| File name: | EE832E95A4563886C665E7696A7D5067.exe |
| Full analysis: | https://app.any.run/tasks/d1750f65-e5f7-45d9-8143-60d84e2b4145 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
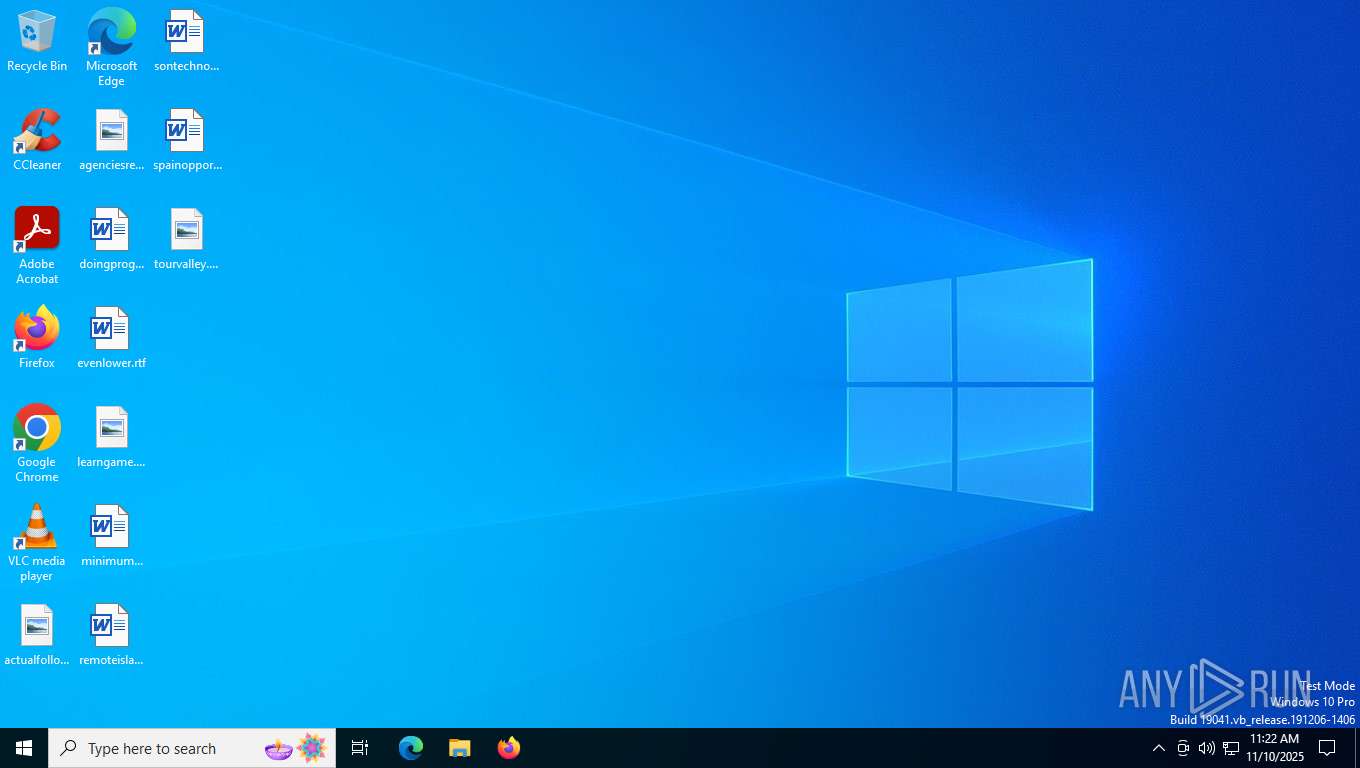
| Analysis date: | November 10, 2025, 11:22:16 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | EE832E95A4563886C665E7696A7D5067 |
| SHA1: | DFB805F1097BF493C00C715E938CCF212E2E9DC2 |
| SHA256: | ACBBF07DFBB725ED594CD0037385855DDADD11DD64C630019CE9E4D603369995 |
| SSDEEP: | 49152:57Y4DFaJB6yiBRiV3a9kMw7JOehcdGP3rwZpv4FsuX7Y4DFaJB6yiBRiV3a9kMwZ:26bj9kfQdGKp086bj9kfQdGKpVrtx1PS |
MALICIOUS
Changes the autorun value in the registry
- EE832E95A4563886C665E7696A7D5067.exe (PID: 7376)
ASYNCRAT has been detected (YARA)
- reuntime.exe (PID: 7676)
ASYNCRAT has been detected (SURICATA)
- reuntime.exe (PID: 7676)
SUSPICIOUS
Starts CMD.EXE for commands execution
- EE832E95A4563886C665E7696A7D5067.exe (PID: 7376)
Executing commands from a ".bat" file
- EE832E95A4563886C665E7696A7D5067.exe (PID: 7376)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7576)
Executable content was dropped or overwritten
- EE832E95A4563886C665E7696A7D5067.exe (PID: 7376)
The executable file from the user directory is run by the CMD process
- reuntime.exe (PID: 7720)
Contacting a server suspected of hosting an CnC
- reuntime.exe (PID: 7676)
Connects to unusual port
- reuntime.exe (PID: 7676)
INFO
Checks supported languages
- EE832E95A4563886C665E7696A7D5067.exe (PID: 7376)
- reuntime.exe (PID: 7676)
- reuntime.exe (PID: 7720)
Reads the computer name
- EE832E95A4563886C665E7696A7D5067.exe (PID: 7376)
- reuntime.exe (PID: 7676)
- reuntime.exe (PID: 7720)
Create files in a temporary directory
- EE832E95A4563886C665E7696A7D5067.exe (PID: 7376)
Reads the machine GUID from the registry
- EE832E95A4563886C665E7696A7D5067.exe (PID: 7376)
- reuntime.exe (PID: 7676)
- reuntime.exe (PID: 7720)
Launching a file from a Registry key
- EE832E95A4563886C665E7696A7D5067.exe (PID: 7376)
Creates files or folders in the user directory
- EE832E95A4563886C665E7696A7D5067.exe (PID: 7376)
Manual execution by a user
- reuntime.exe (PID: 7676)
Reads the software policy settings
- reuntime.exe (PID: 7676)
- slui.exe (PID: 2192)
Found Base64 encoded reference to WMI classes (YARA)
- reuntime.exe (PID: 7676)
Checks proxy server information
- slui.exe (PID: 2192)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(7676) reuntime.exe
C2 (2)Seznam.accesscam.org
rony.publicvm.com
Ports (3)6606
7707
8808
Version0.5.6D
BotnetDefault
Options
AutoRuntrue
Mutexiwpthvhbvqqlkqvpw
InstallFolder%AppData%
BSoDfalse
AntiVMfalse
Certificates
Cert1MIIE8jCCAtqgAwIBAgIQANHIVSbkZWNBHEaLabW7PzANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjAxMjI2MTMyNzU4WhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBALf+x830ty99anTQ0lvzEEVA57PH4vyK7TsrCexPEzERBmGPqpXmZdzXOZm9EYCt3BrT+7yhQqIe...
Server_SignatureJiYbCVhWppRB/8fZI3A3fNdZe9W8o4AfjQ7q4oVPc5MTTBgmsW5mhXZ9FPfx5RMpeEH7nIpgcoHsO7JFbb7PBlyI0vUwTQAO7YGjTOWpcPJ4thDIJO6AAhKBdDCXQYXAFAKSYrl3BVkheLCS+guItaPBcQLNMqHAVq83s/4mKDKK2LVnYk50D9MrYchmPBR+DRkojZ7rucDbll7e8/LGHOpfoxlm3h0hsVO2oQy7SkyCecWvHI5w8tCv6EeiZdE2umpwOHsN9E2tVIy21d6JoP5vjnE/s1t5Fpl4KjXvAD7g...
Keys
AESb7b731db9c8554b76f685d72462a56f45fdba7f50fc4babcf2c6389f1417986e
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:11:06 16:28:58+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 993792 |
| InitializedDataSize: | 1206272 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xf488a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | ASHAMPOO@2025 |
| FileVersion: | 1.0.0.0 |
| InternalName: | ASHAMPOO@2025.exe |
| LegalCopyright: | Copyright © 2025 |
| OriginalFileName: | ASHAMPOO@2025.exe |
| ProductName: | ASHAMPOO@2025 |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
153
Monitored processes
8
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2192 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2276 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7376 | "C:\Users\admin\AppData\Local\Temp\EE832E95A4563886C665E7696A7D5067.exe" | C:\Users\admin\AppData\Local\Temp\EE832E95A4563886C665E7696A7D5067.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: ASHAMPOO@2025 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 7576 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\tmp302D.tmp.bat"" | C:\Windows\SysWOW64\cmd.exe | — | EE832E95A4563886C665E7696A7D5067.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7600 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7648 | timeout 3 | C:\Windows\SysWOW64\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7676 | "C:\Users\admin\AppData\Roaming\reuntime.exe" | C:\Users\admin\AppData\Roaming\reuntime.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: ASHAMPOO@2025 Version: 1.0.0.0 Modules
AsyncRat(PID) Process(7676) reuntime.exe C2 (2)Seznam.accesscam.org rony.publicvm.com Ports (3)6606 7707 8808 Version0.5.6D BotnetDefault Options AutoRuntrue Mutexiwpthvhbvqqlkqvpw InstallFolder%AppData% BSoDfalse AntiVMfalse Certificates Cert1MIIE8jCCAtqgAwIBAgIQANHIVSbkZWNBHEaLabW7PzANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjAxMjI2MTMyNzU4WhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBALf+x830ty99anTQ0lvzEEVA57PH4vyK7TsrCexPEzERBmGPqpXmZdzXOZm9EYCt3BrT+7yhQqIe... Server_SignatureJiYbCVhWppRB/8fZI3A3fNdZe9W8o4AfjQ7q4oVPc5MTTBgmsW5mhXZ9FPfx5RMpeEH7nIpgcoHsO7JFbb7PBlyI0vUwTQAO7YGjTOWpcPJ4thDIJO6AAhKBdDCXQYXAFAKSYrl3BVkheLCS+guItaPBcQLNMqHAVq83s/4mKDKK2LVnYk50D9MrYchmPBR+DRkojZ7rucDbll7e8/LGHOpfoxlm3h0hsVO2oQy7SkyCecWvHI5w8tCv6EeiZdE2umpwOHsN9E2tVIy21d6JoP5vjnE/s1t5Fpl4KjXvAD7g... Keys AESb7b731db9c8554b76f685d72462a56f45fdba7f50fc4babcf2c6389f1417986e Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941 | |||||||||||||||
| 7720 | "C:\Users\admin\AppData\Roaming\reuntime.exe" | C:\Users\admin\AppData\Roaming\reuntime.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: ASHAMPOO@2025 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
7 838
Read events
7 837
Write events
1
Delete events
0
Modification events
| (PID) Process: | (7376) EE832E95A4563886C665E7696A7D5067.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | reuntime |
Value: "C:\Users\admin\AppData\Roaming\reuntime.exe" | |||
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7376 | EE832E95A4563886C665E7696A7D5067.exe | C:\Users\admin\AppData\Local\Temp\tmp302D.tmp.bat | text | |
MD5:B652496C0048EF213F74AC5BD4869089 | SHA256:A1D3189051E962C318EC823742894326C89B204DB864CCACE9DD10CF748C9856 | |||
| 7376 | EE832E95A4563886C665E7696A7D5067.exe | C:\Users\admin\AppData\Roaming\reuntime.exe | executable | |
MD5:EE832E95A4563886C665E7696A7D5067 | SHA256:ACBBF07DFBB725ED594CD0037385855DDADD11DD64C630019CE9E4D603369995 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
25
DNS requests
18
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2388 | svchost.exe | GET | 200 | 95.101.35.8:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5892 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
3080 | svchost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5892 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | — | — | whitelisted |
5892 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
5892 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2388 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5596 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3548 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7088 | SearchApp.exe | 2.16.204.150:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2388 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2388 | svchost.exe | 95.101.35.8:80 | crl.microsoft.com | Orange | NL | whitelisted |
7676 | reuntime.exe | 64.225.11.206:8808 | rony.publicvm.com | DIGITALOCEAN-ASN | US | malicious |
3080 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
rony.publicvm.com |
| malicious |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2276 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS Observed DNS Query to DynDNS Domain (publicvm .com) |
7676 | reuntime.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
7676 | reuntime.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT/zgRAT Style SSL Cert |
7676 | reuntime.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT Server) |
7676 | reuntime.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |