- SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe (PID: 1092)
Reads the machine GUID from the registry
- SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe (PID: 1092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
RedLine
(PID) Process(1092) SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe
C2 (1)38.47.221.193:34368
Botnet55000
Options
ErrorMessage
Keys
XorEyres
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2080:10:05 20:52:03+02:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 180224 |
| InitializedDataSize: | 640000 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6e15a0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
33
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1092 | "C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe" | C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
RedLine(PID) Process(1092) SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe C2 (1)38.47.221.193:34368 Botnet55000 Options ErrorMessage Keys XorEyres | |||||||||||||||
Total events
1 783
Read events
1 771
Write events
0
Delete events
12
Modification events
| (PID) Process: | (1092) SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFilesHash |
Value: 431F34506088F43C96011C9426A8E4E300D38B70FE602C9A9286D4F96B7E6642 | |||
| (PID) Process: | (1092) SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFiles0000 |
Value: C:\Users\admin\AppData\Local\Google\Chrome\User Data\lockfile | |||
| (PID) Process: | (1092) SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (1092) SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | SessionHash |
Value: 81CDE163600D314B282A5DC42C8A08BE506CAD03E9B2C9BEE4D18F7E85BD3ABD | |||
| (PID) Process: | (1092) SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Owner |
Value: 44040000528400021C25DA01 | |||
| (PID) Process: | (1092) SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1092) SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFilesHash |
Value: 4B2B9199446CC820B2CDD82F616C82782D306435603D643FAE1B2B936537A062 | |||
| (PID) Process: | (1092) SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFiles0000 |
Value: C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\lockfile | |||
| (PID) Process: | (1092) SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | SessionHash |
Value: 36020CFD8E1683A47AA719CB01AE8EEE4511FF972E1ECBD5B8FA4D4B19D342EC | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
7
DNS requests
2
Threats
25
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
324 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1956 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1092 | SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe | 38.47.221.193:34368 | — | COGENT-174 | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1092 | SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe | Potentially Bad Traffic | ET INFO Microsoft net.tcp Connection Initialization Activity |
1092 | SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] RedLine Stealer Family Related (MC-NMF Authorization) |
1092 | SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |
1092 | SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC - Id1Response |
1092 | SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |
1092 | SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |
1092 | SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe | A Network Trojan was detected | ET MALWARE Redline Stealer Family Activity (Response) |
1092 | SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |
1092 | SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe | Successful Credential Theft Detected | SUSPICIOUS [ANY.RUN] Clear Text Password Exfiltration Atempt |
1092 | SecuriteInfo.com.BScope.Trojan.Wacatac.22459.11003.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |